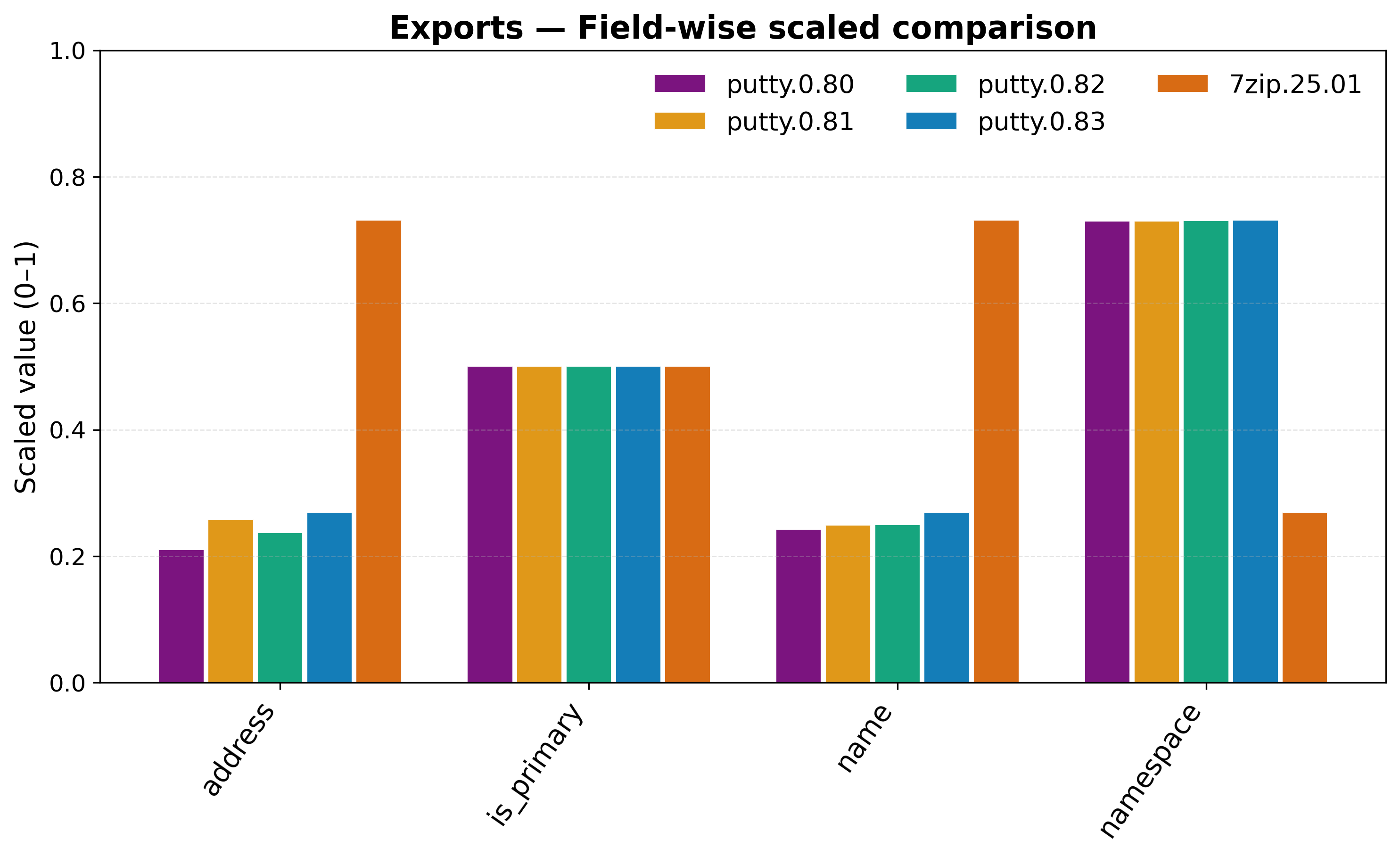
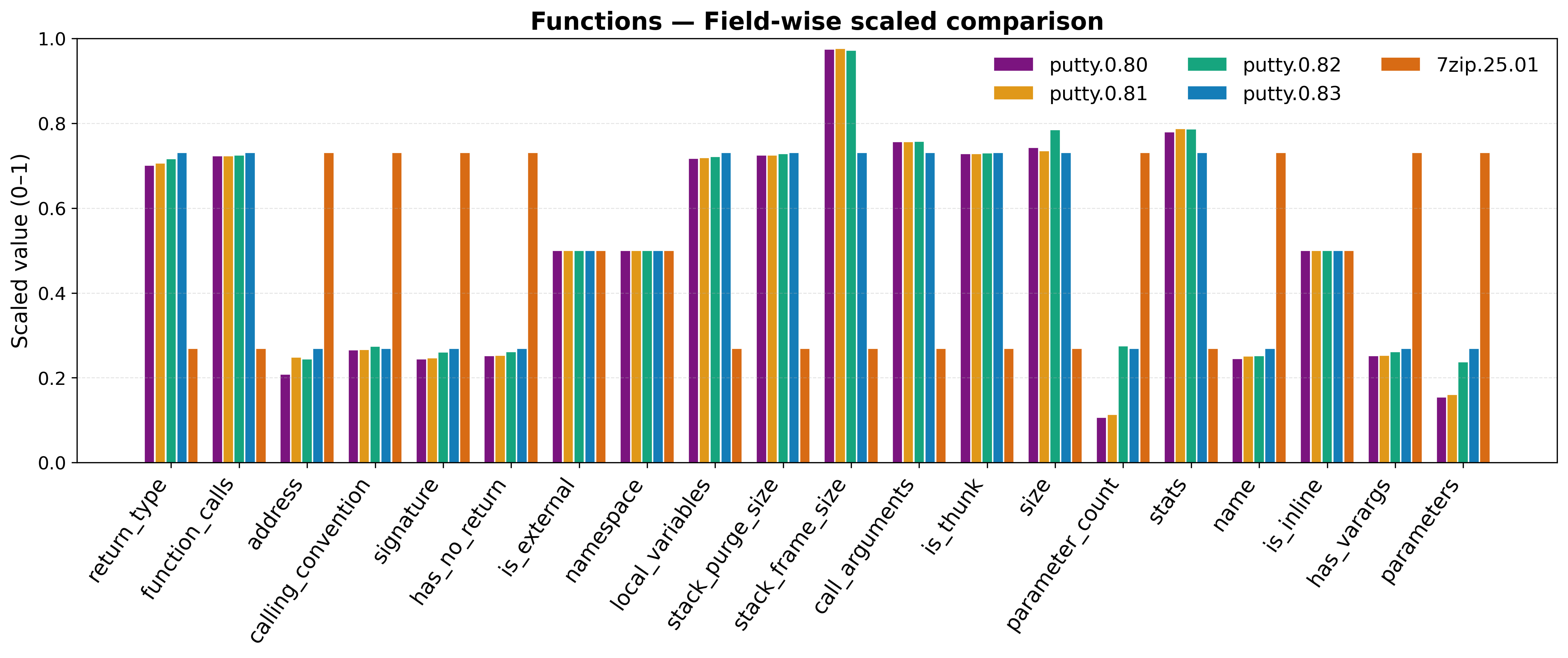
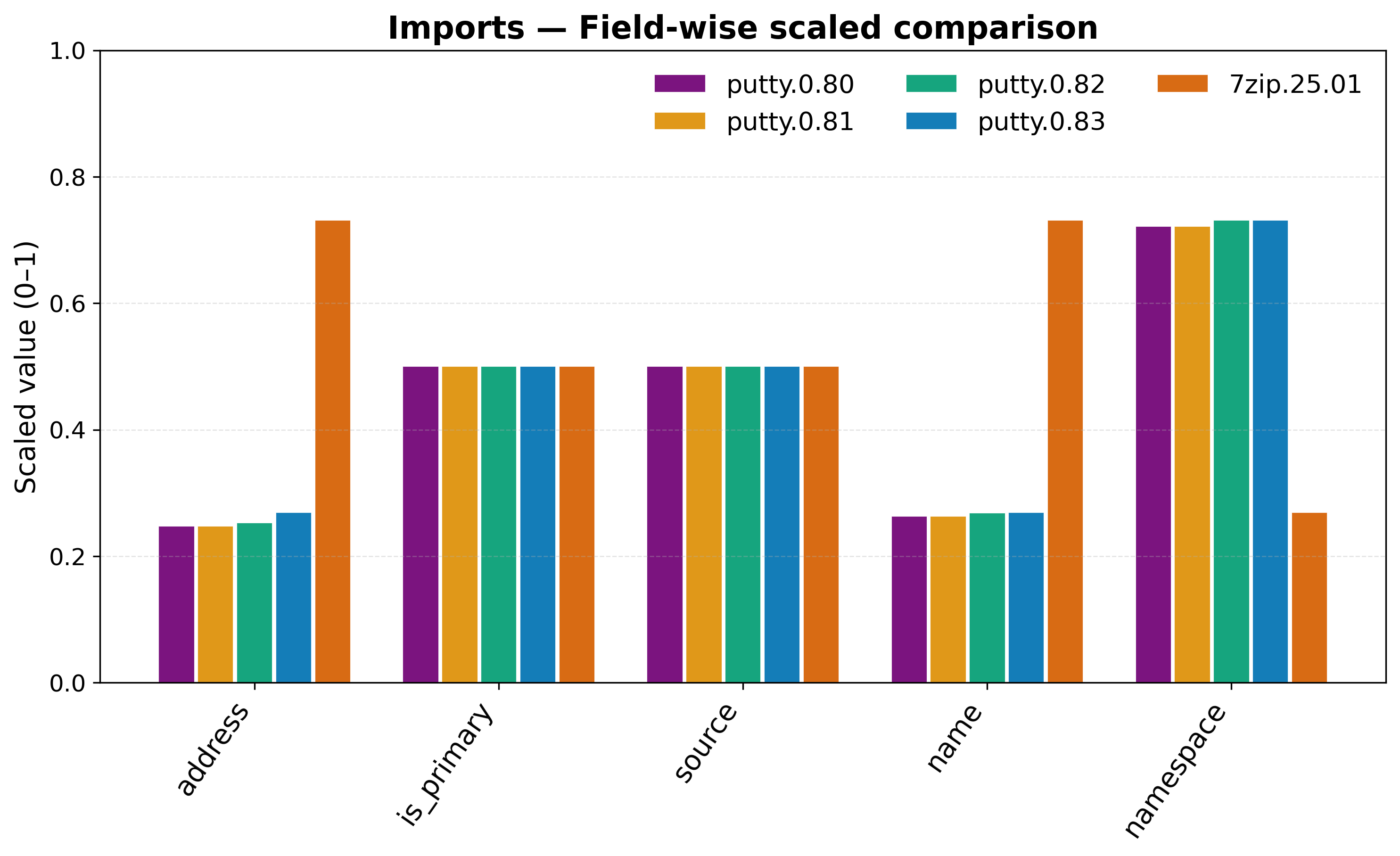
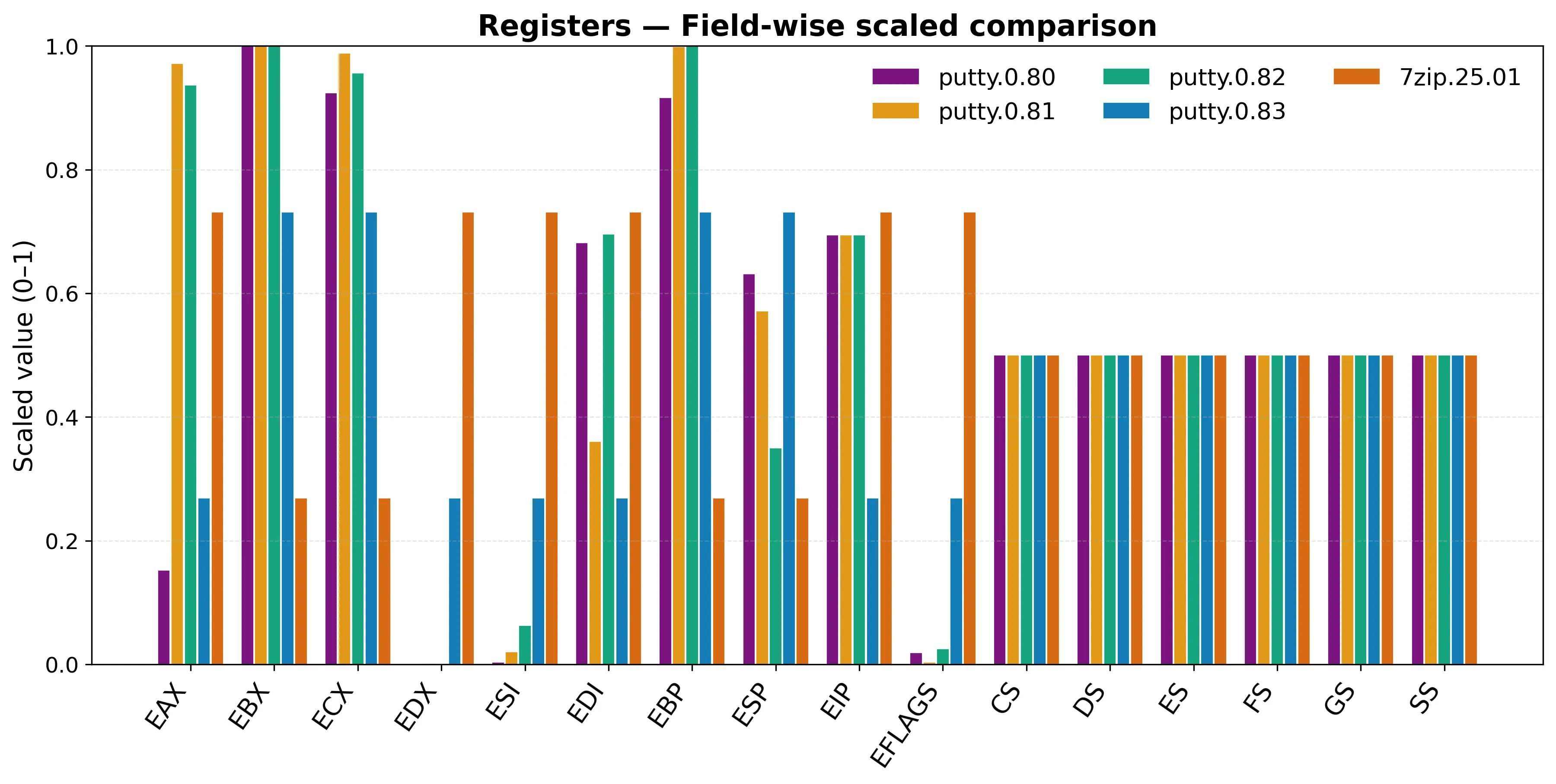
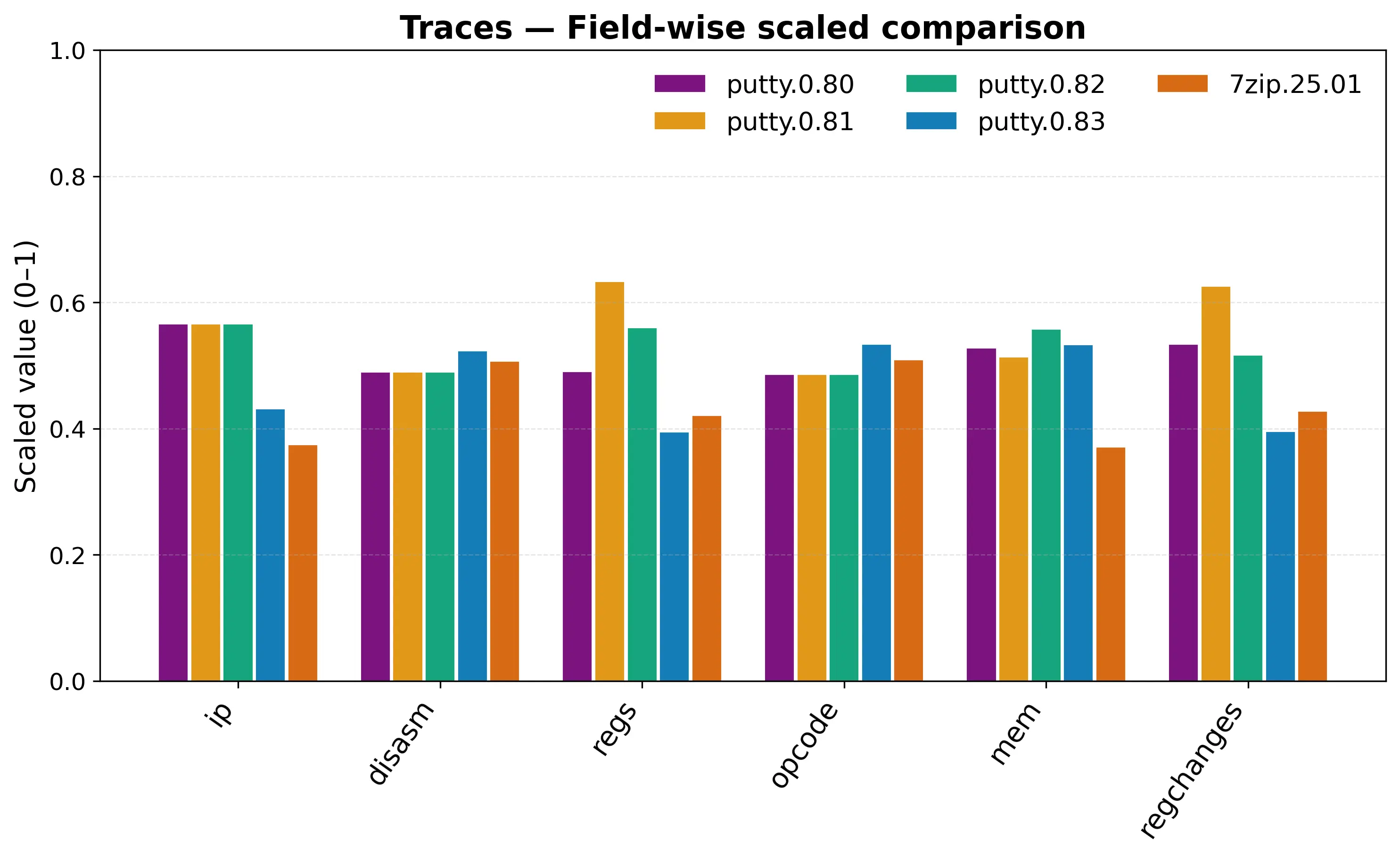
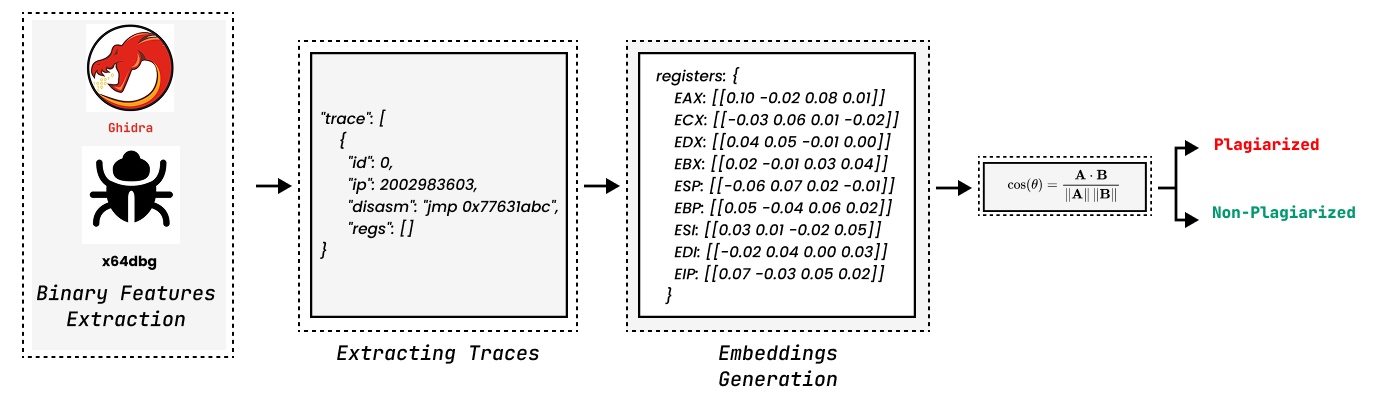
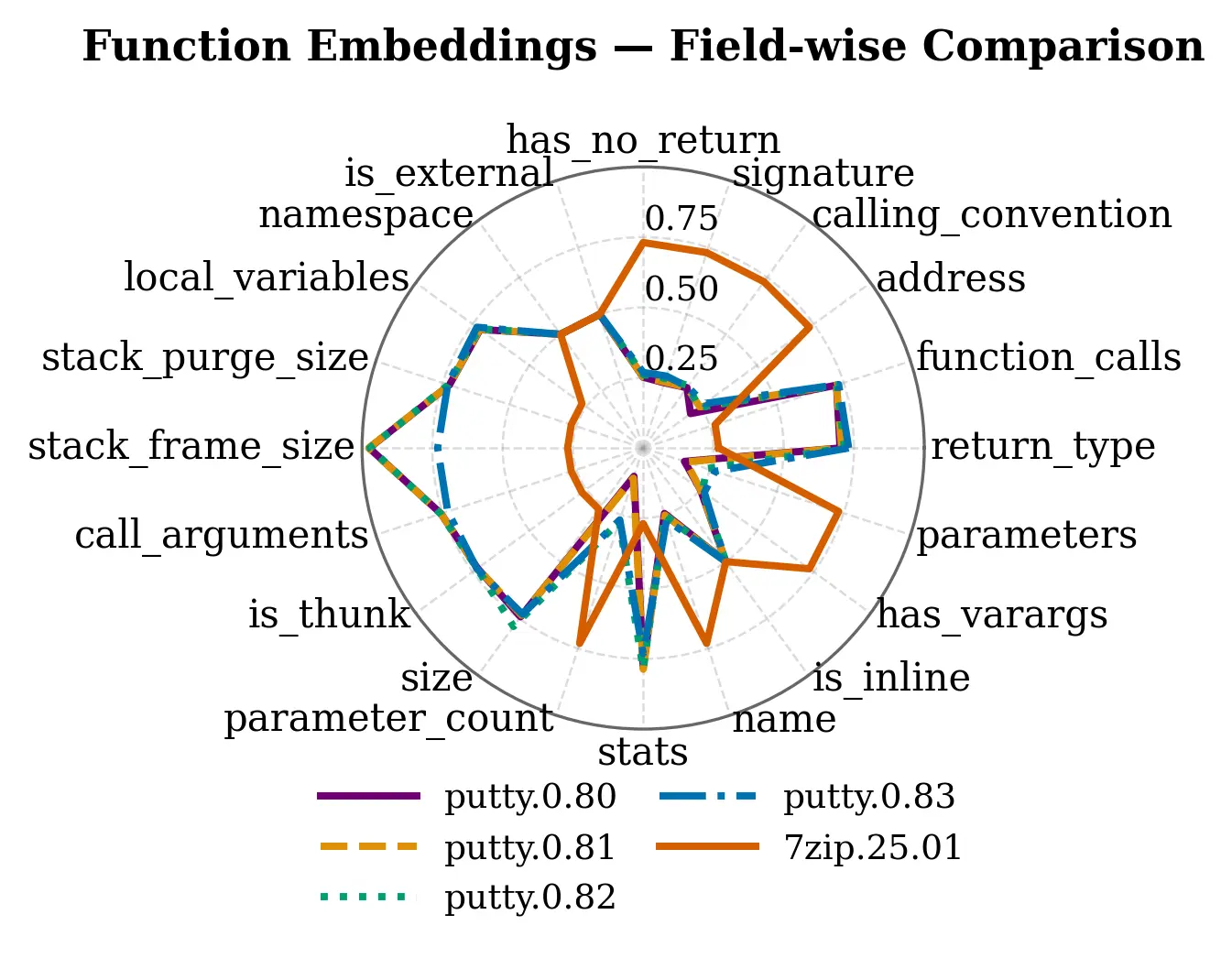
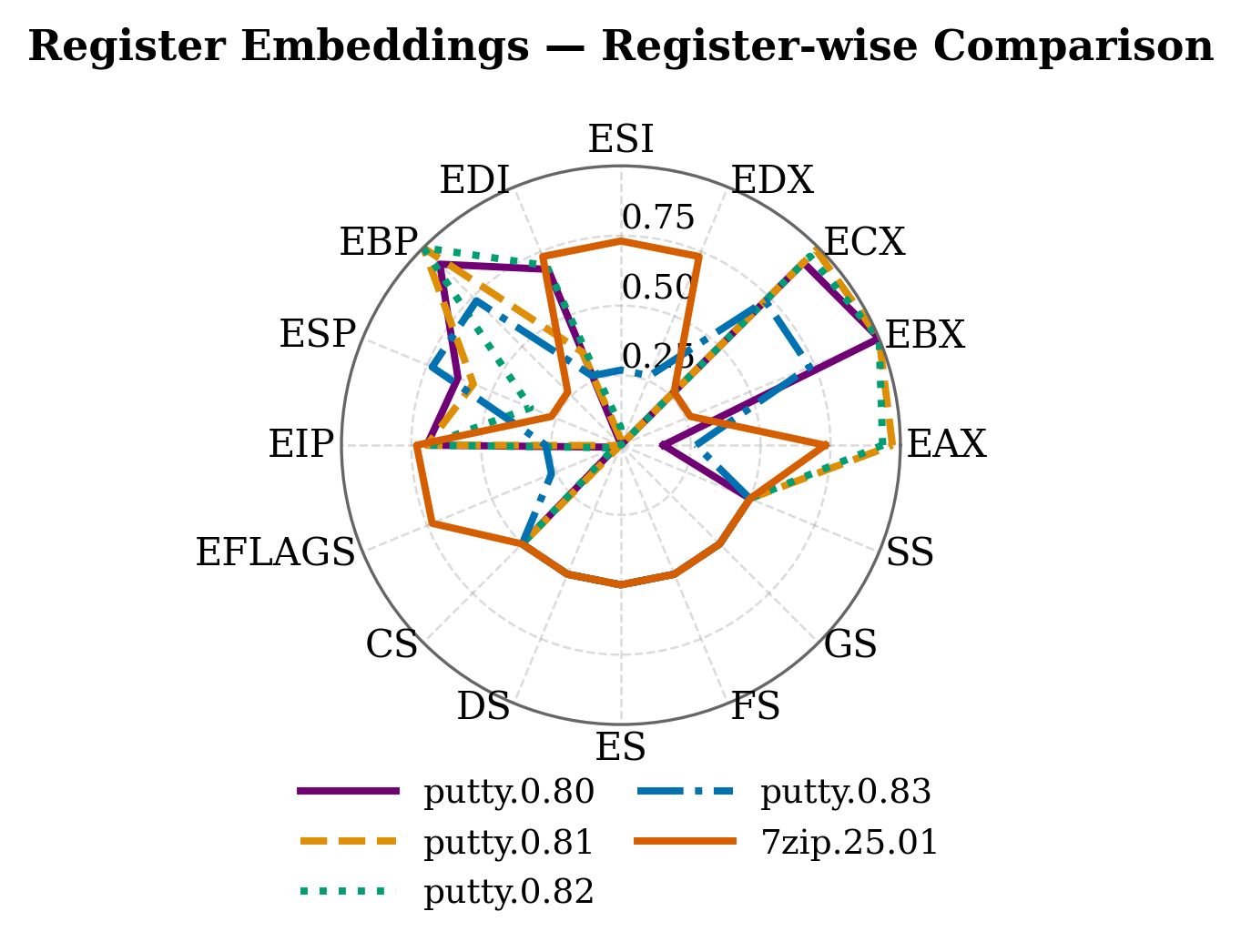
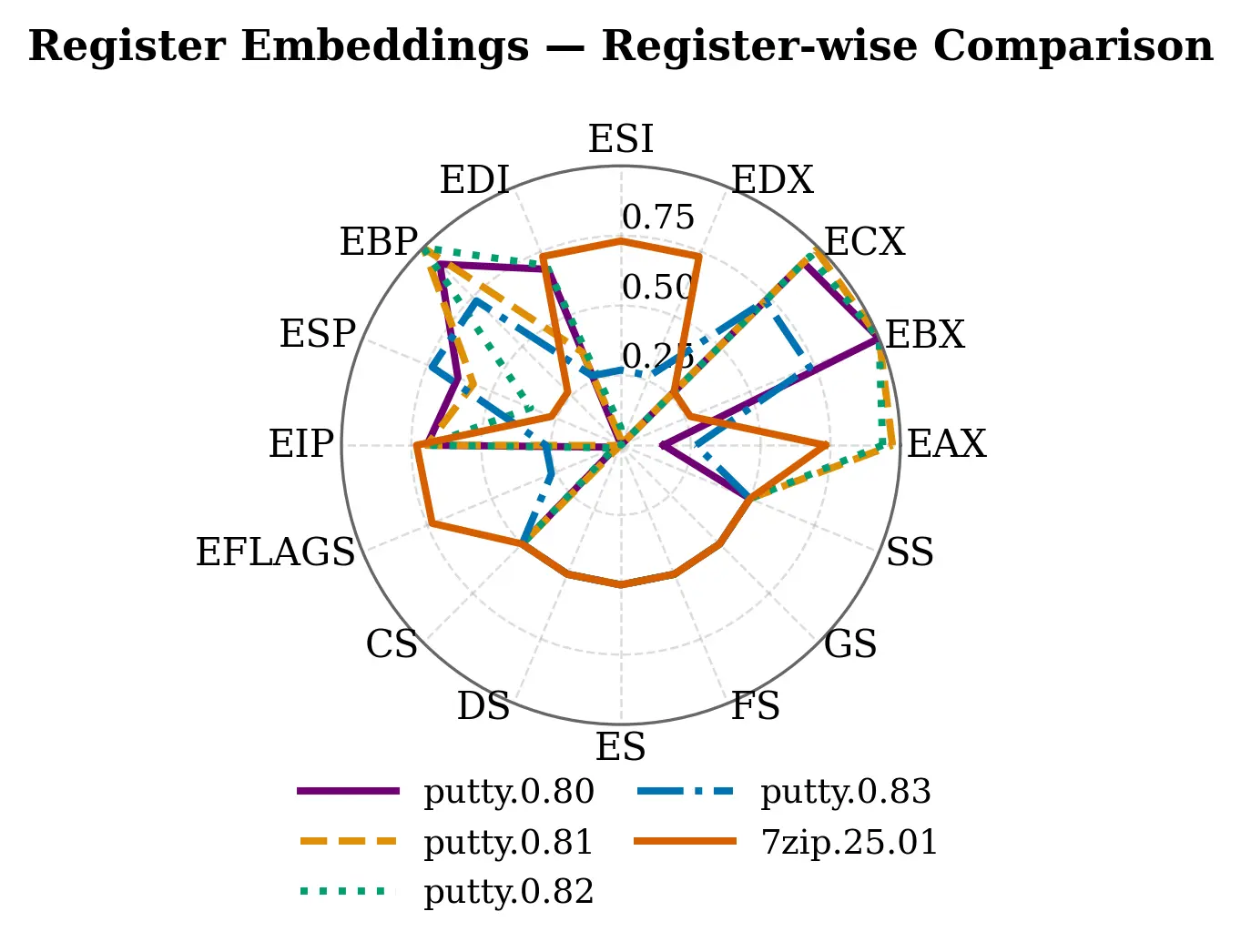
We introduce Bin2Vec, a new framework that helps compare software programs in a clear and explainable way. Instead of focusing only on one type of information, Bin2Vec combines what a program looks like (its built-in functions, imports, and exports) with how it behaves when it runs (its instructions and memory usage). This gives a more complete picture when deciding whether two programs are similar or not. Bin2Vec represents these different types of information as views that can be inspected separately using easy-to-read charts, and then brings them together into an overall similarity score. Bin2Vec acts as a bridge between binary representations and machine learning techniques by generating feature representations that can be efficiently processed by machine-learning models. We tested Bin2Vec on multiple versions of two well-known Windows programs, PuTTY and 7-Zip. The primary results strongly confirmed that our method compute an optimal and visualization-friendly representation of the analyzed software. For example, PuTTY versions showed more complex behavior and memory activity, while 7-Zip versions focused more on performance-related patterns. Overall, Bin2Vec provides decisions that are both reliable and explainable to humans. Because it is modular and easy to extend, it can be applied to tasks like auditing, verifying software origins, or quickly screening large numbers of programs in cybersecurity and reverse-engineering work.
Deep Dive into Bin2Vec: Interpretable and Auditable Multi-View Binary Analysis for Code Plagiarism Detection.
We introduce Bin2Vec, a new framework that helps compare software programs in a clear and explainable way. Instead of focusing only on one type of information, Bin2Vec combines what a program looks like (its built-in functions, imports, and exports) with how it behaves when it runs (its instructions and memory usage). This gives a more complete picture when deciding whether two programs are similar or not. Bin2Vec represents these different types of information as views that can be inspected separately using easy-to-read charts, and then brings them together into an overall similarity score. Bin2Vec acts as a bridge between binary representations and machine learning techniques by generating feature representations that can be efficiently processed by machine-learning models. We tested Bin2Vec on multiple versions of two well-known Windows programs, PuTTY and 7-Zip. The primary results strongly confirmed that our method compute an optimal and visualization-friendly representation of th
This is the authors’ original preprint version of a paper accepted for publication at the 8th International Conference on Advanced Communication
Technologies and Networking (CommNet 2025), Rabat, Morocco, December 3–5, 2025. The final version will be published and made available via IEEE
Xplore.
Bin2Vec: Interpretable and Auditable Multi-View
Binary Analysis for Code Plagiarism Detection
Moussa MOUSSAOUI1, Tarik HOUICHIME2, and Abdelalim SADIQ3
1,3Computer Science Research Laboratory(LaRI), Faculty of Science, Ibn Tofail University,
Kenitra, 14000, Morocco
2LRIT, Faculty of Science, Mohammed V University In Rabat, Rabat, 10112, Morocco
Emails: 1 moussa.moussaoui@uit.ac.ma, 2 tarik_houichime@um5.ac.ma, 3 a.sadiq@uit.ac.ma
Abstract—We introduce Bin2Vec, a new framework that helps
compare software programs in a clear and explainable way.
Instead of focusing only on one type of information, Bin2Vec com-
bines what a program looks like (its built-in functions, imports,
and exports) with how it behaves when it runs (its instructions
and memory usage). This gives a more complete picture when
deciding whether two programs are similar or not. Bin2Vec
represents these different types of information as views that
can be inspected separately using easy-to-read charts, and then
brings them together into an overall similarity score. Bin2Vec
acts as a bridge between binary representations and machine
learning techniques by generating feature representations that
can be efficiently processed by machine-learning models. We
tested Bin2Vec on multiple versions of two well-known Windows
programs, PuTTY and 7-Zip. The primary results strongly
confirmed that our method compute an optimal and visualization-
friendly representation of the analyzed software. For example,
PuTTY versions showed more complex behavior and memory
activity, while 7-Zip versions focused more on performance-
related patterns. Overall, Bin2Vec provides decisions that are
both reliable and explainable to humans. Because it is modular
and easy to extend, it can be applied to tasks like auditing,
verifying software origins, or quickly screening large numbers of
programs in cybersecurity and reverse-engineering work.
Index Terms—Binary similarity, embeddings, dynamic traces,
software forensics, plagiarism detection, interpretability, au-
ditability, xAI
I. INTRODUCTION
Binary code similarity (BCS) forms the base for various
critical tasks, such as hunting security flaws and examining
software patches, tracing malware origins and grouping them,
detecting code sources or plagiarism in multiple releases, and
scanning vast code repositories. Though highly useful, BCS
remains inherently challenging: compilers and linkers modify
instruction and data flows; removing identifiers eliminates
meaningful indicators of code intent; deliberate obfuscation
distorts the overall structure; and comparisons across diverse
architectures or optimization variants produce significant struc-
tural variations. In practical settings, these approaches must
expand from identifying differences in small code segments
to retrieving matches over entire programs within hundreds of
thousands of artifacts.
Graph-based methodologies translate code functions into
semantic vector encodings, enabling robust similarity detection
despite compiler-induced variations. While this structural-
semantic approach captures deep programmatic logic, it is
computationally intensive and struggles with significant code
obfuscation or cross-architectural comparisons. An alternative,
high-performance approach scales function-level vector encod-
ings for rapid, real-time matching, trading explanatory power
for build resilience and speed. Massive-scale comparisons
are achieved by further compressing entire programs into
compact, fixed-size representations, which introduces a trade-
off between search velocity and the potential for detail loss.
These static alignment techniques optimize for cross-variant
matching speed and quality, but they remain vulnerable to
structural obfuscation and are fundamentally incapable of
capturing dynamic runtime behavior.
To address this gap, we introduced Bin2Vec (Binary to
Vectors), a modular trace-centric methodology. Which con-
structs compact, comparable embeddings from multiple com-
plementary signals that are readily available or derivable
in practical reverse engineering work-flows. We capture the
dynamic behaviour using x64dbg alongside static informations
from Ghidra [73], [74]. This multi-view design aims to be
robust to single-signal brittleness while maintaining inter-
pretability. We also provide a reproducible end-to-end pipeline
that curates and merges traces, derives per-signal embeddings
with deterministic fallback, computes per-feature and global
similarities. By explicitly incorporating behavioral analysis via
execution traces and register usage, Bin2Vec complements
graph and hashing-based approaches [10], [15], [38], [62],
[71]. Its practical advantages are transpare
…(Full text truncated)…
This content is AI-processed based on ArXiv data.