Privacy-Preserving Iris Recognition: Performance Challenges and Outlook
Iris-based biometric identification is increasingly recognized for its significant accuracy and long-term stability compared to other biometric modalities such as fingerprints or facial features. However, all biometric modalities are highly sensitive…
Authors: Christina Karakosta, Lian Alhedaithy, William J. Knottenbelt
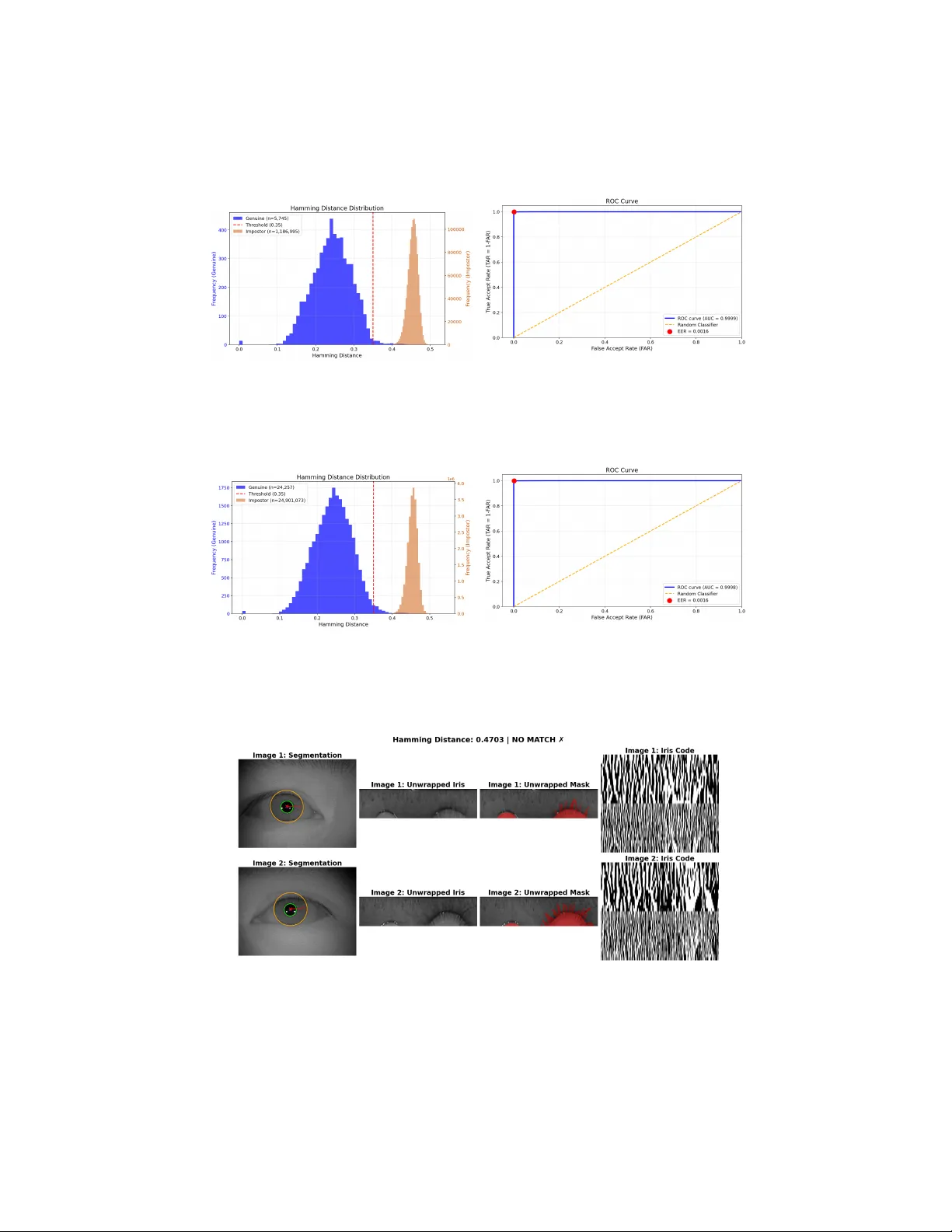
Priv acy-Preserving Iris Recognition: P erformance Challenges and Outlo ok Christina Karak osta , Lian Alhedaithy , and William J. Knottenbelt Departmen t of Computing, Imp erial College London {c.karakosta20,lian.alhedaithy24,w.knottenbelt}@imperial.ac.uk Abstract. Iris-based biometric identification is increasingly recognized for its significan t accuracy and long-term stabilit y compared to other biometric mo dalities such as fingerprints or facial features. How ever, all biometric modalities are highly sensitiv e data that raise serious priv acy and securit y concerns, particularly in decen tralized and un trusted en- vironmen ts. While F ully Homomorphic Encryption (FHE) has emerged as a promising solution for protecting sensitive data during computa- tion, existing priv acy-preserving iris recognition systems face significant p erformance limitations that hinder their practical deploymen t. This pa- p er in vestigates the p erformance challenges of the curren t landscap e of priv acy-preserving iris recognition systems using FHE. Based on these insigh ts, we outline a scalable priv acy-preserving framework that aligns with all the requiremen ts sp ecified in the ISO/IEC 24745 standard. Lev eraging the Op en Iris library , our approac h starts with robust iris segmen tation, follow ed b y normalization and feature extraction using Gab or filters to generate iris co des. W e then apply binary masking to fil- ter out unreliable regions and p erform matching using Hamming distance on encrypted iris co des. The accuracy and performance of our prop osed priv acy-preserving framework is ev aluated on the CASIA-Iris-Thousand dataset. Results show that our priv acy-preserving framew ork yields very similar accuracy to the cleartext equiv alent, but a m uch higher compu- tational ov erhead with respect to pairwise iris template comparisons, of ∼ 120 000 × . This p oin ts tow ards the need for the deploymen t of t wo-lev el sc hemes in the context of scalable 1–N template comparisons. Keyw ords: Biometrics · Iris recognition · Iris segmentation · Iris co des · Priv acy-preserving iris recognition · F ully Homomorphic Encryption. 1 In tro duction Biometric iden tification systems ha v e become one of the most reliable forms of p ersonal authentication in the digital world. In particular, iris-based identi- fication has emerged as highly reliable due to the uniqueness and stability of iris patterns throughout an individual’s lifetime [2]. Studies indicate that an iris co de can contain o ver 200 bits of entrop y , which is significan tly more than finger- prin ts [33], providing enough discriminatory p ow er to distinguish ov er 8 billion 2 C. Karakosta et al. p eople [12]. This high en tropy makes iris recognition more accurate than facial recognition. In the early 1990s, John Daugman pioneered the foundational w ork in iris recognition b y dev eloping algorithms for iris pattern enco ding and matc hing with v ery high accuracy . Daugman’s approac h enco des the iris texture using m ulti-scale 2D Gabor w a velets and compares the binary iris codes using the fractional Hamming distance as a similarity metric [11]. Highly reliable iden- tification is p ossible by testing for statistical independence b etw een iris co des, ac hieving rapid matc hing via X OR operations on IrisCo des. How ev er, biometric data are highly sensitive Personally Iden tifiable Information (PI I). This creates serious securit y and priv acy threats in the even t of a data breach. A stolen bio- metric template could b e reused b y attack ers for identit y theft or cross-matc hing across databases. If an attack er accesses a biometric template from one system, that individual’s identit y could b e compromised in all other systems using the same biometric. Such risks are increased in decen tralized en vironments where data and computation are distributed across multiple entities without a cen- tral authorit y . In resp onse to these concerns, international standards suc h as ISO/IEC 24745 [17] pro vide requirements and guidelines for protecting biomet- ric information, emphasizing principles such as irrev ersibility , unlink ability , and confiden tiality of biometric data throughout its lifecycle. Therefore, there is a critical need to handle biometric data differently than passw ords, in order to preven t reconstruction, cross-linking, and unauthorized use of these immutable p ersonal identifiers. Priv acy-Enhancing T echnologies (PET s) hav e b een explored to address these challenges. V arious approaches ha ve b een prop osed for priv acy-preserving biometric authentication, including F ully Homomorphic Encryption (FHE), Secure Multi-Part y Computation (MPC), and other h ybrid approaches. Problem Statement: Ho wev er, existing iris recognition systems using PET s, esp ecially FHE-based solutions, face serious scalability constraints. There is a fundamental trade-off b et w een priv acy , p erformance, and usabilit y . Curren t fully homomorphic approaches incur substantial computation and communica- tion ov erhead when scaling to large databases or real-time iden tification scenar- ios. One analysis show ed that transmitting a single 12 800-bit iris co de under t ypical FHE would require ab out 37 MB of ciphertext [26]. Storing an encrypted database of 100 000 iris co des could require 3.5 terabytes of storage space [26], whic h is an impractical burden on net work and storage resources. Similarly , computation latency is a c hallenge, since executing a homomorphic iris code comparison can take seconds of CPU time [24], and performing thousands or millions of such comparisons for iden tification would b e prohibitively slo w with- out significan t optimization or parallelization. Another b ottlenec k is the handling of rotation alignmen t and masking of iris co des under encryption. Iris templates must be aligned (rotationally shifted) ac- cording to the ey e orientation differences, which normally requires m ultiple X OR comparisons of shifted co des. Doing this ov er encrypted data is extremely exp en- siv e, inv olving costly cyclic shifts on ciphertext or re-encrypting multiple shifted Priv acy-Preserving Iris Recognition: Performance Challenges and Outlo ok 3 copies. Bassit et al.’s study confirms that supp orting rotations under encryption reduces matc hing p erformance, whereas alignment-in v arian t metho ds (such as Blo om filter representations) maintain a sp eed adv antage [3]. Thus, the k ey bar- riers to practical deplo yment are: (i) the computational cost of homomorphic op erations on large binary iris co des, (ii) the complexity of template alignment and masking when data is encrypted, and (iii) the explosion of ciphertext size whic h affects storage and bandwidth. This res earc h aims to surv ey these b ottlenec ks in existing FHE-based iris recognition frameworks and then outline an end-to-end priv acy-preserving iris biometric system suitable for real-world use. W e identify ho w current metho ds lac k a balance b et ween priv acy and p erformance, and prop ose architectural and algorithmic optimizations to bridge that gap. In particular, w e presen t a frame- w ork for trust worth y , priv acy-b y-design digital identit y systems using FHE that addresses the abov e challenges. Our approach incorp orates efficient iris co de gen- eration and matching techniques for encrypted op erations, including metho ds to deal with masks and rotations in a cost-effective fashion. W e also ensure the framew ork aligns with international standards (ISO/IEC 24745) for biometric information protection, embedding priv acy and security requirements b y design. Con tributions: The main contributions of this pap er are: – Performanc e A nalysis: W e provide a structured survey of prior priv acy- preserving iris recognition systems and analyze their p erformance limita- tions. W e highligh t p erformance b ottlenec ks in encrypted matc hing, mask handling, rotation, storage, and comm unication ov erheads. – Pr op ose d F r amework: W e integrate a standard iris-recognition pip eline (seg- men tation, normalization, Gab or encoding, masking) into an FHE-based matc hing workflo w. W e ev aluate the masking and rotation cost, and the fea- sibilit y of p erforming end-to-end iris-recognition under fully homomorphic op erations. – Implementation and Evaluation: W e implement a pro of-of-concept system using a lattice-based FHE scheme and ev aluate cleartext vs. encrypted matc h- ing on the CASIA-Iris-Thousand dataset. W e quan tify computational la- tency , communication ov erhead, ciphertext size, and the impact of parameter c hoices on p erformance. The remainder of this pap er is organized as follows. Section 2 provides back- ground on biometric priv acy c hallenges and an ov erview of priv acy-enhancing tec hnologies applicable to biometrics. Section 3 reviews related work in priv acy- preserving iris recognition and compares different approaches. Section 4 de- scrib es the prop osed system architecture, participan ts, and security mo del. Sec- tion 5 details our metho dology , including the iris co de generation pro cess and the homomorphic encryption and matching tec hniques. Section 6 presen ts the exp erimen tal setup and metrics for ev aluation. Section 7 discusses the results, p erformance analysis, and insigh ts from the ev aluation. Finally , Section 8 con- cludes the pap er and outlines directions for future work. 4 C. Karakosta et al. 2 Bac kground 2.1 Biometric Priv acy Concerns Biometric data requires different handling than conv entional authen tication se- crets, lik e passwords or tokens, because of its p ermanence and link to an individ- ual’s identit y [15]. Biometrics suc h as fingerprints, face images, or iris patterns are uniquely link ed to a p erson and effectively irreplaceable. – Irrev ersible Disclosure: A stolen biometric template can b e used to re- construct or imp ersonate the original trait. Researchers hav e demonstrated that compromised iris co de data could p oten tially b e used to generate a fak e iris image. Thus, biometric identifiers must b e highly protected to preven t irrev ersible priv acy violation. – Cross-Con text Link age: Because biometric identifiers are globally unique to a p erson, leaks can enable link age across databases. F or example, if one’s iris co de from an authentication system is exp osed, an adversary could scan other databases or systems for a matching co de to link that p erson’s activities across differen t services. This could lead to a violation of unlink abilit y , mass surv eillance or profiling. – Iden tity Theft and F raud: Stolen biometrics can be used for identit y theft or unauthorized access. A ttack ers might use fingerprints or high-resolution iris images to bypass biometric access control (presentation attacks). Alter- nativ ely , an attack er could create a synthetic iden tity by com bining some- one’s biometric with false demographic data. Since biometrics are often con- sidered highly secure, many systems may not ha ve secondary verification, making a stolen biometric a single p oin t of failure for identit y . – Sybil Attac ks in Digital ID: In decen tralized iden tit y systems, a k ey threat is a Sybil attack, where one person tries to obtain m ultiple identities. Biometrics are often employ ed to resist Sybil attacks by enforcing uniqueness ( one per son = one I D ). How ever, if biometric protections fail, an attack er could duplicate or forge biometrics to create many fake identities. F or in- stance, without robust protection, a malicious user might replay an iris co de to register multiple times under differen t names. Preven ting Sybil attac ks requires ensuring the biometric cannot b e easily duplicated or abused across the system. In summary , biometrics offer strong authentication b enefits due to their uniqueness, but these same prop erties demand stronger safeguards. Reconstruc- tion, link age, identit y fraud, and Sybil attac ks are primary threats. This necessi- tates sp ecialized priv acy protections (e.g., template encryption, secure storage, liv eness detection) b ey ond what is needed for traditional secrets. 2.2 Priv acy-Enhancing T echnologies for Biometrics Priv acy-Enhancing T echnologies (PET s) can secure biometric data ev en during pro cessing. Key PET s approaches in the biometric field include the follo wing: Priv acy-Preserving Iris Recognition: Performance Challenges and Outlo ok 5 – F ully Homomorphic Encryption (FHE): FHE allows computations to b e performed on encrypted data without ever decrypting it. In a biomet- ric system, this means an iris or fingerprint template can remain encrypted while the server computes a match score. FHE guaran tees confiden tiality b ecause the server, or any eav esdropp er, sees only encrypted results. This directly addresses priv acy and confiden tiality requiremen ts (ISO/IEC 24745 emphasizes confidentialit y and irreversibilit y). FHE p erformance is limited b y homomorphic op erations that are orders of magnitude slo wer than nor- mal operations and produce m uch larger ciphertexts. F or example, basic FHE schemes might encrypt each bit of an iris co de into a large ciphertext p olynomial, leading to huge data sizes and computational ov erhead for each comparison. FHE also assumes an “honest-but-curious” threat mo del where the server will not alter computations maliciously . Despite these costs, FHE pro vides a trustable model where even an un trusted server cannot learn biometric data, so a single server suffices, simplifying deplo yment if the p er- formance can b e managed. – Secure Multi-P arty Computation (MPC): MPC proto cols distribute the computation across m ultiple parties so that no single party can see the en tire input. In a biometric setting, the biometric template can b e split into shares held by different servers. The servers then engage in an interactiv e proto col to jointly compute a function, without rev ealing their shares. The strength of MPC is that it can often b e more efficient than FHE for cer- tain op erations by lev eraging light w eight secret-sharing sc hemes and parallel computation. F or instance, W orldcoin’s deplo yment uses an MPC proto col to compare iris co des for uniqueness across millions of users [29]. The iris co de and its mask are split into shares and distributed to multiple servers, whic h p erform comparison without reconstructing the co de [29]. Man y linear op erations (X ORs, additions) can b e done with no comm unication in MPC, and clever proto cols exist for non-linear op erations (e.g., counting bits) with far less communication than naive metho ds [26]. MPC relies on a trust mo del where a threshold of parties m ust remain honest and non-colluding. While it in tro duces netw ork latency due to message exchanges for every op eration, MPC has demonstrated practical scalabilit y . – F unctional Encryption (FE): F unctional Encryption is a newer approac h where possessing a certain secret k ey allo ws one to learn only a specific function of the encrypted data. In biometrics, FE enables a server to use a sp ecific key that rev eals only the match score or a binary decision from encrypted data. F or example, a p olicy could b e enco ded so that decryption rev eals “ match if distance < thr eshold ” without exp osing ra w biometric templates. In this wa y it can enforce access control at a data lev el, while the serv er acc esses only a p ermitted result and never the raw biometric. FE can b e though t of as an extension of attribute-based encryption for computations. Ho wev er, general functional encryption is complex and often less efficient. While prototypes like inner pro duct schemes exist [13], FE is curren tly not efficien t enough for high-dimensional biometrics and ma y still require trust in a k ey issuer or authority for key distribution and policy enforcement. 6 C. Karakosta et al. – Hybrid Approaches: Bloom filters provide a cancelable, priv acy-protecting transformation for biometric templates. They enco de feature p ositions into bit strings, obscuring exact bits while allowing similarit y comparisons (e.g., w eighted Hamming distance) [3]. Blo om filters are fast, space-efficient, po- ten tially non-inv ertible, and inheren tly handle rotations without brute-force shifting. Ho wev er, p o or designs risk link abilit y [23]. Hybrid approac hes, like Bassit et al. [3], address this by combining randomized Blo om filters with homomorphic encryption. This ac hieves the sp eed of Blo om filters with the securit y of encryption, significan tly outp erforming pure FHE while meeting ISO priv acy standards. While promising, hybrid schemes add system com- plexit y and ma y offer weak er security guarantees than FHE, as protection relies partially on transformation rather than encryption. – T rusted Execution En vironments (TEEs): T rusted Execution Environ- men ts (TEEs), such as Intel SGX or ARM T rustZone , provide hardware- isolated execution for sensitiv e co de and can p erform iris matching on plain- text data inside an enclav e. This eliminates the hea vy computational ov er- head of FHE since Hamming distance can b e computed directly on the plain- text template. How ever, their security relies on trusting hardw are v endors, firm ware updates, and resistance to side-c hannel attacks [14,21,22,25,28]. Th us, the reliance on TEEs introduces securit y risks, reinforcing the deci- sion of building a cryptographic and hardw are-agnostic solution. Eac h of these approaches can b e part of a priv acy-b y-design biometric system. In practice, com binations may b e used to leverage the adv an tages of each. 2.3 Biometric T emplate Protection Mec hanisms Bey ond cryptographic PET s, several mechanisms protect biometric templates against irrev ersible disclosure and link age attac ks. Canc elable biometrics use non-in vertible transformations (e.g., random pro jection, BioHashing) that allow rev o cation and re-issuance if a template is compromised. Se cur e sketch and fuzzy c ommitment schemes cryptographically bind biometric data to auxiliary help er data without leaking the underlying template. Even if stored data are leak ed, the original iris co de cannot b e reconstructed. Finally , fuzzy extr actors derive stable cryptographic keys from noisy biometric signals while exp osing only public help er data with prov ably limited leak age. Strengthened fuzzy extractors increase en tropy extraction and reduce cross-database link ability . Our work fo cuses on protecting the matching pro cess using FHE, and suc h template-protection metho ds could b e lay ered on top of our design. 3 Related W ork Early research on priv acy-preserving biometric recognition explored b oth cryp- tographic proto cols and signal transformations. In the context of iris recogni- tion, some of the first solutions used partial homomorphic encryption or t wo- part y proto cols to compute the Hamming distance securely . Blan ton and Gasti Priv acy-Preserving Iris Recognition: Performance Challenges and Outlo ok 7 (2011) [4] proposed secure proto cols for iris and fingerprin t iden tification us- ing an additively homomorphic cryptosystem (DGK) and garbled circuits [10]. Their proto col could compare 2048-bit iris co des in ab out 150 ms, highlighting the feasibility of fast encrypted matching [4]. How ever, the efficiency came with a trade-off: the smaller ciphertext size in their scheme meant low er cryptographic securit y , underscoring the tension b et ween efficiency and strength. Subsequent w orks mov ed to stronger encryption at the cost of sp eed. Kulk arni et al. imple- men ted an iris authentication using a somewhat homomorphic encryption (SHE) sc heme, achieving 58 seconds server time for matching a 2 048-bit iris co de, with a few rounds of interaction [19]. Karabat et al. (2015) prop osed a threshold ho- momorphic encryption proto col ac hieving server and client computation times of ∼ 6.1 s and 2.1 s, resp ectiv ely [18]. These studies highlight that FHE, while more secure, requires significan t optimization for practicality . More recent works hav e fo cused on leveraging improv ed FHE schemes and data handling techniques. Morampudi et al. (2020) introduced a priv acy-pre- serving iris authentication metho d based on the BFV homomorphic encryption sc heme [20]. They addressed one of the ma jor p erformance issues, rotation align- men t, by generating rotation-inv ariant iris co des so that the costly cyclic shifts under encryption could b e av oided. They also used SIMD batching on cipher- texts to pac k multiple iris co de bits into a single p olynomial, amortizing opera- tion costs. Their system satisfied the ISO/IEC 24745 requirements for biometric template protection and rep orted no loss in accuracy compared to an unen- crypted system. In fact, they achiev ed an Equal Error Rate (EER) of 0.19% on the standard CASIA-Iris V1 dataset, whic h is on par with cleartext iris recog- nition p erformance. Their homomorphic Hamming distance for a 2 560-bit iris co de to ok only ab out 0.0185 seconds. On the MPC side, W orldcoin’s W orld ID system represents a state-of-the-art deplo yment for secure and scalable iris-based iden tification. Rather than per- forming heavy cryptography on a single server, W orldcoin secret-shares eac h iris co de among m ultiple nodes and uses MPC to c heck for duplicates [31]. Their pro- to col enables priv ate, million-scale matching via efficient distributed Hamming distance and threshold c hecks [26]. A k ey technical innov ation is the use of an “ef- ficien t dot pro duct” metho d to compute Hamming distances with communication costs indep enden t of vector size [26]. By con verting binary shares to arithmetic shares ov er a ring (e.g., 16-bit integers), the proto col reduces the complexity of a 12 800-bit Hamming distance computation from 25 000 AND gates to a fixed constan t. This efficiency enables significan t scalability , considering that sending a single iris co de of 32 MB FHE ciphertext would exceed the communication cost of their entire MPC proto col for a 100 000 record database. Th us, while MPC outp erforms FHE in multi-serv er en vironments, it necessitates higher op- erational complexity regarding server synchronization and strictly non-colluding parties. T emplate transformations, such as cancelable biometrics and fuzzy schemes, complemen t cryptographic metho ds. While less robust than FHE or MPC, these tec hniques prev en t reconstruction if data is stolen. Y ang et al. [32] highligh t 8 C. Karakosta et al. the benefit of hybrid approaches, where encrypting transformed templates adds defense-in-depth against decryption failures. How ev er, challenges remain regard- ing biometric v ariabilit y (e.g., rotation, noise) and standards compliance. Scalabilit y and latency remain primary bottlenecks for secure biometrics. FHE struggles with scaling, while MPC requires multiple serv ers and hea vy comm unication. T ransformations like Bloom filters offer sp eed but demand rig- orous securit y analysis. Building on [20,29], our work targets optimized p erfor- mance deploymen t b y strictly addressing encrypted iris rotations and masking, whic h were often simplified or brute-forced in prior works. Our design ensures unlink abilit y and preven ts raw biometric exp osure in compliance with priv acy standards. 4 System Arc hitecture and Securit y Mo del A high-level architecture of the prop osed priv acy-preserving iris recognition sys- tem is presented in Figure 1. The user-side device captures the iris image and lo cally computes the iris code ( x ) and mask ( m ) . The iris co de bits and masks are then encrypted ( ε ( x ) , ε ( m )) using the user’s public key ( δ ε ) before b eing sen t to the server. T he encrypted iris co de ( ε ( x )) is used as a query for matching against existing encrypted templates. The serv er (un trusted) performs homo- morphic computations on encrypted data to get the Hamming Distance result ( ε ( H D )) . Then, the result ( ε ( H D )) is decrypted using the priv ate decryption k ey ( δ d ), and compares the decrypted result with a threshold ( t ) . If the Ham- ming Distance is b elo w the threshold the user is already verified, otherwise the system enrolls the new user in the database. Fig. 1: FHE iris recognition system Priv acy-Preserving Iris Recognition: Performance Challenges and Outlo ok 9 P articipants in our system include: (1) The User , who o wns their biometric data. This could be an individual enrolling their iris on a personal device or an orb-like device. This device is resp onsible for the iris code generation and encryption of the iris code with the user’s public k ey . W e assume the user keeps their FHE priv ate key secure, whic h is needed to decrypt match results. (2) The Server , which is untrusted, stores encrypted biometric templates and p erforms homomorphic computations. The server is considered “ honest-but-curious ” by computing the Hamming Distance honestly , but may attempt to infer sensitive information from an y data it sees. In our design, the serv er only handles en- crypted data, and we do not require an y trusted hardw are on the serv er side . In an identification scenario ( 1–N matc hing), the server migh t play the dual role of pro viding the result to the user or an authorized verifier. Ho wev er, our current implemen tation ev aluates only 1–1 individual pairwise comparisons. Extending the system to encrypted 1–N iden tification remains future work. Threat Mo del: Our threat mo del assumes that all the main infrastructure, including the net work and the server, is untrusted. Communications pass ov er an untrusted netw ork, an eav esdropper could intercept messages, and an activ e attac ker might attempt “ man-in-the-midd le ” modifications. Thus, w e use stan- dard netw ork securit y (TLS) and ensure that all biometric data are encrypted. The serv er is considered curious, but non-colluding. It will follow the proto col steps, but is curious to learn sensitiv e information. It may also b e compromised b y an adv ersary who gains read-access to stored data. The user side is assumed to b e trusted with regard to their o wn biometric. The user will not inten tionally leak their priv ate k ey or biometric data. How ev er, malw are on a user’s device is a p oten tial threat. If an attac ker steals the user’s priv ate key , they could de- crypt the user’s template or results. Regarding key storage, we specifically av oid cen tralized management. While traditional systems secure master keys inside or- ganization trust b oundaries using Hardware Security Modules (HSMs), rep orted hac ks on HSMs [6] demonstrate that even FIPS-certified hardware can be com- promised. Th us, key protection on the client side, via secure storage or use of a hardw are tok en, is assumed. Also, multiple users do not collude by sharing keys or data, since eac h user has their own key pair. Insider thr e ats with database access ma y attempt to insp ect ciphertexts or misuse system metadata. Our design ensures that ciphertexts leak no biomet- ric information, but w e assume secure management of priv ate k eys. Malicious server outputs might return incorrect encrypted scores or manipulate threshold decisions. Detecting such b eha vior requires verifiable computation or redundant computation across multiple servers, which w e discuss as future work. Key loss of the user’s priv ate key requires re-enrolled under a fresh key . This preven ts cross-database link age but requires secure user-side key bac kup. Our security goals are: (1) No L e akage of R aw Biometric Data: The server or an y external adv ersary should not learn an y information about the user’s iris image or iris co de b ey ond what is rev ealed by the final match result. Even partial leak age, like num b er of bits matching, should b e minimized or prov ably b ounded. (2) Encrypte d Matching: All biometric comparisons for matching are 10 C. Karakosta et al. calculated on encrypted data. The system never needs to decrypt templates on the serv er side. (3) T emplate Pr ote ction (Irr eversibility): The stored encrypted template should not allow an attack er to reconstruct the original iris. Even if an attac ker somehow obtained a user’s encrypted iris co de and also knew the en- cryption sc heme, without the key they should not b e able to recov er the co de or an y significant part of it. Our use of FHE guarantees this under standard cryp- tographic assumptions. (4) Unlinkability: It should b e infeasible for an attac ker to determine if t wo encrypted templates b elong to the same p erson (unless they are an authorized party p erforming a match). This means, for example, if a user enrolls in tw o different databases with the same iris, the encrypted templates should b e unrelated. W e achiev e this by having each user use their own k ey so that encryptions of the same iris under differen t keys cannot b e linked. In summary , our arc hitecture addresses threats from netw ork adversaries, cu- rious or partially compromised serv ers, ins ider misuse, and client-side key com- promise, while ensuring priv acy through end-to-end encryption pro cessing. 5 Metho dology Our pro cessing pip eline consists of the following stages of iris recognition: (1) se gmentation , (2) normalization , (3) fe atur e extr action , and (4) matching . Fig- ure 2 outlines these stages in sequence. Fig. 2: Iris code feature extraction and matching proces s 5.1 Iris Co de Generation Pr epr o c essing: Input eye images are already in gra yscale. W e assess image quality b ecause p o or-qualit y images can degrade recognition and also waste computa- tional resources if pro cessed under encryption. W e detect and remo ve sp ecular highligh ts (reflections) which app ear as saturated white sp ots on the iris. A sim- ple method is using p ercen tile thresholding and then inpainting or smo othing o ver them, since sp ecularities can falsely app ear as unique features if not handled. After reflection remov al, the image is enhanced using contrast normalization to impro ve iris feature detection in the next steps. Se gmentation: This step isolates the iris region from the rest of the ey e im- age by determining the iris inner (pupil) b oundary and outer (sclera) b oundary , and identifying o cclusions by eyelids or eyelashes. W e emplo y a deep learning- based segmen tation approac h us ing the Op en Iris framework [30], whic h uti- lizes a conv olutional neural net work (CNN) trained on diverse iris datasets to Priv acy-Preserving Iris Recognition: Performance Challenges and Outlo ok 11 ac hieve robust b oundary detection. The mo del outputs precise pixel-lev el seg- men tation masks that distinguish the iris region from the pupil, sclera, eyelids, and eyelashes. This mo dern approach provides sup erior accuracy compared to classical metho ds, particularly for handling challenging cases with p oor ligh ting, partial occlusions, or off-angle captures. The output of segmentation is a bi- nary mask indicating which pixels b elong to the clear iris region ( 1 = v alid iris, 0 = o ccluded/in v alid), along with the detected inner and outer iris b oundaries. Normalization: Once the iris region is segmen ted, we transform it to a nor- malized co ordinate system to account for differences in iris size, pupil dilation, and imaging angle. W e use the standard Daugman rubb er-sheet mo del [11]: the ann ular iris region is mapp ed to a fixed-size rectangle with angular co ordinate θ along the horizontal axis and radial co ordinate r along the vertical axis. In our implementation, we adopt a resolution of 512 angular samples and 64 radial samples, yielding a normalized image of size 512 × 64 . This effectiv ely "unrolls" the iris in to a rectangular band where eac h ro w corresponds to a concen tric circular ring of the iris. The normalization comp ensates for iris size differences b y stretching or compressing radii to a constant length, and accoun ts for pupil dilation b y anchoring the mapping b etw een the pupil and iris boundaries. F e atur e Extr action: The normalized iris texture is encoded in to a binary iris co de using multi-scale 2D Gab or wa velets to extract lo cal phase information [11]. W e apply Gab or filters at multiple scales (w av elengths of 16 and 32 pixels) to capture texture features at different resolutions. Each Gabor filter produc es a complex-v alued resp onse, and we quantize the phase into t wo bits using quadrant enco ding: the real and imaginary comp onents determine whic h of four quadran ts the phase vector falls into, yielding tw o binary v alues p er filter resp onse. This pro cess is applied across the entire normalized iris image, generating t wo binary matrices (one for eac h scale). These matrices are then flattened and concatenated to form the final iris code. In our implementation, with a 128 × 512 effectiv e sampling grid (after do wnsampling from the 512 × 64 normalized image) and t wo scales, w e generate an iris co de of 128 × 512 × 2 = 131 072 bits. How ever, for computational efficiency in the FHE matching stage, w e downsample this to a co de length of 32 × 512 = 16 384 bits, which provides a balance b et w een discriminativ e p o wer and encryption ov erhead. Mask Gener ation: Alongside the iris co de, we generate a binary mask of the same dimensions indicating which bits of the iris co de are v alid. Bits are marked as in v alid (0 in the mask) due to o cclusion b y eyelids or ey elashes, sp ecular reflections, or regions near segmentation boundaries where texture reliabilit y is low. The segmentation stage identifies these regions, and we propagate this information through the normalization and feature extraction stages to mark the corresp onding co de bits as masked. Masking is crucial for robust matching, as it prev ents noise from con tributing to the Hamming distance. In our system, the mask is encrypted alongside the iris co de to enable priv acy-preserving masked matc hing. The mask and co de together form the biometric template. 12 C. Karakosta et al. Co de Alignment: Before encryption, w e prepare for handling rotation misalign- men t b etw een enrollmen t and verification captures. Ey e rotation or head tilt can cause the iris co de to shift circularly along the angular dimension. T o handle this, during the matching phase we p erform a rotational searc h by computing Hamming distances across multiple circular shifts of the iris co de. In our im- plemen tation, w e allow a searc h windo w of ± 15 columns (out of 512 angular samples), which corresp onds to approximately ± 10 . 5 ◦ of physical rotation. This range is sufficient to handle natural head tilt v ariations in co operative acquisition scenarios typical of datasets like CASIA-Iris-Thousand. Under FHE, this rota- tional search can b e implemented efficiently using ciphertext rotation op erations (automorphisms in the BFV sc heme) [24], though in our current implementation w e p erform the searc h by encrypting and comparing multiple shifted v ersions. By the end of these steps, the user has an iris co de and a corresp onding mask (b oth binary vectors). A t this p oin t, b oth are still in cleartext on the user side. The next phase inv olv es encrypting these templates and transmitting them to the serv er for priv acy-preserving matching. 5.2 Encryption and Hamming Distance Computation F ul ly Homomorphic Encryption Scheme: W e employ a F ully Homomorphic En- cryption technique based on the General Learning with Errors (GL WE) scheme, implemen ted through V aultree’s venumML [27] library . The GL WE scheme pro- vides the cryptographic foundation for all encrypted computations, enabling priv acy-preserving iris template matching without data exposure. Other libraries suc h as Microsoft SEAL [9] and Op enFHE [1] provide highly optimized BFV / BGV implemen tations and efficient bitwise op erations, which would likely pro- vide low er latency than a full PPML stack. Similarly , HElib [16] offers efficient ciphertext pac king (SIMD), making it suitable for 1–N matching scenarios. The General Learning With Errors (GL WE) sc heme is a lattice-based cryp- tographic primitive that generalizes the Learning with Errors (L WE) problem. It in tro duces structured noise ov er p olynomial rings, enabling compact ciphertexts and efficien t homomorphic op erations. GL WE is considered secure against clas- sical and quan tum attacks, making it suitable for p ost-quantum cryptography . Giv en a binary iris co de vector and a corresp onding mask, b oth arrays are flattened and eac h element is encrypted as follows: c i = ctx.encrypt ( b i ) , b i ∈ { 0 , 1 } (1) where ctx is the encryption con text initialized using SecretContext() . Encrypte d Matching with Hamming Distanc e: The template matc hing is p er- formed using normalized Hamming distance calculation b et ween iris co des. The fractional Hamming distance is computed using the generated masks to exclude unreliable bits from the comparison. The fractional Hamming distance (HD) quan tifies the dissimilarities b etw een tw o iris-co des, co de A and co de B , using their corresp onding mask vectors, mask A and mask B , as follo ws: Priv acy-Preserving Iris Recognition: Performance Challenges and Outlo ok 13 H D = || co de A ⊕ co de B ∩ mask A ∩ mask B || || mask A ∩ mask B || (2) In our system, the Hamming Distance (HD) is computed betw een encrypted iris co des homomorphically: – The encrypted X OR of tw o bits a and b is computed as: X OR ( a, b ) = a + b − 2 ab – The v alid mask is computed as the element-wise pro duct of the tw o encrypted masks. – The mask ed XOR v alues are summed to count the differing bits. – The total n umber of v alid bits is summed homomorphically . Let D denote the encrypted coun t of differing bits, and N the coun t of v alid comparisons. The encrypted normalized Hamming distance is D / N . After computation, the encrypted outputs D and N are sen t bac k to the user, who decrypts them using their priv ate key . The final Hamming distance is computed in cleartext: HD = D N Then, the HD is compared with a threshold ( thr eshol d = 0 . 35 ) to determine whether the t wo iris templates match. 6 Exp erimen tal Ev aluation and Results W e ev aluated our framework on a GNU/Lin ux system with an NVIDIA GeF orce GTX 1 080 GPU. W e utilized the Op en Iris library [30] for biometric pro cessing and V aultree’s venumML [27] library for all FHE operations, configured for a 128-bit security lev el. The analysis w as p erformed on the CASIA-Iris-Thousand dataset [8], which contains 20 000 iris images from 1 000 sub jects (10 images for eac h eye of 1 000 sub jects). After removing images with glasses, as they affect the image quality , we created four subsets of v arying sizes comprising 50, 100, 500 and 1 000 sub jects. Then, we p erformed all p ossible intra-class (genuine) and in ter-class (imp oster) comparisons to establish a cleartext p erformance baseline and assess scalabilit y . F urther details on the exp erimen tal setup are pro vided in App endix A.1. – CASIA 50 : A database of 50 sub jects con taining 755 iris templates. – CASIA 100 : A database of 100 sub jects con taining 1 487 iris templates. – CASIA 500 : A database of 500 sub jects con taining 6 777 iris templates. – CASIA 1K : A database of 1,000 sub jects containing 14 191 iris templates. 6.1 Cleartext Performance and Scalabilit y Analysis The cleartext matching p erformance demonstrated high accuracy and stability as the database size increased, as summarized in T able 1. The Equal Error Rate (EER) remained consistently low, ranging b et ween 0.12% and 0.27%, while the 14 C. Karakosta et al. F1 Scores exceeded 0.99 across all subsets, confirming the robustness of the feature extraction and matc hing algorithm. The ROC curv e and Hamming distance distributions for the largest 1 000- sub jects test ( CASIA 1K ), shown in Figure 3, illustrate the high separability b et w een genuine and imp oster p opulations ( d ′ ≈ 5 . 96 ). Unlike earlier baselines, the improv ed mean Imp ostor Hamming Distance ( ≈ 0 . 45 ) provides a significant safet y margin against false matc hes. The R OC curves for the smaller datasets w ere highly similar and are provided in the App endix A.2. T able 1: Performance Metrics Across Different Dataset Scales Metric CASIA 50 CASIA 100 CASIA 500 CASIA 1K T otal Comparisons 300.7k 1.19M 24.9M 107.4M Gen uine HD (Mean) 0.242 0.243 0.241 0.239 Imp ostor HD (Mean) 0.454 0.454 0.454 0.454 EER (%) 0.27 0.16 0.16 0.12 F1 Score 0.9945 0.9949 0.9928 0.9948 (a) ROC Curve and EER (b) Hamming Distance Distributions Fig. 3: Performance on the CASIA 1K dataset. The EER is approximately 0.12% at a threshold of 0.35, with an A UC of 0.9999. 6.2 Homomorphic Encryption Performance F or the FHE ev aluation, 1–1 comparisons on represen tative genuine (same ey e, differen t images) and imp oster (different sub jects) pairs demonstrated high pre- cision with a significant but predictable computational ov erhead. The complete pro cessing pip eline for the genuine pair comparison, from segmentation to iris co de generation, is visualized in Figure 4; a similar visualization for the imposter pair is pro vided in the App endix A.2. As detailed in T able 2, a single encrypted matc h to ok appro ximately 295–299 seconds, dominated by the homomorphic computation time ( ≈ 296s), with fast encryption ( ≈ 3.0s) and decryption ( < 0.01s). The decrypted Hamming distance for a genuine pair (0.1627) was iden tical to the cleartext result. F or the imp oster pair, the FHE result (0.4701) show ed a negligible difference ( 0 . 0002 ) compared to the cleartext baseline (0.4703), confirming that our priv acy-preserving frame- w ork maintains the accuracy of the underlying biometric algorithm. Priv acy-Preserving Iris Recognition: Performance Challenges and Outlo ok 15 Fig. 4: Processing and matching pipeline for a gen uine pair (HD = 0.1627). T able 2: Cleartext vs. FHE Comparison for Genuine and Imp oster P airs P air Method HD Numerator Denominator Time (s) Gen uine Cleartext 0.1627 1 914 11 761 0.003 FHE 0.1627 1 914 11 761 299.4 Imp oster Cleartext 0.4703 4 736 10 071 0.003 FHE 0.4701 4 734 10 071 295.1 7 Discussion The exp erimental results demonstrate the feasibilit y and reliability of iris recog- nition using homomorphic encryption-based matching. The cleartext baseline on the CASIA 1K dataset yielded an Equal Error Rate (EER) of just 0.12% and a separability index ( d ′ ) of 5.96, confirming that our segmen tation, normal- ization, and enco ding pip eline is highly effectiv e even at scale. The lo w F alse Rejection Rate (FRR) of approx. 0.96% suggests that the preprocessing steps handle common noise factors, such as eyelid o cclusion and partial illumination, robustly . Our prop osed priv acy-preserving pip eline achiev es effectiv ely iden tical matc h- ing accuracy under homomorphic encryption as in cleartext. F or genuine pairs, the decrypted Hamming distance w as iden tical to the plain text baseline, while imp ostor pairs show ed negligible deviation. This v alidates the mathematical cor- rectness of our FHE implementation for biometric authen tication. How ev er, this securit y comes with a significan t computational cost. A single 1–1 matching op eration, including encryption and 31 rotational shifts, requires approximately 295–300 seconds. While this latency is currently to o high for real-time user v er- ification, it prov es the viability of the approach for high-security , asynchronous v erification scenarios where priv acy is paramount. Applying an FHE sc heme end-to-end enables strong recognition accuracy without exp osing biometric templates. The primary b ottlenec k identified in our 16 C. Karakosta et al. analysis is the homomorphic execution of rotational shifts to correct for head tilt, whic h accounted for o ver 98% of the total computation time. These results are part of our ongoing work to balance sec urit y and usability . Next steps include exploring more sophisticated occlusion masks and analyzing the trade-offs of restricting the rotational searc h space to reduce latency . Limitations: While our results establish a strong pro of-of-concept, the current implemen tation is not y et a pro duction-ready solution for real-time applications. The latency introduced b y the homomorphic op erations, sp ecifically the iterative calculation of Hamming distances across m ultiple rotations, remains the critical c hallenge. F uture work will fo cus on optimizing this computational ov erhead. W e aim to explore adv anced FHE optimization tec hniques, such as batc hing m ultiple comparisons or utilizing sc hemes like CKKS, whic h could offer signifi- can t sp eedups b y vectorizing the distance computation at the cost of negligible appro ximation. 8 Conclusions and F uture W ork This paper in v estigated the k ey performance c hallenges of priv acy-preserving iris recognition systems, demonstrating that F ully Homomorphic Encryption (FHE) can protect sensitiv e biometric data throughout the entire authentication pip eline without compromising accuracy . Our exp erimen ts on the CASIA-Iris- Thousand dataset confirmed that the cryptographic ov erhead do es not degrade the underlying matching p erformance, achieving an Equal Error Rate (EER) of 0.12% and effectively identical Hamming Distance calculations in the encrypted domain compared to cleartext. The framework meets critical priv acy-by-design standards, making it suitable for high-securit y , decentralized identit y applica- tions. Ho wev er, we confirmed that the primary barrier to real-time adoption remains the significant computational latency , particularly for the iterativ e task of secure rotational alignmen t. 8.1 F uture W ork Our future researc h will fo cus on p erformance optimization and scalabilit y to bridge the gap b et w een proof-of-concept and production deplo ymen t. T o en- able scalable 1–N template comparisons, we will deploy a t wo-lev el hierarc hical searc h strategy . This approach will utilize a fast, ligh tw eigh t screening tier to rapidly filter out non-matc hing candidates, reserving the computationally inten- siv e full FHE comparisons only for the most promising matches. T o address the curren t latency b ottlenec ks, we will explore more efficient FHE schemes, such as CKKS, which can offer significan t sp eedups by vectorizing Hamming distance computations through approximate arithmetic. T o enhance practical utility for decen tralized identit y , we will w ork to wards implementing essential features such as template revocability and secure up dates. Through these directions, we aim to bridge the gap b et ween theoretical cryptographic primitives and a scalable priv acy-preserving biometric identification solution. Priv acy-Preserving Iris Recognition: Performance Challenges and Outlo ok 17 References 1. Al Bada wi, A., Bates, J., Bergamasc hi, F., et al.: OpenFHE: Open-source fully homomorphic encryption library . In: Pr o c e e dings of the 10th W orkshop on Encrypte d Computing & Applie d Homomorphic Crypto gr aphy (W AHC) . pp. 53–63 (2022) 2. Ammour, B., Boub c hir, L., Bouden, T., Ramdani, M.: F ace–iris m ultimo dal bio- metric identification system. Electr onics 9 (1), 85 (2020) 3. Bassit, A., Hahn, F., V eldh uis, R., Peter, A.: Hybrid biometric template protection: Resolving the agony of choice b et ween blo om filters and homomorphic encryption. IET Biometrics 11 (5), 430–444 (2022) 4. Blan ton, M., Gasti, P .: Secure and efficient proto cols for iris and fingerprint iden ti- fication. In: Eur op e an Symp osium on R ese ar ch in Computer Se curity . pp. 190–209. Springer, Heidelb erg (2011) 5. Blan ton, M., Aliasgari, M.: Secure outsourced computation of iris matching. Journal of Computer Se curity 20 (2–3), 259–305 (2012) 6. Campana, G., Bédrune, J.-B.: Ev eryb ody be co ol, this is a robb ery! Breaking a FIPS 140-2 Level 3 HSM. In: Black Hat USA (2019) 7. CER T-EU: A Hardware Security Mo dule is found not immune to hacking. CER T- EU Thr e at Memo 190612-1 (2019) 8. CASIA-Iris-Thousand: Chinese A cademy of Sciences Institute of Automation. http://www.cbsr.ia.ac.cn/china/Iris%20Databases%20CH.asp (accessed August 5, 2025) 9. Chen, H., Laine, K., Pla yer, R.: Simple encrypted arithmetic library - SEAL v2.1. In: Financial Crypto gr aphy and Data Se curity . Springer, Cham (2017) 10. Damgård, I., Geisler, M., Krøigaard, M.: Homomorphic encryption and secure comparison. International Journal of Applie d Crypto gr aphy 1 (1), 22–31 (2008) 11. Daugman, J.: How iris recognition w orks. In: The Essential Guide to Image Pr o- c essing . pp. 715–739. Academic Press, Amsterdam (2009) 12. Daugman, J.: Collision av oidance on national and global scales: Understanding and using big biometric entrop y . Author e a Pr eprints (2021) 13. Ernst, J., Mitrokotsa, A.: A framework for UC secure priv acy preserving biometric authen tication using efficien t fun ctional encryption. In: International Confer enc e on Applie d Crypto gr aphy and Network Se curity (ACNS 2023) . pp. 167–196. Springer, Cham (2023) 14. Georgia T ec h and Purdue Universit y researchers: TEE.fail: Breaking trusted exe- cution environmen ts via DDR5 memory bus in terp osition. Security Rese ar ch R ep ort (2025) 15. Gupta, R., Sehgal, P .: A survey of attacks on iris biometric systems. International Journal of Biometrics 8 (2), 145–178 (2016) 16. Halevi, S., Shoup, V.: Algorithms in HElib. In: A dvanc es in Cryptolo gy–CR YPTO 2014 . pp. 554–571. Springer, Heidelberg (2014) 17. ISO/IEC JTC1 SC27 Security T echniques: ISO/IEC 24745:2011. Information tech- nology—Securit y tec hniques—Biometric information protection. 18. Karabat, C., Kiraz, M.S., Erdogan, H., Sav as, E.: THRIVE: Threshold homomor- phic encryption based secure and priv acy preserving biometric verification system. EURASIP Journal on Advanc es in Signal Pr o c essing 2015 , 71 (2015) 19. Kulk arni, R., Nambo odiri, A.: Secure Hamming distance based biometric authen- tication. In: Pr o c e e dings of the 2013 International Confer enc e on Biometrics (ICB) . pp. 1–6. IEEE, Madrid (2013) 18 C. Karakosta et al. 20. Morampudi, M.K., Prasad, M.V., Ra ju, U.S.N.: Priv acy-preserving iris authen- tication using fully homomorphic encryption. Multime dia T o ols and Applic ations 79 (27), 19215–19237 (2020) 21. Muñoz, A., Ríos, R., Román, R., Lóp ez, J.: A survey on the (in) securit y of trusted execution environmen ts. Computers & Se curity 129 , 103180 (2023) 22. Nilsson, A., et al.: A survey of published attacks on Intel SGX. arXiv pr eprint arXiv:2006.13598 (2020) 23. P atgiri, R., Nay ak, S., Muppalaneni, N.B.: Is bloom filter a bad choice for se- curit y and priv acy? In: 2021 International Confer enc e on Information Networking (ICOIN) . pp. 648–653. IEEE (2021) 24. Song, X., Chen, Z., Sun, D.: Iris ciphertext authentication system based on fully homomorphic encryption. Journal of Information Pr o c essing Systems 16 (3), 599– 611 (2020) 25. V an Bulck, J., Oswald, D., Marin, E., Aldoseri, A., Garcia, F.D., Piessens, F.: A tale of tw o w orlds: Assessing the vulnerability of enclav e shielding run times. In: Pr o- c e e dings of the 2019 ACM SIGSAC Confer enc e on Computer and Communic ations Se curity (CCS 2019) . pp. 1741–1758 (2019) 26. W alch, R., Kales, D.: MPC’s Role in Adv ancing W orld ID Priv acy F eatures. In: T ACEO Cor e (Octob er 16, 2024). [Online]. A v ailable: https://core.taceo.io/ articles/mpc- for- iris- code- uniqueness/ (accessed July 25, 2025) 27. V aultree: VENumML: Encrypted Mac hine Learning library that leverages V aultree’s VENumpy F ully Homomorphic Encryption library . GitHub rep ository , https://github.com/Vaultree/VENumML (accessed September 21, 2025) 28. W ang, W., Chen, G., Pan, X., Zhang, Y., Gunter, C.A.: Leaky cauldron on the dark land: Understanding memory side-c hannel hazards in SGX. arXiv pr eprint arXiv:1705.07289 (2017) 29. Blo emen, R., Gillespie, B., Kales, D., Sippl, P ., W alc h, R.: Large-scale MPC: Scaling priv ate iris code uniqueness chec ks to millions of users. arXiv pr eprint arXiv:2405.04463 (2024) 30. W orldcoin: open-iris. GitHub rep ository , https://github.com/worldcoin/open- iris (accessed August 5, 2025) 31. W orldcoin F oundation: W orldc oin Whitep ap er – A New Identity and Financial Net- work (July 2023). [Online]. A v ailable: https://whitepaper.world.org/ (accessed July 25, 2025) 32. Y ang, W., W ang, S., Cui, H., T ang, Z., Li, Y.: A review of homomorphic encryption for priv acy-preserving biometrics. Sensors 23 (7), 3566 (2023) 33. Y oung, M.R., Elliott, S.J., Tilton, C.J., Goldman, J.E.: Entrop y of fingerprints. International Journal of Scienc e, Engine ering and Computer T e chnolo gy 3 (2), 43 (2013) App endix A Supplemen tary Details and Figures This app endix provides detailed information on the exp erimental setup, a de- tailed breakdown of p erformance metrics at different op erational thresholds for the largest dataset, and supplementary p erformance figures for the smaller datasets. Priv acy-Preserving Iris Recognition: Performance Challenges and Outlo ok 19 A.1 Exp erimen tal Setup – Hardw are: All exp eriments were conducted on a single GNU/Linux system GPU mac hine equipp ed with an NVIDIA GeF orce GTX 1 080 graphics card and 32 GB of system memory . – Soft ware: The iris pro cessing pip eline, including segmentation and fea- ture enco ding, utilized the Op en Iris library [30]. The FHE implementation w as built using V aultree’s venumML [27] library . All cryptographic parame- ters were configured to provide a 128-bit security level, ensuring protection against all kno wn classical and quantum computational attacks. – Dataset: The ev aluation was conducted using subsets of the publicly av ail- able CASIA-Iris-Thousand dataset, whic h contains 20 000 iris images from 1 000 sub jects (10 images for each eye of 1 000 sub jects) [8]. The 640 × 480 pixel, 8-bit grayscale JPEG images feature clear, well-cen tered iris patterns, making them ideal for biometric iden tification. W e remov ed the images with glasses, as they affect the image quality , and created four template databases of v arying sizes to assess scalability and performance: 1. CASIA 50 : A database of 50 sub jects con taining 755 iris templates. 2. CASIA 100 : A database of 100 sub jects containing 1 487 iris templates. 3. CASIA 500 : A database of 500 sub jects containing 6 777 iris templates. 4. CASIA 1K : A database of 1 000 sub jects con taining 14 191 iris tem- plates. All p ossible intra-class (genuine) and in ter-class (imposter) comparisons w ere p erformed on these databases to generate Hamming distance (HD) distributions and ev aluate the system’s discriminativ e pow er. F or the FHE ev aluation, w e p erformed 1–1 comparisons on represen tativ e gen uine and imposter pairs to precisely measure computational o verhead and accuracy . A.2 Supplemen tary Figures (a) Hamming Distance Distribution (b) ROC Curve ( E E R = 0 . 27% , AU C = 0 . 9999 ) Fig. 5: Hamming distance distributions and R OC curve for CASIA 50 . 20 C. Karakosta et al. (a) Hamming Distance Distribution (b) ROC Curve ( E E R = 0 . 16% , AU C = 0 . 9999 ) Fig. 6: Hamming distance distributions and R OC curve CASIA 100 . (a) Hamming Distance Distribution (b) ROC Curve ( E E R = 0 . 16% , AU C = 0 . 9999 ) Fig. 7: Hamming distance distributions and R OC curve CASIA 500 . Fig. 8: Visualisation of the full pro cessing pip eline for an imp oster pair compar- ison, resulting in a non-matc h Hamming distance of 0.4703.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment