Efficient Joint Resource Allocation for Wireless Powered ISAC with Target Localization
Wireless powered integrated sensing and communication (ISAC) faces a fundamental tradeoff between energy supply, communication throughput, and sensing accuracy. This paper investigates a wireless powered ISAC system with target localization requireme…
Authors: Boyao Li, Qinwei He, Boao Zhang
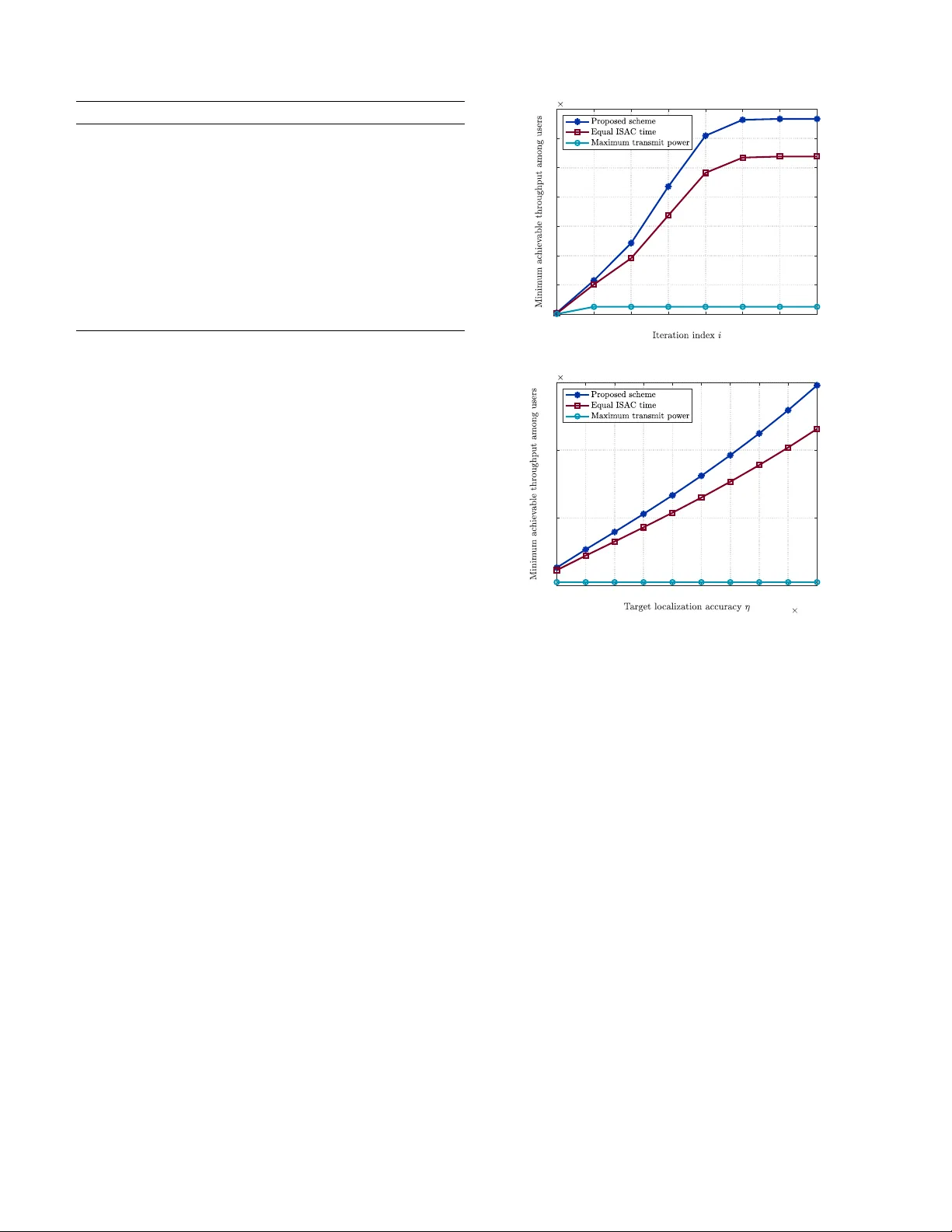
Ef ficient Joint Resource Allocation for W ireless Po wered ISA C with T ar get Localization Boyao Li † , Qinwei He ‡ , Boao Zhang † , Xiaopeng Y uan †∗ and Anke Schmeink † † IND A Chair, R WTH Aachen Univ ersity , Germany , Email: l i | y uan | schmeink @inda.rwth-aachen.de ‡ Global Energy Interconnection Research Institute Europe GmbH, Germany , Email: q inw ei.he @geiri.eu Abstract —Integrated sensing and communication (ISA C) en- ables 6G networks to share radio r esources for sensing and data transmission. F or energy-limited ISA C systems, wireless power transfer (WPT) can be integrated as a power supply , which also introduces tradeoffs among harvested energy , com- munication throughput, and sensing accuracy . Motivated by this, we study a wireless powered multi-user ISAC system for multi-target localization, where a base station (BS) broadcasts a WPT signal for energy harvesting and users then transmit data with the harv ested energy to the BS sequentially . Meanwhile, both the WPT signal and the users’ data signals are exploited for target localization at the BS. By imposing Cramér-Rao bound (CRB) constraints to guarantee localization accuracy , we formulate a minimum user throughput maximization problem that jointly optimizes the WPT duration, per -user transmission durations, and user transmit powers. T o address the variable coupling and inherent noncon vexity of the problem, we derive a mor e tractable r eformulation via variable substitutions and logarithmic objective transf ormations. Since the CRB constraints remain noncon vex, we further develop a successive conv ex ap- proximation (SCA)-based iterative algorithm and finally obtain an efficient suboptimal solution. Numerical r esults demonstrate the algorithm con vergence and significant performance gains of the proposed scheme over benchmark schemes, highlighting the importance of joint resource allocation design for wireless powered ISA C systems. Index T erms —Integrated sensing and communication (ISA C), wireless power transfer (WPT), target localization, Cramér -Rao bound (CRB), efficient r esource allocation. I . I N T R O D U C T I O N Integrated sensing and communication (ISAC) has emerged as a key pillar of 6G wireless networks, enabling high-quality wireless connectivity and accurate sensing capability within a unified infrastructure [1]. By sharing spectrum and hardware, ISA C is expected to support di verse applications such as smart home, human-computer interaction, and vehicle-to-e verything (V2X) [2]. This tight integration, howe ver , also introduces tradeoffs between sensing and communication due to shared limited resources. T o navigate these tradeoffs, extensiv e research ef forts hav e been de voted to ISAC, e.g., in wa veform design [3], [4] and advanced multiple access schemes [5]. In accordance with The work was supported in part by BMFTR Germany in the projects 6G- RIC under Grant 16KISK028, 6GEM+ under Grant 16KIS2409K, and GEM- X under Grant 16KISS004K, and in part by the State Grid Corporation of China under Grant 5700-202358798A-3-9-HW . ∗ X. Y uan is the corresponding author. different sensing demands, various sensing tasks ha ve been studied, including detection, estimation, and recognition [6]. In particular, target localization, as a representative estimation task, is crucial for location-a ware services such as indoor navigation and tracking. This has spurred increasing interest in localization-oriented ISAC, e.g., in cooperativ e networks [7] and unmanned aerial vehicle (U A V)-assisted scenarios [8]. Despite its potential, ISA C deployment becomes challeng- ing in energy-limited scenarios. T o address this challenge, wireless power transfer (WPT), by harvesting energy from ambient or dedicated radio frequency (RF) signals, has be- come a natural solution to enable sustainable ISA C operation for batteryless devices [9], [10]. Under a finite time budget, extending the WPT phase increases the harvested energy , but inevitably reduces the av ailable time for the subsequent ISA C phase. T o optimize this tradeoff, ef ficient resource allocation is crucial to orchestrate the energy-communication-localization interplay in wireless powered ISAC systems. T o this end, se veral works hav e in vestigated resource allo- cation for wireless po wered ISAC. In [11], the authors jointly optimize power control as well as WPT and ISA C beamform- ing to improve sensing performance while guaranteeing the communication requirements. In addition, [12] inv estigates a U A V -enabled wireless powered ISA C system and jointly optimizes the filter and waveform design, time scheduling and uplink powers of users, and U A V trajectory . Howe ver , these designs do not explicitly consider the target localization as the sensing task. Their sensing objecti ves are characterized by nonspecific metrics such as signal-to-interference-plus-noise ratio (SINR), rather than localization-specific metrics such as Cramér-Rao bound (CRB) that directly quantifies localization accuracy . Moreover , they do not fully exploit the sensing opportunities from all phases and nodes, and thus cannot lever - age the sensing geometry required for accurate localization. Consequently , the potential gains from WPT -ISA C co-design and CRB-constrained resource allocation remain insufficiently explored. T o fill this gap, we study a wireless po wered multi-user ISA C system, where the base station (BS) first performs WPT to energize the users, and then users transmit data to the BS with the obtained energy , while both phases jointly contribute to the multi-target localization task guaranteed via CRB constraints. The main contributions of this paper are summarized as follo ws: ©2026 IEEE. Personal use of this material is permitted. Permission from IEEE must be obtained for all other uses, in any current or future media, including reprinting/republishing this material for advertising or promotional purposes, creating new collectiv e works, for resale or redistribution to servers or lists, or reuse of any copyrighted component of this work in other works. ... ... ... Fig. 1. Illustration of a wireless powered M -user ISAC system with N targets under a total time budget T max . • Localization-specific wireless power ed ISA C frame- work: W e propose a two-phase WPT -ISA C protocol for multi-target localization in energy-limited systems, where the localization geometry and opportunities are fully considered and exploited. Under this design, we formulate a max-min throughput problem by jointly opti- mizing the WPT duration, per-user transmission time and power , subject to energy causality and per-tar get CRB- based localization accuracy constraints. The formulation explicitly captures the tradeoffs among harvested energy , communication performance, and localization accuracy . • Efficient joint resour ce allocation: T o tackle the re- sulting nonconv ex time-power coupled problem with in- tricate CRB constraints, we dev elop an equiv alent refor- mulation via variable substitutions and logarithmic trans- formations, which remo ves the multiplicati ve coupling. After the reformulation, we construct con vex surrogates for the remaining noncon ve xity in CRB constraints and propose an efficient successive conv ex approximation (SCA)-based iterative algorithm to obtain a high-quality suboptimal solution. • Numerical inv estigation: Numerical results demonstrate fast conv ergence of the iterativ e algorithm and significant throughput gains of the proposed scheme ov er benchmark schemes, and provide insights into how resources can be jointly allocated to balance heterogeneous performance requirements in wireless powered ISAC systems. The rest of this paper is org anized as follows. In Section II, we introduce the system model and the CRB model, and formulate the optimization problem. Section III develops the proposed iterati ve algorithm. Numerical results are presented in Section IV , and conclusions are drawn in Section V . I I . P RO B L E M F O R M U L ATI O N A. System Model W e consider a wireless powered ISA C system consisting of M batteryless users, N passive targets, and a BS located at x 0 ∈ R 2 , as shown in Fig. 1. The position of user m ∈ M ≜ { 1 , . . . , M } is denoted by x m ∈ R 2 , while the reference position of target n ∈ N ≜ { 1 , . . . , N } is denoted by q n ∈ R 2 . The users aim to transmit data to the BS, while the BS is required to localize the passi ve tar gets based on the recei ved sensing signals. In the WPT phase, the BS broadcasts an energy-carrying signal with power p 0 ov er a duration t 0 , from which all users harvest energy for the subsequent ISA C phase. The harvested energy at user m is gi ven by E m ( t 0 ) = ζ m h m t 0 p 0 , ∀ m ∈ M , (1) where ζ m is the energy con version efficienc y of user m and h m denotes the channel gain from the BS to user m . After the WPT phase, the system enters an ISA C phase consisting of M slots. In the m -th slot, user m transmits an information-bearing wav eform with power p m ov er a duration t m , which simultaneously supports target localization and uplink communication. During the ISA C phase, while illuminating the targets for sensing, user m simultaneously transmits its data to the BS. In slot m , the signal-to-noise ratio (SNR) at the BS is γ m ( p m ) = p m h m σ 2 , ∀ m ∈ M . (2) The achiev able throughput of user m for a transmission duration t m is expressed as R m ( t m , p m ) = t m W log 2 (1 + γ m ( p m )) , ∀ m ∈ M . (3) The total transmission duration of the WPT phase and all ISA C slots is constrained by a total time budget T max , i.e., M X m =0 t m ≤ T max . (4) Since the transmission of batteryless user m is solely pow- ered by the harv ested ener gy E m ( t 0 ) , the following energy causality constraint must hold: t m p m ≤ E m ( t 0 ) , ∀ m ∈ M . (5) Furthermore, due to hardware limitations, the transmit po wer of each user is bounded by 0 < p m ≤ P max , ∀ m ∈ M . (6) B. CRB-Based Localization Model T o quantify the target localization accuracy , we adopt a CRB-based localization model. Both the WPT signal and the users’ ISA C signals illuminate all targets, which then backscatter the incident ener gy to ward the BS. The BS re- ceiv es the echo signals and processes them to estimate the target positions. Thus, each user provides a distinct bistatic sensing geometry , while the BS provides a monostatic geom- etry for localization. For each target n ∈ N , we characterize both the bistatic and monostatic sensing geometries. The bistatic round-trip distance in slot m is given by r m,n = ∥ x m − q n ∥ + ∥ x 0 − q n ∥ , ∀ m ∈ M , ∀ n ∈ N , (7) while the monostatic round-trip distance is r 0 ,n = 2 ∥ x 0 − q n ∥ , ∀ n ∈ N . (8) T aking the gradient of r m,n with respect to the reference target location q n yields ∇ q n r m,n = − x m − q n ∥ x m − q n ∥ − x 0 − q n ∥ x 0 − q n ∥ , m ∈ M , − 2 x 0 − q n ∥ x 0 − q n ∥ , m = 0 , ≜ X m,n Y m,n , ∀ m ∈ M ∪ { 0 } , ∀ n ∈ N . (9) Follo wing the classical CRB analysis for range-based target localization [13], [14], the obtained gradient terms in (9) are used to construct the Fisher information matrix (FIM) associated with target n ∈ N , which can be expressed as J n = M X m =0 p m K m,n X 2 m,n X m,n Y m,n X m,n Y m,n Y 2 m,n , (10) where the scaling factor K m,n is defined as K m,n = 8 π 2 W 2 h m,n σ 2 c 2 , ∀ m ∈ M ∪ { 0 } , ∀ n ∈ N . (11) Here, W denotes the effecti ve bandwidth, h m,n denotes the channel gain from transmitter m to tar get n , with m = 0 corresponding to the BS and m ∈ M corresponding to the users. Moreov er, σ 2 is the noise power at the BS and c is the speed of light. For notational con venience, the FIM associated with target n in (10) is re written in the compact form: J n = A n C n C n B n , ∀ n ∈ N , (12) where A n = M X m =0 p m K m,n X 2 m,n , B n = M X m =0 p m K m,n Y 2 m,n , C n = M X m =0 p m K m,n X m,n Y m,n . (13) Under non-degenerate localization geometry , the FIM is pos- itiv e definite, i.e., A n B n − C 2 n > 0 and the CRB matrix can be expressed as the inv erse of FIM: J − 1 n = 1 A n B n − C 2 n B n − C n − C n A n , ∀ n ∈ N . (14) The trace of the CRB matrix represents a lower bound for the target location estimation and is gi ven by tr( J − 1 n ) = A n + B n A n B n − C 2 n , ∀ n ∈ N . (15) Giv en a required localization accuracy threshold η > 0 , the following constraint must be satisfied: tr( J − 1 n ) ≤ η , ∀ n ∈ N . (16) T o maximize the communication performance while ensur- ing fairness among all users, the minimum achiev able through- put is adopted as the optimization objective. Accordingly , the ov erall optimization problem is formulated as ( P 1) : max t , p min m ∈M { R m ( t m , p m ) } s.t. t m > 0 , ∀ m ∈ M ∪ { 0 } , (17a) (4) , (5) , (6) , (16) , where t ≜ [ t 0 , t 1 , . . . , t M ] T ∈ R M +1 collects the transmit durations of the BS and all users. Problem ( P 1) is noncon vex since R m ( t m , p m ) is not jointly concav e in ( t m , p m ) and noncon vex constraints (5) and (16) in volv e multiplicativ e couplings among the optimization variables. As a result, problem ( P 1) cannot be directly solved using standard con vex optimization techniques. I I I . P R O P O S E D I T E R AT I V E S O L U T I O N This section dev elops an ef ficient iterative algorithm to solve ( P 1) . W e first reformulate ( P 1) via variable substitu- tions and logarithmic transformations, and then apply SCA to handle the remaining nonconv exity . A. Problem Reformulation T o handle the multiplicativ e coupling between t m and p m in constraints (5) and (16), we apply a logarithmic change of variables by replacing ( t m , p m ) with ( u m , v m ) as u m = log( t m ) , v m = log( p m ) , ∀ m ∈ M , (18) which guarantees t m > 0 and p m > 0 automatically . Under this substitution, the energy causality constraint (5) becomes u m + v m ≤ log( E m ( t 0 )) , ∀ m ∈ M , (19) which con verts the original product terms t m p m into a lin- ear term. Moreover , since E m ( t 0 ) in (1) is affine in t 0 , log( E m ( t 0 )) is concav e in t 0 , and thus constraint (19) is con vex. Also, with variable replacement, the throughput (3) transforms to e R m ( u m , v m ) = e u m W log 2 1 + h m σ 2 e v m , ∀ m ∈ M , (20) which is still not jointly concave in ( u m , v m ) . T o overcome this difficulty , we apply a logarithmic trans- formation to e R m ( u m , v m ) , inspired by a similar technique to that in our prior works [15], [16]. Since the logarithm is strictly increasing, maximizing e R m ( u m , v m ) is equiv alent to maximizing log e R m ( u m , v m ) , which can be expressed as log e R m ( u m , v m ) (21) = u m + log ( W ) + log log 2 1 + h m σ 2 e v m , ∀ m ∈ M . The first term is affine in u m and log( W ) is a constant, while the last term is concave in v m , as established in the following lemma. Lemma 1. F or any h m > 0 and σ 2 > 0 , the function f ( v m ) = log log 2 1 + h m σ 2 e v m (22) is strictly concave in v m ∈ R . Pr oof. T o prove the conca vity of f ( v m ) , we define k m = h m σ 2 > 0 and g ( v m ) = 1 + k m e v m > 1 . Using the identity log 2 g ( v m ) = log g ( v m ) log 2 , the function f ( v m ) becomes f ( v m ) = log (log g ( v m )) − log (log 2) . (23) The first deri vati ve of f ( v m ) is therefore f ′ ( v m ) = k m e v m g ( v m ) log g ( v m ) . (24) Differentiating once more yields f ′′ ( v m ) = k m e v m g ( v m ) log g ( v m ) − k m e v m (log g ( v m ) + 1) g ( v m ) 2 (log g ( v m )) 2 = k m e v m (log g ( v m ) − k m e v m ) g ( v m ) 2 (log g ( v m )) 2 , (25) Since g ( v m ) > 1 , using the well-kno wn inequality log( y ) < y − 1 , ∀ y > 1 , (26) we have log g ( v m ) < g ( v m ) − 1 = k m e v m . (27) Hence, the numerator of f ′′ ( v m ) is negati ve, while the denom- inator is positi ve, and therefore f ′′ ( v m ) < 0 for all v m ∈ R , which completes the proof. Consequently , log e R m ( u m , v m ) is jointly conca ve in ( u m , v m ) , as the sum of an affine function in u m and a concav e function in v m . Moreov er , the objective function min m ∈M { log e R m ( u m , v m ) } is concave as the pointwise min- imum of concav e functions. As for CRB constraint (16), since A n B n − C 2 n > 0 , the abov e inequality can be re written as A n + B n − η ( A n B n − C 2 n ) ≤ 0 , ∀ n ∈ N . (28) T o rev eal the algebraic structure of A n B n − C 2 n and its dependence on the power v ariables { p m } , for each n ∈ N , we define a m,n = p p m K m,n X m,n , b m,n = p p m K m,n Y m,n . W ith these definitions, A n = P M m =0 a 2 m,n , B n = P M m =0 b 2 m,n , and C n = P M m =0 a m,n b m,n . Applying Lagranges identity , we obtain A n B n − C 2 n = 1 2 M X i =0 M X j =0 ( a i,n b j,n − a j,n b i,n ) 2 = 1 2 M X i =0 M X j =0 p i p j K i,n K j,n ( X i,n Y j,n − X j,n Y i,n ) 2 . (29) By substituting (29) and separating the terms in volving the fixed BS power p 0 , the CRB constraint (28) can be equiv alently reformulated as F n ( p ) = M X m =1 α m,n p m + µ n − η 2 M X i =1 M X j =1 β i,j,n p i p j − η p 0 M X m =1 φ m,n p m ≤ 0 , ∀ n ∈ N , (30) where p ≜ [ p 1 , . . . , p M ] T denotes the vector of transmit powers. The coefficients for each n ∈ N are defined as α m,n ≜ K m,n ( X 2 m,n + Y 2 m,n ) , m ∈ M , (31) µ n ≜ p 0 K 0 ,n ( X 2 0 ,n + Y 2 0 ,n ) , (32) β i,j,n ≜ K i,n K j,n ( X i,n Y j,n − X j,n Y i,n ) 2 , i, j ∈ M , (33) φ m,n ≜ K 0 ,n K m,n ( X 0 ,n Y m,n − X m,n Y 0 ,n ) 2 , m ∈ M . (34) Replacing the optimization variables, (30) can be written as e F n ( v ) = M X m =1 α m,n e v m + µ n − η 2 M X i =1 M X j =1 β i,j,n e v i + v j − η p 0 M X m =1 φ m,n e v m , ∀ n ∈ N . (35) While the first term is conv ex in v and µ n is constant, the last two terms are concave because e v i + v j and e v m are conv ex in v , and the ne gative of a con ve x function is concave. Thus, e F n ( v ) is nonconv ex. Overall, the reformulated optimization problem is giv en by ( P 2) : max t 0 , u , v min m ∈M { log e R m ( u m , v m ) } s.t. t 0 > 0 , (36a) t 0 + M X m =1 e u m ≤ T max , (36b) v m ≤ log P max , ∀ m ∈ M , (36c) u m + v m ≤ log( E m ( t 0 )) , ∀ m ∈ M , (36d) e F n ( v ) ≤ 0 , ∀ n ∈ N , (36e) where u ≜ [ u 1 , . . . , u M ] T ∈ R M and v ≜ [ v 1 , . . . , v M ] T ∈ R M . Compared with the original problem ( P 1) , problem ( P 2) is considerably more tractable due to the concave objectiv e function and con vex constraints, except for (36e). T o tackle this issue, we construct suitable con vex approximations and Algorithm 1 Proposed Iterative Algorithm f or ( P 1) Initialization Initialize a feasible point ( t (0) 0 , u (0) , v (0) ) , set iteration index r = 0 and threshold λ th . Iteration a) Build e F ( r ) n ( v ) and corresponding conv ex problem ( P 2 ( r ) ) using v ( r ) ; b) Solve problem ( P 2 ( r ) ) to obtain ( t ( r⋆ ) 0 , u ( r⋆ ) , v ( r⋆ ) ) ; c) If the relative objectiv e improvement is below the threshold λ th Define ( t ⋆ 0 , u ⋆ , v ⋆ ) = ( t ( r⋆ ) 0 , u ( r⋆ ) , v ( r⋆ ) ) and go to d) . Else Define ( t ( r +1) 0 , u ( r +1) , v ( r +1) ) = ( t ( r⋆ ) 0 , u ( r⋆ ) , v ( r⋆ ) ) , r = r + 1 , and go back to a) . Reconstruction d) Reco ver t ⋆ m = e u ⋆ m and p ⋆ m = e v ⋆ m , ∀ m ∈ M , and calculate the corresponding objective value. dev elop an SCA-based solution framework in the following subsection [17]. B. Iterative Algorithm T o handle the remaining noncon vexity in (36e), we adopt an SCA-based approach by constructing a con vex surrogate of e F n ( v ) . At the r -th iteration, let v ( r ) denote the current feasible point. Note that the noncon vexity of e F n ( v ) stems from the last tw o conca ve terms. Since a concave function admits a global upper bound given by its first-order T aylor expansion, we upper-bound these concave terms at v ( r ) , which leads to an affine upper bound and thus a conv ex e F ( r ) n ( v ) satisfying e F n ( v ) ≤ e F ( r ) n ( v ) for all v . The resulting surrogate is giv en in (37). Accordingly , we obtain a conv ex optimization problem at iteration r as ( P 2 ( r ) ) : max t 0 , u , v min m ∈M { log e R m ( u m , v m ) } s.t. e F ( r ) n ( v ) ≤ 0 , ∀ n ∈ N , (38a) (36a) − (36d) , which can be easily solved using conv ex optimization tools. The inequality in (37) ensures that the constraint (38a) is always stricter than (36e), thus the feasible point in ( P 2 ( r ) ) is always feasible in ( P 2) . The ov erall SCA-based iterative procedure is summarized in Algorithm 1. I V . N U M E R I C A L R E S U LT S In this section, numerical results are presented to ev aluate the performance of the proposed wireless powered ISA C system. W e consider an ISAC system consisting of one BS, M = 10 users, and N = 10 tar gets, where the BS is located at the origin and users as well as targets are randomly and independently distrib uted ov er a circular area of radius 10 m centered at the BS. The wireless channel gain is giv en by h = z κd − ν , where d denotes the distance, κ = 10 − 3 is the reference channel gain, ν = 2 . 5 is the path loss exponent, and z represents a Rayleigh-distributed small-scale fading factor . Unless otherwise stated, the default simulation parameters are set as follows: c = 3 × 10 8 m/s, T max = 10 s, p 0 = 10 W , P max = 2 W , σ 2 = − 70 dBm, η = 5 × 10 − 2 , W = 1 MHz, ζ m = 0 . 7 , ∀ m ∈ M , and λ th = 10 − 5 . 0 1 2 3 4 5 6 7 0 1 2 3 4 5 6 7 10 4 Fig. 2. Conv ergence behavior of the proposed and benchmark schemes. 1 2 3 4 5 6 7 8 9 10 10 -2 0 5 10 15 10 4 Fig. 3. Minimum achie vable throughput versus target localization accuracy requirement. T o further demonstrate the effecti veness of the proposed joint resource allocation scheme, we provide the follo wing two benchmark schemes for performance comparison: • Equal ISA C T ime : The total ISAC transmission duration is equally divided among all users, i.e., t m = t , ∀ m ∈ M , while the v ariables ( t 0 , t, p ) are jointly optimized using a simplified variant of Algorithm 1. • Maximum T ransmit Power : All users transmit with the maximum allo wable po wer , i.e., p m = P max , ∀ m ∈ M , while the variables ( t 0 , t ) are jointly optimized using a simplified variant of Algorithm 1. At first, we examine the con ver gence behavior of the proposed iterative algorithm. Fig. 2 illustrates the ev olution of the minimum achie vable throughput among users versus the iteration index. It is observed that the proposed algo- rithm con ver ges rapidly and stabilizes within a fe w iterations, demonstrating its reliability and efficienc y . Compared with the benchmark schemes, the proposed method achiev es a higher throughput. Then, we ev aluate ho w the system performance varies with the target localization accuracy requirement η . As shown in Fig. 3, the achiev able throughput of both the proposed joint optimization scheme and the equal ISA C time scheme increases with η , since a higher η corresponds to a more relaxed localization constraint. In contrast, the maximum e F n ( v ) ≤ M X m =1 α m,n e v m + µ n − η 2 M X i =1 M X j =1 β i,j,n e v ( r ) i + v ( r ) j h 1 + ( v i − v ( r ) i ) + ( v j − v ( r ) j ) i − η p 0 M X m =1 φ m,n e v ( r ) m h 1 + ( v m − v ( r ) m ) i ≜ e F ( r ) n ( v ) , ∀ n ∈ N (37) 5 6 7 8 9 10 11 12 13 14 15 0 5 10 15 10 4 Fig. 4. Minimum achievable throughput versus WPT transmit power . transmit po wer benchmark scheme remains insensitive to η whenev er it is feasible, because the CRB constraint depends only on the fixed transmit powers and sensing geometry . When η is suf ficiently small, the localization requirement cannot be satisfied under P max , and this benchmark becomes infeasible. Overall, the proposed method outperforms the benchmark schemes in varying localization requirements, highlighting the benefit of jointly optimizing the energy harvesting duration, ISA C transmission time, and transmit po wer . Finally , we in vestigate the impact of the WPT transmit power on the achiev able throughput. Fig. 4 shows the min- imum achiev able throughput among users as a function of the WPT transmit power p 0 . As p 0 increases, the achiev able throughput of all schemes improves, since more energy can be harvested during the WPT phase to support subsequent ISA C transmissions under the same total time budget. The proposed method consistently outperforms the benchmark schemes ov er the entire range of p 0 , demonstrating the benefit of joint resource allocation. In contrast, the equal ISA C time scheme exhibits inferior performance due to its limited flexibility in time allocation. Moreo ver , the maximum transmit power scheme achieves significantly lo wer throughput since fixing the user transmit power reduces the degrees of freedom to balance energy harvesting, localization, and communication. V . C O N C L U S I O N This paper in vestigates a wireless powered ISA C system with CRB-based target localization requirements. W e propose a joint resource allocation frame work that balances harv ested energy , communication throughput, and localization accuracy . T o tackle the resulting noncon ve x problem, we first refor- mulate it via variable substitutions and logarithmic trans- formations, then develop an efficient SCA-based iterativ e algorithm. Numerical results demonstrate fast con ver gence and consistent throughput gains over benchmark schemes under varying localization requirements and ener gy-harvesting conditions, highlighting the effecti veness of the proposed joint time and power allocation in wireless powered ISA C systems. The proposed framework pav es the way for extensions to more general network architectures, such as multi-BS deployments and cooperative ISA C systems. R E F E R E N C E S [1] S. Lu et al., “Integrated Sensing and Communications: Recent Advances and T en Open Challenges, ” IEEE Internet Things J. , vol. 11, no. 11, pp. 19094-19120, Jun. 2024. [2] Y . Cui, F . Liu, X. Jing and J. Mu, “Integrating Sensing and Communica- tions for Ubiquitous IoT : Applications, Trends, and Challenges, ” IEEE Netw . , vol. 35, no. 5, pp. 158-167, Sep. 2021. [3] S. W ang, W . Dai, H. W ang and G. Y . Li, “Robust W aveform Design for Integrated Sensing and Communication, ” IEEE T rans. Signal Pr ocess. , vol. 72, pp. 3122-3138, Jun. 2024. [4] P . W ang, D. Han, Y . Cao, W . Ni and D. Niyato, “Multi-Objective Optimization-Based W aveform Design for Multi-User and Multi-T arget MIMO-ISA C Systems, ” IEEE T rans. W ir eless Commun. , vol. 23, no. 10, pp. 15339-15352, Oct. 2024. [5] L. Sun, Z. Zhao, S. W ang, Z. Ding and M. Peng, “On the Study of Non-Orthogonal Multiple Access (NOMA)-Assisted Integrated Sensing and Communication (ISAC), ” IEEE Tr ans. Commun. , vol. 72, no. 11, pp. 7278-7293, Nov . 2024. [6] F . Liu et al., “Integrated Sensing and Communications: T oward Dual- Functional W ireless Networks for 6G and Beyond, ” IEEE J . Sel. Areas Commun. , vol. 40, no. 6, pp. 1728-1767, Jun. 2022. [7] Z. Zhang et al., “T arget Localization in Cooperative ISA C Systems: A Scheme Based on 5G NR OFDM Signals, ” IEEE T rans. Commun. , vol. 73, no. 5, pp. 3562-3578, May 2025. [8] X. Jing, F . Liu, C. Masouros and Y . Zeng, “ISAC From the Sky: U A V T rajectory Design for Joint Communication and T arget Localization, ” IEEE T rans. W ir eless Commun. , vol. 23, no. 10, pp. 12857-12872, Oct. 2024. [9] X. Li et al., “Integrating Sensing, Communication, and Power T ransfer: From Theory to Practice, ” IEEE Commun. Mag. , vol. 62, no. 9, pp. 122-127, Sep. 2024. [10] Y . Chen, Z. Ren, J. Xu, Y . Zeng, D. W . K. Ng and S. Cui, “Integrated Sensing, Communication, and Powering: T oward Multi-Functional 6G W ireless Networks, ” IEEE Commun. Mag. , vol. 63, no. 8, pp. 146-153, Aug. 2025. [11] X. Li, Z. Han, Z. Zhou, Q. Zhang, K. Huang, and Y . Gong, Wirelessly Powered Integrated Sensing and Communication, in Pr oc. 1st ACM MobiCom W orkshop ISCS , Sydney , Australia, 2022, pp. 1-6. [12] O. Rezaei, M. M. Naghsh, S. M. Karbasi and M. M. Nayebi, “Resource Allocation for UA V -Enabled Integrated Sensing and Communication (ISA C) via Multi-Objective Optimization, ” in Proc. IEEE Int. Conf. Acoust., Speech Signal Process. (ICASSP) , Rhodes Island, Greece, 2023, pp. 1-5. [13] H. Godrich, A. Petropulu and H. V . Poor, “Power Allocation Schemes for T arget Localization in W idely Distributed MIMO Radar Systems, ” in Pr oc. IEEE Mil. Commun. Conf. (MILCOM) , San Jose, CA, USA, 2010, pp. 846-851. [14] H. Godrich, A. P . Petropulu and H. V . Poor, “Power Allocation Strategies for T arget Localization in Distributed Multiple-Radar Archi- tectures, ” IEEE T rans. Signal Pr ocess. , vol. 59, no. 7, pp. 3226-3240, Jul. 2011. [15] X. Y uan, Y . Hu, M. Liu, T . Matsumura and A. Schmeink, “Optimal Beam Deployment for FSO Link Assisted Satellite-Ground Multicasting Communication, ” in Pr oc. IEEE W ireless Commun. and Networking Conf. (WCNC) , Milan, Italy , 2025, pp. 1-6. [16] P . Zheng, B. Li, X. Y uan, Y . Hu and A. Schmeink, “Multi-U A V -Enabled Cognitiv e Radio Networks: Joint U A V Deployment and Resource Al- location Design, ” in Proc. 28th Int. W orkshop Smart Antennas (WSA) , Erlangen, Germany , 2025, pp. 208-213. [17] G. Scutari and Y . Sun, “Parallel and Distributed Successive Con vex Approximation Methods for Big-Data Optimization, ” in Multi-Agent Optimization . Cham, Switzerland: Springer , Jan. 2018, pp. 141-308.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment