Mission Aware Cyber-physical Security
Perimeter cybersecurity, while essential, has proven insufficient against sophisticated, coordinated, and cyber-physical attacks. In contrast, mission-centric cybersecurity emphasizes finding evidence of attack impact on mission success, allowing for targeted resource allocation to mitigate vulnerabilities and protect critical assets. Mission Aware is a systems-theoretic cybersecurity analysis that identifies components which, if compromised, destabilize the overall mission. It generates evidence by finding potential attack vectors relevant to mission-linked elements and traces this evidence to mission requirements, prioritizing high-impact vulnerabilities relative to mission objectives. Mission Aware is an informational tool for system resilience by unifying cybersecurity analysis with core systems engineering goals.
💡 Research Summary
The paper begins by critiquing conventional perimeter‑based cybersecurity for cyber‑physical systems (CPS). While firewalls, encryption, and other boundary defenses are necessary, they are largely prescriptive and oblivious to the specific mission a system is intended to accomplish. As a result, sophisticated, coordinated attacks can bypass these defenses and jeopardize the overall mission, especially in safety‑critical domains such as defense, aerospace, and industrial control.
To address this gap, the authors introduce “Mission Aware,” a mission‑centric cybersecurity framework that integrates systems‑theoretic risk analysis with graph‑based modeling. The central premise is that security assessment should be tied directly to mission success: identifying which components, if compromised, would destabilize the mission and prioritizing mitigation efforts accordingly.
Mission Aware follows a structured, four‑stage workflow:
-
Requirements & Mission Information Elicitation – A guided, stakeholder‑driven interview process gathers mission scenarios, objectives, unacceptable outcomes, and an initial threat prognosis. Stakeholders include mission owners, operators, attack analysts, and cost experts. The elicited qualitative data are captured as high‑level mission requirements and as a set of potential hazards.
-
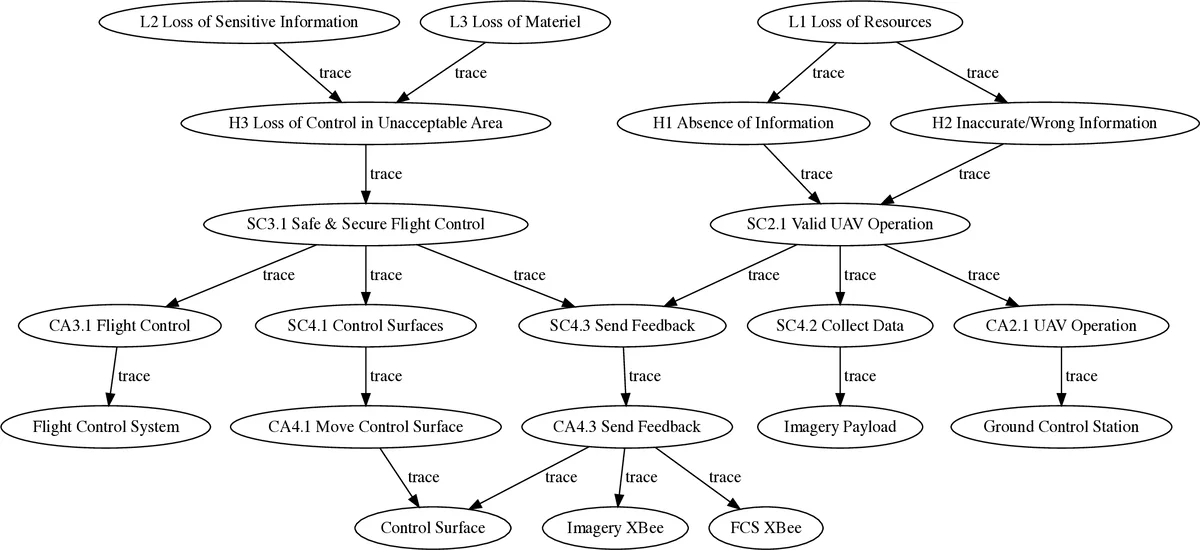
Disturbance and Consequence Modeling (STAMP / STPA‑Sec) – Using the Systems‑Theoretic Accident Model and Process (STAMP) and its security extension STPA‑Sec, the methodology translates stakeholder inputs into a hierarchical causality table. Unacceptable losses, hazardous conditions, and unsafe control actions are explicitly documented, providing a systematic link between mission‑level goals and system‑level behavior.
-
SysML System Modeling – The mission, functional behavior, and architectural aspects of the CPS are modeled in SysML. The model is organized into three domains (mission, behavior, architecture) and is designed to evolve throughout the system lifecycle. This model serves as the structural backbone for later security analysis.
-
Attack Vector Space & Graph Metamodeling – Public vulnerability repositories (CAPEC, CWE, CVE) are mined for relevant attack patterns, weaknesses, and exploits. These data are mapped onto the SysML components, producing a graph metamodel where nodes represent system elements, mission requirements, and hazard conditions, while edges encode dependencies and potential attack paths. Graph traversal algorithms are then used to identify paths that would violate mission‑level requirements, effectively quantifying the impact of each vulnerability on mission success.
Key contributions of Mission Aware include:
- Evidence‑Based Impact Assessment – By attaching real‑world attack data to system components, the framework can rank vulnerabilities according to their projected mission impact, rather than merely their technical severity.
- Strategic Resource Allocation – Decision makers can focus mitigation resources on the few high‑impact components that are critical to mission success, achieving a better cost‑benefit balance.
- Early‑Lifecycle Integration – Because the process starts at requirements elicitation, security considerations are baked into the design phase, reducing costly retrofits later in development.
- Unified Graph Formalism – Graphs provide a common language for both system models and attack representations, enabling automated reasoning, visualization, and reuse across different analysis tools.
The authors position Mission Aware relative to prior work. While many studies apply safety‑oriented system‑theoretic methods (e.g., STPA‑SafeSec) or model‑based security using UML/SysML, they often treat safety and security separately or focus on compliance with standards. Mission Aware, by contrast, directly ties security evidence to mission outcomes, thereby shifting the defender’s perspective to that of the attacker’s graph‑centric view.
The paper also surveys a body of technical reports, conference papers, and prototype tools that have previously explored model‑based security, co‑engineering of safety and security, and graph‑based attack analysis. Mission Aware consolidates these strands into a single, coherent methodology and demonstrates its applicability to defense‑related CPS use cases.
Future research directions identified include: (1) automating the ingestion and normalization of vulnerability data, (2) scaling graph analysis techniques for large‑scale system models, (3) integrating real‑time mission monitoring with the graph‑based risk engine, and (4) extending the approach to incorporate human and organizational factors more explicitly.
In summary, Mission Aware offers a proactive, risk‑oriented, and graph‑theoretic approach to cyber‑physical security that aligns cybersecurity analysis with core systems‑engineering objectives. By focusing on mission impact rather than isolated component failures, it promises to enhance the resilience of critical CPS deployments against sophisticated, coordinated attacks.
Comments & Academic Discussion
Loading comments...
Leave a Comment