Impact of Differentials in SIMON32 Algorithm for Lightweight Security of Internet of Things
SIMON and SPECK were among the first efficient encryption algorithms introduced for resource-constrained applications. SIMON is suitable for Internet of Things (IoT) devices and has rapidly attracted the attention of the research community to underst…
Authors: Jonathan Cook, Sabih ur Rehman, M. Arif Khan
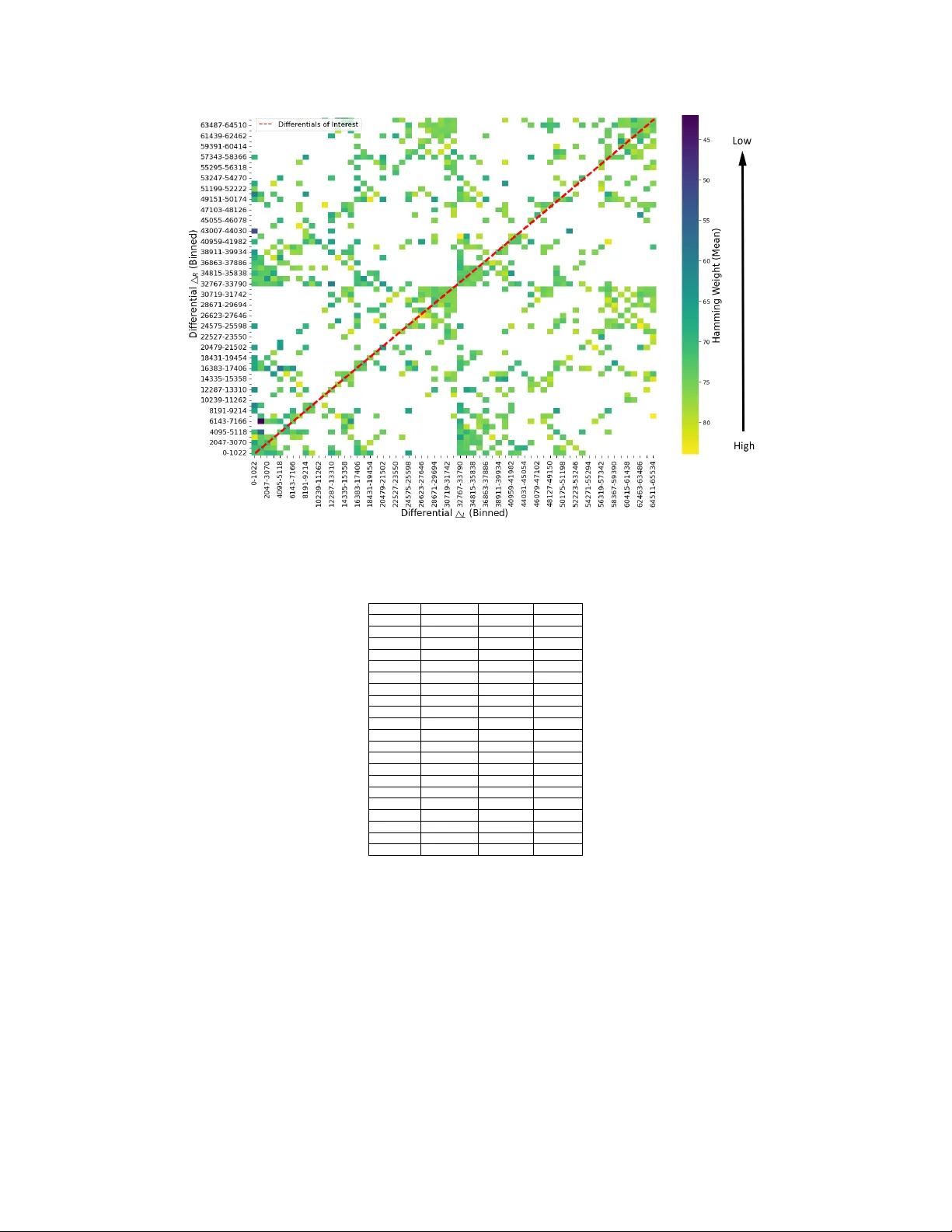
I M P A C T O F D I FF E R E N T I A L S I N S I M O N 32 A L G O R I T H M F O R L I G H T W E I G H T S E C U R I T Y O F I N T E R N E T O F T H I N G S P R E P R I N T V E R S I O N Jonathan Cook*, Sabih ur Rehman* and M. Arif Khan* *School of Computing, Mathematics and Engineering, Charles Sturt Univ ersity , Australia A B S T R AC T SIMON and SPECK were among the first ef ficient encryption algorithms introduced for resource- constrained applications. SIMON is suitable for Internet of Things (IoT) devices and has rapidly attracted the attention of the research community to understand its structure and analyse its security . T o analyse the security of an encryption algorithm, researchers often emplo y cryptanalysis techniques. Howe ver , cryptanalysis is a resource and time-intensive task. T o improv e cryptanalysis efficiency , state-of-the-art research has proposed implementing heuristic search and sampling methods. Despite recent advances, the cryptanalysis of the SIMON cypher remains inefficient. Contributing factors are the large size of the difference distribution tables utilised in cryptanalysis and the scarcity of differentials with a high transition probability . T o address these limitations, we introduce an analysis of differential properties of the SIMON 32 cypher , revealing dif ferential characteristics that pave the way for future ef ficiency enhancements. Our analysis has further increased the number of targeted rounds by identifying high probability differentials within a partial difference distribution table of the SIMON cypher , exceeding existing state-of-the-art benchmarks. The code designed for this work is av ailable at https://github.com/johncook1979/simon32-analysis. K eywords SIMON 32 , Differential, Security Analysis, Internet of Things, Lightweight Security 1 Introduction Internet of Things (IoT) devices have traditionally exhibited limited processing capacity , hindering their ability to ex ecute complex cyphers [ 1 ]. Addressing the security gaps of unencrypted IoT data, in 2013 , the US National Security Agency (NSA) introduced SIMON, a lightweight c ypher suitable for hardw are-constrained applications, such as IoT [ 2 ]. Since its introduction, the International Organisation for Standardisation (ISO) has provided support for block/key sizes greater than 64 / 96 under ISO/IEC 29167-21:2018 [ 3 ]. The key to SIMON’ s strength lies in its series of transformation rounds that create confusion and dif fusion to encrypt data [ 4 ]. Howe ver , while SIMON is a rob ust algorithm, it is crucial to analyse its security to ensure that the data encrypted by the algorithm remains secure. The imminent arriv al of Sixth Generation (6G) networks necessitates an ur gent need to ensure SIMON remains rob ust, as potential vulnerabilities can lead to compromised data and insecure de vices. Howe ver , analysing and identifying vulnerabilities of SIMON 32 requires using various cryptanalysis techniques without resorting to brute force methods [ 5 , 6 ]. While Differential Cryptanalysis (DC) has demonstrated ef fectiv eness against block algorithms, such as SIMON [ 6 ], cryptanalysis itself remains inefficient. Many DC methods employ a Dif ference Distribution T able (DDT) [ 7 , 8 , 9 ], which is a large matrix that allows researchers to analyse how differences to an input propagate to differences in the output. Ho we ver , the size of DDTs can become vast [ 10 ]. The DDT for a n-bit S-box, which normally operates on a 4-bit or 8-bit word, will comprise a matrix of 2 n × 2 n [ 10 ]. An S-box DDT for a small state size is relati vely simple. Howe ver , addition, rotate XOR (ARX) cyphers such as SIMON, lev erage modular addition to introduce non-linearity [ 10 ]. Therefore, constructing a DDT for n-bit words is infeasible as it will require 2 3 n × 4 bytes of memory for a standard 32 -bit word size [ 10 ]. T o address this limitation, the authors of [ 10 ] proposed a partial DDT (pDDT) to reduce the search space. Howe ver , the distribution of significant dif ferentials in a pDDT is sparse, which reduces the efficiency of cryptanalysis. The three leading solutions to enhance efficienc y are employing quantum computing [ 11 ], which is not yet commercially av ailable to consumers, applying heuristic search [ 12 ], and reducing the search space through sampling [ 13 ]. While A pr eprint - Mar ch 20, 2026 Figure 1: Our methodology the heuristic may not produce optimal solutions to all problems, the answer will often be sufficient for the problem presented [ 14 ]. This ability to sufficiently solve complex problems establishes it as a viable solution for the cryptanalysis of lightweight encryption algorithms such as SIMON. Ho we ver , as briefly mentioned abo ve and explained in deeper detail in Section 2.1, pDDTs contain numerous differentials with v ery few e xhibiting a high probability of differential transition, highlighting a limitation of heuristics. For ef fectiv e cryptanalysis, it is crucial to identify high-probability differential transitions. Ho wev er , with a limited number of high-probability differential transitions in a pDDT , it is unlikely to discov er them by chance. While the authors in [ 13 ] demonstrated that reducing the search space decreases the number of differentials and time required for cryptanalysis, heuristic methods remain largely inef fectiv e. Heuristic techniques that rely on simple random selection may choose differentials that produce poor results, necessitating the selection of an alternativ e path, which increases time and computational resources. While existing work on SIMON 32 presents substantial benchmarking through various techniques, many are inhibited by the size of the DDT and the method of optimal path self-discovery [ 10 , 12 , 13 ]. This paper seeks to address these limitations by identifying optimal differential characteristics and patterns to f acilitate efficient cryptanalysis of the SIMON c ypher through an analytical in vestigation of dif ferential characteristics. Through a rigorous analysis of SIMON 32 differentials, we discover and utilise distinct characteristics to enhance cryptanalysis efficienc y . W e expand on our contribution by generating the dif ferential trails on the significant differen- tials, demonstrating an increase in the number of rounds tar geted with improv ed probability ov er existing techniques. Although ISO standards pertain to block/key sizes of 64 / 96 and greater , SIMON 16 / 32 provides an experimental testbed to explore preliminary results which can be later applied to larger v ariants of SIMON. As stated by [12], ideal cyphers follow the random distribution of cyphertext and plaintext pairs with a probability of 2 2 n , where 2 n is the cyphers’ size. If the differential path probability is greater than 2 2 n , the differential path can be used to distinguish the cypher from a random permutation. Previous studies reduced the number of rounds to achie ve probabilities relati ve to the block size of the cypher . Increases in the number of rounds tar geted without reducing the probability indicate improv ement in the cryptanalysis technique. T o understand SIMON 32 differentials, this in vestigation takes a deep di ve to identify differential characteristics to increase the number of tar geted rounds efficiently . As this is an analytical study , our analysis is not negati vely influenced by heuristic methods or seeks to be efficient. 2 Methodology All experiments are performed on a standard retail W indo ws 10 Enterprise edition 64 bit laptop utilising Jupyter Note- book [ 15 ]. The methodology is summarised in Figure 1, which describes the processes employed in our in vestigation. W e be gin at step A by creating a pDDT . Differentials are sorted at step B based on their calculated probability . At C , we conduct preliminary experiments and compare Hamming W eight (HW) distributions. At step D , we extract the promising dif ferentials from the preliminary experiments for further analysis and ev aluate their differential trails and cumulativ e probability ov er 20 rounds (Step E ). 2.1 Create pDDT A DDT for the SIMON 32 cypher is infeasibly large and time-consuming to produce. T o address the large size of DDTs, [ 10 ] proposed the creation of a partial DDT (pDDT) where only differences above a Differential Probability (DP) threshold ( P thr ) are recorded. The pDDT can be expressed as: ( a, b, c ) ∈ pD D T ⇔ D P ( a, b → c ) ≥ P thr . (1) The efficient computation of the pDDT can be e xecuted with the follo wing proposition: 2 A pr eprint - Mar ch 20, 2026 Proposition 1 The DP of the XOR operation combined with addition modulo 2 n decr eases as the wor d size of the differ ences a , b , c incr eases, such that: p n ≤ · · · ≤ p k ≤ p k − 1 ≤ · · · ≤ p 1 ≤ p 0 , (2) where p k denotes the DP from a k , b k progressing to c k , where n ≥ k ≥ 1 , p 0 = 1 and x k denotes the k Least-Significant Bit (LSB) difference x , such that x k = x [ k − 1 : 0] . The algorithm produces the pDDT commencing at the LSB position k = 0 . It then allocates the values to a k , b k and c k recursiv ely [ 10 ]. At each bit position k , for n > k ≥ 0 , the likelihood of a ( k + 1) th bit differential with a partial structure is e valuated to establish whether it exceeds the specified threshold. If true, the algorithm proceeds to the next bit. If not, it returns and assigns different values to a k , b k and c k . k is initialised with a value of 0 , such that a 0 = b 0 = c 0 = Φ . The algorithm is repeated until k = n , at which point it is terminated and the XOR differential ( a k , b k → c k ) is added to the pDDT [ 10 ]. W e define our threshold as 0 . 1 in Algorithm 1, which produces 3951388 pDDT elements. Reducing the threshold increases the number of pDDT elements and generation time. Algorithm 1 : Compute pDDT Input : n, p thr , k, p k , a k , b k , c k Output : pDDT D:(a, b, c) ∈ D: D P ( a, b → c ) ≥ p thr 1: function C A L C P D D T ( n, p thr , k , p k , a k , b k , c k ) 2: if n == k then 3: Add ( a, b, c ) ← ( a k , b k , c k ) to D 4: end if 5: retur n 6: for x,y ,z ∈ 0 , 1 do 7: a k + 1 ← x | a k , b k + 1 ← y | b k , c k + 1 ← z | c k 8: p k + 1 = D P ( a k + 1 , b k + 1 → c k + 1) 9: if p k + 1 ≥ p thr then 10: CALCPDDT ( n, p thr , k + 1 , p k + 1 , a k + 1 , b k + 1 , c k + 1 ) 11: end if 12: end for 13: retur n 14: end function 2.2 Sorting differentials T o determine if the differentials are statistically significant, they are sorted into two sets of data. The sorting of differentials D , representing the set of differentials, is presented in Algorithm 2 and is e xpressed as: D = { d 1 , d 2 , . . . d n } , (3) where d represents each differential up to n differentials. Each d n has an associated probability used to sort significant differentials ( D sig ), where the DP is equal to or greater than 0 . 5 , and non-significant differentials D non − sig as: D sig = d n ∈ D | P d n ≥ P thr , (4) D non − sig = d n ∈ D | P d n < P thr , (5) where P ( d n ) is the dif ferential probability and P thr is the predefined probability threshold for sorting. While sorting creates two subsets of data, the number of insignificant differentials is quantifiably higher . Therefore, it is infeasible to test each non-significant differential as it will consume significant resources. Therefore, we take a quota-based sample of 10 % of the total insignificant output differentials for analysis [ 13 ]. The number of samples to take from the population of n is given as: n = max 1 , l x 100 × N h m , (6) where x is the sample size of the stratum, and N h is the total number of observations of the h th type in the population, with at least one of each h th discrete value, and ⌈ . ⌉ represents the ceiling function. 3 A pr eprint - Mar ch 20, 2026 Algorithm 2 : Sort differentials based on probability Input : pDDT Output : Significant differentials list as sigDif Output : Non-significant differentials list as nonSigDif 1: Initialise array of significant dif ferentials as sigDif 2: Initialise array of non-significant dif ferentials as nonSigDif 3: f or each differential in PDDT do 4: if differential ≥ 0 . 5 then 5: Append to sigDif 6: else 7: Append to nonSigDif 8: end if 9: end for Algorithm 3 : Execute experiments Input : differential , num_trials Output : Array of hamming weights as results 1: function E X E C U T E E X P E R I M E N T 2: Initialise mask = 2 16 − 1 3: Initialise alpha , beta , gamma = 1, 8, 2 4: Initialise SIMON_ROUNDS = 10 5: Initialise empty array results = [] 6: for each trial from 1 to num_trials do 7: Calculate differential hamming weight 8: Append Weight to results 9: end for 10: retur n results 11: end function 2.3 Compare hamming weight distribution Follo wing sorting, we perform a preliminary analysis of HW distribution. W e take a sample of non-significant dif ferentials, extracted using Equation 6, and significant differentials for analysis. The HW of each set of differentials is calculated employing Algorithm 3. The distributions of HWs are analysed and compared. Differentials that produce a zero HW indicates that the input pair did not result in any observ able output difference. Algorithm 3 can be called any number of times to calculate differential HWs. 2.4 Extract promising differentials Significant differentials that produce a near zero HW are extracted for further analysis. This step in volves e xtracting the most promising differentials from the set of significant differentials. The extraction of promising dif ferentials D prom is defined as: D prom = d n ∈ D sig | H W d n = 0 , (7) where H W d n is the differential HW . 2.5 Generate differential trails Once the most promising differentials hav e been identified, the next stage is to test and generate differential trails. This will yield the HW at each round and the DC probability . The round simulation is presented in Algorithm 4 and is called for each of the promising dif ferentials. Algorithm 4 calls the simulate rounds function presented in Algorithm 5. The number of SIMON 32 rounds is passed as a function attribute. Algorithm 5 returns each round △ L , △ R and logarithmic probability as log 2 P . Algorithm 4 returns the results with the sum of the round r probability for the differential as P r P r . 4 A pr eprint - Mar ch 20, 2026 Algorithm 4 : Generate differential trails of promising dif ferentials Input : Significant Differentials as sigDif Output : Differential trails 1: SIMON_R OUNDS = 18 2: f or diff in sigDif do 3: differentials, probabilities = S I M R O U N D S ( diff, SIMON_ROUNDS ) 4: for Index, dif ferential, probability in (differentials, probabilities) do 5: △ L , △ R , △ out = differential 6: retur n △ L , △ R , probability 7: end for 8: end for Algorithm 5 : Simulate rounds Input : differential, SIMON_ROUNDS Output : Array of differentials as differentials Output : Array of probabilities as probabilities 1: function S I M R O U N D S 2: Initialise empty array differentials = [] 3: Initialise empty array probabilities = [] 4: for each round in SIMON_ROUNDS do 5: △ L , △ R , △ out = Calculated SIMON round 6: HW = Calculate HW 7: probability = 2**(-HW) 8: Append probability to probabilities 9: Append △ L , △ R , △ out to differentials 10: end for 11: retur n differentials 12: retur n probabilities 13: end function 3 Results and Analysis This section presents the results of our experiments to identify significant differentials for the cryptanalysis of the SIMON 32 cypher . W e begin by analysing the distribution of differentials between two data subsets to identify potential high-probability differentials. W e then extract these dif ferentials and examine their trails and associated probabilities. Finally , the results are sorted to highlight the differentials with the most promising probability transitions. As illustrated in Figures 2 and 3, the significant and non-significant differentials produce a similar distribution of HWs. Howe ver , as evidenced in Figure 2, some significant differentials produced a HW near 0 while non-significant differentials did not. Additionally , an observation of the distribution of both plots indicates a binomial distrib ution of HWs [ 16 ]. Howe ver , both figures are slightly left-ske wed, indicating a median higher HW . Further in vestigations on finding the exact distrib ution of the data is the future work of this paper . A HW of 0 indicates that there are transitions within some dif ferentials where there is no difference to the output. As shown in Figure 4, significant differentials indicate the presence of differentials that produce a HW near 0 , while the non-significant differentials do not. Although outliers in the non-significant differentials are present, the y’ re not near 0 . W e can examine the HW distribution relati ve to input dif ferentials in greater detail using a heatmap, as presented in Figure 5. W e grouped the differentials into smaller bins by dividing the 16 bit space into 64 equal parts. Each cell represents the mean HW over 10 simulated SIMON 32 rounds of all differentials within the range. An interesting observ ation is the linear con vergence of differentials along the 45 degree gradient highlighted by the red dashed line. As shown, po wers of two differentials reside within the bins along the same gradient. Although these bins do not produce the lowest mean HW , influences of other differentials within the bin alter the mean HW . As highlighted by the colour intensity , most differentials produce a HW between 65 and 75 , with very fe w producing low HWs. Indeed, from the 4096 cells, only 2 produce a significantly low mean HW . Interestingly , cells that align with power of tw o differentials do not produce the deepest colour . This suggests the mean HW of differential transitions within the bin is ske wed. W e can scrutinise these results by extracting dif ferentials within one of the aligned bins and ev aluating the sum of their logarithmic probability over 10 rounds. W e take the conv ergence of the cells within the centre of the heatmap, aligning with the power of two differential of 32768 . While the mean HW suggests a value of approximately 70 , calling Algorithm 5 on the differentials 32768 within the bin produces a summed logarithmic 5 A pr eprint - Mar ch 20, 2026 Figure 2: Frequency distribution of significant dif ferentials probability of 2 − 17 , far belo w the mean results within the bin. This indicates that the mean value is ske wed by non-significant differentials. Furthermore, although several cells produce a light colour , the bins are largely de void of power of tw o differentials, with fe wer non-significant differentials to sk ew the mean result. Finally , as observed by the colourbar legend, the lowest mean HW is 30 , higher than the powers of two differentials tested abo ve. This indicates an abundance of non-significant dif ferentials influencing results. Next, we apply statistical testing to v alidate our observations in Figures 2, 3 and 4. W e employ the p-value which is a statistical method used in hypothesis testing to determine the significance of the result [ 17 ]. In addition to the p-value, we employ the t-statistic commonly used in t-tests comparing the means of two groups. W e first analyse the significant and non-significant dif ferentials to ev aluate the p-value. For our analysis, the p-value returned 0 . 0 , indicating a v ery low probability of the observ ed differences occurring by chance. T o validate the results, the t-statistic returned a v alue of − 65 . 09 , suggesting that the mean between the tw o is large. This validates the p-v alue, indicating a high degree of statistically significant differences between the tw o subsets of differentials. Next, we extract 31 promising differentials from the full set of significant differentials for further inv estigation. An observ ation of the promising differentials rev eals that all output differentials are a value of 0 , and most input differentials are a power of two. As presented in T able 1, the best dif ferential trail identified from the promising differentials has a probability of 2 − 32 from a total of 20 simulated SIMON 32 rounds, exceeding previous best results as presented in T able 2. While SIMON is predominantly a bitwise encryption algorithm represented in binary form, analysis of differential propagation is commonly undertak en using hexadecimal format. As highlighted in Section 1, attaining a dif ferential path probability equal to or greater than the size of the cypher distinguishes the path from random permutation. Previous in vestigations achie ved similar results ov er fewer rounds. Indeed, both [ 13 ] and [ 12 ] acknowledged that increasing the number of rounds significantly hampered their heuristic efficienc y . Examining the results of this analysis highlights se veral interesting cypher characteristics. The prev alence of power of two differentials and the limited bitwise movements and permutations of the cypher rounds highlight potential future av enues of in vestigation. The features identified can be utilised to enhance differential cryptanalysis ef ficiency . Although the results presented in this work open une xplored av enues for the ef fectiv e cryptanalysis of the SIMON 32 6 A pr eprint - Mar ch 20, 2026 Figure 3: Frequency distribution of non-significant dif ferentials Figure 4: Boxplot of differential Hamming W eights 7 A pr eprint - Mar ch 20, 2026 Figure 5: Heat map of mean best hamming weight grouped by input differentials T able 1: Best significant differential trail Round ∆ L ∆ R log 2 P 0 0 xa 000 0 x 8000 − 1 1 0 xa 800 0 xa 000 − 1 2 0 x 8 a 00 0 xa 800 − 2 3 0 x 8 a 80 0 x 8 a 00 − 1 4 0 xa 8 a 0 0 x 8 a 80 − 3 5 0 xa 0 a 8 0 xa 8 a 0 − 2 6 0 x 808 a 0 xa 0 a 8 − 3 7 0 x 8 a 0 x 808 a − 1 8 0 xa 8 0 x 8 a − 2 9 0 xa 0 0 xa 8 − 1 10 0 x 80 0 xa 0 − 1 11 0 x 80 0 x 80 0 12 0 xa 0 0 x 80 − 1 13 0 xa 8 0 xa 0 − 1 14 0 x 8 a 0 xa 8 − 2 15 0 x 808 a 0 x 8 a − 1 16 0 xa 0 a 8 0 x 808 a − 3 17 0 xa 8 a 0 0 xa 0 a 8 − 2 18 0 x 8 a 80 0 xa 8 a 0 − 3 19 0 x 8 a 00 0 x 8 a 80 − 1 P r P r − 32 cypher , it is not an exhaustiv e inv estigation. Nevertheless, the in vestigation identifies differentials that exceed the number of rounds while maintaining a low probability . 4 Conclusion Current differential cryptanalysis techniques targeting the SIMON 32 cypher , such as heuristics and sampling, are inefficient large search space and a high distrib ution of lo w-probability differentials. T o address e xisting limitations, this paper presented a technique based on an analytical inv estigation of dif ferentials to identify optimal paths from a partial difference distrib ution table. From these optimal differentials, we hav e identified specific characteristics, such as power of two dif ferentials, which can be exploited to narrow the search space and improve dif ferential cryptanalysis efficienc y . While not all identified differentials produce desirable optimal results, the best optimal results in this paper exceed the best results in previous w orks. Although this in vestigation is focused on the SIMON 32 variant as a proof of 8 A pr eprint - Mar ch 20, 2026 T able 2: Summary of differential paths for SIMON. Cypher Distingisher rounds Probability Y ear Reference SIMON 32 13 2 − 29 . 69 2009 [18] 13 2 − 30 . 2 2015 [19] 14 2 − 30 . 81 2015 [20] 11 2 − 30 . 0 2017 [21] 15 2 − 32 . 0 2023 [12] 9 2 − 30 . 82 2024 [22] 17 2 − 68 . 83 2024 [22] 15 2 − 32 . 0 2024 [13] 20 2 − 32 . 0 2025 Our work concept, the analytical in vestigation presented in this paper can be scaled to other variants of the SIMON f amily and SIMON-like cyphers. Furthermore, future studies can lev erage contemporary disciplines such as machine learning and knowledge graphs to exploit dif ferential characteristics, impro ving cryptanalysis efficienc y and increasing the number of tar geted rounds. Finally , in vestigating po wer of two properties in the cryptanalysis of the SIMON c ypher can yield further ef ficiency enhancements. References [1] Jonathan Cook, Sabih Ur Rehman, and M Arif Khan. Security and Pri vac y for Low Po wer IoT Devices on 5G and Beyond Networks: Challenges and Future Directions. IEEE Access , 11:39295–39317, 2023. [2] Ray Beaulieu, Douglas Shors, Jason Smith, Stefan T reatman-Clark, Bryan W eeks, and Louis W ingers. The SIMON and SPECK lightweight block ciphers. In Pr oceedings of the 52nd Annual Design A utomation Conference , pages 1–6, 2015. [3] International Organization for Standardization. ISO/IEC 29167-21:2018(en) Information technology — Automatic identification and data capture techniques — Part 21: Crypto suite SIMON security services for air interface communications. https://www.iso.org/obp/ui/es/#iso:std:iso- iec:29167:- 21:ed- 1:v1:en:sec: 3.1.13 , 2018. [4] Naman Singhal, Priyanka Joshi, and Bodhisatwa Mazumdar . Entropy Reduction Model for Pinpointing Dif ferential Fault Analysis on SIMON and SIMECK Ciphers. IEEE T ransactions on Computer -Aided Design of Inte grated Cir cuits and Systems , 40(6):1090–1101, 2021. [5] Christophe De Canniere, Alex Biryukov , and Bart Preneel. An introduction to Block Cipher Cryptanalysis. Pr oceedings of the IEEE , 94(2):346–356, 2006. [6] W illiam Easttom and William Easttom. Cryptanalysis. Modern Cryptography: Applied Mathematics for Encryption and Information Security , pages 357–372, 2021. [7] Eli Biham. On Matsui’ s Linear Cryptanalysis. In Advances in Cryptology—EUR OCRYPT’94: W orkshop on the Theory and Application of Cryptogr aphic T ec hniques P erugia, Italy , May 9–12, 1994 Pr oceedings 13 , pages 341–355. Springer , 1995. [8] T im Beyne and V incent Rijmen. Differential Cryptanalysis in the Fixed-K ey Model. In Pr oceedings of Advances in Cryptology – CR YPTO 2022 , pages 687–716. Springer , 2022. [9] Howard M He ys. A T utorial on Linear and Differential Cryptanalysis. Cryptologia , 26(3):189–221, 2002. [10] Alex Biryuko v and V esselin V elichkov . Automatic Search for Differential T rails in ARX Ciphers. In Pr oceedings of The Cryptographer’ s T rack at the RSA Confer ence: T opics in Cryptolo gy–CT -RSA , pages 227–250. Springer , 2014. [11] Ravi Anand, Arpita Maitra, and Sourav Mukhopadh yay . Evaluation of Quantum Cryptanalysis on SPECK. In Pr oceedings of 21st International Conference on Cryptology in India, Pr ogr ess in Cryptology–INDOCRYPT 2020 , pages 395–413. Springer , 2020. [12] Ashutosh Dhar Dwiv edi and Gautam Sriv astava. Security analysis of lightweight IoT encryption algorithms: SIMON and SIMECK. Internet of Things , page 100677, 2023. [13] Jonathan Cook, Sabih Ur Rehman, and M Arif Khan. Lightweight Cryptanalysis of IoT Encryption Algorithms: Is Quota Sampling the Answer? IEEE Access , 2024. 9 A pr eprint - Mar ch 20, 2026 [14] Gerd Gigerenzer and W olfgang Gaissmaier . Heuristic Decision Making. Annual Review of Psycholo gy , 62:451– 482, 2011. [15] João Felipe Pimentel, Leonardo Murta, V anessa Braganholo, and Juliana Freire. Understanding and improving the quality and reproducibility of Jupyter notebooks. Empirical Softwar e Engineering , 26(4):2, article no. 65, 2021. [16] Uwe W ehrspohn and Dietmar Ernst. When Do I T ake Whic h Distribution?: A Statistical Basis for Entrepr eneurial Applications . Springer Nature, 2022. [17] Andrew A Ja wlik. Statistics fr om A to Z: Confusing Concepts Clarified . John W iley & Sons, 2016. [18] T ristan Cazena ve. Nested Monte-Carlo Search. In Pr oceedinsg of 21st International Joint Confer ence on Artificial Intelligence , v olume 9, pages 456–461, 2009. [19] Farzaneh Abed, Eik List, Stefan Lucks, and Jak ob W enzel. Differential Cryptanalysis of Round-Reduced Simon and Speck. In Pr oceedings of 21st International W orkshop F ast Softwar e Encryption (FSE) , pages 525–545. Springer , 2015. [20] Stefan Kölbl, Gregor Leander , and T yge Tiessen. Observations on the SIMON Block Cipher Family. In Pr occedings of the 35th Annual Cryptology Conference: Advances in Cryptology–CRYPT O 2015 , pages 161–185. Springer , 2015. [21] Zhengbin Liu, Y ongqiang Li, and Mingsheng W ang. Optimal Differential T rails in SIMON-like Ciphers. Cryptol- ogy ePrint Ar chive , 2017. [22] Ke xin Qiao, Zehan W u, Junjie Cheng, Changhai Ou, An W ang, and Liehuang Zhu. Bit-Wise Mixture Dif ferential Cryptanalysis and Its Application to SIMON. IEEE Internet of Things Journal , 11(13):23398–23409, 2024. 10
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment