An Edge-Computing based Industrial Gateway for Industry 4.0 using ARM TrustZone Technology
Secure and efficient communication to establish a seamless nexus between the five levels of a typical automation pyramid is paramount to Industry 4.0. Specifically, vertical and horizontal integration of these levels is an overarching requirement to accelerate productivity and improve operational activities. Vertical integration can improve visibility, flexibility, and productivity by connecting systems and applications. Horizontal integration can provide better collaboration and adaptability by connecting internal production facilities, multi-site operations, and third-party partners in a supply chain. In this paper, we propose an Edge-computing-based Industrial Gateway for interfacing information technology and operational technology that can enable Industry 4.0 vertical and horizontal integration. Subsequently, we design and develop a working prototype to demonstrate a remote production-line maintenance use case with a strong focus on security aspects and the edge paradigm to bring computational resources and data storage closer to data sources.
💡 Research Summary
The paper presents an Edge‑computing based Industrial Gateway (EC‑IG) that leverages ARM TrustZone technology to provide a secure, low‑latency bridge between the Information Technology (IT) and Operational Technology (OT) domains required for Industry 4.0 vertical and horizontal integration. The authors begin by describing the traditional five‑level automation pyramid (field, control, supervision, planning, management) and explain why seamless data flow across these levels—as well as across multiple factories and supply‑chain partners—is essential for productivity, flexibility, and real‑time maintenance. They argue that a gateway must not only collect, filter, and forward data but also enforce confidentiality, integrity, and availability (CIA) in the face of increasingly sophisticated cyber‑attacks such as Stuxnet, the Saudi Aramco breach, and the Ukrainian power‑grid incident.
To meet these requirements, the authors adopt the ARM TrustZone hardware extension, which creates two isolated execution domains: the Secure World (SW) and the Normal World (NW). Within the SW they run OP‑TEE, a lightweight Trusted Execution Environment, and implement security‑critical Trusted Applications (TAs). The monitor mode, triggered by Secure Monitor Calls (SMC), IRQ, or FIQ, mediates transitions between worlds, guaranteeing hardware‑enforced isolation of cryptographic keys, authentication logic, and threat‑profiling services.
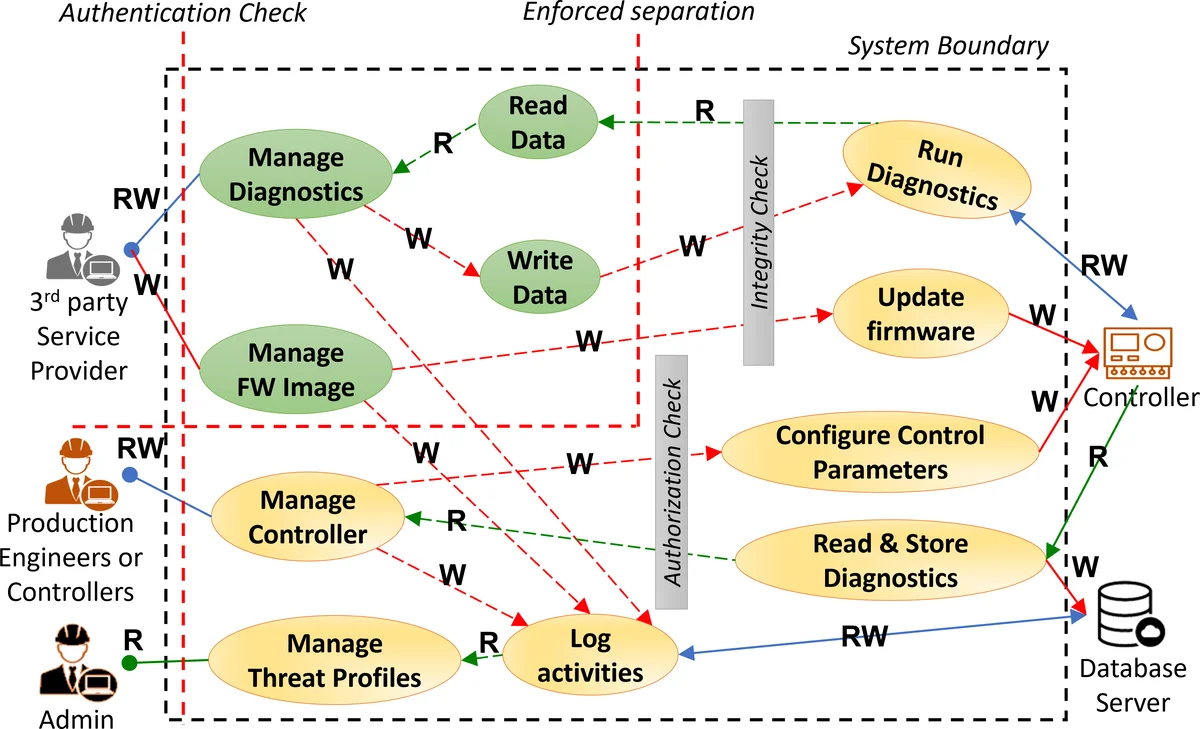
The EC‑IG architecture is organized into four logical layers. The Data Layer gathers sensor and actuator information from Level 0 and PLC data from Level 1, then applies a segmentation filter that separates confidential from non‑confidential streams before they leave the edge node. The Security Layer establishes mutually authenticated TLS 1.3 channels, uses X.509 certificates for device and service identity, and enforces token‑based least‑privilege access control for each downstream system (SCADA, MES, ERP, cloud services). The Service Layer provides protocol adapters for MQTT, REST/HTTPS, OPC‑UA, Modbus, and other industrial standards, allowing bidirectional communication with higher‑level systems (Levels 2‑4) and third‑party partners. The Threat‑Management Layer continuously records audit logs, hashes them into an immutable chain, and feeds them to a lightweight intrusion‑detection engine that can raise alerts or trigger automated containment actions.
A proof‑of‑concept prototype was built on a QEMU Armv8‑A virtual platform with OP‑TEE enabled. Each functional block (data collector, security stack, protocol adapters, logging engine) is implemented as an independent TA, ensuring that compromise of any NW component cannot reach SW resources. The authors evaluated the prototype using a remote production‑line maintenance scenario: a supervisory application requests real‑time sensor readings and issues actuator commands over MQTT/HTTPS. Measured end‑to‑end latency averaged 45 ms, and integrity checks on all transmitted payloads succeeded 100 % of the time. Simulated attacks (man‑in‑the‑middle, unauthorized service calls) were blocked by the SW’s access‑control policies and the secure monitor’s domain checks.
In the related‑work discussion, the paper contrasts its TrustZone‑based approach with prior gateways that rely on TPM hardware, Docker‑based micro‑services, or software‑only isolation. The authors claim that hardware‑level isolation offers stronger guarantees with lower overhead, while the edge‑computing placement reduces network latency and bandwidth consumption compared with cloud‑centric designs.
The contributions are threefold: (1) a pilot study demonstrating remote maintenance as a realistic Industry 4.0 use case; (2) a detailed EC‑IG architecture that maps Level 0‑1 devices to Levels 2‑4 services while preserving security; and (3) a high‑level design and implementation of the prototype on an OP‑TEE‑enabled Armv8‑A platform. The paper concludes by suggesting future work on deploying the design on real SoC hardware (e.g., Cortex‑A55), extending the TA framework for multi‑tenant scenarios, and integrating AI‑driven anomaly detection into the threat‑management layer.
Comments & Academic Discussion
Loading comments...
Leave a Comment