Multiple-Input Multiple-Output Gaussian Broadcast Channels with Common and Confidential Messages
This paper considers the problem of the multiple-input multiple-output (MIMO) Gaussian broadcast channel with two receivers (receivers 1 and 2) and two messages: a common message intended for both receivers and a confidential message intended only fo…
Authors: Hung D. Ly, Tie Liu, Yingbin Liang
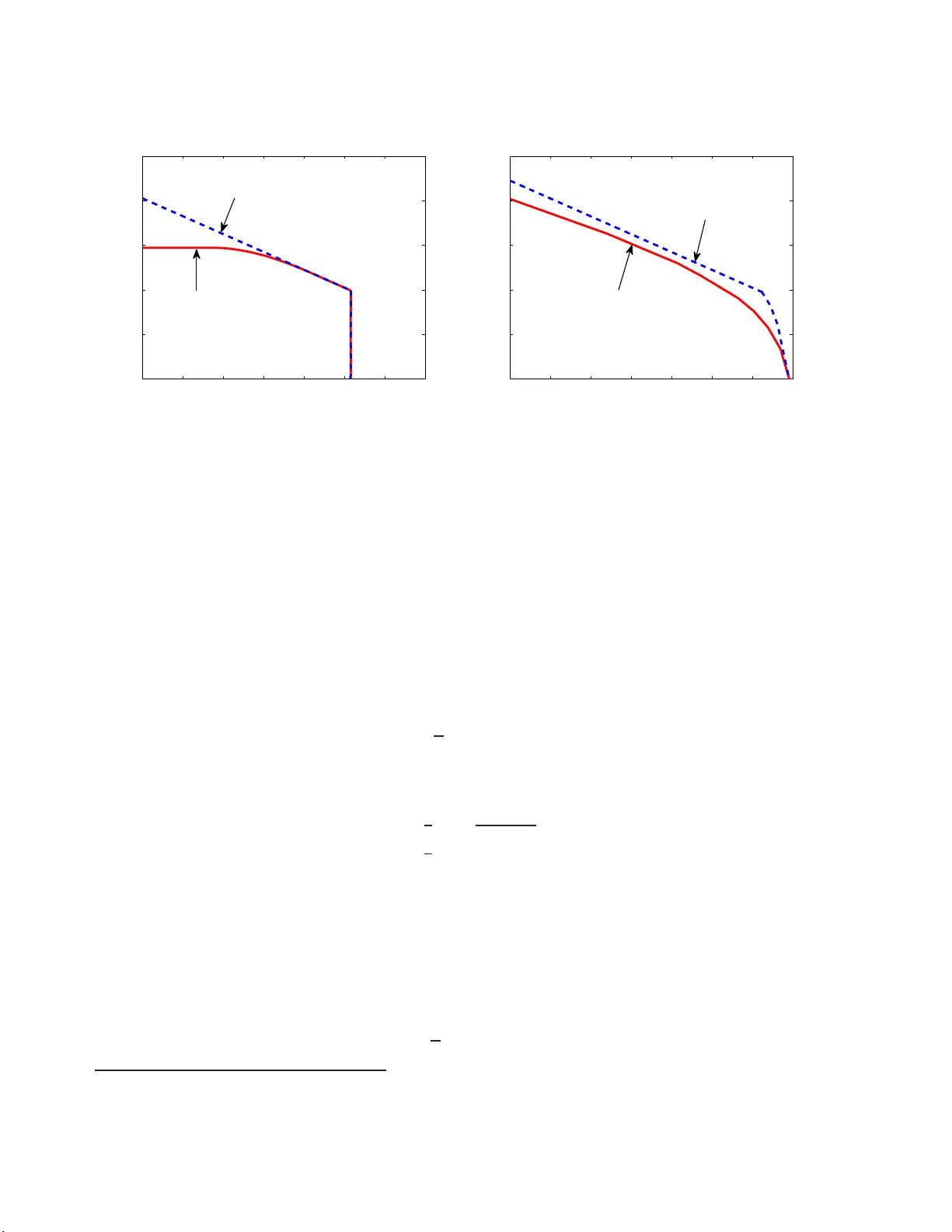
Multiple-Input Multiple-Output Gaussian Broadcast Channels with Common and Confiden tial Messages Hung D. Ly , Tie Liu, and Yi ngbin Liang ∗ Octob er 29 , 2018 Abstract This paper co nsiders the problem of the m ultiple-input multiple- output (MIMO) Gaussian broadcast c hann el with t wo receiv ers (receiv ers 1 and 2) and t wo messages: a common message intended for b oth receiv ers and a confid en tial message inte nded only for rec eiv er 1 b u t needing to b e k ept asymptotic ally p erfectly secure from receiv er 2. A matrix c haracterization of the secrecy capac it y region is established via a c hannel enhancemen t a rgumen t. The enhanced c h an n el is constru cted by first splitting r eceiv er 1 in to t w o virtual receiv ers and then enhancing only the virtual receiv er that deco des the confi d en tial message. The secrecy capacit y region of the enhan ced channel is c h ar- acterized using an extremal entrop y inequ alit y p reviously established for charac terizing the capacit y regio n of a degraded comp oun d MIMO Gaussian b roadcast channel. 1 In tro duction Understanding the fundamen ta l limits of mu ltiple-input multiple-output (MIMO) secrecy comm unication is an imp ortant researc h topic in wireless ph ysical lay er securit y . A basic mo del of MIMO secrecy comm unicatio n is a MIMO Gaussian broadcast c hannel with tw o receiv ers, for whic h the c hannel o utputs at time in dex m a re giv en b y Y k [ m ] = H k X [ m ] + Z k [ m ] , k = 1 , 2 (1) where H k is the (real) channel matrix of size r k × t for receiv er k , and { Z k [ m ] } m is an indep enden t and iden tically distributed (i.i.d.) additiv e v ector Gaussian noise pro cess with ∗ The material of this pa per was presented in par t at the International Sympo sium o n I nfo r mation Theo ry and Its Applications (ISIT A), Auckland, New Zealand, December 2008. Hung D. Ly and Tie Liu are with the Department of Electrical and Computer Engineering , T exas A&M Universit y , College Station, TX 778 43, USA (e-mail: { h ungly ,tieliu } @tamu.edu). Yingbin Liang is with the Department of E lectrical Engineer ing, Univ ersity of Haw aii, Honolulu, HI 96 822, USA (e-mail: yingbinl@hawaii.edu). 1 Transmitter Receiver 1 Receiver 2 X n Y n 1 ( ˆ W 0 , ˆ W 1 ) Y n 2 ˆ W 0 ( W 0 , W 1 ) 1 n I ( W 1 ; Y n 2 ) → 0 H 1 Z n 1 i.i.d ∼ N ( 0 , I r 1 ) H 2 Z n 2 i.i.d ∼ N ( 0 , I r 2 ) (a) Th e general case Receiver 1 Receiver 2 Transmitter Y n 1 ( ˆ W 0 , ˆ W 1 ) Y n 2 ˆ W 0 1 n I ( W 1 ; Y n 2 ) → 0 X n ( W 0 , W 1 ) Z n 1 i.i.d ∼ N ( 0 , N 1 ) Z n 2 i.i.d ∼ N ( 0 , N 2 ) (b) The aligned case Figure 1: MIMO Gaussian broadcast c hannel w ith common and confiden tial mes sages. zero mean and iden tity cov ariance matrix. The channel input { X [ m ] } m is sub ject to an a v erage total p o wer constrain t: 1 n n X m =1 k X [ m ] k 2 ≤ P . (2) The transmitter has a set of tw o indep enden t messages ( W 0 , W 1 ), where W 0 is a common message in tended for b oth receiv ers 1 and 2, and W 1 is a confiden tia l message in tended for receiv er 1 but needing to be k ept secret fr o m receiv er 2. The confiden t ia lit y of message W 1 at receiv er 2 is measured using the info rmation-theoretic criterion [1, 2]: 1 n I ( W 1 ; Y n 2 ) → 0 (3) where Y n 2 := ( Y 2 [1] , . . . , Y 2 [ n ]), and the limit is taken as the blo c klength n → ∞ . An illus- tration of this communic ation scenario is sho wn in F igure 1(a ). The goal is to c haracterize the entire rate region C s ( H 1 , H 2 , P ) that includes all rate pairs ( R 0 , R 1 ) t hat can b e achie v ed b y any co ding sche me. In this pap er, w e term C s ( H 1 , H 2 , P ) as the se cr e cy c ap ac i ty r e gion despite the fa ct that W 0 is not a confiden tial message. In their seminar w ork [2], Csisz´ ar and K¨ orner considered the discrete memoryles s case of the problem. A single -letter expression of the sec recy capacit y region w a s given as the set of nonnegativ e rate pairs ( R 0 , R 1 ) satisfying R 0 ≤ min [ I ( U ; Y 1 ) , I ( U ; Y 2 )] R 1 ≤ I ( V ; Y 1 | U ) − I ( V ; Y 2 | U ) (4) 2 for some p ( u , v , x, y 1 , y 2 ) = p ( u ) p ( v | u ) p ( x | v ) p ( y 1 , y 2 | x ), whe re p ( y 1 , y 2 | x ) is the transition probabilit y of the discrete memoryless broadcast ch annel. Th us, in principle, the secrecy capacit y region C s ( H 1 , H 2 , P ) can b e computed b y ev aluat ing the Csisz´ ar-K¨ orner region (4) for the MIMO G aussian broadcast ch annel (1 ) . Ho wev er, directly ev aluating (4) for the MIMO Gaussian broadcast c hannel (1) app ears difficult due to the presence o f the auxiliary v ar ia bles U and V . Consider, for example, the sp ecial case where the common message W 0 is absen t, i.e., R 0 = 0. Let U b e deterministic in (4). Then, the maxim um of R 1 can b e determined b y solving the optimization pro g ram max p ( x,v ) [ I ( V ; Y 1 ) − I ( V ; Y 2 )] . (5) In literature, the problem of comm unicating a confidential message o v er a MIMO Gaussian broadcast c hannel is termed as the MIMO Gaussian wiretap channel problem. Characterizing the secrecy capacity of the MIMO Gaussian wiretap c hannel has b een an a ctiv e area of researc h in recen t y ears. Ho we v er, despite intens iv e effort [3, 4, 5, 6, 7], determining the secrecy capacit y of the MIMO G aussian wiretap c hannel via dir e ctly solving the optimization program (5) remains in tractable. Recen tly , Khisti and W ornell [5] a nd Ogg ier and Hassibi [6] studied the MIMO Gaus- sian wiretap c hannel pro blem and pro p osed an indir e ct approac h to solv e the o ptimizatio n program (5). The main idea w as to compute an upp er b ound on the secrecy capacit y b y considering a fictitious MIMO Gaussian wiretap c hannel in which the legitimate receiv er has access to b oth receiv ed signals { Y 1 [ m ] } m and { Y 2 [ m ] } m . F or an y fixed correlation b et w een the additiv e no ise Z 1 [ m ] a nd Z 2 [ m ], Khisti and W o r nell [5] a nd Oggier and Hassibi [6] sho wed that Gaussian ra ndom binning without prefix co ding is optimal fo r the fictitious c hannel. Comparing the upp er b ound (minimized o v er a ll p ossible correlations b et w een Z 1 [ m ] and Z 2 [ m ]) with the ac hiev able secrecy rate b y c ho osing a Gaussian V = X in the o b jective func- tion of (5) established an exact matrix c haracterization of the secrecy capacit y . H o w ev er, matc hing the upp er and low er b ounds requires complicated matrix analysis, whic h mak es the approac h difficult to extend to the more general scenario with b o th common and confiden tial messages. More recen tly , Liu a nd Shamai [7] presen ted an a lternativ e, simpler characterization o f the secrecy capa city of the MIMO Gaussian wiretap c ha nnel. Compared with the w or k of [5] and [6], there are t w o k ey differences in the arg umen t o f [7] 1. Instead of the a ve rage total p o w er constraint (2), [7] considered the more general matrix p o w er constraint: 1 n n X m =1 X [ m ] X T [ m ] S (6) where S is a p ositiv e semidefinite matrix, and “ ” denotes “less than or equal to” in the p ositiv e semidefinite ordering b etw een real symmetric mat rices. 2. Different from the Sat o -lik e [8] argumen t o f [5] and [6], the upp er b ound on the secrecy capacit y in [7] w as obtained by considering an enha nc e d MIM O G aussian wiretap 3 c hannel that has the same secrecy capacit y as the or ig inal wiretap channel. Channel- enhancemen t argumen t w as first in tro duce d b y W eingarten et al. [9] t o ch aracterize the private message capacit y r egio n of the MIMO Gaussian broadcast c hannel; [7] w as the first to a pply this ar g umen t t o MIMO se cr e cy comm unication problems. The main goal of this pap er is to a dapt the c hannel-enhancemen t argumen t of [7] to the more general problem of MIMO Gaussian broadcast channel with b oth common and confiden tial messages. Our main result is that for the MIMO G aussian broadcast c hannel (1), a jointly Gaussian ( U, V , X ) with V = X is optimal for the Csisz´ ar-K¨ orner region (4). This establishes a matrix c haracterization of the secrecy capacit y region of t he MIMO Gaussian broadcast c hannel under a matrix p o w er constrain t. The rest of the pap er is organized as f o llo ws. In Section 2, we summarize the main results of the pap er. In Section 3, w e consider the sp ecial case o f the MIMO Gaussian broadcast c hannel (1 ) in whic h t he c hannel matrices H 1 and H 2 are square and in v ertible, and use a c hannel-enhancemen t argumen t to c har a cterize the secrecy capacit y region. In Section 4 , w e broaden the result of Section 3, via a limiting a rgumen t, t o the g eneral case, and c ha r acterize the secrecy capacit y region of the g eneral MIMO Gaussian broadcast channel. Finally , in Section 5, we pro vide some numeric al examples to illustrate the main results of t he pap er. 2 Main Resul ts The following theorem summarizes the secrecy capacit y region of the MIMO Gaussian broad- cast c hannel with common and confiden tial messages under a matrix p ow er constrain t. Theorem 1. The se cr e cy c ap acity r e gion C s ( H 1 , H 2 , S ) of the MIMO Gaussian br o adc ast channel ( 1 ) with m essages W 0 (intende d for b o th r e c eivers 1 and 2) and W 1 (intende d for r e c eiver 1 but n e e ding to b e kept asymptotic al ly p erfe ctly se cr et fr om r e c eiver 2) under the matrix p ower c onstr aint (6) is given by the set of al l no nne gative r ate p airs ( R 0 , R 1 ) satisfying R 0 ≤ min 1 2 log H 1 SH T 1 + I r 1 H 1 BH T 1 + I r 1 , 1 2 log H 2 SH T 2 + I r 2 H 2 BH T 2 + I r 2 R 1 ≤ 1 2 log H 1 BH T 1 + I r 1 − 1 2 log H 2 BH T 2 + I r 2 (7) for some 0 B S . Her e , I r k denotes the iden tity m atrix of size r k × r k . As men tioned previously , the MIMO Gaussian wiretap channel problem can b e considered as a sp ecial case here with the common rate R 0 = 0. W e hav e th us reco v ered t he ma in result of [7], restated b elo w as a corollary . Corollary 2 ([7]) . The se cr e cy c ap acity C s ( H 1 , H 2 , S ) of the MIMO Gaussian br o adc a s t channel (1) with a c onfidential message mes s ages W (intende d for r e c eiver 1 but ne e ding to b e ke pt a symptotic al ly p erfe c tly se cr et fr om r e c eiver 2) unde r the matrix p ower c o n str aint (6) is given by C s ( H 1 , H 2 , S ) = max 0 B S 1 2 log H 1 BH T 1 + I r 1 − 1 2 log H 2 BH T 2 + I r 2 . (8) 4 In engineering practice, it is particularly relev an t to consider the av erage total p o w er constrain t. The follo wing coro lla ry summarizes the secrecy capacit y r egio n of the MIMO Gaussian broadcast channel with common and confiden tial messages under an a v erage total p o w er constrain t. The result is a simple consequence of [9, Lemma 1]. Corollary 3. The se cr e cy c ap aci ty r e gion C s ( H 1 , H 2 , P ) of the MIMO Gaussian br o adc ast channel ( 1 ) with m essages W 0 (intende d for b o th r e c eivers 1 and 2) and W 1 (intende d for r e c eiver 1 but n e e ding to b e kept asymptotic al ly p erfe ctly se cr et fr om r e c eiver 2) under the aver age total p ower c onstr aint (2) is given by the set of al l nonn e ga tive r ate p ai rs ( R 0 , R 1 ) satisfying R 0 ≤ min h 1 2 log H 1 ( B 1 + B 2 ) H T 1 + I r 1 H 1 B 1 H T 1 + I r 1 , 1 2 log H 2 ( B 1 + B 2 ) H T 2 + I r 2 H 2 B 1 H T 2 + I r 2 i R 1 ≤ 1 2 log H 1 B 1 H T 1 + I r 1 − 1 2 log H 2 B 1 H T 2 + I r 2 (9) for some p o s itive se m idefinite matric es B 1 and B 2 with T r ( B 1 + B 2 ) ≤ P . The ac hiev ability pro of of Theorem 1 follow s from the Csisz´ ar-K¨ orner region (4) b y letting U b e a t -dimensional G aussian v ector with zero mean and co v aria nce matr ix S − B and V = X = U + G , where G is a t -dimensional Gaussian ve ctor with zero mean and co v ariance mat r ix B and is indep enden t of U . Note that prefix co ding is not needed in comm unicating the confiden t ia l message W 1 ev en though the corresp onding ea ve sdropp er c hannel may not b e degraded with resp ect to t he legitimate receiv er c hannel. The conv erse of Theorem 1 follow s from an adapta t ion of the c hannel-enhancemen t ar- gumen t of [7 ] with the following t wo new ingredien ts: 1. T o obtain an enhanced MIMO Ga ussian broadcast c hannel t hat has the same weigh ted secrecy sum-capacit y a s the original channel, w e need to split receiv er 1 in to t wo v i rtual receiv ers: one a s the legitimate receiv er f or the confiden t ial message W 1 , and the other as one of the inte nded receiv ers for the common message W 0 . Only the legitimate receiv er for t he confiden tia l message W 1 is enhanced in the pro of . 2. With only a confiden tial message, in [7], the matrix c hara cterization of the secrecy capacit y of the enhanced channel was o btained via t he worst noise result of Diggavi and Co v er [1 3]. With b o th common and confiden tial messages, c hara cterizing t he secrecy capacit y region of the enhanced c hannel b ecomes more in v olv ed. In our pro of, w e r esort to an extremal entrop y inequalit y whic h was first pro v ed b y W eingarten et al. [12] for c har acterizing the capacit y region of a degraded c omp ound MIMO Gaussian broadcast c hannel. The details of the pro of are provid ed in the next tw o sections. 3 Aligned MIMO G aus sian Broadcast Channel In this section, w e prov e Theorem 1 for the special case where the c hannel matrices H 1 and H 2 are square and inv ertible. In this case, multiply ing b o th sides of (1) b y H − 1 k , the channel 5 mo del can b e equiv alen tly written as Y k [ m ] = X [ m ] + Z k [ m ] , k = 1 , 2 (10) where { Z k [ m ] } m is an i.i.d. additiv e v ector Gaussian noise pro cess with zero mean and co v ariance matrix N k = H − 1 k H − T k . F ollowing [9], w e will term the channel mo del (1 0) a s the align e d MIMO Gaussian broa dcast c hannel (see F igure 1(b)) and (1) as the ge ner a l MIMO G aussian bro adcast c hannel. The main result of t his section is summarized in the following theorem. Theorem 4. Th e se cr e cy c ap acity r e gion C s ( N 1 , N 2 , S ) of the a l i g ne d MIMO Gaussian br o ad- c ast c hannel (10) with messag e s W 0 (intende d fo r b oth r e c eive rs 1 and 2) and W 1 (intende d for r e c eiver 1 b ut n e e di n g to b e kept asymptotic al ly p erfe ctly se cr et fr om r e c eiver 2) under the matrix p o w er c onstr aint (6) is gi ven by the set of al l nonne gative r ate p airs ( R 0 , R 1 ) satisfying R 0 ≤ min 1 2 log S + N 1 B + N 1 , 1 2 log S + N 2 B + N 2 R 1 ≤ 1 2 log B + N 1 N 1 − 1 2 log B + N 2 N 2 (11) for some 0 B S . Pr o o f. Let G b e a t - dimensional Ga ussian v ector with zero mean and co v ariance matrix B . Then, the a c hiev abilit y of (11) can b e obtained fro m the Csisz´ ar-K¨ orner region (4 ) b y letting U b e a t -dimensional Gaussian v ector with zero mean and co v ariance matrix S − B and V = X = U + G , where U and G are assumed to b e indep enden t. W e therefore concen trate on pro ving the con vers e result. T o sho w that an y achie v able secrecy ra te pair ( R 0 , R 1 ) for the aligned MIMO Gaussian broadcast c hannel (1 0) m ust satisfy (11) f o r some 0 B S , w e may assume, without loss o f generalit y , that the matrix p ow er constrain t S ≻ 0. F or the case where S 0 but | S | = 0, let θ = Rank ( S ) < t . W e can define a n e quivalent aligned MIMO Gaussian broadcast c hannel with θ transmit and receiv e an tennas and a new co v a riance matrix pow er constraint that is strictly p ositive definite. Hence, w e can conv ert the case where S 0, | S | = 0 to the case where S ≻ 0 with the same secrecy capacit y region. See [9, Lemma 2] for a formal presen tation of this argumen t. F or the case where S ≻ 0, we shall consider pro of b y con tradiction a s follows. Assume that ( R o 0 , R o 1 ) is an achie v able secrecy rat e pair fo r the aligned MIMO Gaussian broadcast c hannel (10) t ha t lies outside the r ate region (11). Since ( R o 0 , R o 1 ) is ac hiev able, R o 0 can b e b ounded from ab ov e as R o 0 ≤ min 1 2 log S + N 1 N 1 , 1 2 log S + N 2 N 2 = R max 0 . (12) Moreo ver, if R o 1 = 0, then R max 0 can be ac hiev ed b y letting B = 0 in (1 1). Therefore, w e can 6 write R o 1 = R ∗ 1 + δ for some δ > 0 , where R ∗ 1 is giv en by max B 1 2 log B + N 1 N 1 − 1 2 log B + N 2 N 2 sub ject to 1 2 log S + N 1 B + N 1 ≥ R o 0 1 2 log S + N 2 B + N 2 ≥ R o 0 0 B S . (13) The ab ov e optimization program can b e rewritten in the f ollo wing standard form: min B 1 2 log B + N 2 N 2 − 1 2 log B + N 1 N 1 sub ject to R o 0 − 1 2 log S + N 1 B + N 1 ≤ 0 R o 0 − 1 2 log S + N 2 B + N 2 ≤ 0 − B 0 B − S 0 (14) whic h has one semidefinite v ariable, B , constrained b y b oth scalar and semidefinite ineq ual- ities. This is in fact an optimization problem with generalized constrain t s in t he form of semidefinite inequalities [14, p. 267]. Therefore, the Karush-K uhn- T uc ker (KKT) condition states that the deriv at iv e of the La grangian L = 1 2 log B + N 2 N 2 − 1 2 log B + N 1 N 1 + P 2 k =1 µ k R o 0 − 1 2 log S + N k B + N k + T r (( − B ) M 1 ) + T r (( B − S ) M 2 ) (15) m ust v anish at an optimal solution B ∗ . 1 Here, M k , k = 1 , 2, are p o sitiv e semidefinite matrices suc h that B ∗ M 1 = 0 (16) ( S − B ∗ ) M 2 = 0 (17) and µ k ≥ 0, k = 1 , 2, with equality if 1 2 log S + N k B ∗ + N k > R o 0 . W e immediately ha v e µ k R o 0 = µ k 2 log S + N k B ∗ + N k , k = 1 , 2 . (18) T aking deriv ative of the Lagr a ngian in (15) ov er B , the KKT condition can b e written a s ∇ B 1 2 log B + N 2 N 2 − 1 2 log B + N 1 N 1 + 2 X k =1 µ k R o 0 − 1 2 log S + N k B + N k ! − M 1 + M 2 = 0 1 As this o ptimization problem is not necessarily co n vex, a set of constra in t qualifications (CQs) s ho uld be v erified to ma k e s ure that the KKT conditions indeed ho ld. The CQs stated in [9, Appendix D] hold in a trivia l manner for this optimiza tio n progr am. 7 whic h giv es 1 2 ( B ∗ + N 1 ) − 1 + M 1 = µ 1 2 ( B ∗ + N 1 ) − 1 + µ 2 + 1 2 ( B ∗ + N 2 ) − 1 + M 2 . (19) By (13 ) and (18), we ha v e R o 1 + ( µ 1 + µ 2 ) R o 0 = 1 2 log B ∗ + N 1 N 1 − 1 2 log B ∗ + N 2 N 2 + 2 X k =1 µ k 2 log S + N k B ∗ + N k + δ . (20) Next, w e shall find a con tradiction to (20 ) b y sho wing that for any a c hiev able secrecy rate pair ( R 0 , R 1 ), R 1 + ( µ 1 + µ 2 ) R 0 ≤ 1 2 log B ∗ + N 1 N 1 − 1 2 log B ∗ + N 2 N 2 + 2 X k =1 µ k 2 log S + N k B ∗ + N k . W e divide our pro o f in t o three steps. Step 1: Split receiv er 1 in to tw o virtual receiv ers. Consider the fo llo wing aligned MIMO Gaussian broa dcast c hannel with t hree receiv ers: Y 1 a [ m ] = X [ m ] + Z 1 a [ m ] Y 1 b [ m ] = X [ m ] + Z 1 b [ m ] Y 2 [ m ] = X [ m ] + Z 2 [ m ] (21) where { Z 1 a [ m ] } m , { Z 1 b [ m ] } m and { Z 2 [ m ] } m are i.i.d. additiv e v ector G aussian noise pro- cesses with zero means and cov ariance matrices N 1 , N 1 and N 2 , resp ectiv ely . Supp ose that the transmitter has tw o indep enden t messages W 0 and W 1 , where W 0 is in tended for b oth re- ceiv ers 1b and 2 and W 1 is in tended for receiv er 1 a but needs to b e ke pt secret from receiv er 2. The confiden tiality of message W 1 at receiv er 2 is measured using the info rmation-theoretic criterion (3). See Figure 2(a) for an illustration of this communic ation scenario. Note t ha t b oth receiv ers 1a and 1b in the aligned MIMO Gaussian broadcast c hannel (21) hav e the same noise co v ariance matrices as receiv er 1 in the aligned MIMO G aussian broadcast c hannel (10), a nd receiv er 2 in the aligned MIMO G aussian broadcast c ha nnel (21) has the same noise co v aria nce matrix as receiv er 2 in the aligned MIMO Gaussian broadcast c hannel (10). Therefore, any ac hiev able secrecy r a te pair ( R 0 , R 1 ) for the a lig ned MIMO Gaussian broadcast c hannel (21) can also b e ac hiev ed b y the same co ding sc heme for the aligned MIMO G aussian broadcast c hannel (10), and vice v ersa. Th us, the aligned MIMO Gaussian broa dcast c hannel (21 ) has the s a me secrecy capacit y r egio n as the a ligned MIMO Gaussian broadcast c hannel in (10) under the same p ow er constraints . Step 2: Construct an enhanced channe l. Let ˜ N 1 b e a real symmetric matrix satisfying 1 2 ( B ∗ + ˜ N 1 ) − 1 = 1 2 ( B ∗ + N 1 ) − 1 + M 1 . (22) F ollowing [9, Lemma 11], w e ha v e 0 ≺ ˜ N 1 N 1 (23) 8 Receiver 1b Receiver 2 Receiver 1a Transmitter ˆ W 0 1 n I ( W 1 ; Y n 2 ) → 0 ˆ W 0 Z n 2 i.i.d ∼ N ( 0 , N 2 ) ˆ W 1 Z n 1 b i.i.d ∼ N ( 0 , N 1 ) Z n 1 a i.i.d ∼ N ( 0 , N 1 ) Y n 2 Y n 1 b Y n 1 a X n ( W 0 , W 1 ) (a) An equiv alen t view of the aligned MIMO Gaussian broadcast c hannel sho wn in Figure 1 (b ) Receiver 1b Receiver 2 Receiver 1a Transmitter ˆ W 0 1 n I ( W 1 ; Y n 2 ) → 0 ˆ W 0 Z n 2 i.i.d ∼ N ( 0 , N 2 ) ˆ W 1 Z n 1 b i.i.d ∼ N ( 0 , N 1 ) Y n 2 Y n 1 b Y n 1 a X n ( W 0 , W 1 ) Z n 1 a i.i.d ∼ N ( 0 , ˜ N 1 ) (b) The enhanced c hannel Figure 2: Enhanced MIMO Gaussian broa dcast c hannel with common a nd confiden t ial mes- sages. and B ∗ + ˜ N 1 ˜ N 1 = B ∗ + N 1 N 1 . (24) Moreo ver, substitute (22) in to (19) a nd w e ha v e 1 2 ( B ∗ + ˜ N 1 ) − 1 = µ 1 2 ( B ∗ + N 1 ) − 1 + µ 2 + 1 2 ( B ∗ + N 2 ) − 1 + M 2 . (25) Note that ( B ∗ + N 1 ) − 1 , ( B ∗ + N 2 ) − 1 and M 2 are all p ositive semidefinite so we ha v e 1 2 ( B ∗ + ˜ N 1 ) − 1 1 2 ( B ∗ + N 2 ) − 1 and hence ˜ N 1 N 2 . (26) 9 No w consider the follow ing enhanced MIMO Gaussian broadcast c hannel (see Figure 2(b)): ˜ Y 1 a [ m ] = X [ m ] + ˜ Z 1 a [ m ] Y 1 b [ m ] = X [ m ] + Z 1 b [ m ] Y 2 [ m ] = X [ m ] + Z 2 [ m ] (27) where { ˜ Z 1 a [ m ] } m , { Z 1 b [ m ] } m and { Z 2 [ m ] } m are i.i.d. additiv e v ector G aussian noise pro- cesses with zero mean and cov a riance matrix ˜ N 1 , N 1 and N 2 , resp ectiv ely . Note fr o m (23) that ˜ N 1 N 1 . W e conclude that the secrecy capacity region of the enhanc ed MIMO Gaus- sian bro a dcast c hannel (27) is at least as larg e as the secrecy capa city region of the aligned MIMO Gaussian broadcast c ha nnel (21 ) under the same p ow er constraints . Step 3: Bound from ab ov e the weigh ted secrecy sum-capacit y of the enhanced c hannel . Note from (23 ) and (26) that 0 ≺ ˜ N 1 { N 1 , N 2 } . (28) Th us, in the enhanced MIMO Gaussian broadcast c hannel (27), the receiv ed signals Y 1 b [ m ] and Y 2 [ m ] are (sto c hastically) degraded with resp ect to the receiv ed signal Y 1 a [ m ]. In the follo wing prop osition, w e shall consider the discrete memoryless case of the enhanced ch annel (27) and provide a single-letter characterization of the secrecy capacit y region. Prop osition 1. Con s ider a discr ete memoryless br o adc ast channel with tr a nsition pr ob ab i l i ty p ( ˜ y 1 a , y 1 b , y 2 | x ) and messages W 0 (intende d for b oth r e c eivers 1 b an d 2) an d W 1 (intende d for r e c eiver 1a b ut ne e ds to b e kept c onfid ential fr o m r e c eiver 2 ) . If b oth X → ˜ Y 1 a → Y 1 b and X → ˜ Y 1 a → Y 2 form Markov chains in their r esp e ctive or der, then the se cr e c y c a p acity r e gion of this channel is given by the set of nonne gative r ate p airs ( R 0 , R 1 ) satisfying R 0 ≤ min [ I ( U ; Y 1 b ) , I ( U ; Y 2 )] R 1 ≤ I ( X ; ˜ Y 1 a | U ) − I ( X ; Y 2 | U ) (29) for some p ( u , x, ˜ y 1 a , y 1 b , y 2 ) = p ( u ) p ( x | u ) p ( ˜ y 1 a , y 1 b , y 2 | x ) . Pr o o f. The ac hiev ability of (2 9) follo ws from a co ding sc heme that com bines sup erp osition co ding [11] and ra ndom binning [1]. The conv erse pro of fo llows from the steps similar t o those in the con v erse pro of in [2]. The details of the conv erse pro of are pro vided in the App endix. Remark 1. Pr efi x c o ding is no longer ne e de d d ue to the pr e exis ting Markov r elation X → ˜ Y 1 a → Y 2 . Next, t o ev aluate the single-letter expression (29 ) for the enhanced MIMO G aussian broadcast channel (27), w e shall recall an extremal entrop y inequality whic h is a sp ecial case of [12, Corollary 4]. 10 Prop osition 2 ([12]) . L et ˜ Z 1 a , Z 1 b and Z 2 b e t -dimensional Gaussian ve ctors with zer o me ans an d c ov a rianc e matric es ˜ N 1 , N 1 and N 2 , r es p e ctivel y. Assume that ˜ N 1 , N 1 and N 2 ar e o r de r e d as in (28) . L et S b e a t × t p o sitive definite m atrix. If ther e exists a t × t r e al symmetric matrix B ∗ such that 0 B ∗ S and satisfying 1 2 ( B ∗ + ˜ N 1 ) − 1 = µλ 2 ( B ∗ + N 1 ) − 1 + µ (1 − λ ) 2 ( B ∗ + N 2 ) − 1 + M 2 ( S − B ∗ ) M 2 = 0 for some p o s itive se m idefinite matrix M 2 and r e al sc alars µ ≥ 0 an d 0 ≤ λ ≤ 1 , then h ( X + ˜ Z 1 a | U ) − µλh ( X + Z 1 b | U ) − µ (1 − λ ) h ( X + Z 2 | U ) ≤ 1 2 log | 2 π e ( B ∗ + ˜ N 1 ) | − µλ 2 log | 2 π e ( B ∗ + N 1 ) | − µ (1 − λ ) 2 log | 2 π e ( B ∗ + N 2 ) | for any ( X , U ) i n dep endent of ( ˜ Z 1 a , Z 1 b , Z 2 ) such that E [ XX T ] S . W e are now ready to b ound from ab o v e the w eigh ted secrecy sum-capacit y of the enhanced c hannel (27). By Prop osition 1, for an y ac hiev able secrecy rate pair ( R 0 , R 1 ) for the enhanced c hannel (27) we ha v e R 1 + ( µ 1 + µ 2 ) R 0 ≤ I ( X ; ˜ Y 1 a | U ) − I ( X ; Y 2 | U ) + ( µ 1 + µ 2 ) min [ I ( U ; Y 1 b ) , I ( U ; Y 2 )] ≤ I ( X ; ˜ Y 1 a | U ) − I ( X ; Y 2 | U ) + [ µ 1 I ( U ; Y 1 b ) + µ 2 I ( U ; Y 2 )] = h ( Z 2 ) − h ( ˜ Z 1 a ) + µ 1 h ( X + Z 1 b ) + µ 2 h ( X + Z 2 ) + h h ( X + ˜ Z 1 a | U ) − µ 1 h ( X + Z 1 b | U ) − ( µ 2 + 1) h ( X + Z 2 | U ) i ≤ 1 2 log | 2 π e N 2 | − 1 2 log 2 π e ˜ N 1 + 2 X k =1 h µ k 2 log | 2 π e ( S + N k ) | i + h h ( X + ˜ Z 1 a | U ) − µ 1 h ( X + Z 1 b | U ) − ( µ 2 + 1) h ( X + Z 2 | U ) i (30) where the last inequalit y follows from the fa cts that h ( ˜ Z 1 a ) = 1 2 log 2 π e ˜ N 1 , h ( Z 2 ) = 1 2 log | 2 π e N 2 | , h ( X + Z 1 b ) ≤ 1 2 log | 2 π e ( S + N 1 ) | , and h ( X + Z 2 ) ≤ 1 2 log | 2 π e ( S + N 2 ) | . Let µ = µ 1 + µ 2 + 1 and λ = µ 1 / ( µ 1 + µ 2 + 1). W e obtain from (25) (and Prop osition 2) h ( X + ˜ Z 1 a | U ) − µ 1 h ( X + Z 1 b | U ) − ( µ 2 + 1) h ( X + Z 2 | U ) ≤ 1 2 log 2 π e ( B ∗ + ˜ N 1 ) − µ 1 2 log | 2 π e ( B ∗ + N 1 ) | − µ 2 + 1 2 log | 2 π e ( B ∗ + N 2 ) | . (31) 11 Substituting (31) into (30), w e hav e R 1 + ( µ 1 + µ 2 ) R 0 ≤ 1 2 log | 2 π e N 2 | − 1 2 log 2 π e ˜ N 1 + 2 X k =1 h µ k 2 log | 2 π e ( S + N k ) | i + 1 2 log 2 π e ( B ∗ + ˜ N 1 ) − µ 1 2 log | 2 π e ( B ∗ + N 1 ) | − µ 2 + 1 2 log | 2 π e ( B ∗ + N 2 ) | = 1 2 log B ∗ + ˜ N 1 ˜ N 1 − 1 2 log B ∗ + N 2 N 2 + 2 X k =1 µ k 2 log S + N k B ∗ + N k = 1 2 log B ∗ + N 1 N 1 − 1 2 log B ∗ + N 2 N 2 + 2 X k =1 µ k 2 log S + N k B ∗ + N k (32) for an y achiev able secrecy rate pair ( R 0 , R 1 ) for the enhanced MIMO Gaussian broadcast c hannel (27). Here, the last equality follo ws from (24). Finally , combinin g Steps 1 and 2, w e conclude that an y ac hiev able secrecy rate pair for the original aligned MIMO Ga ussian broadcast channe l (1 0) is also ac hiev a ble for the enhanced MIMO G aussian broadcast c hannel (27). Th us, (32) ho lds for an y achiev able secrecy rate pair ( R 0 , R 1 ) for the origina l aligned MIMO Gaussian broadcast c hannel (10). Since δ > 0, this contradicts (20). Therefore, an y achiev a ble secrecy rate pair ( R 0 , R 1 ) for the aligned MIMO Ga ussian broadcast c hannel (10) m ust satisfy (11 ) for some 0 B S . This is the desired con v erse result, whic h completes t he pro of of the theorem. 4 General MIMO Gaussian Broadc ast Channel In this section, w e Theorem 1 b y extending the secrecy capacity result of Theorem 4 on the aligned MIMO G aussian broadcast c ha nnel to the g eneral MIMO broadcast c ha nnel. As men tioned in Section 1, the achie v ability of the rate region (7) can b e obtained from the Csisz´ ar-K¨ orner regio n (4) with prop er choice o f input and auxiliary v ariables ( U, V , X ). W e therefore concen trate on proving the conv erse par t of the t heorem. Also a s mentioned previously , the case when b oth c hannel matrices H 1 and H 2 are square and in ve rtible can b e easily transformed in to an aligned MIMO Gaussian broadcast channe l and thus has been pro v ed b y Theorem 4. Our goal next is to app r ox imate a general MIMO G aussian broadcast c hannel with an aligned MIMO Gaussian broadcast c hannel. Without lo ss of generality , w e assume that the c ha nnel matrices H 1 and H 2 are square (but not necessarily in v ertible). If that is not the case, w e can apply singular v alue decom- p osition (SVD) to sho w that there exists an equiv alen t c hannel that has t × t square c hannel matrices and the same secrecy capacit y region a s the origina l channel [9, Section V-B]. Using SVD, we can write the c ha nnel matrices as H k = U k Λ k V T k , k = 1 , 2 12 where U k and V k are t × t unita r y matrices, a nd Λ k is diagona l. W e now define a new MIMO Gaussian broadcast c ha nnel: Y k [ m ] = H k X [ m ] + Z k [ m ] k = 1 , 2 (33) where H k = U k ( Λ k + α I t ) V T k for some α > 0. Note that the MIMO Gaussian broadcast c ha nnel (33) do es ha v e inv ertible c hannel matrices. By Theorem 4, the secrecy capacit y , C s ( H 1 , H 2 , S ), under the mat r ix p o w er constrain t (6) is giv en by the set of all nonnegat ive rate pairs ( R 0 , R 1 ) satisfying R 0 ≤ min 1 2 log H 1 SH T 1 + I r 1 H 1 BH T 1 + I r 1 , 1 2 log H 2 SH T 2 + I r 2 H 2 BH T 2 + I r 2 R 1 ≤ 1 2 log H 1 BH T 1 + I r 1 − 1 2 log H 2 BH T 2 + I r 2 for some 0 B S . F urther note that we can write H k = D k H k where D k = U k Λ k ( Λ k + α I t ) − 1 U T k . Since D 2 k ≺ I t , w e hav e [12, Definition 1] X → Y k → Y k (34) forms a Marko v c hain for k = 1 , 2. Therefore, b oth r eceiv ers 1 and 2 receiv e a b etter signal in the new channel (33) t han in the o riginal c hannel (1). Note t hat receiv er 2 also plays the role of an ea ves dropp er for the confiden t ia l message W 1 . Therefore, unlik e the priv ate message problem considered in [9], enhancing b o th rece iv ers in the c hannel do es not necessarily lead to an increase in the secrecy capacit y region. In the following, ho wev er, w e sho w that C s ( H 1 , H 2 , S ) ⊆ C s ( H 1 , H 2 , S ) + O ( H 2 , H 2 , S ) (35) where O ( H 2 , H 2 , S ) := (0 , R 1 ) : 0 ≤ R 1 ≤ 1 2 log H 2 SH T 2 + I t − 1 2 log H 2 SH T 2 + I t Let ( R 0 , R 1 ) b e an achiev able secrecy rate pa ir for the MIMO Gaussian broadcast c hannel (1). By the result of Csisz´ ar a nd K¨ orner [2], there exists a collection of input and auxiliary v aria bles ( U, V , X ) satisfying t he Mark ov relation U → V → X suc h that R 0 ≤ min [ I ( U ; Y 1 ) , I ( U ; Y 2 )] R 1 ≤ I ( V ; Y 1 | U ) − I ( V ; Y 2 | U ) . Also b y the result of Csisz´ ar and K¨ orner [2], t he secrecy rate pair ( R 0 , R 1 ) giv en by R 0 = min I ( U ; Y 1 ) , I ( U ; Y 2 ) R 1 = I ( V ; Y 1 | U ) − I ( V ; Y 2 | U ) 13 is ac hiev able for the MIMO Gaussian broadcast c hannel (33) . By the Mark o v relation (3 4 ), w e hav e I ( U ; Y k ) ≤ I ( U ; Y k ) , I ( V ; Y k | U ) ≤ I ( V ; Y k | U ) , and I ( X ; Y k | U, V ) ≤ I ( X ; Y k | U, V ) for k = 1 , 2. Hence, w e hav e R 0 − R 0 ≤ min [ I ( U ; Y 1 ) , I ( U ; Y 2 )] − min I ( U ; Y 1 ) , I ( U ; Y 2 ) ≤ 0 (36) and R 1 − R 1 ≤ I ( V ; Y 1 | U ) − I ( V ; Y 2 | U ) − I ( V ; Y 1 | U ) − I ( V ; Y 2 | U ) = I ( V ; Y 2 | U ) − I ( V ; Y 2 | U ) − I ( V ; Y 1 | U ) − I ( V ; Y 1 | U ) ≤ I ( V ; Y 2 | U ) − I ( V ; Y 2 | U ) = I ( U, V ; Y 2 ) − I ( U, V ; Y 2 ) − I ( U ; Y 2 ) − I ( U ; Y 2 ) ≤ I ( U, V ; Y 2 ) − I ( U, V ; Y 2 ) = I ( X ; Y 2 ) − I ( X ; Y 2 ) − I ( X ; Y 2 | U, V ) − I ( X ; Y 2 | U, V ) ≤ I ( X ; Y 2 ) − I ( X ; Y 2 ) = I ( X ; Y 2 | Y 2 ) (37) ≤ max 0 B S 1 2 log H 2 BH T 2 + I t − 1 2 log H 2 BH T 2 + I t (38) = 1 2 log H 2 SH T 2 + I t − 1 2 log H 2 SH T 2 + I t (39) where (37) follow s from the Mark o v relatio n (34), (38) follows from a w ell- known inequal- it y due to Thomas [15, Lemma 1], and (39) follows from the fact that H T 2 H 2 ≺ H T 2 H 2 . Com bining (36) and (39) established the set relatio nship (35). Finally , let α ↓ 0 on b oth sides of (35). Note that H k → H k for k = 1 , 2, so C s ( H 1 , H 2 , S ) con verges to the rat e region (7) and O ( H 2 , H 2 , S ) → { (0 , 0) } . W e thus ha v e prov ed the desired con v erse result and completed the pro of of t he theorem. 5 Numerical Examples In this section, w e illustrate the results of Theorem 1 and Corollary 3 by n umerical exam- ples. Note that finding the b oundaries of t he secrecy capacit y regio ns C s ( H 1 , H 2 , S ) and C s ( H 1 , H 2 , P ) as expressed in (7) and (9) inv olves solving nonc onvex optimization programs and hence is nontrivial. F o llo wing the work in [10], w e can rewrite the expressions (7) and (9) suc h that the optimization progr a m for finding the b oundar ies of C s ( H 1 , H 2 , S ) and C s ( H 1 , H 2 , P ) b ecome tractable for the case where eac h of the receiv ers is equipp ed with 14 only o ne receiv e an tenna, i.e., r k = 1 for k = 1 , 2. As w e limit the discussion in this section to the single receiv e ante nna case, the ch annel matrices H k b ecome the 1 × t ch annel v ectors h k , k = 1 , 2. T o compute the secrecy capacity region C s ( h 1 , h 2 , S ), consider re-parameterizing ( R 0 , R 1 ) using ( α, γ 0 ) as R 0 = 1 2 log(1 + α γ 0 ) R 1 = 1 2 log(1 + α (1 − γ 0 )) . (40) Th us, to see whether a particular secrecy rate pair ( R 0 , R 1 ) is inside C s ( h 1 , h 2 , S ) as express ed in ( 7), one ma y che c k, instead, whether there exists a p ositiv e semidefinite matrix B whic h satisfies the set of constraints : h 1 ( S − B ) h T 1 ≥ αγ 0 ( h 1 Bh T 1 + 1) h 2 ( S − B ) h T 2 ≥ αγ 0 ( h 2 Bh T 2 + 1) h 1 Bh T 1 − h 2 Bh T 2 ≥ α (1 − γ 0 )( h 2 Bh T 2 + 1) B S . (41) Note t ha t all the constraints in (4 1) a re linear in B . Hence, whether there exists a feasible solution can b e examined using standard semidefinite programming tec hniques (i.e., CVX , a pac k age for sp ecifying and solving con v ex programs [16]). Note from (4 0) that b oth R 0 and R 1 increase as α increases. Therefore, for a fixed γ 0 , a b oundary p oint of C s ( h 1 , h 2 , S ) can b e found by searc hing ov er the maxim um α suc h that the set of constrain t s in (41) admits a feasible solution. Sw eeping o v er γ 0 ∈ [0 , 1] gives all the b oundary p oin ts of C s ( h 1 , h 2 , S ). Similarly , to compute the secrecy capacity region C s ( h 1 , h 2 , P ), w e consider the set of constrain ts for a pair of p ositiv e semidefinite matrices ( B 1 , B 2 ): h 1 B 2 h T 1 ≥ αγ 0 ( h 1 B 1 h T 1 + 1) h 2 B 2 h T 2 ≥ αγ 0 ( h 2 B 1 h T 2 + 1) h 1 B 1 h T 1 − h 2 B 1 h T 2 ≥ α ( 1 − γ 0 )( h 2 B 1 h T 2 + 1) T r( B 1 + B 2 ) ≤ P . (42) Again, a ll the constrain ts in (42) ar e linear in ( B 1 , B 2 ) so whether there exists a f easible solution can b e examined using standar d semidefinite prog ramming tec hniques [16]. There- fore, for a fixed γ 0 , a b oundary p oin t of C s ( h 1 , h 2 , P ) can b e found by searc hing o v er the maxim um α suc h that the set of constrain ts in (4 2) admits a feasible solution. Sw eeping o v er γ 0 ∈ [0 , 1] gives all the b o undar y p oin ts of C s ( h 1 , h 2 , P ). Figure 3 plots the se crecy capacit y regions C s ( h 1 , h 2 , S ) a nd C s ( h 1 , h 2 , P ) for the ch annel v ectors h 1 = [2 0 . 4] and h 2 = [0 . 4 1] and p ow er constraints S = 3 . 3333 1 . 2346 1 . 2346 1 . 6667 and P = T r ( S ) = 5. F or comparison, in Figure 3, w e hav e also plotted the capacit y regions of the same MIMO G aussian broadcast c ha nnel with a common message W 0 in tended for b oth receiv er 1 and 2 and a priv ate message W 1 in tended only for receiv er 1 (but without an y 15 0 0.2 0.4 0.6 0.8 1 1.2 1.4 0 0.5 1 1.5 2 2.5 C s ( h 1 , h 2 , S ) C ( h 1 , h 2 , S ) R 0 (bits) R 1 (bits) (a) The matrix p o wer constraint 0 0.2 0.4 0.6 0.8 1 1.2 1.4 0 0.5 1 1.5 2 2.5 C s ( h 1 , h 2 , P ) C ( h 1 , h 2 , P ) R 0 (bits) R 1 (bits) (b) Th e a v erage total p o w er constraint Figure 3: An illustration of the secrecy capacit y regio ns o f the MIMO G aussian broadcast c hannel with common and confiden tial messages. secrecy constraints). This problem is know n as the MIMO Gaussian broadcast c hannel with degraded message sets [10 , 17]. As shown in [10], the capacity region, C ( h 1 , h 2 , S ), under the matrix p ow er constraint (6) is give n by 2 C ( h 1 , h 2 , S ) = R 1 ( h 1 , S ) ∩ R 2 ( h 1 , h 2 , S ) where R 1 ( h 1 , S ) is giv en by the nonnegativ e rate pairs ( R 0 , R 1 ) satisfying R 0 + R 1 ≤ 1 2 log( h 1 Sh T 1 + 1) , and R 2 ( h 1 , h 2 , S ) is giv en by the nonnegativ e rate pa irs ( R 0 , R 1 ) satisfying R 0 ≤ 1 2 log h 2 Sh T 2 +1 h 2 Bh T 2 +1 R 1 ≤ 1 2 log( h 1 Bh T 1 + 1) for some 0 B S . Similarly , t he capacity region, C ( h 1 , h 2 , P ), under the av erag e t o tal p o w er constrain t (2) is giv en by C ( h 1 , h 2 , P ) = R 1 ( h 1 , P ) ∩ R 2 ( h 1 , h 2 , P ) where R 1 ( h 1 , P ) is giv en by the nonnegativ e rate pairs ( R 0 , R 1 ) satisfying R 0 + R 1 ≤ 1 2 log( P k h 1 k 2 + 1) , 2 As sho wn in [1 0], this result holds for the gener al MIMO Gaussian bro adcast channel, not just for the single r eceive antenna case. 16 and R 2 ( h 1 , h 2 , P ) is give n by the nonnegativ e rat e pairs ( R 0 , R 1 ) satisfying R 0 ≤ 1 2 log h 2 ( B 1 + B 2 ) h T 2 +1 h 2 B 1 h T 2 +1 R 1 ≤ 1 2 log( h 1 B 1 h T 1 + 1) for some B 1 0, B 2 0 and T r( B 1 + B 2 ) ≤ P . The b oundaries of the rate regions R 2 ( h 1 , h 2 , S ) and R 2 ( h 1 , h 2 , P ) can b e computed similarly to t ho se of C s ( h 1 , h 2 , S ) and C s ( h 1 , h 2 , P ), r esp ectiv ely . As exp ected, for an y giv en common rate R 0 , the maxim um secrecy rate is less than (or equal to) the maximum priv ate rate due to the additional secrecy constrain t at receiv er 2. A Pro of of the Con v erse P art of Prop osition 1 In this pro of, we use X j i to denote t he v ector ( X [ i ] , X [ i + 1] , . . . , X [ j ]), and when i = 1, we further simplify the notation b y using X j to denote the ve ctor ( X [1] , X [2] , . . . , X [ j ]). W e also use X i to denote X [ i ]. W e consider a 2 nR 0 , 2 nR 1 , n co de with the av erage blo c k error proba bilit y P ( n ) e . Then w e hav e the follo wing join t probability distribution p ( w 0 , w 1 , x n , ˜ y n 1 a , y n 1 b , y n 2 ) = p ( w 0 ) p ( w 1 ) p ( x n | w 0 w 1 ) n Y i =1 [ p ( ˜ y 1 ai | x i ) p ( y 1 bi y 2 i | ˜ y 1 ai )] . (43) By F ano’s inequalit y , w e hav e H ( W 0 | Y n 1 b ) ≤ nR 0 P ( n ) e + 1 := nδ 1 n (44) H ( W 0 | Y n 2 ) ≤ nR 0 P ( n ) e + 1 := nδ 1 n (45) H ( W 1 | ˜ Y n 1 a ) ≤ nR 1 P ( n ) e + 1 := nδ 2 n (46) where δ 1 n , δ 2 n → 0 if P ( n ) e → 0. W e define the following auxiliary random v ar iable: U i := ( W 0 , ˜ Y i − 1 1 a ) (47) whic h satisfies the Mark ov c hain relationship U i → X i → ( ˜ Y 1 ai , Y 1 bi , Y 2 i ) . 17 W e first b ound R 0 as follows . nR 0 = H ( W 0 ) ≤ I ( W 0 ; Y n 1 b ) + nδ 1 n (48) = n X i =1 I ( W 0 ; Y 1 bi | Y i − 1 1 b ) + nδ 1 n ≤ n X i =1 I ( W 0 , ˜ Y i − 1 1 a ; Y 1 bi | Y i − 1 1 b ) + nδ 1 n ≤ n X i =1 I ( W 0 , ˜ Y i − 1 1 a , Y i − 1 1 b ; Y 1 bi ) + nδ 1 n ≤ n X i =1 I ( W 0 , ˜ Y i − 1 1 a ; Y 1 bi ) + nδ 1 n (49) ≤ n X i =1 I ( U i ; Y 1 bi ) + nδ 1 n (50) where (48) follows from F ano’s inequalit y (44), and (49) follows from the degradedness condition, i.e., ( W 0 , Y 1 bi ) → ˜ Y i − 1 1 a → Y i − 1 1 b . W e can follow the steps similar to those in (48)-(50) with Y 1 b b eing replaced by Y 2 , and obtain the following b ound nR 0 ≤ n X i =1 I ( U i ; Y 2 i ) + nδ 1 n . (51) 18 W e now b ound nR 1 and obtain nR 1 = H ( W 1 | Y n 2 ) (52) = H ( W 1 | W 0 , Y n 2 ) + I ( W 1 ; W 0 | Y n 2 ) ≤ H ( W 1 | W 0 , Y n 2 ) + nδ 1 n = I ( W 1 ; ˜ Y n 1 a | W 0 , Y n 2 ) + H ( W 1 | W 0 , Y n 2 , ˜ Y n 1 a ) + nδ 1 n ≤ I ( W 1 ; ˜ Y n 1 a | W 0 , Y n 2 ) + nδ 2 n + nδ 1 n (53) ≤ I ( W 1 , X n ; ˜ Y n 1 a | W 0 , Y n 2 ) + nδ 2 n + nδ 1 n = I ( X n ; ˜ Y n 1 a | W 0 , Y n 2 ) + nδ 2 n + nδ 1 n (54) = H ( X n | W 0 , Y n 2 ) − H ( X n | W 0 , Y n 2 , ˜ Y n 1 a ) + nδ 2 n + nδ 1 n = H ( X n | W 0 , Y n 2 ) − H ( X n | W 0 , ˜ Y n 1 a ) + nδ 2 n + nδ 1 n (55) = I ( X n ; ˜ Y n 1 a | W 0 ) − H ( X n ; Y n 2 | W 0 ) + nδ 2 n + nδ 1 n = n X i =1 h I ( X n ; ˜ Y 1 ai | ˜ Y i − 1 1 a , W 0 ) − I ( X n ; Y 2 i | Y i − 1 2 , W 0 ) i + nδ 2 n + nδ 1 n = n X i =1 h H ( ˜ Y 1 ai | ˜ Y i − 1 1 a , W 0 ) − H ( ˜ Y 1 ai | ˜ Y i − 1 1 a , W 0 , X n ) − H ( Y 2 i | Y i − 1 2 , W 0 ) + H ( Y 2 i | Y i − 1 2 , W 0 , X n ) i + nδ 2 n + nδ 1 n ≤ n X i =1 h H ( ˜ Y 1 ai | ˜ Y i − 1 1 a , W 0 ) − H ( ˜ Y 1 ai | ˜ Y i − 1 1 a , W 0 , X i ) − H ( Y 2 i | ˜ Y i − 1 1 a , Y i − 1 2 , W 0 ) + H ( Y 2 i | Y i − 1 2 , W 0 , X i ) i + nδ 2 n + nδ 1 n (56) ≤ n X i =1 h H ( ˜ Y 1 ai | ˜ Y i − 1 1 a , W 0 ) − H ( ˜ Y 1 ai | ˜ Y i − 1 1 a , W 0 , X i ) − H ( Y 2 i | ˜ Y i − 1 1 a , W 0 ) + H ( Y 2 i | ˜ Y i − 1 1 a , W 0 , X i ) i + nδ 2 n + nδ 1 n (57) = n X i =1 h I ( X i ; ˜ Y 1 ai | U i ) − I ( X i ; Y 2 i | U i ) i + nδ 2 n + nδ 1 n (58) where (5 2) follows from p erfect secrecy condition, (53 ) follows from F ano’s inequalit y , (54) follo ws f r o m the Mark ov c hain ( W 0 , W 1 ) → ( X n , Y n 2 ) → ˜ Y n 1 a , (55) follows from t he degraded- ness condition, i.e., ( X n , W 0 ) → ˜ Y n 1 a → Y n 2 , (56) f o llo ws from the Mark ov c ha in relationship ( ˜ Y i − 1 1 a , W 0 , X n ) → X i → ˜ Y 1 ai and conditioning do es not increase en tropy , and (5 7) fo llo ws from the Marko v c hain relationships ( Y 2 i , W 0 ) → ˜ Y i − 1 1 a → Y i − 1 2 and ( Y i − 1 2 , ˜ Y i − 1 1 a , W 0 ) → X i → Y 2 i . The single-letter outer b ound can b e obtained by letting J b e a time-sharing v ariable uniformly distributed ov er { 1 , . . . , n } , and define U = ( U J , J ), X = X J , ˜ Y 1 a = ˜ Y 1 aJ , Y 1 b = Y 1 bJ , and Y 2 = Y 2 J . 19 References [1] A. D. Wyner, “The wire-tap c hannel,” Bel l Sys. T e ch. Journal , vol. 54, no. 8, pp. 135 5 – 1387, Oct. 1975 . [2] I. Csisz´ ar and J. K¨ orner, “ Br o adcast channels with confiden tial messages,” I EEE T r an s . Info. The ory , vol. IT-24, no. 3, pp. 339–348 , May 1978. [3] S. Shafiee, N. Liu, and S. Ulukus, “T ow ards t he secrecy capacity o f the Gaussian MIMO wire-tap c hannel,” I EEE T r ans. Inform. The ory , to app ear. [4] A. Khisti, G. W. W ornell, A. Wiesel, and Y. Eldar, “On the Gaussian MIMO wiretap c hannel,” in Pr o c. IEEE Int. S ymp. In form. The ory , Nice, F rance, June 2007, pp. 2 471– 2475. [5] A. Khisti and G. W. W ornell, “Secure transmission with m ultiple antennas: The MI- MOME c hannel,” I EEE T r ans. Info. The ory , to app ear. [6] F. Oggier and B. Hassibi, “The secrecy capacity of the MIMO wiretap ch annel,” in Pr o c . I EEE Int. Symp. I nfo. The ory , T o r o n to, Canada , July 2 008, pp. 524–528 . [7] T. Liu and S. Shamai (Shitz), “A not e on the secrecy capacit y of the multiple -an tenna wiretap c hannel,” IEEE T r an s. I nfo. The ory , v ol. 55, no. 6, pp. 25 4 7–2553, June 2009. [8] H. Sato, “An outer b ound to the capacit y region of broadcast c hannels,” IEEE T r ans. Info. The ory , vol. IT-24, no. 3, pp. 374–377 , May 1978. [9] H. W eingarten, Y. Stein b erg, a nd S. Shamai (Shitz), “The capacity regio n of the Gaussian m ultiple-input- m ultiple-output broadcast channe l,” IEEE T r a ns. Info . The- ory , v ol. 52 , no . 9, pp. 39 36-3964, Sept. 2006. [10] H. W einga r t en, Y. Stein b erg, and S. Shamai (Shitz), “On the capa city region of the m ulti- an tenna broadcast c hannel with common messages,” in Pr o c . IEEE Int. Symp. Info. The ory , Seattle, W A, July 2006, pp. 21 95–2199. [11] P . P . Bergman, “ R andom co ding theorem for broadcast channels with degraded com- p onen ts,” IEEE T r ans. I nfo. The ory , v ol. IT-19 , no . 3, pp. 19 7–207, Marc h 1973. [12] H. W einga r t en, T. Liu, S. Shamai (Shitz), Y. Stein b erg, and P . Visw anath, “The capac- it y region of the degraded m ultiple-input m ultiple-output compo und broadcast c hannel,” IEEE T r ans. Info. T he o ry , to app ear. [13] S. N. D igga vi and T. M. Co ve r, “The worst additiv e noise under a co v ariance constrain t,” IEEE T r ans. Info. T he o ry , v ol. 4 7, no. 7, pp. 3072–30 81, No v. 2 001. [14] S. Bo yd and L. V andenberghe, Conv ex Optimization , Cambridge Univ ersity Press, 200 4. 20 [15] J. A. Thomas, “F eedbac k can a t most double Gaussian multiple access channe l capac- it y ,” I EEE T r a n s. I nfo. The ory , v ol. IT-33, no. 5, pp. 711–716 , Sept. 1987. [16] M. Gran t and S. Bo yd, CVX: Matlab softwar e for disciplin e d c onvex pr o gr ammi n g (web p age and softwar e) . Av ailable at http://stanfor d.edu/ ~ boyd/cvx , F eb. 2009. [17] J. K¨ orner and K. Marton, “G eneral broadcast channels with degraded message sets,” IEEE T r ans. Info. T he o ry , v ol. IT-2 3, no. 1, pp. 60–64, Jan. 1977. 21
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment