
2504.05544
Abstract and deep analysis are available in the full post.

Abstract and deep analysis are available in the full post.
Abstract and deep analysis are available in the full post.
Abstract and deep analysis are available in the full post.
Abstract and deep analysis are available in the full post.
Abstract and deep analysis are available in the full post.
Abstract and deep analysis are available in the full post.
Abstract and deep analysis are available in the full post.

As climate change continues to reshape marginal ice zones in the Arctic, accurate and reliable sea ice data are critical for ensuring maritime safety. This study compares regional ice charts from the Alaska Sea Ice Program (ASIP) with satellite-derived Copernicus sea ice concentration data to evalua
I develop a novel semantics for probabilities of counterfactuals that generalizes the standard Pearlian semantics: it applies to probabilistic causal models that cannot be extended into realistic structural causal models and are therefore beyond the scope of Pearl's semantics. This generalization is

CLIP delivers strong zero-shot classification but remains highly vulnerable to adversarial attacks. Previous work of adversarial fine-tuning largely focuses on matching the predicted logits between clean and adversarial examples, which overlooks uncertainty calibration and may degrade the zero-shot
This work presents an extended formulation of the Least Squares with Virtual Displacements (LSVD) method for estimating shear strength parameters from multiple soil samples under varying resistance conditions including cohesionless, frictional, and mixed types. LSVD is designed to identify a common
This study evaluates two leading approaches for teaching construction robots new skills to understand their applicability for construction automation: a Vision-Language-Action (VLA) model and Reinforcement Learning (RL) methods. The goal is to understand both task performance and the practical effor
3D Gaussian Splatting (3DGS) has emerged as a mainstream solution for novel view synthesis and 3D reconstruction. By explicitly encoding a 3D scene using a collection of Gaussian kernels, 3DGS achieves high-quality rendering with superior efficiency. As a learning-based approach, 3DGS training has b
Large-eddy simulations of incompressible Newtonian fluid flows with approximate deconvolution models based on the van Cittert method are reported. The Legendre spectral element method is used for the spatial discretization to solve the filtered Navier--Stokes equations. A novel variant of approximat
Abstract and deep analysis are available in the full post.
We propose to improve medical decision making and reduce global health care costs by employing a free Internet-based medical information system with two main target groups: practicing physicians and medical researchers. After acquiring patients' consent, physicians enter medical histories, physiolog
The Hidden Web is the vast repository of informational databases available only through search form interfaces, accessible by therein typing a set of keywords in the search forms. Typically, a Hidden Web crawler is employed to autonomously discover and download pages from the Hidden Web. Traditional
Modeling of respiratory motion is important for a more accurate understanding and accounting of its effect on dose to cancers in the thorax and abdomen by radiotherapy. We have developed a model of respiration-induced organ motion in the thorax, without the commonly adopted assumption of repeatable
A subset of a topological space possesses the Baire property if it can be covered by an open set up to a meagre set. For the Cantor space of infinite words Finkel introduced the automatic Baire category where both sets, the open and the meagre, can be chosen to be definable by finite automata.
The algorithm of the creation texts parallel corpora was presented. The algorithm is based on the use of 'key words' in text documents, and on the means of their automated translation. Key words were singled out by means of using Russian and Ukrainian morphological dictionaries, as well as dictionar
Accuracy in spreadsheet modelling systems can be reduced due to difficulties with the inputs, the model itself, or the spreadsheet implementation of the model. When the 'true' outputs from the system are unknowable, accuracy is evaluated subjectively. Less than perfect accuracy can be acceptable dep
One of the major problems in computational biology is the inability of existing classification models to incorporate expanding and new domain knowledge. This problem of static classification models is addressed in this paper by the introduction of incremental learning for problems in bioinformatics.

The C++ programming language provides classes and structs as fundamental modeling entities. Consequently, C++ code tends to favour array-of-structs (AoS) for encoding data sequences, even though structure-of-arrays (SoA) yields better performance for some calculations. We propose a C++ language exte
Abstract and deep analysis are available in the full post.
S.Co.P.E. is one of the four projects funded by the Italian Government in order to provide Southern Italy with a distributed computing infrastructure for fundamental science. Beside being aimed at building the infrastructure, S.Co.P.E. is also actively pursuing research in several areas among which
Abstract and deep analysis are available in the full post.
Many models have been proposed to generate Internet Autonomous System (AS) topologies, most of which make structural assumptions about the AS graph. In this paper we compare AS topology generation models with several observed AS topologies. In contrast to most previous works, we avoid making assumpt
In this paper, we propose a scheme called 'beam-nulling' for MIMO adaptation. In the beam-nulling scheme, the eigenvector of the weakest subchannel is fed back and then signals are sent over a generated subspace orthogonal to the weakest subchannel. Theoretical analysis and numerical results show th
Modeling communication channels as thermal systems results in Hamiltonians which are an explicit function of the temperature. The first two authors have recently generalized the second thermodynamic law to encompass systems with temperature-dependent energy levels, $dQ=TdS+<dmathcal{E}/dT>dT$, where
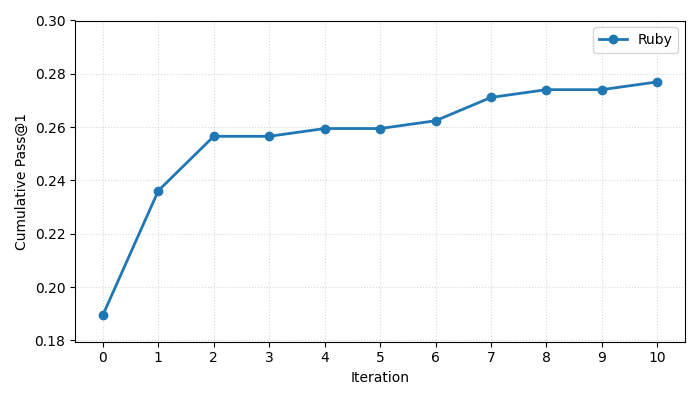
Automated Program Repair (APR) has advanced rapidly with Large Language Models (LLMs), but most existing methods remain computationally expensive, and focused on a small set of languages. Ruby, despite its widespread use in web development and the persistent challenges faced by its developers, has r
Here we demonstrate a synthetic micro-engine, based on long-range controlled movement of colloidal particles, which is induced by a local catalytic reaction. The directed motion at long timescales was achieved by placing specially designed magnetic capped colloids in a hydrogen peroxide solution at
The isotopic composition, for example, 14C/12C, 13C/12C, 2H/1H, 15N/14N and 18O/16O, of the elements of matter is heterogeneous. It is ruled by physical, chemical and biological mechanisms. Isotopes can be employed to follow the fate of mineral and organic compounds during biogeochemical transformat
A compressed full-text self-index represents a text in a compressed form and still answers queries efficiently. This technology represents a breakthrough over the text indexing techniques of the previous decade, whose indexes required several times the size of the text. Although it is relatively new
The author reviews the computer and robotic tools available to urologists to help in diagnosis and technical procedures. The first part concerns the contribution of robotics and presents several systems at various stages of development (laboratory prototypes, systems under validation or marketed sys
Our aim is to build a set of rules, such that reasoning over temporal dependencies within gene regulatory networks is possible. The underlying transitions may be obtained by discretizing observed time series, or they are generated based on existing knowledge, e.g. by Boolean networks or their nondet
Neuroinflammation is one of the key pathological events involved in the progression of brain damage caused by cerebral ischemia. Metabolism of arachidonic acid through cyclooxygenase (COX) enzymes is known to be actively involved in the neuroinflammatory events leading to neuronal death after ischem
Data points are placed in bins when a histogram is created, but there is always a decision to be made about the number or width of the bins. This decision is often made arbitrarily or subjectively, but it need not be. A jackknife or leave-one-out cross-validation likelihood is defined and employed a
The famous Lovasz Local Lemma [EL75] is a powerful tool to non-constructively prove the existence of combinatorial objects meeting a prescribed collection of criteria. Kratochvil et al. applied this technique to prove that a k-CNF in which each variable appears at most 2^k/(ek) times is always satis
Discovering the 'Neural Code' from multi-neuronal spike trains is an important task in neuroscience. For such an analysis, it is important to unearth interesting regularities in the spiking patterns. In this report, we present an efficient method for automatically discovering synchrony, synfire chai
Does the brain construct an efficient representation of the sensory world? We review progress on this question, focusing on a series of experiments in the last decade which use fly vision as a model system in which theory and experiment can confront each other. Although the idea of efficient represe
Hybrid vision transformers combine the elements of conventional neural networks (NN) and vision transformers (ViT) to enable lightweight and accurate detection. However, several challenges remain for their efficient deployment on resource-constrained edge devices. The hybrid models suffer from a wid
Multi-instrument observations of NOAA AR10938 on Jan. 14-18, 2007, are utilized to study the evolution of a magnetic thread system with multiple crossings suggestive of a twisted coronal flux rope. A C-class flare recorded by GOES on Jan. 16, at approximately 2:35 UT led to the brightening of the st
As the large language models (LLMs) grow in size each day, efficient training and fine-tuning has never been as important as nowadays. This resulted in the great interest in parameter efficient fine-tuning (PEFT), and effective methods including low-rank adapters (LoRA) has emerged. Although the var
There is an intrinsic relationship between the molecular evolution in primordial period and the properties of genomes and proteomes of contemporary species. The genomic data may help us understand the driving force of evolution of life at molecular level. In absence of evidence, numerous problems in
Text-attributed graphs are widely used across domains, offering rich opportunities for zero-shot learning via graph-text alignment. However, existing methods struggle with tasks requiring fine-grained pattern recognition, particularly on heterophilic graphs. Through empirical and theoretical analysi
The practical applications based on recurrent spiking neurons are limited due to their non-trivial learning algorithms. The temporal nature of spiking neurons is more favorable for hardware implementation where signals can be represented in binary form and communication can be done through the use o
Continuous attractor networks (CANs) are widely used to model how the brain temporarily retains continuous behavioural variables via persistent recurrent activity, such as an animal's position in an environment. However, this memory mechanism is very sensitive to even small imperfections, such as no
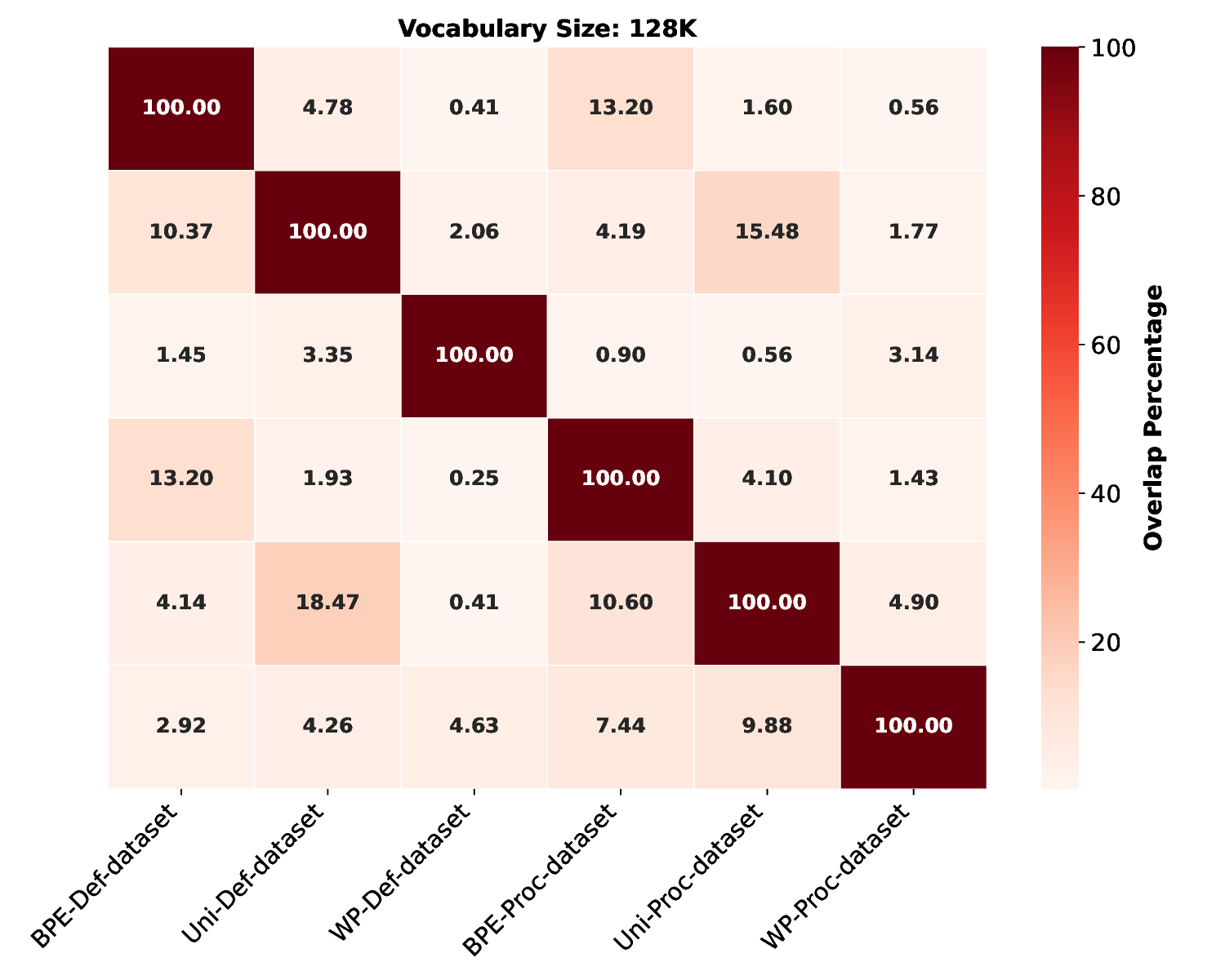
Tokenization is fundamental in assembly code analysis, impacting intrinsic characteristics like vocabulary size, semantic coverage, and extrinsic performance in downstream tasks. Despite its significance, tokenization in the context of assembly code remains an underexplored area. This study aims to
Abstract and deep analysis are available in the full post.
We study Bayesian discriminative inference given a model family $p(c,x, theta)$ that is assumed to contain all our prior information but still known to be incorrect. This falls in between 'standard' Bayesian generative modeling and Bayesian regression, where the margin $p(x,theta)$ is known to be un
Enter keywords to search articles