ACORN-IDS: Adaptive Continual Novelty Detection for Intrusion Detection Systems
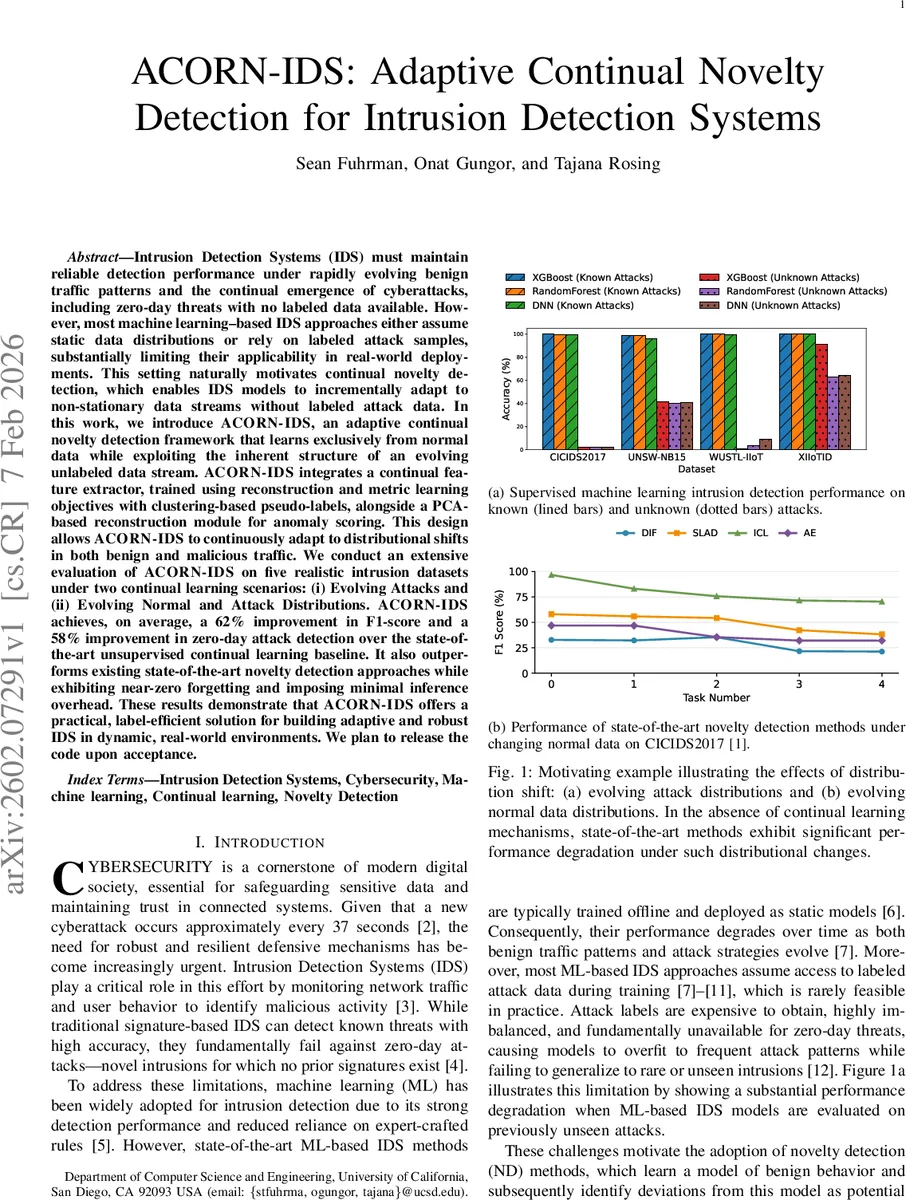
Intrusion Detection Systems (IDS) must maintain reliable detection performance under rapidly evolving benign traffic patterns and the continual emergence of cyberattacks, including zero-day threats with no labeled data available. However, most machine learning-based IDS approaches either assume static data distributions or rely on labeled attack samples, substantially limiting their applicability in real-world deployments. This setting naturally motivates continual novelty detection, which enables IDS models to incrementally adapt to non-stationary data streams without labeled attack data. In this work, we introduce ACORN-IDS, an adaptive continual novelty detection framework that learns exclusively from normal data while exploiting the inherent structure of an evolving unlabeled data stream. ACORN-IDS integrates a continual feature extractor, trained using reconstruction and metric learning objectives with clustering-based pseudo-labels, alongside a PCA-based reconstruction module for anomaly scoring. This design allows ACORN-IDS to continuously adapt to distributional shifts in both benign and malicious traffic. We conduct an extensive evaluation of ACORN-IDS on five realistic intrusion datasets under two continual learning scenarios: (i) Evolving Attacks and (ii) Evolving Normal and Attack Distributions. ACORN-IDS achieves, on average, a 62% improvement in F1-score and a 58% improvement in zero-day attack detection over the state-of-the-art unsupervised continual learning baseline. It also outperforms existing state-of-the-art novelty detection approaches while exhibiting near-zero forgetting and imposing minimal inference overhead. These results demonstrate that ACORN-IDS offers a practical, label-efficient solution for building adaptive and robust IDS in dynamic, real-world environments. We plan to release the code upon acceptance.
💡 Research Summary
Intrusion Detection Systems (IDS) face two intertwined challenges: the continual drift of benign traffic patterns and the emergence of zero‑day attacks for which no labeled data exist. Existing machine‑learning‑based IDS either assume static data distributions or rely on labeled attack samples, leading to rapid performance degradation in real deployments. To address this, the authors propose ACORN‑IDS, an Adaptive Continual Novelty Detection framework that learns exclusively from normal traffic while remaining capable of detecting unseen attacks.
The architecture consists of a Continual Feature Extractor (CFE) and a PCA‑based reconstruction module. The CFE is built on an encoder‑decoder network and is trained jointly with a reconstruction loss and a triplet‑margin metric‑learning loss. Unlabeled streaming data are clustered via K‑Means, and the resulting pseudo‑labels guide the metric learning, ensuring that embeddings remain discriminative across successive tasks and mitigating catastrophic forgetting. The PCA module is fitted only on a small clean normal set; during inference, reconstruction error serves as an anomaly score, flagging samples whose error exceeds a learned threshold.
For evaluation, the authors construct a sequence of tasks that simulate realistic IDS environments. Each task provides a tiny clean normal subset and a larger unlabeled stream containing both normal and attack samples. Normal data are partitioned into clusters to model gradual benign drift, while attack classes are distributed across tasks to emulate evolving adversarial behavior. Two continual‑learning scenarios are considered: (i) Evolving Attacks (EA) and (ii) Evolving Normal and Attack Distributions (EN‑A).
Experiments on five real intrusion datasets—including CICIDS2017, UNSW‑NB15, WUSTL‑IIoT, and XIIoTID—show that ACORN‑IDS outperforms the strongest unsupervised continual‑learning baseline (ADCN) by an average of 62 % in F1 score and 58 % in zero‑day detection rate. Compared with state‑of‑the‑art novelty‑detection methods (SLAD, ICL, DIF, AE), ACORN‑IDS achieves higher detection metrics, near‑zero forgetting across tasks, and minimal inference overhead. The replay‑based memory strategy, which interleaves representative samples from previous tasks, further stabilizes learning without complex regularization.
Key contributions are: (1) the first continual novelty‑detection IDS that jointly handles shifting normal and attack distributions without any attack labels; (2) a novel continual feature‑learning mechanism that combines reconstruction, metric learning, and clustering‑based pseudo‑labels; (3) integration of a lightweight PCA reconstruction scorer for effective zero‑day detection; and (4) extensive empirical validation demonstrating practical robustness and label efficiency. The authors plan to release code upon acceptance, paving the way for real‑world deployment of adaptive, label‑efficient IDS solutions.
Comments & Academic Discussion
Loading comments...
Leave a Comment