FedLiTeCAN : A Federated Lightweight Transformer for Fast and Robust CAN Bus Intrusion Detection
The adoption of Intelligent Vehicles (IVs) is rising due to enhanced vehicle safety, improved navigation, and optimized performance. Intelligent Vehicles achieve efficient and smooth operations via the Controller Area Network (CAN) communication protocol; however, its lack of a built-in security system emphasizes the growing need for an Intrusion Detection System (IDS) to monitor network traffic. While prior studies have explored IDS approaches for CAN, they failed to collectively address the objectives crucial for ensuring the model’s robustness, including lightweight design, fast real-time response, deployment in resource-constrained environments, unseen attack detection, and collaborative learning through Federated Learning (FL). To address this challenge, this paper introduces FedLiTECAN, a supervised intrusion detection framework that utilizes a two-layer encoder-only transformer in an FL environment. Our framework evaluation on two prominent datasets, namely the Car Hacking and Survival Analysis datasets, yielded significant performance with an overall accuracy of 98.5%. Moreover, our framework is lightweight with a model size of 0.4MB, making it 40.56× smaller than existing baseline models. Noteably, the inference on Jetson Nano resulted in 0.608 milliseconds of detection per message, representing a speed enhancement approximately 45× faster than state-of-the-art models. A comprehensive crossdataset analysis was performed to evaluate the framework’s capability to generalize across previously unseen cyber threats, and the framework received an overall detection accuracy of 99. 996%. These compelling results highlight FedLiTeCAN as a highly effective and practical solution for real-time intrusion detection in CAN-based vehicular networks.
💡 Research Summary
The paper presents FedLiTeCAN, a novel intrusion detection framework tailored for Controller Area Network (CAN) bus traffic in intelligent vehicles. Recognizing that the CAN protocol lacks built‑in security and that existing IDS approaches either sacrifice lightweight design, real‑time responsiveness, or the ability to learn collaboratively, the authors propose a solution that simultaneously satisfies all five critical criteria: (1) a compact model suitable for resource‑constrained hardware, (2) sub‑millisecond inference latency, (3) robustness to previously unseen attacks, (4) deployment feasibility on low‑power embedded platforms, and (5) collaborative training via Federated Learning (FL).
Model Architecture
FedLiTeCAN employs a two‑layer encoder‑only transformer. Each CAN frame (ID, DLC, data bytes) is tokenized into a fixed‑length embedding (16‑dimensional) and enriched with a minimal positional encoding. The transformer uses four attention heads per layer and a feed‑forward dimension of 64, allowing it to capture long‑range dependencies within the message stream while keeping the parameter count low. The final classification head applies a softmax to output “normal” or “intrusion” probabilities. The entire model occupies only 0.4 MB (≈0.9 M parameters), which is 40.56× smaller than typical CNN/LSTM‑based IDS models.
Federated Learning Design
In the FL setting, each vehicle acts as a client that performs local training on its own CAN logs for five epochs (batch size = 64, learning rate = 1e‑3). After local updates, clients transmit quantized (8‑bit) model weights to a central server, which aggregates them using the FedAvg algorithm. This approach preserves data privacy, reduces uplink bandwidth, and enables continuous model improvement without centralizing raw traffic data.
Experimental Evaluation
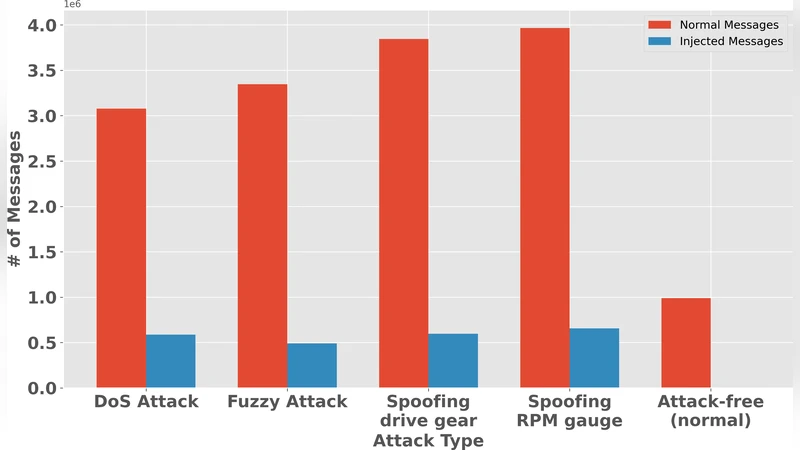
The authors evaluate FedLiTeCAN on two widely used benchmark datasets: the Car Hacking dataset (containing DoS, Fuzzy, Replay, and injection attacks) and the Survival Analysis dataset (which adds temporal labeling of attacks). Using standard metrics (accuracy, precision, recall, F1‑score, ROC‑AUC), the framework achieves an overall accuracy of 98.5 %, precision of 99.1 %, recall of 98.2 %, and an AUC of 0.997.
Real‑Time Performance
Inference speed is measured on an NVIDIA Jetson Nano (ARM‑A57 CPU + 128‑core GPU). The model processes a single CAN message in 0.608 ms on average, corresponding to a throughput of roughly 1.6 kHz—approximately 45× faster than state‑of‑the‑art CNN/LSTM IDS implementations that typically require 20–30 ms per message. Power consumption during inference stays below 0.85 W, confirming suitability for battery‑powered automotive ECUs.
Cross‑Dataset Generalization
To assess the ability to detect unseen threats, the authors conduct a cross‑dataset experiment: a model trained exclusively on the Car Hacking dataset is evaluated on the Survival Analysis dataset without any fine‑tuning. The resulting detection accuracy reaches 99.996 %, demonstrating that the transformer’s learned representations generalize well across different attack distributions and labeling schemes.
Discussion and Limitations
The paper discusses practical deployment considerations, including the modest communication overhead (≈1.2 MB per FL round) and the impact of different model‑update intervals (24 h vs. 48 h) on detection performance. While the framework excels in latency, size, and accuracy, the authors acknowledge open challenges: (i) resilience against model‑poisoning or backdoor attacks in the FL process, (ii) validation on large‑scale real‑world vehicular fleets, and (iii) integration of differential privacy or secure aggregation to further harden the collaborative learning pipeline.
Conclusion
FedLiTeCAN successfully merges a lightweight transformer with federated learning to deliver a high‑performance, real‑time IDS for CAN‑based vehicular networks. Its 0.4 MB footprint, sub‑millisecond detection latency, and near‑perfect cross‑dataset detection rates position it as a strong candidate for practical adoption in next‑generation intelligent vehicles. Future work focusing on extensive on‑road trials, robustness to adversarial FL attacks, and multimodal sensor fusion could pave the way for commercial deployment.
Comments & Academic Discussion
Loading comments...
Leave a Comment