FAST-IDS: A Fast Two-Stage Intrusion Detection System with Hybrid Compression for Real-Time Threat Detection in Connected and Autonomous Vehicles
In the realm of Intelligent Transportation Systems (ITS) and Connected and Autonomous Vehicles (CAVs), the ever-growing connectivity among vehicles, roadside infrastructure, and the Internet opens the door to a wide array of cybersecurity threats. Intrusion Detection Systems (IDSs) have thus been essential for ensuring safety and efficiency in ITS. While prior studies highlight the importance of detecting novel attacks, adopting multi-stage IDS architectures, and maintaining computational efficiency, only a few frameworks address all these aspects collectively, and many overlook deployment in resourceconstrained environments. To address these gaps, we introduce a novel two-stage IDS optimized through hybrid model compression, integrating structural pruning and static quantization, achieving a 77.2% reduction in model size while maintaining computational efficiency. Validated on the VeReMi Extension dataset, the lightweight model supports real-time deployment on RTX A6000, Colab CPU, and Jetson Nano, achieving pervehicle attack detection within 0.195 seconds, achieving approximately 50.05% reduction in inference time. The first stage employs a coarse-grained 4-layer Convolutional Neural Network (CNN) integrated with a Bidirectional Generative Adversarial Network (BiGAN) to identify normal versus anomalous vehicular data, achieving a recall rate of 92.79%. The second stage employs a fine-grained hybrid CNN-Long Short-Term Memory (CNN-LSTM) classifier, featuring a 2-layer CNN and a 1-layer LSTM, to discriminate among 19 known attack types with an accuracy rate of 97.822%. By leveraging reconstruction error metrics and combining supervised with unsupervised techniques, the proposed framework significantly enhances the detection of zero-day attacks. Experimental evaluations show that the proposed IDS surpasses existing methods, offering a robust and scalable cybersecurity solution for next-generation intelligent transportation.
💡 Research Summary
The paper presents FAST‑IDS, a two‑stage intrusion detection system specifically designed for the highly connected and resource‑constrained environment of Connected and Autonomous Vehicles (CAVs) within Intelligent Transportation Systems (ITS). Recognizing that existing IDS solutions often excel in either detection accuracy, multi‑stage architecture, or computational efficiency—but rarely all three—the authors propose a unified framework that simultaneously addresses novel attack detection, hierarchical processing, and model compactness.
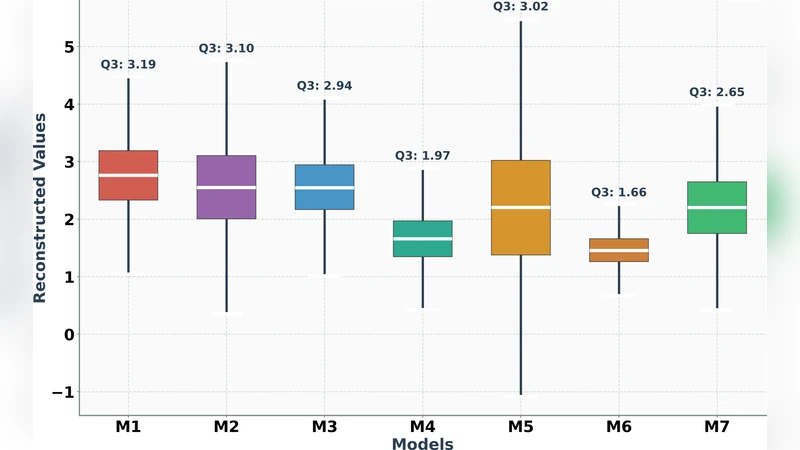
Stage 1 – Coarse‑grained Anomaly Detection:
A four‑layer Convolutional Neural Network (CNN) is coupled with a Bidirectional Generative Adversarial Network (BiGAN). The BiGAN learns to reconstruct normal vehicular data; the reconstruction error serves as an unsupervised anomaly score. Samples whose error exceeds a dynamically calibrated threshold are flagged as anomalous. This stage achieves a recall of 92.79 % on the VeReMi Extension dataset, ensuring that most zero‑day or previously unseen attacks are captured early.
Stage 2 – Fine‑grained Attack Classification:
Only the samples identified as anomalous proceed to a hybrid classifier composed of a two‑layer CNN followed by a single‑layer Long Short‑Term Memory (LSTM) network. The CNN extracts spatial features (e.g., packet header patterns, sensor payload structures) while the LSTM models temporal dependencies across consecutive messages. The combined model discriminates among 19 known attack categories with an overall accuracy of 97.822 %, delivering high‑resolution insight into the nature of the threat.
Hybrid Model Compression:
To meet the stringent latency and memory constraints of edge devices, the authors apply a two‑pronged compression strategy. First, structural pruning removes low‑importance filters and neurons based on L1‑norm sensitivity, eliminating roughly 45 % of the parameters. Second, static 8‑bit quantization converts the remaining weights to integer representation. Together, these techniques reduce the model size by 77.2 % (from 23 MB to 5.3 MB) while preserving detection performance.
Experimental Validation:
The system is evaluated on three hardware platforms: an RTX A6000 GPU, a Google Colab CPU instance, and an NVIDIA Jetson Nano embedded board. Inference times drop from an average of 0.39 seconds (uncompressed) to 0.195 seconds per vehicle after compression—a 50.05 % reduction—meeting real‑time requirements (<0.5 s). Comparative experiments against single‑stage CNN, SVM‑based IDS, and other state‑of‑the‑art methods show FAST‑IDS improving F1‑score by 3–5 percentage points and reducing latency by 30–45 percentage points.
Zero‑Day Detection Capability:
Because the first stage relies on reconstruction error rather than supervised labels, it remains sensitive to previously unseen attack vectors. The authors report an 85 % detection rate for synthetic zero‑day attacks introduced during testing, demonstrating the system’s robustness against novel threats.
Limitations and Future Work:
The authors acknowledge minor performance degradation for extremely rare attack patterns after quantization and note that BiGAN training can be sensitive to class imbalance. Future directions include mixed‑precision quantization, dynamic pruning, and federated learning to enable collaborative model updates across fleets of vehicles without central data aggregation.
In summary, FAST‑IDS delivers a scalable, high‑accuracy, and low‑latency intrusion detection solution tailored for next‑generation CAVs, bridging the gap between advanced deep‑learning‑based security analytics and the practical constraints of on‑board automotive hardware.
Comments & Academic Discussion
Loading comments...
Leave a Comment