Privacy Preservation Techniques (PPTs) in IoT Systems: A Scoping Review and Future Directions
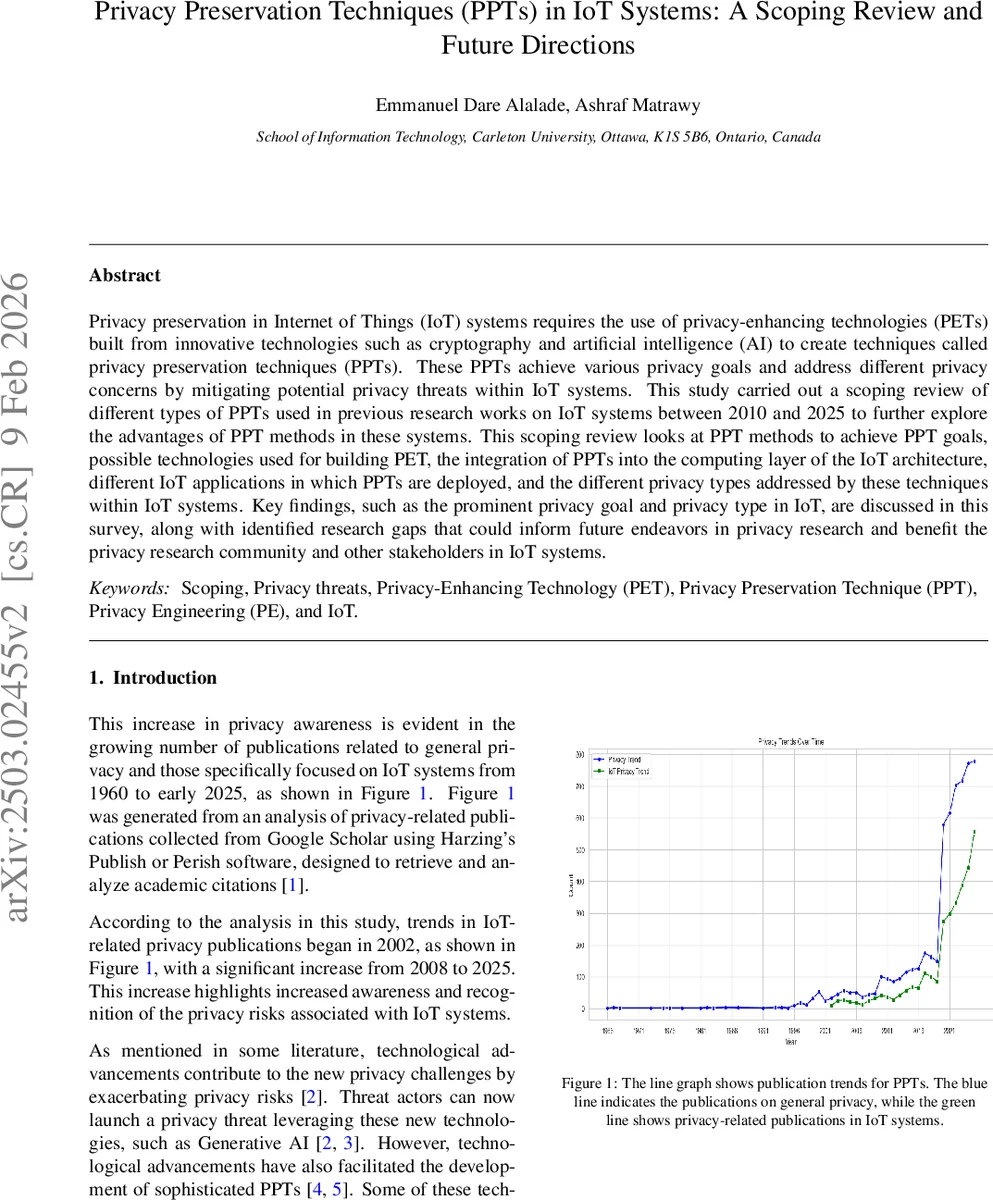
Privacy preservation in Internet of Things (IoT) systems requires the use of privacy-enhancing technologies (PETs) built from innovative technologies such as cryptography and artificial intelligence (AI) to create techniques called privacy preservation techniques (PPTs). These PPTs achieve various privacy goals and address different privacy concerns by mitigating potential privacy threats within IoT systems. This study carried out a scoping review of different types of PPTs used in previous research works on IoT systems between 2010 and early 2023 to further explore the advantages of privacy preservation in these systems. This scoping review looks at privacy goals, possible technologies used for building PET, the integration of PPTs into the computing layer of the IoT architecture, different IoT applications in which PPTs are deployed, and the different privacy types addressed by these techniques within IoT systems. Key findings, such as the prominent privacy goal and privacy type in IoT, are discussed in this survey, along with identified research gaps that could inform future endeavors in privacy research and benefit the privacy research community and other stakeholders in IoT systems.
💡 Research Summary
This paper presents a comprehensive scoping review of privacy preservation techniques (PPTs) applied to Internet of Things (IoT) systems over the period from 2010 to early 2023. Recognizing the rapid growth of IoT‑related privacy publications—particularly after 2008—and the emergence of new threat vectors such as generative AI, the authors set out to map the state‑of‑the‑art PPTs, the underlying privacy‑enhancing technologies (PETs), the layers of the IoT architecture where these techniques are deployed, the application domains they serve, and the specific privacy types they aim to protect.
Methodology
Following an adapted PRISMA‑ScR framework, the authors searched four major scholarly databases (IEEE Xplore, ACM Digital Library, Scopus, Web of Science) using combinations of “privacy”, “IoT”, “privacy preservation technique”, and “privacy‑enhancing technology”. After removing duplicates and screening titles, abstracts, and full texts, 124 relevant papers were retained for detailed analysis. Each paper was coded along five dimensions: (1) privacy goal (e.g., confidentiality, anonymity, integrity), (2) PET implementation technology (cryptography, AI/ML, blockchain, differential privacy, etc.), (3) IoT architectural layer (device, edge, fog, cloud), (4) application domain (smart home, healthcare, industrial IoT, smart city, vehicular networks, etc.), and (5) privacy type addressed (user, device‑identity, communication‑channel, location, group).
Key Findings
-
Dominant Privacy Goals – Data confidentiality (71 % of studies) and anonymity (58 %) are the most frequently targeted goals, closely linked to protecting user privacy and device‑identity privacy. Integrity, data minimization, and transparency also appear but less prominently.
-
PET Technologies – Cryptography dominates (68 % of PPTs), with attribute‑based encryption (ABE), homomorphic encryption, and lightweight symmetric ciphers being the most cited. AI/ML‑based PETs have surged in the last five years, primarily for anomaly detection, privacy‑risk prediction, and adaptive data perturbation. Differential privacy and blockchain are employed for data sharing and immutable audit trails, respectively.
-
Layer‑Specific Deployment –
- Device Layer – Emphasizes lightweight encryption and differential privacy to meet strict memory and power constraints.
- Edge Layer – Uses blockchain and secure multi‑party computation (SMPC) to ensure data integrity and decentralized authentication while supporting near‑real‑time analytics.
- Fog Layer – Focuses on context‑aware privacy and multi‑path routing, often combining anonymization with policy‑driven access control.
- Cloud Layer – Leverages homomorphic encryption and differential privacy for protecting data at rest and in transit during large‑scale analytics.
-
Application Domains – Smart homes (34 % of papers) lead in PPT adoption, mainly through data masking and pseudonymization to hide occupants’ behavior patterns. Healthcare (22 %) relies heavily on homomorphic encryption and differential privacy to enable secure sharing of patient records. Industrial IoT (18 %) and smart cities (12 %) prioritize blockchain‑based provenance and SMPC for secure control‑plane communications. Vehicular networks and agricultural IoT are emerging but still under‑explored.
-
Privacy Types Addressed – User privacy (67 %) and device‑identity privacy (53 %) dominate, followed by communication‑channel privacy (41 %), location privacy (38 %), and group privacy (22 %). The authors note that many techniques simultaneously address multiple types, but explicit mapping is often missing in the literature.
-
Research Gaps – The review identifies several critical gaps:
- Lack of truly lightweight PETs suitable for ultra‑constrained sensors and actuators.
- Limited transparency and explainability of AI‑driven PETs, hindering trust and regulatory compliance.
- Absence of standardized privacy‑goal and threat‑model taxonomies across the IoT community.
- Scarcity of integrated, cross‑layer frameworks that coordinate privacy controls from device to cloud.
- Insufficient empirical evaluations in real‑world deployments and limited discussion of legal/regulatory alignment (e.g., GDPR, CCPA).
Proposed Directions
To bridge these gaps, the authors advocate for a privacy‑by‑design approach that embeds privacy controls throughout the IoT stack, the development of hardware‑accelerated lightweight cryptographic primitives, the incorporation of explainable AI techniques into PETs, and active participation in international standardization efforts. They also call for pilot studies that assess performance, scalability, and compliance of proposed PPTs in operational environments.
Conclusion and Limitations
The paper delivers a structured overview of IoT privacy preservation research, highlighting prevailing techniques, dominant application areas, and unmet needs. Its limitation lies in the focus on peer‑reviewed academic literature, potentially overlooking industry patents and commercial solutions, and the cutoff at early 2023 may miss the most recent advances. Future work should therefore include gray literature, longitudinal studies, and rigorous field trials to validate the efficacy of emerging PPTs.
Comments & Academic Discussion
Loading comments...
Leave a Comment