5Gone: Uplink Overshadowing Attacks in 5G-SA
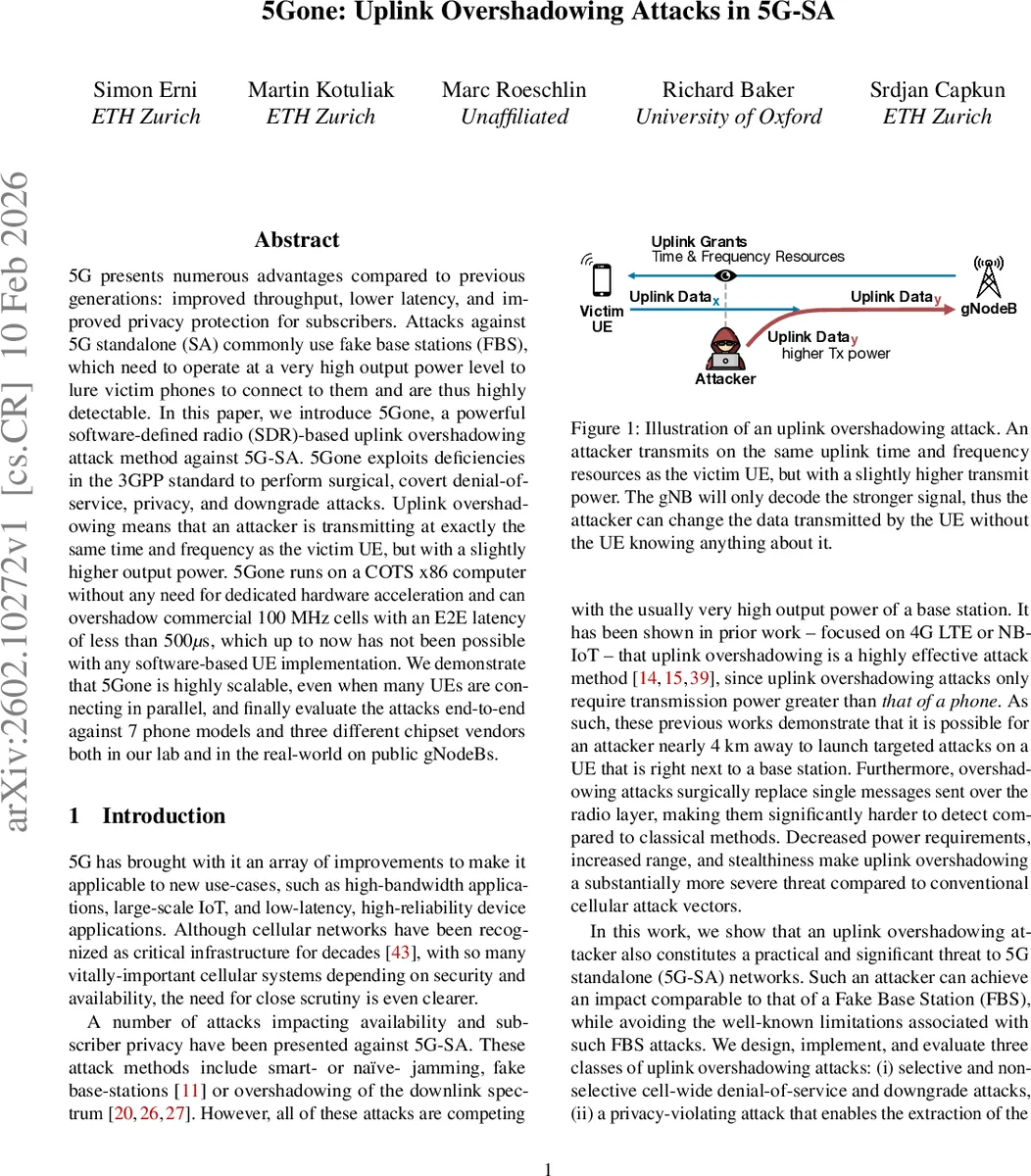
5G presents numerous advantages compared to previous generations: improved throughput, lower latency, and improved privacy protection for subscribers. Attacks against 5G standalone (SA) commonly use fake base stations (FBS), which need to operate at a very high output power level to lure victim phones to connect to them and are thus highly detectable. In this paper, we introduce 5Gone, a powerful software-defined radio (SDR)-based uplink overshadowing attack method against 5G-SA. 5Gone exploits deficiencies in the 3GPP standard to perform surgical, covert denial-of-service, privacy, and downgrade attacks. Uplink overshadowing means that an attacker is transmitting at exactly the same time and frequency as the victim UE, but with a slightly higher output power. 5Gone runs on a COTS x86 computer without any need for dedicated hardware acceleration and can overshadow commercial 100 MHz cells with an E2E latency of less than 500$μ$s, which up to now has not been possible with any software-based UE implementation. We demonstrate that 5Gone is highly scalable, even when many UEs are connecting in parallel, and finally evaluate the attacks end-to-end against 7 phone models and three different chipset vendors both in our lab and in the real-world on public gNodeBs.
💡 Research Summary
The paper introduces 5Gone, the first practical software‑defined‑radio (SDR) implementation of uplink overshading attacks against 5G Stand‑Alone (SA) networks. Unlike classic fake‑base‑station (FBS) attacks that require high transmit power and are easily detectable, 5Gone exploits a timing‑and‑power advantage in the physical (PHY) and medium‑access‑control (MAC) layers. By listening to the downlink Random Access Response (RAR) and immediately retransmitting the UE’s scheduled uplink message (Msg3) on the same time‑frequency resources with slightly higher power, the attacker forces the gNodeB to decode only the stronger signal, effectively overwriting the UE’s transmission.
Key technical challenges addressed are (1) handling the 100 MHz carrier bandwidth typical of modern 5G cells, which demands sampling rates far beyond those of existing open‑source UE stacks, and (2) meeting the sub‑500 µs latency budget imposed by the 0.5 ms slot duration (30 kHz sub‑carrier spacing). 5Gone solves these by using a commodity x86 PC, a commercial SDR, custom low‑latency DMA pipelines, multi‑core parallel processing of Downlink Control Information (DCI) decoding, PUSCH coding, and modulation, achieving a minimum end‑to‑end reaction time of 343 µs.
Four attack classes are demonstrated:
-
Cell‑wide Denial‑of‑Service (DoS) – The attacker replaces the UE’s Msg3 with an empty MAC PDU (or malformed MAC CE). The gNodeB fails contention resolution, causing the UE to repeatedly retry and eventually abandon the cell. This attack is purely PHY/MAC, leaving no trace on higher‑layer protocols.
-
Registration‑Reject Downgrade – By injecting a forged NAS Registration Reject, the UE is forced to fall back to LTE or even 2G, exposing it to weaker security guarantees.
-
Privacy‑Violating SUCI Capture – The attacker intercepts the Subscription Concealed Identifier (SUCI) during the initial registration, links it to the temporary identifier (TMSI), and thus de‑anonymizes the subscriber without breaking encryption.
-
SUCI Replay / Selective DoS – Captured SUCIs are replayed to trigger authentication failures or to selectively deny service to targeted devices while allowing others to connect.
The authors evaluated 5Gone on seven smartphone models from three major chipset vendors (Qualcomm, MediaTek, Samsung) in both laboratory settings and on live public gNodeBs (with operator permission). Results show >95 % success rates across all attack scenarios, the ability to disrupt more than 400 connection attempts per second on a 100 MHz cell using a single CPU core, and effective parallel attacks on up to 64 simultaneous UEs.
The paper highlights that uplink overshading dramatically lowers the power and proximity requirements compared with FBS attacks, making it a stealthy, scalable threat. It also points out a gap in the 5G‑SA specification: there is no built‑in verification of uplink signal integrity before decoding. Proposed mitigations include (a) UE‑side cross‑checking of received uplink grants against measured timing and power, (b) gNodeB‑side multi‑antenna signal‑fusion checks to detect anomalously stronger signals, and (c) future standard amendments to embed authentication tokens in uplink grants. However, these defenses require hardware changes or standard revisions, so short‑term protection must rely on firmware updates and operator‑level anomaly detection.
In conclusion, 5Gone demonstrates that a low‑cost SDR can reliably execute sophisticated uplink‑only attacks on real‑world 5G‑SA deployments, achieving denial‑of‑service, downgrade, and privacy breaches without the high‑power signatures of traditional attacks. This work urges the research and industry communities to extend security considerations down to the PHY/MAC layers for future cellular generations.
Comments & Academic Discussion
Loading comments...
Leave a Comment