Ordering Power is Sanctioning Power: Sanction Evasion-MEV and the Limits of On-Chain Enforcement
Centralized stablecoins such as USDT and USDC enforce financial sanctions through contract-layer blacklist functions, yet on public blockchains a freeze is merely an ordinary transaction that must compete for execution priority. We identify a fundame…
Authors: Di Wu, Yuman Bai, Shoupeng Ren
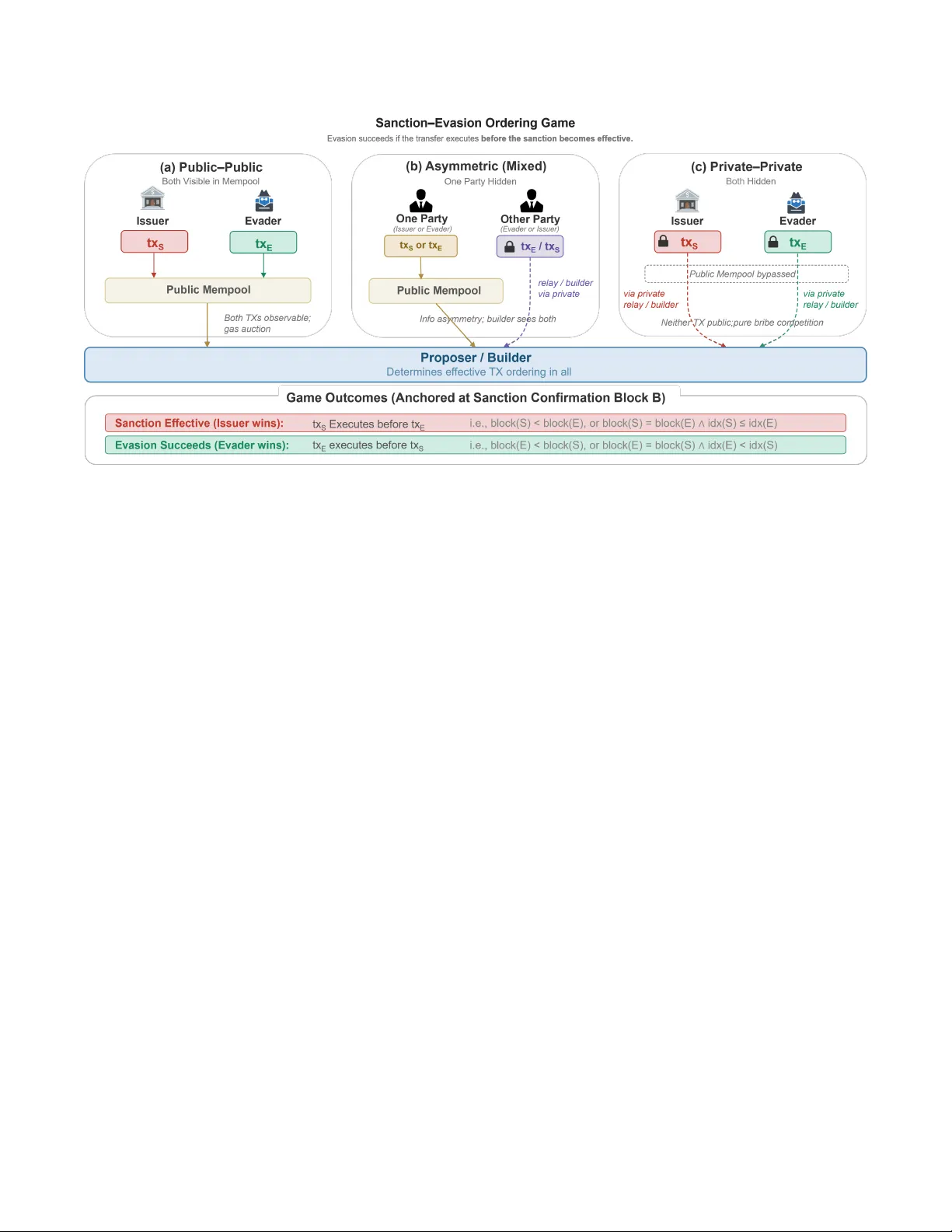
Ordering P ower is Sanctioning P o wer: Sanction Evasion-MEV and the Limits of On-Chain Enf or cement Di W u 1 , 2 † Y uman Bai 1 Shoupeng Ren 1 Xinyu Zhang 3 Y iyue Cao 2 Xuechao W ang 2 ∗ W u W en 1 Jian Liu 1 1 Zhejiang University 2 The Hong K ong University of Science and T echnolo gy (Guangzhou) 3 Sun Y at-Sen University wu.di@zju.edu.cn , baiyuman@zju.edu.cn , spren@zju.edu.cn zhangxy353@mail2.sysu.edu.cn , ycao948@connect.hkust-gz.edu.cn xuechaowang@hkust-gz.edu.cn , wu.wen@intl.zju.edu.cn liujian2411@zju.edu.cn Abstract Centralized stablecoins such as USDT and USDC enforce financial sanctions through contract-layer blacklist functions, yet on public blockchains a freeze is merely an ordinary transaction that must compete for execution priority . W e identify a fundamental gap between contract-layer authority and consensus-layer enforcement: when a sanctioned entity’ s transfer and the issuer’ s freeze race for inclusion in the same block, the outcome is determined not by regulatory mandate but by the economically motiv ated ordering decisions of block producers. W e term the resulting value extraction Sanction- Evasion MEV (SE-MEV) . T o quantify this vulnerability , we construct the first comprehensive dataset of on-chain sanc- tions enforcement and ev asion for Ethereum-based USDC and USDT (Nov 2017–Aug 2025), covering ov er $1.5 bil- lion in frozen assets. W e find that 7.3% of sanctioned USDT addresses and 18.7% of sanctioned USDC addresses were drained to zero balances before enforcement took effect, and document a clear escalation trajectory—from issuer-side out- of-gas f ailures, to public g as auctions, to pri vate order flo w , to direct proposer bribery . W e further develop a g ame-theoretic model that yields three results: (i) compliant issuers cannot ra- tionally stay outside the MEV market; (ii) fixed participation costs concentrate ev asion among specialized, MEV -aware actors; and (iii) the implicit MEV tax extracted by block pro- posers grows without bound as regulatory penalties intensify , creating structural incentiv es for issuers to vertically inte- grate into block-building infrastructure. Our findings demon- strate that on any blockchain where ordering power is allo- cated by economic incenti ves, ordering po wer is sanctioning power—and contract-le vel authority alone cannot guarantee enforcement. * Xuechao W ang is the corresponding author . † This work was carried out jointly at Zhejiang Uni versity and The Hong K ong Univ ersity of Science and T echnology (Guangzhou). 1 Introduction Stablecoins hav e emerged as one of the most critical pieces of infrastructure within the cryptocurrenc y ecosystem, serv- ing as the backbone for trading, lending, and cross-border payments [ 2 ]. Among them, centralized stablecoins, most notably USDT [ 3 ] and USDC [ 1 ], dominate market share. Their issuers can freeze assets at designated addresses through contract-layer blacklist functions. In pre vailing industry and regulatory narrati ves, this capability is typically treated as a sufficient condition for effecti ve sanctions enforcement: as long as the issuer possesses freeze authority , it can pre vent a targeted address from transferring its assets further [ 4 , 8 ]. This intuition, howe ver , does not automatically hold in the context of public blockchains, because a sanctions decision does not itself alter on-chain state. A blacklist in vocation is, in essence, an ordinary on-chain transaction. In networks such as Ethereum [ 19 ], where transac- tion ordering is allocated through economic incentives, under both Proof-of-Stake and Proof-of-W ork, a sanctioned entity can submit a transfer transaction in the same block and com- pete directly with the freeze transaction for execution priority . This is not merely a hypothetical concern. W e observe cases in which the issuer’ s freeze transaction entered the mempool ear- lier , yet the ev asiv e transfer was confirmed on-chain first: the sanction was issued, b ut no target v alue was actually frozen. Not all fund ev asion implicates the ordering layer — if a sanctioned entity mov es assets based on informational ad- vantage or anticipated risk, the issue is fundamentally one of information and timing, orthogonal to block ordering. But r eactive ev asion exposes a far more fundamental question: when a freeze and a transfer compete dir ectly f or execu- tion priority within the same ordering pipeline, who is effectively exer cising sanction enforcement po wer ? The central claim of this paper is that, in r eactiv e sanctions races, contract-layer authority is only a necessary condi- tion. Whether sanctions are actually enf orced depends on how the ordering layer allocates execution priority . Maximal extr actable value (MEV) [ 7 ] arises when transaction- 1 ordering infrastructure profits from controlling execution pri- ority . In reactive sanctions races, this profit opportunity is generated by the confrontation between sanctioning and e vad- ing parties, and we term the resulting marketized competition ov er ex ecution priority Sanction Evasion-MEV (SE-MEV) . T o quantify this vulnerability systematically , we construct the first dataset of on-chain sanctions enforcement and ev asion for Ethereum-based USDC and USDT from Nov 2017 to Aug 2025. Issuers froze more than $1.5 billion in total. Y et under a conservati ve definition, 7.3% of sanctioned USDT addresses and 18.7% of sanctioned USDC addresses had already been drained to zero balances by the time the freeze took effect. The empirical e vidence further rev eals a clear arms-race trajectory: from early issuer-side out-of-gas e xecution f ailures, to public gas bidding, to priv ate transaction submission, and ultimately to e vaders bypassing public fee mechanisms altogether and bribing block proposers directly . While the empirical evidence establishes the phenomenon, understanding its long-run systemic consequences requires theory . W e therefore de velop the first game-theoretic model of stablecoin sanctions that explicitly incorporates MEV . The model yields three central results. First, in a reacti ve sanc- tions en vironment, compliant issuers cannot remain outside the ordering market. Second, fixed participation costs push ev asion toward a small set of specialized, MEV -aw are actors. Third, the implicit MEV tax extracted by block proposers gro ws monotonically with regulatory penalty intensity . T aken together , these results show that as long as ordering power is controlled by profit-driven infrastructure, on-chain sanc- tions are not a one-of f exercise of authority , but an ongoing confrontation with escalating enforcement costs. The model also shows that repeated interaction creates structural incentives for issuers to vertically integrate into block-building infrastructure, placing direct pressure on blockchain neutrality . More broadly , the same structural vul- nerability applies to any pri vileged action that must be imple- mented through ordinary transactions, e.g., emer gency pauses, gov ernance interventions, or judicial freezes. Whenever or - dering po wer is allocated by economic incenti ves, a gap be- tween nominal authority and effecti ve enforcement becomes unav oidable. Our Contributions: • Problem definition. W e define reactiv e on-chain sanc- tions and identify the disconnect between contract-layer authority and consensus-layer enforcement as a system- lev el security limitation. • Empirical measurement. W e construct the first sanc- tions dataset for Ethereum USDT/USDC and quantify the gap between nominal sanctions actions and realized freezing outcomes. • Mechanism identification. W e introduce the concept of SE-MEV and provide the first empirical evidence that block proposers extract MEV from sanctions enforce- ment. • Equilibrium analysis. W e develop a game-theoretic model of sanctions with MEV , sho wing that the hidden enforcement cost grows without bound as regulatory penalties intensify , and rev ealing structural incentiv es for issuers to vertically inte grate into block-building in- frastructure. 2 Preliminaries In this section, we introduce the technical background re- quired to understand on-chain sanction enforcement and ev asion. W e revie w the blockchain and smart contracts, de- scribe digital assets and centralized stablecoins, explain issuer - driv en on-chain sanction mechanisms, and summarize the Ethereum MEV supply chain relev ant to transaction ordering. 2.1 Blockchain and Smart Contracts Blockchains maintain a shared global ledger among mutually untrusted participants. Users submit transactions that request state transitions, and a consensus protocol establishes a canon- ical transaction order so that all honest nodes deterministically apply the same state updates on-chain. Blockchain platforms differ in their state models. Bitcoin adopts a UTXO-based design, whereas Ethereum uses an account-based model in which persistent state is associated with accounts and updated directly by transactions. Ethereum further supports smart con- tracts, enabling general-purpose on-chain computation. Both externally o wned accounts (EOAs) and contract accounts co- exist in the global state: EO As initiate transactions, while contract accounts encapsulate executable code and storage. Contract ex ecution is deterministic under the Ethereum V ir- tual Machine (EVM), and successful executions commit state changes on-chain. Recent protocol updates (e.g., EIP-7702) further blur the distinction between EO As and contract ac- counts by allowing temporary delegation of ex ecution seman- tics, reflecting the flexibility of Ethereum’ s ex ecution model. 2.2 Digital Assets and T okens Native T okens. Blockchains nativ ely support protocol- defined digital assets, referred to as nativ e tokens, which are primarily used to pay transaction fees and incentivize con- sensus participation. T ransfers of native tok ens are enforced directly by the protocol. Fungible T okens. Programmable blockchains additionally support application-lev el fungible tokens implemented via smart contracts. On Ethereum, the ERC-20 standard speci- fies a common interface for such tokens, including balance management, transfers, and delegated transfers through the approve mechanism. 2 Stablecoins. Stablecoins are fungible tokens designed to track external reference assets, most commonly fiat curren- cies. They can be classified into decentralized designs, which rely on on-chain collateral and algorithms, and centralized designs, which are back ed by of f-chain reserves and go verned by a centralized issuer . As of February 2026, centralized sta- blecoins dominate the market, with USDC and USDT jointly exceeding $255 billion in total market capitalization. 2.3 Regulation and Sanctions Blockchain systems enable permissionless value transfer , which complicates the enforcement of traditional financial regulations. Unlike decentralized protocols, centralized sta- blecoin issuers are identifiable legal entities and are therefore subject to regulatory mandates, including financial sanctions imposed by authorities such as OF AC. T o comply with such mandates, centralized stablecoin con- tracts (e.g., USDC and USDT) expose issuer-controlled ad- ministrati ve functions that enforce sanctions directly on-chain. By in voking privile ged operations such as blacklist or freeze , the issuer updates contract state to disable transfers and approv als in volving designated addresses, causing subse- quent attempts to mov e funds to deterministically fail. As a result, regulatory sanctions are realized as on-chain state transitions initiated by the issuer , which must compete for transaction inclusion and ordering with other transactions. This ex ecution model creates observable races between sanc- tion enforcement and attempts to relocate assets before re- strictions take ef fect. 2.4 The MEV Supply Chain MEV refers to the profit that can be extracted by blockchain participants—miners in Proof-of-W ork (PoW) or v alidators in Proof-of-Stake (PoS)—by virtue of their po wer to arbitrarily order , include, or censor transactions within a block. The public mempool, where pending transactions are broad- cast, serves as the arena for MEV e xtraction. In modern PoS architectures like Ethereum’ s Proposer-Builder Separation (PBS), this process has ev olved into a sophisticated, multi- role supply chain [ 20 ]: • Searchers: These are independent actors who continu- ously monitor the mempool for profitable opportunities (e.g., arbitrage, liquidations, or in our conte xt, conflict- ing sanction/ev asion transactions). They express their desired transaction order and ex ecution as "bundles." • Builders: These specialized, trusted entities aggre gate bundles from multiple searchers and construct the most profitable full block possible. The y are responsible for the complex task of optimal block construction. • V alidators (Proposers): In the PBS model, validators delegate the block construction task. They simply select the block header from the builder that offers them the highest "bribe" or payment, then propose that block to the network. This "bribe" is the technical mechanism by which actors compete for block space and ex ecution priority . This compe- tition manifests in se veral ke y forms: (1) a public priority gas auction (PGA) , where actors compete using high transaction fees in the public mempool; (2) a pri vate, b undle-based bid- ding war , where searchers submit bundles with an explicit payment directly to builders (e.g., via services like Flash- bots 1 ); and (3) direct pr oposer payments , where an actor transfers value—typically ETH—directly to the block pro- ducer’ s fee-recipient address via a standalone on-chain trans- action, outside the standard gas-fee or bundle-tip mechanism. T rue off-chain side payments are unobserv able on-chain and therefore out of scope. A sanctioned entity attempting to re- locate funds before enforcement and an issuer attempting to enforce sanctions are thus engaged in this multi-faceted bidding war . The entire MEV supply chain is composed of rational, profit-maximizing actors who will include the trans- action or bundle that yields the highest profit, regardless of the underlying semantics (i.e., sanction vs. ev asion). 3 Threat Model In this section, we describe the threat model for on-chain sanction enforcement. W e specify the scope of systems under consideration, define the strategic roles in volved in sanction enforcement and ev asion, and clarify the observability limits of our analysis. 3.1 Scope of Study Our threat model focuses on sanction enforcement in cen- tralized, fiat-collateralized stablecoins, where issuers retain privile ged on-chain control. In particular , we consider USDC and USDT , which together account for over 80% of the global stablecoin market capitalization according to DeFiLlama [ 2 ]. As a result, sanction e vents in volving these assets constitute the dominant form of real-world on-chain stablecoin enforce- ment. W e focus our analysis on Ethereum, where both issuers maintain their largest circulating supplies—approximately $48B of USDC and $99B of USDT as of February 2026 [ 1 , 3 ]. Ethereum therefore represents the most significant and adver- sarially relev ant setting for on-chain sanction enforcement and ev asion. 1 https://www .flashbots.net/ 3 Figure 1: Reactiv e sanction races escalate into ordering competition across public and priv ate regimes. 3.2 System Roles W e consider three strategic roles in the on-chain sanction process. Issuer . The issuer is the centralized operator of a pri vileged stablecoin contract responsible for enforcing sanctions. The issuer’ s objecti ve is to pre vent sanctioned accounts from trans- ferring assets once a sanction decision is made, while min- imizing unintended disruption to other users. T o this end, the issuer can submit on-chain transactions that update the state of the stablecoin contract, freezing designated addresses and disabling further transfers inv olving those accounts. In practice, sanction enforcement may be carried out through a single or a sequence of transactions, submitted via either public mempools or priv ate channels. Evader . The ev ader is a sanctioned entity that controls ac- counts holding the issuer’ s stablecoin balance and seeks to retain access to these assets despite impending enforcement. The ev ader’ s objective is to move funds out of sanction- targeted accounts before the issuer’ s on-chain sanction update takes effect. T o this end, the ev ader attempts to submit on- chain transactions that transfer or otherwise relocate assets prior to enforcement, competing for timely inclusion and fa- vorable ordering through either public or pri v ate submission channels. Note that a sanctioned entity is tr eated as an evader only when sanction evasion intent can be attributed to it with observable on-chain evidence . Accordingly , we do not consider shared public infrastructure where individual intent cannot be isolated (e.g., Tornado Cash core contracts), nor large compliant e xchange deposit addresses that primarily act as aggregation sinks, as e vaders. Block Producer . The block producer is the entity responsible for constructing blocks, with discretion over transaction in- clusion and ordering. Its objecti ve is to maximize economic returns from block production, and it can prioritize, reorder , or exclude transactions when assembling a block. As a result, both issuer and e v ader transactions are ultimately subject to the block producer’ s economically motiv ated decisions. Note that all roles are subject to the same network condi- tions, such as propagation delays and network congestion, and neither the issuer nor the ev ader directly controls transaction inclusion or ordering. Fig 1 summarizes the resulting ordering game under three visibility regimes. In the simplest case (a), both the sanction transaction and the ev asion transaction are broadcast to the public mempool, and the contest reduces to an observable gas auction. When one party routes its transaction through a priv ate channel (b), the game becomes asymmetric: the builder observes both transactions but the public mempool rev eals only one. In the limiting case (c), both parties bypass the public mempool entirely , and the contest is resolved purely through priv ate bids to builders and proposers. 3.3 Observability Boundary Our analysis is grounded in a clear distinction between infor- mation that is directly observable on-chain, information that is only partially observable, and aspects that are inherently unobservable within the blockchain system. Directly observable (on-chain). W e can directly observe on-chain data, including transactions data and their execu- tion traces, token transfers and e vent logs, block heights and timestamps. These signals allo w us to precisely identify when 4 sanctions become effecti ve on-chain and to measure realized asset movements occurring prior to enforcement in a repro- ducible manner . Partially observable (auxiliary). Some signals relev ant to sanction enforcement are only partially observ able and can- not be treated as definiti ve evidence, yet the y provide useful context. Due to the incomplete and v antage-point–dependent nature of mempool access, we cannot precisely observe trans- action submission times. Entity identities inferred from third- party address labels may be inaccurate or outdated, and the use of priv ate transaction services is largely in visible on-chain. Accordingly , we treat such signals as supporting evidence, rather than as ground truth. Unobservable (off-chain). Certain aspects of the sanction process are not publicly observ able. In particular , we cannot directly observe of f-chain decision timelines, such as when an issuer internally decides to initiate a sanction, nor pri vate off-chain arrangements, such as bilateral agreements or side payments between actors. Our analysis does not rely on access to such information and is limited to what can be established from observable e vidence. 4 Methodology: Dataset Construction In this section, we describe how we construct a reproducible dataset for measuring on-chain sanction–e v asion races from raw ex ecution logs, as shown in Fig 2 . W e design a four- phase data construction pipeline that incrementally transforms raw on-chain data into an adversarial dataset. W e describe each phase in turn, including the methods, challenges, and design choices in volved. W e also collect auxiliary data used in specific empirical analyses and discuss the limitations of our methodology . 4.1 Phase 0: Raw On-Chain Data Collection Phase 0 collects raw on-chain data related to sanction enforce- ment, consisting of sanctioned addresses and their stablecoin transfer activity . These data form the raw dataset used by all subsequent phases of our pipeline. Time span and data sources. W e collect data from 2017- 11-28 12:41:21 UTC (the USDT contract creation time) to 2025-08-31 23:59:59 UTC using Google’ s public BigQuery Ethereum dataset and public archiv e nodes. Sanction event extraction. W e scan execution traces and ev ent logs of the USDT and USDC contracts to extract all sanction related operations, including blacklist updates and, for USDT , the destroyBlackFunds operation. For each op- eration, we record the affected address, tok en, block number , and transaction identifier . Raw sanctioned addr ess set. From these sanction e vents, we deriv e a raw set of sanctioned addresses, without applying any filtering. Stablecoin transfer and appro val histories. F or each sanc- tioned address, we retriev e the complete on-chain history of the corresponding stablecoin, including all incoming and outgoing transfers, approv al ev ents, and re verted transfer at- tempts. This yields a raw activity dataset capturing all token mov ements and delegated spending authorizations in volving sanctioned addresses ov er time. 4.2 Phase I: Sanction Semantic Filtering Since on-chain sanction actions do not always reflect true sanction intent, Phase I applies semantic filtering based on surrounding on-chain activity to remov e addresses that are not representativ e of actual sanction enforcement, yielding a cleaned set of sanctioned entities for downstream analysis. Revok ed sanctions. W e remov e addresses whose sanctions are later lifted through explicit unblacklist operations (e.g., removeBlackList ). Such cases typically correspond to tem- porary testing actions, false positi ves, or compliance remedi- ation, and do not constitute persistent sanction enforcement suitable for ev asion analysis. Recovery-moti vated sanctions. For USDT , we remove sanc- tions that are triggered as part of issuer-dri ven fund recov ery rather than enforcement. In particular , when tokens are acci- dentally sent to irrecoverable or unintended addresses (e.g., 0x0 ), T ether may blacklist the address to prev ent permanent loss, destroy the frozen balance, and subsequently re-issue the funds to a treasury or user -controlled address (e.g., a freeze → destroy → re-issuance sequence). Such sanctions are ad- ministrativ e in nature and are initiated to restore funds, not to restrict adversarial beha vior . W e therefore exclude related addresses from the ev asion dataset. After applying the above semantic filters, we retain a set of sanctioned addresses whose blacklist actions are more likely to reflect genuine sanction enforcement. This filtered address set forms the Sanctioned Entity Dataset (SED) used in subsequent phases. 4.3 Phase II: Adversarial Actor Filtering While Phase I isolates sanction actions that are more likely to reflect genuine enforcement, the resulting SED still contains many sanctioned addresses that are not modeled as e vaders under our threat model (§ 3.2 ). Phase II therefore filters the SED to remov e such cases, retaining only sanctioned entities for which ev asion intent and strategic action are observ able. Non-Strategic Intermediaries. W e exclude sanctioned ad- dresses that correspond to shared public infrastructure or com- pliant aggre gation sinks, such as mixer core contracts, generic routing contracts, and lar ge compliant e xchange deposit ag- gr egation cluster s . These addresses may appear in sanctioned fund flows and therefore reflect the outcomes of ev asion or enforcement actions. Ho we ver , they are not the entities that initiate or decide such actions. Because ev asion intent cannot 5 Inputs Logs Labels Phase 0: Extract Parse Eve nts Sanction & Unban Trace Hist ory All Transfers Raw Data Phase 1: Saniti ze Filter : Delisted Rm U nsanctioned Filter : Rescu ed For USDT Only SED Phase 2: Prune Filter : Agency Rm Non - Strategic Filter : Iner t Rm Zero I nflow AED Phase 3 : Con struct Episode( τ) Time Clusterin g Econ Fil ter ( α, β) Value Thresholds ESD Figure 2: Overvie w of the dataset-construction pipeline be attributed to these endpoints as independent actors, we do not treat them as adversarial e vaders in our analysis. Inert addresses. W e further exclude sanctioned addresses that nev er hold any stablecoin balance, i.e., addresses with no observed stablecoin inflo w . Such addresses hav e no as- sets to relocate and therefore cannot exhibit sanction e v asion behavior . After applying the abov e filters, we obtain a refined set of sanctioned entities that both control stablecoin assets and ex- hibit observable capacity for e v asion. This filtered population forms the Adversarial Evasion Dataset (AED) , which serves as the primary input for the final phase. 4.4 Phase III: Evasion Episode Identification After identifying adversarial actors, the remaining challenge is to define what constitutes concrete sanction evasion be- havior . On-chain data is recorded as discrete transactions, whereas ev asion corresponds to a sustained behavioral intent to relocate assets prior to sanction enforcement. Labeling individual transfers as ev asion would therefore be arbitrary and fragile: e vasion may unfold across multiple transactions, be interleav ed with routine usage, or occur through contract- mediated ex ecution paths. Phase III addresses this ambiguity through behavioral ab- straction . W e reconstruct raw transaction streams of adver- sarial entities into temporally coherent intent-level evasion episodes , each representing a contiguous period of activity plausibly driv en by a single ev asion attempt. These episodes serve as the fundamental units for identifying and analyzing sanction–ev asion behavior . Intent episode construction. For each address in the AED, we first order all of its transactions by block timestamp and compute the time gaps between consecutive transactions. W e then aggregate these inter-transaction gaps across all addresses and estimate their distribution using kernel den- sity estimation (KDE). W e define a threshold τ at the first prominent valle y of this distribution, which corresponds to the transition between short gaps associated with temporally related actions and longer gaps indicati ve of unrelated activ- ity . Using τ , we partition each address’ s transaction history into disjoint, time-ordered intent episodes , where consecutiv e transactions within an episode are separated by less than τ . Episode-level economic filtering . Intent episodes vary widely in economic significance. T o distinguish plausible sanction e v asion from routine usage or dust-le vel activity , we jointly quantify each episode’ s economic scale and apply a conservati ve materiality criterion grounded in regulatory practice and economic rationality . For an intent episode S , W e define the total av ailable liq- uidity during an episode as L episode = B start + ∑ tx ∈ episode Inflow ( t x ) , where B start is the stablecoin balance immediately before the episode begins, and Inflow ( t x ) denotes the stablecoin amount receiv ed by the address in transaction t x during the episode. This quantity captures the maximum amount of stablecoin the entity could plausibly relocate within the episode. Let V out denote the total stablecoin outflow within the episode. W e summarize the episode’ s asset relocation using the outflow ratio V out / L episode . W e classify S as an ev asion episode only if it satisfies ( V out ≥ β ) ∧ V out L episode ≥ α . The absolute threshold β is set to $1,000, reflecting widely adopted international AML standards (e.g., the F A TF T ravel Rule). The relativ e threshold α captures the fraction of av ail- able liquidity relocated. W e e valuate the robustness of our results under different choices of α in later analysis. Applying this procedure yields a dataset of evasion episodes , each representing a temporally coherent and eco- nomically material attempt to relocate assets in anticipation 6 of sanction enforcement. This dataset forms the basis for our empirical analysis of sanction–ev asion races. 4.5 A uxiliary Data Collection In addition to the datasets produced by the above pipeline, we collect a set of auxiliary data that are used where needed throughout the pipeline and in subsequent empirical analyses. Gover nance forensics. Because sanction enforcement is real- ized through issuer-controlled pri vileged functions, e xecution logs alone may miss failed or rev erted enforcement attempts. T o capture the full set of issuer-initiated sanction acti vity , we perform tar geted go vernance forensics to reconstruct sanction- related actions initiated by authorized controllers of USDT and USDC. For USDT , this in volves tracing blacklist opera- tions initiated by multisig o wners. For USDC, which employs an upgradeable proxy architecture, we follow role changes ov er time and track blacklist actions issued by authorized roles blacklister . This reconstruction allows us to observe sanction attempts rather than only successful executions, pro- viding a more complete view of issuer enforcement beha vior . USDT multisig timestamp reconstruction. For USDT , we further distinguish between the commitment time and the effecti ve time in the multisignature enforcement workflo w . Specifically , we record the timestamp at which sanction intent is first confirmed on-chain via Submission , denoted t submit , and the later timestamp at which the blacklist actually be- comes ef fective via Execution , denoted t exec . Throughout the paper , our main sanction-a ware e vasion labels, the ∆ statistics, and the race / tactical-reacti ve / strategic-migration re gimes remain uniformly anchored at t exec . By contrast, t submit is used only as a mechanism-le vel interpreti ve v ariable to character - ize an issuer -side committed-but-not-yet-ef fectiv e exposure window , rather than to redefine ev asion itself. Address attrib ution. T o support actor classification and fil- tering throughout the pipeline, we collect address labels from multiple sources, including Etherscan, Dune labels, and third- party security intelligence providers. W e adopt a conserv ati ve, hierarchical fusion strategy: when labels are consistent, we retain the attribution; when labels conflict or supporting e vi- dence is insufficient, we assign the address as unknown . This approach av oids forced attribution and limits the introduction of systematic bias, while providing auxiliary signals for iden- tifying issuers, intermediaries, and sanctioned entities where attribution is reliable. Regulatory and legal anchors. T o contextualize on-chain sanction activity , we collect external regulatory records, in- cluding the OF A C SDN list and publicly av ailable court seizure warrants indexed via the CourtListener API. These records serve as temporal and semantic anchors linking on- chain enforcement actions to documented regulatory or leg al e vents. W e do not assume that such of f-chain records are com- plete, timely , or perfectly aligned with on-chain execution; rather , they are used as reference points to support interpreta- tion of sanction timing and issuer behavior . T ransaction submission timing. T o estimate transaction submission timing prior to confirmation, we collect pub- lic mempool observations as a conserv ati ve lower bound. W e aggregate two mempool archives—Blocknati ve “Mem- pool Archi ve” (2019-01-11 to 2025-01-03) and the Flash- bots “Mempool Dumpster” (2023-07-08 to 2025-08-31)—and record, for each transaction, the earliest observed first-seen timestamp. Private submission signals. T o identify transactions that may bypass the public mempool, we collect auxiliary signals re- lated to priv ate submission. This includes priv ate-transaction flags from mempool sources and public Dune data on Flash- bots Protect and MEV -Share. Fee Baselines. T o isolate sanction–e v asion bidding behavior from ambient network congestion, we compute block-lev el fee baselines for comparison. For each block that contains a blacklist transaction or a candidate ev asion episode, we calculate the median and interquartile range (IQR) of ef fectiv e transaction fees in that block. These baselines characterize the contemporaneous fee en vironment faced by all transactions in the same block, allowing us to assess whether issuer or ev ader transactions pay fees that are unusually high relati ve to background conditions, while remaining robust to outliers. 4.6 Limitations Our measurements should be interpreted as conservative lower bounds . Sev eral sources of incompleteness and lim- ited observability constrain what can be inferred from the av ailable data. Mempool observability . Mempool visibility is v antage-point dependent and inherently incomplete. First-seen timestamps provide only lower bounds on transaction submission time, and historical cov erage is limited to av ailable archiv es. Address attribution. Address labels may be noisy or stale despite cross-source validation. Regulatory records. Judicial and regulatory data may be delayed, partial, or unav ailable (e.g., sealed cases), and non- U.S. sanctions are outside our primary scope. Private transaction channels. Cov erage of pri vate routing (e.g., Flashbots) is incomplete. Priv ate-transaction signals are treated as indicativ e evidence, not exhausti ve measurements. Off-chain coordination. W e observe standard transaction fees and direct proposer payments (standalone ETH transfers to fee-recipient addresses) on-chain. Purely off-chain side payments are unobservable and not quantified. Overall, these limitations bias our results to ward under- estimating the prev alence, intensity , and sophistication of sanction–ev asion behavior rather than ov erstating it. 7 Figure 3: Statistics for Frozen V alues T able 1: Filtering of sanctioned addresses into the adversarial e vasion dataset (AED). Percentages are relati ve to the Phase 0 raw set. Phase # USDT addr . # USDC addr . P0: Raw 2418 (100.0%) 341 (100.0%) P1: Filtered 352 (14.6%) 102 (29.9%) P1: Output (SED) 2066 (85.4%) 239 (70.1%) P2: Filtered 76 (3.1%) 116 (34.0%) P2: Output (AED) 1990 (82.3%) 123 (36.1%) 5 Empirical Study of On-chain Sanction In this section, we present empirical measurements and anal- yses of on-chain sanction enforcement and ev asion. 5.1 The Landscape of On-Chain Sanctions W e begin by characterizing the empirical landscape of on-chain sanctions after applying the dataset construction pipeline described in Section 4 . From raw execution logs, we extract 2,418 sanctioned USDT addresses and 341 sanc- tioned USDC addresses (Phase 0). After applying Sanction Semantic Filtering (Phase I) and Adversarial Actor Filtering (Phase II), we obtain the final Adversarial Evasion Dataset (AED) , comprising sanctioned addresses that remain consis- tent with our threat model and retain observ able ev asion po- tential. The AED contains 1,990 USDT addresses and 123 USDC addresses. In addition, we identify $24,808,527 of USDT that are destroyed via destroyBlackFunds as part of issuer-dri ven recovery workflows. Unless otherwise stated, the analysis in this subsection is address-le vel, i.e., each ob- servation corresponds to one sanctioned address in the AED. W e next characterize the pr ovenance of sanctioned ad- dresses in the AED. Cross-referencing the dataset with the OF AC Specially Designated Nationals (SDN) list sho ws that only a small fraction of sanctioned addresses can be directly linked to publicly listed OF AC designations, specifically 26 USDT addresses and 15 USDC addresses. T o further contex- tualize the remaining cases, we query publicly av ailable liti- gation records via CourtListener and identify 121 additional Figure 4: Prov enance of Sanctioned Addresses USDT addresses and 18 USDC addresses associated with documented legal proceedings. Beyond publicly disclosed regulatory designations and litigation records, we observe a distinct behavioral pattern among a subset of sanctioned addresses: repeated transfers of zero-v alue amounts to other addresses. Such activity is widely recognized as a phishing or address-poisoning technique used to create confusion in transaction histories and lure victims into misdirected trans- fers. Using this beha vioral signature, we further label 431 USDT addresses and 30 USDC addresses as phishing-like. The remaining sanctioned addresses cannot be directly at- tributed to public regulatory disclosures, litigation records, or phishing-like behavior , and are therefore categorized as unknown . Figure 4 summarizes the distribution of sanctioned addresses in these categories. Finding 1: Over 94% of on-chain sanctions are ini- tiated through issuer-dri ven enforcement or compli- ance actions without a corresponding public OF A C designation. From this point onward, we keep the sanctioned-address population fixed and switch only the measurement axis from address counts to frozen value at sanction ef fectiv eness. W e next quantify the economic impact of on-chain sanc- tions by measuring how much stablecoin value is actually frozen at the time of enforcement. For each address in the AED, we compute its stablecoin balance immediately be- fore the corresponding blacklist transaction becomes effec- tiv e on-chain. Aggregating across all sanctioned addresses yields the total amount of v alue directly frozen by issuer en- forcement actions. Figure 3 reports the distribution of frozen balances across sanctioned addresses. In aggregate, USDT sanctions freeze $1,411,842,932.22, while USDC sanctions freeze $108,250,166.32. These figures represent the lower bound of enforceable v alue, as they only account for balances remaining at the moment sanctions take ef fect. A closer inspection, howe ver , reveals a notable anomaly . A non-trivial fraction of sanctioned addresses hold little or no 8 balance at the time of enforcement. For USDT , 146 addresses (7.34%) hav e a zero balance, and an additional 250 addresses (12.56%) hold less than $1,000. For USDC, 23 addresses (18.7%) hav e a zero balance, and 7 addresses (5.69%) hold less than $1,000. Since all addresses in the AED are confirmed to hav e received stablecoin inflo ws prior to sanctioning, the presence of zero-balance and low-balance sanctions suggests potential existence of tar geted on-chain sanction e v asion. Finding 2: Despite over $1.5B in stablecoins being frozen in aggreg ate, a substantial fraction of sanc- tioned addresses hold zero or near-zero balances at the time enforcement takes ef fect. 5.2 Characterizing Evasion Beha vior W e next examine whether the balance anomalies observed in Section 5.1 reflect systematic on-chain sanction ev asion, and if so, what forms such beha vior takes. Beginning in this sub- section, the unit of analysis shifts from sanctioned addresses to intent-le vel e vasion episodes; accordingly , counts refer to episodes unless we explicitly report the number of unique addresses. Note that, USDT’ s enforcement architecture creates an additional commitment-to-effecti veness window; all primary labels remain anchored at t exec . Follo wing the procedure described in Section 4.4 , we recon- struct the complete transaction histories of all addresses in the AED and aggregate raw transactions into intent-le vel evasion episodes . W e collect a total of 132,251 transactions associated with AED addresses and compute inter-transaction time gaps across all addresses. Applying kernel density estimation to the gap distrib ution, we identify the first prominent v alley and obtain a data-dri ven temporal threshold of τ = 107 seconds. Using this threshold, we group temporally proximate trans- actions into coherent episodes. This process yields 110,199 intent episodes in total, comprising 108,275 episodes from 1,990 USDT -sanctioned addresses and 1,924 episodes from 123 USDC-sanctioned addresses. Each episode represents a contiguous period of acti vity that plausibly reflects a single asset-mov ement intent rather than isolated transfers. Applying the episode-le vel materiality criteria ( α = 10% , β = $1 , 000 ) filters out low-significance acti vity and yields a set of economically meaningful intent episodes with substan- tial outflows relativ e to av ailable liquidity (we examine ro- bustness to α values in Appendix ?? ). Howe ver , the presence of such episodes alone is insuf ficient to establish sanction e v a- sion. When we examine the temporal distance ∆ between the final net outflo w of an episode and the corresponding on-chain sanction becoming effecti ve, we observe extreme heterogene- ity: ∆ spans from seconds to multiple years. Episodes with large ∆ may reflect routine historical activity unrelated to a specific sanction action, whereas episodes occurring imme- diately before enforcement carry a much stronger causal and adversarial interpretation. This moti vates a time-aw are char- acterization of ev asion behavior that distinguishes near -term, sanction-reactiv e outflows from long-horizon asset move- ments with weak causal linkage to enforcement. T o identify natural time-scale separations in pre-sanction outflows, we analyze the distrib ution of the temporal gap ∆ between an episode’ s final net outflow and the corresponding on-chain sanction becoming ef fectiv e. When examined in log space, log ( ∆ ) exhibits a pronounced hea vy tail and clear multi-modal structure, indicating that ev asion-related activity spans multiple, qualitativ ely different temporal regimes. W e therefore fit a Gaussian Mixture Model (GMM) to log ( ∆ ) and select the model complexity using the Bayesian In- formation Criterion (BIC) over k ∈ [ 1 , 50 ] . BIC is minimized at k = 30 , suggesting that the empirical distrib ution cannot be adequately captured by a small number of components (e.g., k = 3 or k = 4 ) and exhibits substantial structural complexity . Importantly , we do not interpret the resulting 30 Gaussian components as distinct semantic classes of ev asion behav- ior . Instead, we treat the high- k GMM as a high-resolution density estimator whose role is to faithfully approximate the long-tailed, multi-peaked shape of log ( ∆ ) . This enables us to robustly identify stable lo w-density regions (valleys) and their associated posterior decision boundaries, which serve as data- dri ven cut points between adjacent temporal re gimes. Using a smaller k would force heterogeneous modes to be artificially merged, obscuring these natural separations by redistributing mass across components. Using the lo w-density v alleys induced by the k = 30 GMM as decision boundaries, we merge adjacent components to obtain a small set of reproducible time-scale regimes. This yields four regimes, defined by the temporal distance ∆ be- tween an episode’ s final net outflow and the corresponding on-chain sanction: (1) Race : ∆ ≤ 242 seconds; (2) T actical r eactive : 242 seconds < ∆ ≤∼ 1 day; (3) Strate gic migration : ∼ 1 day < ∆ ≤∼ 3 months; (4) Long-tail : ∆ > ∼ 3 months. W e focus our analysis on the first three regimes: race , tactical r eactive , and strate gic migration . W e do not analyze the long- tail regime further , as episodes in this range are temporally distant from the corresponding sanction ev ents and exhibit weak causal coupling, making them unsuitable for attribut- ing sanction-aware behavior . W e characterize the scale and prev alence of ev asion episodes in terms of episode counts, transferred v alue, and distrib utional statistics. These results are summarized in T able 2 , which reports regime-le vel aggre- gates separately for USDT and USDC. T able 2 reports regime-lev el counts, unique-address cover - age, total outflo w , and timing statistics. Three patterns stand out. First, canonical race episodes are rare and appear only in USDT (9 episodes; min ∆ = 24s), while USDC sho ws no race- regime episodes. Second, race-regime episodes, though fe w in number , are disproportionately high in v alue: the median outflow per episode is $3.83M, roughly 50 × the median ob- served in the tactical-reacti ve and strategic-migration regimes 9 T able 2: Ev asion episode statistics by temporal regime and token. Regime boundaries are derived from the GMM-based segmentation of log ( ∆ ) . Human-readable durations: 242 s ≈ 4 min , 95 , 514 s ≈ 26 . 5 h , 7 , 614 , 341 s ≈ 88 d . Outflow v alues are in USD. Regime T oken # Ep. # Addr . T otal Outflow ($) Median Outflow ($) Median ∆ (s) Min ∆ (s) Race ( ∆ ≤ 242 s) USDT 9 9 25,721,865 3,827,942 72 24 USDC 0 0 — — — — T actical reactive (242 s < ∆ ≤ 26 . 5 h) USDT 494 222 150,867,282 66,514 38,751 276 USDC 10 7 30,246,015 1,054,288 39,852 17,256 Strategic migration (26 . 5 h < ∆ ≤ 88 d) USDT 6,232 517 1,551,578,583 69,879 2,431,194 95,688 USDC 99 37 76,111,317 33,066 2,529,168 114,000 Long-tail ( ∆ > 88 d) USDT 11,489 351 2,015,455,042 64,000 35,939,484 7,616,620 USDC 99 29 13,123,274 30,535 43,469,848 7,856,556 ($64K–$70K). This suggests that direct ordering competition, with its associated infrastructure and fee costs, is econom- ically viable only when the balance at stake is suf ficiently large. Finding 3: Sanction-aw are asset relocation occurs across multiple time scales, with substantial v alue exiting in the days and months preceding on-chain enforcement. T o understand how sanctioned value e xits prior to enforce- ment, we analyze the destination addresses of outflo ws asso- ciated with e vasion episodes in the race , tactical r eactive , and strate gic migration re gimes. Across all regimes, we identify 6,256 distinct destination addresses. Using multi-source ad- dress attribution, 2,152 of these addresses can be assigned semantic labels. W e group destination addresses into coarse functional categories, including centralized custodial entry points (e.g., exchanges, brokers, custodians), instant swap and aggregation services, cross-chain bridges, mark et-facing infrastructure (e.g., MEV bots or market-making contracts), and a small number of high-risk or already-sanctioned entities. Figure ?? summarizes the distrib ution of outflo w destinations across these categories. Overall, sanctioned outflo ws predominantly move into liq- uid exit venues, most notably centralized custodial platforms and fast exchange mechanisms, rather than remaining within long-liv ed DeFi positions or complex contract structures. 5.3 Sanction Evasion MEV (SE-MEV) W e now zoom in on the shortest time-scale e vasion beha vior and examine ho w sanction enforcement and ev asion escalate into direct competition at the block-construction layer, nar - rowing the lens from episode-le vel prev alence to mechanism- lev el evidence in the short-horizon race regime. In the race regime identified in Section 5.2 , e vasion is no longer dri ven by informational asymmetry or long-horizon planning, but by adversarial bidding for transaction inclusion and ordering. This setting naturally giv es rise to a form of MEV induced by sanction enforcement, which we refer to as Sanction-Evasion MEV (SE-MEV) . Level 1: Gas-Price Competition. As shown in Figure 5 , the most direct mechanism for competing o ver block inclusion is transaction fees. W e therefore begin by e xamining the gas prices paid by issuer sanction transactions and by ev asion transactions in the race and tactical r eactive regimes. T o robustly assess fee aggressiv eness while controlling for background congestion and MEV -induced volatility , we normalize each transaction’ s ef fectiv e gas price against the median gas price of its containing block. This allows us to ev aluate whether a transaction pays a premium relati ve to contemporaneous block conditions. W e observe a clear asymmetry in early enforcement behav- ior . Prior to the first half of 2024, USDC issuer transactions consistently pay abov e-median gas prices, whereas USDT is- suer transactions largely cluster around the block median and, in some cases, fall belo w it. During this period, we identify 8 rev erted USDT sanction transactions caused by out-of-gas failures, spanning from October 2021 to February 2024. These failures indicate that early USDT enforcement did not sys- tematically account for adversarial competition at the block lev el. From the second half of 2023 onward, ho we ver , USDT is- suer gas prices rise sharply and be gin to track the ele v ated pre- miums paid by ev asion transactions. This shift coincides with a sustained increase in gas premiums on both sides, indicating the onset of explicit fee-based competition for inclusion. Finding 4: Gas-price competition marks the first stage of SE-MEV , with both issuers and evaders paying increasing fee premiums to secure transac- tion inclusion. Stake-sensitiv e fee competition. The pre vious analysis documents escalating gas premiums, but leav es open why 10 Figure 5: T rend of Gas Price Ratio of Sanction and Evasion some ev aders bid more aggressively than others. A natural mechanism-lev el question is whether the amount of value at stake helps explain the intensity of public fee competition. T o examine this, we relate episode-lev el controllable liq- uidity to public fee aggressiveness. Follo wing Section 4.4, we use total av ailable liquidity within an ev asion episode, L episode , as a proxy for the stake in volv ed in that episode. W e measure public fee aggressiv eness as the ratio between the fees actually paid by the e vader and a counterfactual bench- mark computed at the block-median gas price. Intuiti vely , this metric is intended to capture the public fee premium paid for ex ecution priority , rather than primarily reflecting differences in gas usage or transaction counts. The resulting pattern is strongly time-scale dependent. The canonical race regime ( ∆ ≤ 242 s) contains only 9 qualify- ing episodes, which is too small to support stand-alone in- ference. W e therefore also examine slightly broader nested short-horizon windows ( ∆ ≤ 1 , 200 s and ∆ ≤ 3 , 600 s) to as- sess whether the same directional relationship persists nearby; these are not new beha vioral regimes, b ut relaxed windows around the same short-horizon ordering setting. As T able 3 shows, L episode is positiv ely associated with public fee premia in these short-window specifications, b ut the relationship becomes weak once we mov e to the broader tactical-reactiv e horizon. This pattern suggests that stake- sensitiv e public fee competition is primarily a short-horizon phenomenon: when reaction time is highly constrained, ev aders with more controllable value appear willing to pay higher premia for execution priority , whereas ov er longer horizons the public gas signal is diluted by greater behavioral heterogeneity and by channels less visible in public gas prices, such as pri vate submission or pre-positioned ex ecution. W e therefore interpret this result as mechanism-consistent sup- port for SE-MEV on the public fee channel, rather than as a stand-alone causal claim. Level 2: Private Order Flow . As fee competition inten- sifies, actors have incenti ves to bypass the public mempool altogether and submit transactions through pri vate channels. W e therefore examine the use of priv ate transactions by both issuers and e v aders, using mempool archi ve data as a lower - bound observation windo w . W e find that USDT issuers experimented with pri vate trans- action submission as early as March 2022, although this usage was sporadic and discontinued until reappearing at scale in 2025, with 74 observed priv ate submissions. Ev asion beha vior lags slightly: USDT e v aders begin using pri vate channels in Nov ember 2022, with 116 observed instances. USDC issuers do not adopt pri vate submission until December 2024, after which both issuers and e vaders use pri vate relayers in small but comparable numbers. The adoption of pri vate order flow by both sides reflects a 11 T able 3: Relationship between episode-lev el stake and public fee premia across pre-sanction time windows. L episode proxies the value controllable within an ev asion episode. Public fee premia are measured as the ratio between fees actually paid and counterfactual fees computed at the block-median gas price. Positi ve associations appear in short-horizon windo ws but weak en in the broader tactical-reactiv e regime. W indow Interpretation n Spearman ρ OLS ˆ β p -value ∆ ≤ 242s Canonical race 9 0.4407 – – ∆ ≤ 1200s Relaxed short horizon 20 0.4910 0.2317 0.0017 ∆ ≤ 3600s Relaxed short horizon 31 0.1150 0.1366 0.0226 242s < ∆ ≤ 86400s T actical-reactiv e 456 -0.0387 -0.0172 0.0594 shared recognition that mempool visibility itself has become a strategic liability: issuers seek to conceal impending sanctions, while e v aders seek to a void being front-run once enforcement intent is rev ealed. Finding 5: Both issuers and ev aders adopt priv ate transaction submission, indicating that mempool visibility becomes a strategic bottleneck in sanction races. Level 3: Infrastructur e Capture and Dir ect Proposer Pay- ments. At the final stage of escalation, competition moves beyond gas prices and priv ate relayers to direct interaction with block-building infrastructure. W e identify a representative case in which the issuer’ s sanction transaction appears in the mempool approximately 22 minutes before the final ev asion outflow , yet is confirmed on-chain nearly 2.8 hours later . Despite the issuer’ s earlier visibility , the e vasion transaction is included first, indicating preferential ordering inconsistent with public fee competition alone. Due to the limited visibility of mempool data, such cases represent a conservati ve lo wer bound. For USDT , one additional measurement qualifier is needed. Because its sanction workflow follows a two-step multisig- nature process, sanction intent is first publicly committed on- chain via Submission , whereas blacklist effecti veness arri ves only later at Execution . Accordingly , the USDT race-re gime episodes studied in this paper are still ordering contests iden- tified relativ e to effective enforcement , but in practice they often unfold within a wider committed-b ut-not-yet-ef fectiv e window created by the issuer’ s execution architecture. W e therefore interpret this window as an issuer -side amplifier of exposure, rather than as a separate SE-MEV mechanism or a redefinition of ev asion. As auxiliary statistics, this committed-b ut-not-yet-effecti ve window contains 116 economically material episodes totaling $73.7M, with a median duration of about 5.3 hours. Finally , we find direct e vidence of explicit bribery . In 122 instances, ev aders transfer ETH directly to block fee recipients outside the standard transaction fee mechanism, consistent with direct proposer payments for preferential inclusion. Finding 6: Ev asion escalates to direct infrastructure capture, including preferential ordering and direct proposer payments, providing concrete e vidence of SE-MEV . Summary . Be yond fee escalation and proposer payments, we observe structural evidence of e v asion specialization. In sev eral instances, a single entity drained multiple sanctioned addresses within a narrow time window by leveraging pre- positioned ERC-20 approv als, consistent with the delegation- based e v asion bot predicted by our model (Observ ation 2, §6.4). A detailed analysis of these delegation patterns is de- ferred to the extended v ersion. T aken together , these observations re veal a clear escalation path: from nai ve fee setting, to gas-price w ars, to pri v ate or- der flow , and finally to direct interaction with block-building infrastructure. At each stage, additional v alue is transferred to builders and v alidators, not as a byproduct of generic MEV , but as a direct consequence of adv ersarial sanction enforce- ment and ev asion. W e define Sanction-Evasion MEV (SE-MEV) as the value extracted by block-b uilding infrastructure from this adversar - ial competition. In the next section, we formalize this mecha- nism and analyze its implications for protocol neutrality and regulatory enforcement. 6 A Game-Theoretic Model of MEV -based Sanctions 6.1 Inf ormal Over view W e model fiat-backed stablecoin sanctions as a T ullock contest ov er transaction ordering [ 6 , 9 ]. A compliant issuer I and an ev ader B compete ov er a fixed illicit balance V > 0 at a risky address; MEV infrastructure and block proposers determine whether V is frozen or successfully e v aded. A contest is triggered by a publicly observable off-c hain r egulatory or risk signal (e.g., sanctions list updates, public attribution of hacks/fraud, la w-enforcement announcements, or on-chain risk flags). W e treat this signal as the common start time at which both parties can react. 12 W e study a single sanction contest tied to one block. Issuer I prepares a freezing transaction T x I and ev ader B prepares an ev asion transaction T x B that attempts to move V to a fresh address. Both can route transactions via the public mempool (gas price/tip bidding) and priv ate MEV channels (builders, re- lays, pri vate RPCs). W e abstract these mechanisms into scalar contest expenditur es b I and b B , interpreted as the incremental payments and priority fees attributable to the corresponding ex ecution path. The contest starts when both players can simultaneously choose e xpenditures, and r esolves in the first block in which a proposer sees mutually e xclusi ve v alid bundles corresponding to the freeze and ev ade paths. W e treat this first-block resolu- tion as a one-shot stage game; subsequent blocks correspond to separate contests. The terminal outcomes are: (i) fr eeze , where T x I ex ecutes first and renders V non-transferable, and (ii) evade , where T x B ex ecutes first and mov es V before any freeze can take effect. If neither side participates, the contest is degenerate and the state does not change in that block. The issuer values av oiding expected regulatory loss (not seizing V ), the ev ader values ev asion by V , and proposers capture MEV rev enue induced by ( b I , b B ) . 6.2 F ormal T ullock Contest Model W e study a single sanction contest ov er balance V > 0 be- tween issuer I and e vader B ; proposers and MEV infrastruc- ture M mediate execution and recei ve contest expenditures. V aluations. If ev asion succeeds, the issuer incurs an ex- pected regulatory loss Ψ > 0 , so Ψ is I ’ s v aluation for winning (freeze). The ev ader values winning by V . Assumption 1 (Strong regulatory penalties) . Ψ ≥ 2 V . This bound is conservati ve: under IEEP A, the statutory civil penalty cap is the greater of a fix ed amount or twice the transaction value . 2 T echnology and costs. After an of f-chain trigger , each player k ∈ { I , B } decides whether to participate (paying a fixed cost C k ≥ 0 ) and, conditional on entry , chooses an ex- penditure b k ≥ 0 via gas/tips and pri vate MEV side payments. Assumption 2 (Competiti ve MEV access) . I and B can r oute T x I and T x B to an overlapping, economically meaningful set 2 50 U.S.C. §1705; 31 C.F .R. §560.701(a)(2) (inflation-adjusted to $377,700 as of 2025). Criminal fines under 18 U.S.C. §3571 are likewise capped at twice the pecuniary gain or loss. Because the GENIUS Act desig- nates stablecoin issuers as financial institutions under the Bank Secrecy Act, IEEP A penalties apply directly . The Act further mandates that issuers main- tain the technical capability to freeze or burn tokens upon la wful order [ ? ], so a failed freeze is itself a sanctionable act. Reputational costs, license- rev ocation risk, and potential compounding across multiple violations push the effecti ve Ψ well abo ve 2 V . of pr oposers (dir ectly or via builder s/r elays); neither has an exclusive c hannel. Giv en ( b I , b B ) , the contest resolves according to the T ullock ( r ) success function P I ( b I , b B ) = b r I b r I + b r B , P B ( b I , b B ) = b r B b r I + b r B , with r ≥ 1 capturing contest sharpness (as r → ∞ the out- come approaches highest-bid-wins; latency and intermediary selection generate noise). Utilities. Per-contest payof fs are U B ( b I , b B ) = P B ( b I , b B ) ( V − b B ) − C B , U I ( b I , b B ) = P I ( b I , b B ) Ψ − b I − C I . W e model the issuer’ s marginal bidding expenditure b I as all-pay and the e vader’ s marginal bidding expenditure b B as conditional-pay . The issuer-side choice is moti vated by insti- tutional rather than technical constraints: while the issuer may choose priv ate or public submission channels, its compliance role requires it to attempt enforcement independent of the expected frozen amount. Accordingly , conditional on entry , the issuer’ s marginal e xpenditure is functionally all-pay . By contrast, modern MEV infrastructure enables e vaders to make proposer-f acing marginal payments contingent on e xecution success (e.g., via atomic bundle e xecution in Flashbots), con- sistent with the priv ate-order-flo w patterns documented in Section 5.3 . Under the single-block contest formulation, the ev ader can make at most one effecti ve submission attempt in the contested ordering game, so the cost of e xecution failure (e.g., re verted gas consumption) is absorbed into the fix ed par - ticipation cost C B on a per -contest basis; this is a conserv ati ve approximation in that it understates per -attempt v ariable costs and therefore, if anything, o verstates the e vader’ s net payof f. Timing within a block. A single contest associated with one block proceeds as: 1. ( Off-c hain trig ger . ) A public risk signal indicates that the address holding V is likely to be sanctioned. 2. ( P articipation. ) Each player decides whether to partici- pate, pays C k if so, and prepares T x I or T x B . 3. ( Bidding. ) Participants simultaneously choose b I , b B ≥ 0 . 4. ( Resolution. ) Proposers recei ve all relev ant bundles; ( P I , P B ) determines whether freeze or e vade i s realized first. If freeze wins, V is frozen; otherwise V is ev aded. This defines the SE-MEV contest for a single block: a two- player T ullock ( r ) contest between I and B ov er prize pair ( Ψ , V ) , with contest expenditures accruing to proposers as MEV re venue (or dissipated as contest ef fort, depending on implementation). 13 6.3 Equilibrium of a Single SE-MEV Contest W e fix the ev ader’ s prize at V and the issuer’ s prize at Ψ , with Ψ ≥ 2 V . Conditional on participation, the interaction between I and B is a two-player T ullock ( r ) contest with prize pair ( Ψ , V ) , in which the issuer is all-pay (always pays b I ) and the e vader is conditional-pay (pays b B only upon successful ev asion). Participation costs C I and C B do not af fect equilib- rium bids conditional on entering, so we suppress them in this subsection. Proposition 1 (Equilibrium bids in the SE-MEV contest) . Consider a single sanction contest in which both I and B participate and play pur e strate gies. There exists a unique interior Nash equilibrium with bids b ∗ I = Ψ r P ∗ I P ∗ B , b ∗ B = rP ∗ I V 1 + r P ∗ I , success pr obabilities P ∗ I = ( s ∗ ) r 1 + ( s ∗ ) r , P ∗ B = 1 1 + ( s ∗ ) r , and intensity ratio s ∗ = b ∗ I b ∗ B given by the unique positive solu- tion to s ∗ 1 + ( s ∗ ) r 2 = Ψ V 1 + ( 1 + r )( s ∗ ) r . The expected total contest e xpenditure (MEV r evenue) is T ∗ ≡ b ∗ I + P ∗ B b ∗ B = b ∗ B s ∗ + 1 1 + ( s ∗ ) r . The proof follows a two-player T ullock ( r ) contest analysis and is deferred to the appendix. Because Ψ ≥ 2 V , we hav e P ∗ I > 1 2 , T ∗ > r r + 2 V . Thus, a regulated issuer can k eep the per-contest e vasion probability belo w one-half, but doing so requires substantial contest expenditures that gro w without bound (relative to V ) as sanctions become more sev ere. W e next use Proposition 1 to deriv e two corollaries and two observ ations. Corollary 1 (The MEV tax) . In SE-MEV equilibrium, block pr oposers (and MEV intermediaries) extr act an implicit MEV tax equal to T ∗ in expectation. Pr oposition 1 implies that T ∗ / V → ∞ as Ψ / V → ∞ . The sanction outcome (freeze vs. ev ade) affects the in- cidence of this tax (issuer via enforcement vs. ev ader via ev asion), but not whether the tax is paid. If I nev er bids, then an active ev ader can bid b B = ε > 0 , yielding P B ( 0 , ε ) = 1 and issuer payoff U no - MEV I = − Ψ − C I . By Proposition 1 , equilibrium play giv es U ∗ I = P ∗ I Ψ − b ∗ I − C I > − C I > − Ψ − C I = U no - MEV I , so nev er bidding is strictly dominated whenever B is acti ve. Observation 1 (Issuers are forced into MEV) . Under As- sumptions 1 and 2 , a compliant issuer cannot rationally ig- nor e MEV contests: any strate gy with b I ≡ 0 against an active evader is strictly dominated by participating and bidding ac- cor ding to the SE-MEV equilibrium. Lemma A.3 strengthens Observation 1 . Under r ≥ 1 and Ψ / V ≥ 2, it shows that U ∗ I + C I > 0 , that is, conditional on entry , the expected enforcement g ain P ∗ I Ψ strictly exceeds the equilibrium bidding expenditure b ∗ I , regardless of the fix ed participation cost C I . Thus, the issuer is not merely better off participating than choosing b I ≡ 0 against an acti ve e vader; the equilibrium contest itself yields a strictly positi ve gross enforcement v alue for the issuer . In this sense, Lemma A.3 goes beyond a simple dominance state- ment: once sanctions are sufficiently consequential, MEV participation becomes an economically meaningful compo- nent of compliant enforcement rather than a purely defensive or symbolic action. 6.4 Centralization of Evasion into Specialized Bots Fixed participation costs C B create economies of scale for ev asion. Consider n ev aders A 1 , . . . , A n with balances V i and penalties Ψ i such that ∑ i V i = V , ∑ i Ψ i = Ψ , and Ψ i / V i = Ψ / V . When sanctioning becomes likely , ev ader A i either acts solo (paying C B and contesting ( Ψ i , V i ) ) or delegates V i to a specialized bot S that aggregates v olume and contests ( Ψ , V ) , charging commission f ∈ ( 0 , 1 ) . Solo payoffs are U solo A i = P ∗ B ( Ψ i , V i ) V i − b ∗ B ( Ψ i , V i ) − C B = V i 1 + ( 1 + r )( s ∗ ) r − C B , where the last equality uses that Ψ i / V i (and r ) are common, so the equilibrium intensity ratio (and hence the constant factor) is identical across i . Thus the gross gain is Θ ( V i ) and v anishes as V i → 0, implying U solo A i < 0 for suf ficiently small V i . Under delegation, e vaders pool their funds into a special- ized bot S , which earns U gross S = P ∗ B ( Ψ , V ) V − b ∗ B ( Ψ , V ) , 14 pays C B once, and distributes ( 1 − f ) pro rata, so U delegate A i = ( 1 − f ) V i V U gross S − C B , which is positiv e whenever U gross S > C B and V i > 0. Observation 2 (Centralized e v asion bots) . W ith non-trivial fixed costs C B , small evaders optimally dele gate to a few spe- cialized bots that amortize C B acr oss larg e illicit volume; the issuer ther efor e competes against a small number of sophisti- cated MEV -awar e adversaries. 6.5 Dynamic Extension: V ertical Integration and Consensus Capture W e extend the model to a repeated setting and show that a large re gulated issuer has incenti ves to acquire block proposal rights. Let I acquire an exogenous long-run proposer share α ∈ [ 0 , 1 ] (e.g., via staking). W ith probability α the proposer is issuer-controlled, so I enforces a freeze with probability 1 and incurs cost C I . W ith probability 1 − α the proposer is neutral, and the block resolves via the SE-MEV contest. Thus the issuer’ s per-contest e xpected enforcement-cost component is C total I ( α ; V , Ψ ) = C I + ( 1 − α ) b ∗ I ( Ψ , V ) + P ∗ B ( Ψ , V ) Ψ . This quantity captures the issuer’ s expected enforcement e x- posure arising from sanction contests. It is not intended to represent the issuer’ s full net benefit from acquiring proposer share; rather , it isolates the loss component that can be re- duced by increasing control ov er ordering. Corollary 2 (V alue of ordering control) . F ix the SE-MEV con- test equilibrium of Pr oposition 1 . F or any exog enous issuer pr oposer share α ∈ [ 0 , 1 ] , the issuer’ s per-contest expected enfor cement-cost component C total I ( α ; V , Ψ ) = C I + ( 1 − α ) b ∗ I ( Ψ , V ) + P ∗ B ( Ψ , V ) Ψ is strictly decr easing in α , with ∂ ∂α C total I ( α ; V , Ψ ) = − b ∗ I ( Ψ , V ) + P ∗ B ( Ψ , V ) Ψ < 0 . Mor eover , − ∂ α C total I ( α ; V , Ψ ) V → ∞ as Ψ V → ∞ . Corollary 2 sho ws that increasing issuer control ov er order - ing strictly reduces this component of enforcement exposure. Therefore, stronger ordering influence creates a corresponding pressure for the issuer to e xpand its share of proposal rights, ev en though the optimal degree of such expansion depends on off-model considerations. 7 Discussion In this section, we discuss broader insights of SE-MEV for blockchain ecosystems, focusing on why incremental issuer - side fixes cannot fully remove SE-MEV , the implications for blockchain decentralization, and the protocol-dependent manifestation across different chains. Why Issuer -Side Hardening Is Not Enough. Our findings suggest that SE-MEV should not be understood as a narro w implementation flaw , but as a mechanism-le vel limitation of on-chain sanctions on public blockchains. The root cause is that sanction authority is expressed through ordinary transac- tions, while effecti ve enforcement is determined by economi- cally moti vated transaction ordering. From this perspecti ve, the USDT multisignature workflo w is best understood as an amplifier rather than the fundamental cause: by separating commitment from ex ecution, it enlarges the committed-but- not-yet-ef fectiv e window during which e vasion can occur , b ut the underlying vulnerability already exists whene ver enforce- ment must pass through the same ordering pipeline as the ev ading transfer . This also explains why simply hardening the issuer-side workflo w is insufficient. A single-transaction design, as in USDC-style enforcement, can reduce the extra delay intro- duced by a multi-step process, b ut it does not remo ve the core race. As long as the freeze remains an ordinary transaction, a sanctioned party can still compete for inclusion and ordering in the same block or along adjacent blocks. In other words, the problem is not only latency , but the lack of atomic coupling between sanction authority and final ex ecution ordering. For the same reason, partial compliance by some builders or pro- posers with OF AC constraints cannot fully resolv e the issue: heterogeneous visibility , pri vate order flo w , and synchroniza- tion gaps imply that enforcement cannot be guaranteed as long as ordering remains distrib uted across profit-dri ven actors and channels. The broader implication is that ef fective mitigation likely requires protocol- or infrastructure-lev el support, rather than issuer-side optimization alone. An y rob ust design w ould need to either move privile ged enforcement outside the ordinary public ordering path, or substantially reduce the visibility and synchronization gap before enforcement becomes ef fective. Possible directions include trusted sequencing, confidential or TEE-assisted ordering, or other mechanisms that provide stronger coupling between pri vileged actions and ex ecution priority . The GENIUS Act reinforces the mechanism our model identifies. By mandating that ev ery permitted issuer maintain freeze-or-b urn capability and comply with lawful blocking orders, the Act ensures that enforcement failur e is no longer a mere operational lapse but a statutory violation carrying per-day ci vil penalties of up to $100,000 and potential crim- inal liability . In the language of our model, this codifies a lower bound on Ψ that is anchored to the transaction value 15 (via IEEP A ’ s 2 × rule) and further augmented by ongoing per-day fines, making the MEV -tax escalation predicted by Corollary 1 a direct consequence of the tightening regulatory en vironment. W e leav e the design and e valuation of such mechanisms to future work; the main point here is that SE-MEV re veals a structural limit of public-chain enforcement, not merely a transient inefficienc y in current issuer implementations. Implications f or Decentralization. SE-MEV exposes a struc- tural erosion of blockchain decentralization driv en by regu- latory . T o comply with sanctions, stablecoin issuers are com- pelled to acti vely participate in the MEV supply chain. Owing to their scale, capital reserves, and organizational capacity , these issuers are naturally advantaged in competing for trans- action ordering power , allowing them to occupy privileged positions as dominant bidders, preferred counterparties, or tightly integrated participants in MEV infrastructure. More importantly , stablecoin issuers are themselves centralized en- tities subject to direct regulatory oversight. This creates an indirect but powerful channel through which state authori- ties can influence transaction ordering by exerting pressure on issuers rather than on the blockchain protocol itself. In this setting, decentralization is undermined not by explicit protocol-lev el censorship, but by the concentration of eco- nomic and operational control over ordering decisions in a small set of re gulated actors. As SE-MEV incentives intensify , transaction ordering increasingly reflects the constraints and objectiv es of these actors, weakening the decentralized secu- rity assumptions that permissionless blockchains are designed to uphold. Protocol-Dependent Manifestation. Although our empiri- cal analysis focuses on USDT and USDC on Ethereum, the core SE-MEV conflict is not limited to these assets or to Ethereum. It can arise for any centralized stablecoin (e.g., PYUSD, TUSD) that enforces sanctions through reactiv e, on-chain mechanisms, across both Layer -1 and Layer-2 sys- tems where transaction ordering is controlled by block pro- posers, builders, or sequencers whose decisions are economi- cally incenti vized. While the underlying incenti ves are shared, SE-MEV does not manifest uniformly across protocols. On Ethereum, where transaction ordering is mediated through an open, auction-based MEV market, SE-MEV tends to materi- alize as market capture, with stablecoin issuers incenti vized to become dominant bidders or to integrate tightly with MEV infrastructure. In contrast, on systems such as Tron, where ordering power is concentrated among a small, fixed set of validators and public auctions are absent, similar incenti ves may instead fa vor of f-chain coordination between stablecoin issuers and ordering authorities. These dif ferences highlight that SE-MEV is an unav oidable but protocol-dependent phe- nomenon, whose impact on decentralization is shaped by the specific design of transaction ordering mechanisms. 8 Related W orks Recent work has quantitati vely e xamined the impact of regu- lation and sanctions on blockchain systems. Zola et al. [ 22 ] analyze the effecti veness of financial sanctions on sanctioned entities in the Bitcoin ecosystem. W ahrstätter et al. [ 17 ] study blockchain censorship under regulatory pressure, analyzing how OF AC sanctions af fect transaction inclusion at the con- sensus and infrastructure layers. Liu et al. [ 11 ] in vestigate the effecti veness of blockchain sanctions using T ornado Cash as a case study on Ethereum, focusing on post-sanction fund propagation under enforcement. While these studies provide important insights into sanction-induced censorship and en- forcement effecti veness, they do not offer a comprehensive empirical analysis of on-chain sanction enforcement behavior itself across centralized stablecoins. The earliest empirical studies on Maximal Extractable V alue (MEV) were conducted by Daian et al. [ 7 ], with subse- quent contributions from T orres et al. [ 16 ] and Qin et al. [ 15 ]. These works laid the foundation for understanding the prev a- lence and impact of MEV in blockchain ecosystems. Later, W eintraub et al. [ 18 ] applied similar methods to measure the occurrence of MEV within pri v ate pools, while Li et al. [ 10 ] specifically examined MEV acti vities within Flashbots b un- dles. From a theoretical perspecti ve, Mazorra et al. [ 13 ] em- ployed game theory to analyze the strategies of MEV partici- pants, of fering a deeper understanding of their beha vior in the market. Additionally , v arious works hav e explored mitigation strategies for MEV at the DeFi application layer [ 12 , 14 , 21 ] or consensus layer [ 5 ], aiming to reduce its negati ve impacts on fairness and security . 16 References [1] Circle T oken Transparenc y , 2026. https://www. circle.com/multi- chain- usdc . [2] DefiLlama Stablecoins Data, 2026. https:// defillama.com/stablecoins . [3] T ether T oken Transparenc y, 2026. https://tether. to/ru/transparency/?tab=usdt . [4] 119th United States Congress. Guiding and estab- lishing national innov ation for U.S. stablecoins act (GENIUS act). https://www.congress.gov/bill/ 119th- congress/senate- bill/1582 , 2025. S.1582, signed into law July 18, 2025. [5] Jan Bormet, Sebastian Faust, Hussien Othman, and Ziyan Qu. { BEA T -MEV } : Epochless approach to batched threshold encryption for { MEV } prev ention. In 34th USENIX Security Symposium (USENIX Security 25) , pages 3457–3476, 2025. [6] Subhasish M Cho wdhury and Roman M Sheremeta. A generalized tullock contest. Public Choice , 147(3):413– 420, 2011. [7] Philip Daian, Stev en Goldfeder, T yler Kell, Y unqi Li, Xueyuan Zhao, Iddo Bento v , Lorenz Breidenbach, and Ari Juels. Flash boys 2.0: Frontrunning in decentralized exchanges, miner extractable v alue, and consensus insta- bility . In 2020 IEEE symposium on security and privacy (SP) , pages 910–927. IEEE, 2020. [8] European Parliament and Council of the Euro- pean Union. Regulation (EU) 2023/1114 of the European Parliament and of the Council of 31 May 2023 on markets in crypto-assets (MiCA). https://eur- lex.europa.eu/legal- content/ EN/TXT/?uri=CELEX:32023R1114 , 2023. OJ L 150, 9.6.2023, p. 40–205. Stablecoin provisions (Titles III–IV) applicable from 30 June 2024; full application from 30 December 2024. [9] Christian Ewerhart. Mixed equilibria in tullock contests. Economic Theory , 60(1):59–71, 2015. [10] Zihao Li, Jianfeng Li, Zheyuan He, Xiapu Luo, Ting W ang, Xiaoze Ni, W enwu Y ang, Xi Chen, and Ting Chen. Demystifying defi me v acti vities in flashbots b un- dle. In Pr oceedings of the 2023 A CM SIGSAC Confer - ence on Computer and Communications Security , pages 165–179, 2023. [11] Endong Liu, Mark Ryan, Liyi Zhou, and Pascal Berrang. Evasion under blockchain sanctions. arXiv preprint arXiv:2507.11721 , 2025. [12] Zuchao Ma, Muhui Jiang, Feng Luo, Xiapu Luo, and Y ajin Zhou. Surviving in dark forest: T ow ards e v ading the attacks from front-running bots in application layer . In Pr oceedings of the 34th USENIX Security Symposium (USENIX SEC) , 2025. [13] Bruno Mazorra, Michael Reynolds, and V anesa Daza. Price of mev: towards a game theoretical approach to me v . In Pr oceedings of the 2022 A CM cCS workshop on decentralized finance and security , pages 15–22, 2022. [14] Jason Milionis, Ciamac C Moallemi, and Tim Rough- garden. Automated market making and arbitrage profits in the presence of fees. In International Conference on F inancial Cryptography and Data Security , pages 159–171. Springer , 2024. [15] Kaihua Qin, Liyi Zhou, and Arthur Gervais. Quantifying blockchain extractable v alue: How dark is the forest? In 2022 IEEE Symposium on Security and Privacy (SP) , pages 198–214. IEEE, 2022. [16] Christof Ferreira T orres, Ramiro Camino, et al. Frontrun- ner jones and the raiders of the dark forest: An empirical study of frontrunning on the ethereum blockchain. In 30th USENIX Security Symposium (USENIX Security 21) , pages 1343–1359, 2021. [17] Anton W ahrstätter , Jens Ernstberger , A vi v Y aish, Liyi Zhou, Kaihua Qin, T aro Tsuchiya, Sebastian Steinhorst, Dav or Svetino vic, Nicolas Christin, Mikolaj Barczen- tewicz, et al. Blockchain censorship. In Pr oceedings of the ACM W eb Confer ence 2024 , pages 1632–1643, 2024. [18] Ben W eintraub, Christof Ferreira T orres, Cristina Nita- Rotaru, and Radu State. A flash (bot) in the pan: mea- suring maximal extractable value in priv ate pools. In Pr oceedings of the 22nd ACM Internet Measur ement Confer ence , pages 458–471, 2022. [19] Gavin W ood et al. Ethereum: A secure decentralised generalised transaction ledger . Ethereum pr oject yellow paper , 151(2014):1–32, 2014. [20] Sen Y ang, Kartik Nayak, and Fan Zhang. Decentral- ization of ethereum’ s builder market. In 2025 IEEE Symposium on Security and Privacy (SP) , pages 1512– 1530. IEEE, 2025. [21] Mengqian Zhang, Y uhao Li, Xinyuan Sun, Elynn Chen, and Xi Chen. Maximal extractable v alue in batch auc- tions. In Proceedings of the 26th A CM Conference on Economics and Computation , pages 510–510, 2025. [22] Francesco Zola, Jon Ander Medina, and Raúl Orduna. Assessing the impact of sanctions in the crypto ecosys- tem: Effecti ve measures or ineffecti ve deterrents? In 17 Eur opean Symposium on Resear ch in Computer Secu- rity , pages 292–308. Springer , 2024. A The Proofs Pr oof of Pr oposition 1 . W e condition on entry and suppress the fixed costs C I , C B , which do not affect equilibrium bids once both players participate. For b I + b B > 0, the contest success probabilities are P I = b r I b r I + b r B , P B = b r B b r I + b r B = 1 − P I . A standard first-order calculation gi ves the interior best re- sponses b I = Ψ rP I P B , b B = rP I V 1 + r P I . Hence any interior equilibrium must satisfy the bid formulas stated in Proposition 1 . Let s ∗ ≡ b ∗ I / b ∗ B > 0. Using P ∗ I = ( s ∗ ) r 1 + ( s ∗ ) r , P ∗ B = 1 1 + ( s ∗ ) r , and dividing the tw o equilibrium bid equations yields s ∗ 1 + ( s ∗ ) r 2 = Ψ V 1 + ( 1 + r )( s ∗ ) r . (1) Equiv alently , with Φ ( s ) ≡ s ( 1 + s r ) 2 1 + ( 1 + r ) s r , we hav e Φ ( s ∗ ) = Ψ / V . Under Assumption 1 , Lemma A.1 with N = 2 implies that any interior equilibrium must satisfy P ∗ I ≥ 1 / 2 , hence s ∗ ≥ 1 . On ( 0 , 1 ] , one checks that Φ ( s ) < 2 , so ( 1 ) has no solution there when Ψ / V ≥ 2 . On [ 1 , ∞ ) , Lemma A.2 shows that Φ is strictly increasing, while Φ ( 1 ) = 4 r + 2 < 2 ≤ Ψ V , Φ ( s ) → ∞ ( s → ∞ ) . Therefore ( 1 ) has a unique solution s ∗ > 1 , which pins down a unique interior equilibrium. In particular , P ∗ I > 1 / 2. For the e xpenditure bound, let T ∗ ≡ b ∗ I + P ∗ B b ∗ B . Since P ∗ I > 1 / 2 and b ∗ B = rP ∗ I V 1 + rP ∗ I is increasing in P ∗ I , b ∗ B > r r + 2 V . Also s ∗ > 1 implies T ∗ > b ∗ B . Hence T ∗ > r r + 2 V . Pr oof of Cor ollary 1 . By Lemma A.1 , s ∗ → ∞ as Ψ / V → ∞ . Using the equilibrium formulas from Proposition 1 , T ∗ V = r ( s ∗ ) r 1 + ( 1 + r )( s ∗ ) r s ∗ + 1 1 + ( s ∗ ) r ∼ r 1 + r s ∗ . Hence T ∗ / V → ∞ as Ψ / V → ∞ . Pr oof of Cor ollary 2 . The deriv ati ve formula is immediate from the definition of C total I . Let M ( Ψ , V ) ≡ − ∂ α C total I ( α ; V , Ψ ) = b ∗ I ( Ψ , V ) + P ∗ B ( Ψ , V ) Ψ . Using the equilibrium bid formulas from Proposition 1 , b ∗ I P ∗ B b ∗ B = Ψ V ( 1 + r P ∗ I ) . Under Assumption 1 , Ψ / V ≥ 2 , so b ∗ I ≥ 2 P ∗ B b ∗ B . Therefore, with T ∗ ≡ b ∗ I + P ∗ B b ∗ B , M ( Ψ , V ) ≥ b ∗ I ≥ 2 3 T ∗ . Combining this with Corollary 1 yields M ( Ψ , V ) V → ∞ as Ψ V → ∞ . Lemma A.1. F ix r ≥ 1 . Let ( b ∗ I , b ∗ B ) be any interior equilib- rium, and define s ∗ ≡ b ∗ I / b ∗ B and P ∗ I = ( s ∗ ) r 1 + ( s ∗ ) r . F or any N > 1 , if Ψ V ≥ N ( N − 1 ) 1 / r , then P ∗ I ≥ 1 − 1 N , s ∗ ≥ ( N − 1 ) 1 / r . Pr oof. Let x ≡ ( s ∗ ) r > 0. Then P ∗ I = x 1 + x , P ∗ I ≤ 1 − 1 N ⇐ ⇒ x ≤ N − 1 . Rewriting ( 1 ) in terms of x gi ves Ψ V = x 1 / r ( 1 + x ) 2 1 + ( 1 + r ) x . (2) Assume x ≤ N − 1. Since D ( x ) ≡ N 1 + ( 1 + r ) x − ( 1 + x ) 2 18 is concave and satisfies D ( 0 ) = N − 1 > 0 and D ( N − 1 ) = N r ( N − 1 ) ≥ 0, we hav e ( 1 + x ) 2 ≤ N 1 + ( 1 + r ) x for x ∈ [ 0 , N − 1 ] . Substituting this into ( 2 ) yields Ψ V ≤ N x 1 / r ≤ N ( N − 1 ) 1 / r . T aking the contrapositive pro ves the claim. Lemma A.2. Fix r ≥ 1 and define Φ ( s ) = s ( 1 + s r ) 2 1 + ( 1 + r ) s r , s ≥ 1 . Then Φ is strictly incr easing on [ 1 , ∞ ) . Pr oof. Let x = s r and write e Φ ( x ) ≡ x 1 / r ( 1 + x ) 2 1 + ( 1 + r ) x . Since x = s r is strictly increasing for s ≥ 1 , it suf fices to sho w that e Φ is increasing on [ 1 , ∞ ) . A direct calculation giv es d d x log e Φ ( x ) = Q ( x ) rx ( 1 + x ) 1 + ( 1 + r ) x , where Q ( x ) = 1 + ( 2 + 2 r − r 2 ) x + ( 1 + r ) 2 x 2 . The denominator is positiv e for x ≥ 1. Moreov er, Q ′ ( x ) = 2 + 2 r − r 2 + 2 ( 1 + r ) 2 x > 0 ( x ≥ 1 ) , and Q ( 1 ) = 4 ( r + 1 ) > 0 . Hence Q ( x ) > 0 for all x ≥ 1 , so d d x log e Φ ( x ) > 0 and therefore e Φ , and thus Φ , is strictly increasing on [ 1 , ∞ ) . Lemma A.3. If r ≥ 1 and Ψ / V ≥ 2 , then U ∗ I + C I > 0 . Pr oof. At an interior equilibrium, U ∗ I + C I = Ψ P ∗ I − b ∗ I . Using the issuer first-order condition from Proposition 1 , U ∗ I + C I = Ψ P ∗ I ( 1 − r P ∗ B ) . Thus it suffices to sho w P ∗ B < 1 / r , or equiv alently ( s ∗ ) r > r − 1 . Let x ≡ ( s ∗ ) r . From ( 1 ), Ψ V = x 1 / r ( 1 + x ) 2 1 + ( 1 + r ) x . If x ≤ r − 1, then ( 1 + x ) 2 ≤ 1 + ( 1 + r ) x , so Ψ V ≤ x 1 / r ≤ ( r − 1 ) 1 / r < 2 , contradicting Assumption 1 . Hence x > r − 1 , as required. 19
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment