Post-Quantum Cryptography(PQC): Generalized ElGamal Cipher over GL(8,F251)
Post-quantum cryptography (PQC) attempts to find cryptographic protocols resistant to attacks using for instance Shor’s polynomial time algorithm for numerical field problems like integer factorization (IFP) or the discrete logarithm (DLP). Other aspects are the backdoors discovered in deterministic random generators or recent advances in solving some instances of DLP. Using alternative algebraic structures like non-commutative or non-associative partial groupoids, magmas, monoids, semigroups, quasigroups or groups, are valid choices for these new protocols. This paper focuses on an asymmetric cipher based on a generalized ElGamal non-arbitrated protocol using a non-commutative general linear group. The developed protocol forces a hard subgroup membership search problem into a non-commutative structure. The protocol involves at first a generalized Diffie-Hellman key interchange and further on the private and public parameters are recursively updated each time a new cipher session is launched. Security is based on a hard variation of the Generalized Symmetric Decomposition Problem (GSDP). Working with GL(8, F251) 64-bit security is achieved, and if GL(16, F251) is chosen, the security rises to 127-bit. An appealing feature is that there is no need for big number libraries as all arithmetic is performed in Z_251. Therefore the new protocol is particularly useful for computational platforms with very limited capabilities like smartphones or smartcards.
💡 Research Summary
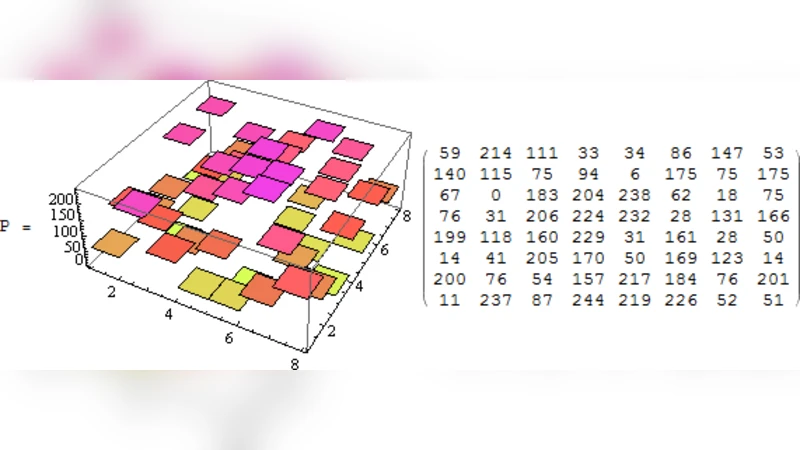
The paper proposes a post‑quantum asymmetric cipher built on the non‑commutative general linear group GL(8, F₂₅₁). By operating entirely within the prime field Z₍₂₅₁₎, the scheme avoids big‑integer arithmetic, making it suitable for constrained platforms such as smartphones and smart‑cards. The construction is a generalized ElGamal protocol that first performs a generalized Diffie‑Hellman key exchange in the non‑commutative setting, then encrypts messages as 8×8 matrices using the shared secret. After each session the private and public parameters are recursively updated, preventing key‑reuse attacks.
Security rests on two hard problems: (1) the Subgroup Membership Search Problem (SMSSP) in a non‑commutative matrix group, i.e., determining whether a given matrix belongs to a hidden subgroup; and (2) the Generalized Symmetric Decomposition Problem (GSDP), which asks for a hidden matrix S satisfying X = Y·S·Z for known X, Y, Z. Both problems are believed to be intractable for classical and known quantum algorithms, as they lack the algebraic structure exploited by Shor’s algorithm. Consequently, the scheme is claimed to provide 64‑bit security for GL(8, F₂₅₁) and 127‑bit security when the dimension is doubled to GL(16, F₂₅₁).
Performance analysis shows that each matrix multiplication requires only 64 modular multiplications and 56 additions modulo 251, leading to sub‑millisecond runtimes on typical microcontrollers and memory footprints of only a few kilobytes. The authors present experimental timings on a smartphone processor and a smart‑card chip, confirming the practicality of the approach.
The paper’s contributions are threefold: (i) introducing a non‑commutative group‑based hardness assumption distinct from lattice or code‑based PQC; (ii) demonstrating that all cryptographic operations can be carried out with small‑modulus arithmetic, eliminating the need for heavyweight big‑number libraries; and (iii) providing a session‑wise recursive key update mechanism that enhances forward secrecy.
However, the work leaves open several important questions. The exact complexity class of SMSSP and GSDP in GL(n, Fₚ) has not been rigorously established, and no concrete quantum‑attack simulations are presented. Scaling the group dimension to achieve higher security levels increases computational cost, which may limit applicability on ultra‑low‑power devices. Future research should focus on formal security reductions, quantum‑resistance proofs, and hardware‑accelerated implementations.
In summary, the authors present a novel, implementation‑friendly post‑quantum cipher that leverages the algebraic richness of non‑commutative matrix groups, offering a promising alternative for environments where traditional PQC schemes are too heavyweight.
Comments & Academic Discussion
Loading comments...
Leave a Comment