Authenticated encryption for space telemetry
We explore how command stack protection requirements outlined in NASA-STD-1006A can be satisfied within the context of emergency space telemetry. Proposed implementation of lightweight authenticated encryption offers strong security without sacrificing performance in resource-constrained environments. It produces fixed-length messages, maintaining compatibility with the underlying data transport protocols. By focusing on predictable properties and robust authentication, we create a scheme that protects the confidentiality, integrity and authenticity of telemetry data in emergency communications while balancing security requirements with the operational constraints.
💡 Research Summary
**
The paper “Authenticated encryption for space telemetry” addresses the pressing need to protect emergency telemetry data transmitted from spacecraft while adhering to the stringent security requirements of NASA‑STD‑1006A and CCSDS recommendations. Current Second Generation Beacon (SGB) messages are sent in clear text, exposing the satellite’s operational state to potential adversaries and leaving the system vulnerable to confidentiality breaches, denial‑of‑service attacks, message tampering, and replay attacks. The authors propose a lightweight, deterministic authenticated encryption scheme based on AES‑GCM, a well‑studied algorithm with widespread hardware acceleration support, making it suitable for power‑constrained, compute‑limited space platforms.
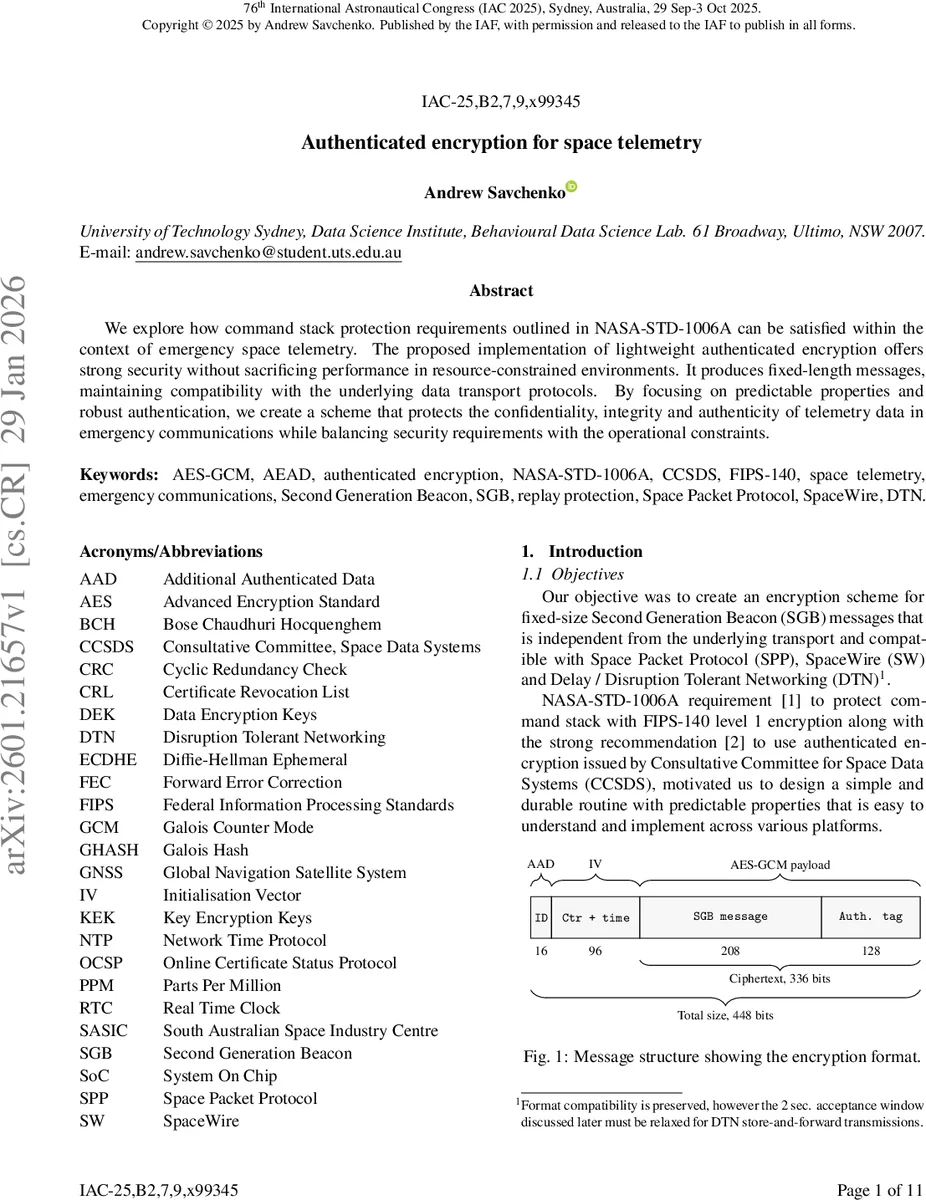
Key design choices include a fixed‑size 448‑bit (56‑byte) frame that consists of a 2‑byte Additional Authenticated Data (AAD) asset identifier, a 12‑byte initialization vector (IV), a 208‑bit (26‑byte) encrypted payload, and a 128‑bit authentication tag. The IV is constructed from a 64‑bit timestamp and a 32‑bit monotonic counter, guaranteeing uniqueness without the need for random number generation and simplifying replay‑protection logic. The 96‑bit IV conforms to the GCM standard, avoiding the more costly GHASH processing required for non‑standard nonce sizes.
The authors carefully analyse the system constraints typical of low‑Earth‑orbit (LEO) missions: limited power budget due to solar array degradation, a 9.6 kb/s UHF downlink, modest CPU resources, non‑volatile memory for storing the counter, and short ground‑station contact windows (5–15 minutes). From these constraints they derive operational parameters such as a ≤1 Hz transmission rate and a payload size of roughly 450 bits, which keeps the encryption overhead within the available bandwidth.
A detailed timing and link‑budget analysis demonstrates that the additional 79 % overhead of the encrypted frame (448 bits versus the original 250‑bit SGB frame) translates into a negligible increase in end‑to‑end latency (≈20 ms) and Doppler shift (≈0.8 kHz). Propagation delay, satellite motion, and antenna beam footprint are all quantified, showing that the overhead does not materially affect the ability to deliver emergency telemetry within the tight latency windows required for command‑and‑control operations.
The protocol flow is straightforward: the transmitter generates the timestamp, increments the counter, forms the IV, encrypts the payload with AES‑GCM using a pre‑shared symmetric key, and concatenates AAD, IV, ciphertext, and tag. The receiver parses the fields, verifies that the timestamp falls within a 2‑second acceptance window (accounting for clock drift up to ±3 ppm), checks that the counter and timestamp are greater than the last accepted values (providing replay protection), and then decrypts and authenticates the message. All fields are treated as big‑endian, and the authentication tag size of 128 bits follows the CCSDS 352.0‑B‑2 recommendation for MAC security.
Security analysis highlights several strengths: deterministic nonce generation eliminates the risk of IV reuse; hardware‑accelerated AES‑GCM offers strong confidentiality and integrity with low power consumption; the scheme meets FIPS‑140 Level 1 requirements; and the fixed‑size frame simplifies integration with existing transport layers such as the Space Packet Protocol (SPP), SpaceWire (SW), and Delay‑Tolerant Networking (DTN). However, the reliance on a pre‑shared symmetric key introduces a single point of failure: if the key is compromised, forward secrecy is lost and all past telemetry could be decrypted. The paper deliberately avoids public‑key infrastructure (PKI) to keep computational overhead low, but this trade‑off may be problematic for long‑duration missions where key rotation is desirable.
The authors acknowledge this limitation and suggest future work could explore lightweight public‑key mechanisms (e.g., ECC‑based Diffie‑Hellman) to provide forward secrecy without excessive cost. They also note that the 128‑bit tag could be reduced for bandwidth‑critical scenarios, and that a more sophisticated key‑management framework would be needed for constellations involving many satellites and multiple ground stations.
In conclusion, the paper delivers a pragmatic, standards‑compliant solution for securing emergency space telemetry. By leveraging AES‑GCM with a timestamp‑counter IV, fixing the message size, and implementing a simple replay‑protection window, the authors achieve the required confidentiality, integrity, and authenticity while respecting the severe power, processing, and bandwidth constraints of spacecraft. The work bridges the gap between high‑assurance cryptographic practice and the operational realities of space missions, and it lays a solid foundation for future enhancements that could incorporate forward secrecy and scalable key distribution for larger satellite constellations.
Comments & Academic Discussion
Loading comments...
Leave a Comment