Universe Reduction for APSP: Equivalence of Three Fine-Grained Hypotheses
The APSP Hypothesis states that the All-Pairs Shortest Paths (APSP) problem requires time $n^{3-o(1)}$ on graphs with polynomially bounded integer edge weights. Two increasingly stronger assumptions are the Strong APSP Hypothesis and the Directed Unw…
Authors: Nick Fischer
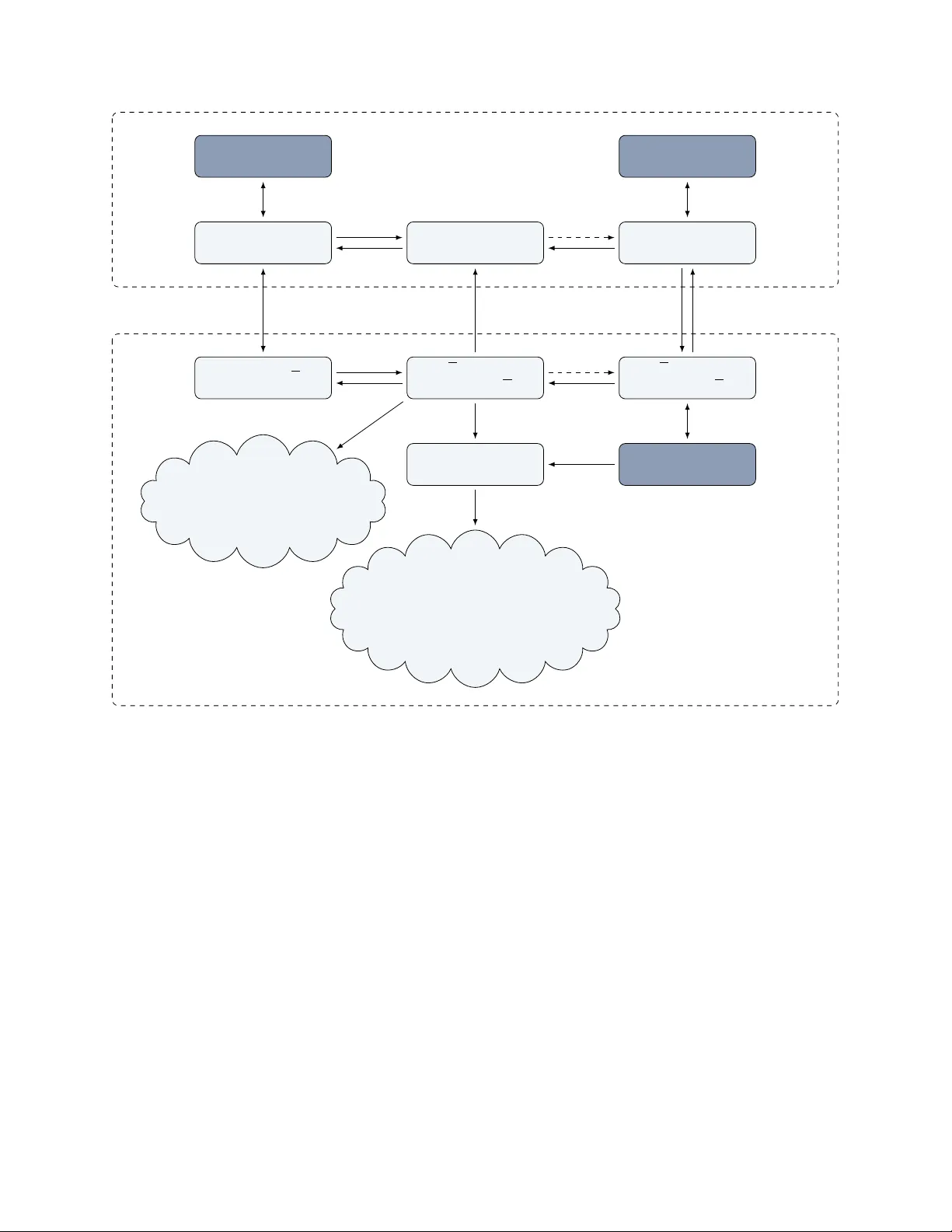
Univ erse Reduction for APSP: Equiv alence of Three Fine-Grained Hyp otheses Nic k Fisc her ∗ Abstract The APSP Hyp othesis states that the All-P airs Shortest Paths (APSP) problem requires time n 3 − o (1) on graphs with p olynomially bounded integer edge w eigh ts. T wo increasingly stronger assumptions are the Str ong APSP Hypothesis and the Dir e cte d Unweighte d APSP Hyp othesis , which state that the fastest-kno wn APSP algorithms on graphs with small w eights and un w eighted graphs, respectively , are b est-possible. In this paper, we design an efficient universe r e duction for APSP , which pro ves that these three hypotheses are, in fact, e quivalent , conditioned on ω = 2 and a plausible additive combinatorics assumption. Along the wa y , we resolv e the fine-grained complexity of many long-standing graph and matrix prob- lems with “intermediate” complexit y such as Node-W eigh ted APSP , All-Pairs Bottleneck Paths, Mono- tone Min-Plus Product in certain settings, and man y others, b y designing matching APSP-based low er b ounds. ∗ Max Planck Institute for Informatics. Email: nfischer@mpi-inf.mpg.de . Con ten ts 1 In tro duction 1 1.1 All-P airs Shortest Paths . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1 1.2 Univ erse Reductions for APSP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3 1.2.1 Small-Univ erse Reduction: F rom Small to No W eigh ts . . . . . . . . . . . . . . . . . . 3 1.2.2 Large-Univ erse Reduction: F rom Large to Small W eigh ts . . . . . . . . . . . . . . . . 3 1.2.3 Critical Remarks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5 1.3 APSP-Based Lo wer Bounds for Intermediate Problems . . . . . . . . . . . . . . . . . . . . . . 6 1.4 Pro of Ideas . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7 1.4.1 Select-Plus Rank . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8 1.4.2 Lo w-Rank Min-Plus Pro duct in Action . . . . . . . . . . . . . . . . . . . . . . . . . . . 8 1.4.3 Sub cubic Algorithm for Low-Rank Min-Plus Pro duct . . . . . . . . . . . . . . . . . . . 10 1.5 Real W eigh ts . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12 2 Preliminaries 12 2.1 APSP , Min-Plus Product and Exact T riangle . . . . . . . . . . . . . . . . . . . . . . . . . . . 13 2.2 P arameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13 2.3 P otential Adjustmen ts . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 14 2.4 A dditive Combinatorics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15 2.5 Mac hine Mo del . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15 3 Select-Plus Rank 16 3.1 Basic F acts . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16 3.2 Regular Rank Decompositions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16 4 Lo w-Rank Exact T riangle 19 4.1 Reduction from Lo w-Rank to Slice-Uniform Exact T riangle . . . . . . . . . . . . . . . . . . . 20 4.2 Reduction from Slice-Uniform to Uniform Exact T riangle . . . . . . . . . . . . . . . . . . . . 22 4.3 Reduction from Lo w-Rank to Uniform Regular Exact T riangle . . . . . . . . . . . . . . . . . 26 4.4 Reduction from Uniform Regular to Uniform Low-Doubling Exact T riangle . . . . . . . . . . 29 4.5 Putting the Pieces T ogether . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 31 5 Univ erse Reductions for Min-Plus Pro duct 32 5.1 Listing-to-Decision Reduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32 5.2 Small-Univ erse Reduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33 5.3 Doubling Reduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37 5.4 Large-Univ erse Reduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 41 6 Lo wer Bounds for In termediate Problems 43 6.1 No de-W eigh ted APSP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43 6.2 Min Product . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 44 6.3 Min-Max Product . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45 6.4 Min-Equalit y Pro duct . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45 6.5 Bounded-Difference and Monotone Min-Plus Pro duct . . . . . . . . . . . . . . . . . . . . . . . 46 6.6 Min-Witness Product . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 50 A Sum-Order-Preserving Hashing 58 A.1 Quasi-P olynomial Bounds . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 58 A.2 P olynomial Bounds? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 60 B Derandomization of the Conflict-F ree Cov ering Lemma 61 1 In tro duction The ov erarc hing goal of fine-grained complexity is to pinpoint the exact complexity of polynomial-time prob- lems conditioned on a small set of believ able core assumptions. Over the y ears, three such hypotheses hav e crystallized: SETH [ 67 , 68 ], the 3SUM Hyp othesis [ 56 ], and the APSP Hyp othesis [ 97 ]. In this mo dern view, a problem is considered “closed” when we can establish b oth an n c + o (1) upp er b ound and a matching n c − o (1) lo wer bound conditioned on one of these three assumptions. The framework has become a ma jor success story , resolving the exact complexit y of n umerous imp ortan t problems in P . Y et man y other cen tral problems currently resist lo wer b ounds under these “primary” assumptions. A common w ork around is to resort to stronger “secondary” h yp otheses (suc h as Quan tified SETH [ 21 ], Strong 3SUM [ 10 ], and Minimum-W eigh t k -Clique [ 7 ], to name a few). Often, these secondary assumptions p ostulate that the primary problems are hard ev en on restricted instances (as is the case for Strong 3SUM and Minim um-W eight k -Clique). On the one hand, these v arian ts are extremely helpful: they are typically easier to reduce from, and we still regard them as “morally equiv alen t” to their primary coun terparts. On the other hand, these secondary h yp otheses are, of course, less con vincing. Unlik e the three core assumptions, they often lack decades of effort dedicated to breaking them. As a result, while conditional lo wer b ounds based on secondary hypothes es are still seen as strong hardness barriers, they must b e taken with a grain of salt. Another drawbac k is conceptual: With every new hypothesis we mo ve a little further a wa y from the dream goal of classifying the complexit y in P conditioned on a smal l set of core assumptions. This naturally rais es an imp ortan t quest in fine-grained complexity: to r elate our primary and secondary h yp otheses to each other, ideally reducing all of our secondary assumptions back to the original three primary ones. Unfortunately , so far there has b een little progress in this direction. In this paper, w e take one of the first significant steps. W e consider the APSP Hyp othesis and tw o of its prominen t secondary v ariants, and prov e that these three hypotheses are not only morally related but are in fact e quivalent , mo dulo the assumption ω = 2 and some plausible additive combinatorics assumption. Along the w ay we derive strong APSP-based low er b ounds—man y of whic h resolve long-standing op en problems. 1.1 All-P airs Shortest P aths The Al l-Pairs Shortest Paths (APSP) problem is to compute all pairs of distances in an edge-w eighted graph. F ew other graph problems ha v e spark ed as muc h atten tion as the quest for fast algorithms for APSP . Y et in the 60 y ears since the classic O ( n 3 ) -time Flo yd–W arshall algorithm [ 54 , 100 ], a long line of impro vemen ts [ 54 , 100 , 55 , 46 , 91 , 62 , 92 , 105 , 93 , 30 , 63 , 31 , 64 ] only shav ed off p olylogarithmic factors, culminating in Williams’ [ 101 , 36 ] curren t b est b ound of n 3 / 2 O ( √ log n ) . Whether this can be improv ed to truly sub cubic time O ( n 2 . 99 ) , say , remains a ma jor op en question. With the rise of fine-grained complexity in the 2010s, this barrier was rein terpreted as a hardness assumption [ 97 ], which has since evolv ed in to one of the three primary hypotheses of the area: Hyp othesis 1.1 (APSP) . F or every c onstant ϵ > 0 ther e is a c onstant c such that APSP on gr aphs with weights in { 0 , . . . , n c } c annot b e solve d in time O ( n 3 − ϵ ) . 1 2 3 The APSP Hypothesis forms the basis for fine-grained low er bounds for many imp ortan t problems, including natural graph and matrix problems [ 97 , 13 , 65 , 74 , 5 , 72 ], tree edit distance [ 24 , 80 ], triangle 1 Unless stated otherwise we assume that graphs are directed. How ever, it is known that Hyp othesis 1.1 holds equiv alently for directed and undirected graphs [ 97 ]. 2 Here and throughout we only consider nonnegative weigh ts, although it is equiv alent to assume weigh ts in {− n c , . . . , n c } . Indeed, with Johnson’s trick [ 71 ], it suffices to solve a Single-Source Shortest Paths instance (e.g., using [ 19 ]) to compute a potential function that transforms negative weigh ts into nonnegative integers. 3 In many pap ers the dep endence b et ween ϵ and c is not made explicit. In particular, another reasonable formulation of the hypothesis is to change the quan tifiers, i.e., to postulate that there is some absolute constan t c such that for all ϵ > 0 APSP on graphs with weigh ts { 0 , . . . , n c } cannot b e solved in time O ( n 3 − ϵ ) . W e consider the weak er Hyp othesis 1.1 throughout (so that our results take the strongest form). In fact, one could weak en the hypothesis further to w eights bounded b y exp( n o (1) ) and our results would still apply . 1 listing [ 98 ], as w ell as approximate [ 2 , 37 ] and dynamic problems [ 6 , 98 ], even in planar graphs [ 3 ]. In fact, man y such problems hav e b een shown not merely to b e APSP-hard, but APSP-equiv alen t. The tw o secondary hypotheses we consider can b oth b e seen as strengthenings of the APSP hypothesis concerning graphs with smal l w eights and no weigh ts. (In fact, the restriction to small-weigh t instances is a common secondary pattern, see e.g. the Strong 3SUM [ 10 ], Strong Zero T riangle [ 2 ] and Strong Min-Plus Con volution [ 33 ] Hyp otheses.) Sp ecifically , the fastest-known algorithm for graphs with w eights in { 0 , . . . , u } runs in time ˜ O ( n ω u ) [ 9 ], where 2 ≤ ω < 2 . 372 is the matrix multiplication exp onen t [ 8 ]. Th us, for a univ erse of size u = n 3 − ω the fastest-kno wn algorithms take cubic time n 3 − o (1) , and it is plausible to hypothesize that this is b est-possible. Chan, V assilevsk a W., and Xu [ 35 ] first prop osed this as the following hardness assumption, whic h has b ecome the basis for several conditional low er bounds [ 35 , 66 ]: Hyp othesis 1.2 (Strong APSP) . F or every c onstant ϵ > 0 , APSP on gr aphs with weights in { 0 , . . . , n 3 − ω } c annot b e solve d in time O ( n 3 − ϵ ) . Con versely , APSP on graphs with w eights smaller than n 3 − ω and therefore also unweighte d directed graphs is kno wn to be in sub cubic time. The fastest-known algorithm for this problem is due to Zwick [ 104 ] and runs in time ˜ O ( n 2+ µ ) = ˜ O ( n 2 . 528 ) . This running time dep ends on a rectangular matrix multiplication constan t 4 0 . 5 ≤ µ ≤ 0 . 528 and becomes ˜ O ( n 2 . 5 ) if ω = 2 . This time b ound has not b een c hallenged for more than 20 years, which recen tly led Chan, V assilevsk a W., and Xu [ 33 ] to hypothesize that Zwick’s algorithm is best-p ossible. Hyp othesis 1.3 (Directed Un w eighted APSP) . F or every c onstant ϵ > 0 , APSP on dir e cte d unweighte d gr aphs c annot b e solve d in time O ( n 2+ µ − ϵ ) . This hypothesis turns out to b e surprisingly p o werful—it is equiv alen t to v arious ˜ O ( n 2+ µ ) -time prob- lems [ 33 ], and conditionally resolves the complexit y of man y well-studied graph problems with “intermediate” complexit y; see the discussion below in Section 1.3 . Min-Plus Pro duct. T o relate these three h yp otheses, it is helpful to introduce some more background. The min-plus pr o duct of tw o matrices A and B of size n 1 × n 2 and n 2 × n 3 , resp ectiv ely , is the matrix A ∗ B of size n 1 × n 3 defined by ( A ∗ B )[ i, j ] = min k ( A [ i, k ] + B [ k , j ]) . W e refer to the problem of computing A ∗ B as the Min-Plus Pr o duct problem, and w e denote its complexit y by MinPlus( n 1 , n 2 , n 3 ) . W e sometimes annotate b ounds on the maximum en try u in the three matrices by MinPlus( n 1 , n 2 , n 3 | u ) . It is a long- kno wn fact that the complexity of APSP is exactly MinPlus( n, n, n ) (up to n o (1) factors). Via tw o elegant reductions [ 90 , 36 ] one can similarly give equiv alent characterizations of the Strong and Directed Unw eigh ted APSP Hypotheses in terms of some Min-Plus Product problems: Hyp othesis 1.4 (APSP) . MinPlus( n, n, n ) = n 3 ± o (1) . Hyp othesis 1.5 (Strong APSP [ 90 ]) . MinPlus( n, n, n | u ≤ n 3 − ω ) = n 3 ± o (1) . Hyp othesis 1.6 (Directed Unw eighted APSP [ 33 ]) . MinPlus( n, n µ , n | u ≤ n 1 − µ ) = n 2+ µ ± o (1) . F rom these characterizations it is easy to read off that, when ω = 2 , the Directed Un weigh ted APSP Hyp othesis implies the Strong APSP Hypothesis. 5 In summary , the three assumptions get incr e asingly str onger —i.e., the Directed Unw eigh ted APSP Hyp othesis implies the Strong APSP Hyp othesis (if ω = 2 ) whic h in turn implies the APSP Hypothesis. 4 Namely , the constant µ satisfying that ω (1 , µ, 1) = 1 + 2 µ , where ω ( · , · , · ) is the rectangular matrix multiplication exp onen t. 5 Note that MinPlus( n, √ n, n | u ≤ √ n ) = O ( n · MinPlus( √ n, √ n, √ n | u ≤ √ n )) . Thus, MinPlus( n, n, n | u ≤ n ) = O ( n 3 − ϵ ) implies that MinPlus( n, √ n, n | u ≤ √ n ) = O ( n 2 . 5 − ϵ/ 2 ) . 2 1.2 Univ erse Reductions for APSP The main goal of this pap er is to establish that these three hypotheses are actually equiv alent. It is reasonable to exp ect that suc h an equiv alence result hinges on the assumption that ω = 2 ; we will later commen t on this issue in detail, but for now assume that ω = 2 . The t wo missing “hard” directions can b oth b e seen as universe r e ductions for APSP: from large (p olynomially b ounded) weigh ts to weigh ts b ounded b y n ( lar ge- universe r e duction ), and from w eights bounded b y n to no weigh ts at all ( smal l-universe r e duction ). W e start with the latter task which turns out to b e the slightly simpler one. 1.2.1 Small-Univ erse Reduction: F rom Small to No W eigh ts There has b een partial progress tow ards a small-univ erse reduction. In the same pap er that introduces the Strong APSP Hyp othesis, Chan, V assilevsk a W., and Xu [ 35 ] develop an exciting tec hnique called “F redman’s tric k meets dominance pro duct” and thereby establish a non-tigh t reduction: Directed Unw eigh ted APSP cannot b e solved in time O ( n 7 / 3 − ϵ ) unless the Strong APSP Hyp othesis fails. Ultimately , they left op en if the tw o hypotheses are equiv alent, but their tec hnique is inspiring. W e prop ose a new approac h, low-r ank APSP, and based on this new technique we successfully prov e the desired equiv alence result: Theorem 1.7 (Strong APSP Implies Directed Unw eighted APSP) . APSP in dir e cte d unweighte d gr aphs c annot b e solve d in time O ( n 2 . 5 − ϵ ) (for any c onstant ϵ > 0 ), unless the Str ong APSP Hyp othesis fails. In p articular, c onditione d on ω = 2 , the Str ong APSP and Dir e cte d Unweighte d APSP Hyp otheses ar e e quivalent. Theorem 1.7 constitutes one of the very rare cases that tw o fine-grained h yp otheses are shown to be equiv alen t—in fact, we are not aw are of any prior case where tw o explicitly established fine-grained assump- tions hav e later b een sho wn to b e equiv alent. Moreov er, Theorem 1.7 constitutes an equiv alence result of t wo problems with the same input and output size but differ ent complexities ( n 3 v ersus n 2 . 5 ). This, to o, is quite exceptional; there are only few other examples suc h as the Mono-Conv olution problem by Lincoln, V assilevsk a W., and Polak [ 73 ]. More generally , our universe reduction correctly interpolates b et w een un weigh ted and [ n ] -w eighted graphs, b oth in the directed and undirected settings. Sp ecifically , for directed graphs with weigh ts { 0 , . . . , u } Zwick’s algorithm [ 104 ] tak es time ˜ O ( n 2+1 / (4 − ω ) u 1 / (4 − ω ) ) . If ω = 2 then this running time b ecomes ˜ O ( n 2 . 5 √ u ) . F or undirected graphs with weigh ts { 0 , . . . , u } the Shoshan–Zwick algorithm [ 90 ] takes time ˜ O ( n ω u ) . W e show b oth algorithms are b est-possible if ω = 2 , for all v alues of u : Theorem 1.8 (Zwick’s Algorithm is Optimal) . L et 0 ≤ δ ≤ 1 b e a c onstant. APSP in dir e cte d gr aphs with weights { 0 , . . . , n δ } c annot b e solve d in time O ( n 2 . 5+ δ / 2 − ϵ ) (for any c onstant ϵ > 0 ), unless the Str ong APSP Hyp othesis fails. Theorem 1.9 (Shoshan–Zwic k Algorithm is Optimal) . L et 0 ≤ δ ≤ 1 b e a c onstant. APSP in undir e cte d gr aphs with weights { 0 , . . . , n δ } c annot b e solve d in time O ( n 2+ δ − ϵ ) (for any c onstant ϵ > 0 ), unless the Str ong APSP Hyp othesis fails. 1.2.2 Large-Univ erse Reduction: F rom Large to Small W eigh ts Next, fo cus on the univ erse reduction from p olynomially large w eights to weigh ts bounded b y n . This reduction app ears even more difficult. In fact, we are neither aw are of any prior progress on this question, nor are we aw are of an y other (exact) graph distance problem where a similar weigh t reduction is known. In the related, more restricted setting where one graph has to b e mapp ed one-to-one to a graph with smaller w eights such a reduction turns out to b e imp ossible [ 18 ]. Our approach inv olves tw o steps. The first builds on the new low-r ank APSP tec hnique from b efore. The second builds on additive c ombinatorics . In fact, the low-r ank APSP tec hnique also relies on some additive com binatorics, so this w ork should b e seen as part of a recen t trend to exploit additiv e com binatorics in fine-grained complexit y and algorithm design [ 32 , 27 , 50 , 29 , 28 , 1 , 35 , 70 , 39 , 20 , 69 , 41 , 38 , 40 , 23 , 52 , 53 , 4 ]. 3 Step 1: Doubling Reduction. W e start with the first and technically more inv olv ed step. Sp ecifically , w e establish that APSP on general graphs with p olynomially b ounded w eights can b e reduced to graphs with at most n distinct w eights (i.e., muc h fewer than the trivial upper bound of n 2 ). In addition, w e can enforce that there are only few distinct sums of tw o weigh ts. T o formalize this requirement we use the follo wing notation: F or an integer set X w e write X + X = { x + y : x, y ∈ X } to denote its so-called sumset . In the additiv e combinatorics literature the ratio | X + X | / | X | is typically called the doubling of X (hence the term “doubling reduction”). F ormally w e pro ve: Theorem 1.10 (Uniform Lo w-Doubling APSP) . L et κ > 0 b e a c onstant. APSP in gr aphs with inte ger weights X ⊆ Z wher e | X | ≤ n and | X + X | ≤ n κ | X | c annot b e solve d in time O ( n 3 − ϵ ) (for any c onstant ϵ > 0 ), unless the APSP Hyp othesis fails. Theorem 1.10 is already a strong and arguably surprising result. Even ignoring the extra constraint on the doubling of X , it demonstrates that the worst-case APSP instances ha ve only n distinct w eights (rather than the naiv e upper b ound of n 2 )! An appropriate technical generalization of Theorem 1.10 is the key to ol for v arious interesting fine-grained low er b ounds (that we will survey so on). W e are optimistic that it will b e similarly helpful in the design of future APSP-based low er b ounds. Step 2: Sum-Order-Preserving Hashing. But ho w is Theorem 1.10 useful for the desired universe reduction? T o understand this, let us take a step back and forget ab out Theorem 1.10 for a minute, to review a naiv e hashing-b ase d approac h for the universe reduction. At first though t hashing app ears to b e a reasonable idea—after all, for man y problems (suc h as 3SUM) we can analogously obtain weigh t reductions using additiv e hash functions. But as we will see, naively this approach is b ound to fail. In the language of Hyp otheses 1.4 and 1.5 our goal is to reduce the computation of a min-plus pro duct of t wo arbitrary n × n matrices A, B to the computation of a min-plus pro duct with entries b ounded b y n . Let X ⊆ Z b e the set of entries that app ear in A and B . Supp ose there was a hash function h : X → { 0 , . . . , n } satisfying the property that for all x 1 , x 2 , y 1 , y 2 ∈ X : x 1 + x 2 < y 1 + y 2 implies h ( x 1 ) + h ( x 2 ) < h ( y 1 ) + h ( y 2 ) . W e call such a function h sum-or der-pr eserving. W e could then define matrices A ′ = h ( A ) and B ′ = h ( B ) (where we apply h en try-wise) whic h, as desired, ha ve entries b ounded by n , and we could read off A ∗ B from A ′ ∗ B ′ with the aid of some standard tricks. 6 Unfortunately , clearly such a hash function cannot exist in general! There are up to | X | 2 distinct sums of the form x + y , which in the worst case is up to n 4 , but only O ( n ) p ossible v alues for h ( x ) + h ( y ) . By the pigeonhole principle there is necessarily a collision h ( x 1 ) + h ( x 2 ) = h ( y 1 ) + h ( y 2 ) for some x 1 + x 2 < y 1 + y 2 . So it seems that the hashing-based idea is fundamen tally flaw ed. This is where Theorem 1.10 comes in to pla y . It allows us to assume that the sumset X + X does not ha ve size up to n 4 as the trivial b ound would suggest, but rather only roughly line ar in n . F or this reason it would b e sufficient to ha ve a sum-order-preserving hash function h : X → { 0 , . . . , | X + X |} . The previous pigeonhole argument do es not rule out suc h a function. So could it p ossibly b e the case that such a hash function alw ays exists? At least in the relev ant special case when X has small doubling, i.e., when | X + X | is small? The surprising answer is: y es, almost! By combining tw o results from additiv e combinatorics—the first b y Amirkhan yan, Bush, and Cro ot [ 11 ] on so-called order-preserving F reiman isomorphisms, and second, the quasi-p olynomial b ounds for the F reiman-Ruzsa theorem due to Sanders [ 87 ]—one obtains the follo wing theorem stating that for an y small-doubling set X there exists a reasonably large subset Y ⊆ X that can b e hashed by a sum-order-preserving hash function. (See Appendix A.1 for how to derive Theorem 1.11 from [ 11 , 87 ].) 6 Specifically , call k a witness of ( i, j ) in A ∗ B if ( A ∗ B )[ i, j ] = A [ i, k ] + B [ k, j ] . Then the sum-order-preserving property implies that any witness k of ( i, j ) in A ′ ∗ B ′ is also a witness of ( i, j ) in A ∗ B . Moreov er, by a standard trick we can turn any algorithm to compute the min-plus pro duct of tw o matrices into an algorithm that also rep orts a witness for each en try ( i, j ) ; see Lemma 5.1 . 4 Theorem 1.11 (Sum-Order-Preserving Hashing with Quasi-Polynomial Bounds [ 11 , 87 ]) . F or every inte ger set X with doubling | X + X | ≤ K | X | ther e is a subset Y ⊆ X of size | Y | ≥ | X | / exp((log K ) O (1) ) and a sum-or der-pr eserving function h : Y → { 0 , . . . , | X |} . Unfortunately , Theorem 1.11 is slightly to o weak. In principle it is acceptable that only a subset Y ⊆ X admits the sum-order-preserving hash function (as with some further ov erhead we can cov er X by few trans- lates of Y ); how ev er, the quan titative b ounds on | Y | are not strong enough for our purp oses. Theorem 1.11 en tails that Y cov ers at least a fraction of X that dep ends quasi-p olynomial ly on K , but we would require a dependence that is at most p olynomial. This is a common c hallenge in additive com binatorics. In fact, it is a ma jor conjecture in additive com binatorics, termed the Polynomial F r eiman-Ruzsa (PFR) Conje ctur e (see e.g. [ 103 ] and also [ 76 , 77 ]), that Sanders’ [ 87 ] aforementioned quasi-p olynomial b ounds for the F reiman-Ruzsa theorem can b e impro ved to polynomial. Notably , in a recen t breakthrough, Go wers, Green, Manners, and T ao [ 59 ] hav e positively resolved the PFR conjecture in characteristic 2 . Their result do es not ha ve immediate implications for the integer case—in fact, they leav e the integer case as a “challenging op en problem”. In an even more recent preprint, Ragha- v an [ 82 ] further impro ved the integer PFR b ound to exp((log K ) 1+ o (1) ) . Given these promising dev elopments there is reason to b e optimistic that the PFR Conjecture will ev entually b e p ositiv ely resolved and that ide- ally along the w ay the bounds in Theorem 1.11 can b e improv ed to p olynomial. W e formulate this as the follo wing plausible hypothesis: Hyp othesis 1.12 (Sum-Order-Preserving Hashing with Polynomial Bounds) . Ther e is a c onstant c such that for every inte ger set X with doubling | X + X | ≤ K | X | ther e is a subset Y ⊆ X of size | Y | ≥ Ω( | X | /K c ) and a sum-or der-pr eserving function h : Y → { 0 , . . . , | X |} . Mor e over, given X one c an c ompute Y and h in time | X | 1+ o (1) K O (1) . W e defer further discussion of Hypothesis 1.12 to App endix A.2 , and instead finally return to the APSP univ erse reduction. Com bined with Theorem 1.10 and a couple of other tricks, Hyp othesis 1.12 implies the desired univ erse reduction for APSP: Theorem 1.13 (APSP Conditionally Implies Strong APSP) . Conditione d on Hyp othesis 1.12 , ther e is a sub cubic r e duction fr om APSP to APSP over the universe { 0 , . . . , n } . In p articular, c onditione d on Hyp oth- esis 1.12 and on the assumption that ω = 2 , the APSP and Str ong APSP Hyp otheses ar e e quivalent. 1.2.3 Critical Remarks Ultimately we reach our goal, pro ving that the APSP , Strong APSP and Directed Un weigh ted APSP Hy- p otheses are equiv alent, only conditioned on tw o strong assumptions: ω = 2 and Hypothesis 1.12 . Let us tak e a moment to scrutinize these t wo assumptions. On the one hand, it is to b e exp ected that we hav e to assume ω = 2 . The reason is that the Strong APSP and Directed Un weigh ted APSP Hyp otheses b oth dep end on tw o differ ent matrix multiplication constan ts, ω and µ , and so the equiv alence would (in a sense) tightly relate ω and µ . Ho wev er, these constants are only kno wn to b e lo osely related by trivial b ounds like µ ≤ 1 / (4 − ω ) . Only if ω = 2 (and thus µ = 1 2 ) would this trivial b ound b ecome tight, and so only if ω = 2 would the hypothetical equiv alence not hav e surprising implications for the matrix m ultiplication constants. Finally , w e emphasize that all of our results remain meaningful ev en in a w orld with ω > 2 . On the other hand, despite our confidence that Hyp othesis 1.12 is plausible, it is a new assumption and should th us b e considered with some care. W e find it somewhat ironic that we show that some fine-grained h yp otheses are equiv alen t at the cost of introducing yet another new h yp othesis. How ev er, we b eliev e that there is significant v alue in this conditional equiv alence result. First, Hyp othesis 1.12 is not a fine-gr aine d c omplexity assumption, but rather a purely mathematic al assumption, whic h w e hope will b e even tually resolv ed or refuted by the additiv e combinatorics communit y alongside their effort to resolve the p olynomial F reiman-Ruzsa conjecture. In this sense, w e view it as remotely analogous to the (admittedly m uch more established) Extended Riemann Hyp othesis that some modern algorithms rely on. 5 Second, intuitiv ely it seems unav oidable to rely on Hyp othesis 1.12 or a similar additiv e com binatorics assumption. The v ague reason is that we can embed [ u ] in man y w ays in to lo w-doubling sets X , for instance, b y stretc hing [ u ] to an arithmetic progression X = { a, 2 a, . . . , ua } . A universe reduction would effectively invert this embedding. But then it would implicitly answer the structural question b ehind the F reiman-Ruzsa theorem, namely if all low-doubling sets can b e co vered by progression-like sets. Third, and p erhaps most imp ortan tly , for the APSP-based low er b ounds we dev elop along the wa y it is not necessary to assume Hyp othesis 1.12 . W e will now elab orate on these lo wer b ounds in detail. 1.3 APSP-Based Lo w er Bounds for In termediate Problems An extensive line of work in the fine-grained algorithms and complexity literature is concerned with studying graph problems of “in termediate” complexity , i.e., with complexity strictly betw een ˜ O ( n ω ) and O ( n 3 ) . On the upp er b ound side this trend started in the 2000s [ 104 , 95 , 89 , 49 , 96 , 47 , 48 , 31 , 102 , 4 , 97 , 17 , 45 , 60 , 26 ]. Most algorithms follow the same high-level sc heme: One identifies a matrix m ultiplication-type problem that exactly captures the complexit y of the graph problem, and then designs specialized algorithms for that matrix problem. A prominent example is Dir e cte d Unweighte d APSP which, as men tioned before, can be solv ed b y Zwic k’s algorithm [ 104 ] in time ˜ O ( n 2+ µ ) . The corresp onding matrix problem is the min-plus product of tw o rectangular matrices with b ounded en tries. Progress on the low er b ound side is more recent. Several works [ 15 , 73 , 98 , 33 ] established fine-grained connections b etwe en in termediate problems (ev en on the finer-grained scale that distinguishes betw een run- ning times like n (3+ ω ) / 2 ± o (1) and n 2+ µ ± o (1) , say [ 98 ]). These connections imply matching low er b ounds only conditioned on secondary h yp otheses such as the Directed Un weigh ted APSP Hyp othesis (which itself is ab out a problem of intermediate complexity). As men tioned b efore, there is one result b esides these mostly simple connections that stands out: In their work on F r e dman ’s T rick me ets Dominanc e Pr o duct , Chan, V assilevsk a W., and Xu give non-matching lo wer b ounds for v arious intermediate problems conditioned on the Strong APSP Hypothesis. This is still a secondary assumption, but their ideas are inspiring and can to some degree be seen as the baseline for this pap er. In summary , despite significant effort, prior to this work no non-trivial low er b ounds under the primary h yp otheses are kno wn for an y intermediate problem—not even non-matching n 2 . 1 − o (1) lo wer b ounds. F rom our equiv alence result (Theorems 1.7 and 1.13 ) it follows immediately that we can turn the Di- rected Un weigh ted APSP-based low er bounds into APSP-based ones, assuming that ω = 2 and the additive c ombinatorics Hyp othesis 1.12 . This result already leads to exciting new APSP-based lo wer b ounds for many problems that are additionally conditioned on tw o extra assumptions (Hyp othesis 1.12 and ω = 2 ). Ho wev er, it turns out that we can ev en remov e these t wo extra assumptions! The reason is that our reductions only dep end on step 1 (the unconditional doubling reduction) from b efore. W e th us obtain clean n 2 . 5 − o (1) -time low er b ounds for man y imp ortan t intermediate problems based on the APSP Hypothesis. In all cases, these match the kno wn upper b ounds if ω = 2 . This statement is essen tially the strongest conditional lo w er bound one could hop e for, 7 so our work successfully closes the resp ectiv e in termediate problems. W e now discuss three particularly interesting cases in detail, and lea ve further low er b ounds to Section 6 . Lo wer Bound 1: Node-W eighted APSP. The first subcubic-time algorithm for APSP on directed no de-weighte d graphs is due to Chan [ 31 ] and runs in time ˜ O ( n (9+ ω ) / 4 ) = O ( n 2 . 843 ) . This was later im- pro ved by Y uster [ 102 ] using rectangular matrix multiplication. Only v ery recently , Abboud, Fisc her, Jin, V assilevsk a W., and Xi [ 4 ] obtained an algorithm in time ˜ O ( n (3+ ω ) / 2 ) (with slight improv ements using rectan- gular matrix m ultiplication). In [ 33 ] it was observed that No de-W eighted APSP (even in undirected graphs) is at least as hard as Directed Unw eigh ted APSP . Here we give the strengthened lo wer b ound based on the primary APSP Hypothesis: 7 Perhaps a first instinct would be to hop e for higher low er b ounds, say n (3+ ω ) / 2 − o (1) . Lo wer bounds of this type can only be exp ected for hypotheses which themselves depend on ω , lik e the Strong APSP Hyp othesis. The APSP Hyp othesis is agnostic of ω , hence a low er b ound higher than n 2 . 5 would imply low er b ounds on ω conditioned on the APSP Hyp othesis. 6 Theorem 1.14 (No de-W eigh ted APSP) . APSP in undir e cte d no de-weighte d gr aphs c annot b e solve d in time O ( n 2 . 5 − ϵ ) (for any c onstant ϵ > 0 ), unless the APSP Hyp othesis fails. Lo wer Bound 2: All-Pairs Bottleneck Paths. The A l l-Pairs Bottlene ck Paths (APBP) problem is to compute, for all pairs of no des s, t in a directed edge-capacitated graph, the maximum flow that can b e routed on one path from s to t . The complexity of APBP is exactly captured by the complexity of computing the min-max pr o duct of t wo matrices (see Section 6.3 ), and based on this insight V assilevsk a, Williams, and Y uster [ 95 ] designed the first sub cubic-time algorithm for APBP , running time ˜ O ( n 2+ ω / 3 ) = O ( n 2 . 791 ) . A t the time they raised the question if APBP can be solved in matrix m ultiplication time ˜ O ( n ω ) . Their algorithm was later improv ed by Duan and Pettie [ 49 ] to time ˜ O ( n (3+ ω ) / 2 ) . W e sho w that Duan and Pettie’s algorithm is best-p ossible (if ω = 2 ), and consequen tly that time ˜ O ( n ω ) cannot be achiev ed. Theorem 1.15 (All-Pairs Bottleneck P aths) . Al l-Pairs Bottlene ck Paths c annot b e solve d in time O ( n 2 . 5 − ϵ ) (for any c onstant ϵ > 0 ), unless the APSP Hyp othesis fails. Via kno wn reductions, Theorem 1.15 settles the complexit y of even more problems. F or instance, the A l l-Pairs Nonde cr e asing Paths (APNP) problem is to compute, for all pairs of no des s, t in a directed edge-w eighted graph, the smallest weigh t w such that there is an s - t -path along whic h the w eights are nondecreasing and at most w . When the edge weigh ts mo del de parture times, this can be interpreted as tra veling from s to t in the fastest p ossible time. The first sub cubic-time algorithm is due to V assilevsk a [ 96 ], and later impro vemen ts due to Duan, Gu, Zhang [ 47 ] and Duan, Jin, W u [ 48 ] hav e optimized the time complexit y to ˜ O ( n (3+ ω ) / 2 ) . APNP is kno wn to generalize APBP [ 96 ], and th us Theorem 1.15 provides a matc hing APSP-based low er bound. As a final example, Bringmann, Künnemann, and Węgrzycki [ 26 ] prov ed that APBP is further equiv alen t to (1 + ϵ ) -Appr oximate APSP for str ongly p olynomial algorithms (i.e., for algorithms for whic h the n umber of arithmetic op erations do es not dep end on the univ erse size u ). Thus, combined with Theorem 1.15 we obtain a matc hing lo wer bound. Lo wer Bound 3: Bounded-Difference and Monotone Min-Plus Pro duct. An imp ortan t sp ecial case of the Min-Plus Product problem is to consider matrices A where all adjacent entries differ at most by a constant. Bringmann, Grandoni, Saha, and V assilevsk a W. [ 25 ] first designed a sub cubic-time algorithm for this sp ecial case, and as a consequence developed faster algorithms for string problems lik e language edit distance and RNA-folding; see also [ 78 ]. This inspired a line of researc h [ 99 , 61 , 43 , 44 ] to optimize the sub cubic running time that recently led to the state-of-the-art ˜ O ( n (3+ ω ) / 2 ) -time algorithm due to Chi, Duan, Xie, and Zhang [ 44 ]. In fact, they give tw o different algorithms to treat the strictly more general cases where A is r ow-monotone or c olumn-monotone . W e prov e that the first algorithm is optimal, conditioned on the APSP Hyp othesis; w e leav e op en whether the second algorithm is similarly optimal. Theorem 1.16 (Row-Bounded-Difference Row-Monotone Min-Plus Pro duct) . The min-plus pr o duct of a r ow-b ounde d-differ enc e, r ow-monotone matrix A ∈ Z n × n and a c olumn-b ounde d-differ enc e, c olumn-monotone matrix B ∈ Z n × n c annot b e c ompute d in time O ( n 2 . 5 − ϵ ) (for any c onstant ϵ > 0 ), unless t he APSP Hyp othesis fails. And More . . . In Section 6 w e give some more matching APSP-based low er b ounds for in termediate- complexit y problems such as Min Pr o duct and Min-Equality Pr o duct , and recap how via known reductions these further imply low er b ounds for ev en more problems such as A l l-Edges Mono chr omatic T riangle [ 98 ]. Finally , w e give a non-matching n 7 / 3 − o (1) lo wer b ound for the important Min-Witness Pr o duct problem. 1.4 Pro of Ideas On a technical lev el, our approac h differs from most other fine-grained reductions. Typically , to design a reduction, w e study the problem to reduce to , aiming to understand the hard instances to reduce to. 7 Here, w e instead study the problem to reduce fr om , namely APSP or Min-Plus Product, and give sub cubic algorithms for a large class of input graphs (or matrices) satisfying a certain structur al pr op erty . Then, to design APSP-based hardness reductions, we can first apply this subcubic-time algorithm to handle the structured part of the graph (or matrix) and reduce to its unstructured core, whic h is often easier to reduce from. This p erspective can b e seen as a recen t trend with comparably few successful applications [ 2 , 1 , 35 , 70 , 37 ], including the aforementioned w ork introducing the “F redman’s tric k meets dominance pro duct” tec hnique [ 35 ]. A significant c hallenge is to identify the right structural prop ert y . W e prop ose a new, expressive one: a rank measure for matrices that we call the sele ct-plus r ank . 1.4.1 Select-Plus Rank Definition 1.17 (Select-Plus Rank) . The select-plus rank of a matrix A ∈ ( Z ∪ {⊥} ) n × m , denote d by r ( A ) , is the smal lest inte ger r ≥ 0 such that ther e ar e inte ger matric es U ∈ Z n × r and V ∈ Z r × m satisfying for al l ( i, j ) ∈ [ n ] × [ m ] : A [ i, j ] ∈ { U [ i, 1] + V [1 , j ] , . . . , U [ i, r ] + V [ r , j ] } ∪ {⊥} . This definition is reminiscen t of standard matrix rank, which can be characterized as the smallest r such that A = U V for some U ∈ Z n × r and V ∈ Z r × m , i.e., suc h that eac h entry can b e written as: A [ i, j ] = U [ i, 1] · V [1 , j ] + · · · + U [ i, r ] · V [ r, j ] . Hence, the select-plus rank can b e seen as the mo dification where we replace multiplication by addition, and addition b y “selection”. 8 In man y asp ects it also b eha ves like the standard matrix rank, e.g., the select-plus rank of an n × n matrix ranges from 0 to n . Our k ey technical result is the follo wing algorithm. Theorem 1.18 (Lo w-Rank Min-Plus Pro duct) . The min-plus pr o duct of two given matric es A, B c an b e c ompute d in deterministic time n 3+ o (1) · ( r /n 3 − ω ) Ω(1) , pr ovide d that we have ac c ess to a sele ct-plus r ank- r de c omp osition of A or B (or of a matrix C that appr oximates A ∗ B with entry-wise additive err or ± O (1) ). The p oin t is that when the select-plus rank is at most r ≤ n 3 − ω − ϵ the running time is truly sub cubic, n 3 − Ω( ϵ ) . In particular, if ω = 2 the running time is sub cubic for ranks up to r ≤ n 1 − ϵ —i.e., unless all matrices ha ve almost full rank, w e obtain a sub cubic-time algorithm for Min-Plus Pro duct! Theorem 1.18 implies that low-rank APSP , i.e., APSP on graphs whose adjacency lists hav e select-plus rank at most n 3 − ω − ϵ , can b e solv ed in sub cubic time. This result unifies and generalizes several previously studied classes of graphs known to admit sub cubic-time algorithms, including sparse graphs, graphs with small w eights in [ n 3 − ω − ϵ ] [ 88 , 57 , 9 , 90 , 104 ], no de-w eighted graphs [ 31 , 102 , 4 ], and ev en graphs with at most n 3 − ω − ϵ distinct edge w eights p er node [ 102 , 4 ]. In the follo wing, w e will first explore ho w the claimed univ erse reductions and fine-grained lo wer b ounds can be derived from Theorem 1.18 (Section 1.4.2 ), and then describ e on a high lev el how Theorem 1.18 can b e prov ed (Section 1.4.3 ). 1.4.2 Lo w-Rank Min-Plus Pro duct in A ction The main pow er of our new low-rank technique is that it allo ws us to significan tly restrict the set of “hard” Min-Plus Pro duct instances. Such restrictions are already known, though mostly simple ones. F or example, call any index k attaining the minimum min k ( A [ i, k ]+ B [ k , j ]) a witness of ( A ∗ B )[ i, j ] . In a hard instance A ∗ B w e exp ect that most entries ha ve only very few, say at most n ϵ , witnesses. Otherwise we could narrow our 8 Another reasonable notion could be the min-plus r ank of a matrix, defined analogously with the condition that A [ i, j ] = min { U [ i, 1] + V [1 , j ] , . . . , U [ i, r ] + V [ r , j ] } . This is a strictly more restrictive notion, i.e., the select-plus rank is alwa ys upp er- bounded by the min-plus rank. Therefore, all of our algorithmic results immediately also apply to the min-plus rank. How ever, for some applications (sp ecifically , Lemma 5.3 ) we crucially exploit the extra freedom tha t the select-plus rank offers. 8 atten tion to ˜ O ( n 1 − ϵ ) randomly sampled indices k —with high probability these include at least one witness , and the resulting smaller pro duct can b e computed in sub cubic time ˜ O ( n 3 − ϵ ) . The immediate consequence is that in all low er b ound constructions based on Min-Plus Pro duct w e can now assume the given matrices A, B to fulfill an extra requiremen t (namely that most entries in A ∗ B hav e few witnesses). Of course, this particular insigh t ab out the num b er of witnesses has limited impact. Instead, a quan tity which we really care about (for reasons that w e will outline soon) is the num b er of q -pseudo-witnesses , i.e., the n umber of indices k attaining the minim um min k ( ⌊ A [ i,k ] q ⌋ + ⌊ B [ k,j ] q ⌋ ) . In w ords, k is a q -pseudo-witness if it b ecomes a witness after rounding all en tries to multiples of q . In the previous paragraph we argued by elementary means that w e exp ect at most n ϵ 1 -pseudo-witnesses (a.k.a. witnesses) p er output entry . With the help of low-rank Min-Plus Pro duct one can show that, more generally for an y q ≥ 1 , there are at most q · n ϵ q -pseudo-witnesses p er output en try in the hard instances. As we will see this fact has surprisingly strong implications! F or instance, the equiv alence of the Strong APSP and Directed Un weigh ted APSP Hypotheses follows almost immediately . W e now describ e the main idea b ehind this fact. F o cus on the simplified setting that al l en tries ( A ∗ B )[ i, j ] ha ve more than q · n ϵ q -pseudo-witnesses. W e show that A ∗ B has small select-plus rank, r ( A ∗ B ) ≤ ˜ O ( n 1 − ϵ ) , and thus Theorem 1.18 allo ws to compute A ∗ B in subcubic time. In particular, A ∗ B cannot b e a hard instance. T o pro ve the rank b ound we proceed in tw o steps: 1. Consider the matrices A ′ = ⌊ A q ⌋ and B ′ = ⌊ B q ⌋ . The first step is to show that r ( A ′ ∗ B ′ ) ≤ ˜ O ( n 1 − ϵ /q ) . T o see this, take a subset K of ˜ O ( n 1 − ϵ /q ) randomly sampled indices k . With high probabilit y each output entry has at least one q -pseudo-witness in the sample. So consider the restriction U of A ′ to the columns in K , and the restriction V of B ′ to the rows in K . Eac h en try ( A ′ ∗ B ′ )[ i, j ] can b e expressed as a sum of the form U [ i, k ] + V [ k , j ] for some k ∈ K , which, by Definition 1.17 , implies that r ( A ′ ∗ B ′ ) ≤ |K| = ˜ O ( n 1 − ϵ /q ) . 2. Next, observe that w e can express A ∗ B = q · ( A ′ ∗ B ′ ) + R for some remainder matrix R with en tries b ounded b y O ( q ) . That matrix trivially has select-plus rank r ( R ) ≤ O ( q ) (F act 3.2 ). Since the select-plus rank b eha ves subm ultiplicatively (F act 3.3 ), it follows that r ( A ∗ B ) ≤ r ( A ′ ∗ B ′ ) · r ( R ) ≤ ˜ O ( n 1 − ϵ /q · q ) = ˜ O ( n 1 − ϵ ) as claimed. The description so far demonstrates generically that low-rank Min-Plus Pro duct can b e helpful in the design of reductions. W e no w give some v ery abstract pointers how our sp ecific applications b enefit from this approac h. Application 1: Small-Universe Reduction. Theorem 1.7 follows rather easily now b y pic king q = n 1 / 2 and adapting the ideas from [ 35 ]. Sp ecifically , knowing that there are at most n 1 / 2+ ϵ n 1 / 2 -pseudo-witnesses p er output entry , w e can afford to list all such pseudo-witnesses. When everything is set up carefully this list also con tains all prop er witnesses, so we can easily read off the min-plus pro duct A ∗ B . Based on this idea one can sho w that MinPlus( n, n, n | u ≤ n ) reduces to n 1 / 2+ ϵ instances of MinPlus( n, n 1 / 2 , n | u ≤ n 1 / 2 ) (in case that ω = 2 ) whic h entails the desired reduction. See Section 5.2 for the details. Application 2: Doubling Reduction. The pro of of Theorem 1.10 is more complicated and requires dev eloping more technical ideas. This result applies to arbitrarily large p olynomial universes u , so our approac h is to “grow” q from 1 to u in small steps. In some step the num b er of q -pseudo-witnesses must jump from less than n ϵ to at least n ϵ —this is the step where w e can effectively apply the previous ideas. On the one hand, the num ber of pseudo-witnesses is large enough so that the (appropriately rounded) min-plus pro duct matrix has small rank. On the other hand, the num b er of pseudo-witnesses is small enough so that we can afford to list all pseudo-witnesses (and thereby all witnesses). This idea essen tially allo ws us to assume that the initial Min-Plus Product instance is low-rank, so it remains to reduce low-rank Min-Plus Pro duct to uniform Min-Plus Pro duct. W e obtain this reduction as a by-product of our low-rank Min-Plus Pro duct algorithm (to b e describ ed next in Section 1.4.3 ). W e defer the many technical details to Section 5.3 . 9 n 3 ± o (1) n 2 . 5 ± o (1) APSP Strong APSP MinPlus( n, n, n ) n -Uniform MinPlus( n, n, n ) n -Univ erse MinPlus( n, n, n ) MinPlus( n, √ n, n ) √ n -Uniform MinPlus( n, √ n, n ) √ n -Univ erse MinPlus( n, √ n, n ) Min-Max Pro duct Dir. Unw. APSP No de-W eigh ted APSP , Ro w-Monotone Min-Plus Product, Min-Equalit y Product, . . . All-P airs Bottlenec k Paths, All-P airs Nondecreasing Paths, Appro ximate APSP (without Scaling), . . . [ 90 ] [ 33 ] Lem. 5.7 Lem. 5.13 Lem. 5.7 Lem. 5.13 Cor. 5.4 Lem. 6.5 Sec. 6 [ 73 ] [ 95 , 96 , 26 ] Figure 1. Illustrates our fine-grained reductions and resulting low er bounds assuming that ω = 2 . Each arro w sym b olizes a (tight) fine-grained reduction. Unlab eled arrows corresp ond to trivial reductions. The dashed arro ws are conditioned on the additiv e com binatorics Hyp othesis 1.12 . Application 3: Conditional Low er Bounds. Finally , our conditional lo wer b ounds follo w from the doubling reduction when appropriately generalized to r e ctangular matrices (see Corollary 5.9 ). Besides applying this big hammer, most of the individual reductions require only simple or previously known ideas. One exception is Theorem 1.16 . See Section 6 for details and Figure 1 for the resulting w eb of reductions. Ev en More Applications? Overall, we are confident that our new lo w-rank APSP algorithm will find more applications in the future—p erhaps in the design of more fine-grained reductions, or, ev en more am bi- tiously , p erhaps even as a step tow ards c hallenging the APSP Hypothesis. 1.4.3 Sub cubic Algorithm for Low-Rank Min-Plus Pro duct The proof of Theorem 1.18 is extremely inv olv ed. It builds on the recen t algorithm for APSP with few distinct edge w eigh ts per no de due to Abboud, Fischer, Jin, V assilevsk a W., and Xi [ 4 ], which itself is already a complicated chain of reductions, and adds more lay ers to the chain. Ev en w orse: T o obtain the 10 most general form of Theorem 1.18 (which is necessary e.g. for the doubling reduction) w e are forced to op en up their algorithm, recast it in a restricted framew ork of reductions (so-called p otential-adjusting reductions to b e defined in Section 2.3 ), and generalize all steps to rectangular matrices. F ortunately , along the wa y we manage to simplify one of the highly technical steps in [ 4 ] (again leveraging the expressiveness of the nov el select-plus rank), and in doing so, we even obtain a slightly faster APSP algorithm for the few-weigh ts case. 9 As in [ 4 ], our sub cubic-time algorithm also works for the strictly harder low-rank Exact T riangle problem. In this problem w e are additionally given a matrix C , and the goal is to report all en tries in the min-plus pro duct A ∗ B that coincide with C . W e now describ e the key insights b ehind this algorithm for low-rank Exact T riangle. Main Idea: Reduction to Slice-Uniform Instances. Let ( A, B , C ) b e a given Exact T riangle instance with select-plus rank r ( C ) ≤ r . Let C ℓ denote the submatrix of C consisting of all entries that are captured b y the ℓ -th part of the rank decomp osition (i.e., C [ i, j ] = U [ i, ℓ ] + V [ ℓ, j ] ), where all other en tries are replaced by some dumm y sym b ol ⊥ . Our strategy is to iterativ ely solv e the subinstances ( A, B , C 1 ) , . . . , ( A, B , C r ) one- b y-one. As w e aim for total time O ( n 3 − ϵ ) , eac h suc h subinstance m ust b e solved in time O ( n 3 − ϵ /r ) . Recall that the most in teresting case is when r is v ery close to n , so this time budget is just barely sup erquadratic. F o cus on an instance ( A, B , C ℓ ) , and define matrices A ′ , B ′ b y A ′ [ i, k ] = A [ i, k ] − U [ i, ℓ ] , B ′ [ k , j ] = − ( B [ k , j ] − V [ ℓ, j ]) . Then an y exact triangle A [ i, k ] + B [ k , j ] = C ℓ [ i, j ] corresponds to a solution of the m uch simpler equality condition A ′ [ i, k ] = B ′ [ k , j ] . This remaining problem is t ypically called Equality Pr o duct (where in our case the set of relev ant outputs is only the non- ⊥ entries in C ℓ ). Up to this point the algorithm can be seen as the “F redman’s trick” part of the “F redman’s tric k meets dominance pro duct” tec hnique [ 35 ]. Next, this tec hnique would solv e the Equalit y Pro duct instances each in time ˜ O ( n (3 − ω ) / 2 ) b y Matoušek’s algorithm [ 79 ] applied as a black-box. This running time is to o slow for our purp oses, so from now on our algorithm differs. Matoušek’s algorithm can b e viewed as a simple hea vy/light trick, so it is natural to pro ceed similarly . Call an entry in A ′ light if in its resp ectiv e column in the same integer entry app ears at most n 1 − ϵ /r times, and he avy otherwise. This threshold is c hosen in suc h a wa y that a simple brute-force algorithm can deal with instances con taining no hea vy entries in our time budget, O ( n 3 − ϵ /r ) . More in terestingly , consider the other extreme where al l en tries in A ′ are hea vy . If we ever reach this situation then we will “giv e up” on the iterative algorithm, go bac k to the original instance ( A, B , C ) , and solv e it in one shot. Ho w? Let C ′ b e the matrix defined b y C ′ [ i, j ] = C [ i, j ] − U [ i, ℓ ] . This is chosen in a wa y that the instances ( A, B , C ) and ( A ′ , B , C ′ ) are exactly equiv alen t (as the term U [ i, ℓ ] cancels in A ′ [ i, k ] + B [ k , j ] = C ′ [ i, j ] ). It th us suffices to solve the augmented instance ( A ′ , B , C ′ ) . The b enefit is that the augmen ted instance satisfies the extra constrain t that each column in A ′ con tains a truly sublinear n umber d ≤ r · n ϵ of distinct entries (as each heavy entry repeats at least n 1 − ϵ /r times p er column in A ′ ). This is exactly the d -slic e-uniform special case known to b e in sub cubic time due to Abb oud, Fischer, Jin, V assilevsk a W., and Xi [ 4 ]. T ec hnical Challenge: Regular Rank Decomp ositions. Unfortunately , th e previous paragraph just treats the unrealistic situations that either no or al l entries are hea vy—but what if only some entries are hea vy? This remaining case p oses some serious tec hnical challenges. Our solution inv olves t wo sub cases. The goo d subcase is when the n umber of hea vy en tries is still quite large, say at least n 2 − δ for some 9 T o be precise, the previously fastest APSP algorithm with at most n 3 − ω − ϵ distinct edge weights p er no de [ 4 ] runs in subcubic time O ( n 3 − Ω ϵ (1) ) where the hidden dep endence on ϵ is p olynomial. This unusual dep endence is due to a complicated recursion. In our newer version we obtain a more streamlined recursion leading to a linear dep endence Ω( ϵ ) as in Theorem 1.18 . 11 sufficien tly small δ > 0 . In this case a simple modification of the previous approac h works: after solving an instance ( A ′ , B , C ′ ) simply contin ue with the iterativ e algorithm, but r emove the at least n 2 − δ hea vy entries from A in all future iterations. W e thereby solve at most n δ instances ( A ′ , B , C ′ ) in total. The bad sub case is when the num b er of hea vy entries is less than n 2 − δ . Here, a natural idea is to exploit the sparsity of C ℓ . Sp ecifically , we could enumerate all heavy entries A ′ [ i, k ] and further all C ℓ [ i, j ] = ⊥ . F or eac h pair we can test in constan t time whether A ′ [ i, k ] = B ′ [ k , j ] . Heuristically speaking, if the en- tries of C w ere uniformly distributed among the matrices C 1 , . . . , C r , then w e would exp ect only O ( n/r ) en tries C ℓ [ i, j ] = ⊥ , leading to a total time of O ( n 3 − δ /r ) as in tended. The c hallenge lies in making this heuristic argument rigorous. More precisely , we would lik e to assume that the giv en rank decomposition is r ow-r e gular , i.e., that the matrices C 1 , . . . , C r eac h hav e at most ˜ O ( n/r ) non- ⊥ entries p er ro w. Is this p ossible without loss of generalit y? It is illuminating to consider the follo wing example. Suppose that C contains a large rank- 1 submatrix, of size s × s for some s ≫ n/r , and suppose that this submatrix is fully con tained in some part C ℓ . Then that part violates the row-regularit y condition. Ev en worse: There could be up to n 2 /s 2 suc h low-rank submatrices, leading to several violations. Luc kily , suc h submatrices essen tially turn out to be the only obstacles. W e show that, p erhaps surprisingly , we can construct an alternative decomp osition for (the union of ) these obstructions with rank ˜ O ( n/s ) ≪ r . That is, conceptually , the only wa y to violate the regularity condition is when some parts of C hav e strictly smal ler rank. F ormally , w e show that an arbitrary rank- r matrix C can b e decomposed in to three parts C row , C col , and C sm suc h that C row has a row-regular rank- r decomp osition, C col has an analogously defined column- regular rank- r decomp osition, and C sm has rank at most r / 2 (see Section 3.2 ). Then C row is as planned for our lo w-rank Min-Plus Pro duct algorithm, C col can b e dealt with by symmetry , and C sm can b e dealt with b y r e cursion . 1.5 Real W eigh ts A remark able consequence of our results is that w e conditionally resolv e the complexit y of All-P airs Shortest P aths for al l v arian ts: undirected or directed, with edge or no de weigh ts, ranging from unw eighted instances o ver small weigh ts { 0 , . . . , n } up to polynomially large integer weigh ts. Out of these v ariants, only undirected un weigh ted APSP is in time ˜ O ( n ω ) by Seidel’s algorithm [ 88 ]. F or all other v ariants—i.e., directed graphs, or undirected graphs with edge or node weigh ts in { 0 , . . . , n δ } for some constant δ > 0 —the resp ectiv e fastest-kno wn algorithms with sup er-quadratic complexit y turn out to b e optimal (in the sense that b eating an y such algorithm implies a sub cubic-time algorithm for general APSP , at least if ω = 2 , and conditioned on Hypothesis 1.1 ). See Section 6.1 for the full treatment of no de-w eighted graphs. A remaining in teresting question is to further connect the APSP problem on in teger-w eighted graphs with its more general counterpart on r e al-weighte d graphs. This problem, and the implications of the weak er R e al APSP Hyp othesis (along with other real-v alued hypotheses) ha ve b een explored in [ 34 ]. A particularly am bitious op en question is whether there is a “univ erse reduction” from the (uncoun tably infinite) real univ erse to the in tegers. While parts of our results apply to real-w eigh ted instances as w ell, other parts inheren tly rely on the finite bit representation of in tegers (suc h as the scaling trick to reduce from Min-Plus Pro duct to Exact T riangle), and so w e leav e further progress in this direction for future researc h. 2 Preliminaries W e write [ n ] = { 1 , . . . , n } . Throughout w e t ypically consider matrices A, B , C ∈ ( Z ∪ {⊥} ) n × m that con- sist of in teger en tries plus some designated sym b ol ⊥ representing a missing en try (e.g., when taking A to b e the adjacency matrix of a w eighted graph, ⊥ represen ts a missing edge). 10 W e follo w the con ven- tions x + ⊥ = ⊥ + x = ⊥ and min { x, ⊥} = x for all x ∈ Z ∪ {⊥} , and min ∅ = ⊥ . W e say that A is p artitione d 10 In some contexts it would b e natural to write ∞ , but to b e consistent ov erall we decided to write ⊥ . 12 in to tw o matrices A 1 , A 2 of the same size, denoted b y A = A 1 ⊔ A 2 , if each entry A [ i, j ] = ⊥ appears in exactly one of the tw o matrices (i.e., A 1 [ i, j ] = A [ i, j ] and A 2 [ i, j ] = ⊥ , or A 1 [ i, j ] = ⊥ and A 2 [ i, j ] = A [ i, j ] ). Let MM( n 1 , n 2 , n 3 ) denote the time complexity of multiplying an n 1 × n 2 with an n 2 × n 3 in teger matrix. Let 2 ≤ ω < 2 . 372 [ 8 ] denote the exp onen t of square matrix multiplication. 2.1 APSP , Min-Plus Pro duct and Exact T riangle Definition 2.1 (APSP) . The All-Pairs Shortest Paths (APSP) pr oblem is to c ompute the u - v -distanc es for al l p airs of no des u, v in a given dir e cte d e dge-weighte d n -vertex gr aph. Definition 2.2 (Min-Plus Pro duct) . The min-plus pro duct of A ∈ ( Z ∪ {⊥} ) n 1 × n 2 , B ∈ ( Z ∪ {⊥} ) n 2 × n 3 is the matrix A ∗ B ∈ ( Z ∪ {⊥} ) n 1 × n 3 define d by ( A ∗ B )[ i, j ] = min k ∈ [ n 2 ] ( A [ i, k ] + B [ k , j ]) . The Min-Plus Pro duct pr oblem is to c ompute the min-plus pr o duct A ∗ B of two given matric es A, B . Definition 2.3 (Exact T riangle) . L et A ∈ ( Z ∪ {⊥} ) n 1 × n 2 , B ∈ ( Z ∪ {⊥} ) n 2 × n 3 and C ∈ ( Z ∪ {⊥} ) n 1 × n 3 . A triangle is a triple ( i, k , j ) ∈ [ n 1 ] × [ n 2 ] × [ n 3 ] such that A [ i, k ] = ⊥ , B [ k , j ] = ⊥ , C [ i, j ] = ⊥ , and an exact triangle is a triangle ( i, k , j ) such that A [ i, k ] + B [ k , j ] = C [ i, j ] . 11 The (All-Edges) Exact T riangle 12 pr oblem is, given A, B , C , to de cide for e ach e dge ( i, k ) ∈ [ n 1 ] × [ n 2 ] and ( k , j ) ∈ [ n 2 ] × [ n 3 ] and ( i, j ) ∈ [ n 1 ] × [ n 3 ] if it is involve d in an exact triangle ( i, k , j ) . It is long-known that the APSP and Min-Plus Pro duct problems hav e the same complexity up to loga- rithmic factors. V assilevsk a W. and Williams [ 97 ] further prov ed that Min-Plus Pro duct reduces to All-Edges Exact T riangle b y a scaling tric k that only incurs an o verhead logarithmic in the univ erse size. 2.2 P arameters W e study the Min-Plus Pro duct and Exact T riangle problems constrained by v arious parameters, often by m ultiple parameters at the same time. T o simplify notation, we prop ose a systematic naming scheme. F or an y Min-Plus Pro duct instance ( A, B ) or any Exact T riangle instance ( A, B , C ) , consider the following six parameters: Parameter 2.4 ( r -Rank) . The sele ct-plus r ank of A or B (or C ) is at most r . W e assume that as p art of the input we additional ly r e c eive a r ank- r de c omp osition of that r esp e ctive matrix. Parameter 2.5 ( d -Slice-Uniform) . The r ows or c olumns in A or B (or C ) have at most d distinct non- ⊥ entries e ach. 13 Parameter 2.6 ( D -Uniform) . The total numb er of distinct non- ⊥ entries in al l matric es A and B (and C ) is at most D . Parameter 2.7 ( ρ -Regular) . In every r ow and c olumn of A and B (and C ), no non- ⊥ entry app e ars in mor e than a ρ -fr action of the r esp e ctive r ow or c olumn. Parameter 2.8 ( K -Doubling) . L et X b e the set of inte ger entries in A and B (and C ). Then X has doubling | X + X | ≤ K | X | . Parameter 2.9 ( u -Univ erse) . Al l non- ⊥ entries in the matric es A and B (and C ) ar e fr om { 0 , . . . , u } . 11 Of course, one could equiv alently define an exact triangle to satisfy that A [ i, k ] + B [ k, j ] + C [ i, j ] = 0 ; in this case the problem is typically called the Zer o T riangle problem. W e stick to the version in Definition 2.3 which is nicer to relate to the Min-Plus Pro duct problem. 12 The established name in the fine-grained literature is “All-Edges” Exact T riangle. Ho wev er, in this pap er we are exclusively concerned with the All-Edges version and so we will usually drop the “All-Edges” prefix for the sake of brevity . 13 In [ 4 ] this constraint was instead called d -weights . 13 F or instance, the r -r ank Exact T riangle problem is to solv e an Exact T riangle instance ( A, B , C ) for whic h we additionally receive access to a select-plus rank- r decomposition of A , B or C . W e also introduce the follo wing notation. W e write MinPlus( n 1 , n 2 , n 3 | c onstr aint ; . . . ; c onstr aint ) and ExactT ri( n 1 , n 2 , n 3 | c onstr aint ; . . . ; c onstr aint ) to denote the b est-p ossible running times of the Min-Plus Product and Exact T riangle problems, resp ectively , restricted to instances that satisfy the list of constraints. Each c onstr aint takes tw o p ossible forms. The first is p ar ameter ≤ value , for an y of the parameters defined ab o ve, to indicate that this parameter is b ounded b y value . E.g., MinPlus( n, n, n | d ≤ n 0 . 9 ) refers to the running time of the n 0 . 9 -slice-uniform Min-Plus Pro duct problem (where in one of the tw o matrices the rows or columns con tain at most n 0 . 9 distinct entries eac h). The second form is a free parameter. E.g., the fact that Min-Plus Pro duct with entries in { 0 , . . . , u } can b e solved in time ˜ O ( n ω u ) [ 9 ] can b e expressed concisely as MinPlus( n, n, n | u ) = ˜ O ( n ω u ) . As a more complicated example consider ExactT ri( n, n, n | D ≤ n 0 . 9 ; ρ ≤ 1 /D ; K ) . This expresses the running time of the Exact T riangle problem, restricted to matrices A, B , C with at most D distinct non- ⊥ entries such that D ≤ n 0 . 9 , where each entry in A, B and C app ears in at most a 1 /D -fraction of its row and column, and where the set of in teger en tries in the three matrices has doubling at most K . (W e will indeed encoun ter this problem in Lemma 4.13 .) Remark 2.10. Note that many of these p ar ameters ar e trivial ly r elate d to e ach other. F or instanc e, e ach u -universe instanc e is trivial ly u -uniform, and e ach D -uniform instanc e is trivial ly D -slic e-uniform. It is also not har d to se e that e ach d -slic e-uniform instanc e is trivial ly d -r ank. In Se ction 4 we wil l essential ly show the opp osites of some of these trivial dir e ctions, ther eby pr oving that many of these p ar ameters ar e equiv alen t in terms of sub cubic-time algorithms. Remark 2.11. W e wil l usual ly assume that al l entries ar e p olynomial ly b ounde d, so we always implicitly add the c onstr aint u ≤ ( n 1 n 2 n 3 ) O (1) . Having said that, al l r e ductions her e also apply to lar ger universes u with an overhe ad of (log u ) O (1) . 14 Remark 2.12. It is str aightforwar d to verify that V assilevska W. and Wil liams’ [ 97 ] r e duction fr om Min- Plus Pr o duct to Exact T riangle, MinPlus( n 1 , n 2 , n 3 | u ) = O (ExactT ri( n 1 , n 2 , n 3 | u ) · log u ) , also pr eserves the p ar ameters r , d , and D . 2.3 P oten tial A djustments It turns out to b e useful to define a particularly constrained t yp e of fine-grained reductions. W e often w ant to transform an Exact T riangle instance ( A, B , C ) into one or more instances that are equiv alen t in the follo wing sense: Each exact triangle is preserved, and for all other triangles ( i, k , j ) w e do not change the v alue A [ i, k ] + B [ k , j ] − C [ i, j ] . Informally , this requirement is exactly what allo ws us to simulate reductions for Min-Plus Product (see Lemma 5.7 ). The follo wing definitions mak e these requiremen ts formal: Definition 2.13 (Poten tial Adjustmen t) . L et ( A, B , C ) , ( A ′ , B ′ , C ′ ) b e Exact T riangle instanc es of the same size n 1 × n 2 × n 3 . W e say that ( A ′ , B ′ , C ′ ) is a p oten tial adjustment of ( A, B , C ) if ther e ar e p oten tial functions u ∈ Z n 1 , v ∈ Z n 2 , w ∈ Z n 3 so that A ′ [ i, k ] = A [ i, k ] + u [ i ] + v [ k ] or A ′ [ i, k ] = ⊥ for al l ( i, k ) ∈ [ n 1 ] × [ n 2 ] , B ′ [ k , j ] = B [ k , j ] − v [ k ] + w [ j ] or B ′ [ k , j ] = ⊥ for al l ( k , j ) ∈ [ n 2 ] × [ n 3 ] , C ′ [ i, j ] = C [ i, j ] + u [ i ] + w [ j ] or C ′ [ i, j ] = ⊥ for al l ( i, j ) ∈ [ n 1 ] × [ n 3 ] . 14 There is a technical detail: Somewhere along our chain of reductions, in Lemma 4.9 , we rely on a deterministic algorithm with a running time o verhead of 2 ˜ O ( √ log u ) = u o (1) . Ho wev er, this deterministic algorithm can b e replaced by a randomized algorithm with only p olylogarithmic o verhead. 14 That is, in a p oten tial adjustment, one is allo wed to “delete edges” and to add “node weigh ts” in such a wa y that A [ i, k ] + B [ k , j ] − C [ i, j ] remains unchanged for all surviving triangles. This use of potential adjustmen ts is akin to that in sev eral shortest-path problems, e.g., the well-kno wn Johnson tric k [ 71 ]. Definition 2.14 (P otential-A djusting Reduction) . A p otential-adjusting 1 -to- N reduction in time T is an algorithm that runs in time T , takes as input a (p ossibly c onstr aine d) Exact T riangle instanc e ( A, B , C ) of size n 1 × n 2 × n 3 , and r eturns as output a p air ( I , T ) wher e • I is a set of N (p ossibly c onstr aine d) p otential adjustments of ( A, B , C ) , and • T ⊆ [ n 1 ] × [ n 2 ] × [ n 3 ] with size |T | ≤ T , so that, for e ach exact triangle ( i, k , j ) in ( A, B , C ) , ( i, k , j ) app e ars as an (exact) triangle in an instanc e in I , or ( i, k , j ) ∈ T . Remark 2.15. An even stricter notion would b e to enfor c e that e ach exact triangle app e ars either in T or in exactly one instanc e in I . This would dir e ctly imply r e ductions b etwe en c ounting versions of the pr oblems as wel l. It c an b e che cke d that al l of our r e ductions c an actual ly achieve this stricter c onstr aint (with some minor mo dific ations her e and ther e)—however, sinc e the r e ductions ar e alr e ady quite involve d we have de cide d to stick to the simpler Definition 2.14 . 2.4 A dditiv e Com binatorics Let X, Y ⊆ Z be tw o finite sets. W e write X + Y = { x + y : x ∈ X , y ∈ Y } to denote their sumset . W e also set X − Y = { x − y : x ∈ X , y ∈ Y } and − X = {− x : x ∈ X } , and for an integer x w e write X + x = X + { x } . Let r X + Y ( z ) denote the multiplicity of z in the sumset X + Y , i.e., the num b er of representations z = x + y with x ∈ X, y ∈ Y , or equiv alen tly , r X + Y ( z ) = | X ∩ ( z − Y ) | . W e o ccasionally rely on the follo wing tw o basic facts from additive com binatorics; see e.g. the textbo oks [ 94 , 103 ]. Lemma 2.16 (Plünnec k e-Ruzsa Inequality [ 81 , 84 ]) . L et X , Y b e finite sets with | X + Y | ≤ K | X | . Then, letting nY denote the n -fold sumset Y + · · · + Y , it holds for al l nonne gative inte gers n, m that: | nY − mY | ≤ K n + m | X | . Lemma 2.17 (Ruzsa’s T riangle Inequalit y [ 85 ]) . F or al l finite sets X , Y , Z : | X + Y | ≤ | X + Z | | Y + Z | | Z | . W e also need the follo wing algorithm to efficien tly compute sumsets: Lemma 2.18 (Sparse Conv olution [ 22 ]) . Ther e is an algorithm that, given sets X , Y ⊆ {− u, . . . , u } , c om- putes their sumset X + Y along with the multiplicities r X + Y ( · ) in deterministic time | X + Y | · (log u ) O (1) . 2.5 Mac hine Mo del Throughout we consider the W ord RAM model with logarithmic word size Θ(log n ) , where n is the input size. Moreov er, for all graph and matrix problems w e alw ays only consider w eights that are p olynomially (i.e., n O (1) ) bounded and can th us be stored in O (1) mac hine w ords. As is the standard in fine-grained complexit y , w e allow randomized algorithms (that succeed with high probability 1 − n − c for an arbitrarily large constan t c ) in h yp otheses and reductions. 15 3 Select-Plus Rank In this section, w e recap the cen tral definition of select-plus rank, establish some basic facts (Section 3.1 ), and dev elop a refined notion of rank decomp ositions that will be crucial later on (Section 3.2 ). Definition 1.17 (Select-Plus Rank) . The select-plus rank of a matrix A ∈ ( Z ∪ {⊥} ) n × m , denote d by r ( A ) , is the smal lest inte ger r ≥ 0 such that ther e ar e inte ger matric es U ∈ Z n × r and V ∈ Z r × m satisfying for al l ( i, j ) ∈ [ n ] × [ m ] : A [ i, j ] ∈ { U [ i, 1] + V [1 , j ] , . . . , U [ i, r ] + V [ r , j ] } ∪ {⊥} . W e reiterate that this alternative rank notion is reminiscent of the standard matrix rank, which can b e c haracterized as the smallest n umber r suc h that A can b e written as U V for matrices U of size n × r and V of size r × m , resp ectiv ely . In the following we will often refer to the select-plus rank simply as the “rank” of a matrix. 3.1 Basic F acts W e gather some basic facts concerning the select-plus rank. The first t wo inv olve trivial upper bounds on the rank based on the size and maximum entry . Fact 3.1. r ( A ) ≤ min { n, m } for al l matric es A ∈ ( Z ∪ {⊥} ) n × m . Pro of. T ake U to b e all-zero and V = A , or vice versa. Fact 3.2. r ( A ) ≤ u for al l matric es A ∈ ([ u ] ∪ {⊥} ) n × m . Pro of. T ake U to b e all-zero and define V by V [ k , j ] = k . Fact 3.3 (Subm ultiplicativity) . r ( A 1 + A 2 ) ≤ r ( A 1 ) · r ( A 2 ) for al l matric es A 1 , A 2 ∈ ( Z ∪ {⊥} ) n × m . Pro of. Let U 1 , V 1 b e matrices witnessing r ( A 1 ) and let U 2 , V 2 b e matrices witnessing r ( A 2 ) . Consider the follo wing matrices U, V , where we index the rows of U and columns of V by pairs ( k 1 , k 2 ) ∈ [ r ( A 1 )] × [ r ( A 2 )] : U [ i, ( k 1 , k 2 )] = U 1 [ i, k 1 ] + U 2 [ i, k 2 ] , V [( k 1 , k 2 ) , j ] = V 1 [ k 1 , j ] + V 2 [ k 2 , j ] . Eac h entry in A 1 + A 2 can be expressed as A 1 [ i, j ] + A 2 [ i, j ] = U 1 [ i, k 1 ] + V 1 [ k 1 , j ] + U 2 [ i, k 2 ] + V 2 [ k 2 , j ] = U [ i, ( k 1 , k 2 )] + V [( k 1 , k 2 ) , j ] , for some pair ( k 1 , k 2 ) ∈ [ r ( A 1 )] × [ r ( A 2 )] . Th us, U, V witnesses that r ( A 1 + A 2 ) ≤ r ( A 1 ) · r ( A 2 ) . 3.2 Regular Rank Decomp ositions W e will no w make the concept of a select-plus rank decomp osition formal. Definition 3.4 (Rank Decomposition) . L et A, U, V and r b e as in Definition 1.17 . L et S ∈ ([ r ] ∪ {⊥} ) n × m b e a matrix such that A [ i, j ] = ( U [ i, S [ i, j ]] + V [ S [ i, j ] , j ] if S [ i, j ] = ⊥ , ⊥ if S [ i, j ] = ⊥ . Then we c al l ( U, V , S ) a select-plus rank- r decomp osition of A . 16 Of course, knowing only A , U , and V it is easy to complete the rank decomposition by constructing S in time O ( nmr ) (for all our applications this running time is strictly sub cubic and hence tolerable). The b enefit of Definition 3.4 is rather that it is conv enient to hav e access to the “selector” matrix S . In a later key step, it will b e crucial that the giv en rank decomposition satisfies an additional structural prop ert y , namely that it is r ow- or c olumn-r e gular defined as follows. Definition 3.5 (Regular Rank Decomposition) . L et ( U, V , S ) b e a r ank- r de c omp osition of some n × m matrix, and let R ≥ 1 . W e c al l ( U, V , S ) R -row-regular if, for al l ℓ ∈ [ r ] and al l i ∈ [ n ] , |{ j ∈ [ m ] : S [ i, j ] = ℓ }| ≤ R · m r . A nalo gously, we c al l ( U, V , S ) R -column-regular if, for al l ℓ ∈ [ r ] and al l j ∈ [ m ] , |{ i ∈ [ n ] : S [ i, j ] = ℓ }| ≤ R · n r . The following lemma states that w e can transform any rank decomp osition into a regular one without loss of generality . Specifically , it states that any matrix A with a giv en rank- r decomp osition can be split into a row-regular part A row , a column-regular part A col , and a smal l part A sm with strictly smaller rank, r / 2 . Algorithmically w e will simply r e curse on this small part, whic h effectively means that we can alwa ys treat A as partly ro w-regular and partly column-regular. Lemma 3.6 (Regular Rank Decomp osition) . F or any matrix A ∈ ( Z ∪ {⊥} ) n × m with r ank r ( A ) ≤ r ther e is a p artition A = A row ⊔ A col ⊔ A sm such that • A row has an O (log( nm )) -r ow-r e gular r ank- r de c omp osition, • A col has an O (log( nm )) -c olumn-r e gular r ank- r de c omp osition, and • A sm has r ank r ( A sm ) ≤ r / 2 . Mor e over, given A and a c orr esp onding r ank- r de c omp osition we c an c ompute the matric es A row , A col , A sm along with their claime d de c omp ositions in deterministic time ˜ O ( nmr ) . The proof of Lemma 3.6 relies on the follo wing co vering-t yp e lemma. Lemma 3.7 (Conflict-F ree Co vering) . L et x 1 , . . . , x n ∈ [ r ] and let C 1 , . . . , C n ⊆ [ r ] b e sets of size at most s such that x i ∈ C i for al l i . W e say that a set S ⊆ [ r ] cov ers item i if x i ∈ S and C i ∩ S = ∅ . Then ther e is a c ol le ction S of size |S | ≤ O ( s log n ) so that e ach i ∈ [ n ] is c over e d by some set S ∈ S . Mor e over, ther e is a deterministic ˜ O ( nr ) -time algorithm that c onstructs S , along with a mapping [ n ] → S indic ating for e ach item i by which set it is c over e d. Pro of Sk etch. Here, w e only pro vide a quick pro of sketc h based on a probabilistic argumen t; in App endix B w e will then efficiently derandomize this argument based on the method of conditional exp ectations. The construction of S is simple: T ake O ( s log n ) indep enden tly random sets S ⊆ [ r ] with sample rate 1 / (2 s ) . Eac h such set S co vers an y fixed index i with probability at least Ω(1 /s ) . Indeed, the probabilit y that x i ∈ S is 1 / (2 s ) , and indep enden tly we av oid all conflicts, C i ∩ S = ∅ , with probability at least 1 − | C i | / (2 s ) ≥ 1 / 2 . Hence, after O ( s log n ) rep etitions we cov ered all items with high probabilit y . Pro of of Lemma 3.6 . Let ( U, V , S ) denote the rank- r decomp osition of A , and let R = Θ(log( nm )) (where w e determine the implied cons tan t later). If r ≤ R then this rank- r decomp osition is trivially R -row-regular (and we can simply take A row = A without modifying the decomp osition), so supp ose that r > R . F or eac h ℓ ∈ [ r ] define the sets I ℓ = n i ∈ [ n ] : |{ j ∈ [ m ] : S [ i, j ] = ℓ }| > R · m r o , J ℓ = n j ∈ [ m ] : |{ i ∈ [ n ] : S [ i, j ] = ℓ }| > R · n r o . 17 That is, I ℓ is the set of rows that violate the row-regularit y condition for ℓ , and J ℓ is the set of columns that violate the column-regularity condition for ℓ . Let A = A row ⊔ A col ⊔ A sm denote the partition of A where in A row w e retain the entries ( i, j ) with i ∈ I S [ i,j ] , in A col w e retain the entries ( i, j ) with i ∈ I S [ i,j ] and j ∈ J S [ i,j ] , and in A sm w e retain the entries ( i, j ) with i ∈ I S [ i,j ] and j ∈ J S [ i,j ] ; we will call these entries ( i, j ) irr e gular . In the following w e argue that the three matrices A row , A col , A sm admit the claimed rank decomp ositions. Rank Decomp osition of A row and A col . It is simple to construct an R -ro w-regular rank- r decomp o- sition ( U row , V row , S row ) of A row : T ake U row = U and V row = V , and let S row b e the restriction of S to the en tries ( i, j ) satisfying that i ∈ I S [ i,j ] . This is clearly a v alid rank- r decomp osition of A row . T o see that it is also R -ro w-regular, focus on any ℓ ∈ [ r ] and any row i ∈ [ n ] . In S row w e ha ve only retained the en tries S [ i, j ] = ℓ with i ∈ I ℓ , hence by definition |{ j ∈ [ m ] : S row [ i, j ] = ℓ }| ≤ R · m r . The construction for A col is analogous. Rank Decomp osition of A sm . Next, w e construct a rank- r / 2 decomp osition ( U sm , V sm , S sm ) of A sm . In this step we will crucially rely on the cov ering lemma from b efore. Sp ecifically , for each irregular pair ( i, j ) define x i,j = S [ i, j ] , and C i,j = { ℓ ∈ [ r ] : i ∈ I ℓ or j ∈ J ℓ } \ { S [ i, j ] } . W e run Lemma 3.7 on the items x i,j ∈ [ r ] and conflict sets C i,j ⊆ [ r ] . Let S denote the resulting collection of sets, and write T i,j ∈ S for the set cov ering ( i, j ) . Let U sm ∈ Z [ n ] ×S , V sm ∈ Z S × [ m ] , S sm ∈ ( S ∪ {⊥} ) n × m b e the matrices defined as follows (here, for simplicity of notation we assume that the columns of U sm , the rows of V sm , and the entries of S sm are indexed b y sets T ∈ S , but this can easily b e replaced by the in tegers [ |S | ] ): U sm [ i, T ] = ( U [ i, ℓ ] for some ℓ ∈ T with i ∈ I ℓ , 0 if suc h ℓ do es not exist, V sm [ T , j ] = ( V [ ℓ, j ] for some ℓ ∈ T with j ∈ J ℓ , 0 if suc h ℓ do es not exist, S sm [ i, j ] = ( T i,j if ( i, j ) is irregular, ⊥ otherwise. (The assignmen t 0 of U sm , V sm in the failure case is arbitrary .) W e claim that ( U sm , V sm , S sm ) is a v alid decomp osition of A sm . This is trivially true for the regular pairs, so fix some irregular pair ( i, j ) . Lemma 3.7 guaran tees that x i,j ∈ T i,j and C i,j ∩ T i,j = ∅ . This means that ℓ := x i,j = S [ i, j ] is the only element in T i,j that satisfies i ∈ I ℓ or j ∈ J ℓ , and th us U sm [ i, T i,j ] = U [ i, ℓ ] , V sm [ T i,j , j ] = V [ ℓ, j ] . Hence, U sm [ i, S sm [ i, j ]] + V sm [ S sm [ i, j ] , j ] = U sm [ i, T i,j ] + V sm [ T i,j , j ] = U [ i, ℓ ] + V [ ℓ, j ] = A sm [ i, j ] . It follows that we ha ve indeed constructed a v alid rank- |S | decomp osition. W e finally argue that |S | ≤ r/ 2 for an appropriate choice of parameters. First observ e that each conflict set C i,j has size at most s := 2 r /R , as eac h index i is part of at most r /R sets I ℓ , and similarly each index j is part of at most r /R sets J ℓ . Therefore, by Lemma 3.7 we hav e |S | ≤ O ( s log ( nm )) = O ( r log( nm ) /R ) . Hence, picking R = Θ(log( nm )) for some sufficien tly large hidden constan t, we get that |S | ≤ r / 2 as w as in tended. 18 Running Time. T o compute the sets I ℓ and J ℓ w e first precompute the statistics |{ j ∈ [ m ] : S [ i, j ] = ℓ }| (for all i, ℓ ) and |{ i ∈ [ n ] : S [ i, j ] = ℓ }| (for all j, ℓ ) in time ˜ O ( nm + nr + mr ) . Afterw ards we can read off I ℓ and J ℓ in the same running time. Then it is straightforw ard to compute the partition A = A row ⊔ A col ⊔ A sm in time ˜ O ( nm ) . It remains to analyze the time to compute the rank decomp ositions of A row , A col and A sm . The decomp ositions of A row and A col are computable from ( U, V , S ) in linear time ˜ O ( nm ) . F or the decom- p osition of A sm the dominating step is the computation of S in time ˜ O ( nmr ) b y Lemma 3.7 ; the remaining steps run in time ˜ O ( nm + nr + mr ) . 4 Lo w-Rank Exact T riangle The main result of this section is that Lo w-Rank Exact T riangle can b e solved in sub cubic time: Theorem 4.1 (Low-Rank Exact T riangle) . The r -r ank Exact T riangle pr oblem c an b e solve d in deterministic time ExactT ri( n, n, n | r ) ≤ n 3+ o (1) · r n 3 − ω 1 / 200000 . The p oint of this theorem is that for r ≤ n 3 − ω − ϵ this running time is truly sub cubic, O ( n 3 − Ω( ϵ ) ) . W e ha ve not attempted to optimize the constant 200000. Likely , it can b e improv ed dramatically , but for all our applications the constant do es not matter. The pro of of Theorem 4.1 is an algorithmic reduction from the Low-Rank Exact T riangle problem via v arious in termediate steps to the Uniform Lo w-Doubling Exact T riangle problem: Lemma 4.2 (Reduction from Lo w-Rank to Uniform Lo w-Doubling Exact T riangle) . F or any p ar ameter K ≥ 1 ther e is a p otential-adjusting r e duction fr om any r -rank Exact T riangle instanc e to K ( n 1 n 2 n 3 ) o (1) instanc es that ar e e ach D -uniform , 1 /D -regular and K -doubling for some D ≤ r . The r e duction runs in deterministic time ( n 1 n 2 n 3 /K 1 / 98000 + ( n 1 n 2 + n 1 n 3 + n 2 n 3 ) r K ) 1+ o (1) . In p articular: ExactT ri( n 1 , n 2 , n 3 | r ) ≤ K · ExactT ri( n 1 , n 2 , n 3 | D ≤ r ; ρ ≤ 1 /D ; K ) + n 1 n 2 n 3 K 1 / 98000 + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r K 1+ o (1) . In tuitively , this lemma states that we can reduce an r -rank instance in sub cubic time to few instances that are r -uniform and K -doubling, for an arbitrarily small p olynomial K = n ϵ ′ . (In fact, the instances are also regular, but we do not need to rely on this extra constraint here.) This is a special case of Exact T riangle that can be solved in sub cubic time b y a simple algebraic algorithm; see [ 4 , Lemma 5.5] 15 . Lemma 4.3 (Uniform Lo w-Doubling Exact T riangle [ 4 ]) . A ny Exact T riangle instanc e ( A, B , C ) c an b e solve d in deterministic time ˜ O (MM( n 1 , n 2 , n 3 ) · | X + X | ) , wher e X is the set of inte ger entries in A , B and C . In p articular: ExactT ri( n 1 , n 2 , n 3 | D ; K ) = ˜ O (MM( n 1 , n 2 , n 3 ) · D K ) . 15 A subtlety in [ 4 , Lemma 5.5] is that it only determines the edges ( i, j ) ∈ [ n 1 ] × [ n 3 ] that are inv olved in exact triangles, but not the edges ( i, k ) ∈ [ n 1 ] × [ n 2 ] and ( k , j ) ∈ [ n 2 ] × [ n 3 ] . How ever, since in Lemma 4.3 X denotes the set of entries in all three matrices A, B , C , we can simply apply [ 4 , Lemma 5.5] three times on all rotations of the instance ( A, B , C ) . Alternatively , as stated in [ 4 ], one can apply the Baur-Strassen trick [ 51 , 16 ]. 19 Lo w-Rank r ≤ n 3 − ω − ϵ Slice-Uniform d ≤ n 3 − ω − ϵ Uniform D ≤ n 3 − ω − ϵ Uniform Regular D ≤ n 3 − ω − ϵ ρ ≤ 1 /D Uniform Lo w-Doubling D ≤ n 3 − ω − ϵ K ≤ n ϵ ′ Section 4.1 Section 4.2 [ 4 ] Section 4.3 Section 4.4 [ 4 ] Figure 2. Illustrates the four steps in the reduction from Lo w-Rank Exact T riangle to Uniform Lo w- Doubling Exact T riangle. (The dashed arrow symbolizes a recursiv e dep endence; see Section 4.3 .) Pro of of Theorem 4.1 . Combining Lemmas 4.2 and 4.3 we obtain that, for an y parameter K ≥ 1 , ExactT ri( n, n, n | r ) = K · ExactT ri( n, n, n | D ≤ r ; K ) + n 3 K 1 / 98000 + n 2 r K 1+ o (1) = K · n ω r K + n 3 K 1 / 98000 + n 2 r K 1+ o (1) = n ω r K 2 + n 3 K 1 / 98000 1+ o (1) . W e pick K = ( n 3 − ω /r ) 98 / 200 and argue that then the running time is as claimed. Indeed, the second term is clearly n 3+ o (1) ( r /n 3 − ω ) 1 / 200000 . The first term can b e rewritten as n 3+ o (1) ( r /n 3 − ω )( n 3 − ω /r ) 98 / 100 whic h is at most n 3+ o (1) ( r /n 3 − ω ) 2 / 100 and th us dominated b y the second term. F or the remainder of this section, we focus on the pro of of Lemma 4.2 . The reduction can b e split into four individual steps, which w e treat in Sections 4.1 to 4.4 . See Figure 2 for an outline. Step 1 is new and can b e regarded as one of the key technical parts of this pap er. Steps 2 and 4 are already established in [ 4 ] and can b e taken almost without mo difications; we pro vide full pro ofs here for the sak e of completeness and b ecause we need appropriately generalized statements throughout (such as a rectangular version, and the assertion that all reductions are p oten tial-adjusting). Step 3 could be taken as in [ 4 ], but we give an alternativ e pro of that significan tly improv es the parameters (otherwise we would get the weak er statement that n 3 − ω − ϵ -rank Exact T riangle can b e solved in time O ( n 3 − Ω ϵ (1) ) where the hidden dep endence on ϵ is w orse than Ω( ϵ ) ). Throughout, we will consider the rectangular case of size n 1 × n 2 × n 3 . Moreo v er, we will often implicitly assume that the parameter in question ( r , d or D ) satisfies that r ≤ n 1 , n 2 , n 3 . This is without loss of generalit y , as all algorithms we consider spend time at least Ω( r · ( n 1 n 2 + n 1 n 3 + n 2 n 3 )) , and hence if the assumption w as violated w e could alternatively solve the instance naively in time O ( n 1 n 2 n 3 ) . 4.1 Reduction from Lo w-Rank to Slice-Uniform Exact T riangle The following lemma captures the first step in our chain of reductions. An imp ortan t ingredient for its pro of is the previously established Lemma 3.6 . Lemma 4.4 (Reduction from Low-Rank to Slice-Uniform Exact T riangle) . F or any p ar ameter t ≥ 1 ther e is a p otential-adjusting r e duction fr om any rank- r Exact T riangle instanc e to O ( t 2 log r ) r -slice-uniform instanc es. The r e duction runs in deterministic time ˜ O ( n 1 n 2 n 3 /t + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r t 2 ) . In p articular: ExactT ri( n 1 , n 2 , n 3 | r ) ≤ ˜ O t 2 · ExactT ri( n 1 , n 2 , n 3 | d ≤ r ) + n 1 n 2 n 3 t + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r t 2 . 20 Pro of. Let us assume that w e are given a lo w-rank decomp osition of C ; the statemen ts for A and B follo w b y first rotating the given instance. By Lemma 3.6 we may further assume that the given rank- r decom- p osition of C is R -ro w-regular for some R = O (log ( n 1 n 3 )) . F ormally , we apply the lemma to partition C in to C row ⊔ C col ⊔ C sm , where C row has an R -row-regular rank- r decomp osition, C col has an R -column-regular rank- r decomp osition, and C sm has a rank- r / 2 decomp osition. It then remains to solve the Exact T riangle instances ( A, B , C row ) , ( A, B , C col ) and ( A, B , C sm ) . W e will describ e how to solv e ( A, B , C row ) in the fol- lo wing. The instance ( A, B , C col ) can b e equiv alen tly view ed as ( B T , A T , C T col ) ; in this case, to o, we hav e access to a R -ro w-regular rank- r decomp osition of C T col , so we can solve the instance also as describ ed in the follo wing. Finally , w e solv e ( A, B , C sm ) recursiv ely—since the rank r halves with every recursiv e call this only leads to a logarithmic ov erhead. Let ( U, V , S ) denote the R -ro w-regular rank- r decomp osition of C . Let T ← ∅ b e a set of exceptional triples, and let I ← ∅ b e a set of r -slice-uniform p otential adjustments of ( A, B , C ) . Consider the following algorithm. In an outer lo op, w e en umerate ℓ ← 1 , . . . , r . W e maintain the in v ariant that after the ℓ -th iteration each exact triangle ( i, k , j ) with S [ i, j ] = ℓ has been inserted in to T or is presen t in one of the instances in I . 1. (He avy/Light Setup) Define the matrices A ℓ and B ℓ of sizes n 1 × n 2 and n 2 × n 3 , respectively , b y A ℓ [ i, k ] = A [ i, k ] − U [ i, ℓ ] , B ℓ [ k , j ] = − ( B [ k , j ] − V [ ℓ, j ]) . Note that for all pairs ( i, j ) with S [ i, j ] = ℓ the conditions A [ i, k ]+ B [ k, j ] = C [ i, j ] and A ℓ [ i, k ] = B ℓ [ k , j ] are equiv alen t. W e no w classify the non- ⊥ en tries ( i, k ) in A ℓ as follo ws: W e say that ( i, k ) is light if |{ i ′ ∈ [ n 1 ] : A ℓ [ i, k ] = A ℓ [ i ′ , k ] }| ≤ n 1 r t , and he avy otherwise. In the following tw o steps we separately deal with the exact triangles ( i, k , j ) in volving light and heavy edges ( i, k ) , respectively . R unning Time: O (( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r ) ov er all iterations. 2. (Light Edges) W e enumerate all triples ( i, k , j ) with A ℓ [ i, k ] = B ℓ [ k , j ] for which ( i, k ) is light as follows. En umerate all pairs ( k , j ) ∈ [ n 2 ] × [ n 3 ] . Only if there is a light edge ( i ′ , k ) do w e enumerate the at most n 1 / ( r t ) ro ws i with A ℓ [ i, k ] = B ℓ [ k , j ] . W e insert each triple ( i, k , j ) with A [ i, k ] + B [ k , j ] = C [ i, j ] in to the set T . This correctly main tains the in v ariant for all exact triangles in volving light edges. R unning Time: O ( n 1 n 2 n 3 / ( r t )) p er iteration, and thus O ( n 1 n 2 n 3 /t ) across all iterations. 3. (He avy Edges) W e distinguish tw o cases depending on the n umber of heavy edges: 3.1. (F ew He avy Edges) If there are at most n 1 n 2 /t hea vy edges, then we apply brute-force as follows. En umerate all hea vy pairs ( i, k ) , and enumerate all columns j with S [ i, j ] = ℓ . Eac h triple ( i, k , j ) en umerated in this wa y that satisfies A [ i, k ] + B [ k , j ] = C [ i, j ] is inserted into T . This again clearly main tains the in v ariant for all exact triangles in volving a heavy edge. R unning Time: F or each ro w i there are at most R · ( n 3 /r ) columns j with S [ i, j ] = ℓ as the given rank decomp osition is assumed to be R -row-regular. Hence the running time is O ( n 1 n 2 /t · R · ( n 3 /r )) = ˜ O ( n 1 n 2 n 3 / ( r t )) p er iteration, and thus ˜ O ( n 1 n 2 n 3 /t ) across all iterations. 21 3.2. (Many He avy Edges) The remaining case is that there are more than n 1 n 2 /t hea vy pairs. Let H denote the set of heavy pairs ( i, k ) , and let A H b e the matrix A restricted to the en tries in H (where all other entries are set to ⊥ ). Our strategy is to solv e the entire instance ( A H , B , C ) in this step (by means of the reduction), and afterwards to remov e all heavy entries from A glob al ly . T o this end, construct matrices A ′ and C ′ b y A ′ [ i, k ] = A [ i, k ] − U [ i, ℓ ] if ( i, k ) ∈ H , A ′ [ i, k ] = ⊥ otherwise, and C ′ [ i, j ] = C [ i, j ] − U [ i, ℓ ] . By definition ( A ′ , B , C ′ ) is a p oten tial-adjusting restriction of ( A, B , C ) that retains all the exact triangles inv olving heavy edges. Moreov er, we claim that eac h column in A ′ con tains at most r t distinct entries. Indeed, by construction A ′ coincides with A ℓ on the non- ⊥ (i.e., heavy) en tries, and by definition eac h heavy en try app ears at least n 1 / ( r t ) times in its column in A ℓ . It follo ws that the instance ( A ′ , B , C ′ ) is rt -slice-uniform. W e now further reduce ( A ′ , B , C ′ ) to t instances that are r -slice-uniform (in the trivial w ay) and insert these instances in to the collection I . Afterw ards, w e remov e all entries in H glob al ly , i.e., we set A [ i, k ] ← ⊥ for all ( i, k ) ∈ H for all future iterations. Regarding the correctness, observ e that each exact triangle ( i, k , j ) with ( i, k ) ∈ H and S [ i, j ] = ℓ is preserved in ( A ′ , B , C ′ ) . In fact, we ha ve dealt with al l exact triangles with ( i, k ) ∈ H (irresp ectiv e of S [ i, j ] ), so we can indeed safely remov e all pairs in H from A for the future itera- tions. R unning Time: The construction of H and of the t equiv alent instances takes linear time ˜ O (( n 1 n 2 + n 1 n 3 + n 2 n 3 ) t ) p er iteration. Moreo v er, with each execution of step 3.2 we increase the size of I by at most t . Notably , ho wev er, we execute this step 3.2 at most t times in total, as after each iteration we replace | H | ≥ n 1 n 2 /t non- ⊥ entries in A by ⊥ . It follows that the total running time is ˜ O (( n 1 n 2 + n 1 n 3 + n 2 n 3 ) t 2 ) and that |I | ≤ t 2 throughout. This completes the pro of. The correctness should b e clear from the in-text explanations, and the total running time as analyzed b efore is ˜ O ( n 1 n 2 n 3 /t + ( n 1 n 2 + n 1 n 3 + n 2 n 3 ) r t 2 ) as claimed. (Here w e only lo osely b ound the dep endence on t .) 4.2 Reduction from Slice-Uniform to Uniform Exact T riangle The second step is captured by the following lemma. Its pro of can b e fully attributed to [ 4 ]—no new ideas are necessary . W e include a complete proof here only b ecause we need the more general rectangular v ersion, and to point out that the reduction is p oten tial-adjusting. Readers familiar with [ 4 ] can safely skip this section. Lemma 4.5 (Reduction from Slice-Uniform to Uniform Exact T riangle [ 4 ]) . F or any p ar ameter t ≥ 1 ther e is a p otential-adjusting r e duction fr om any d -slice-uniform Exact T riangle instanc e to O ( t 41 log 2 ( n 1 n 2 n 3 )) d -uniform instanc es. The r e duction runs in deterministic time ˜ O ( n 1 n 2 n 3 /t + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) dt 41 ) . In p articular: ExactT ri( n 1 , n 2 , n 3 | d ) ≤ ˜ O t 41 · ExactT ri( n 1 , n 2 , n 3 | D ≤ d ) + n 1 n 2 n 3 t + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) dt 41 . The pro of of Lemma 4.5 requires some setup. Recall that r X + Y ( z ) denotes the multiplicit y of z in the sumset X + Y , i.e., the n umber of represen tations of the form z = x + y for ( x, y ) ∈ X × Y . 22 Definition 4.6 (P opular Sums) . F or two inte ger sets X , Y ⊆ Z , we define their set of s -p opular sums as P s ( X, Y ) = { z ∈ X + Y : r X + Y ( z ) ≥ s } . Observ ation 4.7. | P s ( X, Y ) | ≤ | X | | Y | /s . It is easy to compute (a superset of ) the set of s -popular sums in randomized time ˜ O ( | X | | Y | /s ) . The idea is to subsample X ′ ⊆ X with rate roughly 1 /s ; with go od probability the p opular sums are preserved in X ′ + Y . Fischer, Jin, and Xu [ 53 ] sho wed that with more effort this task can b e derandomized in essentially the same running time. Lemma 4.8 (Appro ximating Popular Sums [ 53 , Theorem 1.9]) . Given sets X, Y ⊆ [ u ] and s ≥ 1 , we c an c ompute P 2 s ( X, Y ) ⊆ P ⊆ P s ( X, Y ) in r andomize d time ˜ O ( | X | | Y | /s ) or deterministic time | X | | Y | /s · u o (1) . The follo wing lemma—the so-called “p opular sum decomp osition”—is the k ey insight b ehind this reduc- tion step from [ 4 ]. Intuitiv ely , it states that sets X 1 , . . . , X n and Y 1 , . . . , Y m can b e decomp osed into few structured parts that lo ok exactly alike (up to shifts), plus some remainders X ∗ 1 , . . . , X ∗ n and Y ∗ 1 , . . . , Y ∗ n . Almost all remainder pairs X ∗ i , Y ∗ j , ho wev er, ha ve no p opular sum. Lemma 4.9 (Popular Sum Decomp osition [ 4 ]) . L et X 1 , . . . , X n , Y 1 , . . . , Y m ⊆ [ u ] b e sets of size at most d , and let p ≥ 1 . Then ther e exist p artitions X i = X ∗ i ⊔ p 2 G g =1 X i,g , Y j = Y ∗ j ⊔ p 2 G h =1 Y j,h satisfying the fol lowing two pr op erties: 1. Ther e ar e sets S g of size | S g | ≤ d and shifts s i,g so that X i,g ⊆ S g + s i,g (for al l i ∈ [ n ] , g ∈ [ p 2 ] ), and ther e ar e sets T h of size | T h | ≤ d and shifts t j,h so that Y j,h ⊆ T h + t j,h (for al l j ∈ [ m ] , h ∈ [ p 2 ] ). 2. |{ ( i, j ) ∈ [ n ] × [ m ] : P 2 d/p ( X ∗ i , Y j ) = ∅}| ≤ nm/p , and |{ ( i, j ) ∈ [ n ] × [ m ] : P 2 d/p ( X i , Y ∗ j ) = ∅}| ≤ nm/p . Mor e over, ther e is an algorithm that, given the sets X i , Y j , c omputes the p artitions along with the sets S g , T h and the shifts s i,ℓ , t j,ℓ in r andomize d time ˜ O ( nmdp 3 ) or deterministic time nmdp 3 · u o (1) . Pro of. W e only show how to construct the partition of X and the accompan ying sets S g and shifts s i,g . The partition of Y is obtained symmetrically by exc hanging X 1 , . . . , X n and Y 1 , . . . , Y m . Consider the following algorithm. F or each g ← 1 , 2 , . . . we run the follo wing steps: 1. Apply Lemma 4.8 to compute sets P 2 d/p ( X i , Y j ) ⊆ P i,j ⊆ P d/p ( X i , Y j ) for all ( i, j ) ∈ [ n ] × [ m ] . 2. If |{ ( i, j ) ∈ [ n ] × [ m ] : P i,j = ∅}| ≤ nm/p : Pick X ∗ i ← X i for all i ∈ [ n ] and stop the algorithm. 3. Otherwise: Pic k some j ∈ [ m ] with |{ i ∈ [ n ] : P i,j = ∅}| ≥ n/p . W e c ho ose S g = − Y j . Let us call an index i go o d if P i,j = ∅ and b ad otherwise. F or each bad i we choose X i,g = ∅ and s i,g arbitrarily . F or eac h go o d i we instead choose an arbitrary shift s i,g ∈ P i,j . Then we pick X i,g = X i ∩ ( S g + s i,g ) . This forms the next part in the partition of X i , so w e can safely remo ve it, X i ← X i \ X i,g . 23 Correctness. It is clear that if the algorithm terminates then we hav e satisfied the tw o claimed prop erties: By construction X i is indeed partitioned into X i, 1 , X i, 2 , . . . and X ∗ i , we hav e that X i,g ⊆ S g + s i,g , and when the algorithm terminates then also |{ ( i, j ) ∈ [ n ] × [ m ] : P 2 d/p ( X ∗ i , Y j ) = ∅}| ≤ nm/p (as P 2 d/p ( X i , Y j ) ⊆ P i,j ). It remains to pro ve that the algorithm terminates after at most p 2 iterations. T o see this, fo cus on an arbitrary iteration g , let j b e the index pick ed in step 3 , and let i b e go od in this iteration. W e claim that the constructed set X i,g has size at least d/p . Indeed, as s i,g ∈ P i,j ⊆ P d/p ( X i , Y j ) w e hav e that | X i,g | = | X i ∩ ( s i,g + S g ) | = | X i ∩ ( s i,g − Y j ) | = r X i + Y j ( s i,g ) ≥ d p . Th us, w e reduce the size | X i | of every go od index i by at least d/p . In total there are at least n/p such go od indices, hence in each step we reduce P i ∈ [ n ] | X i | b y at least nd/p 2 . Initially we ha ve P i ∈ [ n ] | X i | ≤ nd , and so the claim follows. Running Time. F ocus on a single iteration. In step 1 w e apply Lemma 4.8 nm times. Eac h execution tak es deterministic time d 2 / ( d/p ) · u o (1) = dp · u o (1) , so step 1 takes time nmdp · u o (1) . T esting the condition in step 2 takes negligible time O ( nm ) . In step 3 w e sp end time prop ortional to the total set sizes, O ( nmd ) . Summing ov er these contributions and o ver the at most p 2 iterations, the claimed time b ound nmdp 3 · u o (1) follo ws. The randomized time bound follows analogously . Pro of of Lemma 4.5 . Let ( A, B , C ) denote the giv en d -slice-uniform instance. Note that the statemen t is symmetric with resp ect to the sizes n 1 , n 2 , n 3 , hence by rotating and/or transp osing the given instance we ma y assume without loss of generalit y that the ro ws of A con tain at most d distinct entries eac h. Outer Regularization. Before we giv e the core reduction, we run the following simple preprocessing step to ens ure that all entries in A app ear roughly equally often in their columns, and similarly for B . W e partition A in to L = ⌈ log n 2 ⌉ matrices A 0 , . . . , A L where in the matrix A ℓ w e include all entries that appear at least 2 ℓ and at most 2 ℓ +1 times in their resp ectiv e r ow . Similarly partition B into B 0 , . . . , B L according to the frequencies p er c olumn . It remains to deal with all pairs of instances ( A ℓ , B ℓ ′ , C ) (for ℓ, ℓ ′ ∈ [ L ] ). F or the rest of the pro of, fix one suc h instance, and let us write A = A ℓ and B = B ℓ ′ for simplicity of notation. Let d A = min { d, n 2 / 2 ℓ } and d B = n 2 / 2 ℓ ′ , and verify that there are at most d A distinct entries p er ro w in A , and at most d B distinct en tries p er column in B . Let d ′ = max { d A , d B } . Finally , we argue that we may assume that d B ≤ d A · t in the following. Indeed, if instead d B ≥ d A · t then we can solve the instance by brute-force as follo ws. En umerate all pairs ( i, j ) ∈ [ n 1 ] × [ n 3 ] , enumerate the at most d A en tries x in the i -th row of A , and enumerate all k ∈ [ n 2 ] with B [ k , j ] = C [ i, j ] − x . W e insert all exact triangles ( i, k , j ) en umerated in this step in to T . R unning Time: ˜ O ( n 1 n 3 · d A · ( n/d B )) = ˜ O ( n 1 n 2 n 3 /t ) . Uniformization. Let X i denote the set of entries in the i -th row of A . Let Y j denote the set of entries in the j -th column of B . All these sets ha ve size at most d ′ . Run the p opular sum decomp osition (Lemma 4.9 ) for these sets, and some parameter p ≥ 1 to b e determined later. W e call an exact triangle ( i, k , j ) A -exc eptional if A [ i, k ] ∈ X ∗ i , B -exc eptional if B [ k , j ] ∈ Y ∗ j , and or dinary otherwise. R unning Time: ˜ O ( n 1 n 3 dp 3 · u o (1) ) (recall that throughout u = ( n 1 n 2 n 3 ) O (1) , hence u o (1) = ( n 1 n 2 n 3 ) o (1) ). 1. (Exc eptional T riangles) W e will explicitly enumerate all exceptional exact triangles. Here we describe ho w to list all A -exceptional exact triangles and omit the analogous argumen t for listing B -exceptional triangles. The first step is to apply Lemma 4.8 to compute sets P 4 d ′ /p ( X ∗ i , Y j ) ⊆ P i,j ⊆ P 2 d ′ /p ( X ∗ i , Y j ) , for all pairs ( i, j ) ∈ [ n 1 ] × [ n 3 ] . W e call an A -exceptional triangle ( i, k , j ) p opular if C [ i, j ] ∈ P i,j and unp opular otherwise. W e will deal with the p opular and unp opular exceptional triangles in tw o separate steps: 24 1.1. (Unp opular T riangles) Enumerate all pairs ( i, j ) ∈ [ n 1 ] × [ n 3 ] with C [ i, j ] ∈ P i,j . By definition, C [ i, j ] ∈ P i,j ⊇ P 4 d ′ /p ( X ∗ i , Y j ) can b e expressed as a sum x + y of elements x ∈ X ∗ i and y ∈ Y j in at most 4 d ′ /p wa ys. Enumerate all such represen tations ( x, y ) , then enumerate all k ∈ [ n 2 ] with A [ i, k ] = x and test if ( i, k , j ) is an exact triangle; if yes, we insert it into the set T . R unning Time: F or each pair ( i, j ) we sp end time O ( d A ) to list the relev an t representations, plus time O ( d ′ /p · n 2 /d A ) to en umerate all pairs x, y , k . The total time is: O n 1 n 3 · d A + d ′ p · n 2 d A = O n 1 n 3 · d + d A t p · n 2 d A = O n 1 n 3 d + n 1 n 2 n 3 t p . 1.2. (Popular T riangles) The num b er of pairs ( i, j ) with P i,j ⊆ P 2 d ′ /p ( X ∗ i , Y j ) = ∅ is at most n 1 n 3 /t b y Lemma 4.9 . F or each suc h pair we en umerate all p ossible k ∈ [ n 2 ] , test if ( i, k , j ) is an exact triangle, and in that case store ( i, k , j ) in T . R unning Time: O ( n 1 n 2 n 3 /t ) . 2. (Or dinary T riangles) Enumerate all pairs g , h ∈ [ p 2 ] . Let A h , B g , C g ,h b e the matrices defined b y A g [ i, k ] = ( A [ i, k ] − s i,g if A [ i, k ] ∈ X i,g , ⊥ otherwise, B h [ k , j ] = ( B [ k , j ] − t j,h if B [ k , j ] ∈ Y j,h , ⊥ otherwise, C g ,h [ i, j ] = ( C [ i, j ] − s i,g − t j,h if C [ i, j ] = ⊥ , ⊥ otherwise. Eac h ordinary triangle ( i, k , j ) app ears in exactly one Exact T riangle instance ( A g , B h , C g ,h ) , namely the instance with A [ i, k ] ∈ X i,g and B [ k , j ] ∈ Y j,h . Moreo ver, the v alue of the triangle is unc hanged in that instance as the terms s i,g and t j,h cancel: A g [ i, k ] + B h [ k , j ] − C g ,h [ i, j ] = A [ i, k ] + B [ k , j ] − C [ i, j ] . It is easily verified that all non- ⊥ en tries in A g stem from the set S g (as X i,g − s i,g ⊆ S g ) and all non- ⊥ en tries in B h stem from the set T h (as Y j,h − t j,h ⊆ T h ). Recall that further | S g | , | T h | ≤ d ′ , so in each instance ( A g , B h , C g ,h ) the matrices A g and B h satisfy the d ′ -uniformit y condition. In the following we will further mo dify C g ,h to also b ecome d ′ -uniform. Let q b e another parameter to b e determined later, and compute the set P := P d ′ /q ( S g , T h ) (b y brute-force, say , in negligible time). Then call a pair ( i, j ) p opular if C g ,h [ i, j ] ∈ P and unp opular otherwise. Consider the follo wing t wo cases: 2.1. (Unp opular Entries) This case is similar to step 1.1 . Our goal is to list all exact triangles ( i, k , j ) in ( A g , B h , C g ,h ) where ( i, j ) is unp opular. T o this end en umerate all unp opular pairs ( i, j ) . Recall that there are at most d ′ /q represen tations of C [ i, j ] as a sum x + y where x ∈ S g and y ∈ T h . W e en umerate all such represen tations, and further all k ∈ [ n 2 ] with A g [ i, k ] = x . W e test if ( i, k , j ) is an exact triangle, and in this case store ( i, k , j ) in T . 25 R unning Time: F or each unp opular pair ( i, j ) w e sp end time O ( d ′ ) to list all relev an t repre- sen tations, plus time O ( d ′ /q · n 2 /d A ) to en umerate all x, y , k . In total, w e rep eat this step p 4 times, leading to a total time of: O p 4 · n 1 n 3 · d ′ + d ′ q · n 2 d A = O p 4 · n 1 n 3 · dt + d A t q · n 2 d A = O n 1 n 2 n 3 dtp 4 + n 1 n 2 n 3 tp 4 q . 2.2. (Popular Entries) Let C pop g ,h b e the restriction of C g ,h to the popular entries (where we replace all unp opular en tries by ⊥ ). By Observ ation 4.7 w e hav e that | P | ≤ | S g | | T h | / ( d ′ /q ) ≤ d ′ q , so b y construction the instance ( A g , B h , C pop g ,h ) is d ′ q -uniform. W e trivially reduce that instance further to at most (( d ′ q ) /d ) 3 ≤ t 3 q 3 instances that are d -uniform and store the resulting instances in I . R unning Time: ˜ O ( p 4 t 3 q 3 · ( n 1 n 2 + n 2 n 3 + n 1 n 3 )) . This completes the description of the reduction. Clearly it is p oten tial-adjusting (with p otential functions u [ i ] = − s i,g , v [ k ] = 0 , and w [ j ] = − t j,h ). Running Time. The prepro cessing step takes time ˜ O ( n 1 n 2 n 3 /t ) as argued b efore and leads to O (log 2 n 2 ) instances we ha ve to deal with. The running time of the uniformization step is bounded as follo ws b y summing o ver all the contributions analyzed b efore: ˜ O ( n 1 n 2 + n 1 n 3 + n 2 n 3 ) d · p 4 t 3 q 3 + n 1 n 2 n 3 t + n 1 n 2 n 3 t p + n 1 n 2 n 3 tp 4 q . This b ecomes as claimed b y setting the parameters p = t 2 and q = t 10 . F rom this c hoice of parameters it also follo ws that |I | ≤ O (log 2 ( n 1 n 2 n 3 ) · p 4 t 3 q 3 ) ≤ O ( t 41 log 2 ( n 1 n 2 n 3 )) as claimed. 4.3 Reduction from Lo w-Rank to Uniform Regular Exact T riangle The third step is to reduce to instances that are not only D -uniform but also 1 /D -r e gular (i.e., each integer app ears in at most a 1 /D -fraction of the en tries of each row and column in all three matrices). This is one of the most technical steps in [ 4 ]. Roughly , the idea is to sho w that eac h D -uniform instance can b e partitioned into tw o pieces: a D -uniform 1 /D -regular part, and a remaining part that is D ′ -slice-uniform for some D ′ ≪ D . The first part is as intended. And the second part can b e solved b y first applying Lemma 4.5 and then r e cursing on the p olynomially man y resulting D ′ -uniform instances. By carefully choosing the in volv ed parameters this indeed leads to a subcubic reduction—but with quite bad quan titativ e b ounds. Sp ecifically , the resulting algorithm for n 3 − ω − ϵ -slice-uniform Exact T riangle runs in time n 3 − ϵ O (1) . Here we prop ose a twist to the argument in [ 4 ]: Instead of recursing on p olynomially man y instances that are D ′ -slice-uniform for some D ′ ≪ D , it turns out to be p ossible to recurse on just O (1) instances that are r -rank for some r ≪ D . This, in contrast, results in a final running time of n 3 − Ω( ϵ ) as stated in Theorem 4.1 . Lemma 4.10 (Reduction from Lo w-Rank to Uniform Regular Exact T riangle) . F or any p ar ameter t ≥ 1 ther e is a p otential-adjusting r e duction fr om any rank- r Exact T riangle instanc e to t 875 ( n 1 n 2 n 3 ) o (1) instanc es that ar e e ach D -uniform and 1 /D -regular for some D ≤ r . The r e duction runs in deterministic time ( n 1 n 2 n 3 /t + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r t 875 ) 1+ o (1) . In p articular: ExactT ri( n 1 , n 2 , n 3 | r ) ≤ t 875 · ExactT ri( n 1 , n 2 , n 3 | D ≤ r ; ρ ≤ 1 /D ) + n 1 n 2 n 3 t + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r t 875 1+ o (1) . 26 Pro of. Let q b e a parameter to b e determined later. W e design a recursiv e algorithm that transforms the given low-rank instances in three steps into (1) slice-uniform instances, (2) uniform instances, (3) uni- form and regular instances. The third step is incomplete in the sense that w e cannot deal with some en tries A sm , B sm , C sm in the matrices A, B , C . F or these remaining entries, how ev er, we can compute rank decomp ositions of strictly smaller rank r ′ < r , so in a fourth step we will simply recurse on these matrices. In detail: 1. (L ow-R ank to Slic e-Uniform) Run the p oten tial-adjusting reduction from Lemma 4.4 with some pa- rameter t sl to transform the given low-rank instance into r -slice-uniform instances; let ( I sl , T sl ) denote the output. R unning Time: ˜ O ( n 1 n 2 n 3 /t sl + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r t 2 sl ) . 2. (Slic e-Uniform to Uniform) W e further reduce (in a p oten tial-adjusting wa y) to ( I unif , T unif ) as follows. Initialize I unif ← ∅ , T unif ← T sl . F or eac h instance ( A ′ , B ′ , C ′ ) ∈ I sl run Lemma 4.5 with some parameter t unif to obtain an r -uniform instances ( I ′ , T ′ ) . Let I unif ← I unif ∪ I ′ and T unif ← T unif ∪ T ′ . This is the comp osition of t wo p oten tial-adjusting reductions, and thus also p oten tial-adjusting. R unning Time: ˜ O ( |I sl | · ( n 1 n 2 n 3 /t unif + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r t 2 unif )) . 3. (Uniform to Uniform R e gular) Next, w e reduce the instances in I unif further to regular instances I reg (where initially I reg ← ∅ ). In this reduction step we will miss some exact triangles, but we will make sure that each missed triangle is part of one of the three instances ( A sm , B , C ) , ( A, B sm , C ) , ( A, B , C sm ) . These three instances are required to b e lo w-rank, hence we will also maintain lo w-rank decomposi- tions of A sm , B sm , C sm . Initially , A sm , B sm , C sm are all- ⊥ matrices and w e start with trivial rank- 0 decomp ositions. En umerate all instances ( A ′ , B ′ , C ′ ) ∈ I unif . Since ( A ′ , B ′ , C ′ ) is a p oten tial adjustment of the initial instance, there are p oten tial functions u ∈ Z n 1 , v ∈ Z n 2 suc h that A ′ [ i, k ] = A [ i, k ] + u [ i ] + v [ k ] or A ′ [ i, k ] = ⊥ for all entries. Let q b e a parameter. W e call an entry A ′ [ i, k ] r ow-he avy if the same entry app ears in more than a q /r -fraction of the entries in its row (i.e., |{ k ′ : A ′ [ i, k ] = A ′ [ i, k ′ ] }| > q /r · n 2 ), otherwise w e call the en try c olumn-he avy if it appears in more than a q/r -fraction of the entries in its column (i.e., |{ i ′ : A ′ [ i, k ] = A ′ [ i ′ , k ] }| > q /r · n 1 ), and otherwise we call the entry light . Let A ′ = A ′ row ⊔ A ′ col ⊔ A ′ light denote the partition of A ′ in to the row-hea vy , column-heavy and ligh t entries, resp ectiv ely . In the same w ay we obtain partitions of B and C in to their row-hea vy , column-hea vy and light parts, resp ectively . W e pro ceed in tw o substeps: 3.1. (Light Entries) By definition each entry in A ′ light app ears at most in a q/r -fraction of its ro w and column. By a simple transformation we can further partition A ′ light in to q 2 matrices where eac h en try appears in at most a 1 /r -fraction of its row and column. Hence, we can transform the subinstance ( A ′ light , B ′ light , C ′ light ) (in a p oten tial-adjusting wa y) to q 6 instances that are r -uniform and 1 /r -regular. Insert these instances in to I reg . R unning Time: ˜ O ( |I unif | · q 6 · ( n 1 n 2 + n 2 n 3 + n 1 n 3 )) . 27 3.2. (He avy Entries) F o cus on the row-hea vy entries in A ′ for now. F or eac h such ro w-heavy entry ( i, k ) w e will up date A sm [ i, k ] ← A [ i, k ] . Recall that we need to up date the resp ectiv e rank decomp o- sition of A sm to match these new entries. T o this end observ e that eac h ro w in A ′ row con tains at most r /q distinct entries, so we can trivially compute a rank- ( r /q ) decomp osition ( U ′ , V ′ , S ′ ) of A ′ row . Next w e adjust this decomposition by U [ i, ℓ ] = U ′ [ i, ℓ ] − u [ i ] , V [ ℓ, j ] = V ′ [ ℓ, j ] − v [ j ] , leading to a same-rank decomp osition ( U, V , S = S ′ ) of the restriction of A to the ro w-heavy en tries (of A ′ ). Indeed, for each hea vy en try ( i, k ) we ha ve that A [ i, k ] = A ′ [ i, k ] − u [ i ] − v [ k ] = U ′ [ i, S ′ [ i, k ]] + V ′ [ S ′ [ i, k ] , k ] − u [ i ] − v [ k ] = U [ i, S [ i, k ]] + V [ S [ i, k ] , k ] . W e repeat the same pro cedure with the column-heavy entries A ′ col to up date A sm . Then, sym- metrically , w e up date B sm and C sm for all ro w-heavy and column-hea vy entries in B ′ and C ′ . In the upcoming step 4 we will see why this treatment was useful. R unning Time: ˜ O ( |I unif | · ( n 1 n 2 + n 2 n 3 + n 1 n 3 )) . After w e ha ve enumerated all instances in I unif in this wa y , w e claim that we hav e transformed the initial instance in a p oten tial-adjusting manner into ( I reg ∪ { ( A sm , B , C ) , ( A, B sm , C ) , ( A, B , C sm ) } , T unif ) . T o s ee that this is correct take any exact triangle ( i, k , j ) in ( A, B , C ) . After step 2 , the triangle is part of T unif or it app ears as an exact triangle in some instance ( A ′ , B ′ , C ′ ) ∈ I unif . In the former case we are done, so fo cus on the latter case. W e contin ue with tw o sub cases: If the entries ( i, k ) , ( k, j ) , ( i, j ) are all ligh t in A ′ , B ′ , C ′ , respectively , then by construction ( i, k , j ) app ears as an exact triangle in some instance in I reg . Otherwise, if ( i, k ) is row-hea vy , sa y , then ( i, k , j ) app ears as an exact triangle in ( A sm , B , C ) . 4. (R e cursion) W e recurse on the three instances ( A sm , B , C ) , ( A, B sm , C ) and ( A, B , C sm ) . Recall that w e hav e indeed constructed lo w-rank decompositions for the three matrices A sm , B sm , C sm as required b y the theorem statement. W e will so on analyze ho w small these rank decomp ositions actually are, and discuss why this recursion leads to a terminating algorithm. Let ( I A , T A ) , ( I B , T B ) , ( I C , T C ) denote the outputs of the three recursive calls. W e return ( I , T ) = ( I A ∪ I B ∪ I C ∪ I reg , T A ∪ T B ∪ T C ∪ T unif ) . This completes the description of the recursiv e step. In the base case, when r = 0 , one of the matrices con tains only ⊥ -entries and so w e can trivially return I , T ← ∅ . It follo ws from the in-text explanation that this algorithm is indeed a potential-adjusting reduction (assuming it terminates), and that all resulting instances are regular. It remains to argue that w e hav e constructed sets ( I , T ) of the claimed sizes. Analysis of the Recursion. The critical part is to analyze the rank decompositions of A sm , B sm , C sm . Note that with each iteration of step 3.2 we increase their sizes by at most 2 r /q (namely , plus r /q due to the ro w-heavy entries, and plus r /q due to the column-hea vy entries). Thus, letting n = max { n 1 , n 2 , n 3 } and letting r ′ denote the final size of the rank decomp ositions, we ha ve that r ′ ≤ 2 r q · |I unif | ≤ O 2 r q · |I sl | · t 41 unif · log 2 n ≤ O 2 r q · t 2 sl · t 41 unif · log 3 n . 28 Pic k q = t 41 unif · t 2 sl · 2 √ log n , then it follows that r ′ ≤ r 2 Ω( √ log n ) . First, this implies that each recursive call indeed mak es progress and that the algorithm terminates. Second, this further implies that the recursion reaches depth at most O ( √ log n ) , and as each call of the algorithms spa wns only three recursiv e calls the total n umber of recursive calls is 3 O ( √ log n ) . W e can use this to b ound the final size of ( I , T ) . F o cus on an y recursive call of the algorithm. The sets w e construct hav e size |T unif | ≤ |T sl | + |I sl | · ˜ O n 1 n 2 n 3 t unif ≤ ˜ O n 1 n 2 n 3 t sl + n 1 n 2 n 3 t 2 sl t unif and |I reg | ≤ q 6 · |I unif | ≤ q 6 · t 2 sl · t 41 unif · log 3 n ≤ t 14 sl · t 287 unif · 2 O ( √ log n ) . The total sizes |T | and |I | are worse only b y a factor 3 O ( √ log n ) . Cho osing t sl = t and t unif = t 3 , this is as claimed in the theorem statement. Running Time. Finally , fo cus on the running time. Per recursive call the sum of all con tributions analyzed b efore is, lo osely bounded, ˜ O n 1 n 2 n 3 t sl + n 1 n 2 n 3 t 2 sl t unif + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r · t 41 unif · t 2 sl · q 6 ≤ n 1 n 2 n 3 t + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r t 875 1+ o (1) . A cross all recursive calls the running time w orsens only b y 3 O ( √ log n ) = n o (1) . 4.4 Reduction from Uniform Regular to Uniform Low-Doubling Exact T riangle The fourth and final step is to reduce to uniform (regular) lo w-doubling Exact T riangle. This step is again due to [ 4 ] and [ 32 ] almost without mo difications—we merely extend the pro of to rectangular matrices and sho w the sligh tly stronger condition that the join t set of entries of all three matrices A, B , C has small doubling. The reduction crucially relies on the regularity condition established b efore and also on the BSG theorem from additiv e com binatorics [ 14 , 58 ]. Sp ecifically , w e use the follo wing algorithmic cov ering version of the BSG theorem due to Chan and Lew enstein [ 32 ]. Theorem 4.11 (BSG Cov ering [ 32 ]) . L et X , Y , Z ⊆ Z b e sets of size at most n , and let L ≥ 1 . Then ther e ar e subsets X 1 , . . . , X L ⊆ X and Y 1 , . . . , Y L ⊆ Y satisfying the fol lowing pr op erties: 1. | X ℓ + Y ℓ | ≤ O ( L 5 n ) for al l ℓ ∈ [ L ] , 2. | R | ≤ O ( n 2 /L ) wher e R = { ( x, y ) ∈ X × Y : x + y ∈ Z } \ S L ℓ =1 ( X ℓ × Y ℓ ) . The sets X 1 , . . . , X L , Y 1 , . . . , Y L and R c an b e c ompute d in deterministic time ˜ O ( n ω L ) . The follo wing simple lemma will also be useful. Lemma 4.12. L et X , Y ⊆ Z b e sets with doubling | X + X | ≤ K | X | and | Y + Y | ≤ K | Y | . Then Z = X + Y has doubling | Z + Z | ≤ K 8 | Z | . 29 Pro of. W e write nX = X + · · · + X for the n -fold iterated sumset of X . The pro of is by rep eated applications of Ruzsa’s triangle inequality (Lemma 2.17 ). The first application is with X ′ = 2 X , Y ′ = 2 Y and Z ′ = Z to conclude that | Z + Z | = | 2 X + 2 Y | ≤ | 2 X + Z | | 2 Y + Z | | Z | = | 3 X + Y | | X + 3 Y | | Z | . The second application is with X ′ = 3 X , Y ′ = Y and Z ′ = X to obtain | 3 X + Y | ≤ | 3 X + X | | X + Y | | X | = | 4 X | | Z | | X | ≤ K 4 | X | | Z | | X | = K 4 | Z | ; here w e also used the Plünnec ke-Ruzsa inequality (Lemma 2.16 ) | nX | ≤ K n | X | . The third application is symmetric: | X + 3 Y | ≤ | X + Y | | 3 Y + Y | | Y | = | Z | | 4 Y | | Y | ≤ | Z | K 4 | Y | | Y | = K 4 | Z | . The statemen t follows from putting these three bounds together. Lemma 4.13 (Reduction from Uniform Regular to Uniform Low-Doubling Exact T riangle) . F or any p a- r ameter K ≥ 1 ther e is a p otential-adjusting r e duction fr om any D -uniform 1 /D -regular Exact T riangle instanc e to O ( K 1 / 112 ) instanc es that ar e e ach D -uniform , 1 /D -regular and K -doubling . The r e duction runs in deterministic time ˜ O ( n 1 n 2 n 3 /K 1 / 112 + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) D K 1 / 112 ) . In p articular: ExactT ri( n 1 , n 2 , n 3 | D ; ρ ≤ 1 /D ) ≤ ˜ O K 1 / 112 · ExactT ri( n 1 , n 2 , n 3 | D ; ρ ≤ 1 /D ; K ) + n 1 n 2 n 3 K 1 / 112 + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) D K 1 / 112 . Pro of. Let X denote the set of entries in the given D -uniform instance, i.e., | X | ≤ D . W e apply BSG Co vering with X = Y = Z with some parameter L to b e pick ed later, resulting in sets X 1 , . . . , X L , Y 1 , . . . , Y L and R . W e say that a triangle ( i, k, j ) is in the structur e d part if ( A [ i, k ] , B [ k , j ]) ∈ X ℓ × Y ℓ (for some ℓ ∈ [ L ] ), and otherwise, if ( A [ i, k ] , B [ k , j ]) ∈ R , w e sa y that it is in the r emainder . W e deal with these tw o t yp es of triangles in t wo separate steps: 1. (R emainder) W e will explicitly list all exact triangles in the remainder. En umerate all pairs ( x, y ) ∈ R , en umerate all k ∈ [ n 2 ] and enumerate all i ∈ [ n 1 ] with A [ i, k ] = x and all j ∈ [ n 3 ] with B [ k , j ] = y . All exact triangles ( i, k , j ) that w e detect in this w ay are stored in a set T . R unning Time: Recall that the given instance is 1 /D -regular, hence for all fixed k , x there are at most n 1 /D indices i with A [ i, k ] = x , and similarly for B . It follo ws that the running time is: O ( | R | · n 2 · ( n 1 /D ) · ( n 3 /D )) = O ( n 1 n 2 n 3 /L ) . 2. (Structur e d Part) Enumerate all ℓ ∈ [ L ] . W e compute the set X ℓ + Y ℓ (b y brute-force, sa y) and construct the matrices A ℓ [ i, k ] = ( A [ i, k ] if A [ i, k ] ∈ X ℓ , ⊥ otherwise, B ℓ [ k , j ] = ( B [ k , j ] if B [ k , j ] ∈ Y ℓ , ⊥ otherwise, C ℓ [ i, j ] = ( C [ i, j ] if C [ i, j ] ∈ X ℓ + Y ℓ , ⊥ otherwise. 30 Clearly each exact triangle in the structured part app ears in some instance ( A ℓ , B ℓ , C ℓ ) . T o pro ceed, w e distinguish tw o cases: 2.1. (Sp arse Case: | X ℓ | ≤ D /L 2 or | Y ℓ | ≤ D /L 2 ) In this case one of the matrices A ℓ or B ℓ is sparse. Indeed, suppose that | X ℓ | ≤ D /L 2 . Then A ℓ con tains at most n 1 n 2 /L 2 non- ⊥ entries, as it con tains at most | X ℓ | distinct en tries eac h of whic h appears in at most a 1 /D -fraction of the en tries (by the regularity assumption). W e thus solve the instance ( A ℓ , B ℓ , C ℓ ) by brute-force and place all exact triangles in T . R unning Time: O ( n 1 n 2 n 3 /L 2 ) per iteration, so time O ( n 1 n 2 n 3 /L ) in total. 2.2. (Dense Case: | X ℓ | ≥ D /L 2 and | Y ℓ | ≥ D /L 2 ) Let Z ℓ = X ℓ ∪ Y ℓ ∪ ( X ℓ + Y ℓ ) and observ e that all en tries in the three matrices A ℓ , B ℓ , C ℓ stem from the set Z ℓ . In the remainder we b ound the doubling of Z ℓ . The doubling of X ℓ can b e b ounded by one application of Ruzsa’s triangle inequalit y (Lemma 2.17 ): | X ℓ + X ℓ | ≤ | X ℓ + Y ℓ | | X ℓ + Y ℓ | | Y ℓ | ≤ O ( L 10 D 2 ) D /L 2 = O ( L 12 D ) = O ( L 14 ) | X ℓ | , It follows that X ℓ ∪ { 0 } has doubling O ( L 14 ) . Symmetrically , Y ℓ ∪ { 0 } has doubling O ( L 14 ) . But Z ℓ = ( X ℓ ∪ { 0 } ) + ( Y ℓ ∪ { 0 } ) , and thus Z ℓ has doubling at most O ( L 14 ) 8 = O ( L 112 ) b y Lemma 4.12 . (Again, w e ha ve not attempted to optimize this constan t.) W e pic k L = Θ( K 1 / 112 ) so that Z ℓ has doubling at most K . The Exact T riangle instance ( A ℓ , B ℓ , C ℓ ) is therefore a K -doubling (and D -uniform and 1 /D -regular) instance as desired, so we place it in I . R unning Time: O ( L · ( n 1 n 2 + n 2 n 3 + n 1 n 3 )) in total. It is clear that this is a p oten tial-adjusting reduction with |I | ≤ L ≤ O ( K ) (crudely b ounded). It remains to analyze the running time. The initial BSG Cov ering tak es time ˜ O ( D ω L ) = ˜ O ( D 3 L ) = ˜ O ( n 1 n 2 D L ) (crudely b ounding ω ≤ 3 and D ≤ n 1 , n 2 ), so summing ov er the running time of steps 1 and 2 as analyzed b efore the total running time is ˜ O n 1 n 2 n 3 L + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) D L = ˜ O n 1 n 2 n 3 K 1 / 112 + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) D K 1 / 112 , as claimed. 4.5 Putting the Pieces T ogether W e finally put Lemmas 4.10 and 4.13 together to complete the proof of Lemma 4.2 . Lemma 4.2 (Reduction from Lo w-Rank to Uniform Lo w-Doubling Exact T riangle) . F or any p ar ameter K ≥ 1 ther e is a p otential-adjusting r e duction fr om any r -rank Exact T riangle instanc e to K ( n 1 n 2 n 3 ) o (1) instanc es that ar e e ach D -uniform , 1 /D -regular and K -doubling for some D ≤ r . The r e duction runs in deterministic time ( n 1 n 2 n 3 /K 1 / 98000 + ( n 1 n 2 + n 1 n 3 + n 2 n 3 ) r K ) 1+ o (1) . In p articular: ExactT ri( n 1 , n 2 , n 3 | r ) ≤ K · ExactT ri( n 1 , n 2 , n 3 | D ≤ r ; ρ ≤ 1 /D ; K ) + n 1 n 2 n 3 K 1 / 98000 + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r K 1+ o (1) . Pro of. First run Lemma 4.10 on the given low-rank Exact T riangle instance with parameter t = K 1 / 98000 . Then transform each of the t 875 ( n 1 n 2 n 3 ) o (1) resulting uniform regular Exact T riangle instances by running 31 Lemma 4.13 with parameter K . This results in a set of t 875 ( n 1 n 2 n 3 ) o (1) · K 1 / 112 ≤ K ( n 1 n 2 n 3 ) o (1) instances that are uniform, regular and low-doubling as claimed. The total running time is n 1 n 2 n 3 t + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r t 875 + t 875 · n 1 n 2 n 3 K 1 / 112 + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r K 1 / 112 1+ o (1) = n 1 n 2 n 3 K 1 / 98000 + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r K 1+ o (1) . This completes the reduction and thus the pro of of Theorem 4.1 . 5 Univ erse Reductions for Min-Plus Pro duct In this section, w e develop the universe reductions for Min-Plus Product (and thereb y for APSP). The structure of this section is as follo ws: In Section 5.1 we recap a standard tric k from fine-grained complexit y . In Section 5.2 we give the universe reduction from small universes to even smaller universes (say from u = n to u = √ n ), pro ving Theorem 1.7 . In Section 5.3 we giv e the reduction from Min-Plus Pro duct to Uniform Lo w-Doubling Min-Plus Pro duct. And in Section 5.4 w e conclude the conditional universe reduction from p olynomially large to small univ erses, proving Theorem 1.13 . 5.1 Listing-to-Decision Reduction Before we start, we recap a standard listing-to-de cision r e duction that allo ws to transform any detection algorithm into an algorithm that also lists some “witnesses” for a quite general class of problems. In the con text of Min-Plus Pro duct, we call k a witness of ( A ∗ B )[ i, j ] if A [ i, k ] + B [ k , j ] = ( A ∗ B )[ i, j ] . Then: Lemma 5.1 (Listing-to-Decision Reduction for Min-Plus Pro duct) . L et ( A, B ) b e a Min-Plus Pr o duct in- stanc e, and assume that ther e is an algorithm c omputing the min-plus pr o duct A ′ ∗ B ′ of any r estrictions of A and B in time T . Then, for any p ar ameter t ≥ 1 , we c an c ompute lists of up to t witnesses for al l ( A ∗ B )[ i, j ] in r andomize d time ˜ O ( T t ) . Pro of Sk etch. The pro of is a by-no w standard argument from sparse reco very; we only give a quick sketc h here. Consider the restrictions A ′ and B ′ randomly obtained from A and B as follows. Sample ℓ ∈ [ ⌈ log n 2 ⌉ ] uniformly at random, then sample K ⊆ [ n 2 ] uniformly at random with rate 2 − ℓ . Let A ′ b e the matrix obtained from A by setting all columns k that are not present in K to ⊥ . It can b e shown that, for any fixed pair ( i, j ) , with probabilit y at least Ω(1 / log n 2 ) in the min-plus pro duct A ′ ∗ B exactly one witness of ( i, j ) is still presen t. In this case we say that ( i, j ) is suc c essful. Moreo ver, by symmetry this unique witness is sampled uniformly at random. W e now argue that by O (log n 2 ) calls to the fast algorithm we can identify the surviving witness for all successful pairs ( i, j ) . T o this end, identify each entry k ∈ [ n 2 ] with its L = ⌈ log n 2 ⌉ -bit binary representation. W e write k [ ℓ ] for the ℓ -th bit. Let A ′ ℓ b e the matrix obtained from A ′ where we replace the k -th column by ⊥ if k [ ℓ ] = 0 . W e compute the min-plus pro ducts A ′ ℓ ∗ B for all ℓ ∈ [ L ] . No w take any successful pair ( i, j ) , and insp ect the sequence ( A ′ 0 ∗ B )[ i, j ] , . . . , ( A ′ L ∗ B )[ i, j ] . Some of these v alues are exactly equal to ( A ∗ B )[ i, j ] , others are strictly larger—the length- L bit-string indicating the larger v alues is exactly the bit-representation of the unique witness k of ( i, j ) . In particular, for all successful pairs ( i, j ) we can read off (and verify) the surviving witness k . Ov erall, b y rep eating this pro cedure ˜ O ( t ) times, we exp ect to list ˜ O ( t ) uniformly random witnesses for eac h en try ( A ∗ B )[ i, j ] . Thereb y we either list t distinct witnesses (if they exist), or otherwise ha ve listed all witnesses with go o d probability . With exactly the same pro of one can also list witnesses for the Exact T riangle problem, see the following Lemma 5.2 . In this con text we call k a witness of C [ i, j ] if A [ i, k ] + B [ k , j ] = C [ i, j ] . Similarly , in this case j is a witness of A [ i, k ] and i is a witness of B [ k , j ] . 32 Lemma 5.2 (Listing-to-Decision Reduction for Exact T riangle) . L et ( A, B , C ) b e an Exact T riangle instanc e, and assume that ther e is an algorithm solving ( A ′ , B ′ , C ′ ) for any r estrictions A ′ of A , B ′ of B , and C ′ of C in time T . Then, for any p ar ameter t ≥ 1 , we c an c ompute lists of up to t witnesses for al l outputs A [ i, k ] , B [ k , j ] , C [ i, j ] in r andomize d time ˜ O ( T t ) . 5.2 Small-Univ erse Reduction W e start with the reduction from small universes { 0 , . . . , n } to even smaller univ erses { 0 , . . . , n α } (for any constan t α ≤ 1 ). The pro of of this universe reduction can b e split into tw o parts: dealing with the unp opular and p opular outputs. The first part is as in [ 35 ] without mo difications. The innov ation is to solve the second part with “lo w-rank APSP” instead of “F redman’s trick meets dominance pro duct”. Lemma 5.3 (Small-Univ erse Reduction) . F or al l p ar ameters n 1 , n 2 , n ′ 2 , n 3 , u, t with n ′ 2 ≤ n 2 , it holds that MinPlus( n 1 , n 2 , n 3 | u ) = ˜ O MinPlus( n 1 , n ′ 2 , n 3 | u ≤ n ′ 2 ) · n 2 t n ′ 2 + ExactT ri( n 1 , n 2 , n 3 | r ≤ u/t ) . Pro of. Let A, B b e the tw o given matrices. The first step is to apply a scaling trick to obtain an additive appro ximation ˜ C of the output matrix A ∗ B . T o this end, let A ′ b e the matrix obtained from A b y dropping the least significan t bits of all en tries (i.e., A ′ [ i, j ] = ⌊ A [ i, j ] / 2 ⌋ ), and similarly obtain B ′ from B . W e r e cursively compute the min-plus pro duct C ′ = A ′ ∗ B ′ and pick ˜ C = 2 C ′ . It is easy to verify that for all pairs ( i, j ) : ˜ C [ i, j ] ≤ ( A ∗ B )[ i, j ] ≤ ˜ C [ i, j ] + 2 . Let p = ⌈ n ′ 2 ⌉ and q = ⌈ u/n ′ 2 ⌉ . Without loss of generality , w e can assume that A [ i, k ] mo d q < q / 2 and B [ k , j ] mo d q < q / 2 b y the follo wing simple tric k. Partition A in to tw o submatrices, one con taining the en tries with A [ i, k ] mo d q < q / 2 and the other con taining all remaining entries. Subtract ⌈ q / 2 ⌉ from all en tries of the second matrix; then b oth submatrices are as claimed. Similarly partition B in to tw o parts. It remains to compute four min-plus pro ducts from which we can easily recov er the original product A ∗ B (by appropriately adding 0 , ⌈ q / 2 ⌉ , or 2 ⌈ q / 2 ⌉ to the resp ectiv e output matrices). No w view the matrices A and B in their “base- ( p, q ) ” representation, i.e., we rewrite the matrices as A = A 1 · q + A 0 , B = B 1 · q + B 0 , where A 0 , B 0 ha ve nonnegative entries less than q / 2 and where A 1 , B 1 ha ve nonnegative entries less than p . W e call k a witness of ( i, j ) if A [ i, k ] + B [ k , j ] = ( A ∗ B )[ i, j ] , and w e call k a pseudo-witness of ( i, j ) if A 1 [ i, k ] + B 1 [ k , j ] = ( A 1 ∗ B 1 )[ i, j ] . Importantly , note that each witness is also a pseudo-witness (as w e ha ve that ⌊ ( A [ i, k ] + B [ i, k ]) /q ⌋ = ⌊ A [ i, k ] /q ⌋ + ⌊ B [ i, k ] /q ⌋ , using that A 0 , B 0 ha ve entries less than q / 2 ). W e call ( i, j ) p opular if it has at least tn 2 /n ′ 2 pseudo-witnesses, and unp opular otherwise. In the follo wing t wo cases w e separately deal with the unp opular and p opular pairs ( i, j ) . Initially , let C b e the all- ⊥ matrix. 1. (Unp opular Pairs) T o deal with the unp opular pairs ( i, j ) , we will list al l pseudo-witnesses k of ( i, j ) . T o this end, repeat the following steps O ( tn 2 /n ′ 2 · log( n 1 n 3 )) times: 1.1. Sample a uniformly random subset K ⊆ [ n 2 ] with rate ρ = n ′ 2 / (2 tn 2 ) . The resulting set has size |K| ≤ O ( n ′ 2 /t ) ≤ O ( n ′ 2 ) with high probability . 1.2. Restrict A 1 to the columns in K , restrict B 1 to the rows in K , and compute the min-plus product of the resulting matrices. A dditionally , rep ort a witness k for eac h output pair ( i, j ) by Lemma 5.1 . (Note that a witness for A 1 ∗ B 1 is a pseudo-witness in our language.) W e up date C [ i, j ] ← min { C [ i, j ] , A [ i, k ] + B [ k , j ] } for eac h triple ( i, k , j ) rep orted in this wa y . 33 The correctness claim is that after step 1 is complete w e hav e correctly assigned C [ i, j ] = ( A ∗ B )[ i, j ] for all unp opular pairs ( i, j ) . Fix any such pair, and let k be a witness of ( i, j ) . In each iteration the probabilit y that w e include k into K is ρ , and independently the probabilit y that we miss all other pseudo-witnesses of ( i, j ) in K is at least 1 − ρtn 2 /n ′ 2 ≥ 1 / 2 , by a union b ound ov er the at most tn 2 /n ′ 2 pseudo-witnesses of ( i, j ) . Hence, with probability at least ρ/ 2 the only pseudo-witness of ( i, j ) in K is a prop er witness, and s o the algorithm is forced to list the triple ( i, k , j ) . Ov er the O ( ρ − 1 log( n 1 n 3 )) iterations this ev ent happ ens at least once for each unp opular pair ( i, j ) with high probability . R unning Time: ˜ O (MinPlus( n 1 , n ′ 2 , n 3 | u ≤ p ) · tn 2 /n ′ 2 ) . 2. (Popular Pairs) W e deal with the p opular pairs b y solving O (1) low-rank Exact T riangle instances. Sp ecifically , repeat the following steps for all offsets z ∈ { 0 , 1 , 2 } . Recall from the first paragraph that w e hav e access to a matrix ˜ C that approximates A ∗ B with small additive error, so in the z -th iteration our goal is to correctly assign C [ i, j ] = ( A ∗ B )[ i, j ] for all entries p opular pairs ( i, j ) with ( A ∗ B )[ i, j ] = ˜ C [ i, j ] + z . 2.1. Sample a uniformly random subset K ⊆ [ n 2 ] with rate Θ( n ′ 2 / ( tn 2 ) log ( n 1 n 3 )) . The resulting set has size |K | = ˜ O ( n ′ 2 /t ) with high probability . Moreov er, with high probability K contains at least one pseudo-witness for each popular pair ( i, j ) . 2.2. Let U 1 b e the matrix A 1 restricted to the columns in K , let V 1 b e the matrix B 1 restricted to the ro ws in K and compute their min-plus product R 1 = U 1 ∗ V 1 . Additionally , rep ort a witness k for each output en try ( i, j ) b y Lemma 5.1 . Let S 1 b e the matrix that stores these witnesses in the form S 1 [ i, j ] = k . Then observe that ( U 1 , V 1 , S 1 ) is a v alid rank- r 1 decomp osition of R 1 for r 1 = |K| = ˜ O ( n ′ 2 /t ) . R unning Time: ˜ O (MinPlus( n 1 , n ′ 2 , n 3 | u ≤ p )) . 2.3. Let R b e the n 1 × n 3 matrix defined b y R [ i, j ] = ( ˜ C [ i, j ] + z if ⌊ ( ˜ C [ i, j ] + z ) /q ⌋ = R 1 [ i, j ] , ⊥ otherwise. W e can now find a rank- r decomp osition of R for r = r 1 q . As outlined b efore, this step in- v olves trivially b ounding the select-plus rank of R − q · R 1 b y O ( q ) (F act 3.2 ) and then applying subm ultiplicativity (F act 3.3 ). Concretely , we compute the rank decomp osition ( U, V , S ) of R from the data we hav e precom- puted in step 2.2 as follows. Let U ∈ Z [ n 1 ] × ( K× [ q ]) b e the matrix obtained from q · U 1 ∈ Z [ n 1 ] ×K b y replacing each column by q copies, where in the ℓ -th copy we add ℓ to all entries. Next, we ob- tain V ∈ Z ( K× [ q ]) × [ n 3 ] from q · V 1 ∈ Z K× [ n 3 ] b y duplicating each ro w q times (but without further additions). Finally , define S b y S [ i, j ] = ( ( S 1 [ i, j ] , R [ i, j ] mod q ) if R [ i, j ] = ⊥ , ⊥ if R [ i, j ] = ⊥ . 34 Then, indeed, U has |K | q = r columns (and V has |K | q = r ro ws), and by construction w e hav e that R [ i, j ] = ˜ C [ i, j ] + z = ⌊ ˜ C [ i, j ] /q ⌋ · q + (( ˜ C [ i, j ] + z ) mo d q ) = R 1 [ i, j ] · q + ( R [ i, j ] mo d q ) = U 1 [ i, S 1 [ i, j ]] · q + ( R [ i, j ] mo d q ) + V 1 [ S 1 [ i, j ] , j ] · q = U [ i, S [ i, j ]] + V [ S [ i, j ] , j ] , for all non- ⊥ entries. Hence, ( U, V , S ) is a v alid rank- r decomp osition of R . R unning Time: ˜ O ( n 1 n 2 + n 1 n 3 + n 2 n 3 ) (negligible). 2.4. Solv e the r -Rank Exact T riangle instance ( A, B , R ) , and additionally rep ort a witness k for each output entry ( i, j ) b y Lemma 5.2 . Up date C [ i, j ] ← min { C [ i, j ] , A [ i, k ] + B [ k , j ] } for each such triple. R unning Time: ˜ O (ExactT ri( n 1 , n 2 , n 3 | r )) . W e argue that these steps correctly assign all p opular entries C [ i, j ] . In steps 2.1 and 2.2 we construct a matrix R 1 satisfying that ( A 1 ∗ B 1 )[ i, j ] = R 1 [ i, j ] for all p opular pairs (since, as noted b efore, K con tains a pseudo-witness with high probability). Let z ∈ { 0 , 1 , 2 } b e suc h that ( A ∗ B )[ i, j ] = ˜ C [ i, j ] + z . Recalling ⌊ ( A ∗ B )[ i, j ] /q ⌋ = ( A 1 ∗ B 1 )[ i, j ] , it follo ws that ⌊ ( ˜ C [ i, j ] + z ) /q ⌋ = R 1 [ i, j ] . W e therefore set R [ i, j ] = ˜ C [ i, j ] + z = ( A ∗ B )[ i, j ] , and thus ( i, j ) is in volv ed in an exact triangle in the instance ( A, B , R ) . It follows that we list a witness k of ( i, j ) and correctly assign C [ i, j ] in step 2.4 . This completes the algorithm and the correctness pro of, and we finally analyze the running time. Summing o ver the contributions of all steps (analyzed in the boxes), the total time indeed b ecomes ˜ O MinPlus( n 1 , n ′ 2 , n 3 | u ≤ n ′ 2 ) · n 2 t n ′ 2 + ExactT ri( n 1 , n 2 , n 3 | r ≤ u/t ) , where we hav e b ounded p = O ( n ′ 2 ) and r = r 1 q = ˜ O ( n ′ 2 /t · u/n ′ 2 ) = ˜ O ( u/t ) . (Moreov er, here we hav e omitted the negligible ov erhead of ˜ O ( n 1 n 2 + n 1 n 3 + n 2 n 3 ) for the v arious b ookkeeping steps as this time is necessarily dominated by the ExactT ri( n 1 , n 2 , n 3 ) call simply to read the input.) Finally , each recursiv e call reduces u b y a constan t factor. Th us, the recursion reac hes depth at most O (log u ) = O (log( n 1 n 2 n 3 )) and we incur an o verhead that is hidden in the ˜ O notation. Corollary 5.4. L et 0 < α ≤ 1 and ϵ > 0 b e c onstants. If MinPlus( n, n α , n | u ≤ n α ) = O ( n 2+ α − ϵ ) then the Str ong APSP Hyp othesis fails. Pro of. Supp ose that MinPlus( n, n α , n | u ≤ n α ) = O ( n 2+ α − ϵ ) for some ϵ > 0 . Theorem 4.1 states that ExactT ri( n, n, n | r ≤ n 3 − ω − ϵ/ 2 ) ≤ O ( n 3 − ϵ/ 500000 ) . Th us, from Lemma 5.3 with n 1 = n 2 = n 3 = n , n ′ 2 = n α , and t = n ϵ/ 2 w e get that MinPlus( n, n, n | u ≤ n 3 − ω ) = ˜ O MinPlus( n, n α , n | u ≤ n α ) · n 1 − α + ϵ/ 2 + ExactT ri( n, n, n | r ≤ n 3 − ω − ϵ/ 2 ) = ˜ O n 2+ α − ϵ · n 1 − α + ϵ/ 2 + n 3 − ϵ/ 500000 = ˜ O n 3 − ϵ/ 500000 . This con tradicts the Strong APSP Hypothesis. 35 Remark 5.5. The same pr o of shows that the pr emise, MinPlus( n, n α , n | u ≤ n α ) = O ( n 2+ α − ϵ ) , is equiv- alen t for al l α ∈ (0 , 1] , i.e., if the pr emise holds for some α ∈ (0 , 1] then it also holds for al l α ′ ∈ (0 , 1] , pr ovide d that ω = 2 . Curiously, this e quivalenc e statement was alr e ady establishe d for al l α ∈ (0 , 1) in pr e- vious work by Chan, V assilevska W., and Xu [ 35 , Cor ol lary 7.6]—only the e quivalenc e with α = 1 (i.e., the Str ong APSP har dness) was missing. Corollary 5.4 combined with the equiv alence of MinPlus( n, n µ , n | u ≤ n 1 − µ ) and directed unw eigh ted APSP due to [ 33 ] completes the pro of of Theorem 1.7 . In the following, w e quickly prov e the strengthening of Theorem 1.7 that Zwic k’s algorithm is b est-possible for arbitrary w eight b ounds provided that ω = 2 , Theorem 1.8 . F or the pro of we rely on the following simple generalization of [ 33 ]: Lemma 5.6. L et APSP( n | u ) denote the running time of APSP in n -vertex gr aphs with weights { 0 , . . . , u } . Then MinPlus( n, n 2 , n | u ) = O (APSP( n | u ≤ n 2 u/n )) for al l p ar ameters n 2 , u ≤ n . Pro of. Let A, B b e the giv en matrices of sizes n × n 2 and n 2 × n with entries in { 0 , . . . , u } ∪ {⊥} . Pic k the parameters q = ⌊ n 2 u/n ⌋ and p = 2 ⌈ n/n 2 ⌉ . Since pq ≥ u we can rewrite the matrices in their “ ( p, q ) -ary” represen tations A = A 1 · q + A 0 , B = B 1 · q + B 0 , where A 0 , B 0 ha ve entries in { 0 , . . . , q − 1 } ∪ {⊥} and A 1 , B 1 ha ve entries in { 0 , . . . , p − 1 } ∪ {⊥} . Next, w e construct a graph G as follows. The v ertices consist of three separate sets I ⊔ K ⊔ J . The sets I and J are each copies of [ n ] , and K is [ n 2 ] × {− p, . . . , p } . W e choose the edges as follo ws: F or each non- ⊥ entry A [ i, k ] w e insert an edge from i ∈ I to ( k , − A 1 [ i, k ]) ∈ K with w eight A 0 [ i, k ] . F or each non- ⊥ en try B [ k , j ] we insert an edge from ( k , B 1 [ k , j ]) ∈ K to j ∈ J with weigh t B 0 [ k , j ] . And finally we turn each of the vertex sequences ( k , − p ) , . . . , ( k , p ) into a directed path, where each edge along the path has weigh t q . W e claim that the min-plus product A ∗ B equals exactly the I -to- J distances in G . Indeed, the only directed paths from i ∈ I to j ∈ J take the form i, ( k , − A 1 [ i, k ]) , . . . , ( k , B 1 [ k , j ]) , j . The weigh t of suc h a path is exactly A 0 [ i, k ] (the first edge) plus B 0 [ k , j ] (the last edge) plus q · ( A 1 [ i, k ] + B 1 [ k , j ]) (the middle edges). In sum this is A [ i, k ] + B [ k , j ] , so the claim follo ws. Moreo ver, G is a graph on | I | + | K | + | J | ≤ n + O ( pn 2 ) + n = O ( n ) vertices, and the largest edge w eight in G is q ≤ n 2 u/n . Hence we can solve APSP on G in time APSP( n | u ≤ n 2 u/n ) and read off the desired min-plus product from the computed distances. Theorem 1.8 (Zwick’s Algorithm is Optimal) . L et 0 ≤ δ ≤ 1 b e a c onstant. APSP in dir e cte d gr aphs with weights { 0 , . . . , n δ } c annot b e solve d in time O ( n 2 . 5+ δ / 2 − ϵ ) (for any c onstant ϵ > 0 ), unless the Str ong APSP Hyp othesis fails. Pro of. Supp ose that APSP( n | u ≤ n δ ) = O ( n 2 . 5+ δ / 2 − ϵ ) for some constant ϵ > 0 . Then by Lemma 5.6 it follows that MinPlus( n, n 1 / 2+ δ / 2 , n | u ≤ n 1 / 2+ δ / 2 ) = O ( n 2 . 5+ δ / 2 − ϵ ) . This con tradicts the Strong APSP Hyp othesis by Corollary 5.4 (with α = 1 / 2 + δ / 2 ). Finally , we consider undirected graphs and pro ve that the Shoshan-Zwic k algorithm is best-p ossible conditioned on the Strong APSP Hyp othesis. Theorem 1.9 (Shoshan–Zwic k Algorithm is Optimal) . L et 0 ≤ δ ≤ 1 b e a c onstant. APSP in undir e cte d gr aphs with weights { 0 , . . . , n δ } c annot b e solve d in time O ( n 2+ δ − ϵ ) (for any c onstant ϵ > 0 ), unless the Str ong APSP Hyp othesis fails. Pro of. Supp ose that APSP in undirected graphs with weigh ts { 0 , . . . , n δ } is in time O ( n 2+ δ − ϵ ) . By a standard construction it follo ws easily that MinPlus( n, n, n | u < n δ / 2) = O ( n 2+ δ − ϵ ) . Indeed, w e transform the given pair of matrices A, B with entries less than u = n δ / 2 into an undirected graph with three vertex la yers I , K, J , where we set the weigh t of an y edge ( i, k ) ∈ I × K to A [ i, k ] + u and of any edge ( k , j ) ∈ K × J 36 to B [ k , j ] + u , and where w e delete all edges with A [ i, k ] = ⊥ or B [ k , j ] = ⊥ . Observe that the I - J distances in the resulting graph are exactly A ∗ B plus an additive offset of 2 u (except that for distances larger than 2 u whic h corresp ond to ⊥ -entries in A ∗ B ). The reason is that any path of length more than 2 has length at least 4 and thus w eight at least 4 u , whic h exceeds any entry in A ∗ B plus 2 u . But MinPlus( n, n, n | u < n δ / 2) = O ( n 2+ δ − ϵ ) con tradicts the Strong APSP Hypothesis by Corollary 5.4 applied with α = δ (observing that the constant factor 1 / 2 in the universe b ound can easily b e remov ed). 5.3 Doubling Reduction Next, we prov e the following “doubling reduction” which allows to reduce from arbitrary instances of Min-Plus Pro duct to Low-Doubling instances. Lemma 5.7 (Doubling Reduction) . F or al l p ar ameters n 1 , n 2 , n 3 , K with n 2 ≤ n 1 , n 3 it holds that: MinPlus( n 1 , n 2 , n 3 | u ) ≤ K · MinPlus( n 1 , n 2 , n 3 | u ; D ≤ n 2 ; ρ ≤ 1 /D ; K ) + n 1 n 2 n 3 K 1 / 300000 1+ o (1) · log u. Pro of. Let L = ⌈ log u ⌉ . The pro of of the lemma relies on a scaling trick ov er L scales, and requires some notational setup. In analogy to Lemma 5.3 , we call k a witness of ( A ∗ B )[ i, j ] if ( A ∗ B )[ i, j ] = A [ i, k ] + B [ k , j ] , and we call k an q -pseudo-witness if A [ i, k ] + B [ k , j ] < ( A ∗ B )[ i, j ] + q . (Note that the definition of pseudo- witness differs sligh tly from Lemma 5.3 .) F or each 0 ≤ ℓ ≤ L , define the matrices A ℓ = ⌊ A/ 2 ℓ ⌋ and B ℓ = ⌊ B / 2 ℓ ⌋ . W e partition each such matrix in to t wo submatrices, A ℓ = A ℓ, 0 ⊔ A ℓ, 1 , where A ℓ, 0 retains all en tries with A [ i, k ] mo d 2 ℓ < 2 ℓ − 1 , and A ℓ, 1 retains all other en tries. Similarly , partition B ℓ = B ℓ, 0 ⊔ B ℓ, 1 . A observ ation related to this scaling setup is the follo wing: Claim 5.8. F or e ach ( i, j ) ∈ [ n 1 ] × [ n 3 ] and e ach sc ale 0 ≤ ℓ ≤ L , ther e is some p air x, y ∈ { 0 , 1 } such that: (i) ( A ℓ,x ∗ B ℓ,y ) = ⌊ (( A ∗ B )[ i, j ] − ( x + y )2 ℓ − 1 ) / 2 ℓ ⌋ , (ii) some witness of ( A ℓ,x ∗ B ℓ,y )[ i, j ] is a witness of ( A ∗ B )[ i, j ] , and (iii) every witness of ( A ℓ,x ∗ B ℓ,y )[ i, j ] is a 2 ℓ -pseudo-witness of ( A ∗ B )[ i, j ] . Pro of. T o see this, let k ∗ b e an arbitrary witness of ( A ∗ B )[ i, j ] . By construction each non- ⊥ entry in A ℓ sho ws up either in A ℓ, 0 or A ℓ, 1 . T ak e x ∈ { 0 , 1 } such that A ℓ,x [ i, k ∗ ] = ⊥ . Similarly , take y ∈ { 0 , 1 } so that B ℓ,y [ k ∗ , j ] = ⊥ . Now consider an arbitrary k ∈ [ n 2 ] with A ℓ,x [ i, k ] = ⊥ and B ℓ,y [ k , j ] = ⊥ , and note that A ℓ,x [ i, k ] + B ℓ,y [ k , j ] = A [ i, k ] 2 ℓ + B [ k , j ] 2 ℓ = A [ i, k ] + B [ k , j ] − ( A [ i, k ] mo d 2 ℓ ) − ( B [ k , j ] mo d 2 ℓ ) 2 ℓ . By definition, A [ i, k ] mo d 2 ℓ falls into the range x 2 ℓ − 1 + [0 , 2 ℓ − 1 ) , and B [ k , j ] mod 2 ℓ is in y 2 ℓ − 1 + [0 , 2 ℓ − 1 ) . In particular, w e obtain the upper b ound A ℓ,x [ i, k ] + B ℓ,y [ k , j ] ≤ A [ i, k ] + B [ k , j ] − ( x + y )2 ℓ − 1 2 ℓ , and the lo wer b ound A ℓ,x [ i, k ] + B ℓ,y [ k , j ] > A [ i, k ] + B [ k , j ] − ( x + y )2 ℓ − 1 − 2 ℓ 2 ℓ = A [ i, k ] + B [ k , j ] − ( x + y )2 ℓ − 1 2 ℓ − 1 , Recalling that this is an integer, we m ust ha ve A ℓ,x [ i, k ] + B ℓ,y [ k , j ] = A [ i, k ] + B [ k , j ] − ( x + y )2 ℓ − 1 2 ℓ . 37 Therefore, k ∗ is a minimizer of this expression and th us a witness of ( A ℓ,x ∗ B ℓ,y )[ i, j ] , proving (ii) . Moreo v er, for eac h other witness k w e must hav e A [ i, k ] + B [ k , j ] < A [ i, k ∗ ] + B [ k ∗ , j ] + 2 ℓ , and thus k is a 2 ℓ -pseudo- witness, pro ving (iii) . Returning to the proof of Lemma 5.7 , w e are ready to state the reduction. W e classify the pairs ( i, j ) in to three categories based on their n umber of pseudo-witnesses: 1. If ( A ∗ B )[ i, j ] has at least t 1 -pseudo-witnesses (i.e., witnesses) then we call ( i, j ) exc eptional ly p opular . 2. If ( A ∗ B )[ i, j ] has at most t 2 L -pseudo-witnesses then w e call ( i, j ) exc eptional ly unp opular . 3. Otherwise we call ( i, j ) or dinary . F or eac h ordinary pair there is some level 0 ≤ ℓ < L such that ( i, j ) has at most t 2 ℓ -pseudo-witnesses and simultaneously at least t 2 ℓ +1 -pseudo-witnesses—w e say that ( i, j ) is r elevant at that level ℓ . These definitions are only required for the analysis, and w e do not compute the classification explicitly . W e will no w describe the algorithm. W e initially set C to b e the all- ⊥ matrix. Throughout we will only up date C via C [ i, j ] ← A [ i, k ] + B [ k , j ] , so we will never underestimate the v alues of A ∗ B . W e will deal with the exceptionally p opular, exceptionally unp opular and ordinary pairs in three separate steps. The first and esp ecially the second one can be regarded as exceptional sp ecial cases. 1. (Exc eptional ly Popular Pairs) Sample a uniformly random subset K ⊆ [ n 2 ] with rate Θ( t − 1 log( n 1 n 3 )) . Then en umerate all triples ( i, k , j ) ∈ [ n 1 ] × K × [ n 3 ] and up date C [ i, j ] ← min { C [ i, j ] , A [ i, k ] + B [ k , j ] } . Eac h exceptionally p opular pair ( i, j ) has at least t witnesses k , so with high probabilit y we include at least one suc h witness in K . In this case we correctly assign C [ i, j ] . R unning Time: ˜ O ( n 1 n 2 n 3 /t ) . 2. (Exc eptional ly Unp opular Pairs) By definition a pair ( i, j ) is exceptionally unp opular if it has less than t 2 L -pseudo-witnesses. But the matrices A L and B L in fact only contain t wo p ossible en tries: 0 and ⊥ . Hence, a pair ( i, j ) is exceptionally unp opular if and only if the num b er of indices k with A [ i, k ] = ⊥ and B [ k , j ] = ⊥ is at most t . One w ay to deal with these pairs is to apply Lemma 5.1 in combination with the fast algorithm for Min-Plus Pro duct to list t witnesses in the pro duct A L ∗ B L . (Ho wev er, this pro duct is of course just a Bo olean matrix multiplication, so one could hav e also solved this step in ˜ O ( t ) matrix pro ducts.) R unning Time: ˜ O ( t · MinPlus( n 1 , n 2 , n 3 | u ≤ 0)) . 3. (Or dinary Pairs) T o deal with the ordinary pairs, we prepare a low-rank matrix approximating A ∗ B (in a sense that will b e clear so on). Sample a uniformly random subset K ⊆ [ n 2 ] with rate Θ( t − 1 log( n 1 n 3 )) . Let U b e the submatrix of A restricted to the columns in K and let V b e the submatrix of B restricted to the rows in K . Compute the min-plus pro duct R = U ∗ V b y brute-force. Note that R is a matrix of rank at most r = |K | as is witnessed by the rank- r decomp osition ( U, V , S ) (for some appropriate matrix S that is easy to compute along the w a y). With high probabilit y , the rank is b ounded by r = |K| = ˜ O ( n 2 /t ) . R unning Time: ˜ O ( n 1 n 2 n 3 /t ) . Run the follo wing steps for all lev els 0 ≤ ℓ ≤ L , for all x, y ∈ { 0 , 1 } and all z ∈ { 0 , 1 , 2 , 3 } : 38 3.1. Let R ℓ,z = ⌊ R/ 2 ℓ ⌋ be the n 1 × n 3 matrix defined b y R ℓ,z [ i, j ] = R [ i, j ] 2 ℓ − z . Obtain a rank- r ′ = O ( r ) decomposition for R ℓ,z b y appropriately rounding the rank- r decompo- sition of R . Run Lemma 4.2 on the Exact T riangle instance ( A ℓ,x , B ℓ,y , R ℓ,z ) with parameter K . This is a p oten tial-adjusting reduction, and hence the output is ( I , T ) —a set of r ′ -uniform K - doubling Exact T riangle instances I and a set of sp ecial triples T ⊆ [ n 1 ] × [ n 2 ] × [ n 3 ] . Afterw ards, en umerate all triples ( i, k , j ) ∈ T and up date C [ i, j ] ← min { C [ i, j ] , A [ i, k ] + B [ k , j ] } . R unning Time: The O (1) calls to Lemma 4.2 tak e time n 1 n 2 n 3 K 1 / 98000 + ( n 1 n 2 + n 2 n 3 + n 1 n 3 ) r ′ K 1+ o (1) ≤ n 1 n 2 n 3 K 1 / 98000 + n 1 n 2 n 3 K t 1+ o (1) . F or the inequalit y we hav e used that n 2 ≤ n 1 , n 3 and that r ′ = O ( r ) = ˜ O ( n 2 /t ) . 3.2. En umerate all instances ( P ′ , Q ′ , R ′ ) ∈ I . Lemma 4.2 guaran tees that ( P ′ , Q ′ , R ′ ) is an D -uniform 1 /D -regular K -doubling Exact T riangle instance for some D ≤ r ′ . Hence, ( P ′ , Q ′ ) is an D - uniform 1 /D -regular K -doubling Min-Plus Pro duct instance. In fact, w e ma y loosely bound D ≤ r ′ = O ( r ) = O ( n 2 ) here. W e compute the min-plus pro duct P ′ ∗ Q ′ and list t witnesses for eac h output en try ( i, j ) b y Lemma 5.1 . F or eac h triple ( i, k , j ) reported in this wa y w e up date C [ i, j ] ← min { C [ i, j ] , A [ i, k ] + B [ k , j ] } . R unning Time: ˜ O ( |I | · t · MinPlus( n 1 , n 2 , n 3 | u ; D ≤ n 2 ; ρ ≤ 1 /D ; K )) ≤ ( K · t · MinPlus( n 1 , n 2 , n 3 | u ; D ≤ n 2 ; ρ ≤ 1 /D ; K )) 1+ o (1) . W e argue that w e correctly compute C [ i, j ] for all ordinary pairs ( i, j ) . Fix any such pair, and let ℓ b e a lev el at whic h ( i, j ) is relev an t. By definition, ( i, j ) has at least t 2 ℓ +1 -pseudo-witnesses. Thus, with high probability we include at least one 2 ℓ +1 -pseudo-witness in the randomly sampled set K . It follo ws that ( A ∗ B )[ i, j ] ≤ R [ i, j ] < ( A ∗ B )[ i, j ] + 2 ℓ +1 . Prop ert y (i) of Claim 5.8 further implies that there exist x, y ∈ { 0 , 1 } satisfying ( A ℓ,x ∗ B ℓ,y )[ i, j ] = ( A ∗ B )[ i, j ] − ( x + y )2 ℓ − 1 2 ℓ . Putting both statements together, we ha v e R [ i, j ] 2 ℓ − 3 ≤ ( A ℓ,x ∗ B ℓ,y )[ i, j ] ≤ R [ i, j ] 2 ℓ , and consequently , there is some z ∈ { 0 , 1 , 2 , 3 } such that ( A ℓ,x ∗ B ℓ,y )[ i, j ] = R ℓ,z [ i, j ] . In particular, for eac h witness k of ( A ℓ,x ∗ B ℓ,y )[ i, j ] , ( i, k , j ) forms an exact triangle in the instance ( A ℓ,x , B ℓ,y , R ℓ,z ) . Moreo ver, all these witnesses are 2 ℓ -pseudo-witnesses of ( A ∗ B )[ i, j ] by Prop ert y (iii) , and they include at least one prop er witness k ∗ of ( A ∗ B )[ i, j ] by Prop ert y (ii) . 39 W e argue that in the substeps 3.1 and 3.2 we en umerate all witnesses of ( A ℓ,x ∗ B ℓ,y )[ i, j ] , including the desired prop er witness k ∗ . Lemma 4.2 implemen ts a p otential-adjusting reduction. W e are th us guaran teed that each exact triangle in ( A ℓ,x , B ℓ,y , R ℓ,z ) app ears in T or it appears as an exact triangle in one of the instances in I . If the exact triangle ( i, k ∗ , j ) falls into the former case, w e successfully disco ver it in substep 3.1 . W e fo cus on the latter case. F o cus on the instance ( A ′ , B ′ , R ′ ) ∈ I in which the exact triangle ( i, k ∗ , j ) is presen t. Recall that this instance is a p oten tial adjustment of ( A ℓ,x , B ℓ,y , R ℓ,z ) , and th us A ′ [ i, k ] = A ℓ,x [ i, k ] + u [ i ] + v [ k ] or A ′ [ i, k ] = ⊥ for all ( i, k ) ∈ [ n 1 ] × [ n 2 ] , B ′ [ k , j ] = B ℓ,y [ k , j ] − v [ k ] + w [ j ] or B ′ [ k , j ] = ⊥ for all ( k, j ) ∈ [ n 2 ] × [ n 3 ] , R ′ [ i, j ] = R ℓ,z [ i, j ] + u [ i ] + w [ j ] or R ′ [ i, j ] = ⊥ for all ( i, j ) ∈ [ n 1 ] × [ n 3 ] , for some p oten tial functions u, v , w . F rom this it follows that ( A ′ ∗ B ′ )[ i, j ] = R ′ [ i, j ] . On the one hand, k ∗ witnesses ( A ′ ∗ B ′ )[ i, j ] ≤ R ′ [ i, j ] . On the other hand, we cannot hav e ( A ′ ∗ B ′ )[ i, j ] < R ′ [ i, j ] as then, rewriting A ′ , B ′ , R ′ b y the previous three identities, we would also hav e ( A ℓ,x ∗ B ℓ,y )[ i, j ] < R ℓ,z [ i, j ] , leading to a contradiction. No w, as ( A ′ ∗ B ′ )[ i, j ] = R ′ [ i, j ] , it follows that each witness k of ( A ′ ∗ B ′ )[ i, j ] m ust form an exact tri- angle ( i, k , j ) in ( P ′ , Q ′ , R ′ ) and thus also in ( A ℓ,x , B ℓ,y , R ℓ,z ) . Hence, k is a witness of ( A ℓ,x ∗ B ℓ,y )[ i, j ] , and Prop ert y (iii) implies that k is a 2 ℓ -pseudo-witness of ( i, j ) . Recall that we assume that ( i, j ) is relev an t at level ℓ , hence the total num b er of ℓ -pseudo-witnesses is at most t . Therefore, we are guar- an teed to list al l witnesses of ( A ′ ∗ B ′ )[ i, j ] by Lemma 5.1 (with high probability). In particular, w e will list the prop er witness k ∗ , and therefore up date C [ i, j ] as in tended. This completes the description of the reduction and the correctness analysis. Running Time. Summing ov er all O ( L ) = O (log u ) levels, the total time of the steps as analyzed ab o ve is K t · MinPlus( n 1 , n 2 , n 3 | u ; D ≤ n 2 ; ρ ≤ 1 /D ; K ) + n 1 n 2 n 3 K 1 / 98000 + n 1 n 2 n 3 K t 1+ o (1) · log u. Pic k t = K 1+1 / 98000 ≤ K 2 . The total running time b ecomes K 3 · MinPlus( n 1 , n 2 , n 3 | u ; D ≤ n 2 ; ρ ≤ 1 /D ; K ) + n 1 n 2 n 3 K 1 / 98000 1+ o (1) · log u, whic h is as claimed b y readjusting K to K 1 / 3 . Corollary 5.9. L et κ, ϵ > 0 and 0 < α 2 ≤ α 1 , α 3 b e c onstants. If MinPlus( n α 1 , n α 2 , n α 3 | D ≤ n α 2 ; ρ ≤ 1 /D ; K ≤ n κ ) ≤ O ( n α 1 + α 2 + α 3 − ϵ ) then the APSP Hyp othesis fails. Pro of. Supp ose that MinPlus( n α 1 , n α 2 , n α 3 | D ≤ n α 2 ; ρ ≤ 1 /D ; K ≤ n κ ) ≤ O ( n α 1 + α 2 + α 3 − ϵ ) , i.e., the D -uniform 1 /D -regular n κ -doubling Min-Plus Pro duct is in time O ( n α 1 + α 2 + α 3 − ϵ ) for all D ≤ n α 2 . Then by Lemma 5.7 applied with parameter K = n min { κ,ϵ/ 2 } the general Min-Plus Pro duct of size n α 1 × n α 2 × n α 3 o ver the universe [ u ] can b e solv ed in time MinPlus( n α 1 , n α 2 , n α 3 | u ) ≤ MinPlus( n α 1 , n α 2 , n α 3 | u ; D ≤ n α 2 ; K ≤ n κ ) · n ϵ/ 2 + n α 1 + α 2 + α 3 n min { κ,ϵ/ 2 } / 300000 1+ o (1) · log u ≤ n α 1 + α 2 + α 3 − ϵ/ 2 + n α 1 + α 2 + α 3 − min { κ,ϵ/ 2 } / 300000 1+ o (1) · log u ≤ n α 1 + α 2 + α 3 − min { κ,ϵ/ 2 } / 300000+ o (1) · log u. 40 In particular, for any p olynomially b ounded universe u ≤ n c (where c is constant) the running time b ecomes truly sub cubic, O ( n α 1 + α 2 + α 3 − γ ) for any constant 0 < γ < min { κ, ϵ/ 2 } / 300000 . This con tradicts the APSP Hyp othesis. Corollary 5.9 also immediately implies Theorem 1.10 : APSP reduces to Min-Plus Pro duct, whic h reduces to n -Uniform n κ -Doubling Min-Plus Pro duct b y Theorem 1.10 , which in turn can be seen as an APSP instance on a 3-la yered graph with at most n distinct w eights and doubling n κ . F or many lo wer b ounds the follo wing simpler corollary (that ignores the regular and low-doubling constraints) turns out to b e sufficient. Corollary 5.10. L et ϵ > 0 and 0 < α 2 ≤ α 1 , α 3 b e c onstants. If MinPlus( n α 1 , n α 2 , n α 3 | D ≤ n α 2 ) ≤ O ( n α 1 + α 2 + α 3 − ϵ ) then the APSP Hyp othesis fails. 5.4 Large-Univ erse Reduction In this subsection w e finally provide the missing reduction from p olynomially large univ erses { 0 , . . . , n O (1) } to { 0 , . . . , n } , conditioned on the additive combinatorics assumption Hyp othesis 1.12 ; we refer to App endix A for a discussion of this h yp othesis. T o effectiv ely apply Hyp othesis 1.12 w e rely on the following greedy co vering lemma. Lemma 5.11 (Greedy Co vering) . Ther e is an algorithm that, given X, Y ⊆ Z , c omputes a set S ⊆ Z of size at most | Y − X | / | Y | · ln | X | such that X ⊆ Y + S . It runs in deterministic time | Y − X | | S | · (log u ) O (1) , wher e u is an upp er b ound on the lar gest inte ger in X , Y in absolute value. Pro of. W e run a simple greedy algorithm. Initialize S ← ∅ . While X = ∅ we compute a shift s ∈ Z that maximizes r Y − X ( s ) . W e update S ← S ∪ { s } and X ← X \ ( Y + s ) . When the algorithm terminates, w e return S . It is clear that when the algorithm terminates the set S is as desired. It remains to b ound | S | , i.e., to b ound the num ber of iterations. Let X 0 denote the initial set X . W e show that with each iteration of the algorithm remov es at least a | Y | / | Y − X 0 | -fraction of the elements from X ; from this it follows easily that after | Y − X 0 | / | Y | · ln | X 0 | iterations the set X m ust be empty . T o see this, observ e that X s ∈ Y − X r Y − X ( s ) = | X | | Y | , and hence there is some s ∈ Y − X with r Y − X ( s ) ≥ | X | | Y | | Y − X | ≥ | X | | Y | | Y − X 0 | . This shift s witnesses that the algorithm decreases the size of | X | by at least a | Y | / | Y − X 0 | -fraction as desired. W e finally consider the running time. By Lemma 2.18 w e can compute the set Y − X along with all m ultiplicities r Y − X ( · ) in deterministic time O ( | Y − X | · (log u ) O (1) ) . Finding s and updating S and X then runs in time O ( | Y − X | ) . W e rep eat this ov er | S | iterations, leading to the claimed total time. Remark 5.12. This lemma r elates to the wel l-known “Ruzsa’s Covering L emma” [ 86 ]; se e [ 94 , L emma 2.14]. That fundamental r esult alternatively c overs X by shifts of Y − Y (inste ad of Y ) but achieves | S | ≤ | Y − X | / | Y | (without the lo garithmic factor). Equipp ed with Lemma 5.11 , w e no w sho w that Hypothesis 1.12 implies a reduction from lo w-doubling Min-Plus Product to small-universe Min-Plus Pro duct. Lemma 5.13. Assuming Hyp othesis 1.12 ther e is a c onstant c such that for al l p ar ameters n 1 , n 2 , n 3 , K with n 2 ≤ n 1 n 3 : MinPlus( n 1 , n 2 , n 3 | D ≤ n 2 ; K ) = ˜ O ( K c · MinPlus( n 1 , n 2 , n 3 | u ≤ n 2 )) . 41 Pro of. T o b ound MinPlus( n 1 , n 2 , n 3 | D ≤ n 2 ; K ) w e design an algorithm for the n 2 -uniform K -doubling Min-Plus Pro duct problem of size n 1 × n 2 × n 3 . Let A, B ∈ ( X ∪ {⊥} ) n × n b e the giv en matrices where X ⊆ Z denotes their set of in teger en tries, i.e., | X | ≤ n 2 and | X + X | ≤ K | X | . Our goal is to compute their pro duct C . W e first use the algorithm from Hyp othesis 1.12 to compute a set Y ⊆ X of size | Y | ≥ | X | /K c and a sum-order-preserving additiv e hash function h : Y → { 0 , . . . , | X |} . Then apply Lemma 5.11 to construct a set S satisfying that X ⊆ Y + S . W e en umerate all pairs s, t ∈ S , and for eac h such pair construct the follo wing tw o matrices: A s [ i, k ] = ( h ( A [ i, k ] − s ) if A [ i, k ] − s ∈ Y , ⊥ otherwise, B t [ k , j ] = ( h ( B [ k , j ] − t ) if B [ k , j ] − t ∈ Y , ⊥ otherwise. Clearly this is w ell-defined—we only apply h to elements in Y . Moreo ver, the Min-Plus Product instance ( A s , B t ) has a univ erse size of | X | ≤ n 2 . W e solv e the instance and report for each output pair ( i, j ) a witness k b y Lemma 5.1 . W e up date C [ i, j ] ← min { C [ i, j ] , A [ i, k ] + B [ k , j ] } for each triple ( i, k , j ) listed in this w ay . Correctness. Fix any pair ( i, j ) and let k be a witness of ( i, j ) . W e hav e that A [ i, k ] , B [ k , j ] ∈ X ⊆ Y + S , hence there are s, t ∈ S such that A [ i, k ] − s, B [ k , j ] − t ∈ Y . In particular, we hav e that A s [ i, k ] = h ( A [ i, k ] − s ) and B t [ k , j ] = h ( B [ k , j ] − t ) , so it follo ws that ( A s ∗ B t )[ i, j ] ≤ h ( A [ i, k ] − s ) + h ( B [ k , j ] − t ) . Con versely , for an y non-witness k ′ w e hav e A [ i, k ] + B [ k , j ] < A [ i, k ′ ] + B [ k ′ , j ] and th us ( A [ i, k ] − s ) + ( B [ k , j ] − t ) < ( A [ i, k ′ ] − s ) + ( B [ k ′ , j ] − t ) . As the function h is sum-order-preserving, it follows that h ( A [ i, k ] − s ) + h ( B [ k , j ] − t ) < h ( A [ i, k ′ ] − s ) + h ( B [ k ′ , j ] − t ) , or equiv alen tly , A s [ i, k ] + B t [ k , j ] < A s [ i, k ′ ] + B t [ k ′ , j ] (unless one of these entries is ⊥ ). Thus, k ′ is not a witness of ( A s ∗ B t )[ i, j ] . All in all, this prov es that k is a witness of ( A ∗ B )[ i, j ] if and only if k is a witness of min s,t ∈ S ( A s ∗ B t )[ i, j ] . Therefore, the algorithm is forced to en umerate a proper witness k of ( A ∗ B )[ i, j ] and to correctly assign C [ i, j ] . Running Time. First we compute the set Y ⊆ X and the hash function h in time | X | 1+ o (1) · K c ′ , for some constan t c ′ , by Hyp othesis 1.12 . Then w e apply Lemma 5.11 which runs in time | Y − X | | S | · (log u ) O (1) . By the Plünneck e-Ruzsa inequalit y (Lemma 2.16 ) we can b ound | Y − X | ≤ | X − X | ≤ K 2 | X | . The set S is promised to hav e size | S | ≤ O ( | Y − X | / | Y | · log | X | ) ≤ O ( K 2 | X | / | Y | · log | X | ) b y Lemma 5.11 , which, using the b ound | Y | ≥ | X | /K c from Hyp othesis 1.12 , is at most O ( K c +2 log | X | ) . Hence, this step tak es time at most | X | · K c +4 (log u ) O (1) . Then we enumerate all | S | 2 ≤ O ( K 2 c +4 log 2 | X | ) pairs s, t ∈ S , and for eac h pair solv e an n 2 -univ erse Min-Plus pro duct instance. The total time is: ˜ O | X | 1+ o (1) · K c ′ + | X | · K c +4 + K 2 c +4 · MinPlus( n 1 , n 2 , n 3 | u ≤ n 2 ) Recall that | X | ≤ n 2 . Therefore, the lemma statement follo ws for the constan t that is the maxim um of c ′ and 2 c + 4 . 42 Remark 5.14. As is app ar ent fr om the pr o of, L emma 5.13 stil l holds even if the algorithm to c ompute Y and h in Hyp othesis 1.12 is slower than | X | 1+ o (1) K O (1) . A ny algorithm in time | X | 3 − Ω(1) K O (1) would suffic e. The proof of Theorem 1.13 (restated next) is no w a simple com bination of Lemmas 5.7 and 5.13 . Theorem 1.13 (APSP Conditionally Implies Strong APSP) . Conditione d on Hyp othesis 1.12 , ther e is a sub cubic r e duction fr om APSP to APSP over the universe { 0 , . . . , n } . In p articular, c onditione d on Hyp oth- esis 1.12 and on the assumption that ω = 2 , the APSP and Str ong APSP Hyp otheses ar e e quivalent. Pro of. It is clear that the Strong APSP Hyp othesis implies the APSP Hyp othesis. F or the other direction assume that MinPlus( n, n, n | u ≤ n ) = O ( n 3 − ϵ ) . This is in particular the case if the Strong APSP Hyp othesis fails and if simultaneously ω = 2 . A dditionally assume Hyp othesis 1.12 . Under these assumptions it follows that: MinPlus( n, n, n | u ) = K · MinPlus( n, n, n | u ; D ≤ n ; K ) + n 3 K 1 / 300000 1+ o (1) · log u (Lemma 5.7 ) = K c +1 · MinPlus( n, n, n | u ≤ n ) + n 3 K 1 / 300000 1+ o (1) · log u (Lemma 5.13 ) = K c +1 n 3 − ϵ + n 3 K 1 / 300000 1+ o (1) · log u, where c is the constan t from Lemma 5.13 and K is an arbitrary parameter. S etting K = n ϵ/ (2 c +2) , the running time b ecomes n 3 − ϵ/ (600000 c +600000)+ o (1) · log u , which, recalling that u = n c ′ for some arbitrarily large constan t c ′ , is truly sub cubic as claimed. Remark 5.15. The statement of The or em 1.13 r emains valid when assuming the we aker Hyp othesis A.3 inste ad (state d in App endix A ). That hyp othesis le ads to an overhe ad of | X | ϵ ≤ n ϵ for an arbitr arily smal l c onstant ϵ > 0 , and the c onstant c fr om b efor e would dep end on ϵ (i.e., c = c ( ϵ ) ). 6 Lo w er Bounds for In termediate Problems In this section, w e deriv e APSP-based low er b ounds for v arious graph and matrix problems with in termediate complexit y . The pro ofs in this section are mostly tec hnically simple consequences of Corollary 5.9 or 5.10 . 6.1 No de-W eigh ted APSP Recall that no de-w eighted APSP can b e solved in time ˜ O ( n (3+ ω ) / 2 ) [ 31 , 102 , 4 ], ev en in directed graphs. Chan, V assilevsk a W., and Xu [ 36 ] gav e an n 2 . 5 − o (1) lo wer b ound based on the Directed Un weigh ted APSP Hyp othesis, ev en for undirected graphs. Here, w e strengthen this low er boun d to b e based on the APSP Hyp othesis. Theorem 1.14 (No de-W eighted APSP) . APSP in undir e cte d no de-weighte d gr aphs c annot b e solve d in time O ( n 2 . 5 − ϵ ) (for any c onstant ϵ > 0 ), unless the APSP Hyp othesis fails. Pro of. Supp ose that No de-W eighted APSP is in time O ( n 2 . 5 − ϵ ) for some ϵ > 0 ; we sho w that in this case MinPlus( n, √ n, n | D ≤ √ n ) = O ( n 2 . 5 − ϵ ) whic h contradicts the APSP Hyp othesis by Corollary 5.10 . Let n be a square num b er, and let A ∈ ( X ∪ {⊥} ) n × √ n and B ∈ ( X ∪ {⊥} ) √ n × n b e the given matrices, where X ⊆ Z is a set of size √ n . W e construct a 4-lay ered undirected no de-w eighted graph G on 4 n no des as follo ws: • (V ertic es) The v ertices consist of four distinct lay ers: I = [ n ] (the first lay er), K 1 = [ √ n ] × X (the second la yer), K 2 = [ √ n ] × X (the third lay er), and J = [ n ] (the fourth la yer). 43 • (Edges) F or each A [ i, k ] = ⊥ we add an edge ( i, ( k , A [ i, k ])) ∈ I × K 1 , and for eac h B [ k , j ] = ⊥ w e add an edge (( k, B [ k , j ]) , j ) ∈ K 2 × J . Finally , add all edges (( k , x 1 ) , ( k , x 2 )) ∈ K 1 × K 2 . • (No de W eights) Let u = max x ∈ X | x | . All no des in I and J hav e w eight 10 u . All no des ( k , x ) in K 1 and K 2 ha ve weigh t 10 u + x . W e compute the pairwise distances in G in time O ( n 2 . 5 − ϵ ) , and claim that the resulting distances b et w een an y pair of no des i ∈ I and j ∈ J is exactly ( A ∗ B )[ i, j ] + 40 u . Indeed, whenever k is a witness of ( A ∗ B )[ i, j ] then the nodes ( i, ( k , A [ i, k ]) , ( k , B [ k , j ]) , j ) ∈ I × K 1 × K 2 × J form a path of w eight 10 u + (10 u + A [ i, k ]) + (10 u + B [ k , j ]) + 10 u = ( A ∗ B )[ i, j ] + 40 u. Con versely , all i - j -paths of w eight less than 42 u necessarily hav e at most 3 edges, and th us ha ve the form ( i, ( k ′ , w 1 ) , ( k ′ , w 2 ) , j ) ∈ I × K 1 × K 2 × J . But then A [ i, k ′ ] = x 1 and B [ k ′ , j ] = x 2 , and th us ( A ∗ B )[ i, j ] ≤ w 1 + w 2 . W e finally c haracterize the complexity of no de-w eighted APSP in graphs with small w eights { 0 , . . . , u } (conditioned on the Strong APSP Hyp othesis). The c haracterization of directed graphs is easy: Even for un weigh ted directed graphs (i.e., u = 1 ) w e cannot beat time O ( n 2 . 5 ) without breaking the Strong APSP Hyp othesis (Theorem 1.7 ). F or no de-w eighted graphs, the fastest-known APSP algorithm runs in time ˜ O (min { n (3+ ω ) / 2 , n ω u } ) (up to impro vemen ts from rectangular matrix multiplication), by combining the ˜ O ( n (3+ ω ) / 2 ) -time algorithm for general no de weigh ts by [ 4 ], with Shoshan and Zwick’s ˜ O ( n ω u ) -time algorithm for small edge weigh ts [ 90 ]. W e sho w that this time is optimal (if ω = 2 ), conditioned on the Strong APSP Hyp othesis: Theorem 6.1 (Node-W eigh ted APSP with Small W eigh ts) . L et δ ≥ 0 . APSP in undir e cte d no de-weighte d gr aphs with weights in { 0 , . . . , n δ } c annot b e solve d in time O ( n min { 2 . 5 , 2+ δ }− ϵ ) (for any c onstant ϵ > 0 ), unless the Str ong APSP Hyp othesis fails. Pro of. The statemen t is trivially true for δ = 0 (as it is impossible for any sub quadratic-time algorithm to write do wn the n 2 pairwise distances). So supp ose that δ > 0 , and choose α = min { 1 / 2 , δ } > 0 . W e sho w that an O ( n min { 2 . 5 , 2+ δ }− ϵ ) = O ( n 2+ α − ϵ ) -time algorithm for undirected no de-w eighted APSP implies that MinPlus( n, n α , n | u ≤ n α ) = O ( n 2+ α − ϵ ) , whic h con tradicts the Strong APSP Hyp othesis by Corollary 5.4 . F or this reduction we mimic the pro of of Theorem 1.14 almost exactly . Sp ecifically , giv en matrices A, B of sizes n × n α and n α × n with entries b ounded by u = n α , we construct the same undirected graph on the four vertex parts I = [ n ] , K 1 = [ n α ] × X , K 2 = [ n α ] × X , J = [ n ] , where X = { 0 , . . . , u } denotes the set of weigh ts. Analogously , the num b er of no des is at most | I | , | J | ≤ n and | K 1 | , | K 2 | ≤ O ( n 2 α ) ≤ O ( n ) , and the I - J -distances enco de the min-plus pro duct A ∗ B . Notably , this time the node w eights are bounded b y O ( u ) = O ( n α ) . Therefore, we can solv e this constructed instance in time O ( n 2+ α − ϵ ) , leading to the desired con tradiction. 6.2 Min Pro duct Min Pro duct is a particularly simple intermediate matrix pro duct problem, equiv alen t to the restriction of Min-Plus Pro duct where one matrix consists only of entries { 0 , ⊥} . This problem was studied b efore in [ 4 ] (under the name Bo ole an Min-Plus Pro duct). While perhaps not as important in its own right, one can easily conclude the hardness of other intermediate problems from the hardness of Min Pro duct. Definition 6.2 (Min Pro duct) . The min pro duct of two matric es A ∈ Z n × n and B ∈ { 0 , 1 } n × n is the matrix C ∈ Z n × n define d by C [ i, j ] = min k ∈ [ n ] B [ k,j ]=1 A [ i, k ] . The Min Pro duct pr oblem is to c ompute the min pr o duct of two given matric es A, B . 44 Lemma 6.3 (Min Pro duct) . Min Pr o duct c annot b e solve d in time O ( n 2 . 5 − ϵ ) (for any c onstant ϵ > 0 ), unless the APSP Hyp othesis fails. Pro of. Supp ose that Min Pro duct can b e solved in time O ( n 2 . 5 − ϵ ) for some ϵ > 0 ; we sho w that in this case MinPlus( n, √ n, n | D ≤ √ n ) = O ( n 2 . 5 − ϵ ) whic h contradicts the APSP Hyp othesis by Corollary 5.10 . Let A, B denote the tw o given matrices of sizes n × √ n and √ n × n (assuming that n is a square n umber at the cost of doubling n in the worst case), and let X ⊆ Z b e the set of entries appearing in A and B ; we assume that | X | ≤ √ n . Our goal is to compute the min-plus pro duct A ∗ B . Construct the matrices n × n matrices A ′ , B ′ as follo ws, where w e index the inner dimension b y pairs [ √ n ] × X : A ′ [ i, ( k , x )] = A [ i, k ] + x, B ′ [( k , x ) , j ] = ( 1 if B [ k , j ] = x , 0 otherwise. Note that the min pro duct C ′ of A ′ and B ′ satisfies that C ′ [ i, j ] = min ( k,x ) ∈ [ √ n ] × X B ′ [( k,x ) ,j ]=1 A ′ [ i, ( k , x )] = min ( k,x ) ∈ [ √ n ] × X B [ k,j ]= x ( A [ i, k ] + x ) = min k ∈ [ √ n ] ( A [ i, k ] + B [ k , j ]) , and thus C ′ = A ∗ B is the desired min-plus pro duct. The matrices A ′ and B ′ can b e constructed in time ˜ O ( n 2 ) , so the total time is dominated by the Min Pro duct computation in time O ( n 2 . 5 − ϵ ) as claimed. 6.3 Min-Max Pro duct Next, we consider the Min-Max Pro duct problem which was studied in the con text of All-Pairs Bottleneck P aths and All-Pairs Nondecreasing Paths. W e show that Duan and Pettie’s ˜ O ( n (3+ ω ) / 2 ) -time algorithm [ 49 ] is best-p ossible (if ω = 2 ), conditioned on the APSP Hyp othesis. Definition 6.4 (Min-Max Product) . The min-max pro duct of two matric es A, B ∈ Z n × n is the matrix C ∈ Z n × n define d by C [ i, j ] = min k ∈ [ n ] max { A [ i, k ] , B [ k , j ] } . The Min-Max Pro duct pr oblem is to c ompute the min-max pr o duct of two given matric es A, B . Lemma 6.5 (Min-Max Pro duct) . Min-Max Pr o duct c annot b e solve d in time O ( n 2 . 5 − ϵ ) (for any c onstant ϵ > 0 ), unless the APSP Hyp othesis fails. Pro of. The pro of is almost immediate by Lemma 6.3 : The min pro duct of tw o matrices A and B can b e expressed as the min-max pro duct of the matrices A and B ′ , where B ′ is obtained from B b y replacing 1 with −∞ and 0 by ∞ . This lo wer bound entails v arious other low er b ounds. By the known equiv alence [ 95 ] we conclude our lo wer b ound for All-Pairs Bottlenec k P aths (Theorem 1.15 ). Moreo ver, from known reductions [ 96 ] it follows that also the Min- ≤ Pro duct and the All-Pairs Nondecreasing Paths problems cannot b e solv ed in time O ( n 2 . 5 − ϵ ) unless the APSP Hypothesis fails, matc hing their resp ective upp er b ounds if ω = 2 [ 96 , 47 , 48 ]. Lemma 6.5 also implies a matc hing low er b ound for the All-Edges Mono c hromatic Equalit y T riangle problem studied in [ 98 ]. 6.4 Min-Equalit y Pro duct Min-Equalit y Pro duct is y et another matrix problem with in termediate complexity ˜ O ( n (3+ ω ) / 2 ) , first in tro- duced by V assilevsk a W. and Xu in [ 98 ]. An interesting aspect of the problem is that it naturally generalizes the Equalit y Product problem whic h is one of the few in termediate problems for which we currently cannot pro ve conditional low er b ounds. 45 Definition 6.6 (Min-Equalit y Product) . The min-equality pro duct of two matric es A, B ∈ Z n × n is the matrix C ∈ Z n × n define d by C [ i, j ] = min { A [ i, k ] : k ∈ [ n ] , A [ i, k ] = B [ k , j ] } . The Min-Equalit y Product pr oblem is to c ompute the min-e quality pr o duct of two given matric es A, B . Lemma 6.7 (Min-Equality Pro duct) . Min-Equality Pr o duct c annot b e solve d in time O ( n 2 . 5 − ϵ ) (for any c onstant ϵ > 0 ), unless the APSP Hyp othesis fails. Pro of. Supp ose that Min-Equality Pro duct is in time O ( n 2 . 5 − ϵ ) for some ϵ > 0 . W e show that in this case MinPlus( n, √ n, n | D ≤ √ n ; K ≤ n ϵ/ 4 ) = O ( n 2 . 5 − ϵ/ 2 ) whic h contradicts the APSP Hyp othesis b y Corollary 5.9 (applied with parameters ϵ ′ = ϵ/ 2 , κ = ϵ/ 4 and α 1 = 1 , α 2 = 1 / 2 , α 3 = 1 ). Let n b e a square num b er, let A, B b e the giv en matrices of sizes n × √ n and √ n × n , respectively , and let X ⊆ Z denote the set of en tries that app ear in A and B . W e assume that | X | ≤ √ n and | X + X | ≤ K | X | for some K ≤ n ϵ/ 4 . First compute Z = X − X (e.g., by brute-force), and recall that b y the Plünneck e-Ruzsa inequalit y (Lemma 2.16 ) w e hav e | X − X | ≤ K 2 | X | ≤ n 1 / 2+ ϵ/ 2 . Construct the augmen ted matrices A ′ , B ′ indexed by [ n ] × ([ √ n ] × Z ) and ([ √ n ] × Z ) × [ n ] , resp ectively , defined b y A ′ [ i, ( k , z )] = 2 A [ i, k ] − z , B ′ [( k , z ) , j ] = 2 B [ k , j ] + z . W e compute their min-equality pro duct C and claim that C = A ∗ B is exactly the desired min-plus pro duct. On the one hand, w e ha ve that A ′ [ i, ( k , z )] = B ′ [( k , z ) , j ] if and only if z = A [ i, k ] − B [ k , j ] . In this case w e hav e A ′ [ i, ( k , z )] = 2 A [ i, k ] − z = A [ i, k ] + B [ k , j ] , and thus C ≥ A ∗ B . On the other hand, fo cus on an y witness ( A ∗ B )[ i, j ] = A [ i, k ] + B [ k , j ] . Then clearly z = A [ i, k ] − B [ k , j ] ∈ X − X = Z , and thus by construction C [ i, j ] ≤ A [ i, k ] + B [ k , j ] , and therefore C ≤ A ∗ B . The claim follows. Finally , consider the running time. The matrices A ′ , B ′ ha ve size n × n 1+ ϵ/ 2 and n 1+ ϵ/ 2 × n , resp ectiv ely . W e can partition the inner dimension in to O ( n ϵ/ 2 ) blo c ks of size n and thereb y compute the rectangular min-equalit y pro duct of A ′ and B ′ b y n ϵ/ 2 square computations, each running in time O ( n 2 . 5 − ϵ ) . The total time is O ( n 2 . 5 − ϵ/ 2 ) as claimed. 6.5 Bounded-Difference and Monotone Min-Plus Pro duct Next, we consider the restriction of the Min-Plus Pro duct problem to b ounde d-differ enc e or, more generally , monotone matrices defined as follo ws. Definition 6.8 (Bounded Difference) . A matrix A ∈ Z n × n is row-bounded-difference if | A [ i, j ] − A [ i, j + 1] | ≤ O (1) for al l i, j . Similarly, A is column-b ounded-difference if | A [ i, j ] − A [ i + 1 , j ] | ≤ O (1) for al l i, j . A is b ounded-difference if it is b oth r ow- and c olumn-b ounde d-differ enc e. Definition 6.9 (Monotone) . A matrix A ∈ Z n × n is ro w-monotone if 0 ≤ A [ i, 1] ≤ · · · ≤ A [ i, n ] ≤ O ( n ) for al l r ows i . Similarly, A is column-monotone if 0 ≤ A [ n, j ] ≤ · · · ≤ A [1 , j ] ≤ O ( n ) for al l c olumns j . A is monotone if it is b oth r ow- and c olumn-monotone. Bringmann, Grandoni, Saha, and V assilevsk a W. [ 25 ] designed the first sub cubic-time algorithm for b ounded-difference Min-Plus Pro duct, which they used to derive sub cubic-time algorithms for v arious string problems like language edit distance and RNA-folding. Mao [ 78 ] later similarly applied their algorithm to un weigh ted tree edit distance. Motiv ated by these applications, a line of research [ 99 , 61 , 43 , 44 ] sough t to optimize the running time of b ounded-difference and monotone Min-Plus Pro duct. This line culminated only recen tly in an ˜ O ( n (3+ ω ) / 2 ) -time algorithm due to Chi, Duan, Xie, and Zhang [ 44 ]. Sp ecifically , they design t wo differen t algorithms—one to compute the min-plus pro duct of a r ow-monotone matrix A and an unconstrained matrix B , and another one for a c olumn-monotone matrix A and an unconstrained matrix B . 46 It has remained op en if these algorithms are b est-possible. In this section we show that the first algorithm is conditionally optimal (if ω = 2 ); it remains an interesting op en question if the second algorithm is similarly optimal. Theorem 1.16 (Row-Bounded-Difference Row-Monotone Min-Plus Pro duct) . The min-plus pr o duct of a r ow-b ounde d-differ enc e, r ow-monotone matrix A ∈ Z n × n and a c olumn-b ounde d-differ enc e, c olumn-monotone matrix B ∈ Z n × n c annot b e c ompute d in time O ( n 2 . 5 − ϵ ) (for any c onstant ϵ > 0 ), unless the APSP Hyp othesis fails. The conceptual idea behind Theorem 1.16 is simple. F or a reduction based on the Directed Un weigh ted APSP Hyp othesis, i.e., starting from Min-Plus Product of size n × √ n × n with en tries b ounded by √ n , one can readjust the matrix en tries A [ i, k ] ← A [ i, k ] + k · √ n and B [ k , j ] ← B [ k , j ] − k · √ n , whic h leav es A ∗ B unc hanged, and ensures that A is row-monotone and B is column-monotone. This insight w as indep endently comm unicated to us by Łuk asiewicz [ 106 ]. T o make A row-bounded-difference one can additionally blow up the inner dimension from √ n to n , by adding √ n new columns b et ween any pair of consecutiv e columns in A to appropriately interpolate b et ween the previous entries. The ma jor technical complication is that we aim to base the reduction on the APSP Hyp othesis instead. W e thus cannot assume that the entries in the given matrices are bounded by √ n , but only that there are √ n distinct en tries that form a low-doubling set (b y Corollary 5.9 ). W e show that after an appropriate transformation w e can substitute n umbers b y their rank (i.e., p osition in the sorted order), and thereby still reduce to matrices with entries in the range roughly { 0 , . . . , √ n } . W e give the details in the follo wing tec hnical lemma. In this first step we only care to mak e A ro w-monotone; later we comment how to ac hieve the other properties without loss of generalit y . Lemma 6.10. The min-plus pr o duct of a r ow-b ounde d-differ enc e A ∈ [ √ n ] n × n with a matrix B ∈ { 0 , ⊥} n × n c ontaining at most n 1 . 5 non- ⊥ entries c annot b e c ompute d in time O ( n 2 . 5 − ϵ ) (for any c onstant ϵ > 0 ), unless the APSP Hyp othesis fails. Pro of. Assume that there is an O ( n 2 . 5 − ϵ ) -time algorithm for the problem describ ed in the lemma statemen t. W e design an algorithm for the uniform regular lo w-doubling Min-Plus Product problem of size n × √ n × n , pro ving MinPlus( n, √ n, n | D ≤ √ n ; ρ ≤ 1 /D ; K ≤ n ϵ/ 6 ) ≤ O ( n 2 . 5 − ϵ/ 6 ) . This con tradicts the APSP Hyp othesis by Corollary 5.9 . Let n b e a square num b er, and let A and B b e the given n × √ n and √ n × n matrices with integer entries in X . That is, we can assume that D = | X | ≤ √ n and | X + X | ≤ K | X | where K ≤ n ϵ/ 6 . W e compute X + X (b y brute-force, say). Then we sort X and X + X . W e say that y ∈ X is the suc c essor of x ∈ X if it is the next-larger elemen t in X . W e also define t wo functions select : [ | X + X | ] → X + X , rank : X × X → [ | X + X | ] , where select maps each index i to the i -th smallest element in the sumset X + X , and rank( x, y ) is exactly the index i such that x + y is the i -th smallest element in the sumset X + X . In particular, w e hav e that select(rank( x, y )) = x + y . W e now define another function f : X × X → [ | X + X | ] . Let L > 0 be a parameter to be determined later. Initially , set f ( x, y ) ← rank( x, y ) . Now en umerate all pairs ( x, y ) ∈ X 2 in lexicographically descending order. If y has a successor y ′ and if f ( x, y ) < f ( x, y ′ ) − L , then w e up date f ( x, y ) ← f ( x, y ′ ) − L . The resulting function f satisfies the following three prop erties b y construction: (i) F or each fixed x ∈ X the function f ( x, · ) is increasing and L -b ounded-difference, i.e., for any successive y , y ′ ∈ X we hav e that f ( x, y ′ ) − f ( x, y ) ≤ L . (ii) f ( x, y ) ≥ rank( x, y ) for all x, y ∈ X . 47 (iii) Call a pair ( x, y ) ∈ X 2 go o d if f ( x, y ) = rank( x, y ) and b ad otherwise. Let R ⊆ X 2 b e the subset of bad pairs. Then | R | ≤ K | X | 2 /L . Indeed, fix x ∈ X and consider the increasing sequence f ( x, · ) . F or each bad pair ( x, y ) , this sequence “jumps” from f ( x, y ) to f ( x, y ′ ) b y L . How ev er, the range of f is [ | X + X | ] , hence the n umber of such jumps is at most | X + X | /L ≤ K | X | /L . Summing ov er all | X | c hoices of x , w e obtain the total b ound | R | ≤ K | X | 2 /L . The algorithm no w pro ceeds in tw o cases: • (Go o d Case) Let us call a pair ( i, j ) go o d if there is some witness k suc h that ( A [ i, k ] , B [ k , j ]) ∈ X 2 is goo d, and b ad otherwise. Our goal in this step is to compute a matrix C ≥ A ∗ B that correctly solv es all go od entries (i.e., C [ i, j ] = ( A ∗ B )[ i, j ] whenever ( i, j ) is go od). T o this end, construct the matrices A ′ indexed b y [ n ] × ([ √ n ] × X ) and B ′ indexed b y ([ √ n ] × X ) × [ n ] as follo ws: A ′ [ i, ( k , y )] = f ( A [ i, k ] , y ) , B ′ [( k , y ) , j ] = ( 0 if B [ k , j ] = y , ⊥ otherwise. Denote their min-plus pro duct b y C ′ = A ′ ∗ B ′ . No w define the matrix C b y C [ i, j ] = select( C ′ [ i, j ]) . Then indeed it holds for all pairs ( i, j ) that C [ i, j ] = select( C ′ [ i, j ]) = min k select( f ( A [ i, k ] , B [ k , j ])) ≥ min k select(rank( A [ i, k ] , B [ k , j ])) = min k ( A [ i, k ] + B [ k , j ]) , where the inequality is due to Prop ert y (ii). F or any go od pair this inequality is an equality by (iii), so the matrix C is as claimed. It remains to describ e how to compute the min-plus pro duct C ′ = A ′ ∗ B ′ . The matrix A ′ is not ro w-b ounded-difference, but it is close to that. Indeed, from Prop ert y (i) w e get that (1) along an y ro w i there are √ n · | X | pairs of adjacent entries A ′ [ i, ( k , y )] and A ′ [ i, ( k , y ′ )] that differ b y at most L . Moreov er, (2) there are √ n pairs of adjacent entries of the form A ′ [ i, ( k , y )] and A ′ [ i, ( k ′ , y ′ )] (where k = k ′ ), and these en tries can differ b y up to | X + X | . T o turn A ′ in to a ro w-b ounded- difference matrix we will now insert new columns to A ′ , filled with dumm y entries whose only purp ose is to in terp olate the gaps describ ed before. It suffices to add √ n · | X | · L columns to deal with the gaps of type (1), and √ n · | X + X | columns to deal with the gaps of type (2). In total the num ber of new columns is √ n · | X | · L + √ n · | X + X | = ( L + K ) n . F or each column added in this wa y we also add a corresp onding row in B ′ filled with ⊥ -entries. Let A ′′ , B ′′ denote the resulting matrices. This op eration leav es the min-plus product unchanged, A ′ ∗ B ′ = A ′′ ∗ B ′′ . R unning Time: In summary we compute the min-plus pro duct A ′′ ∗ B ′′ , where b oth matrices can b e viewed as square matrices of size at most O (( K + L ) n ) , where A ′′ is ro w-b ounded-difference, has entries b ounded by | X + X | ≤ K | X | ≤ K √ n , and where B ′′ has at most n 1 . 5 non- ⊥ entries. This is an instance of the problem describ ed in the lemma statemen t of size N = O (( K 2 + L ) n ) . Therefore, the running time is O ( N 2 . 5 − ϵ ) = O (( K 5 + L 2 . 5 ) n 2 . 5 − ϵ ) . • (Bad Case) It remains to correct C [ i, j ] for all bad pairs ( i, j ) . T o this end enumerate all bad pairs ( x, y ) ∈ R , and all k ∈ [ √ n ] . Then enumerate all i ∈ [ n ] with A [ i, k ] = x and all j ∈ [ n ] with B [ k , j ] = y . W e up date C [ i, j ] ← min { C [ i, j ] , A [ i, k ] + B [ k , j ] } . If ( i, j ) is bad then by definition we will correctly compute C [ i, j ] in this step. 48 R unning Time: O ( | R | · √ n · ρn · ρn ) = O ( K D 2 /L · √ n · n/D · n/D ) = O ( n 2 . 5 K/L ) , recalling that eac h integer app ears in at most a ρ ≤ 1 /D -fraction of all rows and columns in A and B . The correctness is clear from b efore. The total running time is O (( K 5 + L 2 . 5 ) n 2 . 5 − ϵ + n 2 . 5 K/L ) . Recall that K ≤ n ϵ/ 6 and c ho ose the parameter L = n ϵ/ 3 . The total time b ecomes O ( n 2 . 5 − ϵ/ 6 ) as claimed. T o conclude Theorem 1.16 from Lemma 6.10 w e additionally need to argue that A is row-monotone, and that B is column-b ounded-difference and column-monotone. It turns out that these three extra constrain ts are without loss of generality , based on a sequence of observ ations mostly from previous w ork; see [ 61 ] and [ 44 , Section 2]. Lemma 6.11 ([ 61 , 44 ]) . The c omputation of an n × n × n min-plus pr o duct A ∗ B wher e A is r ow-b ounde d- differ enc e c an b e r e duc e d in time O ( n 2 ) to the c omputation of an n × n × n min-plus pr o duct A ′ ∗ B ′ wher e A ′ is r ow-b ounde d-differ enc e and r ow-monotone and B ′ is c olumn-b ounde d-differ enc e and c olumn-monotone. Pro of. Let A, B b e the giv en matrices, where A is ro w-b ounded-difference, i.e., | A [ i, k ] − A [ i, k + 1] | ≤ c for some constan t c . The reduction is to apply the following four simple transformations step-b y-step. • (Make A Smal l-Universe) When A is ro w-b ounded-difference, by definition each row in A only takes in teger v alues in some interv al { a, . . . , a + O ( n ) } . By subtracting a from the entire ro w w e can mak e sure that A only tak es v alues in { 0 , . . . , u = O ( n ) } . W e can recov er the original min-plus pro duct A ∗ B from this transformation by adding b ac k the respective offset a to each row. • (Make B Smal l-Universe) Next, we also restrict the range of entries in B . F o cus on any column in B , and let b denote its minimum en try . All entries larger than b + 2 u and all ⊥ entries cannot matter in the min-plus product A ∗ B , so we simply replace these entries b y b + 2 u . Afterw ards we can remo ve b from the entire column; the resulting matrix has integer entries in { 0 , . . . , 2 u = O ( n ) } . W e can reco ver the original min-plus pro duct A ∗ B from this transformation by adding bac k the respective offset b to eac h column. • (Make B Column-Bounde d-Differ enc e) Next, to ensure that B is column-b ounded-difference we replace eac h en try B [ k , j ] b y B ′ [ k , j ] = min k ′ ( B [ k ′ , j ] + | k ′ − k | · c ) . W e first claim that this transformation lea ves the min-plus pro duct unchanged, i.e., A ∗ B = A ∗ B ′ . The “ ≥ ” direction is clear, so fo cus on the “ ≤ ” direction. Suppose that ( A ∗ B ′ )[ i, j ] = A [ i, k ] + B ′ [ k , j ] and that B ′ [ k , j ] = B [ k ′ , j ] + | k ′ − k | · c . As A is row-bounded-difference (with constant c ), it follows that indeed ( A ∗ B )[ i, j ] ≤ A [ i, k ′ ] + B [ k ′ , j ] ≤ A [ i, k ] + | k − k ′ | · c + B [ k ′ , j ] = A [ i, k ] + B ′ [ k , j ] = ( A ∗ B ′ )[ i, j ] . Moreo ver, the augmented matrix B ′ is indeed column-b ounded-difference as | B ′ [ k , j ] − B ′ [ k + 1 , j ] | ≤ c , and still consists of integer en tries in the range { 0 , . . . , O ( n ) } . Finally , we remark that B ′ can b e computed in quadratic time from B . W e will separately compute B L [ k , j ] = min k ′ ≤ k ( B [ k ′ , j ] + ( k − k ′ ) · c ) and B R [ k , j ] = min k ′ ≥ k ( B [ k ′ , j ] + ( k ′ − k ) · c ) , and then tak e their entry-wise minimum. But eac h column in B L can b e computed in linear time by a dynamic program ev aluating B L [ k , j ] = min { B ′ [ k , j ] , B L [ k − 1 , j ] + c } , and similarly for B R . In the follo wing w e will contin ue to write B for the augmen ted matrix B ′ . • (Make A R ow-Monotone and B Column-Monotone) W e finally turn A into a row-monotone matrix and B in to a column-monotone matrix based on the follo wing observ ation due to [ 61 ]. Replace each en try A [ i, k ] by A [ i, k ] + kc , and eac h en try B [ k , j ] by B [ k , j ] + ( n − k ) c . The resulting matrices 49 still ha ve entries in { 0 , . . . , O ( n ) } . Eac h row in A forms a monotonically non-decreasing sequence, recalling that b efore the transformation an y t wo adjacen t en tries in the same ro w differed by at most c . Similarly , each column in B forms a monotonically non-increasing sequence. Note that A also remains ro w-b ounded-difference (though with a larger constant, 2 c ), and similarly B remains column-b ounded- difference. The min-plus product A ∗ B remains unchanged, up to adding the fixed offset nc to all en tries. The proof of Theorem 1.16 is no w an immediate com bination of Lemma 6.10 and Lemma 6.11 . 6.6 Min-Witness Pro duct Finally , w e consider the Min-Witness Pro duct problem first introduced by Czuma j, Ko w aluk, and Lingas [ 45 ]. It takes an imp ortant role in the class of intermediate-complexit y problems as it is among the simplest such problems: It can b e solv ed in time ˜ O ( n 2+ µ ) b y fast rectangular matrix m ultiplication, and is kno wn to reduce to many known intermediate problems (via typically very simple reductions). On the flip-side this means that it is among the har dest in termediate problems to establish tight low er bounds. T o date, only non-matc hing low er b ounds are known—an n 11 / 5 − o (1) -time lo wer bound based on Strong APSP , and an n 7 / 3 − o (1) -time low er b ound based on Directed Unw eigh ted APSP [ 35 ]. Here w e give a strengthened albeit still non-matc hing low er bound of n 7 / 3 − o (1) based on the APSP Hyp othesis. Definition 6.12 (Min-Witness Pro duct) . The min-witness pro duct of two matric es A, B ∈ { 0 , 1 } n × n is the matrix C ∈ ([ n ] ∪ {⊥} ) n × n define d by C [ i, j ] = min { k ∈ [ n ] : A [ i, k ] = B [ k , j ] = 1 } (wher e we understand that the minimum is ⊥ if ther e is no k with A [ i, k ] = B [ k , j ] = 1 ). The Min-Witness Pro duct pr oblem is to c ompute the min-witness pr o duct of two given matric es A, B . Lemma 6.13 (Min-Witness Product) . Min-Witness Pr o duct c annot b e solve d in time O ( n 7 / 3 − ϵ ) (for any c onstant ϵ > 0 ), unless the APSP Hyp othesis fails. Pro of. Supp ose that Min-Witness Pro duct is in time O ( n 7 / 3 − ϵ ) for some ϵ > 0 . W e show that in this case MinPlus( n, n 1 / 3 , n | D ≤ n 1 / 3 ) = O ( n 7 / 3 − ϵ ) whic h contradicts the APSP Hyp othesis by Corollary 5.10 . Let A, B b e the given matrices of resp ective sizes n × n 1 / 3 and n 1 / 3 × n (where we assume that n 1 / 3 is an integer), and let X ⊆ Z denote the set of entries appearing in A and B with size | X | ≤ n 1 / 3 . Construct the follo wing t wo augmented matrices A ′ , B ′ indexed b y [ n ] × ([ n 1 / 3 ] × X × X ) and ([ n 1 / 3 ] × X × X ) × [ n ] , resp ectiv ely: A ′ [ i, ( k , x, y )] = ( 1 if A [ i, k ] = x , 0 otherwise, B ′ [( k , x, y ) , j ] = ( 1 if B [ k , j ] = y , 0 otherwise. Moreo ver, define an arbitrary order ≤ on triples [ n 1 / 3 ] × X × X satisfying that ( k 1 , x 1 , y 1 ) ≤ ( k 2 , x 2 , y 2 ) whenev er x 1 + y 1 ≤ x 2 + y 2 . Then compute the min-witness pro duct of A ′ and B ′ , where we order the inner dimension [ n 1 / 3 ] × X × X by that order ≤ . By construction, in the resulting min-witness pro duct eac h en try ( i, j ) is a triple ( k , x, y ) where ( A ∗ B )[ i, j ] = x + y , and where k is a witness of ( A ∗ B )[ i, j ] . In particular, w e can easily read off the desired min-plus pro duct A ∗ B . A c kno wledgemen ts I am v ery grateful to Amir Abboud and Karl Bringmann for v aluable discussions, to Amir Abb oud and Leo W ennmann for many helpful commen ts on an earlier draft of this pap er, and to Ernie Cro ot for answering some questions related to [ 11 ]. 50 References [1] Amir Abb oud, Karl Bringmann, and Nic k Fisc her. Stronger 3-SUM lo wer b ounds for appro ximate distance oracles via additiv e com binatorics. In Barna Saha and Ro cco A. Servedio, editors, 55th A nnual ACM Symp osium on The ory of Computing (STOC 2023) , pages 391–404. ACM, 2023. doi: 10.1145/3564246.3585240 . [2] Amir Abb oud, Karl Bringmann, Seri Khoury , and Or Zamir. Hardness of approximation in P via short cycle remov al: cycle detection, distance oracles, and b ey ond. In Stefano Leonardi and Anupam Gupta, editors, 54th Annual ACM Symp osium on The ory of Computing (STOC 2022) , pages 1487–1500. ACM, 2022. doi:10.1145/3519935.3520066 . [3] Amir Abb oud and Søren Dahlgaard. Popular conjectures as a barrier for dynamic planar graph al- gorithms. In Irit Dinur, editor, 57th Annual IEEE Symp osium on F oundations of Computer Scienc e (F OCS 2016) , pages 477–486. IEEE Computer Society , 2016. doi:10.1109/FOCS.2016.58 . [4] Amir Abboud, Nick Fischer, Ce Jin, Virginia V assilevsk a Williams, and Zo e Xi. All-pairs shortest paths with few weigh ts per node. In Mic hal K oucký and Nikhil Bansal, editors, 57th Annual A CM Symp osium on The ory of Computing (STOC 2025) , pages 1956–1964. A CM, 2025. doi:10.1145/ 3717823.3718240 . [5] Amir Abb oud, F abrizio Grandoni, and Virginia V assilevsk a Williams. Sub cubic equiv alences betw een graph cen trality problems, APSP, and diameter. ACM T r ans. Algorithms , 19(1):3:1–3:30, 2023. doi: 10.1145/3563393 . [6] Amir Abb oud and Virginia V assilevsk a Williams. Popular conjectures imply strong low er b ounds for dynamic problems. In 55th Annual IEEE Symp osium on F oundations of Computer Scienc e (FOCS 2014) , pages 434–443. IEEE Computer So ciet y , 2014. doi:10.1109/FOCS.2014.53 . [7] Amir Abb oud, Virginia V assilevsk a Williams, and Oren W eimann. Consequences of faster alignment of sequences. In Ja vier Esparza, Pierre F raigniaud, Thore Husfeldt, and Elias K outsoupias, editors, 41st International Col lo quium on Automata, L anguages, and Pr o gr amming (ICALP 2014) , v olume 8572 of L e ctur e Notes in Computer Scienc e , pages 39–51. Springer, 2014. doi:10.1007/978- 3- 662- 43948- 7\ _4 . [8] Josh Alman, Ran Duan, Virginia V assilevsk a Williams, Yinzhan Xu, Zixuan Xu, and Renfei Zhou. More asymmetry yields faster matrix multiplication. In Y ossi Azar and Debmalya Panigrahi, editors, 36th Annual ACM-SIAM Symp osium on Discr ete Algorithms (SODA 2025) , pages 2005–2039. SIAM, 2025. doi:10.1137/1.9781611978322.63 . [9] Noga Alon, Zvi Galil, and Oded Margalit. On the exp onen t of the all pairs shortest path problem. J. Comput. Syst. Sci. , 54(2):255–262, 1997. doi:10.1006/JCSS.1997.1388 . [10] Amiho od Amir, Timoth y M. Chan, Moshe Lew enstein, and Noa Lewenstein. On hardness of jum- bled indexing. In Ja vier Esparza, Pierre F raigniaud, Thore Husfeldt, and Elias Koutsoupias, ed- itors, 41st International Col lo quium on Automata, L anguages, and Pr o gr amming (ICALP 2014) , v olume 8572 of L e ctur e Notes in Computer Scienc e , pages 114–125. Springer, 2014. doi:10.1007/ 978- 3- 662- 43948- 7\_10 . [11] Gagik Amirkhany an, Alb ert Bush, and Ernie Cro ot. Order-preserving freiman isomorphisms. Inte gers , 18:A8, 2018. URL: http://math.colgate.edu/%7Eintegers/s8/s8.Abstract.html . [12] Sriniv asan Arunac halam, Da vi Castro-Silv a, Ark opal Dutt, and T om Gur. Classical and quan tum p olynomial F reiman-Ruzsa algorithms. In Sh ubhangi Saraf, editor, 17th Innovations in The or etic al Computer Scienc e Confer enc e (ITCS 2026) , volume 362 of LIPIcs , pages 11:1–11:8. Schloss Dagstuhl - Leibniz-Zen trum für Informatik, 2026. doi:10.4230/LIPICS.ITCS.2026.11 . 51 [13] Arturs Backurs, Nishanth Dikk ala, and Christos T zamos. Tigh t hardness results for maxim um w eight rectangles. In Ioannis Chatzigiannakis, Michael Mitzenmacher, Y uv al Rabani, and Davide Sangiorgi, editors, 43r d International Col lo quium on A utomata, L anguages, and Pr o gr amming (ICALP 2016) , v olume 55 of LIPIcs , pages 81:1–81:13. Schloss Dagstuhl - Leibniz-Zentrum für Informatik, 2016. doi:10.4230/LIPICS.ICALP.2016.81 . [14] An tal Balog and Endre Szemerédi. A statistical theorem of set addition. Combinatoric a , 14:263–268, 1994. URL: https://doi.org/10.1007/BF01212974 . [15] Ho da y a Barr, T svi Kopelowitz, Ely P orat, and Liam Ro ditt y . {− 1 , 0 , 1 } -APSP and (min, max)-pro duct problems. arXiv , 2019. URL: . [16] W alter Baur and V olker Strassen. The complexit y of partial deriv atives. The or. Comput. Sci. , 22:317– 330, 1983. doi:10.1016/0304- 3975(83)90110- X . [17] Mic hael A. Bender, Martin F arach-Colton, Giridhar Pemmasani, Steven Skiena, and P av el Sumazin. Lo west common ancestors in trees and directed acyclic graphs. J. A lgorithms , 57(2):75–94, 2005. doi:10.1016/J.JALGOR.2005.08.001 . [18] Aaron Bernstein, Greg Bo dwin, and Nicole W ein. Are there graphs whose shortest path structure requires large edge weigh ts? In V enk atesan Guruswami, editor, 15th Innovations in The or etic al Computer Scienc e Confer enc e, ITCS 2024, Berkeley, CA, USA, January 30 - F ebruary 2, 2024 , v olume 287 of LIPIcs , pages 12:1–12:22. Sc hloss Dagstuhl - Leibniz-Zentrum für Informatik, 2024. doi:10.4230/LIPICS.ITCS.2024.12 . [19] Aaron Bernstein, Danupon Nanongk ai, and Christian W ulff-Nilsen. Negative-w eigh t single-source shortest paths in near-linear time. In 63r d Annual IEEE Symp osium on F oundations of Computer Scienc e (FOCS 2022) , pages 600–611. IEEE, 2022. doi:10.1109/FOCS54457.2022.00063 . [20] Karl Bringmann. Knapsack with small items in near-quadratic time. In Bo jan Mohar, Igor Shink ar, and Ryan O’Donnell, editors, 56th A nnual ACM Symp osium on The ory of Computing (STOC 2024) , pages 259–270. A CM, 2024. doi:10.1145/3618260.3649719 . [21] Karl Bringmann and Bhask ar Ray Chaudhury . P olyline simplification has cubic complexity . J. Comput. Ge om. , 11(2):94–130, 2020. doi:10.20382/JOCG.V11I2A5 . [22] Karl Bringmann, Nick Fischer, and V asileios Nak os. Deterministic and Las V egas algorithms for sparse nonnegativ e conv olution. In Joseph (Seffi) Naor and Niv Buch binder, editors, 33r d Annual A CM-SIAM Symp osium on Discr ete A lgorithms (SODA 2022) , pages 3069–3090. SIAM, 2022. doi: 10.1137/1.9781611977073.119 . [23] Karl Bringmann, Nic k Fisc her, and V asileios Nakos. Beating Bellman’s algorithm for subset sum. In Y ossi Azar and Debmaly a Panigrahi, editors, 36th A nnual A CM-SIAM Symp osium on Discr ete A lgorithms (SODA 2025) , pages 4596–4612. SIAM, 2025. doi:10.1137/1.9781611978322.157 . [24] Karl Bringmann, Pa w eł Ga wrycho wski, Sha y Mozes, and Oren W eimann. T ree edit distance cannot b e computed in strongly sub cubic time (unless APSP can). In Artur Czuma j, editor, 29th Annual A CM-SIAM Symp osium on Discr ete A lgorithms (SODA 2018) , pages 1190–1206. SIAM, 2018. doi: 10.1137/1.9781611975031.77 . [25] Karl Bringmann, F abrizio Grandoni, Barna Saha, and Virginia V assilevsk a Williams. T ruly sub cubic algorithms for language edit distance and RNA folding via fast b ounded-difference min-plus pro duct. SIAM J. Comput. , 48(2):481–512, 2019. doi:10.1137/17M112720X . 52 [26] Karl Bringmann, Marvin Künnemann, and Karol Węgrzycki. Appro ximating APSP without scaling: equiv alence of appro ximate min-plus and exact min-max. In Moses Charik ar and Edith Cohen, editors, 51st A nnual A CM Symp osium on The ory of Computing (STOC 2019) , pages 943–954. ACM, 2019. doi:10.1145/3313276.3316373 . [27] Karl Bringmann and V asileios Nak os. T op- k -conv olution and the quest for near-linear output-sensitive subset sum. In Konstan tin Mak arychev, Y ury Mak aryc hev, Madh ur T ulsiani, Gautam Kamath, and Julia Ch uzhoy , editors, 52nd Annual ACM Symp osium on The ory of Computing (STOC 2020) , pages 982–995. A CM, 2020. doi:10.1145/3357713.3384308 . [28] Karl Bringmann and V asileios Nak os. F ast n -fold b oolean con v olution via additive com binatorics. In Nikhil Bansal, Eman uela Merelli, and James W orrell, editors, 48th International Col lo quium on A utomata, L anguages, and Pr o gr amming (ICALP 2021) , volume 198 of LIPIcs , pages 41:1–41:17. Sc hloss Dagstuhl - Leibniz-Zen trum für Informatik, 2021. doi:10.4230/LIPICS.ICALP.2021.41 . [29] Karl Bringmann and Philip W ellnitz. On near-linear-time algorithms for dense subset sum. In Dániel Marx, editor, 32nd Annual A CM-SIAM Symp osium on Discr ete Algorithms (SODA 2021) , pages 1777– 1796. SIAM, 2021. doi:10.1137/1.9781611976465.107 . [30] Timoth y M. Chan. All-pairs shortest paths with real w eights in O ( n 3 / log n ) time. Algorithmic a , 50(2):236–243, 2008. doi:10.1007/S00453- 007- 9062- 1 . [31] Timoth y M. Chan. More algorithms for all-pairs shortest paths in weigh ted graphs. SIAM J. Comput. , 39(5):2075–2089, 2010. doi:10.1137/08071990X . [32] Timoth y M. Chan and Moshe Lew enstein. Clustered in teger 3SUM via additiv e combinatorics. In Ro cco A. Servedio and Ronitt Rubinfeld, editors, 47th A nnual A CM Symp osium on The ory of Com- puting (STOC 2015) , pages 31–40. A CM, 2015. doi:10.1145/2746539.2746568 . [33] Timoth y M. Chan, Virginia V assilevsk a Williams, and Yinzhan Xu. Algorithms, reductions and equiv- alences for small weigh t v arian ts of all-pairs shortest paths. In Nikhil Bansal, Emanuela Merelli, and James W orrell, editors, 48th International Col lo quium on Automata, L anguages, and Pr o gr amming (ICALP 2021) , volume 198 of LIPIcs , pages 47:1–47:21. Schloss Dagstuhl - Leibniz-Zentrum für Infor- matik, 2021. doi:10.4230/LIPICS.ICALP.2021.47 . [34] Timoth y M. Chan, Virginia V assilevsk a Williams, and Yinzhan Xu. Hardness for triangle problems under even more b eliev able hypotheses: reductions from real APSP, real 3SUM, and OV. In Stefano Leonardi and Anupam Gupta, editors, 54th Annual ACM Symp osium on The ory of Computing (STOC 2022) , pages 1501–1514. ACM, 2022. doi:10.1145/3519935.3520032 . [35] Timoth y M. Chan, Virginia V assilevsk a Williams, and Yinzhan Xu. F redman’s trick meets dominance pro duct: Fine-grained complexit y of unw eighted APSP, 3SUM coun ting, and more. In Barna Saha and Ro cco A. Servedio, editors, 55th Annual ACM Symp osium on The ory of Computing (STOC 2023) , pages 419–432. A CM, 2023. doi:10.1145/3564246.3585237 . [36] Timoth y M. Chan and R. Ryan Williams. Deterministic APSP, orthogonal vectors, and more: Quickly derandomizing Razb oro v-Smolensky. ACM T r ans. Algorithms , 17(1):2:1–2:14, 2021. doi:10.1145/ 3402926 . [37] Timoth y M. Chan and Yinzhan Xu. Simpler reductions from exact triangle. In Mera v Parter and Seth P ettie, editors, 7th Symp osium on Simplicity in Algorithms (SOSA 2024) , pages 28–38. SIAM, 2024. doi:10.1137/1.9781611977936.4 . [38] Lin Chen, Jia yi Lian, Y uchen Mao, and Guo c huan Zhang. Appro ximating partition in near-linear time. In Bo jan Mohar, Igor Shink ar, and Ryan O’Donnell, editors, 56th Annual ACM Symp osium on The ory of Computing (STOC 2024) , pages 307–318. A CM, 2024. doi:10.1145/3618260.3649727 . 53 [39] Lin Chen, Jiayi Lian, Y uc hen Mao, and Guoch uan Zhang. F aster algorithms for bounded knapsack and b ounded subset sum via fine-grained proximit y results. In David P . W o odruff, editor, 35th A nnual A CM-SIAM Symp osium on Discr ete A lgorithms (SODA 2024) , pages 4828–4848. SIAM, 2024. doi: 10.1137/1.9781611977912.171 . [40] Lin Chen, Jia yi Lian, Y uc hen Mao, and Guo c h uan Zhang. An impro ved pseudopolynomial time algorithm for subset sum. In 65th Annual IEEE Symp osium on F oundations of Computer Scienc e (F OCS 2024) , pages 2202–2216. IEEE, 2024. doi:10.1109/FOCS61266.2024.00129 . [41] Lin Chen, Jiayi Lian, Y uchen Mao, and Guo c h uan Zhang. A nearly quadratic-time FPT AS for knap- sac k. In Bo jan Mohar, Igor Shink ar, and Ryan O’Donnell, editors, 56th Annual ACM Symp osium on The ory of Computing (STOC 2024) , pages 283–294. ACM, 2024. doi:10.1145/3618260.3649730 . [42] Lin Chen, Y uchen Mao, and Guo c huan Zhang. Long arithmetic progressions in sumsets and subset sums: Constructive pro ofs and efficient witnesses. arXiv , 2025. URL: https://doi.org/10.48550/ arXiv.2503.19299 . [43] Sh ucheng Chi, Ran Duan, and Tianle Xie. F aster algorithms for b ounded-difference min-plus pro duct. In Joseph (Seffi) Naor and Niv Buc hbinder, editors, 33r d A nnual ACM-SIAM Symp osium on Discr ete A lgorithms (SODA 2022) , pages 1435–1447. SIAM, 2022. doi:10.1137/1.9781611977073.60 . [44] Sh ucheng Chi, Ran Duan, Tianle Xie, and Tianyi Zhang. F aster min-plus product for monotone instances. In Stefano Leonardi and Anupam Gupta, editors, 54th A nnual ACM Symp osium on The ory of Computing (STOC 2022) , pages 1529–1542. A CM, 2022. doi:10.1145/3519935.3520057 . [45] Artur Czuma j, Miroslaw K ow aluk, and Andrzej Lingas. F aster algorithms for finding low est common ancestors in directed acyclic graphs. The or. Comput. Sci. , 380(1-2):37–46, 2007. doi:10.1016/J.TCS. 2007.02.053 . [46] Wlo dzimierz Dob osiewicz. A more efficient algorithm for the min-plus m ultiplication. International Journal of Computer Mathematics , 32(1-2):49–60, 1990. doi:10.1080/00207169008803814 . [47] Ran Duan, Y ong Gu, and Le Zhang. Impro ved time bounds for all pairs non-decreasing paths in general digraphs. In Ioannis Chatzigiannakis, Christos Kaklamanis, Dániel Marx, and Donald Sannella, editors, 45th International Col lo quium on Automata, L anguages, and Pr o gr amming (ICALP 2018) , v olume 107 of LIPIcs , pages 44:1–44:14. Sc hloss Dagstuhl - Leibniz-Zentrum für Informatik, 2018. doi:10.4230/LIPICS.ICALP.2018.44 . [48] Ran Duan, Ce Jin, and Hongxun W u. F aster algorithms for all pairs non-decreasing paths prob- lem. In Christel Baier, Ioannis Chatzigiannakis, P aola Flo cchini, and Stefano Leonardi, editors, 46th International Col lo quium on A utomata, L anguages, and Pr o gr amming (ICALP 2019) , vol- ume 132 of LIPIcs , pages 48:1–48:13. Sc hloss Dagstuhl - Leibniz-Zentrum für Informatik, 2019. doi:10.4230/LIPICS.ICALP.2019.48 . [49] Ran Duan and Seth P ettie. F ast algorithms for (max, min)-matrix multiplication and bottleneck shortest paths. In Claire Mathieu, editor, 20th Annual ACM-SIAM Symp osium on Discr ete Algorithms (SOD A 2009) , pages 384–391. SIAM, 2009. doi:10.1137/1.9781611973068.43 . [50] Bartłomiej Dudek, P aw eł Gawryc howski, and T atiana Stariko vsk a ya. All non-trivial v ariants of 3-LDT are equiv alen t. In K onstantin Mak aryc hev, Y ury Mak arychev, Madh ur T ulsiani, Gautam Kamath, and Julia Ch uzhoy , editors, 52nd Annual ACM Symp osium on The ory of Computing (STOC 2020) , pages 974–981. A CM, 2020. doi:10.1145/3357713.3384275 . [51] Nic k Fischer. Deterministic sparse pattern matching via the Baur-Strassen theorem. In David P . W o odruff, editor, 35th Annual ACM-SIAM Symp osium on Discr ete A lgorithms (SODA 2024) , pages 3333–3353. SIAM, 2024. doi:10.1137/1.9781611977912.119 . 54 [52] Nic k Fischer. Sumsets, 3SUM, subset sum: Now for real! In Y ossi Azar and Debmalya P anigrahi, editors, 36th A nnual ACM-SIAM Symp osium on Discr ete A lgorithms (SODA 2025) , pages 4520–4546. SIAM, 2025. doi:10.1137/1.9781611978322.155 . [53] Nic k Fischer, Ce Jin, and Yinzhan Xu. New applications of 3SUM-counting in fine-grained complexity and pattern matc hing. In Y ossi Azar and Debmaly a P anigrahi, editors, 36th Annual ACM-SIAM Symp osium on Discr ete A lgorithms (SOD A 2025) , pages 4547–4595. SIAM, 2025. doi:10.1137/1. 9781611978322.156 . [54] Rob ert W. Flo yd. Algorithm 97: Shortest path. Commun. A CM , 5(6):345, 1962. doi:10.1145/ 367766.368168 . [55] Mic hael L. F redman. New bounds on the complexit y of the shortest path problem. SIAM J. Comput. , 5(1):83–89, 1976. doi:10.1137/0205006 . [56] Ank a Ga jentaan and Mark H. Overmars. On a class of O ( n 2 ) problems in computational geometry . Comput. Ge om. , 5:165–185, 1995. doi:10.1016/0925- 7721(95)00022- 2 . [57] Zvi Galil and Oded Margalit. All pairs shortest distances for graphs with small in teger length edges. Inf. Comput. , 134(2):103–139, 1997. doi:10.1006/INCO.1997.2620 . [58] Timoth y W. Gow ers. A new pro of of Szemerédi’s theorem. GAF A Ge ometric And F unctional Analysis , 11:465–588, 08 2001. doi:10.1007/s00039- 001- 0332- 9 . [59] W.T. Gow ers, Ben Green, F reddie Manners, and T erence T ao. On a conjecture of Marton. Annals of Mathematics , 201(2):515–549, 2025. doi:10.4007/annals.2025.201.2.5 . [60] F abrizio Grandoni, Giuseppe F. Italiano, Aleksander Łuk asiewicz, Nikos P arotsidis, and Przemysła w Uznański. All-pairs LCA in D AGs: Breaking through the O ( n 2 . 5 ) barrier. In Dániel Marx, editor, 32nd Annual ACM-SIAM Symp osium on Discr ete A lgorithms (SODA 2021) , pages 273–289. SIAM, 2021. doi:10.1137/1.9781611976465.18 . [61] Y uzhou Gu, A dam Polak, Virginia V assilevsk a Williams, and Yinzhan Xu. F aster monotone min- plus pro duct, range mo de, and single source replacement paths. In Nikhil Bansal, Emanuela Merelli, and James W orrell, editors, 48th International Col lo quium on Automata, L anguages, and Pr o gr am- ming (ICALP 2021) , volume 198 of LIPIcs , pages 75:1–75:20. Sc hloss Dagstuhl - Leibniz-Zentrum für Informatik, 2021. doi:10.4230/LIPICS.ICALP.2021.75 . [62] Yijie Han. Improv ed algorithm for all pairs shortest paths. Inf. Pr o c ess. L ett. , 91(5):245–250, 2004. doi:10.1016/J.IPL.2004.05.006 . [63] Yijie Han. An O ( n 3 (log log n/ log n ) 5 / 4 ) time algorithm for all pairs shortest path. Algorithmic a , 51(4):428–434, 2008. doi:10.1007/S00453- 007- 9063- 0 . [64] Yijie Han and T adao T ak aok a. An O ( n 3 loglog n/ log 2 n ) time algorithm for all pairs shortest paths. J. Discr ete Algorithms , 38-41:9–19, 2016. doi:10.1016/J.JDA.2016.09.001 . [65] Monik a Henzinger, Andrea Lincoln, Stefan Neumann, and Virginia V assilevsk a Williams. Conditional hardness for sensitivity problems. In Christos H. Papadimitriou, editor, 8th Innovations in The or etic al Computer Scienc e Confer enc e (ITCS 2017) , volume 67 of LIPIcs , pages 26:1–26:31. Schloss Dagstuhl - Leibniz-Zen trum für Informatik, 2017. doi:10.4230/LIPICS.ITCS.2017.26 . [66] Noam Horowicz and T svi K op elo witz. Color distance oracles and snipp ets: Separation b et ween exact and approximate solutions. In Anne Benoit, Haim Kaplan, Sebastian Wild, and Grzegorz Herman, editors, 33r d A nnual Eur op e an Symp osium on Algorithms (ESA 2025) , v olume 351 of LIPIcs , pages 72:1–72:17. Sc hloss Dagstuhl - Leibniz-Zen trum für Informatik, 2025. doi:10.4230/LIPICS.ESA. 2025.72 . 55 [67] Russell Impagliazzo and Ramamohan Paturi. On the complexit y of k -SA T. J. Comput. Syst. Sci. , 62(2):367–375, 2001. doi:10.1006/JCSS.2000.1727 . [68] Russell Impagliazzo, Ramamohan Paturi, and F rancis Zane. Whic h problems hav e strongly exp onen tial complexit y? J. Comput. Syst. Sci. , 63(4):512–530, 2001. doi:10.1006/JCSS.2001.1774 . [69] Ce Jin. 0-1 knapsack in nearly quadratic time. In Bo jan Mohar, Igor Shink ar, and Ryan O’Donnell, editors, 56th Annual ACM Symp osium on The ory of Computing (STOC 2024) , pages 271–282. A CM, 2024. doi:10.1145/3618260.3649618 . [70] Ce Jin and Yinzhan Xu. Remo ving additive structure in 3SUM-based reductions. In Barna Saha and Ro cco A. Serv edio, editors, 55th Annual A CM Symp osium on The ory of Computing (STOC 2023) , pages 405–418. A CM, 2023. doi:10.1145/3564246.3585157 . [71] Donald B. Johnson. Efficien t algorithms for shortest paths in sparse netw orks. J. ACM , 24(1):1–13, 1977. doi:10.1145/321992.321993 . [72] T omasz Kociumak a and Adam Polak. Bellman-F ord is optimal for shortest hop-b ounded paths. In Inge Li Gørtz, Martin F arach-Colton, Simon J. Puglisi, and Grzegorz Herman, editors, 31st Annual Eur op e an Symp osium on Algorithms (ESA 2023) , v olume 274 of LIPIcs , pages 72:1–72:10. Sc hloss Dagstuhl - Leibniz-Zen trum für Informatik, 2023. doi:10.4230/LIPICS.ESA.2023.72 . [73] Andrea Lincoln, Adam Polak, and Virginia V assilevsk a Williams. Mono chromatic triangles, in terme- diate matrix pro ducts, and conv olutions. In Thomas Vidic k, editor, 11th Innovations in The or etic al Computer Scienc e Confer enc e (ITCS 2020) , v olume 151 of LIPIcs , pages 53:1–53:18. Sc hloss Dagstuhl - Leibniz-Zen trum für Informatik, 2020. doi:10.4230/LIPICS.ITCS.2020.53 . [74] Andrea Lincoln, Virginia V assilevsk a Williams, and R. Ryan Williams. Tight hardne ss for shortest cycles and paths in sparse graphs. In Artur Czuma j, editor, 29th Annual ACM-SIAM Symp osium on Discr ete Algorithms (SODA 2018) , pages 1236–1252. SIAM, 2018. doi:10.1137/1.9781611975031. 80 . [75] Shac har Lov ett. An exp osition of Sanders’ quasi-p olynomial F reiman-Ruzsa theorem. The ory Comput. , 6:1–14, 2015. doi:10.4086/TOC.GS.2015.006 . [76] Shac har Lo vett and Oded Regev. A coun terexample to a strong v arian t of the polynomial F reiman- Ruzsa conjecture in euclidean space. Discr ete Analysis , 2018. doi:10.19086/da.1640 . [77] F reddie Manners. A note on the p olynomial F re ˘ ıman–Ruzsa conjecture ov er Z . Mathematic al Pr o c e e d- ings of the Cambridge Philosophic al So ciety , 166(2):243–245, 2017. doi:10.1017/s0305004117000809 . [78] Xiao Mao. Breaking the cubic barrier for (unw eigh ted) tree edit distance. In 62nd Annual IEEE Symp osium on F oundations of Computer Scienc e (FOCS 2021) , pages 792–803. IEEE, 2021. doi: 10.1109/FOCS52979.2021.00082 . [79] Jirí Matousek. Computing dominances in E n . Inf. Pr o c ess. L ett. , 38(5):277–278, 1991. doi:10.1016/ 0020- 0190(91)90071- O . [80] Jak ob Nogler, Adam P olak, Barna Saha, Virginia V assilevsk a Williams, Yinzhan Xu, and Christopher Y e. F aster weigh ted and un weigh ted tree edit distance and APSP equiv alence. In Mic hal Kouc ký and Nikhil Bansal, editors, 57th Annual ACM Symp osium on The ory of Computing (STOC 2025) , pages 2167–2178. A CM, 2025. doi:10.1145/3717823.3718116 . [81] Helm ut Plünnec ke. Eine zahlentheoretisc he Anw endung der Graphentheorie. Journal für die r eine und angewandte Mathematik , 1970(243):171–183, 1970. doi:10.1515/crll.1970.243.171 . 56 [82] Rushil Raghav an. Impro v ed bounds for the freiman-ruzsa theorem. arXiv , 2025. URL: https://doi. org/10.48550/arXiv.2512.11217 . [83] Tim Randolph and Karol Węgrzyc ki. Parameterized algorithms on integer sets with small doubling: In teger programming, subset sum and k -SUM. In Timoth y M. Chan, Johannes Fischer, John Iacono, and Grzegorz Herman, editors, 32nd Annual Eur op e an Symp osium on Algorithms (ESA 2024) , volume 308 of LIPIcs , pages 96:1–96:19. Schloss Dagstuhl - Leibniz-Zen trum für Informatik, 2024. doi: 10.4230/LIPICS.ESA.2024.96 . [84] Imre Z. Ruzsa. An application of graph theory to additiv e n um b er theory . Sci. Ser. A Math. Sci. (N.S.) , 3:97–109, 1989. [85] Imre Z. Ruzsa. Sums of finite sets. In David V. Ch udnovsky , Gregory V. Chudno vsky , and Melvyn B. Nathanson, editors, Numb er The ory: New Y ork Seminar 1991–1995 , pages 281–293. Springer US, 1996. doi:10.1007/978- 1- 4612- 2418- 1_21 . [86] Imre Z. Ruzsa. An analog of F reiman’s theorem in groups. In Deshouilliers Jean-Marc, Landreau Bernard, and Y udin Alexander A., editors, Structur e the ory of set addition , num ber 258 in Astérisque, pages 323–326. Société mathématique de F rance, 1999. [87] T om Sanders. On the Bogolyub o v–Ruzsa lemma. Analysis & PDE , 5(3):627–655, 2012. doi:10.2140/ apde.2012.5.627 . [88] Raim und Seidel. On the all-pairs-shortest-path problem in un weigh ted undirected graphs. J. Comput. Syst. Sci. , 51(3):400–403, 1995. doi:10.1006/JCSS.1995.1078 . [89] Asaf Shapira, Raphael Y uster, and Uri Zwick. All-pairs bottleneck paths in vertex weigh ted graphs. A lgorithmic a , 59(4):621–633, 2011. URL: https://doi.org/10.1007/S00453- 009- 9328- x , doi:10. 1007/S00453- 009- 9328- X . [90] A vi Shoshan and Uri Zwick. All pairs shortest paths in undirected graphs with integer w eights. In 40th A nnual IEEE Symp osium on F oundations of Computer Scienc e (F OCS 1999) , pages 605–615. IEEE Computer Society , 1999. doi:10.1109/SFFCS.1999.814635 . [91] T adao T ak aok a. A new upp er b ound on the complexity of the all pairs shortest path problem. Inf. Pr o c ess. L ett. , 43(4):195–199, 1992. doi:10.1016/0020- 0190(92)90200- F . [92] T adao T ak aok a. A faster algorithm for the all-pairs shortest path problem and its application. In Kyung-Y ong Ch wa and J. Ian Munro, editors, 10th A nnual International Confer enc e on Computing and Combinatorics (COCOON 2004) , v olume 3106 of L e ctur e Notes in Computer Scienc e , pages 278– 289. Springer, 2004. doi:10.1007/978- 3- 540- 27798- 9\_31 . [93] T adao T ak aok a. An O ( n 3 loglog n/ log n ) time algorithm for the all-pairs shortest path problem. Inf. Pr o c ess. L ett. , 96(5):155–161, 2005. doi:10.1016/J.IPL.2005.08.008 . [94] T erence T ao and V an H. V u. A dditive Combinatorics . Cambridge Univ ersit y Press, 2006. doi: 10.1017/cbo9780511755149 . [95] Virginia V assilevsk a, R. Ry an Williams, and Raphael Y uster. All-pairs b ottlenec k paths for gen- eral graphs in truly sub-cubic time. In Da vid S. Johnson and Uriel F eige, editors, 39th A n- nual A CM Symp osium on The ory of Computing (STOC 2007) , pages 585–589. ACM, 2007. doi: 10.1145/1250790.1250876 . [96] Virginia V assilevsk a Williams. Nondecreasing paths in a weigh ted graph or: How to optimally read a train sc hedule. ACM T r ans. Algorithms , 6(4):70:1–70:24, 2010. doi:10.1145/1824777.1824790 . 57 [97] Virginia V assilevsk a Williams and R. Ryan Williams. Sub cubic equiv alences b et w een path, matrix, and triangle problems. J. A CM , 65(5):27:1–27:38, 2018. doi:10.1145/3186893 . [98] Virginia V assilevsk a Williams and Yinzhan Xu. Mono c hromatic triangles, triangle listing and APSP. In Sandy Irani, editor, 61st A nnual IEEE Symp osium on F oundations of Computer Scienc e (F OCS 2020) , pages 786–797. IEEE, 2020. doi:10.1109/FOCS46700.2020.00078 . [99] Virginia V assilevsk a Williams and Yinzhan Xu. T ruly sub cubic min-plus product for less structured matrices, with applications. In Sh uchi Chawla, editor, 31st Annual ACM-SIAM Symp osium on Discr ete A lgorithms (SODA 2020) , pages 12–29. SIAM, 2020. doi:10.1137/1.9781611975994.2 . [100] Stephen W arshall. A theorem on Bo olean matrices. J. A CM , 9(1):11–12, 1962. doi:10.1145/321105. 321107 . [101] R. Ryan Williams. F aster all-pairs shortest paths via circuit complexit y . SIAM J. Comput. , 47(5):1965– 1985, 2018. doi:10.1137/15M1024524 . [102] Raphael Y uster. Efficien t algorithms on sets of p erm utations, dominance, and real-weigh ted APSP. In Claire Mathieu, editor, 20th A nnual ACM-SIAM Symp osium on Discr ete Algorithms (SODA 2009) , pages 950–957. SIAM, 2009. doi:10.1137/1.9781611973068.103 . [103] Y ufei Zhao. Gr aph The ory and A dditive Combinatorics: Exploring Structur e and R andomness . Cam- bridge Univ ersity Press, 2023. doi:10.1017/9781009310956 . [104] Uri Zwick. All pairs shortest paths using bridging sets and rectangular matrix multiplication. J. ACM , 49(3):289–317, 2002. doi:10.1145/567112.567114 . [105] Uri Zwick. A slightly impro ved sub-cubic algorithm for the all pairs shortest paths problem with real edge lengths. In Rudolf Fleischer and Gerhard T ripp en, editors, 15th International Symp osium on Algorithms and Computation (ISAAC 2004) , volume 3341 of L e ctur e Notes in Computer Scienc e , pages 921–932. Springer, 2004. doi:10.1007/978- 3- 540- 30551- 4\_78 . [106] Aleksander Łuk asiewicz. Personal comm unication, 2025. A Sum-Order-Preserving Hashing In this section, w e recap the concept of sum-order-preserving hashing, provide a proof of Theorem 1.11 , and further discuss the plausibilit y of Hyp othesis 1.12 . Recall that a function h : X → Z (for some in teger set X ) is sum-or der-pr eserving if for all x 1 , x 2 , y 1 , y 2 ∈ X : x 1 + x 2 < y 1 + y 2 implies h ( x 1 ) + h ( x 2 ) < h ( y 1 ) + h ( y 2 ) . Analogously , w e call h or der-pr eserving if for all x, y ∈ X : x < y implies h ( x ) < h ( y ) . A.1 Quasi-P olynomial Bounds W e will first fo cus on the pro of of Theorem 1.11 (restated next) which claims that for any in teger set X with doubling K there exists a large fraction, dep ending quasi-p olynomial ly on K , that can b e hashed w ith a sum-order-preserving hash function. Theorem 1.11 (Sum-Order-Preserving Hashing with Quasi-Polynomial Bounds [ 11 , 87 ]) . F or every inte ger set X with doubling | X + X | ≤ K | X | ther e is a subset Y ⊆ X of size | Y | ≥ | X | / exp((log K ) O (1) ) and a sum-or der-pr eserving function h : Y → { 0 , . . . , | X |} . 58 The proof of this theorem follo ws by combining the work of Amirkhany an, Bush, and Cro ot [ 11 ] with Sanders’ state-of-the-art bounds [ 87 ] for the F reiman-Ruzsa theorem. T o state these t wo ingredien ts, we start with some definitions. A set of the form P = ( d X i =1 ℓ i a i : | ℓ i | ≤ L i ) is called a (centered) gener alize d arithmetic pr o gr ession . Here, d is called the dimension of the progress ion. W e sa y that P is pr op er if each element p ∈ P has a unique representation of the form P d i =1 ℓ i a i for | ℓ i | ≤ L i . Then Sanders’ result [ 87 ] can b e stated as follows; see also [ 75 ] for an exp osition of this result. Theorem A.1 (Quasi-P olynomial F reiman-Ruzsa [ 87 ]) . L et X b e an inte ger set with | X + X | ≤ K | X | . Then X c an b e c over e d by exp((log K ) O (1) ) tr anslates of a pr op er gener alize d arithmetic pr o gr ession with dimension O ((log K ) O (1) ) and size at most exp((log K ) O (1) ) | X | . The main result from [ 11 ] can b e stated as follows. Theorem A.2 (Condensing Lemma [ 11 ]) . L et P b e a gener alize d arithmetic pr o gr ession of the form P = ( d X i =1 ℓ i a i : | ℓ i | ≤ L i ) such that ( d X i =1 ℓ i a i : | ℓ i | ≤ 4 L i ) is also pr op er. Then ther e ar e inte gers a ′ 1 , . . . , a ′ d such that the map h : P → Z define d by h d X i =1 ℓ i a i ! = d X i =1 ℓ i a ′ i is or der-pr eserving, and such that | h ( x ) | ≤ d O ( d ) | P | for al l x ∈ P . Pro of of Theorem 1.11 . Let X ⊆ Z b e arbitrary with doubling K . F rom Theorem A.1 it follo ws that X can b e cov ered by exp((log K ) O (1) ) translates of a prop er generalized arithmetic progression Q with dimension d ≤ O ((log K ) O (1) ) and size exp((log K ) O (1) ) | X | . W e express Q as Q = ( d X i =1 ℓ i x i : | ℓ i | ≤ L i ) , and let P = ( d X i =1 ℓ i x i : | ℓ i | ≤ L i 4 ) . Note that Q satisfies the conditions of Theorem A.2 , so there are in tegers x ′ 1 , . . . , x ′ d suc h that the map h ′ : Q → Z defined b y h ′ d X i =1 ℓ i x i ! = d X i =1 ℓ i x ′ i . 59 is order-preserving, and such that | h ′ ( x ) | ≤ d O (log d ) | Q | . Let R = ( d X i =1 ℓ i x i : | ℓ i | ≤ L i 8 ) . W e claim that the restriction of h ′ to the domain R is sum-order-preserving. Indeed, fix any x 1 , x 2 , y 1 , y 2 ∈ R , and supp ose that x 1 + x 2 < y 1 + y 2 . Note that x 1 + x 2 is an elemen t of P , and th us h ′ ( x 1 ) + h ′ ( x 2 ) = h ′ ( x 1 + x 2 ) b y definition. The same holds for y 1 and y 2 . Moreo ver, we hav e h ′ ( x 1 + x 2 ) < h ′ ( y 1 + y 2 ) as h ′ is order- preserving. Com bining these facts w e indeed ha ve h ′ ( x 1 ) + h ′ ( x 2 ) < h ′ ( y 1 ) + h ′ ( y 2 ) . Next, observe that O (1) d = exp((log K ) O (1) ) translates of R co ver P , and in turn exp((log K ) O (1) ) translates of P co ver X . Hence, for some translate t the set Y = ( R + t ) ∩ X has size | X | / exp((log K ) O (1) ) . Let h : Y → Z b e defined by h ( x ) = h ′ ( x − t ) . The sum-order-preserving prop erty is maintained under linear transformations, hence h is sum-order-preserving. Moreov er, recall that for all x ∈ Y we hav e that | h ( x ) | = | h ′ ( x − t ) | ≤ d O ( d ) | Q | ≤ d O ( d ) O (1) d | P | ≤ d O ( d ) O (1) d exp((log K ) O (1) ) | X | ≤ exp((log K ) O (1) ) | X | , and th us h : Y → {− K ′ | X | , . . . , K ′ | X |} for some K ′ = exp((log K ) O (1) ) . A final cosmetic mo dification is to restrict the range of h to { 0 , . . . , | X |} as in the theorem statemen t. T o this end partition {− K ′ | X | , . . . , K ′ | X |} in to O ( K ′ ) in terv als of size at most | X | . T ake the range with largest preimage in Y , and restrict Y to that preimage. This preserves at least an exp((log K ) O (1) ) -fraction of the elemen ts in Y and the remaining map is cl early still sum-order-preserving. A.2 P olynomial Bounds? It is an op en question whether the quasi-p olynomial b ounds from the previous section can b e improv ed to p olynomial. This is e xactly Hyp othesis 1.12 —the h yp othesis that our full universe reduction for APSP is conditioned on: Hyp othesis 1.12 (Sum-Order-Preserving Hashing with Polynomial Bounds) . Ther e is a c onstant c such that for every inte ger set X with doubling | X + X | ≤ K | X | ther e is a subset Y ⊆ X of size | Y | ≥ Ω( | X | /K c ) and a sum-or der-pr eserving function h : Y → { 0 , . . . , | X |} . Mor e over, given X one c an c ompute Y and h in time | X | 1+ o (1) K O (1) . In the follo wing paragraphs w e muse on a p ossible pro of of Hypothesis 1.12 . It seems plausible that a pro of of Hyp othesis 1.12 could w ork along the same lines as in the previous subsection. This would require t wo improv emen ts: strengthening the F reiman-Ruzsa theorem as w ell as the condensing lemma to ha ve p olynomial b ounds. The first is exactly the famous Polynomial F r eiman-Ruzsa (PFR) Conje ctur e . Its finite field analogue has recen tly b een resolved in a celebrated pap er by Go wers, Green, Manners, and T ao [ 59 ]. The second is not as w ell-studied. How ever, the proof of the condensing lemma relies on the same “geometry of num b ers” tec hnique that the state-of-the-art pro ofs for the F reiman-Ruzsa theorem also rely on [ 87 ]. F or this reason it is reasonable to hop e that a resolution of the PFR Conjecture migh t resolve our second issue along the w ay . On a technical lev el, there is one more obstacle: The PFR Conjecture is known to b e false for generalized arithmetic progressions by a counterexample due to Lo vett and Regev [ 76 ]. That is, we cannot expect that Theorem A.1 as it is stated here can b e improv ed to p olynomial b ounds. Instead, the usual formulation of the PFR Conjecture inv olves more general ob jects called c onvex pr o gr essions ; see also [ 77 ]. The consequence for us is that, in a h yp othetical pro of of Hyp othesis 1.12 along the lines we describ ed b efore, the condensing lemma would also need to b e generalized to con vex progressions. Alternativ ely , this issue could b e a voided b y resorting to the follo wing even weak er v ersion of Hyp othesis 1.12 : 60 Hyp othesis A.3. F or every ϵ > 0 ther e is some c onstant c ≥ 0 such that t he fol lowing holds. F or every inte ger set X with doubling | X + X | ≤ K | X | ther e is a subset Y ⊆ X of size | Y | ≥ Ω( | X | 1 − ϵ /K c ) and a sum-or der-pr eserving function h : Y → { 0 , . . . , | X |} . Mor e over, given X one c an c ompute Y and h in time | X | 3 − Ω ϵ (1) K O ϵ (1) . Indeed, when allowing a small polynomial loss of the form | X | ϵ then Lov ett and Regev’s coun terexample do es no longer apply , and it is conceiv able that the proof a voids conv ex progressions. Hyp othesis A.3 is still strong enough to imply all of our results implied b y Hyp othesis 1.12 ; see Remark 5.15 . As a final note, recall that for us it is necessary to also c ompute Y and h (as stated in Hyp otheses 1.12 and A.3 ). This is p erhaps the smallest concern—prior work on additive combinatorics in algorithm design has already p orted many existen tial theorems to computational v ersions [ 32 , 29 , 28 , 1 , 83 , 53 ], and most of these adaptations did not deviate significantly from their original proofs (a notable exception is [ 42 ]); relatedly , there has already b een recent work on turning the finite-field PFR theorem [ 59 ] into an efficien t algorithm [ 12 ]. B Derandomization of the Conflict-F ree Co v ering Lemma The purp ose of this section is to complete the missing pro of of Lemma 3.7 . The o verall idea is to derandomize the simple randomized algorithm describ ed earlier in Section 4 by the metho d of conditional exp ectations, ho wev er, to ac hieve a sufficiently efficient algorithm some technical details are necessary . Lemma 3.7 (Conflict-F ree Co vering) . L et x 1 , . . . , x n ∈ [ r ] and let C 1 , . . . , C n ⊆ [ r ] b e sets of size at most s such that x i ∈ C i for al l i . W e say that a set S ⊆ [ r ] cov ers item i if x i ∈ S and C i ∩ S = ∅ . Then ther e is a c ol le ction S of size |S | ≤ O ( s log n ) so that e ach i ∈ [ n ] is c over e d by some set S ∈ S . Mor e over, ther e is a deterministic ˜ O ( nr ) -time algorithm that c onstructs S , along with a mapping [ n ] → S indic ating for e ach item i by which set it is c over e d. Pro of. Let S ← ∅ be the collection of sets w e are about to construct, and let I ⊆ [ n ] denote the set of remaining items i that are not cov ered b y S (i.e., I = { i ∈ [ n ] : ∄ S ∈ S : x i ∈ S and C i ∩ S = ∅} ). W e will rep eatedly construct sets S to b e inserted in to S . W e describ e how to construct the next such set S . Initialize S ← ∅ , and consider the partition I = B ( S ) ⊔ G ( S ) ⊔ U ( S ) in to the remaining b ad , go o d , and unde cide d items defined by B ( S ) = { i ∈ I : C i ∩ S = ∅} , G ( S ) = { i ∈ I : C i ∩ S = ∅ and x i ∈ S } , U ( S ) = { i ∈ I : C i ∩ S = ∅ and x i ∈ S } whic h we will maintain throughout the construction of S . W rite ϕ ( S ) = | G ( S ) | − | B ( S ) | 2 s for the p otential of S . As w e will prov e shortly , we are alw ays in one of t wo cases: (1) there is some j ∈ [ r ] so that when inserting j into S the p oten tial increases b y at least ϕ ( S ∪ { j } ) − ϕ ( S ) ≥ | I | / (8 r ) , or (2) there are man y go od items, | G ( S ) | ≥ | I | / (16 s ) . While we are in the first case w e insert the respective elemen t into S . When we are even tually in the second case w e ha ve completed the construction of S , so w e up date S ← S ∪ { S } , up date I appropriately (i.e., remov e all indices i co vered b y S ), and, while I = ∅ , pro ceed to the construction of the next set S . This almost completes the description of the algorithm, but w e ha ve not describ ed yet how to efficien tly find such an elemen t j ∈ [ r ] . W e will now first analyze that the algorithm is correct, and later describ e the missing efficien t implementation. 61 Correctness. First, it is clear that the algorithm terminates after at most |S | ≤ O ( s log n ) rounds. Indeed, in eac h round w e decrease | I | by at least | G ( S ) | ≥ | I | / (16 s ) , so after O ( s ) rounds the size of | I | has at least halv ed, and after O ( s log n ) rounds the remaining set I m ust be empty . It remains to prov e the k ey claim that whenev er | G ( S ) | < | I | / (16 s ) w e can find some j ∈ [ r ] with a p oten tial increase of at least ϕ ( S ∪ { j } ) − ϕ ( S ) ≥ | I | / (8 r ) . In the construction of S the initial potential ϕ ( ∅ ) is zero and it stays nonnegativ e throughout, th us we can b ound the num b er of bad items by: | B ( S ) | = 2 s · ( | G ( S ) | − ϕ ( S )) ≤ 2 s · | G ( S ) | ≤ | I | 8 . It follo ws that almost all items are undecided: | U ( S ) | = | I | − | B ( S ) | − | G ( S ) | ≥ | I | − | I | 8 − | I | 16 s ≥ 3 | I | 4 . No w pretend that we sample an element j ∈ [ r ] uniformly at random. On the one hand, for each undecided item i ∈ U ( S ) the probabilit y that i b ecomes go o d in S ∪ { j } is exactly 1 /r . On the other hand, for eac h go od item i ∈ G ( S ) ⊔ U ( S ) the probability that i b ecomes bad in S ∪ { j } is at most s/r , and thus: E [ | G ( S ∪ { j } ) | − | G ( S ) | ] ≥ | U ( S ) | r − s | G ( S ) | r ≥ 3 | I | 4 r − s | I | 16 r s ≥ 5 | I | 8 r . A t the same time, the probabilit y that an y item i b ecomes bad is at most s/r , hence E [ | B ( S ∪ { j } ) | − | B ( S ) | ] ≤ s | I | r . It follo ws that E [ ϕ ( S ∪ { j } ) − ϕ ( S )] = E | G ( S ∪ { j } ) | − | G ( S ) | − | B ( S ∪ { j } ) | − | B ( S ) | 2 s ≥ 5 | I | 8 r − s | I | 2 r s = | I | 8 r . In particular, there exists an element j ∈ [ r ] so that b y adding j to S the p oten tial w ould increase b y at least | I | / (8 r ) . Efficien t Implementation. W e now turn to the problem of efficien tly constructing the set S . Specifically , w e giv e an efficient algorithm that, while | G ( S ) | < | I | / (16 s ) , finds some j ∈ [ r ] with a p oten tial increase of at least ϕ ( S ∪ { j } ) − ϕ ( S ) ≥ | I | / (8 r ) . W e rely on some prepro cessing. If necessary increase r to a p ow er of 2 . Recall that a dyadic interv al J ⊆ [ r ] is a set of the form a 2 ℓ + { 1 , . . . , 2 ℓ } for some 0 ≤ ℓ ≤ log r and a ∈ { 0 , . . . , r / 2 ℓ − 1 } . In the prepro cessing phase we compute and store, for all i ∈ [ n ] and all dy adic in terv als J ⊆ [ r ] , the sizes | C i ∩ J | and |{ x i } ∩ J | . With access to this data we can, giv en an y sets G, U ⊆ [ n ] and any dyadic interv al J ⊆ [ r ] , ev aluate the follo wing quantit y in time O ( n ) : E J ( G, U ) = 1 | J | X i ∈ U |{ x i } ∩ J | − X i ∈ G | C i ∩ J | − 1 2 s X i ∈ G ∪ U | C i ∩ J | ! . The key here is that E J ( G ( S ) , U ( S )) = E [ ϕ ( S ∪ { j } ) − ϕ ( S )] , where j is sampled uniformly random from J . Indeed, b y the same argumen t as b efore we ha ve that E J ( G ( S ) , U ( S )) = E X i ∈ U ( S ) |{ x i } ∩ { j }| − X i ∈ G ( S ) | C i ∩ { j }| − 1 2 s X i ∈ G ( S ) ∪ U ( S ) | C i ∩ { j }| = E | G ( S ∪ { j } ) | − | G ( S ) | − | B ( S ∪ { j } ) | − | B ( S ) | 2 s = E [ ϕ ( S ∪ { j } ) − ϕ ( S )] . 62 W e return to the construction of S . If | G ( S ) | < | I | / (16 s ) we hav e that E [ r ] ( G ( S ) , U ( S )) ≥ | I | / (8 r ) by the correctness argument from b efore. Moreov er, note that for any dyadic in terv als J = J 1 ⊔ J 2 , E J ( G, U ) is exactly the av erage of E J 1 ( G, U ) and E J 2 ( G, U ) . Based on this insight, w e binary-searc h for j . W e start with J = [ r ] . While J can b e split into J = J 1 ⊔ J 2 w e up date J ← J 1 if E J 1 ( G ( S ) , U ( S )) ≥ E J ( G ( S ) , U ( S )) , and update J ← J 2 otherwise. Ev entually we reach J = { j } , and then | I | 8 r ≤ E { j } ( G ( S ) , U ( S )) = ϕ ( S ∪ { j } ) − ϕ ( S ) as claimed. Running Time. W e finally analyze the running time of this algorithm. In the prepro cessing step w e consider the n items and O ( r log r ) dyadic interv als; with a little care we can precompute all sizes | C i ∩ J | and |{ x i } ∩ J | in time O ( nr log r ) . T o analyze the main phase of the algorithm we first b ound the size of the sets S . Recall that whenever w e insert an element j into some set S then the p oten tial ϕ ( S ) increases by at least | I | / (8 r ) . Hence, we hav e that | G ( S ) | ≥ ϕ ( S ) ≥ | S | | I | 8 r , and thus after inserting at most r /s elements into S the algorithm halts the construction and pro ceeds to the next set S . That is, | S | ≤ r /s . In particular, we query at most O ( |S | · r /s · log r ) v alues E J ( G, U ) in total. Each query takes time O ( n ) , so the total query time is O ( |S | · r /s · log r · n ) = O ( nr log n log r ) . All other bo okkeeping steps run in negligible time O ( nr ) . 63
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment