Capacity of a Class of Linear Binary Field Multi-source Relay Networks
Characterizing the capacity region of multi-source wireless relay networks is one of the fundamental issues in network information theory. The problem is, however, quite challenging due to inter-user interference when there exist multiple source--des…
Authors: Sang-Woon Jeon, Sae-Young Chung
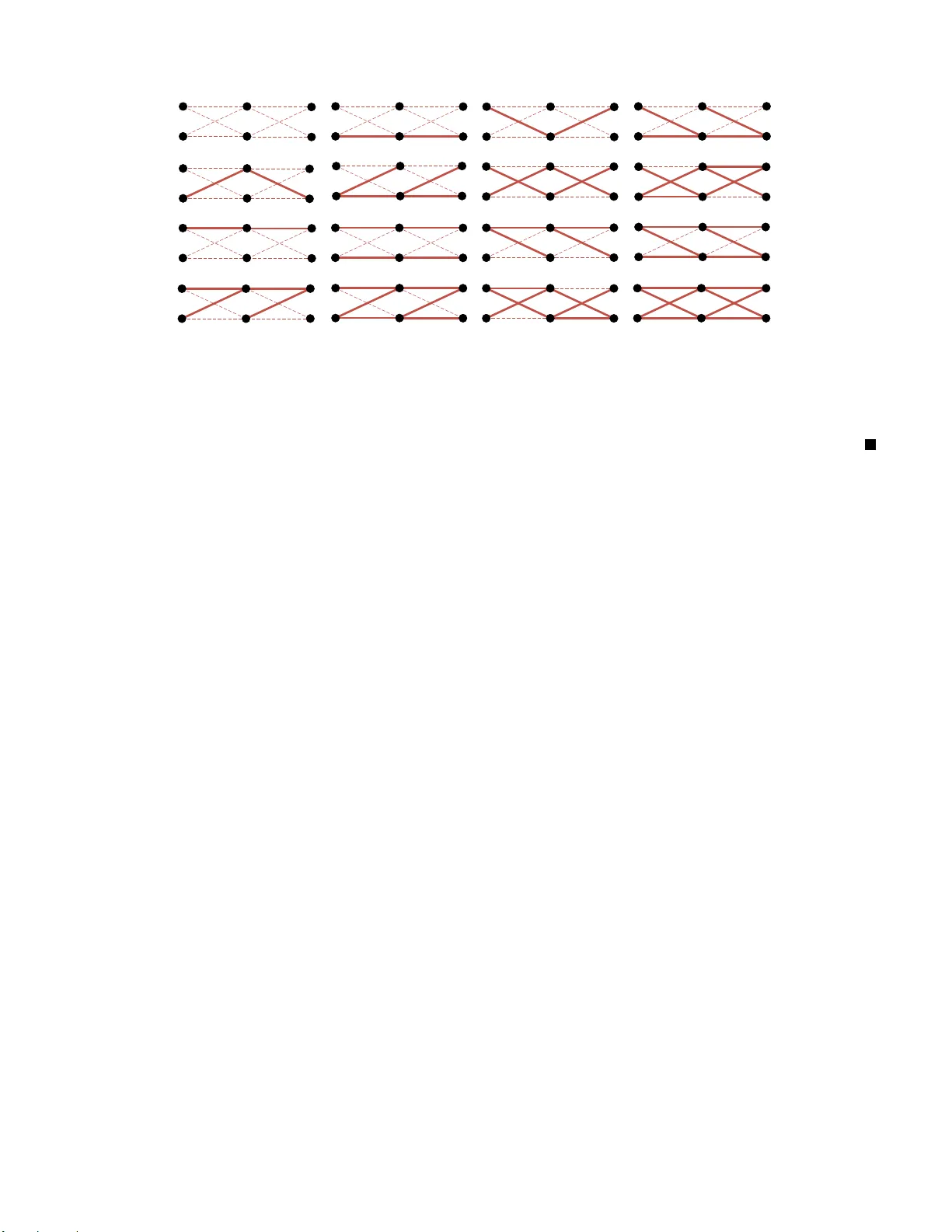
1 Capacity of a Class of Linear Binary Field Multi-source Relay Netw orks Sang-W oon Jeon, Student Member , IEEE and Sae-Y oung Chung, S enior Member , IEEE Abstract Characterizing the capa city region of multi-source wireless relay n etworks is one of th e fundam ental issues in network in formation theory . The pr oblem is, however , quite cha llenging due to in ter-user inter ference whe n there exist multiple source–d estination (S–D) p airs in the network. By fo cusing on a special class o f network s, we show that the cap acity can be fou nd. Namely , we study a layered linear binary field ne twork with time- varying channels, which is a simplified mo del reflecting b roadcast, interfere nce, an d fading natu res of wireless commun ications. W e observe that fading can play an impo rtant role in mitigatin g inter-user in terferenc e effecti vely for both single-ho p and m ulti-hop networks. W e prop ose new e ncoding and relaying sch emes with ran domized channel p airing, which exploit such channel variations, and derive their achievable r ates. By compar ing them with the c ut-set upper boun d, the capacity region of single-h op networks an d the sum capacity o f multi-hop networks can be characterized fo r some classes of c hannel distributions a nd n etwork topolog ies. F or these classes, we show that the capacity region or sum c apacity can be interpreted as the m ax-flow min-cu t th eorem. I . I N T RO D U C T I O N Capacity charac terization of gen eral wireless relay ne tworks is a fundamen tal problem in ne twork information theory . Howe ver , the ca pacity is not fully c haracterized even for the s implest n etwork consisting of sing le source , single relay , and sing le des tination [1]. In wireless en vironme nts, a transmit signa l will be hea rd by multiple node s, which we call the broadcast nature of wireless co mmunications, and a receiver will receiv e the superpo sition of simultane ously transmitted signals from multiple nodes , which we call the interference nature of wireless communications . Furthermore wireless chann els may be time-varying due to fading , an d there is n oise at each receiv er . Considering all thes e makes the proble m vary hard. Hence, o ne of the promising a pproach es is to study simplified rela y networks, who se results can provide insights tow ards exact or app roximate ca pacity c haracterization for more general wireless relay networks. L et us first look at some cas es for which the ca pacity is kn own. For wireline relay networks, routing is enou gh to achieve the unicast capac ity [2]. On the other hand, routing alone cannot achieve the mu lticast ca pacity a nd ne twork coding has be en shown to be optimal in this ca se [3]–[6]. For de terministic relay ne tworks with no interference, the un icast capa city has bee n charac terized in [7] and the extension to the multicast cas e has been studied in [8]. The multicast capacity of e rasure networks with no interference has been also charac terized in [9]. When there is no broadcast, the un icast capac ity of erasu re n etworks has been characterized in [10], which is the dua l ne twork s tudied in [9]. For all these mentioned networks, the unicas t or multicast c apacity can be interpreted a s the max-flo w min-cut theo r em . Notice that although su ch orthog onal transmiss ion or reception is pos sible in prac tice by using time, frequency , or c ode-division techniques , it is s uboptimal in g eneral. Th erefore, simplifica tion of wireless relay ne tworks while preserving both broadc ast and interference natures is cruc ially important to capture the es sence of wireless com- munications. One of the simplest mod els that success fully refle ct both broa dcast an d interference n atures is a linear finite fie ld relay network [11]–[13], whe re a node trans mits an element in the finite field and receiv es the sum of transmit signa ls in the sa me finite fie ld. Rece ntly , the work in [13] has s hown that the max-flow min-cut theorem also ho lds for de terministic linear finite fie ld relay networks. After the cap acity characte rization of linear finite field relay networks, the app roximate ca pacity of Gauss ian relay ne tworks ha s be en charac terized within a constant number of bits/s/Hz u sing the quantize-rand om-map-and-forward by the same au thors [14]. S.-W . Jeon and S. -Y . Chung are with the Department of EE, KAIST , Daejeon, South Korea (e-mail: swjeon@kaist.ac.kr; sy- chung@ee.kaist.ac.kr). The material i n this paper was presented in part at the Information Theory and Applications W orkshop, Univ ersity of California S an Diego, La Jo lla, CA, February 2009, and at the IEEE International Symposium on Information Theo ry (ISI T), Seoul, K orea, June/July 2009. 2 ( ) b 1 s 3 s 2 s 1 s 3 s 2 s Repeat transmission (1 ) 1 H ( 2 ) 1 H ( ) a 1 s 3 s 2 s 1 2 3 s s s 3 s 2 3 s s 1 H 2 H ( ) R e p e a t R e p e a t R e p e a t ( ) s s s 1 3 s 2 3 Fig. 1. Interference mitigation for t he single-hop network (a) and for the two-hop network (b), where the solid lines and t he dashed lines denote the corresponding channels are ones and zeros, respecti vely . In sp ite of the su r ging importance of multi-source relay networks, capacity cha racterization is muc h more challenging if there exist multiple source–de stination (S–D) pairs in a n etwork. Even for linear finite field relay networks, the extension of the results in [13] to the multi-source does not seem to be straightforward. Notice that the main d if ficulty arise s from the fact that the tr ans mission of other se ssions acts as inter-user interference and, as a result, the cu t-set upper b ound is not tight in ge neral. Due to the se dif ficulties, the existing capa city o r approximate ca pacity results a re limited in spe cific network topolog ies such a s two-user interference c hanne l [15], [16], many-to-one and on e-to-many interference chann el [17], two-way channe l [18], [19], two-user two-hop relay network [20], [21], and double Z-channel [22 ]. Therefore, one of the bas ic que stions is whether we can characterize the cap acity or a pproximate c apacity for more ge neral ne twork topo logies o r other class es of relay networks. In this pape r , we study a lay ered multi-sour ce linear binary field relay ne twork with time-va rying chan nels , which captures three key characte ristics of wireless e n v ironment, i.e., broadc ast, interference , and fading. No te tha t a random coding strategy , w hich is still optimal in fading single-source networks [23], [24], does not work anymore for our ne twork model due to the inter -us er interference. A s mentione d be fore, a fundamental issue in multi-source networks is how to mana ge inter- use r interference properly . W e observe tha t fading ca n play an important role in mitigating su ch interferenc e ef ficiently , which leads to the cap acity cha racterization for certain classe s of networks. More specifica lly , for single-hop networks, inter -user interferenc e c an be removed completely at eac h d estination by using two particular channel instances jointly . For mu lti-hop networks, by using a series o f particular c hannel instances over multiple hop s, ea ch de stination can also de code its message withou t interference. As an example, cons ider the three-user linear binary fie ld relay ne twork in Fig. 1, whe re s k ∈ F 2 denotes the information bit of the k -th source and the symb ol in eac h n ode d enotes the transmit signal o f that no de. For single-hop n etworks, as shown in Fig. 1. (a), b y transmitting the s ame bit twice at each s ource through H (1) 1 and H (2) 1 such that H (1) 1 + H (2) 1 = I , eac h destination can canc el interference b y add ing the two rec eiv ed sign als, where H (1) 1 and H (2) 1 denote the two diff erent cha nnel instances of the first hop a nd I den otes the ide ntity matrix. Related works dealing with the inse parability of parallel interference cha nnels can be found in [25]–[28] and the references therein. The idea of opportunistically pairing two cha nnel instan ces, i.e., H (1) 1 + H (2) 1 = I , also appeared in [27], [28]. This can be con sidered a s a d if ferent and simpler way of doing interference alignment [29], [30]. For two-hop networks, as s hown Fig. 1. (b), we notice that each destination can receiv e the information bit without interference if H 2 H 1 = I , where H 1 and H 2 denote the ch annel instances of the first and se cond hop, respectiv ely . In g eneral, the interferenc e-free c ommunication is po ssible for M -hop networks, M ≥ 2 , by opportunistically pairing the series of chan nel instances from H 1 to H M such that H M H M − 1 · · · H 1 = I , where H m denotes the c hannel instance of the m -th hop . Based on these key observations, we propose enco ding and relaying schemes which make such opportunistic pairing of chan nel ins tances possible. By comparing their achievable rate regions with the cut-set upper bound, we cha racterize the ca pacity region of s ingle-hop networks an d the s um cap acity of multi-hop n etworks for so me classes of ne twork topologies and ch annel d istrib utions. 3 1, 1 x 2,1 x 1 , 1 K x 1, 1 1,2 , y x 2,1 2 , 2 , y x 2 2 , 1 , 2 , K K y x 1,2 1,3 , y x 2 , 2 2 ,3 , y x 3 3 , 2 , 3 , K K y x 1, 1 1 , , M M y x 2 , 1 2 , , M M y x , 1 , , M M K M K M y x 1, M y 2 , M y 1 , M K M y first hop second hop - th hop M ( 1 , 1 ) -th node (2,1 ) -th node 1 (K ,1 )-th node ( 1 , 2)-th node (2, 2)-th node 2 (K , 2) -th node ( 1 , 3 )-th node (2, 3)-th node 3 (K , 3)-th node ( 1 , )-th node M (2, )-th node M M (K , )-th node M ( 1 , 1 ) -th node M (2, 1 ) -th node M M+1 (K , 1 )-th node M Fig. 2. Layered multi-source relay network . This pap er is or ganized a s follo ws. In Section II, we d efine the network mode l and state the multi-source relay problem an d the notations u sed in the paper . In Section III, we deriv e the gen eral cut-set upper bo und, which will be used to pro ve the con verses in S ection IV. In Section IV, n ew enc oding an d relaying schemes are prop osed to mitigate inter -us er interference , wh ich chara cterizes the ca pacity region or sum capac ity for certain classes of networks. W e con clude this paper in S ection V and refer the proofs o f the lemmas to Appendices I a nd II. I I . S Y S T E M M O D E L In this section, we first explain the underlying network model and then defin e the achiev able rate region and the notations used in the pap er . Th roughout the pap er , A and a denote a matrix and a vector , respectiv ely . The symbol A den otes a se t a nd |A| deno tes the cardinality of A . A. Linear Binary F ield Relay Networ ks W e study a layered network in Fig. 2 that c onsists of M + 1 layers having K m nodes at the m -th layer , wh ere m ∈ { 1 , · · · , M + 1 } . L et u s denote K max = m ax m { K m } and K min = m in m { K m } . The ( k , m ) -th node refers to the k -th nod e at the m -th la yer . Then K = K 1 = K M +1 is the number of S–D pairs and the ( k , 1) -th n ode and the ( k , M + 1) -th nod e are the source a nd the destination of the k -th S –D pair , respectively . Notice that if M = 1 , the network become s a K -user interference cha nnel. Consider the m -th hop transmiss ion. The ( i, m ) -th node an d the ( j, m + 1) -th node bec ome the i -th transmitter (Tx) an d the j -th receiv er (Rx) of the m -th hop, respe cti vely , whe re i ∈ { 1 , · · · , K m } an d j ∈ { 1 , · · · , K m +1 } . Le t x i,m [ t ] ∈ F 2 denote the trans mit signal of the ( i, m ) -th node at time t and y j,m [ t ] ∈ F 2 denote the rec eiv ed signal of the ( j, m + 1) -t h node a t time t . Let h j,i,m [ t ] ∈ F 2 be the cha nnel from the ( i, m ) -th node to the ( j, m + 1) -th node at time t . Th e relation between the trans mit a nd received signals is giv en by y j,m [ t ] = K m X i =1 h j,i,m [ t ] x i,m [ t ] , (1) where all operations a re p erformed over F 2 1 . W e assume time-varying chan nels such that Pr( h j,i,m [ t ] = 1) = p j,i,m (2) and h j,i,m [ t ] a re ind epende nt of each other for different i , j , m , a nd t . This as sumption can be ge neralized to block fading with coheren ce time of T symbo ls, wh ere T ≫ 1 such tha t there is enough time for CSI to b e spread to relev a nt nodes. W e as sume T = 1 for notational simplicity since our result does not explicitly depend on T as long as it is b ig eno ugh suc h that CS I is av ailable at a ll relevant nodes. Let x m [ t ] an d y m [ t ] be the K m × 1 transmit s ignal vector and K m +1 × 1 rece i ved signal vector of the m -th h op, res pectiv ely , where x m [ t ] = [ x 1 ,m [ t ] , · · · , x K m ,m [ t ]] T , y m [ t ] = y 1 ,m [ t ] , · · · , y K m +1 ,m [ t ] T . T hen the transmiss ion of the m -th hop can be repres ented as 1 W e focus on the binary fi eld F 2 in this paper , but some results can be directly extended to F q (see Remarks 1 and 2). 4 y m [ t ] = H m [ t ] x m [ t ] , (3) where H m [ t ] is the K m +1 × K m channe l matrix of the m -th hop h aving h j,i,m [ t ] as the ( j, i ) -th element. W e assume that bo th Tx s an d Rx s of the m -th ho p ca usally kn ow the globa l cha nnel s tate information (CSI) up to the m -th h op. That is, a t time t 0 , the n odes in the m -th layer know { H 1 [ t ] , · · · , H m [ t ] } t 0 t =1 if m ≤ M an d { H 1 [ t ] , · · · , H M [ t ] } t 0 t =1 if m = M + 1 . For a broad class of networks, if the c hanne l dimension of a certain hop is sma ller than those of the other hops, then the average channel rank of the hop is likely to be less than thos e of the o ther hops . The following definition formally states this clas s of networks. Definition 1: Let m 0 = arg min m ∈{ 1 , ··· , M } E (rank( H m [1])) 2 . A linear binary relay network is said to have a minimum-dimensional b ottleneck-hop m 0 if K m ≥ K m 0 and K m +1 ≥ K m 0 +1 or K m ≥ K m 0 +1 and K m +1 ≥ K m 0 for all m ∈ { 1 , · · · , M } . In this pap er , we will s tudy the class of networks satisfying Definition 1 . No tice that any ne tworks with K m = K for all m ∈ { 1 , · · · , M + 1 } or any one-ho p or two-hop networks are included in this class of networks regardless of chann el distributions. B. Pr o blem Statement Based on the pre vious network mod el, we define a se t of length- n block codes. Let W k be the messag e of the k -th source uniformly distrib uted o ver { 1 , 2 , · · · , 2 nR k } , where R k is the rate of the k -th source. F or simplicit y , we assume nR k is an integer . Then a 2 nR 1 , · · · , 2 nR K ; n code con sists of the following encod ing, relaying, and decoding functions. • (Encoding) For k ∈ { 1 , · · · , K } , the se t of e ncoding functions o f the k -th source is g i ven by { f k , 1 ,t } n t =1 : { 1 , · · · , 2 nR k } → F n 2 such that x k , 1 [ t ] = f k , 1 ,t ( W k ) for t ∈ { 1 , · · · , n } . (4) • (Relaying) For m ∈ { 2 , · · · , M } and k ∈ { 1 , · · · , K m } , the set of relaying functions of the ( k, m ) -th node is given by { f k ,m,t } n t =1 : F n 2 → F n 2 such that x k ,m [ t ] = f k ,m,t ( y k ,m − 1 [1] , · · · , y k ,m − 1 [ t − 1]) for t ∈ { 1 , · · · , n } . (5) • (Decoding) For k ∈ { 1 , · · · , K } , the decod ing function of the k -th destination is g i ven by g k : F n 2 → { 1 , · · · , 2 nR k } such that ˆ W k = g k ( y k ,M [1] , · · · , y k ,M [ n ]) . (6) If M = 1 , the s ources transmit directly to the destinations without relay s. The proba bility of error at the k -th destination is g i ven by P ( n ) e,k = P r( ˆ W k 6 = W k ) . A set of rates ( R 1 , · · · , R K ) is said to be achievable if there exists a s equen ce of (2 nR 1 , · · · , 2 nR K ; n ) c odes with P ( n ) e,k → 0 a s n → ∞ for all k ∈ { 1 , · · · , K } . Then the achievable sum rate is simply g i ven by R sum = P K k =1 R k . T he capa city region is the c losure of all ac hiev able ( R 1 , · · · , R K ) and the sum c apacity is the supremum of a ll achiev able su m rates . C. Notations In this s ubsec tion, we introduce the notations for directed graphs and define s ets of ch annel ins tances and s ets of nodes . 2 Notice that E (rank( H m [ t ])) is the same for all t . 5 1) Notations for dir ec ted graphs: The co nsidered network can b e represe nted as a directed graph G = ( V , E ) consisting of a vertex s et V and a directed e dge s et E . Let v k ,m denote the ( k , m ) -th n ode a nd V m = { v k ,m } K m k =1 denote the s et of nodes in the m -th layer . Then V is given by ∪ m ∈{ 1 , ··· , M +1 } V m . The se ts of source s and des tinations are giv en by S = V 1 and D = V M +1 , respec ti vely . There exists a directed edge ( v i,m , v j,m +1 ) from v i,m to v j,m +1 if p j,i,m > 0 . For V ′ ⊆ V and V ′′ ⊆ V , define E ( V ′ , V ′′ ) as the set of e dges going from V ′ to V ′′ giv en by { ( v ′ , v ′′ ) | v ′ ∈ V ′ , v ′′ ∈ V ′′ , ( v ′ , v ′′ ) ∈ E } . W e s ay node v ′′ is r eachable from n ode v ′ if there exists a s eries of e dges from v ′ to v ′′ , where w e a ssume v ′ is alw ays reachable from v ′ itself. W e further define v ′′ is reachable under V ′ from v ′ if there exists a s eries of edges in E ( V ′ , V ′ ) from v ′ to v ′′ . W e define cut Ω ⊆ V a s a subset of node s such that at least one s ource is in Ω and at least one correspo nding d estination is in Ω c . W e defi ne the follo wing s ets related to Ω : K Ω = { k | v k , 1 ∈ Ω , v k ,M +1 ∈ Ω c , k ∈ { 1 , · · · , K }} , D Ω = { v k ,M +1 | k ∈ K Ω } , S Ω = { v k , 1 | k ∈ K Ω } , Ω D = { v |E (Ω , { v } ) 6 = φ, at least on e of the de stinations in D Ω is reacha ble und er Ω c from v , v ∈ Ω c } , Ω ′ = { v | v ∈ Ω is rea chable from at leas t one o f the sou rces in S Ω } , Ω S = { v |E ( { v } , Ω D ) 6 = φ, v ∈ Ω ′ } . (7) Let X V ′ [ t ] an d Y V ′ [ t ] de note the sets of transmit a nd re ceiv ed signals of the n odes in V ′ at time t , res pectiv ely . Let H V ′ , V ′′ [ t ] be the |V ′′ | × |V ′ | channel matrix at time t from the nod es in V ′ to the nodes in V ′′ . Hence H V m , V m +1 [ t ] = H m [ t ] . For notational simplicity , we use H Ω [ t ] to deno te H Ω S , Ω D [ t ] in this pa per . 2) Sets of c hann el ins tances and no des: For ¯ V ′ ⊆ V ′ , ¯ V ′′ ⊆ V ′′ , and G ∈ F | ¯ V ′′ |×| ¯ V ′ | 2 , we de fine the following sets of cha nnel instan ces. H V ′ , V ′′ G , ¯ V ′ , ¯ V ′′ = H V ′ , V ′′ [1] H ¯ V ′ , ¯ V ′′ [1] = G , H V ′ , V ′′ [1] ∈ F |V ′′ |×|V ′ | 2 , H F V ′ , V ′′ G , ¯ V ′ , ¯ V ′′ = H V ′ , V ′′ [1] rank( H V ′ , V ′′ [1]) = rank( G ) , H ¯ V ′ , ¯ V ′′ [1] = G , H V ′ , V ′′ [1] ∈ F |V ′′ |×|V ′ | 2 . (8) Note that H V ′ , V ′′ G , ¯ V ′ , ¯ V ′′ is the set of all H V ′ , V ′′ [1] ∈ F |V ′′ |×|V ′ | 2 that contain G in H ¯ V ′ , ¯ V ′′ [1] . Similarly , H F V ′ , V ′′ G , ¯ V ′ , ¯ V ′′ is the set of all H V ′ , V ′′ [1] ∈ F |V ′′ |×|V ′ | 2 that hav e the sa me rank a s G and contain G in H ¯ V ′ , ¯ V ′′ [1] . W e further de fine the follo wing sets of nodes. For positiv e integers a ≤ |V ′ | and b ≤ |V ′′ | , V ( a, b, V ′ , V ′′ ) = ( ¯ V ′ , ¯ V ′′ ) | ¯ V ′ | = a, | ¯ V ′′ | = b, ( ¯ V ′ , ¯ V ′′ ) ⊆ ( V ′ , V ′′ ) (9) and for H ∈ F |V ′′ |×|V ′ | 2 , V H , V ′ , V ′′ = ( ¯ V ′ , ¯ V ′′ ) rank( H ¯ V ′ , ¯ V ′′ [1]) = | ¯ V ′ | = | ¯ V ′′ | = r an k( H ) where H V ′ , V ′′ [1] = H , ( ¯ V ′ , ¯ V ′′ ) ⊆ ( V ′ , V ′′ ) , (10) where V ( H , V ′ , V ′′ ) = φ if r ank( H ) = 0 . The s et V ( a, b, V ′ , V ′′ ) con sists of all ( ¯ V ′ , ¯ V ′′ ) ⊆ ( V ′ , V ′′ ) su ch that the number of n odes in ¯ V ′ and the number of nodes in ¯ V ′′ are equa l to a and b , respec ti vely . The s et V ( H , V ′ , V ′′ ) consists of all ( ¯ V ′ , ¯ V ′′ ) ⊆ ( V ′ , V ′′ ) suc h that H ¯ V ′ , ¯ V ′′ [1] is a full-rank matrix and has the s ame rank as H , where H V ′ , V ′′ [1] = H . I I I . U P P E R B O U N D In this s ection, we deriv e a gene ral cut-set upper bound , wh ich will be us ed to show the con verses in Section IV. 6 1, 1 v 2 , 1 v 3, 1 v 1,2 v 2 , 2 v 3, 2 v 1,3 v 2, 3 v 3,3 v 1,4 v 2 , 4 v 3, 4 v : Fig. 3. Example of the cut-set upper bound, where the solid lines mean that the corresponding channe ls become ones with non-zero probabilities. A. Cut-set Upper Bound W e sho w that any seque nce of (2 nR 1 , · · · , 2 nR K ; n ) co des with P ( n ) e,k → 0 for all k ∈ { 1 , · · · , K } satisfies the rate cons traints in the following theorem. Theorem 1: Suppose a linear binary field relay network. For a cut Ω , the set of ach iev a ble rates ( R 1 , · · · , R K ) is uppe r bou nded by X k ∈K Ω R k ≤ E (rank( H Ω [1])) . (11) Pr o of: Let us define W K Ω = { W k k ∈ K Ω } . W e further define a length- n sequenc e a n to denote { a [1] , · · · , a [ n ] } . Then n X k ∈K Ω R k = H ( W K Ω ) = I ( W K Ω ; Y n D Ω , H n 1 , · · · , H n M ) + H ( W K Ω |Y n D Ω , H n 1 , · · · , H n M ) ( a ) ≤ I ( W K Ω ; Y n D Ω , H n 1 , · · · , H n M ) + nǫ n ( b ) = I ( W K Ω ; Y n D Ω | H n 1 , · · · , H n M ) + nǫ n ( c ) ≤ I ( W K Ω ; Y n Ω D | H n 1 , · · · , H n M ) + nǫ n ( d ) ≤ H ( W K Ω |X n Ω \ Ω ′ , H n 1 , · · · , H n M ) − H ( W K Ω |X n Ω \ Ω ′ , Y n Ω D , H n 1 , · · · , H n M ) + nǫ n = I ( W K Ω ; Y n Ω D |X n Ω \ Ω ′ , H n 1 , · · · , H n M ) + nǫ n ≤ H ( Y n Ω D |X n Ω \ Ω ′ , H n 1 , · · · , H n M ) + nǫ n ( e ) = n X t =1 H ( Y Ω D [ t ] |X Ω \ Ω ′ [ t ] , H 1 [ t ] , · · · , H M [ t ]) + nǫ n ( f ) ≤ n E (rank( H Ω [1])) + nǫ n , (12) where ǫ n > 0 s atisfies ǫ n → 0 as n → ∞ . Notice tha t ( a ) holds from Fano’ s inequality , ( b ) holds since the messag es are indepen dent of cha nnels, ( c ) ho lds since W K Ω − Y n Ω D , H n 1 , · · · , H n M − Y n D Ω forms a Markov chain, ( d ) holds since W K Ω is indepe ndent o f X n Ω \ Ω ′ , H n 1 , · · · , H n M and c onditioning reduce s entropy , ( e ) holds sinc e chann els are memoryless, and ( f ) holds with equality if X Ω S [ t ] is uniformly distri buted over F | Ω S | 2 . Therefore, we ha ve (11), which completes the proo f. Theorem 1 s hows that the ag gregate rate of the S–D pairs divided by a cut is uppe r bou nded b y the average rank of the c hannel matrix constructed by the c ut. Example 1 (Cut-set Upper Bou nd): Consider the cu t Ω = { v 1 , 1 , v 2 , 1 , v 3 , 1 , v 2 , 2 , v 3 , 2 , v 3 , 3 , v 3 , 4 } in Fig. 3. Th en we obtain D Ω = { v 1 , 4 , v 2 , 4 } , S Ω = { v 1 , 1 , v 2 , 1 } , Ω D = { v 2 , 3 , v 1 , 4 } , Ω S = { v 2 , 2 , v 3 , 3 } , and H Ω [1] is giv en by [[ h 2 , 2 , 2 [1] , 0] T , [0 , h 1 , 3 , 3 [1]] T ] T . Therefore, R 1 + R 2 is uppe r bou nded by E (rank( H Ω [1])) = p 2 , 2 , 2 + p 1 , 3 , 3 . 7 B. Rate Boun ds for Sing le-hop and Multi-hop Network s In this subsec tion, we obtain u seful rate up per bounds from The orem 1, wh ich will be use d to sh ow the co n verse s in Corollaries 1 and 2. Le t us first c onsider single-hop networks, that is M = 1 . If we s et Ω = { v k , 1 } , then P i ∈K Ω R i = R k and H Ω [ t ] = h k ,k , 1 [ t ] . Thus, we ob tain R k ≤ p k ,k , 1 (13) for all k ∈ { 1 , · · · , K } . Let us now cons ider multi-hop networks, that is M ≥ 2 . By s etting Ω = ∪ i ∈{ 1 , ··· ,m } V i , we have P k ∈K Ω R k = R sum and H Ω [ t ] = H m [ t ] , where m ∈ { 1 , · · · , M } . Hence, we obtain R sum ≤ min m ∈{ 1 , ··· ,M } E (rank( H m [1])) (14) or equiv alently R sum ≤ E (rank( H m 0 [1])) . I V . A C H I E V A B I L I T Y In this sec tion, w e propose transmission sch emes and d eri ve their achievable rate regions. A. Achievability for M = 1 Consider a s ingle-hop n etwork, that is M = 1 . As mentioned in Introduction, e ach source ca n transmit one bit without interference by using two particular instance s H (1) 1 and H (2) 1 jointly suc h tha t H (1) 1 + H (2) 1 = I . The proposed enco ding makes such pairing po ssible. 1) Pr opose d scheme: Let us d i vide a b lock into two su b-blocks having length n/ 2 for each su b-block. For H 1 ∈ F K × K 2 , define T b ( H 1 ) as the set o f time indice s of the b -th su b-block whose chan nel instan ces are equa l to H 1 , where b ∈ { 1 , 2 } . W e further defi ne n ( H 1 ) = c − 1 1 nR min { Pr( H 1 [1] = H 1 ) , Pr( H 1 [1] = H 1 + I ) } , (15) where c 1 = X H 1 ∈ F K × K 2 min { H 1 [1] = Pr( H 1 ) , Pr( H 1 [1] = H 1 + I ) } . (16) The detailed enc oding is as follows. • (Encoding o f the first sub-block ) For all H 1 ∈ F K × K 2 , de clare an error if |T 1 ( H 1 ) | < n ( H 1 ) , otherwise ea ch source transmits n ( H 1 ) information bits using the time indice s in T 1 ( H 1 ) . • (Encoding o f the second sub -block) For all H 1 ∈ F K × K 2 , declare an error if |T 2 ( H 1 ) | < n ( H 1 ) , othe rwise each s ource retransmits n ( H 1 ) information bits tha t were transmitted during T 1 ( H 1 + I ) using the time indices in T 2 ( H 1 ) . Notice that, since e ach source tr ans mits P H 1 ∈ F K × K 2 n ( H 1 ) information bits during n cha nnel uses, the trans- mission rates are g i ven by R 1 = · · · = R K = 1 n P H 1 ∈ F K × K 2 n ( H 1 ) = R . Let s k ( i ) denote the i -th information bit of the k -th s ource, wh ere i = { 1 , · · · , n R } . Let t 1 ( i ) and t 2 ( i ) denote the time indice s ov er which s k ( i ) was transmitted. Then the de tailed d ecoding is as follows. • (Decoding) For i ∈ { 1 , · · · , nR } , the k -th destination sets ˆ s k ( i ) = y k , 1 [ t 1 ( i )] + y k , 1 [ t 2 ( i )] . 2) Achievable rate r e g ion: W e deriv e the a chiev able rate region of the proposed s cheme. Let E b denote the ev ent such that |T b ( H 1 ) | < n ( H 1 ) for any H 1 ∈ F K × K , where b ∈ { 1 , 2 } . The follo wing lemma shows that there is no error if ( E 1 ∪ E 2 ) c occurs. Lemma 1: Supp ose a linear bina ry fie ld relay network with M = 1 . The proba bility of error is uppe r bounde d by P ( n ) e,k ≤ P r( E 1 ) + Pr( E 2 ) (17) for all k ∈ { 1 , · · · , K } . Pr o of: The p roof is in Ap pendix I. 8 Then the remaining thing is to derive R that guarantees P ( n ) e,k → 0 as n → ∞ . Th e follo wing theorem characterizes such R . Theorem 2: Suppose a linear binary field relay ne twork with M = 1 . Th en R k = 1 2 X H 1 ∈ F K × K 2 min { Pr( H 1 [1] = H 1 ) , Pr( H 1 [1] = H 1 + I ) } (18) is achievable for a ll k ∈ { 1 , · · · , K } . Pr o of: Let us co nsider |T b ( H 1 ) | . By the w eak law of large n umbers [31], there exists a se quence ǫ n → 0 as n → ∞ s uch tha t the proba bility |T b ( H 1 ) | ≥ n 2 (Pr( H 1 [1] = H 1 ) − δ n ) for all H 1 (19) is grea ter than or equa l to 1 − ǫ n , wh ere δ n → 0 as n → ∞ . This indicates that Pr( E b ) ≤ ǫ n if n ( H 1 ) ≤ n 2 (Pr( H 1 [1] = H 1 ) − δ n ) for all H 1 . Hence , from (15), if R ≤ c 1 (Pr( H 1 [1] = H 1 ) − δ n ) 2 min { Pr( H 1 [1] = H 1 ) , Pr( H 1 [1] = H 1 + I ) } (20) for all H 1 , then P ( n ) e,k ≤ 2 ǫ n , where we us e the result o f Lemma 1 . Thus we s et R = c 1 2 (1 − δ ∗ n ) , where δ ∗ n = δ n min H ′ 1 ∈ F K × K 2 { Pr( H 1 [1]= H ′ 1 ) } , which co n verges to z ero as n → ∞ . In c onclusion, (18) is a chiev able for all k ∈ { 1 , · · · , K } , which co mpletes the proof. Cor ollary 1: S uppose a linea r binary field relay network with M = 1 . If p k ,k , 1 = 1 / 2 for all k ∈ { 1 , · · · , K } , the cap acity region is given by all rate tuples ( R 1 , · · · , R K ) satisfying R k ≤ 1 2 (21) for all k ∈ { 1 , · · · , K } . Pr o of: Note that Pr( H 1 [1] = H 1 ) = Pr( H 1 [1] = H 1 + I ) for all H 1 if p k ,k , 1 = 1 / 2 . Hence , from (18), R k = 1 2 P H 1 ∈ F K × K 2 Pr( H 1 [1] = H 1 ) = 1 2 is a chiev able for all k ∈ { 1 , · · · , K } . Note that the ach iev a ble rate region coinc ides with the upper bound in (13), which provides the ca pacity region. Therefore, Corollary 1 ho lds. Remark 1: Corollary 1 can b e directly extended to a general linear finite field relay network in which inputs, outputs, a nd ch annels are in F q and c hannels a re i.i.d. un iformly distributed over F q . S pecifically , the capa city region is g i ven b y a ll rate tuples ( R 1 , · · · , R K ) satisfying R k ≤ 1 2 log q for a ll k ∈ { 1 , · · · , K } . Corollary 1 s hows tha t all S–D pairs ca n s imultaneously achieve the capacity o f the point-to-point channe l assuming no inter fer enc e if the d irect chann els are uniformly distributed. This result also shows that the max-flo w min-cut theo r em h olds for a certain clas s of c hannel distributions. Similar to the Gaus sian interferenc e cha nnel in which 1 / 2 degrees of freed om is achiev a ble for eac h S–D pair [29], e ach sou rce can transmit data to its des tination with a non -v anish ing rate even as K tends to infinity . Example 2 ( 2 – 2 ne twork): Consider the case where K = 2 and M = 1 with p j,i, 1 = 1 / 2 for all i and j . If we use each c hannel instance separately , then R sum ≤ 13 / 16 is ac hiev able. However , the p roposed sche me a chieves R sum ≤ 1 . More specifically , R 1 ≤ 1 / 2 and R 2 ≤ 1 / 2 are a chiev able, which is the capacity region o f this network. B. Achievability for M ≥ 2 Consider a multi-hop network, that is M ≥ 2 . As me ntioned in Introduction, each source can transmit one bit to its destination without interferenc e through particular instanc es from H 1 to H M such that H M H M − 1 · · · H 1 = I . (22) Due to network topologie s a nd cha nnel distrib utions, h owe ver , so me ins tances will be ran k-deficient and it is impossible to find a series of pairs satisfying (22) b y using ran k-deficient instanc es. Furthermore, a series o f pa irs satisfying (22) is not uniqu e and the number of pos sible pairing increas es exponentially as the n umber of nodes in a layer or the nu mber of layers increas es. Hence , we fi rst reduc e the size of e f fective cha nnels by transmitting and rec eiving us ing su bsets of nodes at eac h hop s uch tha t the average ranks are balance d between hops and their instances have full-rank. Then we rando mize a series of pairs based o n the se effecti ve chann els. 9 1) Construc tion of ef fective chan nels: Recall that the m 0 -th hop be comes a bo ttleneck for the en tire multi-hop transmission, which ca n b e verified from (14). Hence, we select V m, tx [ t ] ⊆ V m and V m, rx [ t ] ⊆ V m +1 randomly such that ( V m, tx [ t ] , V m, rx [ t ]) ∈ V ( K m 0 , K m 0 +1 , V m , V m +1 ) (23) with e qual probabilities (or in V ( K m 0 +1 , K m 0 , V m , V m +1 ) ). Notice tha t this is poss ible since the c onsidered ne twork has a minimum-dimensional bottlenec k-hop. B ecaus e the maximum number of bits trans mitted at the m -th hop is limited by rank( H V m, tx [ t ] , V m, rx [ t ] [ t ]) , we furt her select ¯ V m, tx [ t ] ⊆ V m, tx [ t ] and ¯ V m, rx [ t ] ⊆ V m, rx [ t ] randomly such that ( ¯ V m, tx [ t ] , ¯ V m, rx [ t ]) ∈ V ( H V m, tx [ t ] , V m, rx [ t ] [ t ] , V m, tx [ t ] , V m, rx [ t ]) (24) with equ al p robabilities. For ea ch time t , the nodes in ¯ V m, tx [ t ] transmit and the node s in ¯ V m, rx [ t ] rece i ve through their effecti ve cha nnel H ¯ V m, tx [ t ] , ¯ V m, rx [ t ] [ t ] a t the m -th hop. Then information bits can be transmitted using particular time indices t 1 , · · · , t M such that ¯ V 1 , tx [ t 1 ] = ¯ V M , rx [ t M ] , ¯ V m, tx [ t m ] = ¯ V m − 1 , rx [ t m − 1 ] for all m ∈ { 2 , · · · , M } , and H ¯ V M, tx [ t M ] , ¯ V M, rx [ t M ] [ t M ] · · · H ¯ V 1 , tx [ t 1 ] , ¯ V 1 , rx [ t 1 ] [ t 1 ] = I , (25) which guarantees interference-free rece ption at the de stinations. It is pos sible to con struct thos e pairs beca use eff ective channels are always in vertible 3 . Let F i be the set of all full -rank matrices in F i × i 2 , where i ∈ { 1 , · · · , K min } . The following lemma shows us eful proba bility d istrib utions, wh ich will be used to derive the achiev able rate region of the propo sed sc heme. Lemma 2: Supp ose a linear binary fie ld relay network with M ≥ 2 . If the ne twork h as a minimum-dimens ional bottleneck-hop and p j,i,m = p for a ll i , j , and m , then the following probabilities hold: 1) For H ∈ F K m 0 × K m 0 +1 2 (or F K m 0 +1 × K m 0 2 ), Pr( H V m, tx [ t ] , V m, rx [ t ] [ t ] = H ) = p u (1 − p ) K m 0 +1 K m 0 − u , (26) where u is the number of ones in H . 2) For G ∈ F i , Pr( H ¯ V m, tx [ t ] , ¯ V m, rx [ t ] [ t ] = G ) = X ( V ′ , V ′′ ) ∈ V ( i,i, V m 0 , V m 0 +1 ) X H ∈H F V m 0 , V m 0 +1 ( G , V ′ , V ′′ ) Pr( H V m, tx [ t ] , V m, rx [ t ] [ t ] = H ) |V ( H , V m 0 , V m 0 +1 ) | , (27) where Pr( H V m, tx [ t ] , V m, rx [ t ] [ t ] = H ) is given by (26). If p = 1 / 2 , we have Pr( H ¯ V m, tx [ t ] , ¯ V m, rx [ t ] [ t ] = G ) = 2 − K m 0 +1 K m 0 N K m 0 +1 ,K m 0 ( i ) N i,i ( i ) , (28) where N a,b ( c ) is the numb er o f channe l matrices in F a × b 2 having rank c . 3) For G ∈ F i and ( V ′ m , V ′ m +1 ) ∈ V ( i , i, V m , V m +1 ) , Pr( H ¯ V m, tx [ t ] , ¯ V m, rx [ t ] [ t ] = G , ¯ V m, tx [ t ] = V ′ m , ¯ V m, rx [ t ] = V ′ m +1 ) = Pr( H ¯ V m, tx [ t ] , ¯ V m, rx [ t ] [ t ] = G ) K m i K m +1 i , (29) where Pr( H ¯ V m, tx [ t ] , ¯ V m, rx [ t ] [ t ] = G ) is gi ven by (27). Pr o of: The p roof is in Ap pendix II. Note that the probabilities in (26) to (29 ) are the same for all m and t . For notational simplicity , we use the shorthand notation P G ( G ) to de note Pr( H ¯ V m, tx [ t ] , ¯ V m, rx [ t ] [ t ] = G ) . T hat is , for G ∈ F i , P G ( G ) = X ( V ′ , V ′′ ) ∈ V ( i,i, V m 0 , V m 0 +1 ) X H ∈H F V m 0 , V m 0 +1 ( G , V ′ , V ′′ ) P H ( H ) |V ( H , V m 0 , V m 0 +1 ) | , (30) where P H ( H ) = p u (1 − p ) K m 0 +1 K m 0 − u and u is the n umber of ones in H . 3 W e do not use t he ef fectiv e channels having all zeros, which gi ve zero rate. 10 2) Pr opose d s cheme: Divide a block into B + M − 1 s ub-blocks having length n B for e ach sub-block, whe re n B = n B + M − 1 . Sinc e block en coding and relaying are applied over M h ops, the nu mber of effecti ve sub-blocks is e qual to B . Th us, the overall rate is gi ven by B B + M − 1 R k . As n → ∞ , the fractiona l rate loss 1 − B B + M − 1 will be negligible be cause we can ma ke both n B and B lar ge e nough. For simplicity , we omit the sub-block index in describing the propos ed s cheme. W e di vide M hop s into tw o parts, the first N hops an d the rest of the M − N hops, wh ere N ∈ { 1 , · · · , M − 1 } . Then, for G ∈ F i , define P α ( G ) = ζ − ( N − 1) i X G 1 , ··· , G N ∈F i , G N ··· G 1 = G N Y m =1 P G ( G m ) , (31) P β ( G ) = ζ − ( M − N − 1) i X G N +1 , ··· , G M ∈F i , G M ··· G N +1 = G M Y m = N +1 P G ( G m ) , (32) and n ( G ) = c − 1 2 n B R min { P α ( G ) , P β ( G − 1 ) } , (33) where ζ i = P G ′ ∈F i P G ( G ′ ) and c 2 = 1 K P K min j =1 j P G ′ ∈F j min { P α ( G ′ ) , P β ( G ′− 1 ) } . W e further de fine n α ( G 1 , · · · , G N ) = c − 1 2 n B Rζ − ( N − 1) i N Y m =1 ( P G ( G m ) − ∆ α ( G 1 , · · · , G N )) , (34) n β ( G N +1 , · · · , G M ) = c − 1 2 n B Rζ − ( M − N − 1) i M Y m = N +1 ( P G ( G m ) − ∆ β ( G N +1 , · · · , G M )) , (35) where G 1 , · · · , G M ∈ F i . He re, ∆ α ( G 1 , · · · , G N ) ≥ 0 a nd ∆ β ( G N +1 , · · · , G M ) ≥ 0 a re s et s uch that X G ′ 1 , ··· , G ′ N ∈F i , G ′ N ··· G ′ 1 = G n α ( G ′ 1 , · · · , G ′ N ) = X G ′ N +1 , ··· , G ′ M ∈F i , G ′ M ··· G ′ N +1 = G − 1 n β ( G ′ N +1 , · · · , G ′ M ) = n ( G ) (36) is satisfied for a ll G ∈ F i . For a gi ven G ∈ F i , the proposed scheme transmits i × n α ( G 1 , · · · , G N ) bits through a series of ef fective c hannels G 1 to G N satisfying G N · · · G 1 = G for all G 1 , · · · , G N ∈ F i . Hence a total of i P G 1 , ··· , G N ∈F i , G N ··· G 1 = G n α ( G 1 , · · · , G N ) = i × n ( G ) bits are transmitted. Then these i × n ( G ) rec eiv ed bits are trans mitted through G N +1 to G M satisfying G M · · · G N +1 = G − 1 for a ll G N +1 , · · · , G M ∈ F i . More s pecifically , i × n β ( G N +1 , · · · , G M ) bits are transmitted through G N +1 to G M and, as a res ult, a total of i P G N +1 , ··· , G M ∈F i , G M ··· G N +1 = G − 1 n β ( G N +1 , · · · , G M ) = i × n ( G ) bits are transmitted. Let n m ( G m ) = ( P G 1 , ··· , G m − 1 , G m +1 , ··· , G N ∈F i n α ( G 1 , · · · , G N ) for m ∈ { 1 , · · · , N } , P G N +1 , ··· , G m − 1 , G m +1 , ··· , G M ∈F i n β ( G N +1 , · · · , G M ) for m ∈ { N + 1 , · · · , M } , (37) where G m ∈ F i . Then i × n m ( G m ) is the total number of bits that are transmitted through G m at the m -th h op. Define T m ( G m , V ′ m , V ′ m +1 ) as the se t of time indices of the sub-bloc k at the m -th ho p s atisfying ¯ V tx ,m [ t ] = V ′ m , ¯ V rx ,m [ t ] = V ′ m +1 , a nd H V ′ m , V ′ m +1 [ t ] = G m , wh ere G m ∈ F i and ( V ′ m , V ′ m +1 ) ∈ V ( i, i, V m , V m +1 ) . For all i ∈ { 1 , · · · , K min } , the detailed en coding and relaying are as follows. • (Encoding) For all G 1 ∈ F i and ( V ′ 1 , V ′ 2 ) ∈ V ( i , i, V 1 , V 2 ) , dec lare an error if |T 1 ( G 1 , V ′ 1 , V ′ 2 ) | < n 1 ( G 1 ) / K 1 i K 2 i , oth- erwise each source in V ′ 1 transmits n 1 ( G 1 ) / K 1 i K 2 i information bits, which are s uppos ed to be transmitted through G 1 , using the time indices in T 1 ( G 1 , V ′ 1 , V ′ 2 ) to the no des in V ′ 2 . • (Relaying for m ∈ { 2 , · · · , M } ) For a ll G m ∈ F i and ( V ′ m , V ′ m +1 ) ∈ V ( i , i, V m , V m +1 ) , declare an error if |T m ( G m , V ′ m , V ′ m +1 ) | is less than n m ( G m ) / K m i K m +1 i , otherwise each node in V ′ m transmits n m ( G m ) / K m i K m +1 i receiv ed bits, which 11 are suppos ed to be transmitted through G m , using the time ind ices in T m ( G m , V ′ m , V ′ m +1 ) to the nodes in V ′ m +1 . If m = M , the transmit bits are con structed by the rec eiv ed b its that o riginate from S ( V ′ M +1 ) , whe re S ( V ′ M +1 ) is the set o f sources of V ′ M +1 . From the prop osed sc heme, the transmission rates a re g i ven by R 1 = · · · = R K = 1 K n B K min X i =1 i X G 1 ∈F i n 1 ( G 1 ) = 1 K n B K min X i =1 i X G 1 , ··· , G N ∈F i n α ( G 1 , · · · , G N ) = R . (38) Let s k ( i ) d enote the i -th information bit of the k -th source a nd t k ,m ( i ) denote the time ind ex of the received s ignal originating from s k ( i ) a t the m -th h op, whe re i ∈ { 1 , · · · , 2 n B R } . That is, s k ( i ) is transmitted u sing the time ind ices t k , 1 ( i ) to t k ,M ( i ) during the multi-hop transmission. The detailed dec oding of the k -th destination is as follows. • (Decoding) For i ∈ { 1 , · · · , n B R } , the k -th destination sets ˆ s k ( i ) = y k ,M [ t k ,M ( i )] . 3) Achievable rate r egion: W e d eri ve the ach iev a ble rate region of the prop osed scheme. Let E m denote the ev ent s uch that |T m ( G m , V ′ m , V ′ m +1 ) | < n m ( G m ) K m i K m +1 i (39) for any G m ∈ F i , ( V ′ m , V ′ m +1 ) ∈ V ( i, i, V m , V m +1 ) , and i ∈ { 1 , · · · , K min } . Th e follo wing le mma shows that there is no error if ( ∪ M m =1 E m ) c occurs. Lemma 3: Supp ose a linear binary fie ld relay network with M ≥ 2 . If the ne twork h as a minimum-dimens ional bottleneck-hop and p j,i,m = p for a ll i , j , and m , then P ( n B ) e,k ≤ M X m =1 Pr( E m ) (40) for all k ∈ { 1 , · · · , K } . Pr o of: The p roof is in Ap pendix I. The followi ng the orem characterizes R that guarantees P ( n B ) e,k → 0 as n B → ∞ . Theorem 3: Suppose a linear binary field relay network with M ≥ 2 . If the network has a minimum-dimensional bottleneck-hop and p j,i,m = p for a ll i , j , and m , then R k = 1 K K min X i =1 i X G ∈F i min { P α ( G ) , P β ( G − 1 ) } (41) is achievable for a ll k ∈ { 1 , · · · , K } , where P α ( G ) and P β ( G ) are defin ed in (31 ) and (32), resp ectiv ely . Pr o of: Let us con sider |T m ( G m , V ′ m , V ′ m +1 ) | . By the we ak law of lar ge numbers [31], there exists a se quence ǫ n B → 0 as n B → ∞ s uch that the proba bility |T m ( G m , V ′ m , V ′ m +1 ) | ≥ n B (Pr( H ¯ V m, tx [ t ] , ¯ V m, rx [ t ] [ t ] = G m , ¯ V m, tx [ t ] = V ′ m , ¯ V m, rx [ t ] = V ′ m +1 ) − δ n B ) = n B P G ( G m ) / K m i K m +1 i − δ n B (42) for all G m ∈ F i , ( V ′ m , V ′ m +1 ) ∈ V ( i, i, V m , V m +1 ) , and i ∈ { 1 , · · · , K min } is greater tha n o r equal to 1 − ǫ n B , where δ n B → 0 a s n B → ∞ . Here the equ ality h olds from the third property of Le mma 2. This indicates that Pr( E m ) ≤ ǫ n B if n m ( G m ) ≤ n B P G ( G m ) − K m i K m +1 i δ n B (43) 12 for all G m ∈ F i and i ∈ { 1 , · · · , K min } . For m ∈ { 1 , · · · , N } , from (37), we also have n m ( G m ) ≤ X G 1 , ··· , G m − 1 , G m +1 , ··· , G N ∈F i c − 1 2 n B Rζ − ( N − 1) i N Y l =1 P G ( G l ) = c − 1 2 n B RP G ( G m ) , (44) where we use the f act that n α ( G 1 , · · · , G N ) ≤ c − 1 2 n B Rζ − ( N − 1) i Q N l =1 P G ( G l ) from (34). Similarly , from (35) a nd (37), n m ( G m ) ≤ c − 1 2 n B RP G ( G m ) for m ∈ { N + 1 , · · · , M } . Then, the cond ition in (43 ) can be sa tisfied if R ≤ c 2 P G ( G m ) − K m i K m +1 i δ n B P G ( G m ) (45) for a ll G m ∈ F i and i ∈ { 1 , · · · , K min } . Henc e, we s et R = c 2 (1 − δ ∗ n B ) , w here δ ∗ n B = ( K max !) 2 δ n B min i ∈{ 1 , ··· ,K min } , G ′ ∈F i { P G ( G ′ ) } , which con verges to ze ro as n B → ∞ . The refore, from Lemma 3, we ha ve P ( n B ) e,k ≤ M ǫ n B , which conv erges to zero as n B → ∞ . In conclusion , R k = c 2 = 1 K K min X i =1 i X G ∈F i min { P α ( G ) , P β ( G − 1 ) } (46) is achievable for a ll k ∈ { 1 , · · · , K } , which c ompletes the proof. For M = 2 , the proposed sc heme pairs G 1 and G 2 satisfying G 2 = G − 1 1 and the a chiev able rate in (41) is giv en b y R k = 1 K K min X i =1 i X G ∈F i min P G ( G ) , P G ( G − 1 ) . (47) Let u s now cons ider the cap acity achieving case. The follo wing corollary shows that if p = 1 / 2 , the sum ca pacity is given by the av erage rank of the cha nnel matrix of the bottleneck-hop . Cor ollary 2: S uppose a linea r binary fi eld relay network with M ≥ 2 . If the network has a minimum-dimens ional bottleneck-hop and p j,i,m = 1 / 2 for all i , j , and m , the s um cap acity is g i ven by C sum = 2 − K m 0 +1 K m 0 X H ∈ F K m 0 +1 × K m 0 2 rank( H ) . (48) Pr o of: From (28), we h av e ζ i = X G ∈F i 2 − K m 0 +1 K m 0 N K m 0 +1 ,K m 0 ( i ) N i,i ( i ) = 2 − K m 0 +1 K m 0 N K m 0 +1 ,K m 0 ( i ) (49) and P α ( G ) = ζ − ( N − 1) i X G 1 , ··· , G N ∈F i , G N ··· G 1 = G N Y m =1 2 − K m 0 +1 K m 0 N K m 0 +1 ,K m 0 ( i ) N i,i ( i ) = 2 − K m 0 +1 K m 0 N K m 0 +1 ,K m 0 ( i ) ( N i,i ( i )) N X G 1 , ··· , G N ∈F i G N ··· G 1 = G 1 = 2 − K m 0 +1 K m 0 N K m 0 +1 ,K m 0 ( i ) N i,i ( i ) . (50) Similarly , P β ( G ) = 2 − K m 0 +1 K m 0 N K m 0 +1 ,K m 0 ( i ) N i,i ( i ) . T hen, from (41), R k = 1 K 2 − K m 0 +1 K m 0 K min X i =1 iN K m 0 +1 ,K m 0 ( i ) = 1 K 2 − K m 0 +1 K m 0 X H ∈ F K m 0 +1 × K m 0 2 rank( H ) (51) 13 2 s 2 s 1 s 1 s 2 s 2 s 2 s 2 s 2 s 2 s 1 s 2 s 1 2 s s 2 s 1 s 1 s 1 s 2 s 1 s 2 s 1 s 1 s 1 s 2 s 1 s 1 2 s s 1 s 1 s 1 s 2 s 1 2 s s 2 s 1 s 2 s 1 2 s s 1 s 1 s 1 s 1 s 2 s 1 s 2 s Fig. 4. Deterministic channel pairing between the first and the second hops. is a chiev able for all k ∈ { 1 , · · · , K } . Hen ce the sum rate in (48) is achievable, which coincides with the sum rate upper bound in (14). In conclusion, Corollary 2 holds. Remark 2: Corollary 2 can b e directly extended to a general linear finite field relay network in which inputs, outputs, and ch annels are in F q and chan nels a re i.i.d. uniformly dis trib uted over F q . T hen C sum = q − K m 0 +1 K m 0 X H ∈ F K m 0 +1 × K m 0 q rank( H ) log q . (52) Notice that Corollary 2 shows that the sum rate of E (r an k ( H m 0 [1])) is ach iev a ble, which is the multi-input multi-output (MIMO) capac ity of the b ottleneck-hop . This result also shows that the max-flow min-cut theorem holds for a c ertain c lass of cha nnel distributions and network topologies. For 2 – 2 – 2 networks, we charac terize the su m ca pacity for more general c lasses of chann el distributi ons by applying deterministic chan nel pairing. Theorem 4: Suppose a linear binary field relay ne twork with M = 2 a nd K 1 = K 2 = K 3 = 2 . 1) For a symmetric channel s atisfying p 1 , 1 , 1 = p 2 , 2 , 1 = p 1 , 1 , 2 = p 2 , 2 , 2 and p 1 , 2 , 1 = p 2 , 1 , 1 = p 1 , 2 , 2 = p 2 , 1 , 2 or a Z c hannel satisfying p 2 , 1 , 1 = p 2 , 1 , 2 = 0 , p 1 , 1 , 1 = p 1 , 1 , 2 , p 1 , 2 , 1 = p 1 , 2 , 2 , a nd p 2 , 2 , 1 = p 2 , 2 , 2 , the sum c apacity is given by C sum = E (rank( H 1 [1])) . (53) 2) For a Z cha nnel satisfying p 2 , 1 , 1 = p 2 , 1 , 2 = 0 , p 1 , 1 , 1 = p 2 , 2 , 2 , p 1 , 2 , 1 = p 1 , 2 , 2 , and p 2 , 2 , 1 = p 1 , 1 , 2 , the sum capac ity is given by C sum = m in { 2 p 1 , 1 , 1 , 2 p 2 , 2 , 1 } . (54) Pr o of: W e use de terministic c hannel pairing between the first and the second hops. The overall bloc k encoding and relaying structure ma king su ch pairing pos sible is the sa me a s in the p revi ous sche me. Let us prove the first resu lt. Fig. 4 illustrates the deterministic chan nel pa iring between the first and the se cond hops a nd related encoding and relaying. The solid lines and the dashed lines denote the correspond ing channe ls are ones and z eros, respectively . The symbols in the figure de note the trans mit s ignals o f the nod es a nd the nod es with no s ymbol transmit z eros, where s k denotes the information bit of the k -th source . Let p (1) m to p (16) m denote 16 possible ins tances o f H m [ t ] as shown in F ig. 5, where m ∈ { 1 , 2 } . Th en the achiev able sum rate o f the deterministic pairing in Fig. 4 is g i ven by R sum = X i ∈{ 2 , 4 , 6 , 9 , 11 , 13 , 16 } min { p ( i ) 1 , p ( i ) 2 } + min { p (3) 1 , p (5) 2 } + min { p (5) 1 , p (3) 2 } + 2 X i ∈{ 7 , 10 , 12 , 14 } min { p ( i ) 1 , p ( i ) 2 } + 2 min { p (8) 1 , p (15) 2 } + 2 min { p (15) 1 , p (8) 2 } . (55) 14 (1 ) m p ( 2 ) m p ( 7 ) m p ( 8) m p ( 6 ) m p ( 5 ) m p ( 4 ) m p ( 3) m p ( 9 ) m p (10) m p (15) m p (16) m p (14) m p (13) m p (12) m p (11 ) m p Fig. 5. 16 possible instances of H m [ t ] . 0 0.2 0.4 0.6 0.8 1 0 0.5 1 1.5 2 2.5 p C sum [bits/channel use] 2−2−2 networks 3−3−3 networks (lower bound) 3−3−3 networks (upper bound) Fig. 6. Sum capacity when p j,i,m = p for all i , j , and m . Since the prob abilities of e ach paired H 1 [ t 1 ] and H 2 [ t 2 ] are the same, from (55), we have R sum = X i ∈{ 2 , 3 , 4 , 5 , 6 , 9 , 11 , 13 , 16 } p ( i ) 1 + 2 X i ∈{ 7 , 8 , 10 , 12 , 14 , 15 } p ( i ) 1 = E (rank( H 1 [1])) . (56) Notice that the ac hiev able sum rate c oincides with the sum rate upper b ound in (14). Now let us prove the seco nd result. Unlike the previous case , the probabilities of some paired H 1 [ t 1 ] and H 2 [ t 2 ] in Fig. 4 are n ot the same. Let us den ote p a = p 1 , 1 , 1 = p 2 , 2 , 2 , p b = p 1 , 2 , 1 = p 1 , 2 , 2 , and p c = p 2 , 2 , 1 = p 1 , 1 , 2 . For p a ≥ p c , from (55), R sum = p (2) 1 + p (6) 1 + p (9) 2 + p (13) 2 + 2 p (10) 1 + 2 p (14) 1 = (1 − p a )(1 − p b ) p c + (1 − p a ) p b p c + (1 − p a )(1 − p b ) p c + (1 − p a ) p b p c + 2 p a (1 − p b ) p c + 2 p a p b p c = 2 p c (57) is achievable. By se tting Ω 1 = { v 1 , 1 , v 1 , 2 , v 2 , 1 } , we have R sum ≤ E (rank( [ h 2 , 2 , 1 [1] , 0] T , [0 , h 1 , 1 , 2 [1]] T ) T ) = 2 p c , (58) which coincides with (57). Similarly , for p a < p c , from (55), R sum = p (2) 2 + p (6) 2 + p (9) 1 + p (13) 1 + 2 p (10) 1 + 2 p (14) 1 = 2 p a (59) is achiev able. From Ω 2 = { v 1 , 1 } and Ω 3 = { v 1 , 1 , v 1 , 2 , v 1 , 3 , v 2 , 1 , v 2 , 2 } , we h av e R 1 ≤ p a and R 2 ≤ p a , re spectively . Then R sum ≤ 2 p a , wh ich coinc ides with (59 ). In conc lusion, Theorem 4 holds. Example 3 ( 2 – 2 – 2 and 3 – 3 – 3 n etworks): Fig. 6 plots sum rates of two-hop networks with p j,i,m = p . For 2 – 2 – 2 networks, the sum c apacity is given by C sum = 4 pq 3 + 8 p 2 q 2 + 8 p 3 q + p 4 , whe re q = 1 − p . Notice that the c onsidered 15 channe l distrib ution is a special cas e of the symmetric ch annel in The orem 4. Therefore, we ca n c haracterize the sum capacity for all p ∈ [0 , 1] . For 3 – 3 – 3 networks, we obtain C sum ≥ 9 pq 8 + 54 p 2 q 7 + 168 p 3 q 6 + 279 p 4 q 5 + 216 p 5 q 4 + 72 | p 5 q 4 − p 6 q 3 | + 216 min { p 5 q 4 , p 6 q 3 } + 90 p 6 q 3 + 90 p 7 q 2 + 18 p 8 q + p 9 and C sum ≤ 9 pq 8 + 54 p 2 q 7 + 168 p 3 q 6 + 279 p 4 q 5 + 324 p 5 q 4 + 198 p 6 q 3 + 90 p 7 q 2 + 18 p 8 q + p 9 . T he lower and upper boun ds are the s ame when p = 1 2 , wh ich c oincides with the resu lt of Corollary 2 (if p = 0 o r 1 the lo wer a nd upp er bound s are triviall y the same). Example 4 (Networks with K = K 1 = · · · = K M +1 ): Suppose a l inear finite field relay network with K = K 1 = · · · = K M +1 in which inputs, o utputs, and c hannels are in F q and channe ls are i.i.d. uniformly distrib uted over F q . From Remarks 1 an d 2, we have C sum = ( K 2 log q if M = 1 , E (rank( H m 0 [1])) log q if M ≥ 2 . (60) For K = K 1 = · · · = K M +1 = 2 and q = 2 , C sum is g i ven by 1 if M = 1 and 21 / 16 if M ≥ 2 . V . C O N C L U S I O N In this pap er , we stud ied lay ered li near binary field relay networks with time-v arying channels, which exhibit broadcas t, interference, and fading natures of wireless commun ications. Capa city c haracterization of s uch relay networks with mu ltiple S–D p airs is quite challenging bec ause the transmiss ion of other ses sion acts as inter- user interference. W e observed that the fading can play a n important role in mitigating interferenc e that lead s to the capa city c haracterization for s ome classe s o f chann el distributions and n etwork top ologies. For these classes , we showed that the capacity region of sing le-hop networks and the sum capacity o f mu lti-hop networks can be interpreted as the max -flow min-cut theorem. A P P E N D I X I U P P E R B O U N D O N T H E P RO BA B I L I T Y O F E R RO R Pr o of of Lemma 1: Let us ass ume that ( E 1 ∪ E 2 ) c occurs. Th en, from the assumption, ea ch source can trans mit n ( H 1 ) bits using the ti me indices in T 1 ( H 1 ) for all H 1 . Sinc e n ( H 1 ) = n ( H 1 + I ) , from the ass umption, each source can retrans mit all information bits that we re transmitted during T 1 ( H 1 + I ) using the time indices in T 2 ( H 1 ) for all H 1 . La stly , there is n o dec oding error if ( E 1 ∪ E 2 ) c occurs sinc e H 1 [ t 1 ( i )] + H 1 [ t 2 ( i )] = I , me aning ˆ s k ( i ) = s k ( i ) . In conclusion, from the u nion bound, we o btain P ( n ) e,k ≤ Pr( E 1 ) + Pr( E 2 ) , which completes the proof. Pr o of of Lemma 3: Let us as sume that ( ∪ M m =1 E m ) c occurs. Then e ach source ca n transmit all information bits to the n odes in the next layer . Conside r the m -th hop transmission through G m ∈ F i , where m ∈ { 2 , · · · , M − 1 } . Each node in V ′ m receiv es n m ( G m ) / K m − 1 i K m i bits from V ′ m − 1 that should be transmitted through G m . Since there are K m − 1 i candidates for V ′ m − 1 , a total of n m ( G m ) / K m i bits should be transmitted through G m . From the assumption, e ach nod e in V ′ m is a ble to transmit n m ( G m ) / K m i K m +1 i bits to the nodes in V ′ m +1 using the time indices in T m ( G m , V ′ m , V ′ m +1 ) . Since there are K m +1 i candidates for V ′ m +1 , e ach nod e in V ′ m can trans mit a total of n m ( G m ) / K m i bits throug h G m . He nce, ea ch no de in V ′ m can transmit all received b its. Co nsider the last hop transmission. Similar to the previous hops, each node in V ′ M receiv es n M ( G M ) / K M i bits that should be transmitted through G M and, a mong them, n M ( G M ) / K 1 i K M i bits are originated from S ( V ′ M +1 ) . From the assumption, each node in V ′ M is able to transmit n M ( G M ) / K M i K M +1 i bits to the nodes in V ′ M +1 using the time indices in T M ( G M , V ′ M , V ′ M +1 ) . Hen ce, each no de in V ′ M can transmit a ll received bits because n M ( G M ) / K 1 i K M i is equa l to n M ( G M ) / K M i K M +1 i , wh ere we use the fact that K = K 1 = K M +1 . Lastly , c onsider the e stimated bit ˆ s k ( i ) at the k -th d estination. Since the ov erall c hannel matrix from ¯ V tx , 1 [ t k , 1 ( i )] to ¯ V rx ,M [ t k ,M ( i )] is given by H ¯ V tx ,M [ t k,M ( i )] , ¯ V rx ,M [ t k,M ( i )] [ t k ,M ( i )] · · · H ¯ V tx , 1 [ t k, 1 ( i )] , ¯ V rx , 1 [ t k, 1 ( i )] [ t k , 1 ( i )] = I , (61) we obtain ˆ s k ( i ) = s k ( i ) . Henc e, there is no error if ( ∪ M m =1 E m ) c occurs. In conc lusion, from the u nion bound, we obtain P ( n B ) e,k ≤ P M m =1 Pr( E m ) , which c ompletes the p roof. 16 T ABL E I N O TA T I O N S U S E D I N A P P E N D I X I . P (1) m ( H m ) Pr( H m [ t ] = H m ) P (2) m ( H ) Pr( H V m, tx [ t ] , V m, rx [ t ] [ t ] = H ) P (3) m ( V ′ , V ′′ H m ) Pr( V m, tx [ t ] = V ′ , V m, rx [ t ] = V ′′ H m [ t ] = H m ) P (4) m ( H H m , V ′ , V ′′ ) Pr( H V m, tx [ t ] , V m, rx [ t ] [ t ] = H H m [ t ] = H m , V m, tx [ t ] = V ′ , V m, rx [ t ] = V ′′ ) P (5) m ( V ′ , V ′′ ) Pr( V m, tx [ t ] = V ′ , V m, rx [ t ] = V ′′ ) P (6) m ( G ) Pr( H ¯ V m, tx [ t ] , ¯ V m, rx [ t ] [ t ] = G ) P (7) m ( V ′ , V ′′ H ) Pr( ¯ V m, tx [ t ] = V ′ , ¯ V m, rx [ t ] = V ′′ H V m, tx [ t ] , V m, rx [ t ] [ t ] = H ) P (8) m ( G H , V ′ , V ′′ ) Pr( H ¯ V m, tx [ t ] , ¯ V m, rx [ t ] [ t ] = G H V m, tx [ t ] , V m, rx [ t ] [ t ] = H , ¯ V m, tx [ t ] = V ′ , ¯ V m, rx [ t ] = V ′′ ) P (9) m ( G , V ′ , V ′′ ) Pr( H ¯ V m, tx [ t ] , ¯ V m, rx [ t ] [ t ] = G , ¯ V m, tx [ t ] = V ′ , ¯ V m, rx [ t ] = V ′′ ) A P P E N D I X I I P R O BA B I L I T Y D I S T R I B U T I O N S O F S U B - C H A N N E L M A T R I C E S In this appendix, we prove the proba bility distrib utions shown in Lemma 2. For notational s implicity , we will use the shorthan d notations in T able I. Pr o of of Lemma 2.(1): W e a ssume that |V m, tx [ t ] | = K m 0 and |V m, rx [ t ] | = K m 0 +1 in the proof. But the sa me result holds for the case wh ere |V m, tx [ t ] | = K m 0 +1 and |V m, rx [ t ] | = K m 0 . W e have P (2) m ( H ) = X ( V ′ , V ′′ ) ∈ V ( K m 0 ,K m 0 +1 , V m , V m +1 ) X H m ∈ F K m +1 × K m 2 P (1) m ( H m ) P (3) m V ′ , V ′′ H m P (4) m H H m , V ′ , V ′′ ( a ) = X ( V ′ , V ′′ ) ∈ V ( K m 0 ,K m 0 +1 , V m , V m +1 ) P (5) m V ′ , V ′′ X H m ∈ F K m +1 × K m 2 P (1) m ( H m ) P (4) m H H m , V ′ , V ′′ ( b ) = X ( V ′ , V ′′ ) ∈ V ( K m 0 ,K m 0 +1 , V m , V m +1 ) P (5) m V ′ , V ′′ X H m ∈H V m , V m +1 ( H , V ′ , V ′′ ) P (1) m ( H m ) ( c ) = p u (1 − p ) K m 0 +1 K m 0 − u , (62) where ( a ) h olds from the fact that P (3) m V ′ , V ′′ H m = P (5) m ( V ′ , V ′′ ) beca use V m, tx [ t ] and V m, rx [ t ] are c hosen regardless of cha nnel instan ces, ( b ) holds s ince P (4) m H H m , V ′ , V ′′ = ( 1 if H m ∈ H V m , V m +1 ( H , V ′ , V ′′ ) 0 otherwise , (63) and ( c ) holds since P H m ∈H V m , V m +1 ( H , V ′ , V ′′ ) P (1) m ( H m ) = p u (1 − p ) K m 0 +1 K m 0 − u . Th erefore, Lemma 2.(1) h olds. 17 Pr o of of Lemma 2.(2): W e ag ain assume that |V m, tx [ t ] | = K m 0 and |V m, rx [ t ] | = K m 0 +1 in the proo f. W e h av e P (6) m ( G ) = X ( V ′ , V ′′ ) ∈ V ( i,i, V m, tx [ t ] , V m, rx [ t ]) X H ∈ F K m 0 +1 × K m 0 2 P (2) m ( H ) P (7) m ( V ′ , V ′′ | H ) P (8) m ( G | H , V ′ , V ′′ ) ( a ) = X ( V ′ , V ′′ ) ∈ V ( i,i, V m, tx [ t ] , V m, rx [ t ]) X H ∈H F V m, tx [ t ] , V m, rx [ t ] ( G , V ′ , V ′′ ) P (2) m ( H ) P (7) m ( V ′ , V ′′ | H ) ( b ) = X ( V ′ , V ′′ ) ∈ V ( i,i, V m, tx [ t ] , V m, rx [ t ]) X H ∈H F V m, tx [ t ] , V m, rx [ t ] ( G , V ′ , V ′′ ) P (2) m ( H ) |V ( H , V m, tx [ t ] , V m, rx [ t ]) | ( c ) = X ( V ′ , V ′′ ) ∈ V ( i,i, V m 0 , V m 0 +1 ) X H ∈H F V m 0 , V m 0 +1 ( G , V ′ , V ′′ ) P (2) m ( H ) |V ( H , V m 0 , V m 0 +1 ) | , (64) where ( a ) ho lds since P (8) m ( G | H , V ′ , V ′′ ) = ( 1 if H ∈ H F V m, tx [ t ] , V m, rx [ t ] ( G , V ′ , V ′′ ) 0 otherwise , (65) ( b ) holds since P (7) m ( V ′ , V ′′ | H ) = 1 |V ( H , V m, tx [ t ] , V m, rx [ t ]) | if H ∈ H F V m, tx [ t ] , V m, rx [ t ] ( G , V ′ , V ′′ ) , and ( c ) holds from the facts that P (2) m ( H ) is the s ame for all m , which is the result of Le mma 2.(1), an d |V ( H , V m, tx [ t ] , V m, rx [ t ]) | is the same for all m . Now con sider the ca se p j,i,m = 1 / 2 . Since r ank( H ¯ V m, tx [ t ] , ¯ V m, tx [ t ] [ t ]) = rank( H V m, tx [ t ] , V m, tx [ t ] [ t ]) , we obtain X G ′ ∈F i P (6) m ( G ′ ) = X H ∈ F K m 0 +1 × K m 0 2 , rank( H )= i P (2) m ( H ) , (66) where P (2) m ( H ) = 2 − K m 0 +1 K m 0 (67) and P (6) m ( G ′ ) = 2 − K m 0 +1 K m 0 X ( V ′ , V ′′ ) ∈ V (rank( G ′ ) , rank( G ′ ) , V m 0 , V m 0 +1 ) X H ∈H F V m 0 , V m 0 +1 ( G ′ , V ′ , V ′′ ) 1 |V ( H , V m 0 , V m 0 +1 ) | . (68) Here, (67) a nd (68) can be derived from L emma 2. (1) and (64). The n we will prove the following two properties: 1) P H ∈H F V m 0 , V m 0 +1 ( G ′ , V ′ , V ′′ ) 1 |V ( H , V m 0 , V m 0 +1 ) | is the same for all V ′ and V ′′ . 2) P H ∈H F V m 0 , V m 0 +1 ( G ′ , V ′ , V ′′ ) 1 |V ( H , V m 0 , V m 0 +1 ) | is the same for all G ′ having the same ran k. T o p rove the first property , consider two ( V ′ a , V ′′ a ) and ( V ′ b , V ′′ b ) . Then we can find a row permutation matrix E row and a column permutation matrix E col such that H F V m 0 , V m 0 +1 ( G ′ , V ′ a , V ′′ a ) = { E row HE col H ∈ H F V m 0 , V m 0 +1 ( G ′ , V ′ b , V ′′ b ) } . (69) Therefore, from the fact that |V ( H , V m 0 , V m 0 +1 ) | = |V ( E row HE col , V m 0 , V m 0 +1 ) | , the first prop erty holds. Now con sider the sec ond prop erty . W e assume tha t V ′ = { v 1 ,m 0 , · · · , v i,m 0 } and V ′′ = { v 1 ,m 0 +1 , · · · , v i,m 0 +1 } for the proof, but the s ame p roperty c an be eas ily de ri ved for arbitrary V ′ and V ′′ by using the first prope rty . Fig. 7 illustrates the con struction of H F V m 0 , V m 0 +1 ( G ′ , V ′ , V ′′ ) . W e ob tain i × ( K m 0 − i ) matrix G 1 = G ′ A , where A ∈ F i × ( K m 0 − i ) 2 . Th en ( K m 0 +1 − i ) × K m 0 matrix G 2 is obtained b y setting G 2 = B [ G ′ , G 1 ] , where B ∈ F ( K m 0 +1 − i ) × i 2 . Therefore, we obtain H F V m 0 , V m 0 +1 ( G ′ , V ′ , V ′′ ) = n [ G ′ , G 1 ] T , [ G 2 ] T T A ∈ F i × ( K m 0 − i ) 2 , B ∈ F ( K m 0 +1 − i ) × i 2 o . (70) 18 ' G 1 ' G G A 2 1 [ ' , ] G B G G i i i K m ! 1 0 i K m 0 Fig. 7. Construction of H F V m 0 , V m 0 +1 ( G ′ , V ′ , V ′′ ) , where A ∈ F i × ( K m 0 − i ) 2 , and B ∈ F ( K m 0 +1 − i ) × i 2 . Then, for gi ven A and B , V [ G ′ , G 1 ] T , [ G 2 ] T T , V m 0 , V m 0 +1 is the same for all G ′ having the same rank. Therefore, the seco nd prop erty h olds. From the above tw o properties, P H ∈H F V m 0 , V m 0 +1 ( G ′ , V ′ , V ′′ ) 1 |V ( H , V m 0 , V m 0 +1 ) | is the same for all V ′ , V ′′ , and G ′ having the same rank. W e also know tha t |V (rank( G ′ ) , rank( G ′ ) , V m 0 , V m 0 +1 ) | is the sa me for all G ′ having the same ra nk. As a res ult, P (6) m ( G ′ ) is the s ame for a ll G ′ having the same rank. Th us, from (66) and (67), we have P (6) m ( G ) X G ′ ∈F i 1 = 2 − K m 0 +1 K m 0 X H ∈ F K m 0 +1 × K m 0 2 , rank( H )= i 1 . (71) Since P G ′ ∈F i 1 = N i,i ( i ) and P H ∈ F K m 0 +1 × K m 0 2 , rank( H )= i 1 = N K m 0 +1 ,K m 0 ( i ) , we fi nally o btain P (6) m ( G ) = 2 − K m 0 +1 K m 0 N K m 0 +1 ,K m 0 ( i ) N i,i ( i ) . (72) In conclus ion, Le mma 2.(2) ho lds. Pr o of o f Lemma 2.(3): From the definitions of P (6) m ( G ) and P (9) m ( G , V ′ , V ′′ ) , we ob tain P (6) m ( G ) = X ( V ′ , V ′′ ) ∈V ( i,i, V m , V m +1 ) P (9) m ( G , V ′ , V ′′ ) = K m i K m +1 i P (9) m ( G , V ′ m , V ′ m +1 ) , (73) where the se cond equ ality holds since |V ( i, i, V m , V m +1 ) | = K m i K m +1 i and P (9) m ( G , V ′ , V ′′ ) is the same for all V ′ and V ′′ . Thus, we h av e P (9) m ( G , V ′ m , V ′ m +1 ) = P (6) m ( G ) / K m i K m +1 i , (74) which completes the proo f. R E F E R E N C E S [1] T . M. Cover and A. El Gamal, “Capacity theorems for the relay channel, ” IEEE Tr ans. I nf. Theory , vol. I T -25, pp. 572–584 , S ep. 1979 . [2] L. R. Ford Jr . and D. R. Fulkerson, Flows in Networks . Princeton, NJ: Princeton Univ . Press, 1962. [3] R. Ahlswede, N. Cai, S.-Y . R. Li, and R. W . Y eung , “Network information flow , ” IE EE T rans. Inf. Theory , vol. 46, pp. 1204 –1216, Jul. 2000. [4] S.-Y . R. L i, R. W . Y uung, and N. Cai, “L inear netwo rk coding, ” IEEE T rans. Inf. Theory , vol. 49, pp. 371– 381, Feb . 2003. [5] R. K oetter and M. M ´ edard, “ An algebraic approach to network coding, ” IEE E Tr ans. Inf. T heory , vol. 11, pp. 782–795, Oct. 2003. [6] T . Ho, M. M ´ edard, R. Koetter , D. R. Karger , M. E ffro s, J. Shi, and B. Leong, “ A random linear network coding approach to multicast, ” IEEE T rans. Inf. Theory , vol. 52, pp. 4413–44 30, Oct. 2006. [7] M. R. Aref, “Information Flow in Relay Networks, ” Ph.D. dissertation, Stanford Univ ., 1980. [8] N. Ratnakar and G. Kramer , “The multicast capac ity of deterministic r elay netwo rks with no interference, ” IEEE T rans. Inf. Theory , vol. 52, pp. 2425–2432, Jun. 2006. [9] A. F . Dana, R. Gowaikar , R. Palanki, B . Hassibi, and M. Effros, “Capacity of wireless erasure networks, ” IEEE T rans. I nf. Theory , vol. 52, pp. 789–804, Mar . 2006. 19 [10] B. S mith and S. V ishwanath, “Unicast transmission over multiple access erasure networks: capacity and duality , ” in Pr oc. IEEE Information Theory W orkshop , Lake T ahoe, CA, Sep. 2007. [11] S. Ray , M. M ´ edard, and J. Abounadi, “Rand om coding in noise-free multiple access networks over finit e fields, ” in Pr oc. IEEE GLOBECOM , San Francisco, CA, Dec. 2003. [12] S. Bhadra, P . Gupta, and S. S hakko ttai, “On network coding for interference networks, ” in Pr oc. IEEE Int. Symp. Information Theory (ISIT) , Seattle, W A, Jul. 2006. [13] A. S. A vestimehr , S. N. Diggavi, and D. Tse, “W ireless netwo rk information flow , ” in Pro c. 45th Annu. Allerton Conf. Communication, Contr ol, and Computing , Monticello, IL, Sep. 2007. [14] ——, “ A pproximate capacity of Gaussian relay networks, ” in Pr oc. I EEE Int. Symp. Information Theory (ISIT) , T oronto, Canada, Jul. 2008. [15] R. H. Etkin, D. Tse, and H. W ang, “Gaussian interference channel capacity to within one bit, ” IEEE T rans. Inf. Theory , vol. 54, pp. 5534–5 562, Dec. 2008. [16] G. Bresler and D. Tse, “The t wo-user Gaussian interference chann el: a deterministic vie w , ” Euro pean T rans. T elecommunications , vol. 19, pp. 333–354, Apr . 2008. [17] G. Bresler , A. Parekh, and D. T se, “The approx imate capacity of the man y-to-one and one-to-many Gaussian interference chann els, ” in Pr oc. 45th Annu. Allerton Conf. Communication, Contro l, and Computing , Monticello, IL, Sep. 2007. [18] A. S. A vestimehr , A. Sezgin, and D . Tse, “ Approx imate capacity of the two-way relay channel: a deterministic approach, ” in Proc . 46th Annu. Allerton Conf. C ommunication, Contr ol, and Computing , Monticello, IL , S ep. 2008. [19] W . Nam, S.-Y . Chung, and Y . H. Lee, “Capacity of t he Gaussian two-way relay channel to within 1 2 bit, ” IEEE T rans. Inf. Theory , vol. 56, pp. 5488–5494, Nov . 2010. [20] S. Mohajer , S. N. Diggavi, C. F ragouli, and D. Tse, “T ransmission techniques for relay-interference networks, ” in Pr oc. 46th Annu. Allerton Conf. Communication, Contro l, and Computing , Monticello, IL, S ep. 2008. [21] S. Mohajer , S. N. Diggavi, and D. Tse, “ Approximate capacity of a class of Gaussian relay-interference networks, ” in Proc. IEEE Int. Symp. Information Theory (ISIT) , Seoul, South K orea, Jun./Jul. 2009. [22] V . Aggarwal, Y . Liu, and A. S abharwa l, “Sum-capacity of interference channels with a l ocal vie w: impact of distr ibuted decisions, ” submitted to IEEE T rans. Inf. T heory , Oct. 2009. [Online]. A v ailable: http://arxiv .org/abs/0 910.3494. [23] R. El Haddad, B. Smith, and S . V ishwanath, “On models for multi-user Gaussian channels with fading, ” in Pr oc. 7th I nt. Symp. Modeling and Optimization in Mobile, A d Hoc, and W ireless Networks (W iOpt) , Seoul, South K orea, Jun. 2009. [24] S.-H. Lim, Y .-H. Kim, and S.-Y . Chung, “Deterministic relay networks with state information, ” in Proc. IEEE Int. Symp. Information Theory (ISIT) , Seoul, South K orea, Jun./Jul. 2009. [25] V . R. Cadambe and S. A. Jafar , “Multiple access outerbounds and the inseparability of parallel interference channels, ” in P r oc. IEEE GLOBECOM , New Orleans, LA, Nov ./Dec. 2008. [26] L. Sankar , X. Shang, E. Erkip, and H. V . Poor, “Ergodic two-user interference channels: is separability optimal?” in Pr oc. 46th Annu. Allerton Conf. Communication, Contro l, and Computing , Monticello, IL, S ep. 2008. [27] S.-W . Jeon and S.- Y . Chung, “Capacity of a class of multi-source relay networks, ” in Information T heory and Applications W orkshop , Univ ersit y of California San Diego, La Jolla , CA, Feb . 2009. [28] B. N azer , M. Gastpar , S. A. Jafar , and S. V ishwanath, “Ergodic interference alignment, ” in Pr oc. IEEE Int. Symp. Information Theory (ISIT) , Seoul, South K orea, Jun./Jul. 2009. [29] V . R. Cadambe and S. A. Jafar , “Interference alignment and degrees of freedom of the K -user interference channel, ” IEEE T rans. Inf. Theory , vol. 54, pp. 3425–3441, Aug. 2008. [30] ——, “Interference alignment and the deg rees of freedom of wireless X networks, ” IEEE Tr ans. Inf. Theory , vol. 55, pp. 3893–3908, Sep. 2009. [31] I. Csisz ´ ar and J. K ¨ orne r, Information Theory: Coding Theor ems for Discr ete Memoryless Systems . New Y ork: Academic Press, 1981.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment