On constructing small subgraphs in the budget-constrained random graph process
Consider the budget-constrained random graph process introduced by Frieze, Krivelevich and Michaeli, where each time an edge is offered through the (standard) random graph process we must irrevocably decide whether to "purchase" this edge or not, wit…
Authors: Sylwia Antoniuk, Alberto Espuny Díaz, Kalina Petrova
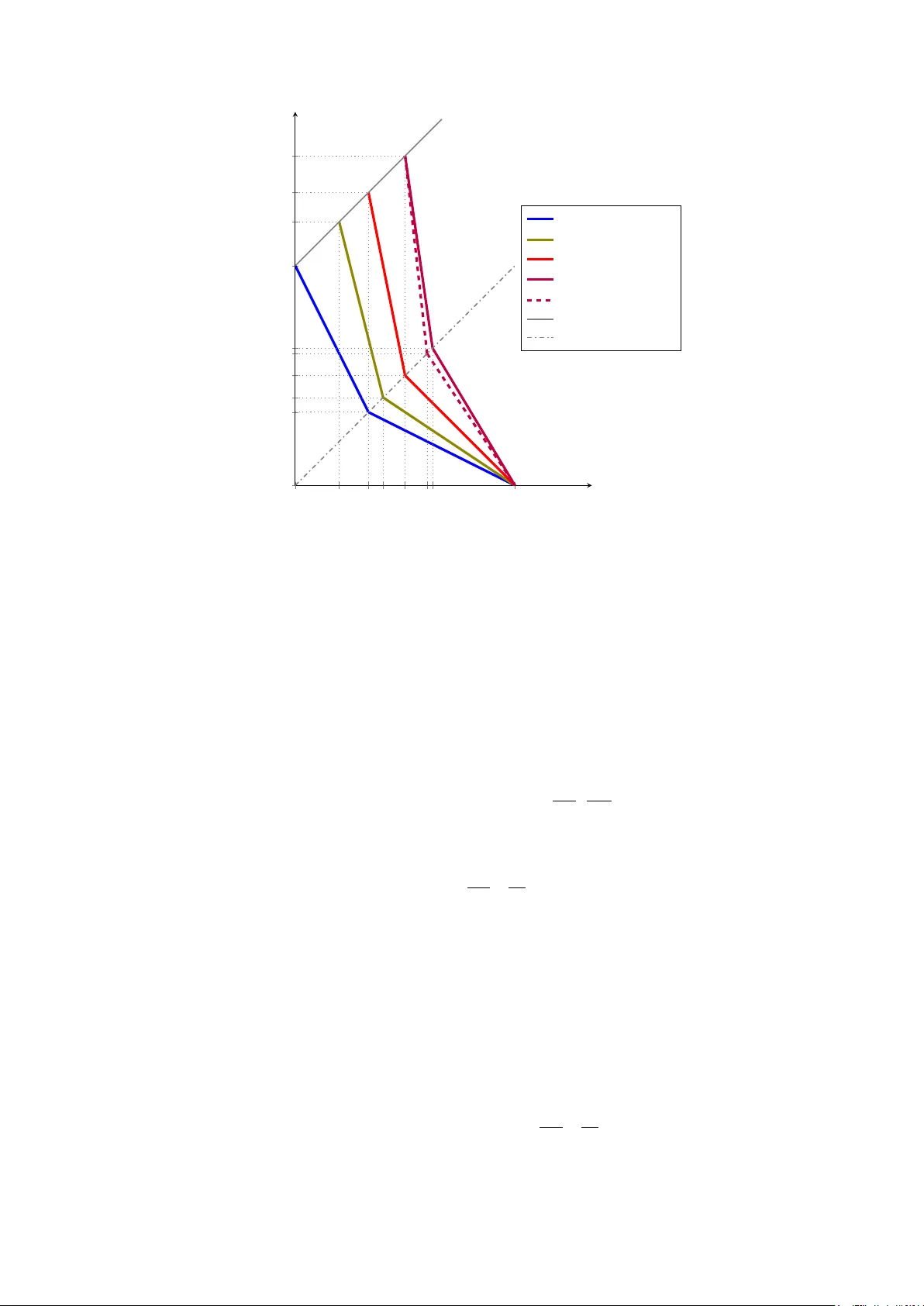
ON CONSTR UCTING SMALL SUBGRAPHS IN THE BUDGET -CONSTRAINED RANDOM GRAPH PR OCESS SYL WIA ANTONIUK, ALBER TO ESPUNY DÍAZ, KALINA PETR OV A, AND MILOŠ ST OJAK OVIĆ Abstract . Consider the budget-constrained r andom graph process introduced by F rieze, Krivelevich and Michaeli, where each time an edge is oered thr ough the (standard) r andom graph pr ocess we must irrevocably decide whether to “purchase” this edg e or not, with our goal being to construct a graph which satises some property within a given time 𝑡 and while purchasing at most 𝑏 edges. W e consider the problem of constructing graphs containing certain xed small subgraphs. W e provide an optimal strategy for building a graph which contains a copy of 𝐾 4 , showing that budget 𝑏 = 𝜔 ( max { 𝑛 8 / 𝑡 5 , 𝑛 2 / 𝑡 } ) suces and that if 𝑏 = 𝑜 ( max { 𝑛 8 / 𝑡 5 , 𝑛 2 / 𝑡 } ) then no strategy can a.a.s. produce a graph containing a copy of 𝐾 4 . This resolves a problem raised by Iľkovič, León and Shu. More g enerally , we obtain analogously tight results for containing a wheel of any xed size, or a graph consisting of a tree plus one additional universal vertex. W e also tackle the problem of constructing graphs containing a copy of 𝐾 5 , obtaining both lower and upper bounds on the optimal budget, though a gap remains in this case. 1. Introduction The study of the evolution of dierent randomised processes for constructing graphs has been a core topic of research in random graph theory . Arguably the most well-studied process in this family is the so-called random graph process . F or a positive integer 𝑛 , let us denote 𝑀 : = 𝑛 2 and [ 𝑛 ] : = { 1 , . . . , 𝑛 } . The random graph process on vertex set [ 𝑛 ] refers to a random sequence of graphs ( 𝐺 0 , 𝐺 1 , . . . , 𝐺 𝑀 ) , all on vertex set [ 𝑛 ] , where 𝐺 0 is the empty graph and, for each 𝑖 ∈ [ 𝑀 ] , a pair of vertices 𝑒 𝑖 is chosen uniformly at random from [ 𝑛 ] 2 \ 𝐸 ( 𝐺 𝑖 − 1 ) before setting 𝐺 𝑖 : = 𝐺 𝑖 − 1 ∪ { 𝑒 𝑖 } . W e think of each 𝑖 ∈ [ 𝑀 ] as a time step , and refer to 𝑒 𝑖 as the edge oered , or presented , at time 𝑖 . W e study a variant of this process, proposed recently by Frieze, Krivelevich and Michaeli [ 3 ] , where an intelligent agent called Builder is introduced as a decision agent. Builder ’ s role is the following: at each time step 𝑖 ∈ [ 𝑀 ] , when the random edge 𝑒 𝑖 is oered, she must decide (immediately and irrevocably) whether this edge is added to the graph or not. The motivation for the inclusion of this agent into the model is related to the optimisation of resources throughout the random graph process: indeed, if the aim is to build a graph which satises a certain property , it may well be that many of the edges oered throughout the random graph process are not “useful” or necessary for (Antoniuk) F acul t y of Ma thema tics and Computer Science, Adam Mickiewicz University , Poznań, Poland . (Espuny Díaz) Dep art ament de Matemà tiques i Informàtica, Universit a t de Barcelona (UB), Gran Via de les Corts Cat alanes, 585, 08007 Barcelona, Sp ain. (P etrova) Institute of Science and Technology Austria (IST A), Am Campus 1, 3400 Klosterneuburg, Aus tria. (Stojak ović) Dep artment of Ma thema tics and Informa tics, F acul ty of Sciences, Universit y of Novi Sad, Serbia. E-mail addresses : antoniuk@amu.edu.pl, aespuny@ub.edu, kalina.petrova@ist.ac.at, milos.stojakovic@dmi.uns.ac.rs . This research was supported by the Oberwolfach Research Institute for Mathematics through its Oberwolfach Research F ellows (OWRF) progr am. S. Antoniuk was supported by Narodowe Centrum Nauki, grant 2024/53/B/ST1/00164. A. Es- puny Díaz was supported by the Deutsche Forschungsgemeinschaft (DFG , German Research F oundation) through project no. 513704762. K. Petr ova was supported by the European Union’ s Horizon 2020 research and innovation programme under the Marie Skłodowska- Curie grant agreement No. 101034413 . M. Stojak ović was partly supported by the Science Fund of the Republic of Serbia, Grant #7462: Graphs in Space and Time: Graph Embeddings for Machine Learning in Complex Dynamical Systems (TIGRA), and partly supported by the Ministry of Science, T echnological Development and Innovation of the Republic of Serbia (grants 451-03-33/2026-03/200125 & 451-03-34/2026-03/200125). 1 2 S. ANTONIUK, A. ESPUNY DÍAZ, K. PETRO V A, AND M. STOJAK OVIĆ attaining the desired property , while adding them to the graph may incur a cost. As such, Builder’s goal will be to nd a strategy that allows her to construct a graph which satises the desired property , within a certain amount of time, but while purchasing as few edg es as possible. More precisely , we will often assume that Builder has a “ deadline” for constructing a graph with the desired property , which is expressed through a time constraint 𝑡 ∈ [ 𝑀 ] . Given this constraint, we will denote the sequence of graphs built by Builder by ( 𝐵 0 , 𝐵 1 , . . . , 𝐵 𝑡 ) ; recall that this is dened through an ambient random graph process ( 𝐺 0 , 𝐺 1 , . . . ) , and thus we have the trivial inclusion 𝐵 𝑖 ⊆ 𝐺 𝑖 for all 𝑖 ∈ [ 𝑡 ] . Moreover , we will assume that there is a limit on the resources that Builder is allowed to use; this is expressed as a budget constraint 𝑏 ∈ [ 𝑡 ] , and the strat egy that Builder follows must ensure that | 𝐸 ( 𝐵 𝑡 ) | ≤ 𝑏 (note that we may assume that 𝑏 ≤ 𝑡 as otherwise this constraint would be trivial). This motivates the name of the budget-constrained random graph process when referring to this family of random graph processes. As is usual when considering random graphs, we are interested in asymptotic statements, that is, we want to know whether Builder has strategies which are very likely to produce a graph with the desired property when 𝑛 is larg e. F ormally , we will say that a statement holds asymptotically almost surely (a.a.s. for short) if the probability that it holds tends to 1 as 𝑛 tends to innity . Given time and budget constraints 𝑡 ∈ [ 𝑀 ] and 𝑏 ∈ [ 𝑡 ] , a ( 𝑡 , 𝑏 ) -strategy is a function which, given a history of the random graph process and the choices of Builder up to some time 0 ≤ 𝑖 < 𝑡 , and presented with a new edg e 𝑒 𝑖 + 1 , outputs whether this next edge should be purchased or not, with the restriction that | 𝐸 ( 𝐵 𝑡 ) | ≤ 𝑏 . W e say that a ( 𝑡 , 𝑏 ) -strategy S is successful for some (monotone increasing) property P if, when running the budget-constrained random graph process under S , a.a.s. 𝐵 𝑡 ∈ P . Our rst main goal is to determine the optimal asymptotic values of 𝑏 , for each time constraint 𝑡 , for which there exist successful ( 𝑡 , 𝑏 ) -strategies for P . W e sometimes informally think of this as a “budget threshold” for ha ving successful strategies. Several papers have considered dierent spanning properties in the budget-constrained random graph process [ 1 , 2 , 3 , 6 , 7 ]. In this paper we instead focus on the case that Builder wants to construct a copy of some xed subgraph 𝐹 . This problem was rst addressed by Frieze, Krivelevich and Michaeli [ 3 ] , who obtained tight results on the optimal order of magnitude of 𝑏 as a function of 𝑡 when attempting to construct copies of any given xed tree or cycle (and their methods can be used to construct any given unicyclic graph). Subsequently , Iľkovič, León and Shu [ 4 ] obtained analogously tight results for the diamond (the complete graph on four vertices with one edge removed) as well as for 𝑘 -fans (where a 𝑘 -fan for 𝑘 ∈ ℕ is a graph consisting of 𝑘 triangles, all sharing a single vertex). No other results for this model were known at the moment. Both sets of authors asked for the development of general tools to deal with other xed graphs 𝐹 , and Iľk ovič, León and Shu [ 4 ] specically asked about the case when 𝐹 is a clique (with 𝐾 4 being the rst natural open problem). A wheel on 𝑘 ≥ 4 vertices, denoted 𝑊 𝑘 , is a graph which consists of a cycle of length 𝑘 − 1 with one additional vertex which is joined by an edge to every vertex of the cycle. Note, in particular , that 𝑊 4 = 𝐾 4 . Our rst main result in this paper establishes the correct order of magnitude of the “budget threshold” required for constructing a copy of 𝑊 𝑘 in the budget-constrained random graph process, for every 𝑘 ≥ 4 and the whole range of 𝑡 (thereby in particular resolving the problem for 𝐾 4 ). This is the rst innite family of graphs containing cycles which share edges for which this threshold is known. See Figure 1 for a visual representation of these results. Theorem 1.1. Let 𝑘 ≥ 4 be an integer . F or all 𝑡 ∈ [ 𝑀 ] , if 𝑡 = 𝑜 𝑛 3 2 − 1 2 ( 𝑘 − 1 ) or 𝑏 = 𝑜 max 𝑛 3 𝑘 − 4 𝑡 2 𝑘 − 3 , 𝑛 2 𝑡 , (1.1) then for any ( 𝑡 , 𝑏 ) -strategy a.a.s. 𝐵 𝑡 does not contain a copy of 𝑊 𝑘 . On the other hand, if 𝑡 ≥ 𝑏 = 𝜔 max 𝑛 3 𝑘 − 4 𝑡 2 𝑘 − 3 , 𝑛 2 𝑡 , (1.2) then there exists a successful ( 𝑡 , 𝑏 ) -strategy for constructing a copy of 𝑊 𝑘 . ON CONSTR UCTING SMALL SUBGRAPHS IN THE BUDGET -CONSTRAINED RANDOM GRAPH PROCESS 3 4 / 3 3 / 2 2 0 1 / 2 4 / 3 log 𝑛 𝑡 log 𝑛 𝑏 𝑊 4 𝑊 5 𝑊 6 𝑊 7 𝑥 ↦→ 𝑥 𝑥 ↦→ 𝑥 − 1 Figure 1. A depiction of the optimal budget 𝑏 for successful ( 𝑡 , 𝑏 ) -strategies for constructing copies of 𝑊 𝑘 with 𝑘 ∈ { 4 , 5 , 6 , 7 } , as given by Theorem 1.1 . The lower bound for the optimal budget constraint 𝑏 expressed in ( 1.1 ) is a corollary (Theorem 3.2 ) of a more general result (Theorem 3.1 ) which can be applied to obtain some lower bound for any xed graph 𝐹 . However , we do not believe these bounds to be tight in g eneral, and thus do not pursue fully g eneral expressions. W e remark that this addresses, in a weak form, the quest for general tools proposed by Frieze, Krivelevich and Michaeli [ 3 ] ; see Section 3 for the general statements, and Section 5 for a more thorough discussion about this. The upper bound expressed via ( 1.2 ) is obtained by exhibiting a specic strategy and analysing its behaviour; the statement pertaining to this bound is reintroduced later as Theorem 4.1 . F or our second main result, we use our techniques to obtain tight results for a richer family of graphs. Given a tree 𝑇 , let 𝐾 1 , 𝑇 denote the graph consisting of a copy of 𝑇 plus one additional vertex which is joined by an edge to all vertices of 𝑇 . Theorem 1.2. Let 𝑇 be a xed tree. Let 𝑚 : = | 𝐸 ( 𝑇 ) | . F or all 𝑡 ∈ [ 𝑀 ] , if 𝑡 = 𝑜 𝑛 3 𝑚 2 𝑚 + 1 or 𝑏 = 𝑜 max ( 𝑛 3 𝑚 𝑡 2 𝑚 , 𝑛 2 𝑡 𝑚 𝑚 + 1 ) ! , then for any ( 𝑡 , 𝑏 ) -strategy a.a.s. 𝐵 𝑡 does not contain a copy of 𝐾 1 , 𝑇 . On the other hand, if 𝑡 ≥ 𝑏 = 𝜔 max ( 𝑛 3 𝑚 𝑡 2 𝑚 , 𝑛 2 𝑡 𝑚 𝑚 + 1 ) ! , then there exists a successful ( 𝑡 , 𝑏 ) -strategy for constructing a copy of 𝐾 1 , 𝑇 . With this theorem, we recover the result of Iľkovič, León and Shu [ 4 ] for the diamond. It also provides tight results for some relevant families of graphs, such as triangular books. The proof is analogous to that of Theorem 1.1 ; for completeness, we include it in Section A . Ev en though our methods lead to tight results for constructing a copy of 𝐾 4 , they do not suce for obtaining tight results for larg er cliques. Still, they can be used to obtain non-trivial upper and lower bounds on the “budget threshold” . As an example, we include our results for the particular case 4 S. ANTONIUK, A. ESPUNY DÍAZ, K. PETRO V A, AND M. STOJAK OVIĆ 1 4 / 3 3 / 2 13 / 8 2 0 1 / 3 2 / 5 1 / 2 3 / 5 1 6 / 5 4 / 3 3 / 2 log 𝑛 𝑡 log 𝑛 𝑏 𝐾 3 , 𝐾 + 3 , 𝐶 4 𝐾 − 4 𝐾 4 𝐾 5 upper bound 𝐾 5 lower bound 𝑥 ↦→ 𝑥 𝑥 ↦→ 𝑥 − 1 Figure 2. A depiction of the optimal budget 𝑏 for successful ( 𝑡 , 𝑏 ) -strategies for 𝐾 4 , as given by Theorem 1.1 , compared with the optimal budget for its cyclic subgraphs ( 𝐾 3 , 𝐾 + 3 and 𝐶 4 are due to Frieze, Krivelevich and Michaeli [ 3 ] , and 𝐾 − 4 is due to Iľk ovič, León and Shu [ 4 ] ). Additional depiction of the upper bound and lower bound on the optimal budget 𝑏 for successful ( 𝑡 , 𝑏 ) -strategies for 𝐾 5 , as given by Theorem 1.3 . of 𝐾 5 . See Figure 2 for a visual representation of this result, compared with the “budget thresholds” for a few other small graphs. Theorem 1.3. F or all 𝑡 ∈ [ 𝑀 ] , if 𝑡 = 𝑜 𝑛 3 / 2 or 𝑏 = 𝑜 max 𝑛 15 𝑡 9 , 𝑛 3 𝑡 3 / 2 , (1.3) then for any ( 𝑡 , 𝑏 ) -strategy a.a.s. 𝐵 𝑡 does not contain a copy of 𝐾 5 . On the other hand, if 𝑡 ≥ 𝑏 = 𝜔 max ( 𝑛 12 𝑡 7 , 𝑛 2 𝑡 5 / 3 ) ! , (1.4) then there exists a successful ( 𝑡 , 𝑏 ) -strategy for constructing a copy of 𝐾 5 . F or the lower bound ( 1.3 ) , we obtain a more general statement which holds for cliques of arbitrary size (see Theorem 3.3 ). On the other hand, the upper bound ( 1.4 ) is harder to generalise, and thus here we only consider the case of 𝐾 5 ; see Theorem 4.3 for the corresponding statement. W e believe that the upper bound should give the correct behaviour . Conjecture 1.4. F or all 𝑡 ∈ [ 𝑀 ] , if 𝑡 = 𝑜 𝑛 3 / 2 or 𝑏 = 𝑜 max ( 𝑛 12 𝑡 7 , 𝑛 2 𝑡 5 / 3 ) ! , then for any ( 𝑡 , 𝑏 ) -strategy a.a.s. 𝐵 𝑡 does not contain a copy of 𝐾 5 . ON CONSTR UCTING SMALL SUBGRAPHS IN THE BUDGET -CONSTRAINED RANDOM GRAPH PROCESS 5 2. Not ation and tools Most of our graph theoretic notation is standard. Given a graph 𝐺 and a set 𝑈 ⊆ 𝑉 ( 𝐺 ) , we denote by 𝐺 [ 𝑈 ] the subgraph of 𝐺 induced by 𝑈 , that is, the graph with vertex set 𝑈 whose edg es are all those edg es of 𝐺 which are contained in 𝑈 . The number of edges of this induced subgraph is denoted by 𝑒 𝐺 ( 𝑈 ) , and we denote 𝑒 ( 𝐺 ) : = 𝑒 𝐺 ( 𝑉 ( 𝐺 ) ) . W e also denote 𝑣 ( 𝐺 ) : = | 𝑉 ( 𝐺 ) | . Given a graph 𝐺 and a verte x 𝑣 ∈ 𝑉 ( 𝐺 ) , the neighbourhood of 𝑣 in 𝐺 is the set 𝑁 𝐺 ( 𝑣 ) : = { 𝑢 ∈ 𝑉 ( 𝐺 ) : { 𝑢 , 𝑣 } ∈ 𝐸 ( 𝐺 ) } , and the degree of 𝑣 is dened as deg 𝐺 ( 𝑣 ) : = | 𝑁 𝐺 ( 𝑣 ) | . The minimum vertex degree of 𝐺 is denoted by 𝛿 ( 𝐺 ) . Given two graphs 𝐺 and 𝐻 on the same vertex set and some set 𝑆 ⊆ 𝑉 ( 𝐺 ) , we denote by 𝐺 \ 𝐻 the graph on the same vertex set with edge set 𝐸 ( 𝐺 ) \ 𝐸 ( 𝐻 ) , and by 𝐺 − 𝑆 the graph on vertex set 𝑉 ( 𝐺 ) \ 𝑆 obtained from 𝐺 by deleting all edges of 𝐺 that intersect 𝑆 . F or a positive integer 𝑛 and 𝑝 ∈ [ 0 , 1 ] , we write 𝐺 ( 𝑛 , 𝑝 ) to denote the probability distribution on all (labelled) 𝑛 -v ertex graphs which results from sampling a graph by including each of its 𝑀 = 𝑛 2 possible edg es independently with probability 𝑝 . W e will use the following standard Cherno bound (see, e.g., the book of Janson, Łuczak and Ruciński [ 5 , Corollary 2.3 and Theorem 2.10]). Lemma 2.1 (Cherno bound) . Let 𝑋 be the sum of 𝑛 independent Bernoulli random variables, or a hypergeometric random variable, and let 𝜇 : = 𝔼 [ 𝑋 ] . Then, for all 𝛿 ∈ [ 0 , 1 ] , we have that ℙ [ | 𝑋 − 𝜇 | ≥ 𝛿 𝜇 ] ≤ 2e − 𝛿 2 𝜇 / 3 . Consider the random graph process ( 𝐺 0 , 𝐺 1 , . . . , 𝐺 𝑀 ) on vertex set [ 𝑛 ] . Let ˜ 𝑛 = ˜ 𝑛 ( 𝑛 ) ∈ [ 𝑛 ] and 𝑚 : = ˜ 𝑛 2 , and let 𝑈 ⊆ [ 𝑛 ] be a set of vertices of size | 𝑈 | = ˜ 𝑛 . While running the random graph process, we can restrict our attention to the oered edges that are contained in 𝑈 to simulate the random graph process on verte x set 𝑈 . F ormally , this is achieved by dening a new sequence of random graphs ( 𝐺 𝑈 0 , 𝐺 𝑈 1 , . . . , 𝐺 𝑈 𝑚 ) as follows. First, we let 𝐺 𝑈 0 be the empty graph on vertex set 𝑈 . Then, while running the random graph process, we let 𝑖 𝑈 1 < . . . < 𝑖 𝑈 𝑚 denote the (random) times at which the oered edge 𝑒 𝑖 𝑈 𝑗 is contained in 𝑈 . F or each 𝑗 ∈ [ 𝑚 ] , we set 𝐺 𝑈 𝑗 : = 𝐺 𝑈 𝑗 − 1 ∪ { 𝑒 𝑖 𝑈 𝑗 } . It is clear that ( 𝐺 𝑈 0 , 𝐺 𝑈 1 , . . . , 𝐺 𝑈 𝑚 ) is then distributed like the random graph process on 𝑈 . It is often useful to refer to dierent segments of the random gr aph process. The segment of the random graph process of length 𝑡 ∈ [ 𝑀 ] starting at time 𝑗 ∈ { 0 } ∪ [ 𝑀 − 𝑡 ] is the (random) sequence of graphs ( ˜ 𝐺 0 , ˜ 𝐺 1 , . . . , ˜ 𝐺 𝑡 ) : = ( 𝐺 𝑗 \ 𝐺 𝑗 , 𝐺 𝑗 + 1 \ 𝐺 𝑗 , . . . , 𝐺 𝑗 + 𝑡 \ 𝐺 𝑗 ) . W e remark that, if the outcome of the random graph process up to time 𝑗 has not been revealed, then the segment of the random graph process of length 𝑡 starting at time 𝑗 has the same distribution as the segment of length 𝑡 starting at time 0 , that is, ( ˜ 𝐺 0 , ˜ 𝐺 1 , . . . , ˜ 𝐺 𝑡 ) ∼ ( 𝐺 0 , 𝐺 1 , . . . , 𝐺 𝑡 ) . Restricting the simulation of the random graph process on a set 𝑈 ⊆ [ 𝑛 ] of size | 𝑈 | = ˜ 𝑛 to the segment of length 𝑡 starting at time 𝑗 leads to a random segment of the random graph process on 𝑈 . More precisely , the outcome is the sequence of graphs ( ˜ 𝐺 𝑈 0 , ˜ 𝐺 𝑈 1 , . . . , ˜ 𝐺 𝑈 | 𝐾 | ) given by taking 𝐾 : = { 𝑘 ∈ [ 𝑚 ] : 𝑖 𝑈 𝑘 ∈ [ 𝑗 + 𝑡 ] \ [ 𝑗 ] } , letting 𝑘 0 : = min { 𝑘 ∈ 𝐾 } − 1 (or 𝑘 0 : = 0 if 𝐾 is empty), and dening ˜ 𝐺 𝑈 0 as the empty graph on 𝑈 , and ˜ 𝐺 𝑈 ℓ : = ˜ 𝐺 𝑈 ℓ − 1 ∪ { 𝑒 𝑖 𝑈 𝑘 0 + ℓ } for each ℓ ∈ [ | 𝐾 | ] . W e will refer to the segment of the random gr aph process on 𝑈 obtained when simulating the random graph process on 𝑈 during the segment of length 𝑡 starting at time 𝑗 (that is, the sequence ( ˜ 𝐺 𝑈 0 , ˜ 𝐺 𝑈 1 , . . . , ˜ 𝐺 𝑈 | 𝐾 | ) above) as the ( 𝑈 , 𝑗 , 𝑡 ) -random graph process (sometimes shortened to ( 𝑈 , 𝑗 , 𝑡 ) -R GP); note, in particular , that the ( [ 𝑛 ] , 𝑗 , 𝑡 ) -RGP corresponds to the segment itself. The length of the ( 𝑈 , 𝑗 , 𝑡 ) -RGP , denoted ℓ ( 𝑈 , 𝑗 , 𝑡 ) , is the random variable | 𝐾 | . It will be useful to have some control over the length of the ( 𝑈 , 𝑗 , 𝑡 ) -RGP for dierent choices of 𝑈 . In fact, we will want this in some situations where the set 𝑈 itself depends on the outcomes of part of the ‘global’ random graph process. The following lemma encompasses the situations we will encounter later . Lemma 2.2. Let ˜ 𝑛 = ˜ 𝑛 ( 𝑛 ) ∈ [ 𝑛 ] , 𝑡 1 = 𝑡 1 ( 𝑛 ) ∈ [ 𝑀 ] , and 𝑡 2 = 𝑡 2 ( 𝑛 ) ∈ [ 𝑀 ] be such that ˜ 𝑛𝑛 ≤ 𝑡 1 = 𝑜 ( 𝑛 2 ) , 𝑡 1 ˜ 𝑛 2 = 𝜔 ( 𝑛 2 ) , and 𝑡 2 ˜ 𝑛 2 = 𝜔 ( 𝑛 2 ) . Let 𝑗 ∈ [ 𝑀 − 𝑡 2 ] \ [ 𝑡 1 ] and x a vertex 𝑥 ∈ [ 𝑛 ] . Then a.a.s. 6 S. ANTONIUK, A. ESPUNY DÍAZ, K. PETRO V A, AND M. STOJAK OVIĆ deg 𝐺 𝑡 1 ( 𝑥 ) ≥ ˜ 𝑛 and, letting 𝑈 denote the set of the rst ˜ 𝑛 neighbours of 𝑥 throughout the random graph process, we have that 𝑡 2 ˜ 𝑛 2 / 2 𝑛 2 ≤ ℓ ( 𝑈 , 𝑗 , 𝑡 2 ) ≤ 3 𝑡 2 ˜ 𝑛 2 / 2 𝑛 2 . Proof . Consider rst the ( [ 𝑛 ] , 0 , 𝑡 1 ) -RGP; during this segment, we are interested in the neighbourhood of 𝑥 and in controlling the number of oered edges contained within this neighbourhood (particularly , within the rst ˜ 𝑛 neighbours of 𝑥 in the random graph process). More precisely , let 𝑋 : = | 𝑁 𝐺 𝑡 1 ( 𝑥 ) | , let 𝑖 ∗ : = ( 𝑡 1 if 𝑋 < ˜ 𝑛 , min { 𝑖 ∈ [ 𝑡 1 ] : | 𝑁 𝐺 𝑖 ( 𝑥 ) | = ˜ 𝑛 } otherwise , let 𝑁 ∗ : = 𝑁 𝐺 𝑖 ∗ ( 𝑥 ) and 𝑋 ∗ : = | 𝑁 ∗ | = min { 𝑋 , ˜ 𝑛 } , and let 𝑌 : = 𝑒 𝐺 𝑡 1 ( 𝑁 ∗ ) . Then, dene the events N : = { 𝑡 1 / 𝑛 ≤ 𝑋 ≤ 3 𝑡 1 / 𝑛 } , N ∗ : = { 𝑋 ∗ = ˜ 𝑛 } ⊇ N and E : = { 𝑌 ≤ ˜ 𝑛 2 𝑡 1 / 𝑀 } . First, reveal 𝑁 𝐺 𝑡 1 ( 𝑥 ) (this includes revealing the times at which the edges 𝑥 𝑣 with 𝑣 ∈ 𝑁 𝐺 𝑡 1 ( 𝑥 ) were oered, but not any other edg e of the process). Note that 𝔼 [ 𝑋 ] = ( 𝑛 − 1 ) 𝑡 1 / 𝑀 ≥ 2 ˜ 𝑛 . Since 𝑋 follows a hypergeometric distribution and ˜ 𝑛 = 𝜔 ( 1 ) , by Theorem 2.1 we have that ℙ [N ] ≤ e − Ω ( ˜ 𝑛 ) = 𝑜 ( 1 ) , so N holds a.a.s. Now reveal the remaining edg es of the ( [ 𝑛 ] , 0 , 𝑡 1 ) -RGP; as the choice of each oered edge is made independently , we have that, upon conditioning on an arbitrary value for 𝑋 , the variable 𝑌 follows a hypergeometric distribution with 𝔼 [ 𝑌 | 𝑋 ] = 𝑋 ∗ 2 𝑡 1 − 𝑋 𝑀 − 𝑋 . In particular , as 𝑡 1 / 𝑛 ≥ ˜ 𝑛 = 𝜔 ( 1 ) , for each integer 𝑘 ∈ [ 𝑡 1 / 𝑛 , 3 𝑡 1 / 𝑛 ] , conditioning on 𝑋 = 𝑘 implies that 𝑋 ∗ = ˜ 𝑛 and thus we hav e that 𝔼 [ 𝑌 | 𝑋 = 𝑘 ] = ( 1 ± 𝑜 ( 1 ) ) ˜ 𝑛 2 𝑡 1 2 𝑀 . As ˜ 𝑛 2 𝑡 1 = 𝜔 ( 𝑛 2 ) , it follows from Theorem 2.1 that ℙ [ 𝑌 > ˜ 𝑛 2 𝑡 1 / 𝑀 | 𝑋 = 𝑘 ] ≤ e − Θ ( ˜ 𝑛 2 𝑡 1 / 𝑀 ) = 𝑜 ( 1 ) . Since N holds a.a.s., by the law of total probability , it follows that E holds a.a.s. too. Now condition on the event that N (and thus also N ∗ ) and E hold, which occurs a.a.s.; from now on, all probabilistic statements refer to this conditional space. Note that 𝑈 = 𝑁 ∗ in this conditional space. Note, moreover , that the sequence of edg es presented during the ( [ 𝑛 ] , 𝑗 , 𝑡 2 ) -RGP is a uniformly random sequence of 𝑡 2 distinct edges from [ 𝑛 ] 2 \ 𝐸 ( 𝐺 𝑡 1 ) , which is a set of size ( 1 − 𝑜 ( 1 ) ) 𝑀 . As ℓ ( 𝑈 , 𝑗 , 𝑡 2 ) follows a hypergeometric distribution with 𝔼 [ ℓ ( 𝑈 , 𝑗 , 𝑡 2 ) ] = ˜ 𝑛 2 − 𝑒 𝐺 𝑡 1 ( 𝑈 ) 𝑡 2 𝑀 − 𝑡 1 = ( 1 ± 𝑜 ( 1 ) ) ˜ 𝑛 2 𝑡 2 𝑛 2 (where the last equality uses the facts that we conditioned on E , that ˜ 𝑛 = 𝜔 ( 1 ) , and that 𝑡 1 = 𝑜 ( 𝑛 2 ) ), Theorem 2.1 implies that ℙ ℓ ( 𝑈 , 𝑗 , 𝑡 2 ) ∉ 𝑡 2 ˜ 𝑛 2 2 𝑛 2 , 3 𝑡 2 ˜ 𝑛 2 2 𝑛 2 ≤ e − Θ ( 𝑡 2 ˜ 𝑛 2 / 𝑛 2 ) = 𝑜 ( 1 ) . □ In the same wa y that we can use the ‘global’ r andom graph process to simulate a random graph process on a subset 𝑈 ⊆ [ 𝑛 ] , even when restricted to segments of the global random graph process, we can also simulate any strat egy on this subset. More precisely , we can use the global random graph process to simulate the random graph process on 𝑈 and then run a strategy designed for this (simulated) random graph process. By this we mean that Builder discards every edge oered (by the global random graph process) which is not contained in 𝑈 , and for edg es contained in 𝑈 she considers the strategy as if it was run on the (simulated) random graph process on | 𝑈 | vertices. Given that, when simulating the random graph process on 𝑈 during a segment of the global random graph process, we do not know the length of the resulting segment, we will simulate ( 𝑡 , 𝑏 ) -strategies on a subset 𝑈 for certain values of 𝑡 and 𝑏 , where we will choose 𝑡 in such a way that a.a.s. the simulated segment has length at least 𝑡 (lik e in Theorem 2.2 ). In the unlik ely event that the simulated segment ON CONSTR UCTING SMALL SUBGRAPHS IN THE BUDGET -CONSTRAINED RANDOM GRAPH PROCESS 7 has length less than 𝑡 , this strategy is still well dened: it is run until the end of the simulated segment, possibly not reaching its desired outcome, but certainly not going over the (simulated) allotted time or budget. The following coupling lemma will also be useful in the proofs of our 1 -statements. Lemma 2.3 ([ 2 , Lemma 3.3]) . Let 𝑘 ∈ ℕ be xed. Let 𝑡 1 , . . . , 𝑡 𝑘 ∈ [ 𝑀 ] be such that 𝑡 𝑖 = 𝜔 ( 1 ) for every 𝑖 ∈ [ 𝑘 ] and 𝑡 𝑖 = 𝑜 ( 𝑀 ) for every 𝑖 ∈ [ 𝑘 − 1 ] . Let 𝑠 0 : = 0 and, for each 𝑖 ∈ [ 𝑘 ] , set 𝑠 𝑖 : = Í 𝑖 𝑗 = 1 𝑡 𝑗 . Let 𝐺 0 , 𝐺 1 , 𝐺 2 , . . . denote a random graph process on [ 𝑛 ] and, for each 𝑖 ∈ [ 𝑘 ] , let ˆ 𝐺 𝑖 : = 𝐺 𝑠 𝑖 \ 𝐺 𝑠 𝑖 − 1 . Then for each 𝑖 ∈ [ 𝑘 ] there exist 𝑝 𝑖 = ( 1 − 𝑜 ( 1 ) ) 𝑡 𝑖 / 𝑀 and 𝑝 𝑖 = 𝑜 ( 𝑡 𝑖 / 𝑀 ) such that there exists a coupling of random graphs ( 𝐻 𝑖 , ˆ 𝐻 𝑖 , 𝐻 𝑖 ) 𝑖 ∈ [ 𝑘 ] satisfying that ( i ) 𝐻 𝑖 ∼ 𝐺 ( 𝑛 , 𝑝 𝑖 ) and 𝐻 𝑖 ∼ 𝐺 ( 𝑛 , 𝑝 𝑖 ) for each 𝑖 ∈ [ 𝑘 ] ; ( ii ) ( ˆ 𝐻 𝑖 ) 𝑖 ∈ [ 𝑘 ] is distributed like ( ˆ 𝐺 𝑖 ) 𝑖 ∈ [ 𝑘 ] ; ( iii ) the graphs { 𝐻 𝑖 , 𝐻 𝑖 : 𝑖 ∈ [ 𝑘 ] } are mutually independent; ( iv ) for each 𝑖 ∈ [ 𝑘 ] , the graphs 𝐻 𝑖 and 𝐻 𝑖 are independent of ( ˆ 𝐻 𝑗 ) 𝑗 ∈ [ 𝑖 − 1 ] , and ( v ) a.a.s. 𝐻 𝑖 \ Ð 𝑖 − 1 𝑗 = 1 ˆ 𝐻 𝑗 ⊆ ˆ 𝐻 𝑖 ⊆ 𝐻 𝑖 ∪ 𝐻 𝑖 for all 𝑖 ∈ [ 𝑘 ] . W e remark that property ( iv ) above is not explicitly stated in [ 2 , Lemma 3.3], but it follows imme- diately from its proof. Similarly , [ 2 , Lemma 3.3] also imposes an upper bound on 𝑡 𝑘 , but it is not actually needed in its proof. 3. Lower bounds In this section, we prove our results about lower bounds on “budget thresholds” . Throughout the section, when we consider subgraphs of a xed graph 𝐹 , or copies of these subgraphs in the random graph process, we always mean labelled subgraphs or copies. The following lemma provides an upper bound on the maximum number of copies of a xed connected graph 𝐹 that Builder can construct (a.a.s.) given any time and budget restrictions 𝑡 and 𝑏 . The formula that it provides corresponds to the following simple intuition: In order to count copies of 𝐹 , we may root them at some edge and count the number of choices for this edge (for which there are at most 𝑏 choices). Then, each other vertex of this copy can be chosen iteratively as a neighbour of a previously xed vertex (there are roughly at most Θ ( min { 𝑏 , 𝑛𝑝 }) choices for each such vertex, where 𝑝 = 𝑡 / 𝑀 , and we must x 𝑣 ( 𝐹 ) − 2 other vertices). This essentially yields an upper bound for the number of copies of a spanning tree of 𝐹 . In order for this tree to be completed to a copy of 𝐹 , each edge of 𝐹 that we ha ve not considered so far must at least be oered, which occurs with probability 𝑝 . The proof of the lemma formalises this simple intuition. W e remark here that, in order to prove the lower bounds for their results, Iľk ovič, León and Shu [ 4 ] already used some ad hoc arguments for counting copies of subgraphs of the graphs they are trying to construct. Moreover , a similar intuition to the one discussed above was also k ey in proving results for 𝐹 -factors in the work of Espuny Díaz, Garbe, Naia and Smith [ 2 ]. Let nc ( 𝐹 , S , 𝑛 , 𝑡 , 𝑏 ) be the number of copies of a labelled graph 𝐹 that Builder purchases when following a ( 𝑡 , 𝑏 ) -strategy S in the random graph process on vertex set [ 𝑛 ] . Note that nc ( 𝐹 , S , 𝑛 , 𝑡 , 𝑏 ) is a random variable that depends on the outcome of the random graph process. W e write simply nc ( 𝐹 ) when the other parameters are clear from the context. Moreover , for an edge 𝑒 ∈ 𝐸 ( 𝐹 ) , let nc ( 𝐹 , 𝑒 , S , 𝑛 , 𝑡 , 𝑏 ) , or nc ( 𝐹 , 𝑒 ) for short, denote the number of copies 𝐹 ′ of 𝐹 purchased by Builder for which the edge 𝑒 ′ ∈ 𝐸 ( 𝐹 ′ ) corresponding to 𝑒 is purchased last among all the edges in 𝐸 ( 𝐹 ′ ) . Lemma 3.1. Let 𝐹 be a xed labelled connected graph with 𝑣 ( 𝐹 ) ≥ 2 . Let 𝑡 = 𝑡 ( 𝑛 ) ∈ [ 𝑀 ] and 𝑏 = 𝑏 ( 𝑛 ) ∈ [ 𝑡 ] . Set 𝑝 : = 𝑡 / 𝑀 and let 𝜂 = 𝜔 ( 1 ) be a function that grows arbitrarily slowly with 𝑛 . For every ( 𝑡 , 𝑏 ) -strategy S , we have that a.a.s. nc ( 𝐹 , S , 𝑛 , 𝑡 , 𝑏 ) ≤ 𝜂 · 𝑏 · min { 𝑏 , 𝑛 𝑝 } 𝑣 ( 𝐹 ) − 2 𝑝 𝑒 ( 𝐹 ) − 𝑣 ( 𝐹 ) + 1 . 8 S. ANTONIUK, A. ESPUNY DÍAZ, K. PETRO V A, AND M. STOJAK OVIĆ Proof . If 𝑡 > 𝑀 / 2 the bound holds trivially , since 𝑝 ∈ ( 1 / 2 , 1 ] and the maximum number of copies of 𝐹 in any subgraph of 𝐾 𝑛 with at most 𝑏 edges is at most 𝑂 ( 𝑏 · min { 𝑏 , 𝑛 } 𝑣 ( 𝐹 ) − 2 ) . Fr om now on, we assume that 𝑡 ∈ [ 𝑀 / 2 ] . Let 𝛾 : = 𝜂 / 𝑒 ( 𝐹 ) ! 1 / 𝑒 ( 𝐹 ) = 𝜔 ( 1 ) . W e will show that, for each connected 𝐻 ⊆ 𝐹 with 𝑣 ( 𝐻 ) ≥ 2 , a.a.s. nc ( 𝐻 , S , 𝑛 , 𝑡 , 𝑏 ) ≤ 𝑒 ( 𝐻 ) ! · 𝛾 𝑒 ( 𝐻 ) · 𝑏 · min { 𝑏 , 𝑛 𝑝 } 𝑣 ( 𝐻 ) − 2 𝑝 𝑒 ( 𝐻 ) − 𝑣 ( 𝐻 ) + 1 (3.1) by induction on the number of edges of 𝐻 . Note that ( 3.1 ) with 𝐻 : = 𝐹 gives precisely the conclusion of the lemma. If 𝐻 consists of a single edge, then nc ( 𝐻 ) ≤ 𝑏 ≤ 𝛾 𝑏 since Builder can claim at most 𝑏 edges. Suppose now that 𝑒 ( 𝐻 ) > 1 and that, for all labelled connected graphs 𝐽 with 1 ≤ 𝑒 ( 𝐽 ) < 𝑒 ( 𝐻 ) , we have that a.a.s. nc ( 𝐽 , S , 𝑛 , 𝑡 , 𝑏 ) ≤ 𝑒 ( 𝐽 ) ! · 𝛾 𝑒 ( 𝐽 ) · 𝑏 · min { 𝑏 , 𝑛 𝑝 } 𝑣 ( 𝐽 ) − 2 𝑝 𝑒 ( 𝐽 ) − 𝑣 ( 𝐽 ) + 1 . (3.2) F or each edge 𝑒 ∈ 𝐸 ( 𝐻 ) , we are going to bound the number nc ( 𝐻 , 𝑒 ) . Fix an edg e 𝑒 ∈ 𝐸 ( 𝐻 ) . W e can distinguish three dierent cases. Case 1. Suppose 𝑒 is a pendant edge, that is, we ha ve 𝑒 = 𝑢𝑣 with 𝑑 𝐻 ( 𝑣 ) = 1 . Let 𝐽 : = 𝐻 − 𝑣 , and note that 𝐽 is a connected graph. F or each copy of 𝐽 , there are at most 𝑏 wa ys for Builder to extend it to a copy of 𝐻 , so nc ( 𝐻 , 𝑒 ) ≤ 𝑏 · nc ( 𝐽 ) . (3.3) On the other hand, at each step 𝑖 ≤ 𝑡 of the random graph process, conditioned on ( 𝐺 0 , . . . , 𝐺 𝑖 − 1 ) , the expected value of the number 𝑋 𝑖 of copies of 𝐻 completed by the edge oered at time 𝑖 and such that it plays the role of 𝑒 in them is 𝔼 [ 𝑋 𝑖 ] ≤ nc ( 𝐽 , S , 𝑛 , 𝑡 , 𝑏 ) 𝑛 𝑀 − 𝑖 + 1 ≤ 2 𝑛 · nc ( 𝐽 ) 𝑀 , where we used that 𝑡 ≤ 𝑀 / 2 and that at most 𝑛 of the 𝑀 − 𝑖 + 1 remaining edges would complete a given copy of 𝐽 to a copy of 𝐻 . Since nc ( 𝐻 , 𝑒 ) ≤ Í 𝑡 𝑖 = 1 𝑋 𝑖 , we conclude that 𝔼 [ nc ( 𝐻 , 𝑒 ) ] ≤ 2 𝑛 · 𝑡 nc ( 𝐽 ) / 𝑀 = 2 𝑛 · nc ( 𝐽 ) · 𝑝 . By Markov ’ s inequality , it follows that ℙ [ nc ( 𝐻 , 𝑒 ) ≥ 𝛾 nc ( 𝐽 ) · 𝑛 𝑝 ] ≤ 2 / 𝛾 = 𝑜 ( 1 ) . (3.4) Combining ( 3.3 ) and ( 3.4 ) and using ( 3.2 ), we thus have that a.a.s. nc ( 𝐻 , 𝑒 ) ≤ 𝛾 · nc ( 𝐽 ) · min { 𝑏 , 𝑛 𝑝 } ≤ 𝛾 · 𝑒 ( 𝐽 ) ! · 𝛾 𝑒 ( 𝐽 ) · 𝑏 · min { 𝑏 , 𝑛 𝑝 } 𝑣 ( 𝐽 ) − 2 𝑝 𝑒 ( 𝐽 ) − 𝑣 ( 𝐽 ) + 1 · min { 𝑏 , 𝑛 𝑝 } = 𝑒 ( 𝐻 ) − 1 ! · 𝛾 𝑒 ( 𝐻 ) · 𝑏 · min { 𝑏 , 𝑛 𝑝 } 𝑣 ( 𝐻 ) − 2 𝑝 𝑒 ( 𝐻 ) − 𝑣 ( 𝐻 ) + 1 . (3.5) Case 2. Suppose 𝑒 is a cut-edge, but not a pendant edge. Then 𝐻 \ { 𝑒 } consists of two connected components, each containing at least one edge; we denote these components as 𝐽 1 and 𝐽 2 . As 𝑏 ≤ 𝑡 ≤ 𝑛 2 𝑝 , we ha ve that 𝑏 𝑝 ≤ min { 𝑏 2 , ( 𝑛𝑝 ) 2 } . By a similar argument as in the previous case, since each copy of 𝐻 in 𝐺 𝑡 completed by an edge corresponding to 𝑒 must be obtained from one copy of 𝐽 1 and one copy of 𝐽 2 , we hav e that 𝔼 [ nc ( 𝐻 , 𝑒 ) ] ≤ 2 𝑡 nc ( 𝐽 1 ) · nc ( 𝐽 2 ) 𝑀 = 2 nc ( 𝐽 1 ) · nc ( 𝐽 2 ) · 𝑝 . Therefore, by Markov’ s inequality and ( 3.2 ), a.a.s. nc ( 𝐻 , 𝑒 ) ≤ 𝛾 · nc ( 𝐽 1 ) · nc ( 𝐽 2 ) · 𝑝 ≤ 𝛾 · 𝑒 ( 𝐽 1 ) ! · 𝑒 ( 𝐽 2 ) ! · 𝛾 𝑒 ( 𝐽 1 ) + 𝑒 ( 𝐽 2 ) · 𝑏 2 · min { 𝑏 , 𝑛 𝑝 } 𝑣 ( 𝐽 1 ) + 𝑣 ( 𝐽 2 ) − 4 𝑝 𝑒 ( 𝐽 1 ) + 𝑒 ( 𝐽 2 ) − 𝑣 ( 𝐽 1 ) − 𝑣 ( 𝐽 2 ) + 3 ≤ 𝑒 ( 𝐻 ) − 1 ! · 𝛾 𝑒 ( 𝐻 ) · 𝑏 2 · min { 𝑏 , 𝑛 𝑝 } 𝑣 ( 𝐻 ) − 4 𝑝 𝑒 ( 𝐻 ) − 𝑣 ( 𝐻 ) + 2 ≤ 𝑒 ( 𝐻 ) − 1 ! · 𝛾 𝑒 ( 𝐻 ) · 𝑏 · min { 𝑏 , 𝑛 𝑝 } 𝑣 ( 𝐻 ) − 2 𝑝 𝑒 ( 𝐻 ) − 𝑣 ( 𝐻 ) + 1 . (3.6) Case 3. Suppose 𝑒 is not a cut-edge and let 𝐽 : = 𝐻 \ { 𝑒 } . In this case, as each copy of 𝐻 completed by an edge corresponding to 𝑒 may only arise from some copy of 𝐽 , by a similar argument as in the ON CONSTR UCTING SMALL SUBGRAPHS IN THE BUDGET -CONSTRAINED RANDOM GRAPH PROCESS 9 previous two cases we have that 𝔼 [ nc ( 𝐻 , 𝑒 ) ] ≤ 2 𝑡 nc ( 𝐽 ) 𝑀 = 2 nc ( 𝐽 ) · 𝑝 . Thus, by Markov’ s inequality and ( 3.2 ), a.a.s. nc ( 𝐻 , 𝑒 ) ≤ 𝛾 · nc ( 𝐽 ) · 𝑝 ≤ 𝛾 · 𝑒 ( 𝐽 ) ! · 𝛾 𝑒 ( 𝐽 ) · 𝑏 · min { 𝑏 , 𝑛 𝑝 } 𝑣 ( 𝐽 ) − 2 𝑝 𝑒 ( 𝐽 ) − 𝑣 ( 𝐽 ) + 2 = 𝑒 ( 𝐻 ) − 1 ! · 𝛾 𝑒 ( 𝐻 ) · 𝑏 · min { 𝑏 , 𝑛 𝑝 } 𝑣 ( 𝐻 ) − 2 𝑝 𝑒 ( 𝐻 ) − 𝑣 ( 𝐻 ) + 1 . (3.7) Now , the desired upper bound ( 3.1 ) on nc ( 𝐻 , S , 𝑛 , 𝑡 , 𝑏 ) follows from ( 3.5 ) , ( 3.6 ) and ( 3.7 ) by summing over all possible options for 𝑒 ∈ 𝐸 ( 𝐻 ) . □ Theorem 3.1 can be used to obtain a lower bound on the minimum budget required for constructing copies of any xed (not necessarily connected) graph 𝐹 , by simply verifying under which conditions for 𝑏 we can guarantee that a.a.s. nc ( 𝐹 , S , 𝑛 , 𝑡 , 𝑏 ) = 𝑜 ( 1 ) for every ( 𝑡 , 𝑏 ) -strategy S , which implies that a.a.s. there are no copies of 𝐹 . W e believe this lower bound is far from optimal in g eneral, but it is optimal when considering wheels. Corollary 3.2. Let 𝑘 ≥ 4 be an integer . F or all 𝑡 ∈ [ 𝑀 ] , if 𝑡 = 𝑜 𝑛 3 2 − 1 2 ( 𝑘 − 1 ) or 𝑏 = 𝑜 max 𝑛 3 𝑘 − 4 𝑡 2 𝑘 − 3 , 𝑛 2 𝑡 , then for any ( 𝑡 , 𝑏 ) -strategy a.a.s. 𝐵 𝑡 does not contain a copy of 𝑊 𝑘 . Proof . Let 𝑝 : = 𝑡 / 𝑀 . If 𝑡 = 𝑜 ( 𝑛 3 / 2 − 1 / 2 ( 𝑘 − 1 ) ) , then a standard application of the rst moment method shows that a.a.s. 𝐺 𝑡 does not contain a copy of 𝑊 𝑘 , and so neither does 𝐵 𝑡 . Thus, assume that 𝑡 = Ω ( 𝑛 3 / 2 − 1 / 2 ( 𝑘 − 1 ) ) and let S be a ( 𝑡 , 𝑏 ) -strategy . By Theorem 3.1 , for any arbitrarily slowly growing function 𝜂 = 𝜔 ( 1 ) we have that a.a.s. nc ( 𝑊 𝑘 ) = nc ( 𝑊 𝑘 , S , 𝑛 , 𝑡 , 𝑏 ) ≤ 𝜂 · 𝑏 · min { 𝑏 , 𝑛 𝑝 } 𝑘 − 2 𝑝 𝑘 − 1 . Note that 𝑛 3 𝑘 − 4 𝑡 2 𝑘 − 3 = 𝑛 2 𝑡 ⇐ ⇒ 𝑡 = 𝑛 3 / 2 . When 𝑡 = 𝑂 ( 𝑛 3 / 2 ) we have that 𝑛 3 𝑘 − 4 / 𝑡 2 𝑘 − 3 = Ω ( 𝑛 2 / 𝑡 ) . F or any 𝑏 = 𝑜 ( 𝑛 3 𝑘 − 4 / 𝑡 2 𝑘 − 3 ) , choose some 𝜂 = 𝜔 ( 1 ) with 𝜂 = 𝑜 ( 1 / 𝑏 𝑛 𝑘 − 2 𝑝 2 𝑘 − 3 ) (which exists as 𝑛 3 𝑘 − 4 / 𝑡 2 𝑘 − 3 = Θ ( 1 / 𝑛 𝑘 − 2 𝑝 2 𝑘 − 3 ) ). W e then conclude that a.a.s. nc ( 𝑊 𝑘 ) ≤ 𝜂 · 𝑏 𝑛 𝑘 − 2 𝑝 2 𝑘 − 3 = 𝑜 ( 1 ) < 1 . If instead 𝑡 = 𝜔 ( 𝑛 3 / 2 ) , then 𝑛 2 / 𝑡 = 𝜔 ( 𝑛 3 𝑘 − 4 / 𝑡 2 𝑘 − 3 ) . Similarly as above, for any 𝑏 = 𝑜 ( 𝑛 2 / 𝑡 ) = 𝑜 ( 1 / 𝑝 ) , we choose some 𝜂 = 𝜔 ( 1 ) with 𝜂 = 𝑜 ( 1 / 𝑏 𝑘 − 1 𝑝 𝑘 − 1 ) . W e conclude that a.a.s. nc ( 𝑊 𝑘 ) ≤ 𝜂 · 𝑏 𝑘 − 1 𝑝 𝑘 − 1 = 𝑜 ( 1 ) < 1 . □ While we do not believe that we can obtain results which are tight in general with our approach, it is instructive to see other applications. Here, for simplicity , we write the result for cliques. W e remark that the case 𝑟 = 3 recovers the tight bound for constructing a triangle given by Frieze, Krivelevich and Michaeli [ 3 ] , and the case 𝑟 = 4 gives a tight lower bound for the 0 - statement in the case 𝑘 = 4 of Theorem 1.1 . The special cases 𝑟 ∈ { 3 , 4 , 5 } of this result are depicted in Figure 2 . Corollary 3.3. Let 𝑟 ≥ 3 be an integer . F or all 𝑡 ∈ [ 𝑀 ] , if 𝑡 = 𝑜 𝑛 2 − 2 𝑟 − 1 or 𝑏 = 𝑜 max ( 𝑛 𝑟 ( 𝑟 − 2 ) 𝑡 ( 𝑟 2 ) − 1 , 𝑛 2 𝑡 ( 𝑟 − 2 ) / 2 ) ! , then for any ( 𝑡 , 𝑏 ) -strategy a.a.s. 𝐵 𝑡 does not contain a copy of 𝐾 𝑟 . 10 S. ANTONIUK, A. ESPUNY DÍAZ, K. PETRO V A, AND M. STOJAK OVIĆ Proof . Let 𝑝 : = 𝑡 / 𝑀 . If 𝑡 = 𝑜 ( 𝑛 2 − 2 / ( 𝑟 − 1 ) ) , then a standard application of the rst moment method shows that a.a.s. 𝐺 𝑡 does not contain a copy of 𝐾 𝑟 , and thus neither does 𝐵 𝑡 . Therefore, assume that 𝑡 = Ω ( 𝑛 2 − 2 / ( 𝑟 − 1 ) ) and let S be a ( 𝑡 , 𝑏 ) -strategy . By Theorem 3.1 , for any arbitrarily slowly growing function 𝜂 = 𝜔 ( 1 ) we have that a.a.s. nc ( 𝐾 𝑟 ) = nc ( 𝐾 𝑟 , S , 𝑛 , 𝑡 , 𝑏 ) ≤ 𝜂 · 𝑏 · min { 𝑏 , 𝑛 𝑝 } 𝑟 − 2 𝑝 ( 𝑟 2 ) − 𝑟 + 1 . Observe that 𝑛 𝑟 ( 𝑟 − 2 ) 𝑡 ( 𝑟 2 ) − 1 = 𝑛 2 𝑡 ( 𝑟 − 2 ) / 2 ⇐ ⇒ 𝑡 = 𝑛 2 − 2 / 𝑟 . When 𝑡 = 𝑂 ( 𝑛 2 − 2 / 𝑟 ) we ha ve that 𝑛 𝑟 ( 𝑟 − 2 ) / 𝑡 ( 𝑟 2 ) − 1 = Ω ( ( 𝑛 2 / 𝑡 ) ( 𝑟 − 2 ) / 2 ) . F or any 𝑏 = 𝑜 ( 𝑛 𝑟 ( 𝑟 − 2 ) / 𝑡 ( 𝑟 2 ) − 1 ) , choose some 𝜂 = 𝜔 ( 1 ) with 𝜂 = 𝑜 ( 1 / 𝑏 𝑛 𝑟 − 2 𝑝 ( 𝑟 2 ) − 1 ) (which exists as 𝑛 𝑟 ( 𝑟 − 2 ) / 𝑡 ( 𝑟 2 ) − 1 = Θ ( 1 / 𝑛 𝑟 − 2 𝑝 ( 𝑟 2 ) − 1 ) ). W e then conclude that a.a.s. nc ( 𝐾 𝑟 ) ≤ 𝜂 · 𝑏 𝑛 𝑟 − 2 𝑝 ( 𝑟 2 ) − 1 = 𝑜 ( 1 ) < 1 . If instead 𝑡 = 𝜔 ( 𝑛 2 − 2 / 𝑟 ) , then ( 𝑛 2 / 𝑡 ) ( 𝑟 − 2 ) / 2 = 𝜔 ( 𝑛 𝑟 ( 𝑟 − 2 ) / 𝑡 ( 𝑟 2 ) − 1 ) . Proceeding similarly as above, for any 𝑏 = 𝑜 ( ( 𝑛 2 / 𝑡 ) ( 𝑟 − 2 ) / 2 ) = 𝑜 ( 𝑝 − ( 𝑟 − 2 ) / 2 ) , take 𝜂 = 𝜔 ( 1 ) with 𝜂 = 𝑜 ( 1 / 𝑏 𝑟 − 1 𝑝 ( 𝑟 2 ) − 𝑟 + 1 ) . W e conclude that a.a.s. nc ( 𝐾 𝑟 ) ≤ 𝜂 · 𝑏 𝑟 − 1 𝑝 ( 𝑟 2 ) − 𝑟 + 1 = 𝑜 ( 1 ) < 1 . □ W e end this section with a lemma that is not strictly needed for our results, but could be of independent interest as a tool for proving lower bounds in future work. Given a xed graph 𝐹 and some integer 𝑘 ∈ { 0 , 1 , . . . , 𝑒 ( 𝐹 ) } , it allows us to bound the probability that Builder can construct a copy of 𝐹 in terms of the number of copies of all subgraphs of 𝐹 on 𝑘 edges that she can build. The lemma can be seen as a formalisation and generalisation of the ideas in the lower bound proofs of Iľkovič, León and Shu [ 4 ] , in that one counts the number of some ‘intermediate’ subgraphs 𝐻 , which form ‘traps’ , and then estimates the probability that any of these traps is completed to a copy of the target graph 𝐹 . F or any (not necessarily connected) labelled graph 𝐻 , any ˜ 𝑝 ∈ ( 0 , 1 ] , and any non-negative integers 𝑛 , 𝑡 , and 𝑏 , let 𝑓 ( 𝐻 , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) denote the minimum integer ˜ 𝑓 such that, for any ( 𝑡 , 𝑏 ) -strategy S , the probability that the budget-constr ained random graph process on [ 𝑛 ] under S contains more than ˜ 𝑓 copies of 𝐻 is at most ˜ 𝑝 . Lemma 3.4. Let 𝐹 be a xed labelled graph. F or any 𝑡 = 𝑡 ( 𝑛 ) ∈ [ 𝑀 ] and 𝑏 = 𝑏 ( 𝑛 ) ∈ [ 𝑡 ] , let 𝑝 : = 𝑡 / 𝑀 , let S be a ( 𝑡 , 𝑏 ) -strategy , and let E 𝐹 be the event that, when considering the budget-constrained random graph process under S , the resulting graph 𝐵 𝑡 contains a copy of 𝐹 . Then, for any integer 𝑘 ∈ { 0 , 1 , . . . , 𝑒 ( 𝐹 ) } and any ˜ 𝑝 = ˜ 𝑝 ( 𝑛 ) ∈ ( 0 , 1 ] , we have that ℙ [ E 𝐹 ] = 𝑂 𝐻 ⊆ 𝐹 , 𝑒 ( 𝐻 ) = 𝑘 , 𝛿 ( 𝐻 ) ≥ 1 𝑓 ( 𝐻 , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) 𝑛 𝑣 ( 𝐹 ) − 𝑣 ( 𝐻 ) 𝑝 𝑒 ( 𝐹 ) − 𝑘 ! + 𝑂 ( ˜ 𝑝 ) . (3.8) This lemma can be useful whenever there is some 𝑘 for which we ha ve some good ‘with high probability’ bounds on the number of copies of 𝑘 -edge subgraphs of 𝐹 that Builder can build. There is a clear trade-o between 𝑓 ( 𝐻 , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) and ˜ 𝑝 , the probability of the ‘bad’ event that Builder can build many copies of some 𝑘 -edge subgraph 𝐻 . One possible application of Theorem 3.4 would be to give an alternative proof of the 𝑟 = 4 case of Theorem 3.3 , by making use of Theorem 3.1 to estimate 𝑓 ( 𝐻 , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) for some ˜ 𝑝 = 𝑜 ( 1 ) and for all 𝐻 ⊆ 𝐾 4 with 𝑒 ( 𝐻 ) = 4 . It is conceivable that, for some graphs 𝐹 , one can obtain better bounds on 𝑓 ( 𝐻 , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) for subgraphs 𝐻 of 𝐹 than what Theorem 3.1 gives, in which case Theorem 3.4 can give better results than Theorem 3.1 . W e have not been able to nd such graphs 𝐹 , but we prove Lemma 3.4 here in the hopes that it could be useful in future work. ON CONSTR UCTING SMALL SUBGRAPHS IN THE BUDGET -CONSTRAINED RANDOM GRAPH PROCESS 11 Proof of Theorem 3.4 . F or each 𝐻 ⊆ 𝐹 , let F 𝐻 be the event that there are at most 𝑓 ( 𝐻 , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) copies of 𝐻 in 𝐵 𝑡 . Then we ha ve that ℙ [ E 𝐹 ] ≤ ℙ E 𝐹 ∩ Ù 𝐻 ⊆ 𝐹 , 𝑒 ( 𝐻 ) = 𝑘 , 𝛿 ( 𝐻 ) ≥ 1 F 𝐻 + 𝐻 ⊆ 𝐹 , 𝑒 ( 𝐻 ) = 𝑘 , 𝛿 ( 𝐻 ) ≥ 1 ℙ h F 𝐻 i ≤ ℙ E 𝐹 ∩ Ù 𝐻 ⊆ 𝐹 , 𝑒 ( 𝐻 ) = 𝑘 , 𝛿 ( 𝐻 ) ≥ 1 F 𝐻 + 𝑒 ( 𝐹 ) 𝑘 ˜ 𝑝 . Since 𝑒 ( 𝐹 ) is a constant, we have that 𝑒 ( 𝐹 ) 𝑘 ˜ 𝑝 = 𝑂 ( ˜ 𝑝 ) , which accounts for the second term of the upper bound in the statement of the lemma. F or the rest of the proof, we focus on bounding the rst term in the expression above, which amounts to bounding the probability of E 𝐹 while being able to assume ‘for free’ that F 𝐻 holds for all subgraphs 𝐻 of 𝐹 with 𝑘 edges and no isolated vertices. More specically , for each subgraph 𝐻 of 𝐹 with 𝑘 edges and no isolated vertices and for each step 𝑖 of the random graph process, we will consider revealing the rst 𝑖 − 1 steps of the process and ‘rejecting’ the outcome if the graph 𝐺 𝑖 − 1 contains more than 𝑓 ( 𝐻 , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) copies of 𝐻 . Thus, in all outcomes that actually count towar ds our upper bound, we g et to assume there are at most 𝑓 ( 𝐻 , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) copies of 𝐻 in 𝐺 𝑖 − 1 . If 𝑡 > 𝑀 / 2 , the conclusion of the lemma holds trivially , since the rst term of the right -hand side in ( 3.8 ) is either Ω ( 1 ) or 0 . Furthermore, it can only be 0 if 𝑓 ( 𝐻 , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) = 0 for all subgraphs 𝐻 ⊆ 𝐹 with 𝑒 ( 𝐻 ) = 𝑘 and 𝛿 ( 𝐻 ) ≥ 1 and, if that is the case, then indeed no copies of 𝐹 can be built as long as Ñ 𝐻 ⊆ 𝐹 , 𝑒 ( 𝐻 ) = 𝑘 , 𝛿 ( 𝐻 ) ≥ 1 F 𝐻 holds. Hence, from now on we assume that 𝑡 ≤ 𝑀 / 2 . If 𝑘 = 𝑒 ( 𝐹 ) , the result is also trivial for the same reason, so assume that 𝑘 < 𝑒 ( 𝐹 ) . Any copy of 𝐹 that Builder may eventually produce is constructed edg e by edg e. W e argue by a union bound over all possible choices for the rst 𝑘 edges of 𝐹 that Builder can purchase, and all choices for the ( 𝑘 + 1 ) -th edge. Let 𝐻 ⊆ 𝐹 be a subgraph with exactly 𝑘 edges (which will play the role of the rst 𝑘 edges of 𝐹 that Builder purchases) and 𝑒 ∈ 𝐸 ( 𝐹 ) \ 𝐸 ( 𝐻 ) (which will play the role of the the ( 𝑘 + 1 ) -th edge of 𝐹 purchased by Builder). Let 𝐻 ′ be the spanning subgraph of 𝐹 with 𝐸 ( 𝐻 ′ ) = 𝐸 ( 𝐻 ) (note that 𝐻 ′ has 𝑣 ( 𝐹 ) − 𝑣 ( 𝐻 ) isolated vertices). Then note that 𝑓 ( 𝐻 ′ , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) ≤ 𝑓 ( 𝐻 , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) 𝑛 𝑣 ( 𝐹 ) − 𝑣 ( 𝐻 ) . F or each step 𝑖 ∈ [ 𝑡 ] of the random graph process, the number of candidates for copies of 𝐻 ′ ∪ { 𝑒 } in 𝐺 𝑖 such that 𝑒 is embedded into 𝐺 𝑖 \ 𝐺 𝑖 − 1 is at most 𝑓 ( 𝐻 ′ , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) . Conditioned on 𝐺 𝑖 − 1 , each such candidate is present in 𝐺 𝑖 with probability 1 / ( 𝑀 − 𝑖 + 1 ) . The probability that the remaining 𝑒 ( 𝐹 ) − 𝑘 − 1 edges are presented after time 𝑖 and before time 𝑡 + 1 is at most 𝑀 − 𝑖 − ( 𝑒 ( 𝐹 ) − 𝑘 − 1 ) 𝑡 − 𝑖 − ( 𝑒 ( 𝐹 ) − 𝑘 − 1 ) 𝑀 − 𝑖 𝑡 − 𝑖 ≤ 𝑡 − 𝑖 𝑀 − 𝑖 ! 𝑒 ( 𝐹 ) − 𝑘 − 1 ≤ 𝑝 𝑒 ( 𝐹 ) − 𝑘 − 1 . All in all, by the union bound, we conclude that ℙ E 𝐹 ∩ Ù 𝐻 ⊆ 𝐹 𝑒 ( 𝐻 ) = 𝑘 , 𝛿 ( 𝐻 ) ≥ 1 F 𝐻 ≤ 𝐻 ⊆ 𝐹 𝑒 ( 𝐻 ) = 𝑘 , 𝛿 ( 𝐻 ) ≥ 1 𝑒 ∈ 𝐸 ( 𝐹 \ 𝐻 ) 𝑡 𝑖 = 1 𝑓 ( 𝐻 , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) 𝑛 𝑣 ( 𝐹 ) − 𝑣 ( 𝐻 ) 1 𝑀 − 𝑖 + 1 𝑝 𝑒 ( 𝐹 ) − 𝑘 − 1 ≤ 𝐻 ⊆ 𝐹 𝑒 ( 𝐻 ) = 𝑘 , 𝛿 ( 𝐻 ) ≥ 1 𝑒 ( 𝐹 ) · 𝑡 · 𝑓 ( 𝐻 , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) 𝑛 𝑣 ( 𝐹 ) − 𝑣 ( 𝐻 ) 2 𝑀 𝑝 𝑒 ( 𝐹 ) − 𝑘 − 1 ≤ 𝐻 ⊆ 𝐹 𝑒 ( 𝐻 ) = 𝑘 , 𝛿 ( 𝐻 ) ≥ 1 2 𝑒 ( 𝐹 ) 𝑓 ( 𝐻 , 𝑛 , 𝑡 , 𝑏 , ˜ 𝑝 ) 𝑛 𝑣 ( 𝐹 ) − 𝑣 ( 𝐻 ) 𝑝 𝑒 ( 𝐹 ) − 𝑘 , as desired. □ 12 S. ANTONIUK, A. ESPUNY DÍAZ, K. PETRO V A, AND M. STOJAK OVIĆ 4. Upper bounds In this section, we provide the proofs for the 1 - statements of our theorems. In other words, we want to show that, if the budget is suciently large (as a function of 𝑡 and 𝑛 ), then there exist successful ( 𝑡 , 𝑏 ) -strategies for containing dierent subgraphs. W e begin by considering wheels. Theorem 4.1. Let 𝑘 ≥ 4 be a xed integer . If 𝑀 ≥ 𝑡 ≥ 𝑏 = 𝜔 max 𝑛 3 𝑘 − 4 𝑡 2 𝑘 − 3 , 𝑛 2 𝑡 , there exists a successful ( 𝑡 , 𝑏 ) - strategy for constructing a copy of 𝑊 𝑘 . Our proof of Theorem 4.1 is split into two cases, depending on whether 𝑡 = 𝑂 ( 𝑛 3 / 2 ) or 𝑡 = 𝜔 ( 𝑛 3 / 2 ) . The strategies for constructing wheels 𝑊 𝑘 for 𝑘 ≥ 4 are rather simple. It is useful to consider the intuition that the random graph process can be split into a number of segments, each of them behaving roughly like a binomial random graph of the appropriate density , as formalised in Theorem 2.3 . When 𝑡 = 𝑂 ( 𝑛 3 / 2 ) , the idea is to rst construct a set of stars, each as large as possible, of an appropriate size. The centres of these stars would play the role of the single vertex of higher degree in 𝑊 𝑘 . Then, in the second round of exposure, one adds all edg es contained in any of the sets of leav es of a star . If this second round of exposure creates a cycle of length 𝑘 − 1 within the set of lea ves of some star , this cycle together with the star it is contained in forms a copy of 𝑊 𝑘 . W e formalise all the details for this strategy below . When 𝑡 = 𝜔 ( 𝑛 3 / 2 ) , the strategy has more levels of “depth ” depending on the value of 𝑘 . Let us illustrate this for the particular case 𝑘 = 4 . W e x a single vertex 𝑥 and, in the rst stage, construct a star with 𝑥 at its centre. Let us denote the set of lea ves of this star by 𝑆 . In the second round of exposure, we x a subset 𝑌 ⊆ 𝑆 of an appropriate size, and purchase all edges contained in 𝑆 which are incident to some vertex in 𝑌 . This leads to sets 𝑆 1 , . . . , 𝑆 | 𝑌 | , denoting the neighbours in 𝑆 of vertices of 𝑌 , respectively , at the end of this second round. In the nal round of exposure, it suces to purchase a single edge contained in one of the sets 𝑆 𝑖 to complete a 𝐾 4 . T o simplify our strategy , we can summarise it as follows: rst, we grow a star centred at 𝑥 , and then we apply an optimal strategy for constructing a triangle within the neighbourhood of 𝑥 . F or general 𝑘 ≥ 4 , the summary is the same: we rst grow a star centred at 𝑥 and then apply an optimal strategy for constructing a cycle of length 𝑘 − 1 within the neighbourhood of 𝑥 . As such strategies for cycles ha ve already been studied, our analysis will be greatly simplied by using the following result. Lemma 4.2 (Frieze, Krivelevich and Michaeli [ 3 , Theorem 1.6 ] ) . Let 𝑘 ≥ 4 be a xed integer . F or all 𝑡 = 𝜔 ( 𝑛 ) with 𝑡 ≤ 𝑀 , if 𝑏 = 𝜔 max 𝑛 ⌊ 𝑘 / 2 ⌋ + 1 𝑡 ⌊ 𝑘 / 2 ⌋ , 𝑛 𝑡 1 / 2 , there exists a successful ( 𝑡 , 𝑏 ) - strategy for constructing a copy of 𝐶 𝑘 − 1 . Proof of Theorem 4.1 . Fix an arbitrary 𝑘 ≥ 4 . F ollowing the statement, we may assume throughout that 𝑀 ≥ 𝑡 = 𝜔 ( 𝑛 ( 3 𝑘 − 4 ) / ( 2 𝑘 − 2 ) ) = 𝜔 ( 𝑛 3 / 2 − 1 / ( 2 𝑘 − 2 ) ) . W e split our proof into two cases, depending on the range of 𝑡 that we consider . Case 1. Assume rst that 𝑡 = 𝑂 ( 𝑛 3 / 2 ) . Note that in this range we have 𝑏 = 𝜔 ( 𝑛 3 𝑘 − 4 / 𝑡 2 𝑘 − 3 ) . Fix any such 𝑏 and let 𝑟 = 𝑟 ( 𝑛 ) be such that 𝑟 = 𝑜 ( 𝑡 ) but it is suciently close to 𝑡 that 𝑛 3 𝑘 − 4 𝑡 𝑟 2 𝑘 − 2 = 𝑜 ( 𝑏 ) . (4.1) Then, consider the strategy outlined in Strategy 1 below . This is a ( 𝑡 , 𝑏 ) -strategy by construction, so it only remains to prove that it is successful for constructing a copy of 𝑊 𝑘 . W e note that, by the assumption that 𝑏 ≤ 𝑡 , ( 4.1 ) implies that 𝑟 = 𝜔 ( 𝑛 ( 3 𝑘 − 4 ) / ( 2 𝑘 − 2 ) ) = 𝜔 ( 𝑛 3 / 2 − 1 / ( 2 𝑘 − 2 ) ) . This in turn implies that | 𝑋 | = ⌈ 𝑛 3 𝑘 − 3 / 𝑟 2 𝑘 − 2 ⌉ = 𝑜 ( 𝑛 ) . ON CONSTR UCTING SMALL SUBGRAPHS IN THE BUDGET -CONSTRAINED RANDOM GRAPH PROCESS 13 Strategy 1. A ( 𝑡 , 𝑏 ) -strategy for 𝑊 𝑘 for 𝑡 = 𝑂 ( 𝑛 3 / 2 ) . 0: Set 𝑋 : = [ ⌈ 𝑛 3 𝑘 − 3 / 𝑟 2 𝑘 − 2 ⌉ ] and 𝑉 : = [ 𝑛 ] \ 𝑋 . 1: F or time 𝑡 / 2 and while the built graph has at most 𝑏 / 2 edges, buy any presented edge with one endpoint in 𝑋 and the other in 𝑉 . 2: F or time 𝑡 / 2 and while the built graph has at most 𝑏 edges, buy an y presented edge which is contained in 𝑁 𝐵 𝑡 / 2 ( 𝑥 ) for at least one 𝑥 ∈ 𝑋 . Let ˆ 𝐺 1 and ˆ 𝐺 2 denote the (random) graphs containing all the edges oered during stages 1 and 2 , respectively . Consider the coupling of the random graph process given by Theorem 2.3 applied with 𝑘 = 2 and 𝑡 1 = 𝑡 2 = 𝑡 / 2 . More precisely , there exist some 𝑝 1 = ( 1 − 𝑜 ( 1 ) ) 𝑡 1 / 𝑀 , 𝑝 2 = ( 1 − 𝑜 ( 1 ) ) 𝑡 2 / 𝑀 , 𝑝 ′ 1 = ( 1 + 𝑜 ( 1 ) ) 𝑡 1 / 𝑀 and 𝑝 ′ 2 = ( 1 + 𝑜 ( 1 ) ) 𝑡 2 / 𝑀 , and a coupling of random graphs ( 𝐻 1 , ˆ 𝐺 1 , 𝐻 ′ 1 , 𝐻 2 , ˆ 𝐺 2 , 𝐻 ′ 2 ) , such that 𝐻 𝑖 ∼ 𝐺 ( 𝑛 , 𝑝 𝑖 ) and 𝐻 ′ 𝑖 ∼ 𝐺 ( 𝑛 , 𝑝 ′ 𝑖 ) for each 𝑖 ∈ [ 2 ] (where 𝐻 ′ 𝑖 corres- ponds to the union 𝐻 𝑖 ∪ 𝐻 𝑖 in Theorem 2.3 ), ( 𝐻 1 , 𝐻 ′ 1 ) is independent of ( 𝐻 2 , 𝐻 ′ 2 ) , 𝐻 ′ 2 is independent of ˆ 𝐺 1 , and a.a.s. 𝐻 1 ⊆ ˆ 𝐺 1 ⊆ 𝐻 ′ 1 (4.2) and 𝐻 2 \ 𝐻 ′ 1 ⊆ ˆ 𝐺 2 ⊆ 𝐻 ′ 2 . (4.3) Note, moreover , that if we are to restrict our random graphs to disjoint subsets of edg es 𝐸 1 , 𝐸 2 ⊆ [ 𝑛 ] 2 , we obtain one further independence property: the appearance of each edge in ( 𝐻 2 \ 𝐻 ′ 1 ) ∩ 𝐸 2 is independent of ( 𝐻 1 ∩ 𝐸 1 , 𝐻 ′ 1 ∩ 𝐸 1 ) (even if 𝐸 2 is allowed to depend on ( 𝐻 1 ∩ 𝐸 1 , 𝐻 ′ 1 ∩ 𝐸 1 ) ). Let ˆ 𝐵 1 and ˆ 𝐵 2 be the graphs containing all edges purchased during stages 1 and 2 , respectively . Let 𝐸 1 : = { { 𝑥 , 𝑣 } : 𝑥 ∈ 𝑋 , 𝑣 ∈ 𝑉 } ⊆ [ 𝑛 ] 2 , and observe that ˆ 𝐵 1 ⊆ ˆ 𝐺 1 ∩ 𝐸 1 . A t the end of Stage 1 , let 𝐸 2 : = Ð 𝑥 ∈ 𝑋 𝑁 ˆ 𝐵 1 ( 𝑥 ) 2 ⊆ [ 𝑛 ] 2 , and note that ˆ 𝐵 2 ⊆ ˆ 𝐺 2 ∩ 𝐸 2 and 𝐸 1 ∩ 𝐸 2 = ∅ (so we can make use of the independence mentioned above). W e are rst going to show that, in fact, a.a.s. ˆ 𝐵 1 = ˆ 𝐺 1 ∩ 𝐸 1 . (4.4) Indeed, this will hold if during Stag e 1 we never purchase 𝑏 / 2 edg es. Note that, for any 𝑥 ∈ 𝑋 , since we have that 𝔼 [ 𝑒 𝐻 ′ 1 ( 𝑥 , 𝑉 ) ] = ( 1 ± 𝑜 ( 1 ) ) 𝑡 / 𝑛 , by Theorem 2.1 and the lower bound on 𝑡 it follows that ℙ [ 𝑒 𝐻 ′ 1 ( 𝑥 , 𝑉 ) ≥ 2 𝑡 / 𝑛 ] = e − Ω ( 𝑡 / 𝑛 ) = e − 𝜔 ( 𝑛 1 / 2 − 1 / ( 2 𝑘 − 2 ) ) . Similarly , ℙ [ 𝑒 𝐻 1 ( 𝑥 , 𝑉 ) ≤ 𝑡 / 2 𝑛 ] = e − 𝜔 ( 𝑛 1 / 2 − 1 / ( 2 𝑘 − 2 ) ) , as 𝔼 [ 𝑒 𝐻 1 ( 𝑥 , 𝑉 ) ] = ( 1 − 𝑜 ( 1 ) ) 𝑡 / 𝑛 . By a union bound over all 𝑥 ∈ 𝑋 and ( 4.2 ) , we conclude that a.a.s. for all 𝑥 ∈ 𝑋 we have that 𝑡 2 𝑛 ≤ 𝑒 𝐻 1 ( 𝑥 , 𝑉 ) ≤ 𝑒 𝐻 ′ 1 ( 𝑥 , 𝑉 ) ≤ 2 𝑡 𝑛 , (4.5) and together with ( 4.2 ) it follows that a.a.s. for every 𝑥 ∈ 𝑋 we hav e that 𝑒 ˆ 𝐺 1 ( 𝑥 , 𝑉 ) ≤ 2 𝑡 𝑛 . (4.6) In particular , by the upper bound on 𝑡 and ( 4.1 ), a.a.s. 𝑒 ˆ 𝐺 1 ( 𝑋 , 𝑉 ) ≤ | 𝑋 | 2 𝑡 𝑛 ≤ 4 𝑛 3 𝑘 − 4 𝑡 𝑟 2 𝑘 − 2 = 𝑜 ( 𝑏 ) , so ( 4.4 ) holds. W e next claim that a.a.s. ˆ 𝐵 2 = ˆ 𝐺 2 ∩ 𝐸 2 . (4.7) This holds if during Stage 2 we never purchase 𝑏 / 2 edges. Indeed, suppose that ( 4.6 ) holds (which occurs a.a.s.). Then, by the upper bound on 𝑡 , we have that | 𝐸 2 | ≤ | 𝑋 | 2 𝑡 / 𝑛 2 ≤ 4 𝑛 3 𝑘 − 5 𝑡 2 / 𝑟 2 𝑘 − 2 . It 14 S. ANTONIUK, A. ESPUNY DÍAZ, K. PETRO V A, AND M. STOJAK OVIĆ follows that 𝔼 [ | 𝐸 ( 𝐻 ′ 2 ) ∩ 𝐸 2 | ] ≤ 6 𝑛 3 𝑘 − 7 𝑡 3 / 𝑟 2 𝑘 − 2 for suciently large 𝑛 . Since 𝐻 ′ 2 is independent of ˆ 𝐺 1 , by Theorem 2.1 we ha ve that ℙ | 𝐸 ( 𝐻 ′ 2 ) ∩ 𝐸 2 | ≥ 8 𝑛 3 𝑘 − 7 𝑡 3 𝑟 2 𝑘 − 2 ≤ exp − Ω 𝑛 3 𝑘 − 7 𝑡 3 𝑟 2 𝑘 − 2 = e − Ω ( 𝑛 1 / 2 ) = 𝑜 ( 1 ) , where the second comparison holds since 𝑟 2 𝑘 − 2 / 𝑡 3 = 𝑜 ( 𝑡 2 𝑘 − 5 ) = 𝑜 ( 𝑛 3 𝑘 − 15 / 2 ) by the upper bounds on 𝑟 and 𝑡 , respectively . Lastly , note that, by the upper bound on 𝑡 , ( 4.1 ) implies that 𝑛 3 𝑘 − 7 𝑡 3 𝑟 2 𝑘 − 2 = 𝑡 2 𝑛 3 𝑛 3 𝑘 − 4 𝑡 𝑟 2 𝑘 − 2 = 𝑜 ( 𝑏 ) , and thus a.a.s. | 𝐸 ( 𝐻 ′ 2 ) ∩ 𝐸 2 | = 𝑜 ( 𝑏 ) , so ( 4.7 ) follows by ( 4.3 ). Combining ( 4.2 ) with ( 4.4 ) and ( 4.3 ) with ( 4.7 ) , respectively , we deduce that a.a.s. 𝐻 1 ∩ 𝐸 1 ⊆ ˆ 𝐵 1 and ( 𝐻 2 \ 𝐻 ′ 1 ) ∩ 𝐸 2 ⊆ ˆ 𝐵 2 . In order to conclude that the strategy is successful, it thus suces to verify that a.a.s. ( 𝐻 1 ∩ 𝐸 1 ) ∪ ( ( 𝐻 2 \ 𝐻 ′ 1 ) ∩ 𝐸 2 ) contains a copy of 𝑊 𝑘 . F or this, we may rst expose 𝐹 1 : = 𝐻 1 ∩ 𝐸 1 , and note that the bounds in ( 4.5 ) hold a.a.s. Next, let 𝐸 ∗ 2 : = Ð 𝑥 ∈ 𝑋 𝑁 𝐹 1 ( 𝑥 ) 2 , and note that a.a.s. 𝐸 ∗ 2 ⊆ 𝐸 2 by ( 4.2 ) . W e next expose 𝐹 2 : = ( 𝐻 2 \ 𝐻 ′ 1 ) ∩ 𝐸 ∗ 2 (where each edge of 𝐸 ∗ 2 is retained independently with some probability 𝑝 ∗ = ( 1 − 𝑜 ( 1 ) ) 𝑡 / 𝑛 2 ). Note that, if for some 𝑥 ∈ 𝑋 the graph 𝐹 2 ∩ 𝑁 𝐹 1 ( 𝑥 ) 2 contains a cycle of length 𝑘 − 1 , then 𝐹 1 ∪ 𝐹 2 contains a copy of 𝑊 𝑘 , so it suces to prove that the former holds a.a.s. In order to prove this, we rst claim that, for every xed integer ℓ ≥ 3 , a.a.s. ( CN ℓ ) every ℓ -set of vertices in 𝑉 ℓ is contained in the 𝐹 1 -neighbourhood of at most ve vertices 𝑥 ∈ 𝑋 . Indeed, recall that, by the assumption that 𝑏 ≤ 𝑡 , ( 4.1 ) implies that 𝑟 = 𝜔 ( 𝑛 ( 3 𝑘 − 4 ) / ( 2 𝑘 − 2 ) ) . Now , for a xed 𝑈 ∈ 𝑉 ℓ , using the upper bound on 𝑡 and this lower bound on 𝑟 , the probability that 𝑈 is contained in the 𝐹 1 -neighbourhood of at least six vertices 𝑥 ∈ 𝑋 is at most | 𝑋 | 6 ( 𝑝 1 ) 6 ℓ = Θ 𝑛 3 𝑘 − 3 𝑟 2 𝑘 − 2 𝑡 ℓ 𝑛 2 ℓ 6 ! = 𝑜 𝑛 1 − ℓ / 2 6 = 𝑜 ( 𝑛 − ℓ ) , and the conclusion follows by a union bound over all ℓ -sets in 𝑉 ℓ . In a similar fashion, we claim that a.a.s. ( CN2 ) every pair of vertices in 𝑉 2 is contained in the 𝐹 1 -neighbourhood of at most 4 𝑘 vertices 𝑥 ∈ 𝑋 . T o show this, x an arbitrary pair of vertices 𝑈 ∈ 𝑉 2 . W e now further split our range for 𝑡 into two. Assume rst that 𝑡 = 𝑂 ( 𝑛 3 / 2 − 1 / ( 4 𝑘 − 4 ) ) . Combining this with ( 4.1 ) and the assumption that 𝑏 ≤ 𝑡 , with calculations analogous to those for proving ( CN ℓ ) , we conclude that the probability that 𝑈 is contained in the 𝐹 1 -neighbourhood of at least 4 𝑘 vertices is at most | 𝑋 | 4 𝑘 ( 𝑝 1 ) 8 𝑘 = Θ 𝑛 3 𝑘 − 3 𝑟 2 𝑘 − 2 𝑡 2 𝑛 4 4 𝑘 ! = 𝑜 𝑡 𝑏 𝑛 3 4 𝑘 ! = 𝑜 𝑡 2 𝑛 3 4 𝑘 ! = 𝑜 𝑛 − 4 𝑘 2 𝑘 − 2 = 𝑜 ( 𝑛 − 2 ) . On the other hand, if 𝑡 = 𝜔 ( 𝑛 3 / 2 − 1 / ( 4 𝑘 − 4 ) ) , by the monotonicity of the “successfulness” of ( 𝑡 , 𝑏 ) - strategies over 𝑏 , we may assume that 𝑏 ≤ 𝑛 3 𝑘 − 4 · 𝑛 𝑘 / ( 4 𝑘 − 4 ) / 𝑡 2 𝑘 − 3 . Then, analogously as above, the probability that 𝑈 is contained in the 𝐹 1 -neighbourhood of at least 4 𝑘 vertices is at most | 𝑋 | 4 𝑘 ( 𝑝 1 ) 8 𝑘 = 𝑜 𝑡 𝑏 𝑛 3 4 𝑘 ! = 𝑜 𝑛 3 𝑘 − 4 𝑡 2 𝑘 − 3 𝑛 𝑘 4 𝑘 − 4 𝑡 𝑛 3 4 𝑘 ! = 𝑜 © « 𝑛 3 𝑡 2 𝑘 − 2 𝑛 𝑘 4 𝑘 − 4 − 1 ! 4 𝑘 ª ® ¬ = 𝑜 𝑛 4 𝑘 ( 𝑘 − 2 2 𝑘 − 2 + 𝑘 4 𝑘 − 4 − 1 ) = 𝑜 ( 𝑛 − 𝑘 ) = 𝑜 ( 𝑛 − 2 ) . In both cases, the conclusion follows by a union bound over all possible pairs of vertices. Condition on the event that ( CN ℓ ) holds for all 3 ≤ ℓ ≤ 𝑘 − 1 , that ( CN 2 ) holds, and that the bounds in ( 4.5 ) hold. W e now claim that the desired conclusion follows from the second moment method. ON CONSTR UCTING SMALL SUBGRAPHS IN THE BUDGET -CONSTRAINED RANDOM GRAPH PROCESS 15 Indeed, let Δ denote the number of ( 𝑘 − 1 ) -sets of vertices { 𝑣 1 , . . . , 𝑣 𝑘 − 1 } ∈ 𝑉 𝑘 − 1 contained in 𝑁 𝐹 1 ( 𝑥 ) for any 𝑥 ∈ 𝑋 , and let 𝑍 denote the number of cycles of length 𝑘 − 1 in 𝐹 2 whose vertex set is contained in 𝑁 𝐹 1 ( 𝑥 ) for some 𝑥 ∈ 𝑋 . F or suciently large 𝑛 , it follows from ( CN ℓ ) and ( 4.5 ) that 1 5 · 2 𝑘 ( 𝑘 − 1 ) ! 𝑛 2 𝑡 𝑟 2 𝑘 − 1 ≤ | 𝑋 | 5 𝑡 / 2 𝑛 𝑘 − 1 ≤ Δ ≤ | 𝑋 | 2 𝑡 / 𝑛 𝑘 − 1 ≤ 4 𝑛 2 𝑡 𝑟 2 𝑘 − 1 , (4.8) and so 𝔼 [ 𝑍 ] = Δ ( 𝑘 − 2 ) ! ( 𝑝 ∗ ) 𝑘 − 1 / 2 = Θ ( ( 𝑡 / 𝑟 ) 2 𝑘 − 2 ) = 𝜔 ( 1 ) . By Chebyshev ’ s inequality , it now suces to verify that Var ( 𝑍 ) = 𝑜 ( ( 𝑡 / 𝑟 ) 4 𝑘 − 4 ) . This is by now a standard argument, but we include the details for the interested reader . W e may expr ess 𝑍 as a sum of indicator random variables 𝑍 = Í 𝐶 𝑍 𝐶 , where the sum is over all copies 𝐶 of 𝐶 𝑘 − 1 in 𝐾 𝑛 which are fully contained in 𝑁 𝐹 1 ( 𝑥 ) 2 for some 𝑥 ∈ 𝑋 , where 𝑍 𝐶 is the indicator variable that 𝐶 ⊆ 𝐹 2 . W e then have that Var ( 𝑍 ) = 𝐶 Var ( 𝑍 𝐶 ) + 𝐶 , 𝐶 ′ Cov ( 𝑍 𝐶 , 𝑍 𝐶 ′ ) ≤ 𝔼 [ 𝑍 ] + 𝐶 , 𝐶 ′ Cov ( 𝑍 𝐶 , 𝑍 𝐶 ′ ) , where the sum is now over all ordered pairs 𝐶 , 𝐶 ′ of copies of 𝐶 𝑘 − 1 as above. It now remains to bound these covariances. The sum can be separated depending on the number of edges shared by 𝐶 and 𝐶 ′ . If 𝐶 and 𝐶 ′ share exactly 𝑎 ∈ [ 𝑘 − 3 ] edges, we have that Cov ( 𝑍 𝐶 , 𝑍 𝐶 ′ ) = ( 𝑝 ∗ ) 2 𝑘 − 2 − 𝑎 − ( 𝑝 ∗ ) 2 𝑘 − 2 ≤ ( 𝑝 ∗ ) 2 𝑘 − 2 − 𝑎 . Moreover , the number of pairs of cycles 𝐶 , 𝐶 ′ sharing exactly 𝑎 ∈ [ 𝑘 − 3 ] edges is 𝑂 𝑛 2 𝑡 𝑟 2 𝑘 − 1 𝑡 𝑛 𝑘 − 𝑎 − 2 ! ; this can be estimated by rst choosing 𝐶 (for which we rst choose some 𝑥 ∈ 𝑋 , then some ( 𝑘 − 1 ) -set in 𝑁 𝐹 1 ( 𝑥 ) , and then a cyclic ordering of the vertices in this set, leading to a similar expression as in the upper bound in ( 4.8 ) ), then choosing the (at most) 𝑘 − 𝑎 − 2 remaining vertices for 𝐶 ′ (which by ( CN 2 ) and ( CN ℓ ) must be contained in the 𝐹 1 -neighbourhood of one of constantly many vertices 𝑥 ′ ∈ 𝑋 , and for each of which we have 𝑂 ( 𝑡 / 𝑛 ) choices by ( 4.5 ) ), and then xing their cyclic order (in at most constantly many ways). Combining these observations and using the upper bound on 𝑡 , we conclude that Var ( 𝑍 ) ≤ 𝔼 [ 𝑍 ] + 𝑘 − 3 𝑎 = 1 𝑂 𝑛 2 𝑡 𝑟 2 𝑘 − 1 𝑡 𝑛 𝑘 − 𝑎 − 2 ( 𝑝 ∗ ) 2 𝑘 − 2 − 𝑎 ! = 𝔼 [ 𝑍 ] 1 + 𝑘 − 3 𝑎 = 1 𝑂 𝑡 2 𝑘 − 2 𝑎 − 3 𝑛 3 𝑘 − 3 𝑎 − 4 ! = ( 1 + 𝑜 ( 1 ) ) 𝔼 [ 𝑍 ] . Case 2. Assume now that 𝑡 = 𝜔 ( 𝑛 3 / 2 ) . Note that in this range we have 𝑏 = 𝜔 ( 𝑛 2 / 𝑡 ) . Fix any such 𝑏 and let ˜ 𝑛 = ˜ 𝑛 ( 𝑛 ) and 𝑡 1 = 𝑡 1 ( 𝑛 ) be such that ˜ 𝑛 = 𝑜 ( 𝑏 ) , ˜ 𝑛 = 𝑜 ( 𝑡 / 𝑛 ) , ˜ 𝑛 = 𝜔 ( 𝑛 2 / 𝑡 ) , ˜ 𝑛𝑛 ≤ 𝑡 1 = 𝑜 ( 𝑡 ) , and 𝑡 1 = 𝜔 ( 𝑛 2 / ˜ 𝑛 2 ) . It is straightforw ard to verify that such functions exist in this range. Now consider the ( 𝑡 , 𝑏 ) -strategy outlined in Strategy 2 below . For suciently large 𝑛 , this is a ( 𝑡 , 𝑏 ) -strategy by construction, so it only remains to prove that it is successful. Strategy 2. A ( 𝑡 , 𝑏 ) -strategy for 𝑊 𝑘 for 𝑡 = 𝜔 ( 𝑛 3 / 2 ) . 1: Fix a vertex 𝑥 ∈ [ 𝑛 ] . F or time 𝑡 1 and while the built graph has at most ˜ 𝑛 edges, buy any presented edge with one endpoint being 𝑥 . 2: F or time 𝑡 / 2 , simulate an optimal ( 𝑡 ˜ 𝑛 2 / 4 𝑛 2 , 𝑏 / 2 ) -strategy for constructing a cycle of length 𝑘 − 1 on 𝑁 𝐵 𝑡 1 ( 𝑥 ) . Reveal rst the set of edges incident to 𝑥 which are oered during the rst 𝑡 1 steps, and their order , but nothing else of the random graph process. This determines 𝑁 𝐵 𝑡 1 ( 𝑥 ) . Note that, by our choice of ˜ 𝑛 , a straightforw ard application of Theorem 2.1 shows that a.a.s. | 𝑁 𝐵 𝑡 1 ( 𝑥 ) | = ˜ 𝑛 ; we will assume that this is the case from now on. 16 S. ANTONIUK, A. ESPUNY DÍAZ, K. PETRO V A, AND M. STOJAK OVIĆ Now let 𝑡 ′ : = 𝑡 ˜ 𝑛 2 / 4 𝑛 2 and consider the application of the optimal ( 𝑡 ′ , 𝑏 / 2 ) -strategy for constructing a cycle of length 𝑘 − 1 on 𝑁 𝐵 𝑡 1 ( 𝑥 ) in Stag e 2 (note that | 𝑁 𝐵 𝑡 1 ( 𝑥 ) | = ˜ 𝑛 = 𝜔 ( 1 ) ). Since we have not revealed the edges of the rst stage of the random graph process except those incident to 𝑥 , we ha ve no information about those oered inside 𝑁 𝐵 𝑡 1 ( 𝑥 ) . As such, the ( 𝑁 𝐵 𝑡 1 ( 𝑥 ) , 𝑡 1 , 𝑡 / 2 ) -RGP has the same distribution as the segment of length ℓ ( 𝑁 𝐵 𝑡 1 ( 𝑥 ) , 𝑡 1 , 𝑡 / 2 ) of the random graph process on vertex set 𝑁 𝐵 𝑡 1 ( 𝑥 ) started at time 0 . Moreover , from Theorem 2.2 we know that a.a.s. ℓ ( 𝑁 𝐵 𝑡 1 ( 𝑥 ) , 𝑡 1 , 𝑡 / 2 ) ≥ 𝑡 ′ . Therefore, since 𝑏 = 𝜔 ( max { ˜ 𝑛 ⌊ 𝑘 / 2 ⌋ + 1 / ( 𝑡 ′ ) ⌊ 𝑘 / 2 ⌋ , ˜ 𝑛 / ( 𝑡 ′ ) 1 / 2 } ) , Theorem 4.2 ensures that a.a.s. Stage 2 in Strategy 2 constructs a cycle of length 𝑘 − 1 inside the Stage - 1 -neighbourhood of 𝑥 , which results in a copy of 𝑊 𝑘 , as desired. □ In order to prove the upper bound on the optimal budg et for ( 𝑡 , 𝑏 ) -strategies for constructing a copy of 𝐾 5 from Theorem 1.3 , we also exhibit an explicit strategy . This bound is reformulated next, and the proof closely follows that for wheels. Theorem 4.3. F or all 𝑡 = 𝜔 ( 𝑛 3 / 2 ) with 𝑡 ≤ 𝑀 , if 𝑏 = 𝜔 max ( 𝑛 12 𝑡 7 , 𝑛 2 𝑡 5 / 3 ) ! , there exists a successful ( 𝑡 , 𝑏 ) - strategy for constructing a copy of 𝐾 5 . Proof . The proof goes along the same lines as the proof of Theorem 4.1 . Due to the analogies between the proofs, we omit some details here. W e begin by splitting the range of 𝑡 into two cases, noting that 𝑛 12 𝑡 7 = 𝑛 2 𝑡 5 / 3 ⇐ ⇒ 𝑡 = 𝑛 13 / 8 . Case 1. Assume rst that 𝑡 = 𝑂 ( 𝑛 13 / 8 ) . Note that in this range we hav e 𝑏 = 𝜔 ( 𝑛 12 / 𝑡 7 ) . Fix any such 𝑏 and let 𝑟 = 𝑟 ( 𝑛 ) be such that 𝑟 = 𝑜 ( 𝑡 ) but it is suciently close to 𝑡 that 𝑟 = 𝜔 ( 𝑛 3 / 2 ) , 𝑛 9 𝑡 4 𝑟 10 = 𝑜 ( 1 ) , and 𝑛 12 𝑡 3 𝑟 10 = 𝑜 ( 𝑏 ) . Then, consider the strategy outlined in Strategy 3 below . This is a ( 𝑡 , 𝑏 ) -strategy by construction, so it only remains to prove that it is successful for constructing a copy of 𝐾 5 . Strategy 3. A ( 𝑡 , 𝑏 ) -strategy for 𝐾 5 for 𝑡 = 𝑂 ( 𝑛 13 / 8 ) . 0: Set 𝑋 : = [ ⌈ 𝑛 16 / 𝑟 10 ⌉ ] and 𝑉 : = [ 𝑛 ] \ 𝑋 . 1: F or time 𝑡 / 2 and while the built graph has at most 𝑏 / 2 edges, buy any presented edge with one endpoint in 𝑋 and the other in 𝑉 . 2: F or time 𝑡 / 2 and while the built graph has at most 𝑏 edges, buy an y presented edge which is contained in 𝑁 𝐵 𝑡 / 2 ( 𝑥 ) for at least one 𝑥 ∈ 𝑋 . First, note that, by the choice of 𝑟 , we hav e | 𝑋 | = ⌈ 𝑛 16 / 𝑟 10 ⌉ = ⌈ 𝑛 ( 𝑛 3 / 2 / 𝑟 ) 10 ⌉ = 𝑜 ( 𝑛 ) . W e then dene the coupling of random graphs ( 𝐻 1 , ˆ 𝐺 1 , 𝐻 ′ 1 , 𝐻 2 , ˆ 𝐺 2 , 𝐻 ′ 2 ) , the graphs ˆ 𝐵 1 , ˆ 𝐵 2 , and the edge sets 𝐸 1 , 𝐸 2 analogously as in the proof of Theorem 4.1 . F ollowing the proof of Theorem 4.1 , since 𝑡 = 𝜔 ( 𝑛 3 / 2 ) and by our choice of 𝑟 , we note that a.a.s. the number of edges purchased during Stage 1 satises 𝑒 ( ˆ 𝐵 1 ) ≤ 𝑒 ˆ 𝐺 1 ( 𝑋 , 𝑉 ) ≤ | 𝑋 | 2 𝑡 𝑛 ≤ 4 𝑛 15 𝑡 𝑟 10 ≤ 4 𝑛 12 𝑡 3 𝑟 10 = 𝑜 ( 𝑏 ) , and thus a.a.s. ˆ 𝐵 1 = ˆ 𝐺 1 ∩ 𝐸 1 . Similarly , a.a.s. the number of edges purchased during Stage 2 satises 𝑒 ( ˆ 𝐵 2 ) ≤ | 𝐸 ( 𝐻 ′ 2 ) ∩ 𝐸 2 | ≤ | 𝑋 | 2 𝑡 / 𝑛 2 2 𝑡 𝑛 2 ≤ 8 𝑛 12 𝑡 3 𝑟 10 = 𝑜 ( 𝑏 ) , ON CONSTR UCTING SMALL SUBGRAPHS IN THE BUDGET -CONSTRAINED RANDOM GRAPH PROCESS 17 and thus a.a.s. ˆ 𝐵 2 = ˆ 𝐺 2 ∩ 𝐸 2 . Therefore, after dening 𝐹 1 and 𝐹 2 analogously as in the proof of Theorem 4.1 , in order to verify that the strategy is successful, it suces to prove that a.a.s. there is some 𝑥 ∈ 𝑋 such that 𝐹 2 ∩ 𝑁 𝐹 1 ( 𝑥 ) 2 contains a copy of 𝐾 4 (recall that, after revealing 𝐹 1 , each edge in 𝑁 𝐹 1 ( 𝑥 ) 2 appears in 𝐹 2 independently with some probability 𝑝 ∗ = ( 1 − 𝑜 ( 1 ) ) 𝑡 / 𝑛 2 ). T o prove this, we rst claim that for every ℓ ≥ 3 we have that a.a.s. ( CN ℓ ) every ℓ -set of vertices of 𝑉 is contained in the 𝐹 1 -neighbourhood of at most ve vertices 𝑥 ∈ 𝑋 . Indeed, for a xed 𝑈 ∈ 𝑉 ℓ , by our choice of 𝑟 and the bounds on 𝑡 , the probability that there are at least six vertices 𝑥 ∈ 𝑋 such that 𝑈 ⊆ 𝑁 𝐹 1 ( 𝑥 ) is at most Θ | 𝑋 | 6 𝑡 𝑛 2 6 ℓ ! = Θ 𝑛 16 𝑟 10 𝑡 ℓ 𝑛 2 ℓ 6 ! = Θ 𝑡 ℓ − 4 𝑛 7 − 2 ℓ 𝑛 9 𝑡 4 𝑟 10 6 ! = 𝑜 𝑡 ℓ − 4 𝑛 7 − 2 ℓ 6 = 𝑜 ( 𝑛 − ℓ ) . Hence, by a union bound, a.a.s. for every ℓ -set 𝑈 ∈ 𝑉 ℓ , there are at most ve vertices 𝑥 ∈ 𝑋 such that 𝑈 ⊆ 𝑁 𝐹 1 ( 𝑥 ) . Now condition on the event that ( CN ℓ ) holds for ℓ ∈ { 3 , 4 } and that the bounds in ( 4.5 ) hold (both of which hold a.a.s.). Let 𝑍 denote the number of 4 - sets in 𝑉 4 that induce a 𝐾 4 in 𝐹 2 and are contained in 𝑁 𝐹 1 ( 𝑥 ) for some 𝑥 ∈ 𝑋 . Then, again by our choice of 𝑟 , 𝔼 [ 𝑍 ] = Θ | 𝑋 | 𝑡 𝑛 4 𝑡 𝑛 2 6 ! = Θ 𝑡 𝑟 10 ! = 𝜔 ( 1 ) . It now remains to bound the variance, similarly as in the proof of Theorem 4.1 . W e have to consider the cases where two dierent potential copies of 𝐾 4 share two or three vertices (for which the covariances of the corresponding indicator random variables are bounded by ( 𝑝 ∗ ) 11 and ( 𝑝 ∗ ) 9 , respectively). F or bounding the number of pairs of indicator variables which we consider , we rst mak e a choice of four vertices within the 𝐹 1 -neighbourhood of some 𝑥 ∈ 𝑋 , for which there are 𝑂 ( | 𝑋 | ( 𝑡 / 𝑛 ) 4 ) choices by the analogue of ( 4.5 ) . Next we bound the number of copies of 𝐾 4 which intersect the rst copy we xed. In the second case (that is, the case that they intersect in three vertices), once we choose which three vertices are shared, by ( CN ℓ ) there are at most ve choices for a vertex 𝑥 ′ ∈ 𝑋 such that the second copy of 𝐾 4 is contained in the neighbourhood of 𝑥 ′ ; once such an 𝑥 ′ is xed, there are at most 2 𝑡 / 𝑛 choices for the fourth vertex, again by the corresponding analogue of ( 4.5 ) . In the rst case, however , once we x the two shared vertices, we do not have any immediate restrictions on the other two . Thus, we rst x a (potentially arbitrary) third vertex, for which there are at most 𝑛 choices. After this has been xed, by ( CN ℓ ) there are at most ve choices for an 𝑥 ′ ′ ∈ 𝑋 such that these three vertices (the two shared and the third one we chose) are contained in the neighbourhood of 𝑥 ′ ′ . Then we can choose the fourth vertex within this neighbourhood. Combining these observations and using also the upper bound on 𝑡 , we conclude that Var ( 𝑍 ) ≤ 𝔼 [ 𝑍 ] + 𝑂 | 𝑋 | 𝑡 𝑛 4 𝑛 𝑡 𝑛 𝑡 𝑛 2 11 + 𝑡 𝑛 𝑡 𝑛 2 9 ! ! = 𝔼 [ 𝑍 ] + 𝑂 | 𝑋 | 𝑡 𝑛 4 𝑡 𝑛 2 6 𝑡 6 𝑛 10 + 𝑡 4 𝑛 7 ! = ( 1 + 𝑜 ( 1 ) ) 𝔼 [ 𝑍 ] . Hence, by Chebyshev ’ s inequality , a.a.s. during Stage 2 Builder will claim at least one copy of 𝐾 4 which completes a copy of 𝐾 5 . Case 2. Assume now that 𝑡 = 𝜔 ( 𝑛 13 / 8 ) . Note that in this range we ha ve 𝑏 = 𝜔 ( ( 𝑛 2 / 𝑡 ) 5 / 3 ) . Fix any such 𝑏 and let ˜ 𝑛 = ˜ 𝑛 ( 𝑛 ) and 𝑡 1 = 𝑡 1 ( 𝑛 ) be such that ˜ 𝑛 = 𝑜 ( 𝑏 ) , ˜ 𝑛 = 𝑜 ( 𝑡 / 𝑛 ) , ˜ 𝑛 = 𝜔 ( ( 𝑛 2 / 𝑡 ) 5 / 3 ) , ˜ 𝑛𝑛 ≤ 𝑡 1 = 𝑜 ( 𝑡 ) , and 𝑡 1 = 𝜔 ( 𝑛 2 / ˜ 𝑛 2 ) . Now consider the ( 𝑡 , 𝑏 ) -strategy outlined in Strategy 4 below . F or suciently large 𝑛 , this is a ( 𝑡 , 𝑏 ) -strategy by construction, so it only remains to prove that it is successful. 18 S. ANTONIUK, A. ESPUNY DÍAZ, K. PETRO V A, AND M. STOJAK OVIĆ Strategy 4. A ( 𝑡 , 𝑏 ) -strategy for 𝐾 5 for 𝑡 = 𝜔 ( 𝑛 13 / 8 ) . 1: Fix a vertex 𝑥 ∈ [ 𝑛 ] . F or time 𝑡 1 and while the built graph has at most ˜ 𝑛 edges, buy any presented edge with one endpoint being 𝑥 . 2: F or time 𝑡 / 2 , simulate an optimal ( 𝑡 ˜ 𝑛 2 / 4 𝑛 2 , 𝑏 / 2 ) -strategy for constructing a copy of 𝐾 4 on 𝑁 𝐵 𝑡 1 ( 𝑥 ) . W e can use the same reasoning as in the proof of Case 2 of Theorem 4.1 with 𝑡 ′ : = 𝑡 ˜ 𝑛 2 / 4 𝑛 2 . Note that by our choice of ˜ 𝑛 we have that 𝑏 = 𝜔 ( max { ˜ 𝑛 8 / ( 𝑡 ′ ) 5 , ˜ 𝑛 2 / 𝑡 ′ } ) . Thus, by Theorem 4.1 with 𝑘 = 4 , we conclude that a.a.s. Stage 2 in Strategy 4 constructs a copy of 𝐾 4 inside 𝑁 𝐵 𝑡 1 ( 𝑥 ) , which results in a copy of 𝐾 5 . □ 5. Concluding remarks and open problems 5.1. Lower bounds. Theorem 3.1 oers a general approach to derive lower bounds for the “budg et threshold” for constructing copies of any given xed graph. With this general lemma we are able to recover previous results from the literature, such as the correct lower bounds for constructing triangles and arbitrary trees (rst obtained by Frieze, Krivelevich and Michaeli [ 3 ] ), as well as diamonds and 𝑘 -fans (rst obtained by Iľkovič, León and Shu [ 4 ] ). Moreover , we also obtain several general new results, such as the correct lower bound for wheels on 𝑘 vertices (Theorem 3.2 ) and copies of 𝐾 1 , 𝑇 for arbitrary trees 𝑇 (Theorem A.1 ). However , the results which follow from Theorem 3.1 are not tight in general, and one can readily verify that we do not recover the tight lower bound for the optimal budget for constructing a copy of any cycle of length at least 4 proved by Frieze, Krivelevich and Michaeli [ 3 ] (see Theorem 4.2 ). It is natural to wonder for which other graphs it is possible to obtain a tight lower bound on the “budget threshold” by applying Theorem 3.1 . Problem 5.1. Characterise all xed graphs 𝐹 for which Theorem 3.1 yields a tight asymptotic lower bound on the optimal budget 𝑏 (as a function of 𝑛 and 𝑡 ) for which there exist successful ( 𝑡 , 𝑏 ) -strategies for constructing a copy of 𝐹 . W e emphasise here that, in order to prove our lower bounds on the optimal budget under which there exists a successful ( 𝑡 , 𝑏 ) -strategy for constructing some copy of a xed graph 𝐹 , in Theorem 3.1 we instead obtain upper bounds on the number of copies of 𝐹 that Builder can construct (the desired lower bounds follow by simply checking where this upper bound on the number of copies is 𝑜 ( 1 ) , which implies that a.a.s. Builder cannot construct any copy of 𝐹 ). Fr om this point of view , the fact that our results are not tight in general is not too surprising: if we consider the intuition for the counting result that we presented in Section 3 when 𝑛𝑝 ≥ 𝑏 = 𝜔 ( 1 ) , it is clear that one cannot really hope to alwa ys have 𝑏 choices for each subsequent vertex that is added towar ds counting a copy of 𝐹 . Indeed, imagine for example that 𝐹 contains some edge 𝑒 = 𝑥 𝑦 and some vertex 𝑧 at distance at least 2 from 𝑒 (say , at distance 2 from 𝑥 ), and that we start constructing 𝐹 from some choice for 𝑒 . If we rst assume that we have 𝑏 choices for a neighbour 𝑢 of 𝑥 , then it is not possible to have 𝑏 choices for 𝑧 for each choice of 𝑢 , as this would require a total of Θ ( 𝑏 2 ) = 𝜔 ( 𝑏 ) edges. Similarly , if 𝑛𝑝 = 𝑜 ( 𝑏 ) , then one cannot really hope to alwa ys hav e 𝑛𝑝 choices for each subsequent vertex that is added towar ds counting a copy of 𝐹 , as most vertices cannot have such a high degree due to the budget constraint. Therefore, in order to obtain sharper counting results, a ner approach is needed. This obvious gap in our approach leads to two interesting problems. On the one hand, since our counting result cannot be tight in g eneral for all graphs 𝐹 , obtaining general sharp counting results becomes a natural challenge. Even when Theorem 3.1 can be used to obtain a sharp lower bound for the optimal budget for constructing some copy of 𝐹 , it is not clear that our bound on the number of copies of 𝐹 is tight for all pairs ( 𝑡 , 𝑏 ) of time and budget constraints. While we hav e made no eort to study this direction, we believe that a general solution would shed much light on the behaviour of the budget-constrained random graph process. ON CONSTR UCTING SMALL SUBGRAPHS IN THE BUDGET -CONSTRAINED RANDOM GRAPH PROCESS 19 Problem 5.2. F or any 𝑡 = 𝑡 ( 𝑛 ) ∈ [ 𝑀 ] and 𝑏 = 𝑏 ( 𝑛 ) ∈ [ 𝑡 ] and any xed graph 𝐹 , determine sharp asymptotic bounds for the number of copies of 𝐹 that 𝐵 𝑡 may contain when running the budget - constrained random graph process under any ( 𝑡 , 𝑏 ) -strategy . On the other hand, there may well be other general tools that allow us to obtain a tight lower bound on the optimal budget constraint for general graphs 𝐹 . A dierent approach for addressing this problem (which is in line with the work of Iľk ovič, León and Shu [ 4 ] and with Theorem 3.4 ) is to obtain bounds for a dierent key quantity: rather than the number of copies of 𝐹 , one can consider the number of pairs of vertices for which there exists a rooted copy of 𝐹 \ { 𝑒 } (a “trap”). If this quantity can be estimated, then one can also estimate the probability that a trap is oered throughout the random graph process, which would then complete a copy of 𝐹 . 5.2. Upper bounds. In Theorems A.3 and 4.1 we ha ve provided explicit strategies for Builder to a.a.s. construct a graph which contains a copy of a wheel (in particular , a 𝐾 4 ) or a 𝐾 1 , 𝑇 for an arbitrary tree 𝑇 . These strategies work with budgets which are optimal up to constant factors for every possible value of 𝑡 . Moreover , in Theorem 4.3 we provided a strategy for constructing a copy of 𝐾 5 which we believe to be optimal up to a constant factor (see Theorem 1.4 ). These dierent strategies are actually very similar , and are particular examples of a general class of strategies. W e believe that the optimal strategies for constructing cliques of any size must be of the same type as those we hav e considered here. R oughly speaking, these strategies work as follows. First, one iteratively grows stars within the set of vertices chosen as leaves of the previous set of stars, until a certain depth. Then, one attempts to nd a copy of a smaller clique contained in one of the sets of leaves of a star built at the previous stage. More formally , such strategies can be described as follows. Suppose we want to construct a graph containing a copy of 𝐾 𝑠 , for some 𝑠 ≥ 3 . W e may describe a strategy of “ depth ” 𝑖 for any 𝑖 ∈ [ 𝑠 ] . First, x an arbitrary equipartition of [ 𝑛 ] into 𝑠 sets, [ 𝑛 ] = 𝑈 1 ∪ · . . . ∪ · 𝑈 𝑠 . (This plays no real role in the strategy and incurs in constant-factor losses on the required budget for the strategy , but should simplify formalising a proof of its correctness.) Then, take a random subset 𝐴 ⊆ [ 𝑛 ] of size 𝛼 , for an appropriate choice of 𝛼 , and for each 𝑖 ∈ [ 𝑠 ] let 𝐴 𝑖 : = 𝐴 ∩ 𝑈 𝑖 and 𝐴 + 𝑖 : = 𝐴 ∩ ( Ð 𝑗 ∈ [ 𝑠 ] \ [ 𝑖 ] 𝑈 𝑗 ) . Now x some 𝑖 ∈ { 0 } ∪ [ 𝑠 − 1 ] . W e are going to discuss a strategy of depth 𝑖 . First, we iterativ ely dene a set of vectors of vertices, which simply represent sets of vertices which form a clique in the built graph. F or each 𝑗 ∈ { 0 } ∪ [ 𝑖 ] , we shall denote the set of all such vectors of length 𝑗 by 𝑉 𝑗 . W e begin by setting 𝑉 0 : = {∅ } , and 𝑁 0 ( ∅) : = 𝐴 . Now , for each 𝑗 ∈ [ 𝑖 ] and assuming that 𝑉 𝑗 − 1 is dened and 𝑁 𝑗 − 1 ( x ) is dened for every x ∈ 𝑉 𝑗 − 1 , we proceed as follows. W e x an appropriate integer 𝑘 𝑗 and, for each x ∈ 𝑉 𝑗 − 1 , we choose a set 𝑌 x 𝑗 ⊆ 𝑁 𝑗 − 1 ( x ) ∩ 𝐴 𝑗 of size 𝑘 𝑗 uniformly at random. Then, for time 𝑡 / 𝑠 and while at most 𝑏 / 𝑠 edges have been bought, we purchase every presented edg e with one endpoint in 𝑌 x 𝑗 and the other in 𝑁 𝑗 − 1 ( x ) ∩ 𝐴 + 𝑗 , for an y x ∈ 𝑉 𝑗 − 1 . At this point, we set 𝑉 𝑗 : = { x 𝑦 : x ∈ 𝑉 𝑗 − 1 , 𝑦 ∈ 𝑌 x 𝑗 } and, for each x ∈ 𝑉 𝑗 , we let 𝑁 𝑗 ( x ) denote the set of all vertices 𝑣 ∈ 𝐴 + 𝑗 such that the edg e 𝑥 𝑗 𝑣 was purchased in this round of exposure. Once this process has been run for all 𝑗 ∈ [ 𝑖 ] , note that for every x ∈ 𝑉 𝑖 we have that all edges between vertices of x ha ve been purchased throughout the process, and that all vertices in 𝑁 𝑖 ( x ) are neighbours of every vertex of x in the built graph. In one last round of exposure, for time 𝑡 / 𝑠 and while at most 𝑏 / 𝑠 edges ha ve been bought, Builder purchases every oered edge which lies in Ð x ∈ 𝑉 𝑖 𝑁 𝑖 ( x ) 2 . If this last round of exposur e results in a copy of 𝐾 𝑠 − 𝑖 contained in some 𝑁 𝑖 ( x ) , then this clique together with the vertices of x forms a copy of 𝐾 𝑠 . W e remark that, for each 𝑖 , the strategy of depth 𝑖 may succeed only in some range of 𝑡 , and dierent depths lead to dierent bounds on the optimal budget; the optimal budget for some 𝑡 would then be tak en as the minimum over all these strategies which are successful for this 𝑡 . As there are multiple parameters to consider , the analysis of these strategies becomes more cumbersome as 𝑠 grows, and already for 𝐾 6 the behaviour seems to be much more complex. W e ha ve performed a preliminary analysis of the 𝐾 6 case and represent some of our ndings in Figure 3 ; this analysis does not lead to any particular insights and, while it follows the same approach 20 S. ANTONIUK, A. ESPUNY DÍAZ, K. PETRO V A, AND M. STOJAK OVIĆ 8 / 5 5 / 3 17 / 10 2 0 2 / 3 1 3 / 2 8 / 5 log 𝑛 𝑡 log 𝑛 𝑏 𝐾 6 upper bound 𝐾 6 lower bound 𝑥 ↦→ 𝑥 − 1 𝑥 ↦→ 8 − 4 𝑥 Figure 3. A depiction of the upper bound and lower bound on the optimal budget 𝑏 for successful ( 𝑡 , 𝑏 ) -strategies for 𝐾 6 . The lower bound follows from Theorem 3.1 , and the proof of the upper bound is omitted. as the proof of Theorem 4.1 , it is much more technical than the ones we ha ve presented, so we ha ve chosen to omit the details. Still, we would lik e to comment on some key aspects. F or instance, the strategy of depth 0 (that is, simply purchasing all edg es which are oered within a subset of [ 𝑛 ] and hoping that this results in a copy of 𝐾 𝑠 ) uses suboptimal budget for all 𝑡 when 𝑠 ∈ { 3 , 4 , 5 } , but when 𝑠 = 6 there is a range of 𝑡 where this strategy seems to outperform all deeper strategies. In particular , if optimal, this makes the log 𝑛 𝑏 -by- log 𝑛 𝑡 depiction of optimal budgets as shown in Figures 1 , 2 and 3 no long er conve x, which is a dierent behaviour from previously known examples. Moreover , rather than having two ranges where the behaviour is dierent, these strategies for 𝐾 6 seem to yield four distinct ranges, which is again dierent from all previous results. In particular , our analysis suggests that, if 𝑀 ≥ 𝑡 ≥ 𝑏 = 𝜔 min ( 𝑛 2 𝑡 4 , max ( 𝑛 21 𝑡 12 , 𝑛 16 𝑡 9 , 𝑛 2 𝑡 7 / 3 ) ) ! , then there is a successful ( 𝑡 , 𝑏 ) -strategy for constructing a copy of 𝐾 6 . It would be very interesting to conrm whether these strategies are indeed optimal or can be outperformed by dierent ones. In even more generality , we may think of strategies for other xed graphs. A property that cliques (as well as wheels 𝑊 𝑘 and graphs 𝐾 1 , 𝑇 ) satisfy is that they contain universal vertices, that is, vertices which are neighbours to every other vertex of the graph. W e believe that, for graphs containing a universal vertex, optimal ( 𝑡 , 𝑏 ) -strategies may to an extent have a similar structure to that discussed above, at least for some range of 𝑡 . More concretely , we wonder whether it is true that, for every xed graph 𝐹 containing a universal vertex 𝑣 , there exists some range of 𝑡 for which the “budg et -threshold” is attained by a strategy which simply xes a vertex 𝑥 ∈ [ 𝑛 ] , spends some amount of time building its neighbourhood, and then the rest of the time simulating an optimal strategy for constructing a copy of 𝐹 − 𝑣 within this neighbourhood. Note that, when 𝑡 is suciently large, this is the case for all the proofs we hav e presented here. In even greater g enerality , we say that a set of vertices 𝑆 is universal for a graph 𝐹 if 𝑆 ⊆ 𝑉 ( 𝐹 ) , 𝐹 [ 𝑆 ] is a (possibly empty) matching, and 𝑆 ⊆ 𝑁 ( 𝑣 ) for all 𝑣 ∈ 𝑉 ( 𝐹 ) \ 𝑆 . W e extend the previous question to the setting of graphs containing a universal set. That is, given a xed graph 𝐹 containing a universal set 𝑆 , does there exist some range of 𝑡 for which the following strategy attains the “budget-threshold”? For as long as needed (a.a.s. constantly many steps), purchase any set of (vertex -disjoint) oered edges until we hav e a matching 𝑀 of size | 𝐸 ( 𝐹 [ 𝑆 ] ) | . Then, x an arbitrary set 𝑋 ⊆ [ 𝑛 ] \ 𝑉 ( 𝑀 ) of size | 𝑆 | − 2 | 𝐸 ( 𝐹 [ 𝑆 ] ) | . F or time 𝑡 / 2 , purchase any oered edge which is incident to any vertex in 𝑋 ∪ 𝑉 ( 𝑀 ) , up to some bound on the total number of purchased edges. Then, for time 𝑡 / 2 , simulate an optimal strategy for constructing a copy of 𝐹 − 𝑆 in the (purchased) common neighbourhood of all xed vertices. ON CONSTR UCTING SMALL SUBGRAPHS IN THE BUDGET -CONSTRAINED RANDOM GRAPH PROCESS 21 References [1] M. Anastos, Constructing Hamilton cycles and perfect matchings eciently. arXiv e-prints (2022). arXiv: 2209.09860 . [2] A. Espun y Díaz, F . Garbe, T . Naia and Z. Smith, Graph factors and powers of Hamilton cycles in the budget-constrained random graph process. arXiv e-prints (2025). arXiv: 2502.20870 . [3] A. Frieze, M. Krivelevich and P . Michaeli, Fast construction on a restricted budget. Random Struct. Algorithms 67.4 (2025), Id/No e70 031, 26 pages, doi : 10.1002/rsa.70031 . [4] D . Iľkovič, J . León and X. Shu, Multi- cyclic graphs in the random graph process with restricted budget. arXiv e-prints (2024). arXiv: 2412.17620 . [5] S. Janson, T . Łuczak and A. Ruciński, Random graphs . Wiley-Int erscience Series in Discrete Mathematics and Optimization, Wiley-Interscience, New Y ork (2000), doi : 10.1002/9781118032718 . [6] K. Katsamaktsis and S. Letzter, Building graphs with high minimum degree on a budget. European J. Comb. 129 (2025), paper nr . 104 119, doi : 10.1016/j.ejc.2025.104119 . [7] L. Lichev, 𝑑 -connectivity of the random graph with restricted budget. J. Graph Theory 108.2 (2025), 293–312, doi : 10.1002/jgt.23180 . Appendix A. Proof of Theorem 1.2 As we did with the other main results in our paper , Theorem 1.2 can be split into two statements, one for the lower bound and one for the upper bound on the optimal budg et for which we can nd a successful ( 𝑡 , 𝑏 ) -strategy . W e begin with the statement for the lower bound. Theorem A.1. Let 𝑇 be a xed tree. Let 𝑚 : = | 𝐸 ( 𝑇 ) | . F or all 𝑡 ∈ [ 𝑀 ] , if 𝑡 = 𝑜 𝑛 3 𝑚 2 𝑚 + 1 or 𝑏 = 𝑜 max ( 𝑛 3 𝑚 𝑡 2 𝑚 , 𝑛 2 𝑡 𝑚 𝑚 + 1 ) ! , then for any ( 𝑡 , 𝑏 ) -strategy a.a.s. 𝐵 𝑡 does not contain a copy of 𝐾 1 , 𝑇 . Proof . Observe that 𝐾 1 , 𝑇 is a graph with 𝑚 + 2 vertices and 2 𝑚 + 1 edges. W e argue as in the proof of Theorem 3.2 . Let 𝑝 : = 𝑡 / 𝑀 . If 𝑡 = 𝑜 ( 𝑛 3 𝑚 / ( 2 𝑚 + 1 ) ) , then a.a.s. 𝐺 𝑡 contains no copy of 𝐾 1 , 𝑇 , by the rst moment method, and thus neither does 𝐵 𝑡 . Hence, we may assume that 𝑡 = Ω ( 𝑛 3 𝑚 / ( 2 𝑚 + 1 ) ) . Given an arbitrary ( 𝑡 , 𝑏 ) - strategy S , Theorem 3.1 ensures that a.a.s. nc ( 𝐾 1 , 𝑇 ) = nc ( 𝐾 1 , 𝑇 , S , 𝑛 , 𝑡 , 𝑏 ) ≤ 𝜂 · 𝑏 · min { 𝑏 , 𝑛 𝑝 } 𝑚 𝑝 𝑚 , where 𝜂 = 𝜔 ( 1 ) is a function that grows arbitrarily slowly . Observe that 𝑛 3 𝑚 𝑡 2 𝑚 = 𝑛 2 𝑡 𝑚 𝑚 + 1 ⇐ ⇒ 𝑡 = 𝑛 3 𝑚 + 1 2 𝑚 + 1 . Suppose rst that 𝑡 = 𝑂 ( 𝑛 3 𝑚 + 1 2 𝑚 + 1 ) . F or any 𝑏 = 𝑜 ( 𝑛 3 𝑚 / 𝑡 2 𝑚 ) , choose some 𝜂 = 𝜔 ( 1 ) with 𝜂 = 𝑜 ( 𝑛 3 𝑚 / 𝑏 𝑡 2 𝑚 ) . Then, we conclude that a.a.s. nc ( 𝐾 1 , 𝑇 ) ≤ 𝜂 · 𝑏 ( 𝑛𝑝 ) 𝑚 𝑝 𝑚 = 𝑂 𝜂 · 𝑏 𝑡 2 𝑚 𝑛 3 𝑚 = 𝑜 ( 1 ) . Suppose next that 𝑡 = 𝜔 ( 𝑛 3 𝑚 + 1 2 𝑚 + 1 ) . Given any 𝑏 = 𝑜 ( ( 𝑛 2 / 𝑡 ) 𝑚 / ( 𝑚 + 1 ) ) , choose some 𝜂 = 𝜔 ( 1 ) with 𝜂 = 𝑜 ( 𝑛 2 𝑚 / 𝑏 𝑚 + 1 𝑡 𝑚 ) . W e then conclude that a.a.s. nc ( 𝐾 1 , 𝑇 ) ≤ 𝜂 · 𝑏 𝑚 + 1 𝑝 𝑚 = 𝑂 𝜂 · 𝑏 𝑚 + 1 𝑡 𝑚 𝑛 2 𝑚 = 𝑜 ( 1 ) . □ F or the upper bound, we proceed analogously as in the proof of Theorem 4.1 . The most relevant change is that, rather than appealing to Theorem 4.2 for the second case of the analysis, we instead use the following result. 22 S. ANTONIUK, A. ESPUNY DÍAZ, K. PETRO V A, AND M. STOJAK OVIĆ Lemma A.2 (Frieze, Krivelevich and Michaeli [ 3 , Theorem 1.5 ] ) . Let 𝑚 ≥ 1 be a xed integer and 𝑇 be a tree with 𝑚 edges. If 𝑀 ≥ 𝑡 ≥ 𝑏 = 𝜔 ( max { ( 𝑛 / 𝑡 ) 𝑚 − 1 , 1 } ) , then there exists a successful ( 𝑡 , 𝑏 ) -strategy for constructing a copy of 𝑇 . Theorem A.3. Let 𝑇 be a xed non-trivial tree. Let 𝑚 : = | 𝐸 ( 𝑇 ) | . If 𝑀 ≥ 𝑡 ≥ 𝑏 = 𝜔 max ( 𝑛 3 𝑚 𝑡 2 𝑚 , 𝑛 2 𝑡 𝑚 𝑚 + 1 ) ! , then there exists a successful ( 𝑡 , 𝑏 ) -strategy for constructing a copy of 𝐾 1 , 𝑇 . Proof . W e argue lik e in the proof of Theorem 4.1 . By reordering the bounds from the statement, we ha ve that 𝑡 = 𝜔 ( 𝑛 3 𝑚 / ( 2 𝑚 + 1 ) ) = 𝜔 ( 𝑛 ) . W e consider two cases, depending on the range of 𝑡 . Case 1. Assume rst that 𝑡 = 𝑂 ( 𝑛 3 𝑚 + 1 2 𝑚 + 1 ) . In this range, we ha ve that 𝑏 = 𝜔 ( 𝑛 3 𝑚 / 𝑡 2 𝑚 ) . Fix any such 𝑏 and let 𝑟 = 𝑟 ( 𝑛 ) be such that 𝑟 = 𝑜 ( 𝑡 ) but it is suciently close to 𝑡 that 𝑟 = 𝜔 ( 𝑛 3 𝑚 / ( 2 𝑚 + 1 ) ) , 𝑛 3 𝑚 𝑡 𝑟 2 𝑚 + 1 = 𝑜 ( 𝑏 ) and 𝑛 3 𝑚 − 3 𝑡 3 𝑟 2 𝑚 + 1 = 𝑜 ( 𝑏 ) . Then, consider the strategy outlined in Strategy 5 below . Since this is a ( 𝑡 , 𝑏 ) -strategy by construction, it only remains to prove that it is successful for constructing a copy of 𝐾 1 , 𝑇 . Strategy 5. A ( 𝑡 , 𝑏 ) -strategy for 𝐾 1 , 𝑇 for 𝑡 = 𝑂 ( 𝑛 3 𝑚 + 1 2 𝑚 + 1 ) . 0: Set 𝑋 : = [ ⌈ 𝑛 3 𝑚 + 1 / 𝑟 2 𝑚 + 1 ⌉ ] and 𝑉 : = [ 𝑛 ] \ 𝑋 . 1: F or time 𝑡 / 2 and while the built graph has at most 𝑏 / 2 edges, buy any presented edge with one endpoint in 𝑋 and the other in 𝑉 . 2: F or time 𝑡 / 2 and while the built graph has at most 𝑏 edges, buy an y presented edge which is contained in 𝑁 𝐵 𝑡 / 2 ( 𝑥 ) for at least one 𝑥 ∈ 𝑋 . First, note that, by the choice of 𝑟 , we have | 𝑋 | = ⌈ 𝑛 3 𝑚 + 1 / 𝑟 2 𝑚 + 1 ⌉ = 𝑜 ( 𝑛 ) . W e then dene the coupling of random graphs ( 𝐻 1 , ˆ 𝐺 1 , 𝐻 ′ 1 , 𝐻 2 , ˆ 𝐺 2 , 𝐻 ′ 2 ) , the graphs ˆ 𝐵 1 , ˆ 𝐵 2 , and the edge sets 𝐸 1 , 𝐸 2 analogously as in the proof of Theorem 4.1 . F ollowing the proof of Theorem 4.1 , by the upper bound on 𝑡 and our choice of 𝑟 , we note that a.a.s. the number of edges purchased during the rst stage satises 𝑒 ( ˆ 𝐵 1 ) ≤ 𝑒 ˆ 𝐺 1 ( 𝑋 , 𝑉 ) ≤ | 𝑋 | 2 𝑡 𝑛 ≤ 4 𝑛 3 𝑚 + 1 𝑡 𝑟 2 𝑚 + 1 𝑛 = 𝑜 ( 𝑏 ) , and thus a.a.s. ˆ 𝐵 1 = ˆ 𝐺 1 ∩ 𝐸 1 . Similarly , a.a.s. the number of edges purchased during the second stage satises 𝑒 ( ˆ 𝐵 2 ) ≤ | 𝐸 ( 𝐻 ′ 2 ) ∩ 𝐸 2 | ≤ | 𝑋 | 2 𝑡 / 𝑛 2 2 𝑡 𝑛 2 ≤ 8 𝑛 3 𝑚 + 1 𝑡 3 𝑟 2 𝑚 + 1 𝑛 4 = 𝑜 ( 𝑏 ) , and thus a.a.s. ˆ 𝐵 2 = ˆ 𝐺 2 ∩ 𝐸 2 . Therefore, after dening 𝐹 1 and 𝐹 2 analogously as in the proof of Theorem 4.1 , in order to verify that the strategy is successful, it suces to prove that a.a.s. there is some 𝑥 ∈ 𝑋 such that 𝐹 2 ∩ 𝑁 𝐹 1 ( 𝑥 ) 2 contains a copy of 𝑇 (recall that, after revealing 𝐹 1 , each edge in 𝑁 𝐹 1 ( 𝑥 ) 2 appears in 𝐹 2 independently with some probability 𝑝 ∗ = ( 1 − 𝑜 ( 1 ) ) 𝑡 / 𝑛 2 ). T o prove this, we rst claim that for every ℓ ≥ 3 we have that a.a.s. ( CN ℓ ) every ℓ -set of vertices of 𝑉 is contained in the 𝐹 1 -neighbourhood of at most ve vertices 𝑥 ∈ 𝑋 . ON CONSTR UCTING SMALL SUBGRAPHS IN THE BUDGET -CONSTRAINED RANDOM GRAPH PROCESS 23 Indeed, for a xed 𝑈 ∈ 𝑉 ℓ , by our lower bound on 𝑟 and the bounds on 𝑡 , the probability that there are at least six vertices 𝑥 ∈ 𝑋 such that 𝑈 ⊆ 𝑁 𝐹 1 ( 𝑥 ) is at most Θ | 𝑋 | 6 𝑡 𝑛 2 6 ℓ ! = Θ 𝑛 3 𝑚 + 1 𝑟 2 𝑚 + 1 𝑡 ℓ 𝑛 2 ℓ 6 ! = 𝑜 𝑛 1 + ℓ ( 3 𝑚 + 1 2 𝑚 + 1 − 2 ) 6 = 𝑜 𝑛 6 − 3 ℓ = 𝑜 ( 𝑛 − ℓ ) . Hence, by a union bound, a.a.s. for every ℓ -set 𝑈 ∈ 𝑉 ℓ there are at most ve vertices 𝑥 ∈ 𝑋 such that 𝑈 ⊆ 𝑁 𝐹 1 ( 𝑥 ) . In a similar fashion, we claim that a.a.s. ( CN2 ) every pair of vertices in 𝑉 2 is contained in the 𝐹 1 -neighbourhood of at most 4 𝑚 + 1 vertices 𝑥 ∈ 𝑋 . T o show this, x an arbitrary pair of vertices 𝑈 ∈ 𝑉 2 . By the bounds on 𝑡 and 𝑟 , with calculations analogous to those for proving ( CN ℓ ) , we conclude that the probability that 𝑈 is contained in the 𝐹 1 -neighbourhood of at least 4 𝑚 + 2 vertices is at most Θ | 𝑋 | 4 𝑚 + 2 𝑡 𝑛 2 8 𝑚 + 4 ! = Θ 𝑛 3 𝑚 + 1 𝑟 2 𝑚 + 1 𝑡 2 𝑛 4 4 𝑚 + 2 ! = 𝑜 𝑛 6 𝑚 + 2 2 𝑚 + 1 − 3 4 𝑚 + 2 = 𝑜 ( 𝑛 − 2 ) . The conclusion follows by a union bound over all possible pairs of vertices. Now condition on the event that ( CN ℓ ) holds for all 2 ≤ ℓ ≤ 𝑚 and that the bounds in ( 4.5 ) hold (both of which occur a.a.s.). Let 𝑍 denote the number of copies of 𝑇 in 𝐹 2 whose vertex set is contained in 𝑁 𝐹 1 ( 𝑥 ) for some 𝑥 ∈ 𝑋 . Then, again by our choice of 𝑟 , 𝔼 [ 𝑍 ] = Θ | 𝑋 | 𝑡 𝑛 𝑚 + 1 𝑡 𝑛 2 𝑚 ! = Θ 𝑛 3 𝑚 + 1 𝑟 2 𝑚 + 1 𝑡 2 𝑚 + 1 𝑛 3 𝑚 + 1 = 𝜔 ( 1 ) . Similarly as in the proof of Theorem 4.1 , we also have that Var ( 𝑍 ) ≤ ( 1 + 𝑜 ( 1 ) ) 𝔼 [ 𝑍 ] and, by Chebyshev ’ s inequality , a.a.s. during the second stage Builder will claim at least one copy of 𝑇 which completes a copy of 𝐾 1 , 𝑇 . Case 2. Suppose now that 𝑡 = 𝜔 ( 𝑛 3 𝑚 + 1 2 𝑚 + 1 ) . Note that in this range we have 𝑏 = 𝜔 ( ( 𝑛 2 / 𝑡 ) 𝑚 / ( 𝑚 + 1 ) ) . Fix any such 𝑏 and let ˜ 𝑛 = ˜ 𝑛 ( 𝑛 ) and 𝑡 1 = 𝑡 1 ( 𝑛 ) be such that ˜ 𝑛 = 𝑜 ( 𝑏 ) , ˜ 𝑛 = 𝑜 ( 𝑡 / 𝑛 ) , ˜ 𝑛 = 𝜔 ( ( 𝑛 2 / 𝑡 ) 𝑚 / ( 𝑚 + 1 ) ) , ˜ 𝑛𝑛 ≤ 𝑡 1 = 𝑜 ( 𝑡 ) , and 𝑡 1 = 𝜔 ( 𝑛 2 / ˜ 𝑛 2 ) . Now consider the strategy outlined in Strategy 6 . F or suciently large 𝑛 , this is a ( 𝑡 , 𝑏 ) -strategy by construction, so it only remains to prove that it is successful. Strategy 6. A ( 𝑡 , 𝑏 ) -strategy for 𝐾 1 , 𝑇 for 𝑡 = 𝜔 ( 𝑛 3 𝑚 + 1 2 𝑚 + 1 ) . 1: Fix a vertex 𝑥 ∈ [ 𝑛 ] . F or time 𝑡 1 and while the built graph has at most ˜ 𝑛 edges, buy any presented edge with one endpoint being 𝑥 . 2: F or time 𝑡 / 2 , simulate an optimal ( 𝑡 ˜ 𝑛 2 / 4 𝑛 2 , 𝑏 / 2 ) -strategy for constructing a copy of 𝑇 on 𝑁 𝐵 𝑡 1 ( 𝑥 ) . W e can use the same reasoning as in the proof of Case 2 of Theorem 4.1 with 𝑡 ′ : = 𝑡 ˜ 𝑛 2 / 4 𝑛 2 , using The - orem A.2 instead of Theorem 4.2 . Note that by our choice of ˜ 𝑛 we have that 𝑏 = 𝜔 ( max { ( ˜ 𝑛 / 𝑡 ′ ) 𝑚 − 1 , 1 } ) . Thus, by Theorem A.2 , we conclude that a.a.s. we construct a copy of 𝑇 inside 𝑁 𝐵 𝑡 1 ( 𝑥 ) , which results in a copy of 𝐾 1 , 𝑇 . □
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment