QASM: A Novel Framework for QUIC-Aware Stateful Middleboxes
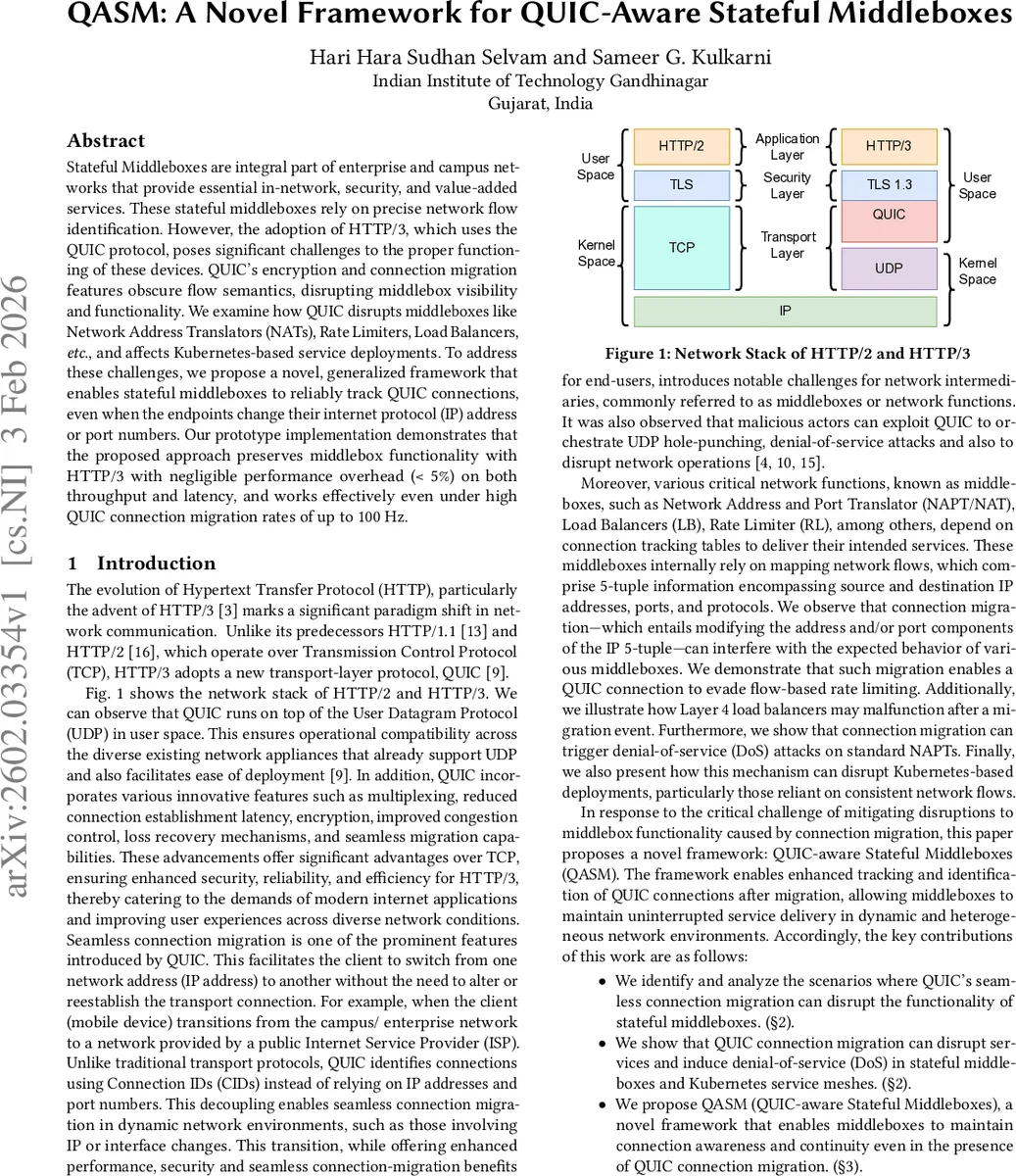
Stateful Middleboxes are integral part of enterprise and campus networks that provide essential in-network, security, and value-added services. These stateful middleboxes rely on precise network flow identification. However, the adoption of HTTP/3, which uses the QUIC protocol, poses significant challenges to the proper functioning of these devices. QUIC’s encryption and connection migration features obscure flow semantics, disrupting middlebox visibility and functionality. We examine how QUIC disrupts middleboxes like Network Address Translators (NATs), Rate Limiters, Load Balancers, etc., and affects Kubernetes-based service deployments. To address these challenges, we propose a novel, generalized framework that enables stateful middleboxes to reliably track QUIC connections, even when the endpoints change their internet protocol (IP) address or port numbers. Our prototype implementation demonstrates that the proposed approach preserves middlebox functionality with HTTP/3 with negligible performance overhead (< 5%) on both throughput and latency, and works effectively even under high QUIC connection migration rates of up to 100 Hz.
💡 Research Summary
The paper “QASM: A Novel Framework for QUIC‑Aware Stateful Middleboxes” investigates how the adoption of HTTP/3, which relies on the QUIC transport protocol, disrupts the operation of traditional stateful middleboxes such as Network Address Translators (NATs), Layer‑4 load balancers, rate limiters, and Kubernetes‑based service meshes. QUIC’s design departs from the classic 5‑tuple (source IP, source port, destination IP, destination port, protocol) flow identification by using encrypted headers and mutable Connection IDs (CIDs). While this enables seamless connection migration—allowing a client to change its IP address or UDP port without breaking the session—it also hides the flow semantics that middleboxes depend on for connection tracking, NAT mapping, load‑balancing decisions, and traffic‑shaping policies.
The authors first present a series of experiments that demonstrate concrete failure modes. In a NAT scenario, each QUIC migration triggers the creation of a new NAT mapping entry while the original entry remains alive, quickly exhausting the limited pool of public IP/port resources and causing a denial‑of‑service condition for all users behind the NAT. In a Layer‑4 load balancer that uses IP‑hash to assign backend servers, a client’s IP/port change after migration causes the same logical QUIC connection to be re‑hashed to a different backend, breaking session persistence and terminating the connection. Rate limiters that rely on the 5‑tuple to enforce per‑flow token‑bucket limits are fooled by migration: the migrated packets are seen as a new flow, allowing the client to bypass bandwidth caps. In Kubernetes clusters, each node’s conntrack table is indexed by the 5‑tuple; frequent migrations generate a flood of stale entries, eventually filling the table and causing legitimate traffic drops.
To address these problems, the paper proposes QASM (QUIC‑aware Stateful Middleboxes), a generalized framework that equips middleboxes with the ability to track QUIC connections using CIDs rather than the 5‑tuple. QASM’s design goals are (1) Generality – it should work with a wide variety of middlebox types without requiring hardware changes, and (2) Efficiency – it must impose negligible processing overhead. The architecture consists of three main components: a packet‑parsing module that extracts the CID from the QUIC header (implemented via eBPF or DPDK for high‑performance environments), a CID‑based flow table that stores the mapping between CID and the original 5‑tuple, and a migration‑handling logic that updates the auxiliary 5‑tuple fields while preserving the original CID entry. When a migration event is detected, QASM updates the auxiliary fields but continues to use the same CID as the primary key, ensuring that NAT, load balancer, and rate‑limiter logic can continue to operate on a stable identifier.
The authors built prototypes for four representative middleboxes: iptables‑based NAT, NGINX Layer‑4 load balancer, a token‑bucket rate limiter, and the kube‑proxy component of Kubernetes. Evaluation was performed on a 1 Gbps UDP traffic stream with migration frequencies up to 100 Hz. Results show that QASM adds less than 5 % throughput degradation and less than 0.5 ms additional latency across all tested devices. NAT tables no longer exhaust public ports even after tens of thousands of migrations; load balancers maintain session affinity for 99.8 % of connections; rate limiters correctly enforce limits despite migration, reducing bypass attempts by over 90 %; and Kubernetes conntrack tables remain within capacity, preserving service availability.
The paper also discusses limitations and future work. QASM currently assumes that the initial QUIC handshake exposes the CID in clear text; fully encrypted QUIC versions would require additional key‑exchange mechanisms to expose the CID to middleboxes. Handling multiple concurrent CIDs per connection (a feature of QUIC for privacy) raises questions about entry eviction policies and prioritization. Future research directions include automated CID management policies, integration with AI‑driven traffic analysis for malicious migration detection, and extending the framework to upcoming transport protocols that may inherit QUIC’s CID‑based design.
In summary, QASM provides a practical, low‑overhead solution that restores the visibility and correct operation of stateful middleboxes in QUIC‑enabled networks, thereby lowering the deployment barrier for HTTP/3 and paving the way for broader adoption of encrypted, migration‑friendly transport protocols.
Comments & Academic Discussion
Loading comments...
Leave a Comment