Secure Filtering against Spatio-Temporal False Data Attacks under Asynchronous Sampling
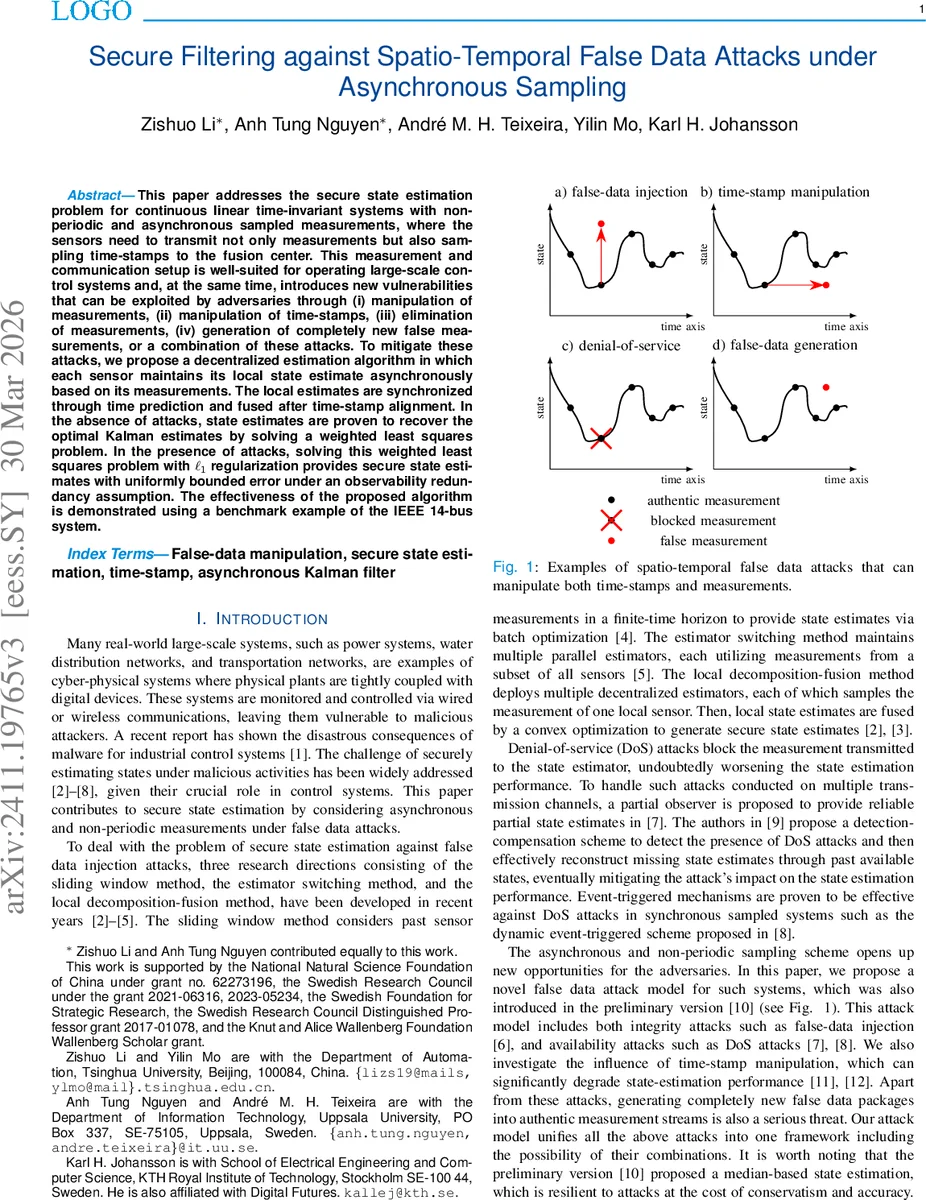
This paper addresses the secure state estimation problem for continuous linear time-invariant systems with non-periodic and asynchronous sampled measurements, where the sensors need to transmit not only measurements but also sampling time-stamps to the fusion center. This measurement and communication setup is well-suited for operating large-scale control systems and, at the same time, introduces new vulnerabilities that can be exploited by adversaries through (i) manipulation of measurements, (ii) manipulation of time-stamps, (iii) elimination of measurements, (iv) generation of completely new false measurements, or a combination of these attacks. To mitigate these attacks, we propose a decentralized estimation algorithm in which each sensor maintains its local state estimate asynchronously based on its measurements. The local states are synchronized through time prediction and fused after time-stamp alignment. In the absence of attacks, state estimates are proven to recover the optimal Kalman estimates by solving a weighted least square problem. In the presence of attacks, solving this weighted least square problem with the aid of $\ell_1$ regularization provides secure state estimates with uniformly bounded error under an observability redundancy assumption. The effectiveness of the proposed algorithm is demonstrated using a benchmark example of the IEEE 14-bus system.
💡 Research Summary
The paper tackles secure state estimation for continuous‑time linear time‑invariant (LTI) systems when measurements are sampled in a non‑periodic, asynchronous manner. Each sensor transmits a data packet consisting of its index, a time‑stamp, and the measured value. This communication model is attractive for large‑scale cyber‑physical systems because it reduces bandwidth requirements and allows flexible sampling, but it also opens new attack surfaces. An adversary may (i) inject false measurements, (ii) manipulate time‑stamps, (iii) drop packets (DoS), or (iv) generate entirely new bogus packets, possibly combining these actions across a set of compromised sensors. The authors formalize this as a “spatio‑temporal false data attack” and assume that at most p sensors are compromised (p‑sparse attacks). To guarantee resilience they require the system (A, C) to be 2p‑sparse observable, i.e., the system remains observable after removing any 2p sensors.
The authors first present an asynchronous sampled‑data Kalman filter (KF) that serves as an “oracle” estimator when no attacks occur. By defining a measurement‑availability indicator ϕ_i
Comments & Academic Discussion
Loading comments...
Leave a Comment