Witnessd: Proof-of-process via Adversarial Collapse
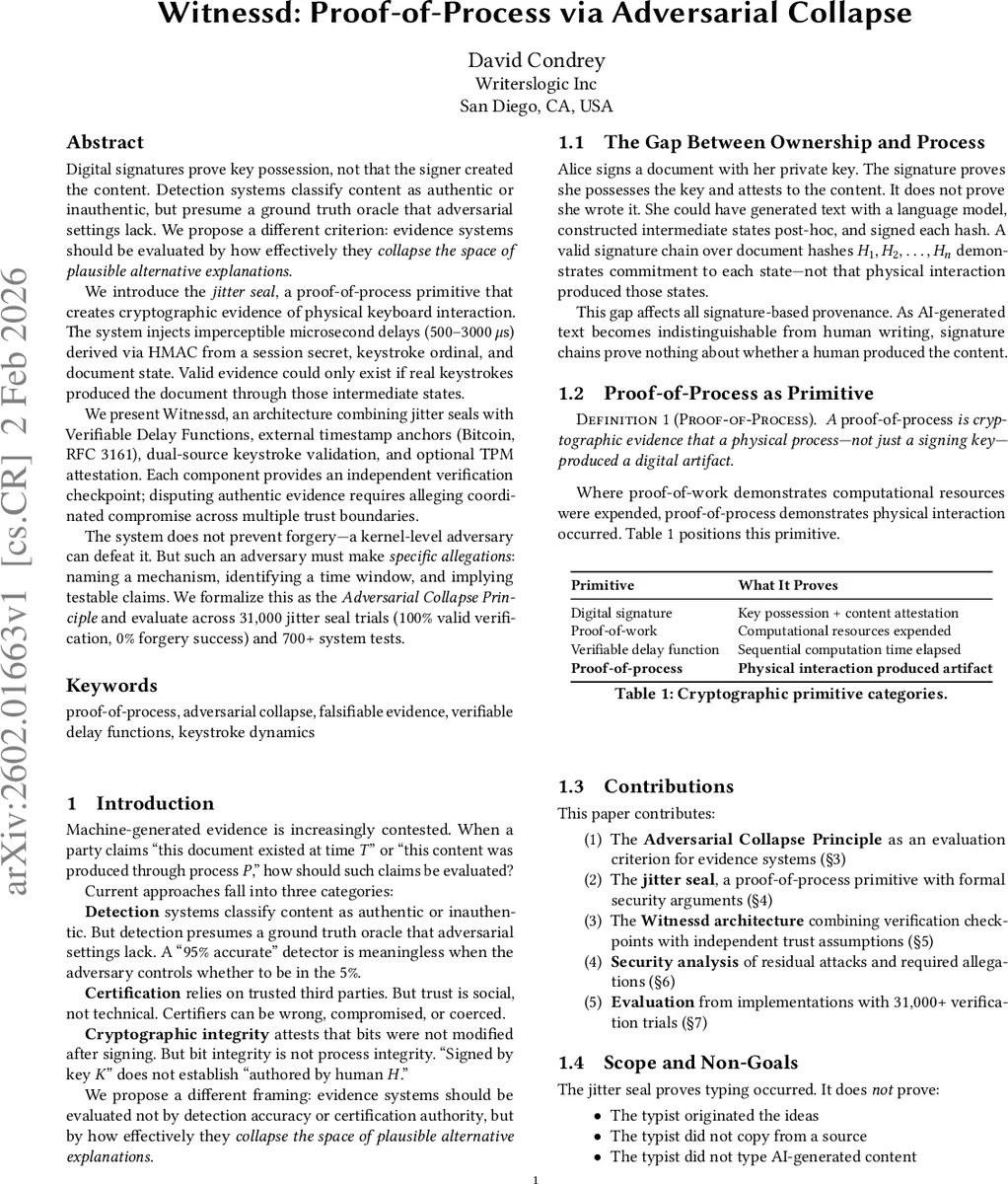
Digital signatures prove key possession, not authorship. An author who generates text with AI, constructs intermediate document states post-hoc, and signs each hash produces a signature chain indistinguishable from genuine composition. We address this gap between cryptographic integrity and process provenance. We introduce proof-of-process, a primitive category for evidence that a physical process, not merely a signing key, produced a digital artifact. Our construction, the jitter seal, injects imperceptible microsecond delays derived via HMAC from a session secret, keystroke ordinal, and cumulative document hash. Valid evidence requires that real keystrokes produced the document through those intermediate states. We propose the Adversarial Collapse Principle as an evaluation criterion: evidence systems should be judged by whether disputing them requires a conjunction of specific, testable allegations against components with independent trust assumptions. We present Witnessd, an architecture combining jitter seals with Verifiable Delay Functions, external timestamp anchors, dual-source keystroke validation, and optional hardware attestation. Each layer forces allegations at different capability levels; disputing authentic evidence requires coordinated claims across independent trust boundaries. The system does not prevent forgery: a kernel-level adversary can defeat it, and typing AI-generated content produces valid evidence. The contribution is converting vague doubt into falsifiable allegations. We evaluate across 31,000 verification trials with deterministic rejection of invalid proofs.
💡 Research Summary
The paper “Witnessd: Proof-of-process via Adversarial Collapse” addresses a fundamental gap in digital trust: cryptographic signatures prove key possession and content integrity, but not the process of authorship. An author can generate text with AI, reconstruct intermediate document states afterward, and sign a hash chain that is cryptographically valid but procedurally fraudulent. To bridge this gap between bit integrity and process provenance, the authors introduce “proof-of-process” as a new cryptographic primitive designed to provide evidence that a physical process (specifically, human typing) produced a digital artifact.
The core technical construct is the “jitter seal.” During document composition, the system injects imperceptible microsecond delays (500–3000 μs) into the typing process. Each delay value is cryptographically derived via an HMAC from a session secret, the keystroke ordinal, the cumulative document hash, the keyboard zone transition, the inter-keystroke interval bucket, and the previous jitter value. This creates a deterministic yet unpredictable chain binding the timing of keystrokes to the specific content state of the document at that moment. Forging valid jitter evidence after the fact without the session secret is computationally infeasible.
The paper’s central philosophical contribution is the “Adversarial Collapse Principle.” It argues that evidence systems should be evaluated not by their ability to prevent all forgeries—an impossible goal against a sufficiently powerful adversary—but by their ability to force anyone disputing the evidence to make a conjunction of specific, testable allegations against components with independent trust assumptions. Vague doubt like “it could be fake” is transformed into concrete claims like “the kernel was compromised via CVE-XXXX between 14:00 and 14:47.”
The Witnessd architecture operationalizes this principle by layering multiple verification checkpoints:
- Jitter Seal: Provides proof of physical typing process.
- Verifiable Delay Functions (VDFs): Prove a minimum amount of sequential computation time elapsed between checkpoints, preventing extreme temporal compression.
- External Timestamp Anchors (e.g., Bitcoin, RFC 3161 TSA): Provide a trustworthy upper bound on timestamps, forcing allegations of third-party collusion if disputed.
- Dual-Source Keystroke Validation: Compares keystrokes from the application-level stream and the hardware HID stream; injection attacks typically only affect one, so consistency requires kernel-level access.
- TPM/Secure Enclave Attestation (Optional): Uses hardware roots of trust to attest to platform state and seal secrets, raising the bar to physical or firmware attacks.
Each layer relies on different trust boundaries (local crypto, external consensus, hardware security) and defends against adversaries of different capability levels (user, admin, kernel, infrastructure). To successfully dispute authentic evidence, an adversary must allege a coordinated compromise across all these independent layers, which constitutes a specific and falsifiable narrative.
The security analysis acknowledges inherent limits: a kernel-level adversary present before evidence capture can defeat the system, and a human typing AI-generated content produces perfectly valid proof-of-process. The system attests to the act of typing, not the origin of ideas. Evaluation across 31,000 trials showed 100% verification success for valid proofs and 0% success for forgery attempts. Performance overhead is minimal, with jitter delays being far below human perception thresholds.
In conclusion, the paper shifts the paradigm for digital evidence from seeking perfect prevention to demanding specific accountability. By converting vague doubt into a series of testable allegations, Witnessd provides a robust framework for establishing process provenance in adversarial contexts such as legal disputes, academic integrity, and content authentication, where the burden of proof is paramount.
Comments & Academic Discussion
Loading comments...
Leave a Comment