Jamming Attacks on the Random Access Channel in 5G and B5G Networks
Random Access Channel (RACH) jamming poses a critical security threat to 5G and beyond (B5G) networks. This paper presents an analytical model for predicting the impact of Msg1 jamming attacks on RACH performance. We use the OpenAirInterface (OAI) open-source user equipment (UE) to implement a Msg1 jamming attacker. Over-the-air experiments validate the accuracy of the proposed analytical model. The results show that low-power and stealthy Msg1 jamming can effectively block legitimate UE access in 5G/B5G systems.
💡 Research Summary
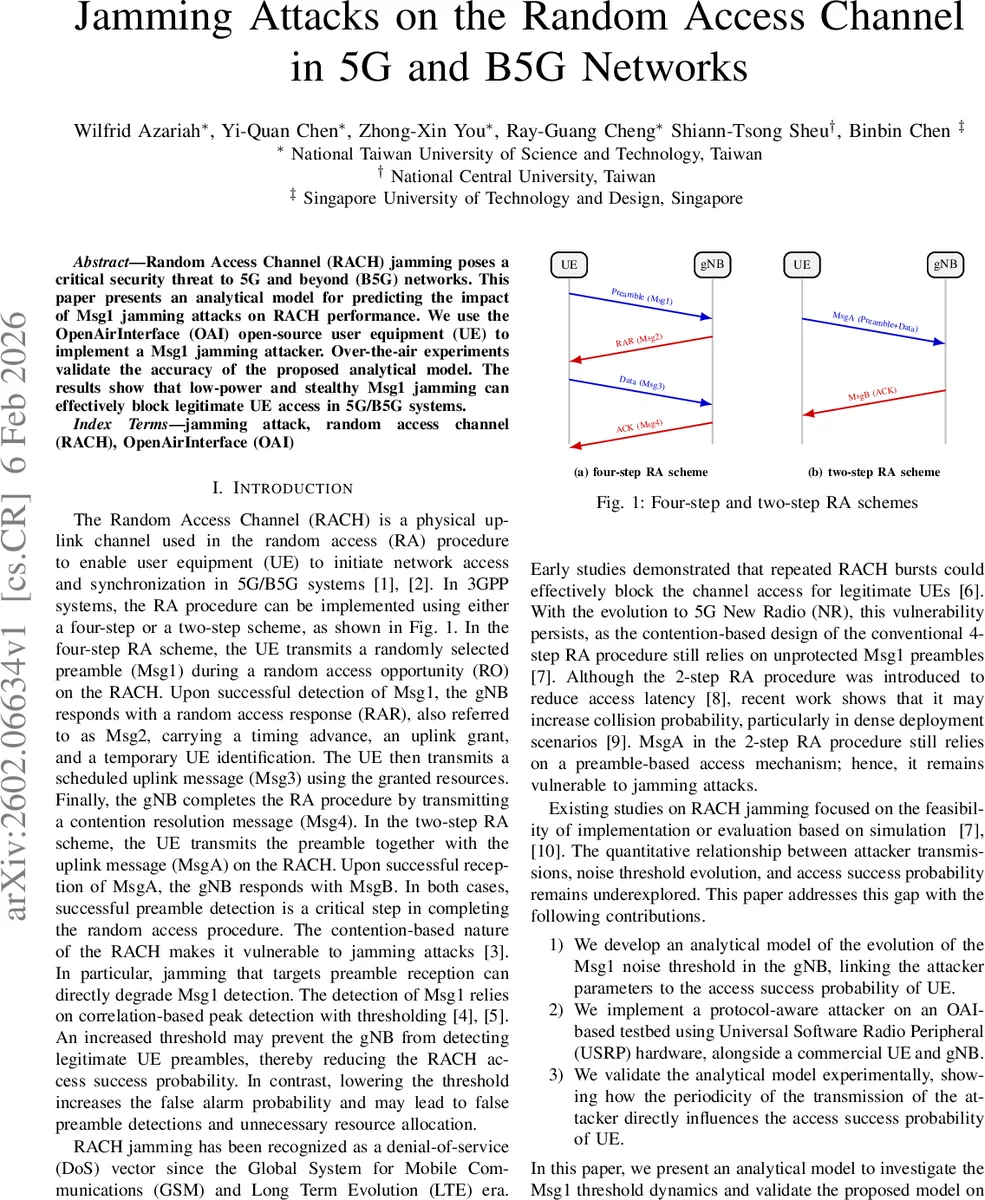
This paper investigates a denial‑of‑service (DoS) threat to 5G and beyond (B5G) networks that targets the Random Access Channel (RACH) by jamming the first message (Msg1), also known as the preamble. The authors develop a recursive analytical model that describes how the gNB’s noise detection threshold evolves under attack, linking attacker parameters (transmit power, periodicity) and gNB configuration parameters (α, β, γ weighting factors, detection margin δ) to the probability that a legitimate user equipment (UE) successfully completes the random‑access procedure.
The model assumes that the gNB updates its threshold p_th,i at each random‑access occasion (RO) as a weighted sum of the current measured power, the previous measured power, and the previous threshold. Different implementations are captured: OAI uses an exponential‑averaging scheme (α=0, β∈(0,1), γ=1‑β) while srsRAN uses an instantaneous update (α=1, β=0, γ=0). An attacker periodically injects a high‑power Msg1 (p_attacker) every T_a RO’s, thereby raising the measured power term in the recursion. For a continuous attacker (T_a=1) the threshold converges to (α+β)p_attacker/(1‑γ); for larger T_a the increase is slower and may decay toward background noise between attacks. The authors derive closed‑form expressions for the steady‑state threshold and show how the forgetting factor γ controls convergence speed.
To validate the theory, the authors build a testbed using OpenAirInterface (OAI) on Intel NUCs, a commercial Samsung 5G smartphone as the legitimate UE, and an OAI‑based nrUE modified to act as a Msg1 jammer. USRP B210 radios provide over‑the‑air transmission. Experimental parameters follow 3GPP specifications: background noise 17.4 dB, attacker power 51 dB, UE power 56.4 dB, sub‑carrier spacing 30 kHz, bandwidth 40 MHz, etc. Three attacker periodicities are examined: T_a=1 (continuous flooding), T_a=2 (moderate duty cycle), and T_a=16 (stealthy low‑duty). Additionally, the impact of the noise‑update factor β (0.24, 0.12, 0.06, 0) and detection margin δ (varied) is studied.
Results show strong agreement between the analytical predictions and measured threshold evolution (p_th) and access success probability (P_S). With T_a=1 the threshold rises rapidly, surpasses the UE’s Msg1 power, and blocks access; with T_a=2 the rise is slower; with T_a=16 the effect is minimal. Smaller β values slow threshold adaptation, temporarily preserving UE access but reducing the system’s ability to react to genuine interference. Lower δ improves UE success by requiring a smaller margin above the threshold, yet overly low δ leads to false alarms. Experiments on srsRAN confirm that even memoryless threshold updates are vulnerable: a single high‑power attacker transmission can cause a temporary spike that blocks UE access.
The paper concludes that Msg1 jamming is an effective DoS vector because the preamble is unprotected and UE transmit power is limited by PRACH power‑control rules. The recursive model accurately captures the dynamics and can be used to evaluate mitigation strategies. Future work is suggested in two directions: (1) extending the attacker to generate multiple preambles across several RO’s simultaneously, increasing spectral occupancy; (2) designing adaptive defenses such as dynamic adjustment of γ, machine‑learning‑based noise estimation, or incorporating authentication into the preamble exchange.
Overall, the study provides a rigorous quantitative framework for understanding RACH vulnerability, validates it with real‑world over‑the‑air experiments, and highlights practical parameters that network operators can tune to improve resilience against Msg1 jamming attacks.
Comments & Academic Discussion
Loading comments...
Leave a Comment