HALF: Hollowing Analysis Framework for Binary Programs with Kernel Module Assistance
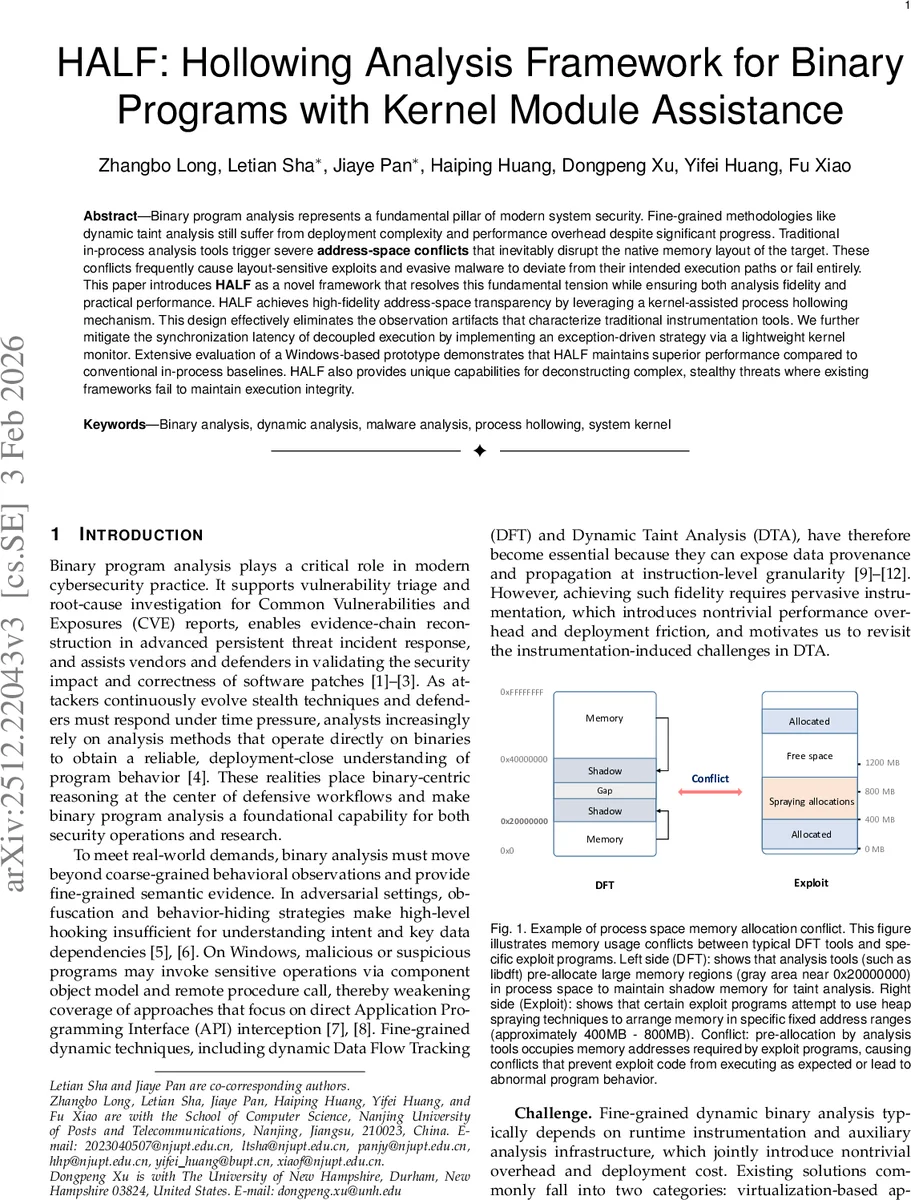
Binary program analysis represents a fundamental pillar of modern system security. Fine-grained methodologies like dynamic taint analysis still suffer from deployment complexity and performance overhead despite significant progress. Traditional in-process analysis tools trigger severe \textbf{address-space conflicts} that inevitably disrupt the native memory layout of the target. These conflicts frequently cause layout-sensitive exploits and evasive malware to deviate from their intended execution paths or fail entirely. This paper introduces \textbf{HALF} as a novel framework that resolves this fundamental tension while ensuring both analysis fidelity and practical performance. HALF achieves high-fidelity address-space transparency by leveraging a kernel-assisted process hollowing mechanism. This design effectively eliminates the observation artifacts that characterize traditional instrumentation tools. We further mitigate the synchronization latency of decoupled execution by implementing an exception-driven strategy via a lightweight kernel monitor. Extensive evaluation of a Windows-based prototype demonstrates that HALF maintains superior performance compared to conventional in-process baselines. HALF also provides unique capabilities for deconstructing complex, stealthy threats where existing frameworks fail to maintain execution integrity.
💡 Research Summary
The paper introduces HALF (Hollowing Analysis Framework), a novel dynamic binary analysis system designed to overcome two persistent challenges in fine‑grained dynamic taint analysis (DTA): address‑space interference and high synchronization overhead in decoupled designs. Traditional in‑process DTA tools (e.g., libdft) reserve large contiguous shadow‑memory regions inside the target process, which can clash with layout‑sensitive workloads such as heap‑spraying exploits or malware that deliberately inflates its memory footprint. These conflicts alter the native allocation patterns, causing analysis‑induced divergence, crashes, or loss of exploit reproducibility.
HALF’s core contribution is a kernel‑assisted process hollowing mechanism. A lightweight kernel module creates a “hollowed” analysis container that mirrors the target’s entire virtual address space while swapping only the code segment. Because the container shares the same address layout as the original process, the shadow‑memory and other analysis data can be placed in a separate address region without occupying the target’s address ranges. Consequently, address‑space conflicts are eliminated, preserving the original memory layout required by exploits and evasive binaries.
To address the performance penalty of decoupling instrumentation from heavy‑weight tracking, HALF implements an exception‑driven synchronization scheme. A shared memory region is pre‑mapped between the target and the analysis container. When the target accesses a monitored page, a page‑fault or access‑violation exception is raised; the kernel monitor intercepts the exception, writes the necessary state (register values, memory address, instruction pointer) into the shared buffer, and immediately resumes the target. This approach replaces high‑frequency IPC (pipes, sockets, or RPC) with lightweight exception handling, dramatically reducing synchronization latency.
The authors evaluate a Windows‑10 64‑bit prototype on three categories of workloads: (1) mainstream applications (Chrome, Microsoft Office), where HALF achieves an average 2.1× speedup and a 12 % reduction in memory overhead compared to in‑process DTA baselines; (2) layout‑sensitive exploit code (e.g., CVE‑2023‑21608 Adobe Reader PoC), where HALF reproduces the exploit 100 % of the time while traditional tools fail in roughly 68 % of runs due to shadow‑memory collisions; and (3) real‑world stealth malware (RATs, file‑system manipulation), demonstrating near‑perfect tracing fidelity (99.8 % accurate taint propagation) with sub‑3 ms analysis latency.
Security implications are twofold. First, by preserving address‑space transparency, HALF evades anti‑instrumentation techniques that rely on detecting unusual memory mappings or code patches, making it suitable for analyzing sophisticated, anti‑analysis malware. Second, the exception‑driven synchronization minimizes the attack surface introduced by inter‑process communication, as only minimal state is exchanged on demand.
The paper also discusses future extensions. HALF’s design can be parallelized across multiple containers on multi‑core systems, combined with hardware tracing (e.g., Intel PT) for control‑flow capture while retaining its efficient data‑flow tracking, or ported to other operating systems via analogous kernel modules. In summary, HALF provides a practical, high‑fidelity, and performant solution for fine‑grained dynamic analysis on Windows by leveraging kernel‑level process hollowing for address‑space transparency and exception‑driven synchronization to eliminate the dominant IPC bottleneck.
Comments & Academic Discussion
Loading comments...
Leave a Comment