Resource Allocation for Downlink Cellular OFDMA Systems: Part II - Practical Algorithms and Optimal Reuse Factor
In a companion paper, we characterized the optimal resource allocation in terms of power control and subcarrier assignment, for a downlink sectorized OFDMA system. In our model, the network is assumed to be one dimensional for the sake of analysis. W…
Authors: Nassar Ksairi, Pascal Bianchi, Phiippe ciblat
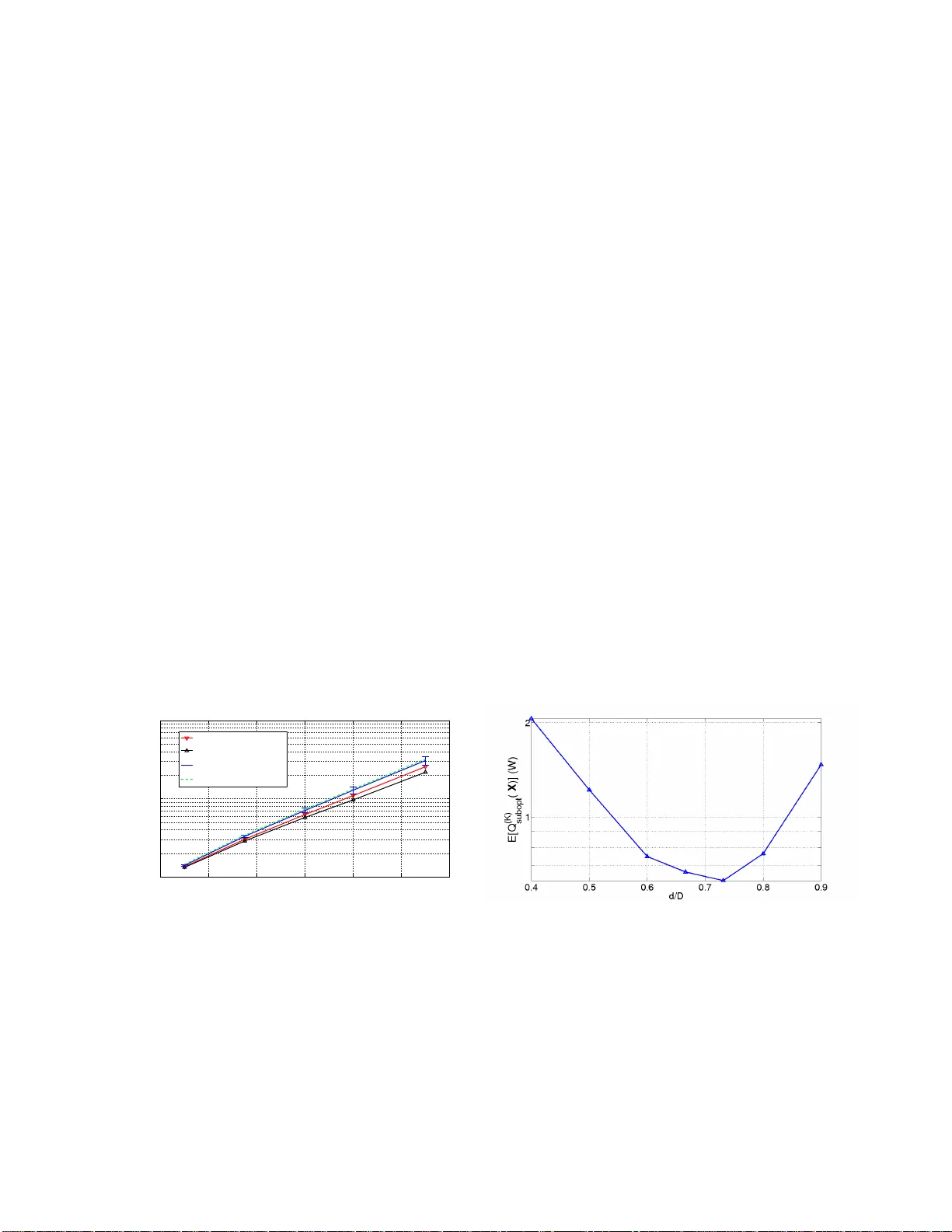
1 Resource Allocation for Do wnlink Cellular OFDMA Systems: P art II—Pract ical Algorithms and Optimal Reuse F actor Nassar Ksairi (1) , Pascal Bianchi (2) , Philippe Ciblat (2) , W alid Hachem (2) Abstract In a compan ion paper (see Res o urce Allocation for Downlink Cellular OFDMA Systems: Part I — Optimal Allo cation), we characterized the optimal resource allocation in terms of power con trol and subcarrier assignment, for a d ownlink sectorized OFDMA system imp aired by multicell interference . In our mo del, the network is assumed to be one dimen sional (linear) fo r the sake of ana lysis. W e also assume that a certain part of the av ailab le ban dwidth is likely to be reused b y different ba se stations while th at the other par t of th e ban dwidth is shared in an ortho gonal way be tween these base stations. The optimal resourc e allocation cha racterized in Part I is obtained by minim izing the total power sp ent by the n etwork under the constraint that all user s’ rate requ irements are satisfied. It is worth noting th at when optimal resource allocation is used, an y user receives data either in th e reused ban dwidth o r in the protected b andwidth, but not in both (excep t for at most one p i vot-user in each cell). W e also pr oposed an algorithm that determ ines the optimal values of users’ resou rce alloca tion parameters. As a matter of fact, the optimal allocation algorithm propo sed in Part I requires a large nu mber of operation s. In the present paper, we propose a distributed practical resource allo cation algo rithm with low complexity . W e study the asymptotic b ehavior o f b oth this simplified resou rce allocation algorith m and the optimal resource allocation algor ithm of Part I as the num ber of user s in ea ch cell tends to infinity . Our a nalysis allo ws to pr ove that the pr oposed simp lified algo rithm is asymptotically o ptimal i.e., it achieves th e same a symptotic transmit p ower as the optimal algorithm as the numb er of users in each cell tends to infinity . As a by produ ct o f our analy sis, we ch aracterize the optimal value o f the frequ ency (1) Sup ´ elec, Plateau de Moulon 91192 Gif-sur -Yvette Cedex, France (nassar .ksairi@supelec.fr). Phone: +33 1 69 85 14 54, Fax: +33 1 69 85 14 69. (2) CNRS / T elecom ParisT ech (ENST), 46 rue Barrault 75634 Paris Cedex 13, France (bianchi@telecom- paristech.fr ,ciblat@telecom-paristech.fr ,walid.hachem@en st.fr). P hone: +33 1 45 81 83 60, Fax: +33 1 45 81 71 44. Nov ember 21, 2021 DRAFT 2 reuse factor . Simulations sustain o ur claims and s how that su bstantial perfo rmance im provements are obtained when the optimal value o f th e fr equency reuse factor is used . Index T erms OFDMA, Multicell Resource Allocation, Distributed Resour ce Allo cation, A symptotic Analysis. I . I N T R O D U C T I O N In a c ompanion paper [1], we introdu ced the p roblem of joint power c ontrol and su bcarrier assignmen t in the downlink of a one-dimensiona l s ectorized two-cell OFDMA system. Resou rce a llocation parameters have be en ch aracterized in s uch a way that i) the total transmit power of the network is minimum a nd ii) all use rs’ rate requirements are satisfied. Similarly to [2], we in vestigate the ca se where the channe l state information at the Base Station (BS) side is limited to s ome cha nnel statistics. Howe ver , contrary to [2], our mod el ass umes that the av ailable bandwidth is di vided into two ba nds: the first one is reused by dif ferent b ase s tations (a nd is thus sub ject to mu lticell interference ) while the se cond o ne is sh ared in an orthogonal way betwee n the adjacent base s tations (and is thus protected from mu lticell interference). The number of subca rriers in ea ch ban d is directly related to the freque ncy reuse factor . W e a lso a ssume that eac h user is likely to modulate subc arriers in eac h o f these two bands and thus we do not a ssume a priori a geographic al sep aration of u sers mo dulating in the two different ba nds. The solution to the ab ove resource allocation problem is g i ven in the first part of this work. This solution turns out to be “ binary”: except for at most one piv ot-use r , users in each c ell must be divided into tw o groups , the nearest users modulating s ubcarriers only in the reu sed ban d and the fart h est us ers mod ulating subca rriers o nly in the protected b and. An algo rithm that determines the optimal values o f u sers’ reso urce alloca tion parameters is also proposed in the first part. It is worth noting that this optimal allocation a lgorithm is still compu tationally dema nding, espec ially when the number of users in each cell is lar ge. One of the computationa lly costliest op erations in volved in the op timal allocation is the determination o f the piv ot-use r in each cell. In the presen t paper , we propose a distributed s implified r e source allocation a lgorithm wit h low co mputational co mplexity , and we discus s its performanc e as co mpared to the optimal resource allocation a lgorithm of Part I. This simplified algorithm assumes a piv ot-distance that is fixed in advance prior to the resou rce allocation process . Of c ourse, this pred efined piv ot-distanc e sh ould be relevantly chos en. For that sake, we s how that wh en the fixed piv ot-distance of the simplified algorithm is chos en according to a c ertain asymptotic analysis of the op timal a llocation scheme, the performance of the s implified algorithm is close to the DRAFT November 21, 2021 3 optimal one , provided that the number of users in the network is large enou gh. Therefore, following the approach of [2], we propos e to characterize the limi t of the total trans mit po wer which results from the optimal resource allocation p olicy as the number of us ers in ea ch c ell tend s to infinity . Several existing works on resource allocation resorted to this kind of asymptotic ana lysis, principa lly in orde r to get tractable formulations of the optimization problem that can be solved a nalytically . For example, the asymptotic analys is was used in [3] an d [4] in the c ontext of downlink and uplink single cell OFDMA systems respectively , as well as in [5] in the co ntext of Code Division Multiple Access (CDMA) systems with fading chann els. Another application o f the asymptotic analys is ca n be found in [6]. The authors of the cited work address ed the optimization of the sum rate pe rformance in a multicell network. In this context, the authors proposed a decentralized algorithm that maximizes an upp er -bo und on the network sum rate. Interestingly , this uppe r -bou nd is proved to be tight in the a symptotic regime wh en the numbe r of use rs per cell is a llo wed to grow to infin ity . Ho w ev e r , the propose d algorithm does not g uaranty fairness among the different us ers. In this pap er , we use the a symptotic analys is in orde r to obtain a compact form of the (asymp totic) power transmitted by the n etwork for the optimal resource allocation algorithm, and we use this result to propos e relev a nt values of the fixed piv ot-distance asso ciated with the s implified allocation algorithm. W e prove in particular that whe n this fixed p i vot-distance is chos en equa l to the asy mptotic optimal piv ot-distance, then the power transmitted when using the p roposed s implified res ource allocation is asymptotically equiv a lent to the minimum power associated with the optimal algorithm. This limiting expression no longe r depe nds on the particular network con figuration, but on an as ymptotic, or “a ver- age”, state of the netw o rk. More precisely , the a symptotic trans mit power depe nds on t h e average rate requirement a nd on the density of users in e ach cell. It also de pends on the value α of the fr e quency reuse factor . As a byprod uct of o ur as ymptotic analysis , we are therefore a ble to determine a n op timal value of the latter reuse factor . This optimal value is defined as the value of α which minimizes the asymptotic power . The rest of this paper is organized as follo ws. In Se ction II we recall the system model as well as the joint resource a llocation problem. In Section III, we prop ose a n ovel subop timal dis trib uted resource allocation algorithm. Section IV is devoted to the as ymptotic analysis of the performance of this simplified allocation algo rithm as well as the performance o f the optimal reso urce allocation s cheme of Part I when the nu mber of users tend s to infinity . Theorem 1 characterizes the a symptotic be havior o f the optimal joint a llocation s cheme. The results of this theorem are us ed in Sub section IV -D in order to determine relev ant v alues of the fixed pi vot-distances associated wit h the simplified allocation algorithm. Pro v ided Nov ember 21, 2021 DRAFT 4 that t h ese relev a nt values are used, Proposition 2 s tates tha t the simplified a lgorithm is asymptotically optimal. Section VI address es the se lection of the best frequency r e use factor . Fina lly , Se ction VII is dev oted to the numerical illustrations of our results. I I . S Y S T E M M O D E L A N D P R E V I O U S R E S U L T S A. Sy stem Model W e consider a sectorized downlink OFDMA cellular network. W e focus on two neigh boring one- dimensional (linear) cells, say Cell A and Cell B , as illustrated by Figure 1. D enote b y D the radius of Figure 1. T w o-Cell S ystem model each cell. W e de note by K A the number o f users of Cell A a nd by K B the number of u sers of Cell B . T he total numbe r of av ailable su bcarriers in the system is denoted by N . For a gi ven user k ∈ 1 , 2 , . . . , K c in Cell c ( c ∈ { A, B } ), we den ote by x k the distance that sepa rates him/her from BS c , and by N k the set of indices corres ponding to the subca rriers modulated by k . N k is a subs et o f { 0 , 1 , . . . , N − 1 } . The signal recei ved by user k at the n th subcarrier ( n ∈ N k ) and at the m th OFDM block is gi ven by y k ( n, m ) = H k ( n, m ) s k ( n, m ) + w k ( n, m ) , (1) where s k ( n, m ) represents the d ata symbo l transmitted by BS c . Proce ss w k ( n, m ) is an a dditi ve noise which encompa sses the thermal noise and the possible multi c ell interference. Coefficient H k ( n, m ) is the freque ncy response of the cha nnel at the subcarrier n and the OFDM block m . R andom v ariables H k ( n, m ) are as sumed Rayleigh distributed with variance ρ c k = E [ | H k ( n, m ) | 2 ] . Chan nel coefficients DRAFT November 21, 2021 5 are s uppose d to b e p erfectly known at the rec ei ver side, and unknown at the BS side. W e ass ume that ρ k vanishes with the distanc e x k based on a given path loss model. The set of avail able subcarriers is partitioned into three su bsets: I c ontaining the reuse d s ubcarriers sha red by the two cells; P A and P B containing the protec ted subc arriers only use d by u sers in Cell A an d B respec ti vely . The reuse factor α is defined as the ratio between the number of reused sub carriers and the total numbe r of sub carriers: α = card ( I ) N so that I co ntains αN subcarriers. If us er k modu lates a subc arrier n ∈ I , the add iti ve n oise c ontains both thermal noise o f v arianc e σ 2 and interf e rence. Therefore, the v ariance σ 2 k of this noise-plus-interference process dep ends o n k and coincides with σ 2 k = E h | ˜ H k ( n, m ) | 2 i Q B 1 + σ 2 , whe re ˜ H k ( n, m ) represents the ch annel betwe en BS B a nd u ser k of Cell A at fr equency n and OFDM block m , and where Q B 1 = P K B k =1 γ B k , 1 P B k , 1 is the average power trans mitted by BS B in the interference band width I . The rema ining (1 − α ) N su bcarriers are shared by the two cells, Cell A and B , in an orthog onal way . I f user k mod ulates such a subcarrier n ∈ P c , the a dditi ve noise w k ( n, m ) contains only thermal noise. In othe r words, subcarrier n does no t suffer from multicell interference. Then we simply write E [ | w k ( n, m ) | 2 ] = σ 2 . The resource allocation p arameters for u ser k are: P c k , 1 the power transmitted on e ach of the sub carriers of the non protec ted band I allocated to him, γ c k , 1 his share o f I , P c k , 2 the power transmitted on ea ch of the subcarriers of the p rotected band P c allocated to him and γ c k , 2 his share of P c . In other w ords, γ c k , 1 = c ard ( I ∩ N k ) / N γ c k , 2 = c ard ( P c ∩ N k ) / N . As a conseque nce, P K c k =1 γ c k , 1 = α and P K c k =1 γ c k , 2 = 1 − α 2 for each cell c . Moreover , let g k , 1 (resp. g k , 2 ) be the channel G ain to Noise Ra tio (GNR) in band I (resp. P c ), namely g k , 1 = ρ k /σ 2 k (resp. g k , 2 = ρ k /σ 2 ). “Setting a resource allocation for c ell c ” means setting a v alue for pa rameters { γ c k , 1 , γ c k , 2 , P c k , 1 , P c k , 2 } k =1 ...K c . B. Joint Resource Allocation for Cells A and B Assume that e ach user k ha s a rate requirement of R k nats/s/Hz. In the first Part o f this work [1], our aim was to jointly optimize the resource allocation for the two cells which i) allo ws to satisfy a ll tar get rates R k of a ll us ers, and ii) minimizes the power used by the two ba se stations in orde r to achieve thes e rates. For each cell c ∈ { A, B } , de note by c the adjac ent cell ( A = B and B = A ). The e r go dic capacity assoc iated with a user k in Cell c is gi ven by C k = γ c k , 1 E log 1 + g k , 1 ( Q ¯ c 1 ) P c k , 1 Z + γ c k , 2 E log 1 + g k , 2 P c k , 2 Z , (2) Nov ember 21, 2021 DRAFT 6 where Z is a sta ndard expon entially distrib uted rando m variable, an d where coefficient g k , 1 ( Q ¯ c 1 ) is given by g k , 1 ( Q ¯ c 1 ) = ρ k E h | ˜ H k ( n, m ) | 2 i Q ¯ c 1 + σ 2 , (3) where ˜ H k ( n, m ) represe nts the chan nel between BS ¯ c and user k of Cell c at frequency n an d OFDM block m . Co ef fi cient g k , 1 ( Q ¯ c 1 ) represents the signa l to interference plus noise ratio in the interf e rence band I . W e a ssume that use rs a re numbe red from the neares t to the BS to the farthest. As in [1], the following problem wi ll be referr e d to as the joint resource alloca tion problem for Cells A and B : Minimize the total power spen t by b oth base stations Q ( K ) T = X c = A,B K c X k =1 ( γ c k , 1 P c k , 1 + γ c k , 2 P c k , 2 ) with respe ct to { γ c k , 1 , γ c k , 2 , P c k , 1 , P c k , 2 } c = A,B k =1 ...K c under the following co nstraint that all us ers’ rate requirements R k are satisfied i.e. , for eac h us er k in any ce ll c , R k ≤ C k . The solution to this problem ha s been determined in the first part of this work [1]. As a no ticeable point, the resu lts of [1] indicate the existence in eac h cell of a pi vot- user that sepa rates tw o groups o f use rs: the “protected ” users and the “non protec ted” use rs. The follo wing propos ition s tates this b inary property of the solution. Proposition 1 ([1]) . An y global so lution to the joint r e source allocation pr oblem is “binary” i.e., there exists a u ser L c in each C ell c such that γ k , 2 = 0 for closest us ers k < L c , and γ k , 1 = 0 for farthest users k > L c . In the sequ el, we denote by d c, ( K ) the position of the piv ot-use r L c in C ell c i.e., d c, ( K ) = x L c . A resource allocation algorithm is also prop osed in [1]. This algorithm turns ou t to have a high c omputational complexity an d the determination of the optimal value o f the piv ot-distanc e d c, ( K ) turns out to be on e of the c ostliest operations in volved in this algorithm. This is why we prop ose in the foll wing section of the present paper a s uboptimal simplified a llocation algorithm that ass umes a prede fined piv o t-distance. I I I . P R A C T I C A L R E S O U R C E A L L O C A T I O N A L G O R I T H M A. Motivations an d Main idea Proposition 1 provides the ge neral form of the op timal resource allocation, s howing in particular the existence of piv o t-users L A , L B in both C ells A , B , separating the users who modulate in ban d I from the users who mod ulate in ba nds P A and P B . As a matter of fact, the determination of p i vot-users L A , L B is one of the costliest ope rations of this optimal alloca tion (se e [1] for a detailed compu tational complexity analysis). Thus , it would be con venie nt to propose an alloca tion procedure for which the piv ot-position would be fixed in advance to a constant rather than systematica lly computed/optimized. W e propos e a DRAFT November 21, 2021 7 simplified resou rce allocation algorithm based on this idea. Furthermore, we prove that when the value of the fixed piv ot-distanc es is relev a ntly c hosen, the prop osed a lgorithm is a symptotically optimal a s the number of use rs inc reases. In other words, the total po wer sp ent by the network for large K when us ing our su boptimal algorithm does not exceed the minimum power that w ou ld have been sp ent by using the optimal resource allocation. Th e proposed a lgorithm is based on the followi n g idea. Recall the defin ition of d A, ( K ) and d B , ( K ) as the resp ecti ve position of the optimal pi vot-users L A and L B defined by Proposition 1. As the optimal pi vot-positions d A, ( K ) and d B , ( K ) are dif fic ult to c ompute explicitly and depen d on the particular ra tes and us ers’ positions, we prop ose to replace d A, ( K ) and d B , ( K ) with predefined v a lues d A subopt and d B subopt fixed before the res ource a llocation process. In ou r suboptimal algorithm, all use rs in Ce ll c who se distance to the BS is les s tha n d c subopt modulate in the interference band I . Use rs farther than d c subopt modulate in the protected band P c . Of c ourse, we still need to determine the pivot- dis tances d A subopt and d B subopt . A procedure that permits the relevant se lection of d A subopt , d B subopt is given in Section IV -C . B. Detailed Des cription Assume that the values of d A subopt and d B subopt have been fixed be forehand prior to the res ource allocation process . For each Cell c , de fine by K c I the subs et of { 1 , . . . K c } corresponding to the users whose distan ce to BS c is les s than d c subopt . Define by K c P the set of u sers whose distance to BS c is lar ger than d c subopt . 1) R esource allocation for pr otected users: Focus for instance on Cell A . For eac h k ∈ K A P , we arbitrarily set γ A k , 1 = P A k , 1 = 0 i.e. , user k is forced to mo dulate in the protec ted band P A only . For such users , the remaining resou rce a llocation parameters γ A k , 2 , P A k , 2 are obtained by solving the following classical single c ell problem w .r .t. ( γ A k , 2 , P A k , 2 ) k ∈ K A P : “Minimize the tr a nsmitted power P k ∈ K A P γ A k , 2 P A k , 2 under rate c onstraint R k < C k for each k ∈ K A P ”. The a bove problem is a simple p articular c ase of the single cell problem addresse d in [1]. Defi ne the functions f ( x ) = E [log(1+ xZ )] E [ Z 1+ xZ ] − x an d C ( x ) = E [log(1 + f − 1 ( x ) Z )] on R + . The s olution is gi ven by P A k , 2 = g − 1 k , 2 f − 1 ( g k , 2 ˜ β 2 ) γ A k , 2 = R k E h log 1 + g k , 2 P A k , 2 Z i , Nov ember 21, 2021 DRAFT 8 where p arameter ˜ β 2 is obtaine d by w riting that constraint P k γ A k , 2 = 1 − α 2 holds or e quiv alently , ˜ β 2 is the unique solution to: X k ∈ K A P R k C ( g k , 2 ˜ β 2 ) = 1 − α 2 . W e proceed similarl y for Cell B . 2) R esource allocation for interfering us ers: W e now focu s o n users k ∈ K c I for each cell c = A, B . For such users , we arbitrarily se t γ c k , 2 = P c k , 2 = 0 i.e . , users in K c I are forced to modulate in the interference band I o nly , for each cell c . Th e rema ining r e source allocation parameters γ A k , 1 , P A k , 1 , γ B k , 1 , P B k , 1 are obtained by solving the foll owing simplified multicell problem. Problem 1. [Multicell] Minimize X c = A,B X k ∈ K c I γ c k , 1 P c k , 1 w .r .t. ( γ A k , 1 , P A k , 1 , γ B k , 1 , P B k , 1 ) k under the following constraints for each cell c ∈ { A, B } : C1 : ∀ c, ∀ k ∈ K c I , R k ≤ C k C2 : ∀ c, X k ∈ K c I γ c k , 1 = α C3 : γ c k , 1 ≥ 0 . Clearly , the above Prob lem can be interpreted as a particular case of the initial resource allocation (Problem 2 in [1]) a ddressed in Section II-B of the present p aper . The main dif ference is that the init ial multicell problem jointly in volves the resource allocation parame ters in three bands I , P A and P B whereas the present problem only optimizes the resource allocation parameters c orresponding to band I , while arbitrarily setting the others to z ero. Therefore, the results of Part I [1], The orem 2 of [1] in particular , can directly be used to determine the global solution to Problem 1. Remark 1 ( F e asibility). Recall that the initial joint r e source allocation Pr o blem (Pr oblem 2 in [1]) descr ibed in Se ction II-B in the present paper was a lways feasible. Intuitively , this was due to the fact that any user was likely to mo dulate in the protected band if n eeded, so that any rate requir ement R k was likely to be satisfied by s imply incr e asing the power in the pr otec ted ban d. In the present cas e, the pr otected band is by definition for bidden to users in K c I . Theoretically speak ing, Problem 1 migh t n ot be feasible due to multicell interference. F ortunately , we will se e this cas e does not happe n, at least for a sufficiently lar ge number of users, if the values of the pivo t-distances d A subopt and d B subopt ar e well chos en. This point will b e discussed in more de tail in S ection V. Define Q c 1 = P k ∈ K c I γ c k , 1 P c k , 1 as the average power t ran smitted by BS c in the interference ban dwidth I . DRAFT November 21, 2021 9 By straightforward a pplication o f Theorem 2, we obtain that for each Cell c and for each user k ∈ K c I , P c k , 1 = g − 1 k , 1 ( Q ¯ c 1 ) f − 1 ( g k , 1 ( Q ¯ c 1 ) ˜ β c 1 ) (4) γ c k , 1 = R k E h log 1 + g k , 1 ( Q ¯ c 1 ) P c k , 1 Z i , (5) where for e ach c = A, B and for a fixed value o f Q ¯ c 1 , pa rameters ( ˜ β c 1 , Q c 1 ) are the unique so lution to the follo wing sy stem of e quations: X k ∈ K c I R k C ( g k , 1 ( Q ¯ c 1 ) ˜ β c 1 ) = α (6) Q c 1 = X k ∈ K c I R k g − 1 k , 1 ( Q ¯ c 1 ) f − 1 ( g k , 1 ( Q ¯ c 1 ) ˜ β c 1 ) C ( g k , 1 ( Q ¯ c 1 ) ˜ β c 1 ) . (7) Note that the first equation is nothing e lse that the constraint C2 : P k γ c k , 1 = α . The secon d eq uation is nothing else tha n the definition Q c 1 = P k ∈ K c I γ c k , 1 P c k , 1 . W e now prove that the system of four equations (6)-(7) for c = A, B admits a unique solution ˜ β A 1 , Q A 1 , ˜ β B 1 , Q B 1 and we provide a simple algorithm allo wing to determine this solution. Focus on a given Cell c a nd con sider any fixed value Q ¯ c 1 . De note by ˜ I c ( Q ¯ c 1 ) the rhs of eq uation (7) where ˜ β c 1 is defined as the unique solution to (6). Since (7) sho uld be satisifed for both c = A and c = B , the follo wing two equations h old Q A 1 = ˜ I A ( Q B 1 ) , Q B 1 = ˜ I B ( Q A 1 ) . The couple ( Q A 1 , Q B 1 ) is therefore clearly a fixed point of the vector- valued function ˜ I ( Q A 1 , Q B 1 ) = ( ˜ I A ( Q B 1 ) , ˜ I B ( Q A 1 )) . ( Q A 1 , Q B 1 ) = ˜ I ( Q A 1 , Q B 1 ) . (8) As a matter of fact, it can be s hown that such a fi xed point of ˜ I is unique. This claim can be proved using the approach p re v iously p roposed by [12 ]. Lemma 1. Function ˜ I is such that the following pr operties hold. 1) P ositivity: ˜ I ( Q A , Q B ) > 0 . 2) Monotonicity: If Q A ≥ Q A ′ , Q B ≥ Q B ′ , then ˜ I ( Q A , Q B ) ≥ ˜ I ( Q A ′ , Q B ′ ) . 3) Scalability: for all t > 1 , t ˜ I ( Q A , Q B ) > ˜ I ( tQ A , tQ B ) . The proof of Le mma 1 uses a r gu ments which are very similar to the proof of Theorem 1 in [11]. It is thus omitted from this paper and provided in [13]. Fu nction ˜ I is then a standard interfer en ce function , Nov ember 21, 2021 DRAFT 10 using the te rminology of [12]. Therefore, as stated in [12], su ch a function ˜ I a dmits at mos t one fixed point. On the other h and, the existence of a fixed po int is ens ured by the fea sibility o f Problem 1 an d b y the fact that (8) ho lds for any globa l solution. In othe r words, if P roblem 1 is feasible, then function ˜ I does admit a fixed point an d this fixed point is unique. Putting all p ieces together , the re exists a u nique solution to (8), which can b e obtained thanks to a simple fi xed p oint algorithm. In practice, resource allocation in band I ca n be a chieved by the follo wing proce dure. Ping-pong algo rithm for interfering users 1) Initialization: Q B 1 = 0 . 2) Cell A: Gi ven the current value of the po we r Q B 1 transmitted by base station B in the interference bandwidth, compute ˜ β A 1 , Q A 1 as the u nique solution to (6)-(7) with c = A . 3) Cell B: Gi ven the current value of Q A 1 , compute ˜ β B 1 , Q B 1 by (6)-( 7 ). 4) Go back to s tep 2 until co n ver g ence. 5) Define resource allocation parameters b y (4)- (5 ). Comments 1) Con vergence of t h e ping-pong a lgorithm. W e stated earlier that Problem 1 is e ither feasible or infeasible, depe nding on the value of ( d A subopt , d B subopt ) . If the latter p roblem is feasible, then function ˜ I wil l heve a unique fixed point due to Lemma 1 and the ping-pong algorithm will conv e r ge to this fixed p oint. If Problem 1 is infeas ible, then function ˜ I will have no fixed p oints a nd the the ping-pong algorithm will d i verge. One of the main pu rposes of Section IV -C is to provide relev ant values of ( d A subopt , d B subopt ) such that co n ver gence of the ping-po ng algorithm h olds for suf ficien tly lar g e number K of users. 2) Note that the only information needed b y Base Station c about Ce ll c is the current value of the power Q c 1 transmitted by Ba se S tation c in the interference band I . This value can i) either be me asured by Base S tation c at eac h iteration o f the ping-pong algo rithm, or ii) it can b e communicated to it by Base Station c over a dedica ted link. In the first ca se, no message passing is requ ired, and in the sec ond case on ly few information is exch anged between the bas e stations. The ping-pong algorithm can thus be implemented in a distri buted fashion. C. Comp le x ity Analysis W e sho we d earlier that allocation for protected users c an be reduced to the determination in e ach ce ll of the v alue of ˜ β c 2 , which is the u nique s olution to the e quation P k ∈ K A P R k C ( g k, 2 ˜ β c 2 ) = 1 − α 2 . W e ar g ued in [1] that solving this kind of equations req uires a computational complexity prop ortional to the numbe r DRAFT November 21, 2021 11 of terms in the lhs of the e quation, which is itself of o rder O ( K ) . Using similar arguments, we can show that each iteration of the ping-pong algorithm for n on protected users can b e performed with a complexity of order O ( K ) . Le t J des ignate the number of iterations nee ded till conv e r ge nce. Th e overall computational complexity of the ping-pong algorithm, and hence of the simplified resource allocation scheme as well, is thu s of the order of O ( J K ) . Our s imulations showed that the ping-pong algorithm con verges relatively qu ickly in most of the ca ses. Indeed, no more than J = 15 iterations w ere n eeded in almost all the simulati o ns settings to reach con ver ge nce within a very reasonable accuracy . The c omplexity of the simplified algorithm is to be comp ared with the computational complexity of the optimal algorithm which was shown in [1] to be of the order of O ( M K log 2 K ) , where M is the number of points inside a certain 2D search grid. I V . A S Y M P T O T I C O P T I M A L I T Y O F T H E S I M P L I FI E D R E S O U R C E A L L O C A T I O N S C H E M E The aim of this sec tion is to ev aluate the pe rformance of the proposed simplified a lgorithm. Th e relev ant pe rformance me tric in the con text of this p aper is the total power that must be transmitted by the base s tations. Since the simplified algorithm ass umes prede fined piv ot-distanc es ( d A subopt , d B subopt ) fixed prior to the resource alloca tion proce ss, the performance of the propo sed algorithm depe nds on the choice of these fixed piv ot-distanc es. One must therefore de termine what relev ant value should be selected for ( d A subopt , d B subopt ) . A p ossible method is ad dressed in this section and co nsists in studying the case where the number of users tends to infinity . A. Main T ools: Asymptotic analysis W e study firs t the performance of the optimal allocation algorithm p roposed in Part I [1] when the number of users in eac h cell tends to infin ity . From the results of this asy mptotic s tudy , we con clude the asymptotic behaviour of the optimal piv ot-distance s d A, ( K ) , d B , ( K ) . It turns out that when the numbe r K of us ers increases , the optimal piv ot-distances as well as the total transmitted power no longer d epend on the particular ce ll configuration, but on an asymptotic state of the network, such as the average rate requirement a nd the density of users in each cell. Thanks to this result, we can n ow c hoose the fixed piv ot-distances asso ciated with the simplified algorithm to be equa l to the asymptotic pi vot-distances. In this case, one c an s how that the performanc e g ap betwee n the simplified and the optimal allocation scheme s vanishes for high numbers o f users. W e introduce n ow the mathematical assump tions a nd tools that we use for d efining the asy mptotic regime. Nov ember 21, 2021 DRAFT 12 1) No tations and Basic Assu mptions: In the sequel, we d enote by B the total b andwidth of the system in Hz. W e consider the asymp totic re gime where the numbe r of users in each cell tend s to infinity . W e denote by r k = B R k the da ta rate requ irement of use r k in n ats/s, and we recall that R k is the data rate requirement of user k in nats/s/Hz . Notice that the total rate P K c k =1 r k which sh ould be d eli vered by B S c tends to infin ity a s we ll. Thus, we nee d to let the bandwidth B grow to infinity in orde r to satisfy the growing data rate requirement. Recalling that K = K A + K B denotes the total number of users in both cells, the asymptotic regime will be characterized by K → ∞ , B → ∞ an d K/B → t where t is a positi ve real number . W e assume on the other hand tha t K c /K ( c ∈ { A, B } ) tends to some positi ve constant as K tends t o infinity . W ithout restricti o ns, this c onstant is as sumed in the s equel to be equal to 1 /2 i.e. , the numbe r of users bec omes equiv alent in ea ch cell. In o rder to simplify the proofs of our results, we assume without restriction that for each k , the rate requirement r k is upper-bounded by a c ertain cons tant r max , r k ≤ r max , where r max can be c hosen as large as nee ded, and that us ers of ea ch cell are loca ted in the interval [ ǫ, D ] whe re ǫ > 0 c an be chos en as small a s ne eded. Recall that x k denotes the pos ition of each user k i.e., the distanc e between the user and the BS. The variance of the channel gain of user k will be writ ten a s ρ k = ρ ( x k ) wh ere ρ ( x ) models the pa th loss. T ypically , function ρ ( x ) h as the form ρ ( x ) = λx − s where λ is a certain g ain and wh ere s is the path-loss co ef fi cient, s ≥ 2 . In the seque l, we denote by g 2 ( x ) = ρ ( x ) σ 2 the received ga in to no ise ratio in the protec ted ban dwidth, for a user at po sition x . This way , g 2 ( x k ) = g k , 2 . Similarly , we define for each user k in ce ll A , g 1 ( x k , Q B 1 ) = g k , 1 ( Q B 1 ) . More ge nerally , g 1 ( x, Q ) den otes the g ain-to-interference-plus-noise ratio in the interference bandwidth at position x when the interfering cell is transmitting with power Q in band I . Functions g 1 ( x, . ) and g 2 ( x ) are assu med to be continuous functions of x . It is w orth noting that for each x , g 2 ( x ) = g 1 ( x, 0) . Finally , recall that coe f fic ient γ c k , 1 (resp. γ c k , 2 ) is defined as the rati o between the part of the interf e rence bandwidth I (resp. protected bandwidth P c ) a nd the total bandwidth. T hus, γ c k , 1 and γ c k , 2 tend to zero as the total bandwidth B tends to infinity for eac h k . 2) S tatistical T ools and Main Ideas o f the Asy mptotic Study: Theorem 2 o f Part I [1] reduce s the determination of the whole set of re source allocation pa rameters in both cells to the determination of ten un known parameters { Q c 1 , β c i , L c , ξ c } c = A,B , i =1 , 2 . Parameter Q c 1 in particular repres ents the power transmitted by Ce ll c in the non protec ted band I . Cons ider no w on e of the two Cells c ∈ { A, B } , and denote by c the secon d (adjac ent) cell. In the s equel, we use the notation Q c, ( K ) 1 (resp. Q c, ( K ) 2 ) instea d of Q c 1 (resp. Q c 2 ) to designate the power trans mitted b y BS c in the non protected ban d I (resp. the protec ted DRAFT November 21, 2021 13 band P c ) when the optimal s olution c haracterized by Proposition 1 is used . Q c, ( K ) 1 = L c X k =1 γ c k , 1 P c k , 1 (9) Q c, ( K ) 2 = K c X k = L c γ c k , 2 P c k , 2 . (10) The n ew notation Q c, ( K ) 1 , Q c, ( K ) 2 is u sed to indicate the depend ency of the results on the number of users K . For the same rea son, parame ters L c , β c 1 , β c 2 , ξ c will be denote d in the se quel by L c, ( K ) , β c, ( K ) 1 , β c, ( K ) 2 , ξ c, ( K ) respectively . Our g oal now is to charac terize the be havior o f the resource allocation s trategy as K, B → ∞ an d, in particular , the behavior of p owers Q c, ( K ) 1 , Q c, ( K ) 2 . By straightforward application of Theorem 2 of Part I, Q c, ( K ) 1 = P L c k =1 γ c k , 1 P c k , 1 can be writ te n as Q c, ( K ) 1 = X k 0 and K A /K → 1 / 2 . Assume that the optimal so lution for the joint r e source allocation pr ob lem (Pr oblem 2 in [1]) is us ed for each K . The total p ower s pent by the ne twork Q ( K ) T = P c = A,B P K c k =1 ( γ c k , 1 P c k , 1 + γ c k , 2 P c k , 2 ) con ve r ges to a constant Q T . The limit Q T has the foll o wing form: Q T = X c = A,B ¯ r c Z d c ǫ F ( x, β c 1 , Q ¯ c 1 , ξ c ) dλ c ( x ) + Z D d c F ( x, β c 2 , 0 , 0) dλ c ( x ) , (18) where for each c = A, B , the following sy stem of e quations in v ariables d c , β c 1 , β c 2 , ξ c is satisfied: ¯ r c Z d c ǫ G ( x, β c 1 , Q ¯ c 1 , ξ c ) dλ c ( x ) = α (19) ¯ r c Z D d c G ( x, β c 2 , 0 , 0) dλ c ( x ) = 1 − α 2 (20) g 1 ( d c , Q ¯ c 1 ) 1 + ξ c F g 1 ( d c , Q ¯ c 1 ) 1 + ξ c β c 1 = g 2 ( d c ) F ( g 2 ( d c ) β c 2 ) (21) ¯ r c Z d c ǫ F ( x, β c 1 , Q ¯ c 1 , ξ c ) dλ c ( x ) = Q c 1 . (22) Nov ember 21, 2021 DRAFT 16 Mor e over , for each c = A, B and for an y arbitrary fixed value ( ˜ Q A 1 , ˜ Q B 1 ) , the system o f equations (19)-(20)-(21)-(22) admits at mos t one solution ( d c , β c 1 , β c 2 , ξ c ) . As a con sequen ce, whe n optimal multicell res ource a llocation is used, the total po we r sp ent by the network con verges to a cons tant which can be ev a luated through the results o f Th eorem 1. This result allows to e valuate the as ymptotic power s pent by the network as a function of the reuse factor α , the av e rage rate requ irement ¯ r and the asymp totic distributi o n of users in e ach cell λ . Now that the asymptotic performance of the optimal allocation s cheme has been studie d, the value of the fixed pi vot-distances d A subopt , d B subopt assoc iated with the simplified allocation algorithm can be rele vantly chosen to be equal in ea ch Ce ll c to the asymp totic piv o t dis tance d c defined by Theorem 1. C. Deter mination of the fix ed p ivot-distances d A subopt , d B subopt for the simplified a llocation scheme W e stated earlier in Sec tion III that the sub optimal algorithm replaces the optimal value d c, ( K ) of the pi vot-distance in each Cell c with a fixed v alue d c subopt . I ntuiti vely , if d A subopt and d B subopt are ch osen such tha t d A, ( K ) ≃ d A subopt and d B , ( K ) ≃ d B subopt for large K , the pe rformance of our algorithm shall be close to the optimal one as K increas es. Therefore, we must determine an asymp totically optimal pair of pi vot-distances ( d A , d B ) . T o that end we propos e the following procedure. Note first by referring to Th eorem 1 that the value of d A , d B can be easily de termined onc e the re le vant values of Q A 1 and Q B 1 have been determined. The remaining task is thus the determination o f the v alue of ( Q A 1 , Q B 1 ) . T o that end, we propose to perform an exhaustiv e se arch on ( Q A 1 , Q B 1 ) . i) For e ach point ( ˜ Q A 1 , ˜ Q B 1 ) on a certain 2D s earch grid, so lve the system (19)-(20)-(21)-(22) introduced by Th eorem 1 for both c = A, B . Theorem 1 states that this system a dmits at mo st one solution for any arbitrary fixed v a lue ( ˜ Q A 1 , ˜ Q B 1 ) . If the inv es tigated point ( ˜ Q A 1 , ˜ Q B 1 ) o f the grid is su ch that the system (19)- (20)-(21)-(22) does admit a solution, we ca n obtain this solution de noted b y d c ( ˜ Q A 1 , ˜ Q B 1 ) , β c 1 ( ˜ Q A 1 , ˜ Q B 1 ) , β c 2 ( ˜ Q A 1 , ˜ Q B 1 ) , ξ c ( ˜ Q A 1 , ˜ Q B 1 ) thanks to a s imple procedure inspired b y the single-cell procedure proposed in Part I [1] for finite number of us ers: • Solve the system (19)-(20 )-(21)-(22 ′ ) formed by replacing the eq uality in equation (22) of sys- tem (19)-(20)-(21)-(22) by the following inequality ¯ r c Z d c ǫ F ( x, β c 1 , Q ¯ c 1 , ξ c ) dλ c ( x ) ≤ ˜ Q c 1 . (22 ′ ) The existence and the uniquene ss of the so lution to this new sy stem for an arbitrary ( ˜ Q A 1 , ˜ Q B 1 ) ∈ R 2 + can be proved by extending, t o the cas e of infinite number of users, Pr oposition 1 which was provided in [1] for the c ase of fi nite number of us ers. DRAFT November 21, 2021 17 • If the res ulting power ¯ r c R d c ǫ F ( x, β c 1 , Q ¯ c 1 , ξ c ) dλ c ( x ) transmitted in the interference band P c is equal to ˜ Q c 1 , then the resu lting value of d c ( ˜ Q A 1 , ˜ Q B 1 ) coincide s with the unique solution to sys tem (19)- (20)-(21)-(22) . Onc e again, this claim can be proved b y extending Proposition 1 of [1] to the ca se of infinite number of us ers. • If the power ¯ r c R d c ǫ F ( x, β c 1 , Q ¯ c 1 , ξ c ) dλ c ( x ) is less than ˜ Q c 1 , then d c ( ˜ Q A 1 , ˜ Q B 1 ) is clea rly no t a solution to sy stem (19)-(20)-(21)-(22) , as equa lity (22) does not hold. In this ca se, it can be easily s hown that system (19)-(20)-( 2 1)-(22) has no solution. The p oint ( ˜ Q A 1 , ˜ Q B 1 ) is thus e liminated. ii) Compute the total po wer Q T ( ˜ Q A 1 , ˜ Q B 1 ) = X c = A,B X k γ c k , 1 P c k , 1 + γ c k , 2 P c k , 2 that would be transmitted if the values of Q A 1 and Q B 1 introduced by The orem 1 were respectiv ely equ al to ˜ Q B 1 and ˜ Q A 1 . iii) The final value of d A , d B is given by d A ( Q A 1 , Q B 1 ) , d B ( Q A 1 , Q B 1 ) , the value as sociated with ( Q A 1 , Q B 1 ) the ar gument of the minimum power transmitted by the network: ( Q A 1 , Q B 1 ) = arg min ( ˜ Q A 1 , ˜ Q B 1 ) Q T ( ˜ Q A 1 , ˜ Q B 1 ) . i v ) Finally , we choo se d A subopt = d A and d B subopt = d B . Note that the s ame procedure provides as a b yproduct the limit Q T of the total transmit p ower as Q T = Q T ( Q A 1 , Q B 1 ) . Comments It is clear from our previous disc ussion that the abov e procedure for computing ( d A , d B ) can be done in advance prior to reso urce allocation. This is essen tially due to the fact that the a symptotically optimal pair of piv ot-distances ( d A , d B ) doe s not d epend o n the p articular c ell co nfiguration, but o n an asymptotic or “ av e rage” state of the network. The proc edure can b e run for instance before base s tations are brought into ope ration. It can also be d one once in a while as the as ymptotic distrib u tion of the users and the av e rage rate requirement ¯ r can b e sub ject to change s: b ut the se chang es occur after long periods o f time. Therefore, the numbe r of operations nee ded for the comp utation of ( d A , d B ) is n ot a major co ncern becaus e it does not af fect the computational complexity of resource allocation. Nov ember 21, 2021 DRAFT 18 D. Asy mptotic P erformance of the Simplified Algorithm Denote by Q ( K ) subopt the total power transmitted when o ur simplified allocation algo rithm is applied. Recall tha t Q ( K ) T designates the total power transmitted by the ne twork when the o ptimal reso urce allocation associated wit h the joint resource a llocation problem (Problem 2 of [1]) is used. Proposition 2. The following equality holds: lim K →∞ Q ( K ) subopt = lim K →∞ Q ( K ) T . Proposition 2 can be proved using the same arguments as the ones used in Ap pendix A. The detailed proof is omitted. The above Proposition states tha t the propos ed s uboptimal algo rithm tends to be o ptimal w . r .t. the joint reso urce allocation p roblem, as the n umber o f users increas es. The refore, our algorithm is at the same time much simpler than the initial optimal resource allocation algorithm of [1], and ha s similar p erformance at leas t for a suf ficien t number of us ers in each c ell. Sec tion VII will furthermore indicate that e ven for a mod erate number of us ers, ou r suboptimal algorithm is actua lly ne arly o ptimal. V . O N T H E C O N V E R G E N C E O F T H E S I M P L I FI E D A L L O C AT I O N A L G O R I T H M As s tated be fore, the s implified algorithm performs the re source alloca tion in each Ce ll c indepe ndently for the protec ted K c P and the n on protected K c I users, whic h are sep arated by the prede fined piv ot-distance d c subopt . Resource allocation for the n on protected use rs is d one by the iterati ve an d d istrib uted ping-pong algorithm described in Section III. It was stated in Section III that the con vergence o f the ping-pong algorithm is ensured by the feas ibility of the the p roblem of resource allocation for the n on protec ted users { K A I , K B I } (Problem 1). If Problem 1 is feasible, the ping-pong algorithm con ver ge s. If Problem 1 is infeasible, the ping-pong algorithm diver ges . It was also stated in Sec tion III that Problem 1 may n ot be fea sible if arbitrary values of the pi vot-distances d A subopt and d B subopt are us ed. Fortunately , feasibility of the latter p roblem will not be an issue if the v a lue of d A subopt and d B subopt are relevantly chosen a s described by the procedure introduced in Section IV -D. Indeed, it c an be s hown in this case that at least for large K , the set K c I will c ontain the users wh o would anyway have b een restricted to the interference band I if the optimal resource all o cation o f Part I [1] was u sed. More precisely , it can be shown that there exists a v alue K 0 of K beyond wh ich Problem 1 is always feasible. T he proof o f this statement is provided in [13 ]. It is b ased on sensiti v ity an alysis of perturbed o ptimization problems [14]. It is worth mentioning that in our simulations, Prob lem 1 was feasible in almost all the s ettings of the sys tem, even for a moderate number of use rs per cell as small as 25. DRAFT November 21, 2021 19 V I . S E L E C T I O N O F T H E B E S T R E U S E F AC T O R The se lection of a rele vant v a lue α a llo wing to optimize the network performance is of crucial importance as f a r as ce llular network design is c oncerned . The defin ition of an optimal reus e factor requires howev e r some c are. Th e first intuition would co nsist in se arching for the v a lue of α which minimizes the total power Q ( K ) T = Q ( K ) T ( α ) transmitted by the network, for a finite number of users K . Howe ver , Q ( K ) T ( α ) depend s on the particular target rates and the particular positions of use rs. In p ractice, the reuse f a ctor should be fixed prior to the resource allocation p rocess and its v alue should be independen t of the particular cells co nfigurations. A solution adopted by sev e ral works in the l iterature c onsists i n performing sy stem lev el s imulations and choosing the corres ponding value of α that resu lts in the best av e rage pe rformance. In this context, we c ite [8], [9] an d [10 ] w ithout being exclusive. In this pa per , we are interested in providing analytical me thods tha t permit to cho ose a relev a nt value of the reuse factor . This is why we propose to select the v alue α opt of the reuse f a ctor as α opt = arg m in α lim K →∞ Q ( K ) T ( α ) . Recall that the limiting power Q T = lim K →∞ Q ( K ) T is given by equation (18). In practice , we propos e to compute the value o f Q T = Q T ( α ) for several values of α on a grid in the interval [0 , 1] . For each value of α on the gri d , Q T ( α ) ca n be obtained us ing the procedure presen ted in s ubsection IV - C. Note a lso that complexity issue s are o f few impo rtance, as the optimization is d one prior to the resource allocation process . It does not af fect t he c omplexity o f the g lobal reso urce allocation procedure. W e s hall see in Section VII that s ignificant gains a re ob tained when us ing the o ptimized value of the reuse factor instead of an arbitr a ry value. V I I . S I M U L A T I O N S W e first begin by presenting the technica l parameters of the system mode l. In our simulations, we considered a Free Sp ace Loss mode l (FSL) characterized by a pa th loss expon ent s = 2 as well as the so-called Okumura-Hata (O-H) mo del for open areas [15] with a path loss expone nt s = 3 . Th e carrier frequency is f 0 = 2 . 4 GH z . At this frequen cy , p ath loss in dB is given by ρ dB ( x ) = 20 log 10 ( x ) + 100 . 04 in the case wh ere s = 2 , wh ere x is the distance in kilometers b etween the BS a nd the user . In the cas e s = 3 , ρ dB ( x ) = 30 log 10 ( x ) + 97 . 52 . The signal band width B is equal to 5 MHz and the thermal n oise power spe ctral de nsity is e qual to N 0 = − 170 dBm/Hz. Each cell has a ra dius D = 500 m. Asymptotically optimal pivot-distance and frequency reuse factor: W e first app ly the results of of Sections IV an d VI in o rder to obtain the v alues of t h e asymptotica lly op timal piv ot-distances d A , d B Nov ember 21, 2021 DRAFT 20 0 2 4 6 8 10 12 14 0.3 0.5 0.7 0.9 1 r t (Mbps) α opt D=500m s=2 s=3 Figure 2. Optimal reuse factor vs. sum rate 0 2 4 6 8 10 12 14 16 0.5 0.6 0.7 0.8 0.9 1 r t (Mbps) d opt /D D=500m s=2 s=3 Figure 3. Optimal pi vot-distance vs. sum rate and the a symptotically optimal reus e factor α opt . Th ese values a re nec essary for the implementation of the simplified allocation algorithm propose d in Section III. Ea ch of the tw o cells is assu med to have in the asymptotic regime the s ame uniform distrib ution o f users: λ A = λ B = λ where dλ ( x ) = dx/D . The average rate requ irement in each cell is assume d to be the same, too: ¯ r A = ¯ r B = ¯ r , where ¯ r c is defined in Subse ction IV -A2 as the av erag e data rate in Cell c measu red in bits/sec/Hz. In this c ase, the optimal piv ot-distance is the same in each cell i.e., d A = d B . Define d opt = d A = d B . The value of d opt and α opt was obtained using the me thod dep icted by S ubsection IV -C a nd Section VI re spectively . Denote by r t the total data rate of all the users of a se ctor measured in bits/sec ( r t = ¯ r ∗ B ). Figu re 2 and Figure 3 plot respec ti vely α opt and the n ormalized pi vot-distance d opt /D as functions of the total rate r t for two v a lues of the path loss expone nt: s = 2 and s = 3 . Note from Figure 2 that α opt and d opt are both dec reasing func tions of r t . This res ult is expected, giv e n that higher values of r t will lead to higher transmit p owers and c onseque ntly to higher lev e ls of interference. Mo re users will ne ed thus to be “ protected” from the high er interference. F or that p urpose, the pi vot-position must be clos er to the base station and a lar ger p art of the available b andwidth must be r eserved for the p rotected band s P A and P B . Note als o that, in the case s = 3 , “less protection” is nee ded than in the case where s = 2 . In other words, d opt ( s = 3) > d opt ( s = 2) a nd α opt ( s = 3) > α opt ( s = 2) . Th is obse rv a tion can be explained by the fact that, when the path los s exp onent is high er , the interference produ ced by the adjace nt base station will undergo more fading tha n in the ca se w hen the p ath loss exponent is lo we r . Simplified r e source allocation: In Section III, we propo sed a sub optimal allocation algorithm cha rac- terized by its red uced compu tational complexity compared to the optimal allocation algo rithm depicted in [1]. Th is algorithm a ssumes fixed piv ot-distance s d A subopt , d B subopt . Here, w e study the pe rformance of this algorithm whe n d A subopt and d B subopt are c hosen ac cording to the proced ure provided in Section IV -C DRAFT November 21, 2021 21 i.e., d A subopt = d opt and d B subopt = d opt , where d opt is the as ymptotically op timal piv ot-distance defin ed earlier in this section. In order to study the performance of this a lgorithm, we need to compare, for a lar g e nu mber of sys tem settings, Q ( K ) subopt the total trans mit power that mus t be spe nt when applying the simplified algorithm, with Q ( K ) T the total transmit power that must b e spen t when the optimal reso urce allocation scheme of P a rt I [ 1 ] is applied. The res ults must then be averaged i n order to obtain performance measureme nts that are indepe ndent of the p articular system s etting. W e c onsider therefore that users in each cell are randomly distrib uted an d that the distance separating each user fr o m the base station is a random variable with a un iform d istrib ution on the interval [0 , D ] . On the othe r hand, we as sume without restriction that all u sers hav e the same tar get rate, and that the number of u sers is the same for the two ce lls K A = K B . Define x as the vector containing the positions of all the users in the sys tem i.e., x = ( x 1 , x 2 , . . . , x K c ) c = A,B . Rec all tha t ∀ k , x k is a rando m variable with a u niform distribution on [0 , D ] . For ea ch rea lization of x , define Q ( K ) T ( x , α ) as the total transmit p ower that results from applying the op timal joint res ource allocation sche me of Part I with the value of the re use factor fixed to α . Define Q ( K ) T ( x ) = min α Q ( K ) T ( x , α ) . In the same way , deno te b y Q ( K ) subopt ( x ) the total transmit power that results fr o m applying the simplified resource allocation scheme of Se ction III with the value of the reuse factor fixed to α opt defined in Section VI. For each rea lization of the rand om v e ctor x , the values of Q ( K ) T ( x ) an d Q ( K ) subopt ( x ) were calculated an d then a veraged to obtain E x [ Q ( K ) T ( x )] an d E x [ Q ( K ) subopt ( x )] respectively . W e plot in Figure 4 the v alues of E x [ Q ( K ) T ( x )] and E x [ Q ( K ) subopt ( x )] for a range o f v alues 4 6 8 10 12 14 16 10 1 10 2 10 3 r t (Mbps) Total Transmit Power (mW) s=2, D=500m asymptotic optimal (K A =K B =50) simplified (K A =K B =50) simplified (K A =K B =25) Figure 4. Optimal and suboptimal transmit power vs. sum r ate Figure 5. T ransmit po wer vs. the pi vot-distance d for t he simplified allocation scheme ( r t = 10 M bps , K c = 50 ) of the sum rate r t measured in bits/sec ( r t = P K c k =1 R k B ) in two cases: K c = 25 a nd K c = 50 . The error bars in the fi gure repres ents the variance of the random variable Q ( K ) subopt ( x ) in the c ase K c = 50 . In the s ame figure, the c orresponding values of the a symptotic transmit p ower Q T defined by Theorem 1 Nov ember 21, 2021 DRAFT 22 are also p lotted. This figu re s hows that, e ven for a reaso nable numbe r of users equal to 25 in each cell, the trans mit power need ed when we apply the su boptimal algorithm is very close to the power needed when we a pply the optimal re source allocation sc heme. The ga p be tween the two powers is of c ourse ev e n smaller for K c = 50 . This result v alidates Propo sition 2 which states that our proposed sub optimal resource allocation sche me is asymptotically o ptimal. Figu re 5 is dedicated to illustrate the sen siti vity of the simplified a llocation scheme with respect to the piv ot-distance d subopt in the case K c = 50 . F or that sake, the figure plots the t o tal tr ansmit po wer resulting from applying the simplified sc heme as a function of d subopt . The minimum in the figure corresp onds to the asymptotically optimal pi vot distance d subopt = d opt . W e n ote that using v alues dif ferent from d opt increases the su boptimality of the simplified scheme . Let u s go ba ck to Figure 4. The latter figure shows that over the range of the co nsidered values of the total data rate r t , the total trans mit power E x [ Q ( K ) T ( x )] for K c = 50 is practically equal to the asymptotic power Q T . This res ult s uggests that, for a number of users equa l to 50 in e ach ce ll, the system is already in its as ymptotic regime. In order to validate the latter a f fi rmation, one still needs to in vestigate the value of the mean squa re error ( Q ( K ) T − Q T ) 2 as well. This is done by Figure 6 which plots E x ( Q ( K ) T ( x ) − Q T ) 2 Q 2 T , the mean s quare error normalized b y Q 2 T . 10 15 20 25 30 35 40 45 50 0 2 4 6 8 10 12 K A =K B E[(Q T (K) −Q T ) 2 ]/Q T 2 (%) s=2, D=500, r t =5 Mbps Figure 6. E x ( Q ( K ) T ( x ) − Q T ) 2 Q 2 T vs. number of users per cell V I I I . C O N C L U S I O N S In this pair o f pape rs, the res ource allocation problem for sectorized downlink OF DMA sys tems has been studied in the context of a partial reuse factor α ∈ [0 , 1] . In the first part of this work, the gene ral solution to the (noncon vex) o ptimization problem h as be en provided. It has bee n proved tha t the solution admits a simple form and tha t the initial tedious p roblem reduc es to the identification of a limited n umber DRAFT November 21, 2021 23 of parame ters. As a noticeable property , it has b een proved that t he optimal res ource allocation policy is “binary”: there exists a pi vot-distance to the BS s uch that users who are farther than this distanc e should only mo dulate protected s ubcarriers, while c losest us ers should o nly mod ulate reused s ubcarriers. A resource allocation a lgorithm has b een also proposed. In the second pa rt, we propos ed a suboptimal resource allocation algorithm wh ich av oids the costly search for parameters s uch as the optimal piv ot-distance. In the propo sed proced ure, the optimal p i vot- distance is simply replaced by a fixed value. In o rder to provide a metho d to relevantly s elect this fixed pi vot-distance, the asymptotic behavior of the optimal resource a llocation has bee n studied as the number of users tends to infinity . In the case where the fixed pi vot-distance asso ciated with the simplified algorithm is ch osen to be e qual to the asymptotically op timal pi vot-distance, it has be en s hown tha t ou r simplified res ource allocation algorithm is a symptotically equivalent to the optimal on e as the number of u sers increases. Simulations prov e d the rele vancy of our algorithm ev e n for a small number of use rs. Using the results of the asymptotic study , the optimal value of the reuse factor has been charac terized. It is defi ned as the v alue of α w hich minimizes the a symptotic value of the minimum transmit power . Our simulations proved that substantial improvements in terms of spectral efficiency can be expected when using the rele vant value o f the reuse f ac tor . A P P E N D I X A P R O O F O F T H E O R E M 1 Theorem 1 cha racterizes the asymptotic behaviour of the minimal transmit power resulting from applying the optimal resource a llocation when the number of u sers K tends to infin ity . It is thus useful at this point to recall the theorem gi ven in the first part of this work which characterize s the optimal allocation for finite values of K . Defi ne the function F ( x ) = E h Z 1+ f − 1 ( x ) Z i . For each cell c = A, B a nd for ea ch l = 1 . . . K c , define by a c l and b c l the un ique positiv e numbers s uch that P l k =1 R k C ( g k, 1 a c l ) = α and P K c k = l +1 R k C ( g k, 2 b c l ) = 1 − α 2 , with a c 0 = b c K c = 0 by conv en tion. Theorem 2 ([1]) . (A) A ny globa l solution to the joint resour c e allocation pr oblem ha s the following form. F or ea ch C ell c , ther e exists an inte ger L c ∈ { 1 , . . . , K c } , a nd there exist four positive numbers β c 1 , β c 2 , ξ c , Q ¯ c 1 such that 1) F or each k < L c , P c k , 1 = g k , 1 ( Q ¯ c 1 ) − 1 f − 1 g k , 1 ( Q ¯ c 1 ) 1 + ξ c β c 1 P c k , 2 = 0 γ c k , 1 = R k E h log 1 + g k , 1 ( Q ¯ c 1 ) P c k , 1 Z i γ c k , 2 = 0 (23) Nov ember 21, 2021 DRAFT 24 2) F or each k > L c , P c k , 1 = 0 P c k , 2 = g − 1 k , 2 f − 1 ( g k , 2 β c 2 ) γ c k , 1 = 0 γ c k , 2 = R k E h log 1 + g k , 2 P c k , 2 Z i (24) 3) F or k = L c P c k , 1 = g k , 1 ( Q ¯ c 1 ) − 1 f − 1 g k , 1 ( Q ¯ c 1 ) 1 + ξ c β 1 P c k , 2 = g − 1 k , 2 f − 1 ( g k , 2 β c 2 ) γ c k , 1 = α − k − 1 X l =1 γ c l, 1 γ c k , 2 = 1 − α 2 − K c X l = k +1 γ c l, 2 . (25) (B) F or each c = A, B , the system S c ( Q A 1 , Q B 1 ) formed by the following four equations is satisfied. L c = min l = 1 . . . K c g l, 1 ( Q ¯ c 1 ) 1 + ξ c F g l, 1 ( Q ¯ c 1 ) 1 + ξ c a l ≤ g l, 2 F ( g l, 2 b l ) (26) g L c , 1 ( Q ¯ c 1 ) 1 + ξ c F g L c , 1 ( Q ¯ c 1 ) 1 + ξ c β c 1 = g L c , 2 F ( g L c , 2 β c 2 ) (27) γ c L c , 1 C g L c , 1 ( Q ¯ c 1 ) 1 + ξ c β c 1 + γ c L c , 2 C ( g L, 2 β c 2 ) = R L c (28) L c X k γ c k , 1 P c k , 1 = Q c 1 , (29) where the values of γ c k , 1 and P c k , 1 in (29) ar e the functions o f ( β c 1 , β c 2 , ξ c ) defined by e quation (23 ). (C) Furthermore, for e ach c = A, B and for any arbitrary values ˜ Q A 1 and ˜ Q B 1 , the system of equations S c ( ˜ Q A 1 , ˜ Q B 1 ) admits at most one solution ( L c , β c 1 , β c 2 , ξ c ) . In subsection IV -A2, we obtained that for eac h ce ll c = A, B , Q c, ( K ) 1 = K c B Z Z ∆ c, ( K ) 1 r F ( x, β c, ( K ) 1 , Q ¯ c, ( K ) 1 , ξ c, ( K ) ) dν c, ( K ) ( r , x ) + o K (1) (30) Q c, ( K ) 2 = K c B Z Z ∆ c, ( K ) 2 r F ( x, β c, ( K ) 2 , 0 , 0) dν c, ( K ) ( r , x ) + o K (1) (31) where ∆ c, ( K ) 1 = [0 , ρ ] × [ ǫ, d c, ( K ) ] and ∆ c, ( K ) 2 = [0 , ρ ] × [ d c, ( K ) , D ] and where d c, ( K ) is the pi vot- distance i.e. , the p osition o f u ser L c, ( K ) . Our aim is to prove that Q ( K ) T = P c Q c, ( K ) 1 + Q c, ( K ) 2 con verges as K → ∞ , an d to characterize the limit. For each cell c ∈ { A, B } , seque nce d c, ( K ) is bounde d by definition ( d c, ( K ) ∈ [0 , D ] ). Cons ider a sub sequen ce φ K such that ( d A, ( φ K ) , d B , ( φ K ) ) con verges to a certain limit, say ( d A , d B ) . W e prove tha t in this c ase, a ll quantities Q c, ( φ K ) 1 , Q c, ( φ K ) 2 , β c, ( φ K ) 1 , β c, ( φ K ) 2 , ξ c, ( φ K ) con verge to some values Q c 1 , Q c 2 , β c 1 , β c 2 , ξ c which we shall chara cterize. Focus for instanc e on sequen ce β c, ( φ K ) 2 . Recalling that γ c L c, ( K ) , 2 tends to zero as K → ∞ ( γ c L c, ( K ) , 2 = o K (1) ) and rep lacing DRAFT November 21, 2021 25 each γ c k , 2 with expression (23) γ c k , 2 = R k /C ( g c k , 2 β c, ( K ) 2 ) , we o btain immediately 1 B X k >L c, ( K ) r k G ( x, β c, ( K ) 2 , 0 , 0) + o K (1) = 1 − α 2 , (32) where we defined G ( x, β , Q , ξ ) = 1 C g 1 ( x, Q ) 1+ ξ β (33) for each x, β , Q , ξ . In the asymptotic regime, we obtain the foll owing lemma. Lemma 2 . As K → ∞ , seq uence β c, ( φ K ) 2 con ve r ges to the uniqu e s olution β c 2 to the following equa tion: t 2 Z ρ 0 Z D d c r G ( x, β c 2 , 0 , 0) dν c ( r , x ) = 1 − α 2 . (34) Pr oof: Existence and unique ness of the solution to (34) is straightforward since function β 7→ G ( x, β , Q , ξ ) is stri c tly decre asing from ∞ to 0 on R + . W e remark that seque nce β c, ( φ K ) 2 is b ounded i.e. , β c, ( φ K ) 2 ≤ κ for a c ertain co nstant κ . In orde r to prove this claim, a ssume that there exists a subsequ ence β c,φ ζ ( K ) 2 which con verges to infi nity . This hypo thesis implies that the sub sequen ce gi ven by the lhs of (32) for K of the form K = ζ ( K ′ ) con verges to zero as K ′ → ∞ . Th is is in con tradiction with (32) which states that the latter sequen ce con verges to 1 − α 2 . Using s imilar arguments, it can be shown that β c, ( φ K ) 2 is l ower bo unded by a certain ǫ ′ > 0 i.e. , ǫ ′ < β c, ( φ K ) 2 < κ . Denote by β 2 any accumu lation point of β c, ( φ K ) 2 and define β c, ( θ K ) 2 a subseque nce of β c, ( φ K ) 2 ( i.e. , θ K coincides wit h φ ζ ( K ) for a certain function ζ ) which con verges to β 2 . W e p rove that β 2 is given by (34). Define G ( r , x, y ) = r G ( x, y , 0 , 0) . W e sh ow that the dif ference ∆ K = Z ρ 0 Z D d c, ( θ K ) G ( r , x, β c, ( θ K ) 2 ) dν c, ( θ K ) ( r , x ) − Z ρ 0 Z D d c G ( r , x, β c, ( θ K ) 2 ) dν c ( r , x ) tends to zero a s K → ∞ . By the triangular inequality , ∆ K ≤ Z ρ 0 Z D d c, ( θ K ) G ( r , x, β c, ( θ K ) 2 ) dν c, ( θ K ) ( r , x ) − Z ρ 0 Z D d c G ( r , x, β c, ( θ K ) 2 ) dν c, ( θ K ) ( r , x ) + Z ρ 0 Z D d c G ( r , x, β 2 ) dν c, ( θ K ) ( r , x ) − Z ρ 0 Z D d c G ( r , x, β c, ( θ K ) 2 ) dν c ( r , x ) + Z ρ 0 Z D d c G ( r , x, β c, ( θ K ) 2 ) − G ( r, x, β 2 ) dν c, ( θ K ) ( u, x ) . Respec ti vely de note b y ∆ K, 1 , ∆ K, 2 , ∆ K, 3 the first, s econd a nd third terms of the ab ove equation. W e first study ∆ K, 1 . Clearly , function G ( u, x, β ) is bou nded on [0 , ρ ] × [ ǫ, D ] × [ ǫ ′ , κ ] . Denote by ξ a n upper bound. Then, ∆ K, 1 ≤ ξ ν θ K c ( I K ) , where I K = [0 , ρ ] × [ d c, ( θ K ) , d c ] (or I K = [0 , ρ ] × [ d c , d c, ( θ K ) ] if d c < d c, ( θ K ) ). Recall that d c, ( θ K ) con verges to d c by definition, so that ν c ( I K ) = ζ c ([0 , ρ ]) λ c ([ d c, ( θ K ) , d c ]) Nov ember 21, 2021 DRAFT 26 con verges to zero as long a s mea sure λ c has no mass point a t d c . Since ν c, ( θ K ) con verges weakly to ν c , it is straightforward to show that ν c, ( θ K ) ( I K ) , a nd thus ∆ K, 1 , ten d to zero. Now focus on ∆ K, 2 . T he first term R R G ( r , x, β 2 ) dν c, ( θ K ) ( r , x ) which co mposes ∆ K, 2 con verges to R R G ( r , x, β 2 ) dν c ( r , x ) by the weak con ver ge nce o f ν c, ( θ K ) to ν c . The sec ond term R R G ( r , x, β c, ( θ K ) 2 ) dν c ( r , x ) c on verges to the sa me limit by L ebesgu e’ s do minated con vergence Theorem. Thus, ∆ K, 2 tends to zero. In order to prove that ∆ K, 3 tends to zero, we remark that sup ∂ G ( x,r,β ) ∂ β < ∞ , whe re the s upremum is taken w .r .t. ( x, r, β ) ∈ [0 , ρ ] × [ ǫ, D ] × [ ǫ ′ , κ ] . Denote by C the latter supremum. W e easily o btain G ( r , x, β c, ( θ K ) 2 ) − G ( r , x, β 2 ) ≤ C β c, ( θ K ) 2 − β 2 , so that ∆ K, 3 ≤ C β c, ( θ K ) 2 − β 2 ν θ K c ([0 , ρ ] × [ d c , D ]) . S ince ν θ K c is a probability measure, ∆ K, 3 ≤ C β c, ( θ K ) 2 − β 2 . Thus ∆ K, 3 tends to z ero as K tends to infinity . Putting all p ieces together , ∆ K tends to z ero. Using (32), t 2 R ρ 0 R D d c G ( r , x, β c, ( θ K ) 2 ) dν c ( r , x ) c on verges to 1 − α 2 . By continuity arguments, β 2 = lim K β c, ( θ K ) 2 satisfies (34). Thus β c, ( φ K ) 2 is a bounde d sequenc e such that any a ccumulation point is equal to β 2 defined by (34). Thus lim K β c, ( φ K ) 2 = β 2 . Using Lemma 2, we may now ch aracterize the limit o f (31) a s K → ∞ . Using the f ac t that lim K β c, ( φ K ) 2 = β c 2 and lim K d c, ( φ K ) = d c along with some tec hnical a r g uments which are similar to the ones used in the proof of Lemma 2, we obtain Q c, ( φ K ) 2 = K c B Z ρ 0 Z D d c r F ( x, β c 2 , 0 , 0) dν c, ( φ K ) ( r , x ) + o K (1) (35) where β c 2 is the unique s olution to (34). As ν c, ( φ K ) con verges weakly to ν c , Q c, ( φ K ) 2 con verges to Q c 2 = t 2 Z ρ 0 Z D d c r F ( x, β 2 , 0 , 0) dν c ( r , x ) . (36) The s ame app roach can be use d to analyze the behavior of sequenc es Q c, ( φ K ) 1 and β c, ( φ K ) 1 for each c = A, B . After similar d eri vations, we obtain the following result. As K → ∞ , sequen ce ( β A, ( φ K ) 1 , Q A, ( φ K ) 1 , ξ A, ( φ K ) , β B , ( φ K ) 1 , Q B , ( φ K ) 1 , ξ B , ( φ K ) ) con verges to the unique solution ( β A 1 , Q A 1 , ξ A , β B 1 , Q B 1 , ξ B ) to the follo wing system of six equations: Q c 1 = t 2 Z ρ 0 Z d c ǫ r F ( x, β c 1 , Q ¯ c 1 , ξ c ) dν c ( r , x ) t 2 Z ρ 0 Z d c ǫ r G ( x, β c 1 , Q ¯ c 1 , ξ c ) ν c ( r , x ) = α g 1 ( d c , Q ¯ c 1 ) 1 + ξ c F g 1 ( d c , Q ¯ c 1 ) 1 + ξ c β c 1 = g 2 ( d c ) F ( g 2 ( d c ) β c 2 ) c = A, B , (37) where β c 2 and d c are the l imits of β c, ( φ K ) 2 and d c, ( φ K ) respectively . W e discu ss now the existence and the uniquenes s of the solution to the above system of equation. F or that sake, recall the definition o f functions F a nd G gi ven by (12) and (33) respectively . Note that F ( x, β , Q , ξ ) = F ( x, β 1+ ξ , Q , 0) , and tha t DRAFT November 21, 2021 27 G ( x, β , Q , ξ ) = G ( x, β 1+ ξ , Q , 0) . Define ˜ β c 1 = β c 1 1+ ξ c for c ∈ { A, B } . By applying this new notation, Th e first two eq uations of sy stem (37) g i ve place to the following system of four equations: Q c 1 = t 2 Z ρ 0 Z d c ǫ r F ( x, ˜ β c 1 , Q ¯ c 1 , 0) dν c ( r , x ) t 2 Z ρ 0 Z d c ǫ r G ( x, ˜ β c 1 , Q ¯ c 1 , 0) ν c ( r , x ) = α c = A, B . (38) The existence an d the unique ness of the so lution ( ˜ β c 1 , Q c 1 ) c = A,B to the s ystem (38) was tho roughly studied in [2]. Applying the results of [2] in our con text, we conclud e that ( β c 1 1+ ξ c , Q c 1 ) c = A,B = ( ˜ β c 1 , Q c 1 ) c = A,B is unique. W e turn now back to t he third equation of system (37) to get the following equality ξ c = g 1 ( d c ,Q ¯ c 1 ) F “ g 1 ( d c ,Q ¯ c 1 ) β c 1 1+ ξ c ” g 2 ( d c ) F ( g 2 ( d c ) β c 2 ) − 1 . The latter equation proves the uniquenes s o f ξ c for c = A, B . The uniquen ess of β c 1 follo ws direc tly fr om the same equation. So far , we have proved the uniquen ess of the solution to the s ystem (37) of e quation. As for the con vergence o f se quence s ( β A, ( φ K ) 1 , Q A, ( φ K ) 1 , ξ A, ( φ K ) , β B , ( φ K ) 1 , Q B , ( φ K ) 1 , ξ B , ( φ K ) ) to this uniqu e solution, its proof is omitted he re due to the lack of space, but follows the same ideas a s the p roof of con vergence of ( β A, ( φ K ) 2 , Q A, ( φ K ) 2 ) and ( β B , ( φ K ) 2 , Q B , ( φ K ) 2 ) provided ab ove. So f a r , me ma naged to prove that for a ny con vergent sub sequen ce ( d A, ( φ K ) , d B , ( φ K ) ) → ( d A , d B ) , the set of p arameters ( Q c, ( φ K ) 1 , Q c, ( φ K ) 2 , β c, ( φ K ) 1 , β c, ( φ K ) 2 , ξ c, ( φ K ) ) c = A,B con verges to some values Q c 1 , Q c 2 , β c 1 , β c 2 , ξ c which are completely characterized b y the system of e quations (34), (36) and (37), as fun ctions ( d A , d B ) . Using dec omposition ν c = ζ c × λ c , the sys tem formed by equations (34), (36) and (37) is equiv alen t to the system (19)-(20)-(21)-(22) provided in Theo rem 1. At this point, we thus proved that at least for some subseq uences φ K defined as above, the sub sequen ce Q c, ( φ K ) T con verges to a limit which has the form gi ven b y Theorem 1. The remaining task is to prov e that Q ( K ) T is a con ver ge nt seq uence. First, note that Q ( K ) T is a bounde d seque nce. Indeed, Q ( K ) T is defined as the minimum po we r that can be transmitted by the network to s atisfy the rate requirements. By definition, Q ( K ) T is thus less than the power obtained when using the nai ve solution wh ich consists in forcing eac h bas e station to transmit only in the p rotected band ( γ c k , 1 is forced to z ero for ea ch us er k of each cell c ). Now it can ea sily be shown that when K → ∞ , the power asso ciated with this naive s olution con verges to a constant. As a conseq uence, one can determine an u pper-bound on Q ( K ) T which does not depend on K . Second , assume for ins tance that Q T and Q ′ T are two a ccumulation points of seq uence Q ( K ) T . By contradiction, as sume that Q T < Q ′ T . Extract for ins tance a c ertain sub sequen ce o f Q ( K ) T which conv e r ge s to Q T . Inside this subsequenc e, one can further extract a sub sequen ce, s ay θ K , such that Q ( θ K ) T − → Q T , d c, ( θ K ) − → d c , ∀ c = A, B Nov ember 21, 2021 DRAFT 28 where d A and d B are some constants b oth (j u st use the f a ct that d c, ( K ) is bounded for each c ). Clearly , Q T can be written as in (18), whe re p arameters β c 1 , β c 2 , d c , Q c 1 , ξ c satisfy the sy stem of equ ations (19)- (20)-(21)-(22) . W e no w consider the follo wing suboptimal res ource alloca tion policy for finite numbe rs of users K A and K B . In each ce ll c ∈ { A, B } , users k whose distance x k to their BS is less than d c are forced to mo dulate in the interference band I only , while users k which a re farther than d c are forced to modulate in the protec ted band P c only . In othe r words, for each user k in cell c , we impose [ C ′ ] x k < d c ⇒ γ c k , 2 = P c k , 2 = 0 x k ≥ d c ⇒ γ c k , 1 = P c k , 1 = 0 ∀ c = A, B . (39) Particular values of the (nonz ero) resou rce allocation parameters γ c k ,i , P c k ,i are obtained by minimizing the classic al joint multi c ell resource alloca tion prob lem (Problem 2 in [1]), only inc luding the add itional constraint [ C ′ ] . As a new c onstraint has been ad ded, it is clear that the total power transmitted by the ne twork, say Q ( K ) , ∗ T , is alw a ys larger than the total p ower Q ( K ) T achieved by the optimal resou rce allocation, for any K . On the other ha nd, us ing the same asymptotic too ls a s previously , it ca n be shown after some algebra that lim K Q ( θ K ) , ∗ T = lim K Q ( θ K ) T = Q T . In other words, this s uboptimal solution pe rforms as go od as the optimal one when K has the form K = θ K ′ for some K ′ . Although we omit the proof, this ob servation is rather intuiti ve. Indeed for s uch K = θ K ′ , the op timal values of the piv ot-distances co n ver g e to the arbitrary ones d A , d B . Even more importantly , it can be shown that the total power Q ( K ) , ∗ T spent whe n using the s uboptimal proced ure con verges as K → ∞ . Therefore, lim K Q ( K ) , ∗ T = Q T . Now co nsider a subseque nce ψ K such that lim K Q ( ψ K ) T = Q ′ T > Q T , and compare o ur subo ptimal allocation p olicy to the optimal one for the K ’ s of the form K = ψ K ′ . As lim K Q ( ψ K ) T > lim K Q ( ψ K ) , ∗ T , there exist a certain ǫ > 0 and there exists a certain K 0 such that for any K > K 0 , Q ( ψ K ) T > Q ( ψ K ) , ∗ T + ǫ . The above inequality con tradicts the fact that Q ( ψ K ) T is the global solution to the joint multicell resource allocation problem (Problem 2 in [1] ). Th erefore, Q ′ T neces sarily coinc ides with Q T . This p roves that Q ( K ) T con verges to Q T . T o complete the proof of Theorem 1 , o ne s till needs to prove that for any fixed v alue of ( Q A 1 , Q B 1 ) ∈ R 2 + , the system formed by equations (19)-(20)-(21)-(22) admits at most one solution. The main ideas of this proof were evoked in the proof of Proposition 1 o f [1]. Howev e r , the complete proof is omitted due to lack of space. DRAFT November 21, 2021 29 R E F E R E N C E S [1] N. K sairi, P . Bianchi, P . Ciblat and W . Hachem, Resour ce A llocation for Downlink Sectorized Cellular OF DMA Systems: P art I—Optimal Allocation , 2008. [2] S . Gault and W . Hachem and P . Ciblat, P erformance Analysis of an OF DMA T ransmission System in a Multi-Cell En viro nment , IEEE T ransactions on Communications, num. 12, vol. 55, pp. 2143-2159, December , 2005. [3] J. Chen, R. A. Berry and M. L. Honig, Asymptotic Analysis of Downlink OFDMA Capacity , Forty-Fourth Annual Allerton Conference, September 2006. [4] H. W ang and B. Chen, Asymptotic distributions and peak power analysis for uplink OFDMA signals , IEEE International Conference on Acoustics, Speech, and Signal Processing, May 2004. [5] E . Biglieri, G. Caire, G . T arri co and E. V iterbo, How fading affects CDMA: an asymptotic analysis with linear r eceivers , IEEE Journal on Selected Areas in C ommunications , V olume 19, Issue 2, Pages:191 - 201, February 2001. [6] D. Gesbert, M. K ountouris, Joint P ower Contro l and User Scheduling in Multi-cell W ir eless Networks: Capacity Scaling Laws, submitted to IEEE T rans. On Information Theory , September 2007. [7] P . Billingsley , Proba bili ty and Measur e , 3rd edition Wiley , Ne w Y ork, 1995. [8] M. Maqbo ol, M. Coupechoux and Ph. Godle wski, Comparison of V arious F req uency Reuse P atterns for W iMAX Networks with Adaptive Beamforming. IEEE V ehicular T echnology Conference, VTC, S ingapore, may 2008. [9] H. Jia, Z. Zhang, G. Y u, P . Cheng, and S. Li, On the P erformance of IEEE 802.16 OF DMA System under Differ ent F r equency Reuse and Subcarrier P ermutation P atterns Proc. of IEEE. ICC, June 2007. [10] F . W ang , A. Ghosh, C. Sankaran, and S. Benes, W iMAX System P erforman ce with Multiple Tr ansmit and Multiple Receive Antennas, Proc. of IEEE VTC, April 2007. [11] T . Thanabalasing ham, S . V . Hanly , L. H. Andre w and J. Papandriopou los, J oint Allocation of Subcarriers and T ransmit P ower s in a Multiuser OFDM Cellular N etwork , IEEE International Conference on Communications ICC ’06, June 2006. [12] R. D. Y ates, A F ramework for Uplink P ower Contr ol in Cellular Radio Systems , IE EE Journal on Selected Areas in Communications, vol. 13, no. 7, September 1995. [13] N. Ksairi, P . B ianchi, P . Ciblat and W . Hachem, Resour ce Allocation for Downlink Cellular OFDMA Systems: T ec hnical Report , T ech. Rep., May 2009. A v ailable at http://www .tsi.enst.fr/ ∼ bianchi/Resource allocation techn ical report.pdf . [14] J. F . Bonnans and A. S hapiro, P erturbation analysis of optimization pr oblems, Springer , 2000. [15] COS T Action 231, Digital Mobile Radio t owar d Future Generation Systems, final rep ort , T ech. Rep., E uropean Communities, EUR 18957 , 1999. Nov ember 21, 2021 DRAFT
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment