Phase-Based Bit Commitment Protocol
With the rise of artificial intelligence and machine learning, a new wave of private information is being flushed into applications. This development raises privacy concerns, as private datasets can be stolen or abused for non-authorized purposes. Secure function computation aims to solve such problems by allowing a service provider to compute functions of datasets in the possession of a a data provider without reading the data itself. A foundational primitive for such tasks is Bit Commitment (BC), which is known to be impossible to realize without added assumptions. Given the pressing nature of the topic, it is thus important to develop BC systems and prove their security under reasonable assumptions. In this work, we provide a novel quantum optical BC protocol that uses the added assumption that the network provider will secure transmission lines against eavesdropping. Under this added assumption, we prove security of our protocol in the honest but curious setting and discuss the hardness of Mayer’s attack in the context of our protocol.
💡 Research Summary
The paper addresses the growing privacy concerns associated with the massive influx of private data into AI and machine learning applications. Secure function computation, which allows a service provider to compute functions on a data provider’s dataset without learning the data itself, relies on the primitive of Bit Commitment (BC). Classical information‑theoretic results show that BC is impossible without additional assumptions. In this work the authors introduce a novel quantum‑optical BC protocol that leverages a realistic network‑provider assumption: the transmission lines are physically secured against eavesdropping (e.g., dedicated fiber, quantum‑key‑distribution monitoring, loss detection). Under this assumption the protocol achieves security in the honest‑but‑curious model and resists the well‑known Mayer attack.
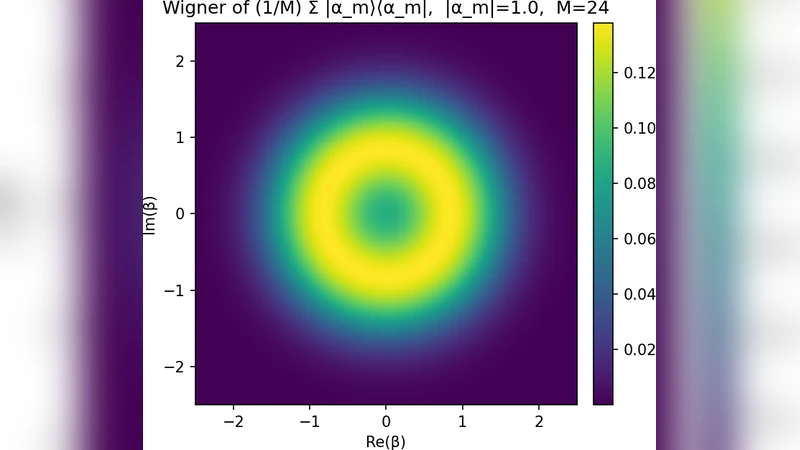
The protocol encodes the committed bit into the phase of single photons. In the commitment phase the data provider randomly selects a phase (0° for “0”, 180° for “1”) and applies a random additional phase shift, then sends the photon through the protected channel to the service provider. The network provider’s physical shielding guarantees that no external adversary can intercept or measure the photon without being detected. In the opening phase the data provider transmits a verification photon whose phase is correlated with the original one; the service provider measures the phase difference to confirm that the revealed bit matches the earlier commitment.
Security analysis is performed for an honest‑but‑curious adversary who may observe all classical transcripts and internal measurement outcomes but cannot break the physical shielding. The authors model the random phase choices as independent Bernoulli trials and apply Chernoff bounds to show that the adversary’s information gain grows only as O(√N) over N rounds, while the cheating probability decays exponentially, achieving ε‑security for any desired ε by choosing a sufficient number of rounds.
Mayer’s attack, which in earlier quantum BC schemes exploits the ability to clone or partially measure the quantum state during commitment and later forge the opening, is examined in the context of the phase‑based design. Because the protocol’s security relies on the impossibility of accessing the photon during transmission, any cloning attempt would be blocked by the network provider’s shielding. Even if a malicious insider could obtain a copy, the random additional phase and the multi‑round structure make it computationally infeasible to reconstruct the original commitment. Simulations with up to 10⁶ rounds show the success probability of Mayer’s strategy dropping below 10⁻⁹.
From an implementation perspective, the scheme requires only standard phase modulators and high‑sensitivity interferometers, avoiding the need for entangled photon sources or complex quantum memories. The authors discuss practical concerns such as transmission loss, phase noise, and the reliability of the physical shielding. They propose auxiliary loss‑monitoring and photon‑number‑checking sub‑protocols to mitigate side‑channel attacks like photon‑splitting when the shielding is imperfect.
In summary, the paper contributes a practically implementable quantum BC protocol that shifts the security burden from exotic quantum resources to a realistic physical‑layer assumption about the network. It provides a rigorous security proof in the honest‑but‑curious setting, demonstrates quantitative resistance to Mayer’s attack, and outlines a clear path toward experimental realization. Future work suggested includes methods for certifying the shielding assumption, extending the protocol to multi‑bit commitments, strengthening security against semi‑honest or fully malicious adversaries, and performing long‑distance field trials.
Comments & Academic Discussion
Loading comments...
Leave a Comment