Mitigation of Radar Range Deception Jamming Using Random Finite Sets
This paper presents a radar target tracking framework for addressing main-beam range deception jamming attacks using random finite sets (RFSs). Our system handles false alarms and detections with false range information through multiple hypothesis tr…
Authors: Helena Calatrava, Aanjhan Ranganathan, Tales Imbiriba
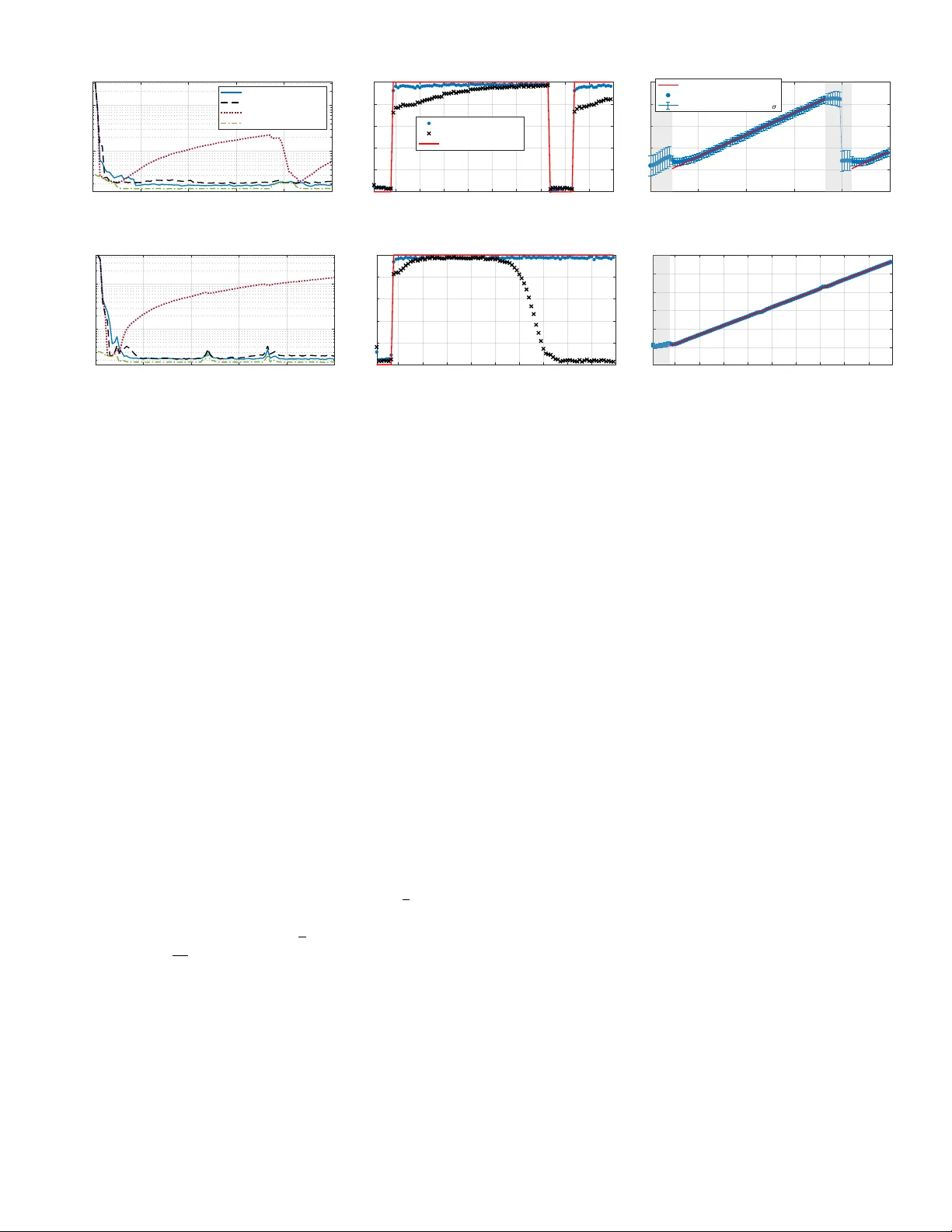
Mitigation of Radar Range Deception J amming Using Random Finite Sets Helena Calatrav a , Student Member , IEEE Northeastern University , Boston, MA 02115, USA Aanjhan Ranganathan , Member, IEEE Northeastern University , Boston, MA 02115, USA T ales Imbiriba , Member, IEEE Northeastern University , Boston, MA 02115, USA Gunar Schirner , Member , IEEE Northeastern University , Boston, MA 02115, USA Murat Akcakaya , Senior, IEEE Northeastern University , Boston, MA 02115, USA Pau Closas , Senior , IEEE Northeastern University , Boston, MA 02115, USA Abstract— This paper presents a radar target tracking frame- work for addressing main-beam range deception jamming attacks using random finite sets (RFSs). Our system handles false alarms and detections with false range information thr ough multiple hypothesis tracking (MHT) to resolve data association uncertainties. W e focus on range gate pull-off (RGPO) attacks, where the attacker adds positiv e delays to the radar pulse, ther eby mimicking the tar get trajectory while appearing at a larger distance from the radar . The proposed framework incorporates knowledge about the spatial behavior of the attack into the assumed RFS clutter model and uses only position information without relying on additional signal features. W e present an adaptive solution that estimates the jammer - induced biases to impro ve tracking accuracy as well as a simpler non-adaptive version that performs well when accurate priors on the jamming range are available. Furthermore, an expression for RGPO attack detection is deri ved, wher e the adaptiv e solution offers superior perf ormance. The presented strategies provide tracking resilience against multiple RGPO attacks in terms of position estimation accuracy and jamming detection without degrading tracking performance in the absence of jamming. Index T erms— Jamming, radar interfer ence, radar tracking, filtering, electronic warfare. Manuscript recei ved XXXXX 00, 0000; re vised XXXXX 00, 0000; accepted XXXXX 00, 0000. This work was supported by the Army Research Laboratory under Cooperativ e Agreement Number W911NF- 23-2-0014, and in part by the National Science Foundation under A wards ECCS-1845833 and CCF-2326559. (Corresponding author: Helena Calatrava) . Helena Calatrav a, Aanjhan Ranganathan, T ales Imbiriba, Gunar Schirner , and Pau Closas are with Northeastern Uni versity , Boston, MA 02115, USA (e-mail: { calatrav a.h, aanjhan, t.imbiriba, g.schirner, closas } @northeastern.edu). Murat Akcakaya is with University of Pitts- bur gh, P A 15260, USA (e-mail: akcakaya@pitt.edu) 0018-9251 © 2024 IEEE I. INTRODUCTION Deception jammers, also known as repeater jammers, are typically used as a self-protection strategy by systems such as tactical aircraft operating in en vironments with a high density of enemy radar systems. These jammers disrupt the focus of target tracking radars (TTR) by intercepting, modifying, and retransmitting the signal of interest with false information, thereby div erting attention aw ay from the actual target of interest (TOI) [ 1 ], [ 2 ], [ 3 ]. Main-beam range deception jamming may also occur when the jammer is co-located with the TOI, or at the same angle relative to the TTR, thus acting as a false target generator [ 4 ]. While more power -ef ficient than noise jammers, deception jammers rely on memory as their critical component. In particular , digital RF memory (DRFM) technology is used to monitor and store radar signals for accurate replay attacks [ 5 ]. Figure 1 contrasts target tracking with (resilient tracker) and without (nai ve tracker) protectiv e measures. The resilient tracker corrects the bias introduced by the attacker in the target range. Range gate pull-off (RGPO) is a self-protection strat- egy where the attacker uses cov er pulses to capture the range gate used for TOI selection and adds delays to shift it aw ay from the target. Once it has moved signifi- cantly , the jammer shuts down and the TTR is forced to restart its search [ 1 ], [ 6 ]. Efforts in the literature focus on optimizing RGPO strategies for track deception. The intricate nature of jammer-radar interactions complicates quantitati ve optimization and leads to the exploration of black-box RGPO jamming, where the jammer lacks kno wledge of the TTR tracking model [ 7 ], [ 8 ], unlike in the white-box scenario [ 9 ]. Range gate pull-in (RGPI) attacks are typically considered impractical [ 10 ] due to the assumption that the TTR employs wav eform di versity and pulse agility strategies [ 11 ], [ 12 ], including the use of random OFDM signals [ 13 ]. Given this, we focus on RGPO attacks. Con ventional anti-jamming strategies use interference feature discrimination or ensure track continuity by con- sidering the TOI motion state [ 14 ]. One possible approach is to leverage that decepti ve measurements often have nearly identical angles to true target measurements [ 15 ], allo wing for the identification of deception based on small angular dif ferences between measurement pairs [ 16 ], [ 17 ]. The study in [ 18 ] takes advantage of a spatial feature where the steering vector of the deception jammer aligns on a cone centered around the TOI steering vector . Furthermore, the amplitude dif ference between cov er and target return pulses has proven informativ e, potentially enhancing tracking accuracy [ 19 ]. Nonetheless, these methods based on low-order statistics may be insuf ficient when jamming signals and true tar gets share similar features. Multiple hypothesis tracking (MHT) is the leading method for addressing the data association (D A) problem in modern target tracking systems [ 20 ], [ 21 ] since it considers multiple hypotheses about the TOI state and up- IEEE TRANSACTIONS ON AER OSP A CE AND ELECTR ONIC SYSTEMS V OL. XX, No. XX XXXXX 2024 1 State Space R e s i l i e n t T r a c k e r N a i v e T r a c k e r Radar J a m m i n g o n s e t P o i n t U n i f o r m C l u t t e r D e t e c t i o n s Deception Jammer F a k e P o s i t i o n J a m m i n g S i g n a l R a d a r E c h o Protection Model Estimated T rajectory (incorrect) Estimated T rajectory (correct) For ged Bias Fig. 1: Comparison of radar tracking without safeguards (naive tracker) and with protection mechanisms (resilient tracker) against main-beam deception jamming. The naiv e tracker is misled by jamming, while the resilient tracker estimates and corrects the jammer -induced bias in the tar get range, thus ensuring accurate target tracking. dates them as new measurements are received. Although MHT provides track continuity , RGPO identification still requires a decision-making process. This can be guided by heuristic methods, such as assuming that larger ranges correspond to false targets. For instance, in [ 22 ] they reduce the association probabilities of measurements at farther ranges. Howe ver , these assumptions can lead to significant errors or track loss, especially in the context of RGPI attacks or false alarm measurements [ 23 ]. Building on the pre vious paragraph, some MHT -based approaches also use signal features, such as amplitude information, to improve deception identification [ 24 ]. T o the best of the authors’ kno wledge, the body of literature addressing range deception jamming through target tracking algorithms like MHT is limited, with most existing studies either relying on feature extraction, requiring multiple radar systems, or depending on the pre viously mentioned heuristic assumptions. In contrast, our work relies on motion state information and incorpo- rates kno wledge of the spatial behavior of RGPO attacks into the clutter model assumed by the tracker . This is made possible through the use of random finite sets (RFSs) [ 25 ], which offer a mathematically ele gant tool for modeling measurement sets with v ariable cardinality [ 26 ] and are useful in the presence of detection uncertainty and false alarms. The main contributions of the paper are as follows: • A feature-independent target tracking solution re- silient to range deception jamming that incorporates the spatial characteristics of RGPO attacks into the RFS clutter model. W e present an adapti ve approach for estimating jammer-induced biases and a non- adapti ve approach for scenarios where accurate pri- ors on decepti ve ranges are av ailable. • A method to monitor the likelihood of deception jamming exposure for the TTR at each time step, enabling RGPO attack detection. • A nov el approach to dynamically manage mixture components from the RFS clutter model that enables the mitigation of simultaneous RGPO attacks. W e ev aluate the proposed strategies across four scenarios in two experiments: one in volving up to one RGPO attack at a time and the other in volving simultaneous attacks, with each experiment cov ering both straight-line and maneuvering target trajectories. Performance is compared to a clairvoyant tracker operating without D A uncertainty , and a naive tracker that only addresses false alarms. Ad- ditionally , a loss of efficiency (LoE) experiment assesses tracking performance without jamming using the posterior Cram ´ er-Rao bound (PCRB) [ 27 ] as a benchmark. The remainder of the paper is structured as follows: Section II describes the system model, including the assumptions and framework of the tracking algorithm; Section III details the proposed MHT -based jamming mitigation and detection approach; Section IV presents the experimental setup and simulation results; and Section V concludes our work. II. SYSTEM MODEL AND A TT A CK VECT OR In this section, we describe the general frame work of our study , the assumptions made by the TTR regarding target motion and attack vectors, and the model used for attack generation. A. General F ramework W e consider a monostatic radar system tasked with tracking a TOI that is either co-located with a deception jammer or functions as a jammer itself. The jammer is equipped with DRFM capabilities. In our scenario, detections can originate from the target, the deception jammer , and false alarms (uniform clutter). The latter includes reflections from b uildings, trees, the ground, weather phenomena, and other objects in the en vironment. For each object, at most one measurement per time step is assumed. The possibly multiple false target detections may be referred to as decepti ve measurements or sec- ondary target-generated measurements, as they depend on the TOI state. This is similar to spawned targets, except that spawned trajectories ev olve independently of their parent target [ 28 ], [ 29 ]. In the proposed scenario, the target is assumed to be continuously present, whereas the attack may appear or disappear . Both primary and sec- ondary target-generated measurements are independently intercepted with a certain detection probability . 2 IEEE TRANSA CTIONS ON AER OSP A CE AND ELECTR ONIC SYSTEMS V OL. XX, No. XX XXXXX 2024 Raw readings in radar systems typically consist of range and Doppler measurements, which are inherently non-linear , rather than direct 2D positional data. These measurements are usually con verted into Cartesian coordi- nates by combining range data with the known orientation and position of the radar . This con version is performed without loss of generality and results in a linear observa- tion model, which eases the integration of multiple sensor readings and simplifies the visualization of target paths. Considering this, the TOI state vector includes the 2D position p k = [ x k , y k ] ⊤ and velocit y v k = [ ˙ x k , ˙ y k ] ⊤ as x k = [ p ⊤ k , v ⊤ k ] ⊤ . W e assume a radar located at the origin of coordinates p 0 k = [ x 0 k , y 0 k ] ⊤ , which giv es the line of sight (LOS) vector r k = p k − p 0 k ∥ p k − p 0 k ∥ at time step k . B. Attac k Description Since the target and the jammer are assumed to be either co-located or the same entity , the echoes sent by the jammer are along the LOS direction. Consequently , the TTR assumes they originate from the true target. This is depicted in Figure 1 . W e focus on linear RGPO attacks, where the decepti ve measurement range is given by [ 6 ] R d k = R t k + v po ( t k − t 0 ) , (1) being R d k and R t k the ranges of the deceptiv e and true target measurements at time step k , v po the attack pull- of f velocity , t k the radar dwell time, and t 0 the attack starting time. It is assumed that the times of arriv al of the real target and jamming returns dif fer more than the radar resolution and consequently the two returns can be resolved. T o pose a threat to the radar with random jumps in po- sition, the jammer must transmit a large number of pulses in the same pulse repetition interval, as proposed in [ 30 ]. This requires sophisticated equipment and precise timing and is inef fectiv e in replicating the consistent motion pattern of a real target. The first experiment focuses on single-return jamming attacks. This type of attack requires fe wer resources to generate than multi-pulse strategies and is therefore more common. The proposed method for handling single-return attacks also effecti vely man- ages multiple returns when they are in close proximity . Additionally , in the second experiment, we extend the method to enhance resilience against simultaneous RGPO attacks, even when their trajectories differ significantly due to v ariations in starting times or pull-off velocities. The T OI trajectories and the jammer -induced positions in the four scenarios under study , spanning 100 time steps, are depicted in Figure 2 . In Experiment 1, the target follo ws a straight-line trajectory (Scenario 1) or makes three 3 g turns (Scenario 2) in the presence of at most one linear RGPO attack at a time. Specifically , in Scenario 1, the first RGPO attack starts at k = 10 and continues until k = 75 ; then a second attack starts at k = 85 and continues indefinitely . In Scenario 2, only one RGPO attack occurs at the start of a 3 g turn, beginning at k = 10 and continuing indefinitely . In Experiment 2, the target follo ws a straight-line trajectory (Scenario 3) or makes three 3 g turns (Scenario 4) in the presence of multiple linear RGPO attacks. In Scenario 3, two simultaneous RGPO attacks occur: the first starting at k = 1 and continuing until k = 50 and the second starting at k = 15 until k = 75 . A third RGPO attack starts at k = 85 and continues indefinitely . Finally , Scenario 4 starts with a linear RGPO until k = 60 . A last attack occurs at the start of a 3 g turn, beginning at k = 40 and continuing until k = 80 . 200 300 400 500 600 700 x-coordinate [m] 300 400 500 600 y-coordinate [m] Scenario 1 TOI Trajectory Jammer-Induced Positions (a) Scenario 1: Straight Line + RGPO 200 300 400 500 600 700 x-coordinate [m] 200 400 600 800 y-coordinate [m] Scenario 2 (b) Scenario 2: T urns + RGPO 100 200 300 400 500 600 700 800 x-coordinate [m] 300 400 500 600 700 800 y-coordinate [m] Scenario 3 (c) Scenario 3: Straight Line + Multiple RGPOs 150 200 250 300 350 400 450 500 550 600 x-coordinate [m] 200 400 600 800 y-coordinate [m] Scenario 4 (d) Scenario 4: T urns + Multiple RGPOs Fig. 2: TOI trajectory and jammer-induced positions for the four scenarios under study . The start and end of each trajectory are marked by circle and triangle markers, respecti vely . The radar is located at the origin of coordi- nates. C . Signal Model In classical Bayesian filtering, the hidden state x k fol- lo ws a first-order Markov process on the state space X ⊆ R d x described by the transition density f k | k − 1 ( x k | x k − 1 ) . The radar partially observes this process in the space Z ⊆ R d z modeled by the measurement likelihood func- tion g k ( z k | x k ) . The observation z k is conditionally in- dependent of the measurement and state histories given the state x k . W e assume a linear Gaussian transition and measurement likelihood as f k | k − 1 ( x k | x k − 1 ) = N ( x k ; F k − 1 x k − 1 , Q k − 1 ) (2) g k ( z k | x k ) = N ( z k ; H k x k , R k ) , (3) CALA TRA V A ET AL.: MITIGA TION OF RADAR RANGE DECEPTION J AMMING USING RANDOM FINITE SETS 3 where F k − 1 is the transition matrix of the target dynamic model and H k is the measurement model matrix. The cov ariances of the transition and measurement models are represented by Q k − 1 and R k , respectively . 1. RFS Measur ement Model T raditional filtering methods operate assuming exactly one target-generated measurement and the absence of clutter , with measurements defined as random vectors on Z . Conv ersely , the RFS framew ork accounts for multiple target-generated measurements, detection uncertainty and false alarms. At time k , the radar receiv es an unordered set of n k = | Z k | measurements Z k = { z k, 1 , . . . , z k,n k } defined on the space of finite subsets of Z , denoted as F ( Z ) . The RFS measurement equation is giv en by Z k = Θ k ( x k ) ∪ J k ( x k ) ∪ W k , (4) where Θ k ( x k ) is the RFS of the primary target-generated measurement, J k ( x k ) is the RFS of the (possibly mul- tiple) secondary target-generated measurements, and W k is the state-independent RFS accounting for false alarm detections. Θ k ( x k ) is modeled as a binary RFSs Θ k ( x k ) = ( ∅ with probability 1 − p D { z k } with prob . density g k ( z k | x k ) p D , (5) where p D is the probability of detection for the primary target-generated measurement, considered to be time- in v ariant and state-independent due to the constant sensor field of vie w (FO V) assumption. 2. TTR Clutter Model Assumption The two sets of secondary target-generated measure- ments are grouped as the union of statistically indepen- dent Poisson RFSs as K k ( x k ) = J k ( x k ) ∪ W k , (6) with intensity function λ K,k ( ·| x k ) = λ J,k ( ·| x k ) + λ W,k ( · ) . The Poisson RFS model typically assumes a variable number of detections that are generated independently . The false alarm detections are assumed to be uniformly distributed ov er the sensor FO V as λ W,k ( z k ) = ¯ λ 0 ,k u ( z k ) , (7) where u ( z ) is the uniform probability density ov er Z and ¯ λ 0 ,k is the expected number of uniform clutter detections. The tracker assumes a linear Gaussian intensity of the secondary target-generated measurements as λ J,k ( z k | x k ) = ¯ λ 1 ,k c 1 ,k ( z k | x k ) , (8) c 1 ,k ( z k | x k ) = N ( z k ; B k x k + b k , D k ) , (9) where ¯ λ 1 ,k is the expected number of jammer-induced returns. The state is observed through matrix B k with a bias b k along the LOS direction and observation noise cov ariance D k . The probability of K k ( x k ) having n k measurements is ρ K,k ( n k | x k ) = ( ρ W,k ∗ ρ J,k )( n k | x k ) , where ∗ denotes con v olution. This cardinality distribu- tion is Poisson with rate ¯ λ 0 ,k + ¯ λ 1 ,k , being ρ W,k ( · ) and ρ J,k ( ·| x k ) the cardinality distributions of W k and J k ( z k | x k ) . The individual elements of K k ( x k ) are in- dependent and identically distributed (IID) follo wing the probability density [ 31 ] c k ( z k | x k ) = w 0 ,k u ( z k ) + w 1 ,k c 1 ,k ( z k | x k ) , (10) where w i,k = ¯ λ i,k / ( ¯ λ 0 ,k + ¯ λ 1 ,k ) is the normalized weight for the density of the i -th secondary set of measurements. D . Interf erence Generation W e consider RGPO attacks that may occur simultane- ously , but each produces at most one return. Rather than a Poisson RFS this attack is modeled as a binary RFS: J ∗ k ( x k ) = ( ∅ with probability 1 − p J { z k } with prob . density c ∗ 1 ,k ( z k | x k ) p J , (11) where p J is the probability of detecting a decepti ve return, which is time-inv ariant and state-independent gi ven the constant FO V assumption, analogous to p D . Here, c ∗ 1 ,k ( ·| x k ) denotes the density used to generate the jammer-induced measurements. Considering that decepti ve measurements are gen- erated as a binary RFS, the TTR assumption that the combined jammer and false alarm measurements follow a Poisson RFS leads to a model mismatch, denoted as ∗ . Nonetheless, successful interference mitigation is still achie ved by integrating the RGPO spatial characteristics into the likelihood model in ( 9 ), as explained in the next section. Furthermore, the dynamic estimation of the jammer-induced bias in the proposed adaptiv e strategy enhances TTR robustness, particularly in scenarios where the ranges of attack cannot be anticipated, which is often the case. Additionally , the Poisson RFS assumption allows the single-return countermeasure to mitigate multiple at- tacks when their starting times and pull-off velocities are similar , even before extending the methodology to handle multiple attacks. Since the interference is not generated using a Poisson RFS, the parameter ¯ λ 1 ,k no longer represents the average number of jamming returns per scan. Nevertheless, we provide an interesting interpretation of this parameter by vie wing the normalized weights in ( 10 ) as an indicator of whether a measurement in K k ( x k ) is clutter-generated ( i = 0 ) or jammer-generated ( i = 1 ). Higher values of ¯ λ 1 ,k are associated with a higher likelihood that the tracker will classify measurements in K k ( x k ) as jammer -generated. III. MHT -BASED DECEPTION J AMMING MITIGA TION AND DETECTION This section introduces the proposed strategies for mitigating radar range deception jamming using MHT to resolve the D A problem. W e present a method for managing mixture components in the RFS clutter model to mitigate multiple RGPO attacks and a technique for deception jamming detection. Implementation notes on model computational complexity are also included. 4 IEEE TRANSA CTIONS ON AER OSP A CE AND ELECTR ONIC SYSTEMS V OL. XX, No. XX XXXXX 2024 A. Backg round This section re views the use of RFSs for Bayesian optimal single-target tracking with set-valued measure- ments under the linear Gaussian assumption. According to [ 31 , Proposition 1] and considering the previously stated system assumptions, the probability density for the set-v alued measurement Z k is given by η k ( Z k | x k ) ∝ (1 − p D ) · ρ K,k ( | Z k | ) · | Z k | ! × Y z k ∈ Z k c k ( z k | x k ) + p D × ρ K,k ( | Z k − 1 | ) · ( | Z k | − 1)! × X z ′ k ∈ Z k g k ( z ′ k | x k ) Y z k = z ′ k c k ( z k | x k ) , (12) where the first summand corresponds to the target mis- detection hypothesis where Z k = K k ( x k ) , and the re- maining | Z k | summands ( | · | denotes the cardinality of a set) correspond to the target detection hypotheses where Θ k ( x k ) = { z ′ k } is the primary target-generated measurement and K k ( x k ) = Z k \{ z ′ k } . The f actorial terms account for the permutation of measurements. The predicted density is the marginal distribution of the state x k gi ven the set-valued measurements up to time k − 1 (denoted as Z 1: k − 1 = { Z 1 , . . . , Z k } ). This distribution is obtained by the Chapman-K olmogorov equation as p k | k − 1 ( x k | Z 1: k − 1 ) = Z f k | k − 1 ( x k | x k − 1 ) p k − 1 | k − 1 ( x k − 1 | Z 1: k − 1 ) d x k − 1 . (13) The update step in volv es obtaining the posterior density by conditioning on Z k and computing Bayes’ rule as p k | k ( x k | Z 1: k ) = η k ( Z k | x k ) p k | k − 1 ( x k | Z 1: k − 1 ) R η k ( Z k | x k ) p k | k − 1 ( x k | Z 1: k − 1 ) d x k . (14) The linear Gaussian assumption allows for the use of the closed-form solution to the RFS single-target Bayes’ recursion in ( 13 ) and ( 14 ) as proposed in [ 31 , Proposition 4]. Under the assumption of linear Gaussian process and measurement models, at most one target-generated measurement, state-independent probability of target de- tection, and uniform clutter , this closed-form solution reduces to the Gaussian mixture filter [ 32 ]. This type of filter is advantageous in target tracking framew orks since it enables managing multiple DA hypotheses by maintain- ing a set of possible tracks. Each hypothesis is represented by a Gaussian component in the posterior mixture. As ne w measurements are recei ved, the algorithm updates the weights and parameters of these Gaussian components using Bayes’ rule. Under these conditions, if we let m index the predictiv e hypotheses and m ′ index the posterior hypotheses, the predicted density takes the form of a Gaussian mixture as p k | k − 1 ( x k | Z 1: k − 1 ) = M k | k − 1 X m =1 ˜ w ( m ) k | k − 1 N ( x k ; m ( m ) k | k − 1 , P ( m ) k | k − 1 ) , (15) where M k | k − 1 is the number of hypotheses at time k for the prediction step, ˜ w ( m ) k | k − 1 are the normalized pre- dicted weights, and m ( m ) k | k − 1 and P ( m ) k | k − 1 are the predicted mean and covariance of the m -th predicted hypothesis. If this density is propagated through the likelihood model in ( 12 ), the resulting density is also a Gaussian mixture gi ven by p k | k ( x k | Z 1: k ) = M k | k X m ′ =1 ˜ w ( m ′ ) k | k N ( x k ; m ( m ′ ) k | k , P ( m ′ ) k | k ) , (16) where M k | k is the number of hypotheses at time k for the update step, ˜ w ( m ′ ) k | k = w ( m ′ ) k | k / P M k | k m ′ =1 w ( m ′ ) k | k are the normalized posterior weights, and m ( m ′ ) k | k and P ( m ′ ) k | k are the posterior mean and co variance of the m ′ -th posterior hypothesis. For the deriv ation and full expression of the predicted and updated means and covariances, see [ 31 , Propositions 3 and 4]. Background on the standard results for the closed-form solution in the linear Gaussian case may be found in [ 33 ], [ 34 ]. B. Adaptiv e Estimation of Interf erence Bias The method presented in [ 31 ] assumes a predeter- mined bias which, if incorrect, can lead to significant performance degradation comparable to that of the naive tracker sho wn in Figure 1 . Figure 3 illustrates the neces- sity of adapti ve tracking in two distinct scenarios. 1. Strate gy Against Single-Return Attacks T o provide a robust and adapti ve tracking solution, the proposed method dynamically estimates the interfer- ence bias b k by augmenting the state vector as ˜ x k = [ p ⊤ k , v ⊤ k , b k ] ⊤ . The state vector is described by the linear Gaussian transition model in ( 2 ) with parameters F k = I 2 ∆ I 2 0 2 × 1 0 2 × 2 I 2 0 2 × 1 0 1 × 2 0 1 × 2 1 , Q k = σ 2 q ∆ 4 4 I 2 ∆ 3 2 I 2 0 2 × 1 ∆ 3 2 I 2 ∆ 2 I 2 0 2 × 1 0 1 × 2 0 1 × 2 α ∆ , (17) where I m is the m × m identity matrix, 0 m × n is an m × n zero matrix, ∆ is the radar sampling period, σ q is the process noise standard deviation, and α scales the uncertainty of the bias estimate. The target position is observed through the model in ( 3 ) with parameters H k = I 2 0 2 × 3 , R k = σ 2 r I 2 , (18) being σ r the measurement noise standard deviation. The target trajectories described in Figure 2 include turns, for which a turning rate model is used for trajectory generation. Howe ver , the tracker consistently assumes the constant velocity model in ( 17 ). While this creates a model mismatch, this challenge is shared by all techniques tested in this study , including the benchmark. The TTR models the jammer-generated measurements as in ( 9 ), with specific parameter choices designed to integrate the spatial characteristics of RGPO attacks. The observ ation matrix depends on the LOS vector estimate, CALA TRA V A ET AL.: MITIGA TION OF RADAR RANGE DECEPTION J AMMING USING RANDOM FINITE SETS 5 380 415 450 485 520 Coordinate y [m] k = 46 Bias estimation uncertainty increases 380 415 450 485 520 Coordinate y [m] k = 47 Successful bias estimation before jammer deceives radar 380 415 450 485 520 k = 39 Update Tgt Pos Protect. Bias Tgt Obs Fake Obs Clutter Obs Fake position masked by protection model 380 415 450 485 520 Coordinate y [m] k = 40 For ged bias increases k = 39 Update Tgt Pos Protect. Bias Tgt Obs Fa Obs Clutter Obs State Space lse (a) Adaptation to time-varying jammer-induced bias. Fake position with bias of 50 m (mitigated) State Space 370 380 390 400 410 420 430 440 450 460 470 Coo d ate y [ ] 370 380 390 400 410 420 430 440 450 460 470 Coordinate y [m] 370 380 390 400 410 420 430 440 450 460 470 Coordinate y [m] 370 380 390 400 410 420 430 440 450 460 470 Coordinate y [m] Fake position masked by protection model Attack stops Bias estimation uncertainty increases Uncertainty decreases when attack resumes (b) Adaptation to time-varying attack status. Fig. 3: Adapti ve tracking in the presence of deception jamming. Each sequence consists of four frames showing the progression over time of the tracking process and the effecti veness of the protection model. In (a), the adaptiv e tracker compensates for a sudden increase in the jammer -induced bias. In (b), the adapti ve tracker increases bias estimation uncertainty when the attack stops and reduces this uncertainty when the attack resumes. which changes for each component of the Gaussian mix- ture in ( 15 ). For the m -th hypothesis, with predicted mean m ( m ) k | k − 1 , the jammer observation model parameters are B ( m ) k = h I 2 0 2 × 2 ˆ r ( m ) k i , D k = R k , (19) where ˆ r ( m ) k = m ( m ) k | k − 1 − p 0 k m ( m ) k | k − 1 − p 0 k . Note that the bias vector is embedded in the model as b ( m ) k = b k ˆ r ( m ) but does not appear as an additiv e term as shown in ( 9 ). This also applies to the extension to multi-pulse attacks. 2. Extension to Multi-Pulse Attacks The proposed adapti ve solution can seamlessly handle multiple attacks without additional algorithmic modifica- tions when they start at similar times and exhibit similar pull-of f velocities. This capability stems from the Poisson RFS clutter model assumed by the TTR, which inherently accounts for multiple detections. Howe ver , an extension of the model is required to maintain resilience when the parameters between RGPO attacks differ . T o address this challenge, the intensity function in ( 8 ) is modified to become a Gaussian mixture with a time-varying number of components C k as λ J,k ( z k | x k ) = C k X i =1 ¯ λ i,k c i,k ( z k | x k ) (20) c i,k ( z k | x k ) = N ( z k ; B i,k x k , D k ) . (21) Analogous to ( 19 ), D k = R k , and the jammer observ ation matrix for the m -th hypothesis can be expressed as B ( m ) i,k = h I 2 0 2 × 2 0 2 × ( i − 1) ˆ r ( m ) k 0 2 × ( C k − i ) i . (22) Note that the model in ( 8 ) corresponds to the case when C k = 1 . The complete clutter measurement model likelihood is given by c k ( z k | x k ) = w 0 ,k u ( z k ) + C k X i =1 w i,k c i,k ( z k | x k ) , (23) where w i,k = ¯ λ i,k / P C k j =1 ¯ λ j,k for i = 0 , 1 , . . . , C k . Each mixture component is responsible for either mitigating an already detected attack or remaining vigilant for the potential appearance of a new attack. Gi ven that the number of attacks in the scene is unkno wn, we introduce a nov el approach to dynamically manage C k to account for the unpredictable nature of RGPO attacks. This approach is used in Experiment 2. W e initialize the algorithm with one Gaussian com- ponent, i.e., C k = 1 , in vigilant status and ˜ x 1 ,k = [ p ⊤ k , v ⊤ k , b 1 ,k ] ⊤ as the state vector . If the uncertainty in the estimation of bias b 1 ,k remains below the threshold U act for T act time steps, it indicates that the tracker is confident about the estimated jammer -induced bias. Since uniform clutter would not consistently reduce uncertainty around a specific bias value, this suggests that the first component of the mixture is indeed tracking an RGPO attack. Consid- ering this, the status of the first component is changed to active and a new component in vigilant status is added to the mixture. This ensures that there is always a component prepared to handle potential new attacks. When a new i -th component is added, the state vector is augmented to estimate a new bias as ˜ x i,k = [( ˜ x ( i − 1) ,k ) ⊤ , b i,k ] ⊤ . T o sav e computational cost, DA hypotheses are reduced by sending a component to dormant status if uncertainty in the estimation of its associated bias exceeds the threshold 6 IEEE TRANSA CTIONS ON AER OSP A CE AND ELECTR ONIC SYSTEMS V OL. XX, No. XX XXXXX 2024 U dorm for T dorm time steps. The state vector is then reduced by removing the corresponding bias term and the mean and cov ariances of all posterior components are adjusted accordingly . In Experiment 1, the number of Gaussian components is fixed at C k = 1 since this experiment focuses on scenarios 1 and 2, where only one attack can occur at a time. Howe ver , to account for the possibility of multiple non-simultaneous attacks, the Gaussian component is allowed to restart to the prior distribution if it appears to be in dormant status. C . Non-Adaptive Highly Uncertain Approach W e present an alternativ e that does not require state augmentation and pro vides a reasonable solution when ac- curate priors on the jammer -induced ranges are a vailable. The choice of parameters for the non-adaptiv e strategy is B N A ,k = I 2 0 2 × 2 , D ( m ) N A ,k = ˆ U ( m ) k Λ ( ˆ U ⊤ k ) ( m ) . (24) In contrast to the adaptive strategy , which embeds the bias vector in the model by including the LOS vector in the observ ation matrix, the non-adaptiv e strategy adds the bias vector as a separate term as shown in ( 9 ). Specifically , b ( m ) N A ,k = b N A ˆ r ( m ) k , where b N A is the predeter- mined jammer-induced bias assumed by the tracker . Due to this modeling difference, the cov ariance matrix must be flattened along the LOS direction by incorporating ˆ r ( m ) k into the matrix of eigen vectors ˆ U ( m ) k , with Λ being an unbalanced diagonal matrix that introduces higher uncertainty along the LOS. RGPO attacks typically start with negligible bias and then gradually increase the induced ranges to div ert attention aw ay from the TOI. Considering this, b N A should be set so that, when added to the 3 σ bound along the LOS direction provided by D ( m ) N A ,k , it covers the vicinity of the TOI. In this way , the protection model is prepared to mitigate the RGPO attack as soon as it starts. D . Jamming Detection T o detect the presence of the deception jammer, we calculate the probability of the event A = {| J k ( x k ) | ≥ 1 } , which represents the scenario where at least one of the measurements in Z k is identified by the tracker as being jammer-generated. If this condition is met, we infer that the jammer is present. A probability value is calculated at the update step for each posterior hypothesis. The set of measurements assumed as secondary for the posterior hypothesis m ′ is denoted as S ( m ′ ) k = { s k, 1 , . . . , s k, | S ( m ′ ) k | } , and corresponds to S ( m ′ ) k = Z k under target misdetection hypothesis and to S ( m ′ ) k = Z k \{ z ( m ′ ) k } under the hypoth- esis that the target is detected with measurement z ( m ′ ) k . T o calculate P ( A ( m ′ ) : = {| J ( m ′ ) k ( x k ) | ≥ 1 } ) , we first determine the probability that all secondary measurements are considered false alarms by the TTR, and then take its complement as P ( A ( m ′ ) ) = 1 − P ( S ( m ′ ) k ∈ W k ) = 1 − | S ( m ′ ) k | Y j =1 P ( s ( m ′ ) k,j ∈ W k ) . (25) Here, we use the fact that false alarm detections are independent, gi ven that W k is a Poisson RFS with the intensity function in ( 7 ). Each factor in the product can be computed by Bayes’ rule as P ( s ( m ′ ) k,j ∈ W k ) = w 0 ,k u ( s ( m ′ ) k,j ) R c k ( s ( m ′ ) k,j | x k ) N ( x k ; m ( m ) k | k − 1 , P ( m ) k | k − 1 ) d x k , (26) where the denominator represents the total clutter proba- bility for the measurement s ( m ′ ) k,j under the posterior hy- pothesis m ′ . Since this hypothesis is formed by updating the predicted hypothesis m , the denominator includes the density of the m -th component of the predicted distribution shown in ( 15 ). This integral can be computed as Z c k ( s ( m ′ ) k,j | x k ) p ( x k ) d x k = w 0 ,k u ( s ( m ′ ) k,j ) + C k X i =1 w i,k Z c i,k ( s ( m ′ ) k,j | x k ) p ( x k ) d x k = w 0 ,k u ( s ( m ′ ) k,j ) + C k X i =1 w i,k N ( s ( m ′ ) k,j ; µ ( m ) i,k , Σ ( m ) i,k ) , (27) where the density p ( x k ) = N ( x k ; m ( m ) k | k − 1 , P ( m ) k | k − 1 ) is used as a notation shorthand, µ ( m ) i,k = B ( m ) i,k m ( m ) k | k − 1 , and Σ ( m ) i,k = B ( m ) i,k P ( m ) k | k − 1 ( B ( m ) i,k ) ⊤ + D k . This expression has been deri ved using the model from the adapti ve strategy for multi-pulse attacks. An analogous expression without the summation ov er the C k mixture components is obtained for the non-adapti ve implementation. E. Implementation Notes If the posterior at time k − 1 has M k − 1 mixture com- ponents, then the posterior at time k has M k components as [ 31 ] M k − 1 C k | Z k | + | Z k | C | Z k |− 1 k = O M k − 1 · C | Z k | k , (28) where we hav e included C k , the varying number of Gaus- sian components from the extension to multiple RGPO at- tacks in ( 20 ). The closed-form solution does not guarantee tractability , given that the increase of mixture components is unbounded [ 35 ]. W e resort to pruning and capping as approximation techniques to manage the number of com- ponents, although more sophisticated strategies exist [ 36 ]. Pruning removes mixture components with low weights while capping limits the total number of components by keeping only the ones with highest weights. T o prevent the mirror effect, where the TTR mistakes the TOI for the jammer , we can le verage domain knowledge about RGPO CALA TRA V A ET AL.: MITIGA TION OF RADAR RANGE DECEPTION J AMMING USING RANDOM FINITE SETS 7 02 0 4 0 60 80 100 Time Ste p k 10 1 10 2 Position RMSE [m] Adaptive Tracker Non-Adaptive Tracker Naive Tracker Benchmark 02 0 4 0 60 80 100 Time Ste p k -10 0 10 20 30 40 Bias [m] Jammer-Induced Bias Adaptive Tracker Estimate Estimation Uncertainty (1 ) 10 20 30 40 50 60 70 80 90 100 Time Ste p k 0 0.2 0.4 0.6 0.8 1 Jamming Event Probability Adaptive Tracker Non-Adaptive Tracker Attack Status (a) Scenario 1: Straight line trajectory in the presence of a single RGPO attack at a time. 02 0 4 0 60 80 100 Time Step k 10 1 10 2 Position RMSE [m] 10 20 30 40 50 60 70 80 90 Time Step k 0 50 100 150 200 250 Bias [m] 10 20 30 40 50 60 70 80 90 100 Time Step k 0 0.2 0.4 0.6 0.8 1 Jamming Event Probability (b) Scenario 2: Trajectory with three 3g turns in the presence of a single RGPO attack at a time. Fig. 4: Results obtained for Experiment 1 in the presence of a single RGPO attack in terms of position RMSE, probability of jamming ev ent, and bias estimation. The grey area in the bias plot denotes when no attack is present. attacks. By using spatial gating, we set the weights of hypotheses with a negati ve bias to zero. IV . SIMULA TION RESUL TS This section outlines the experimental setup and discusses results in terms of position RMSE, jamming detection accuracy , and the ability to handle multiple RGPO attacks. A LoE study is included to verify that the proposed strategy works ef fectiv ely in the absence of interference. A. Experimental Setup Four simulations are conducted with the scenarios pre- sented in Section II.B (see Figure 2 ), spanning 100 time steps with ∆ = 0 . 5 s. The expected number of false alarm detections is giv en by ¯ λ 0 = λ 0 V , where λ 0 = 2 × 10 − 5 m − 2 and V is the volume of Z . The observ ation re gion, in units of meters, is defined as Z = [0 , 1000] × [0 , 1000] , with a balanced probability of detection between tar get and jamming returns as p D = p J = 0 . 98 . For all scenarios, the observ ation model is the one in ( 3 ), with the parameters defined in ( 18 ) and σ r = √ 5 m. The TTR assumes the constant velocity model in ( 2 ) with the parameters in ( 17 ) and σ q = √ 5 m in Scenarios 1 and 3, and σ q = √ 40 m in Scenarios 2 and 4. The latter accounts for higher accelerations during turns, where the constant velocity assumption poses a challenge. Nev ertheless, the process noise used for trajectory generation is set to zero, except during time steps when the target performs a 3 g turn. This introduces a model mismatch that is further discussed when we present the benchmarks at the end of this subsection. For attack generation, Experiment 1 uses pull-of f velocities as defined in ( 1 ) of 0 . 5 m/s for the two attacks in Scenario 1 and 5 m/s for the single attack in Scenario 2. In Experiment 2, for Scenarios 3 and 4, the velocities are 5 m/s for the first attack and 3 m/s for subsequent attacks. W e conduct 1000 Monte Carlo runs on the same target trajectory , with independently generated measurements for each realization. W e perform pruning at each time step with a weight threshold of 10 − 5 and capping by limiting the number of hypotheses to 100 . For the adaptive strategy , the uncertainty of the bias estimate is scaled by a factor of α = 10 as specified in ( 17 ). Initialization of the filter is done with the prior p 0 = N ( · ; [500 , 500 , 0 , 0 , 0] , diag (1 e 4 , 1 e 4 , 1 e 2 , 1 e 2 , 500)) . In Experiment 1, the assumed protection parameter in ( 8 ) is set to ¯ λ 1 = 3 , and the tracker uses the model described in Section III.B.1. In Experiment 2, the tracker uses the model described in Section III.B.2, which includes the extension against multi-pulse attacks, and the assumed protection parameter remains ¯ λ i = 3 for each i -th com- ponent. When a new component is created, its prior mean and variance are the ones for the bias in p 0 , i.e., with a mean 0 and a v ariance of 500 . The acti v ation thresholds are set to U act = 5 m in bias uncertainty and T act = 7 s, while the deactiv ation thresholds are set to U dorm = 5 m and T dorm = 4 s. The same deactiv ation thresholds U dorm and T dorm are used in Experiment 1 to restart the single Gaussian component when appearing dormant. For the non-adaptiv e strategy , the tracker uses the model described in Section III.C with b N A = 70 m, Λ = diag (500 , 1) and prior density p N A , 0 = N ( · ; [500 , 500 , 0 , 0] , diag (1 e 4 , 1 e 4 , 1 e 2 , 1 e 2)) . The eigen- v alue corresponding to the LOS direction matches the ini- tial variance for bias estimation in the adaptiv e approach, i.e., 500. The adaptiv e method starts with a variance of 500 and adjusts it based on the occurrence of attacks, 8 IEEE TRANSA CTIONS ON AER OSP A CE AND ELECTR ONIC SYSTEMS V OL. XX, No. XX XXXXX 2024 02 0 4 0 60 80 100 Time Step k 10 1 10 2 Position RMSE [m] Adaptive Tracker (Multiple) Non-Adaptive Tracker Naive Tracker Benchmark 02 0 4 0 60 80 100 Time step k 1 1.5 2 2.5 3 Num Awake Components Adaptive Tracker (Multiple) 10 20 30 40 50 60 70 80 90 100 Time Step k 0 0.2 0.4 0.6 0.8 1 Jamming Event Probability Adaptive Tracker (Multiple) Non-Adaptive Tracker Attack Status (a) Scenario 3: Straight line trajectory in the presence of multiple, simultaneous RGPO attacks. 02 0 4 0 60 80 100 Time Step k 10 1 10 2 Position RMSE [m] 02 0 4 0 60 80 100 Time step k 0.5 1 1.5 2 2.5 3 Num Awake Components 10 20 30 40 50 60 70 80 90 100 Time Step k 0 0.2 0.4 0.6 0.8 1 Jamming Event Probability (b) Scenario 4: Trajectory with three 3g turns in the presence of multiple, simultaneous RGPO attacks. Fig. 5: Results obtained for Experiment 2 in the presence of multiple RGPO attacks in terms of position RMSE, probability of jamming ev ent, and number of aw ake Gaussian components C k follo wing the model in ( 23 ). while the non-adaptiv e method maintains a high lev el of uncertainty under all conditions since it lacks adaptiv e capabilities to estimate the bias. As a benchmark, we use a clairvoyant tracker without D A uncertainty operating under a constant velocity model. Although prone to errors during high-acceleration turns, this benchmark establishes a performance bound for the proposed technique by demonstrating its potential when RGPO attacks and false alarms are successfully identified. When attack identification is successful, jamming detec- tions become additional observ ations that enhance track- ing performance. Due to the model mismatch between the process noise assumed by the TTR and the actual noise in the generated trajectories, the PCRB is not used as a benchmark in the first two experiments. Instead, we use the clairvoyant tracker , which aligns with our focus on e valuating TTR performance under the constant velocity assumption. In the LoE experiments, where we set σ q = 0 both at the TTR and for trajectory generation, the PCRB is used as a benchmark. In all the experiments, we also include a nai ve tracker that only accounts for false alarms as K k ( x k ) = W k . This unprotected model demonstrates the performance of a single-target tracker that handles DA uncertainties for uniform clutter but is oblivious to RGPO attacks, hence the term naive . B. Experiment 1: Single RGPO Attack Results for Experiment 1 are presented in Figure 4 . In terms of position RMSE, both the adaptiv e and non-adapti ve approaches demonstrate near-optimal per- formance, as indicated by the benchmark in both scenar- ios. The adaptiv e tracker achie ves slightly lo wer errors than the non-adaptive tracker after an initial adaptation period of 20 time steps. In Scenario 2, both strategies recov er within approximately five time steps follo wing the disruptions introduced by the 3 g turns. The deception jammer walks the naiv e tracker away , while the proposed methods maintain a lock on the TOI, improving accuracy by up to 20 meters. When it comes to jamming detection performance, the advantage of the adapti ve approach over its non- adapti ve counterpart is particularly e vident. The non- adapti ve strategy struggles with biases that exceed the 3 σ bound of the protection model cov ariance, making the TTR unaware of the attack. This is especially noticeable for k > 60 in Scenario 2, where jammer-induced biases exceed 100 meters and the calculated probability of the jammer rapidly drops to zero despite the ongoing attack. Nonetheless, this does not impact position RMSE, as the induced bias, although leaving the tracker unprotected, remains too distant from the TOI to disrupt the TTR lock. The uncertainty in bias estimation for the adaptive approach increases in the absence of interference. This can be seen particularly in Scenario 1, given the scale of the figure. The increase in uncertainty occurs because no jammer observations are av ailable, and therefore, no updates using the jammer return likelihood in ( 9 ) are performed. C . Experiment 2: Multiple RGPO Attacks Results for Experiment 2 are presented in Figure 5 , where the subfigures on the right sho w the av erage num- ber of awake Gaussians, i.e., those in either vigilant or acti ve status, for the adaptiv e strategy . In terms of position RMSE, both the adapti ve and non-adaptiv e methods main- tain errors close to the benchmark. Similar to Experiment 1, both algorithms recover after approximately fiv e time steps following a maneuver , with the adaptiv e method CALA TRA V A ET AL.: MITIGA TION OF RADAR RANGE DECEPTION J AMMING USING RANDOM FINITE SETS 9 providing more resiliency in the second turn. Since Sce- narios 3 and 4 begin under the presence of a jammer , the adaptation period seen in Scenarios 1 and 2, where the adaptive strategy initially had slightly higher errors, is not observed. The multiple jammer observations help refine state estimates when the attack model is effecti vely integrated into the RFS clutter model. This is particularly e vident in Scenario 4, where the benchmark achie ves the lo west RMSE for 40 < k < 60 , the period during which two simultaneous attacks occur . In terms of deception detection, the non-adaptiv e approach finds difficulty in detecting interference when jammer-induced biases de- viate significantly from the assumed priors on jamming ranges, similar to what was observed in Experiment 1. F or example, during time steps 65 < k < 75 in Scenario 3, the non-adaptiv e approach outputs a deception probability belo w 20% despite the presence of interference. A similar issue arises in Scenario 4 for 30 < k < 40 . In contrast, the adaptive strategy reliably detects deception. 0 10 20 30 40 50 60 70 80 90 100 Time step k 0 100 200 Bias [m] Component 1 Adaptive Tracker Jammer-Induced Bias 0 10 20 30 40 50 60 70 80 90 100 Time step k 0 100 200 Bias [m] Component 2 0 10 20 30 40 50 60 70 80 90 100 Time step k -20 0 20 40 Bias [m] Component 3 0 10 20 30 40 50 60 70 80 90 100 Time step k -10 0 10 Bias [m] Component 4 Fig. 6: Bias estimation results for the four components in the adaptiv e approach for multiple RGPO mitigation in Scenario 3. Figure 6 analyzes bias estimation uncertainty for the adapti ve strategy , helping to illustrate the dynamic man- agement of C k . Although one jammer is present from the start of the simulation, the initial Gaussian does not transition to activ e status until k > T act = 7 . At that point, a second component is created in vigilant status, preparing for potential ne w attacks. In Scenario 3, the uncertainty of this second component decreases when a second attack appears at k = 15 . Once this uncertainty remains below U act for more than T act time steps, the second component transitions to active status, and a third component is created in vigilant status. When the first attack ends at k = 50 , C k decreases to 2 . Similar ev ents occur throughout the remainder of the simulation and in Scenario 4, illustrating the dynamic management of C k , which adapts to the occurrence of attacks. D . Loss of Efficiency In Figure 7 , we present a LoE analysis in terms of position RMSE, with results compared to the lower bound as gi ven by the PCRB. The naive tracker con verges to the optimal bound since this experiment assumes nominal conditions (absence of attack). The proposed strategies demonstrate successful tracking, with the difference in position RMSE relativ e to the PCRB remaining almost negligible after k = 10 . 01 0 2 0 3 0 40 50 60 70 80 90 100 Time Step k 10 0 10 1 10 2 Position RMSE [m] 10 20 30 40 50 60 70 0.8 1 1.2 1.4 1.6 1.8 2 Adaptive Tracker Naive Tracker Non-Adaptive Tracker PCRB Fig. 7: LoE analysis of the proposed methods in terms of position RMSE under nominal conditions (no attack). V . CONCLUSION In this paper, we introduce a resilient radar tar get tracking framework that effecti vely counters main-beam range deception jamming attacks. W e use random finite sets to model measurement sets with v ariable cardinality and apply multiple hypothesis tracking to address data association uncertainty . Our approach leverages motion state information and remains feature-independent by in- corporating knowledge about the spatial beha vior of range gate pull-off attacks into the clutter model. W e develop an adaptiv e solution that dynamically estimates jammer- induced biases, alongside a non-adaptive approach that performs well when accurate priors on deception ranges are av ailable. Additionally , we introduce a nov el method for jamming detection and a solution for managing the mixture components in volv ed in a countermeasure against multi-pulse attacks. In terms of position error , both the adapti ve and non-adaptive strategies demonstrate near- optimal performance, improving accuracy by up to 20 meters when compared to an unprotected tracker . The adapti ve approach sho ws a clear advantage in jamming detection due to its ability to reduce uncertainty in the interference spatial model. The proposed strategies main- tain tracking performance in the absence of jamming, as sho wn in the loss of efficienc y analysis using the posterior Cram ´ er-Rao bound as a benchmark. Overall, the intro- duced solutions maintain robust tracking in challenging en vironments, such as when the target is maneuvering with high accelerations while facing simultaneous RGPO attacks. 10 IEEE TRANSACTIONS ON AER OSP A CE AND ELECTR ONIC SYSTEMS V OL. XX, No. XX XXXXX 2024 A CKNOWLEDGMENTS Research was sponsored by the Army Research Lab- oratory and was accomplished under Cooperati ve Agree- ment Number W911NF-23-2-0014. The views and con- clusions contained in this document are those of the authors and should not be interpreted as representing the official policies, either expressed or implied, of the Army Research Laboratory or the U.S. Government. The U.S. Gov ernment is authorized to reproduce and distribute reprints for Government purposes notwithstanding any copyright notation herein. This work has been partially supported by the National Science Foundation under A wards ECCS-1845833 and CCF-2326559. REFERENCES [1] Sergei V akin, Lev Shustov , and Robert Dunwell Fundamentals of Electr onic W arfare 2001. [2] David Adamy EW 101: A F irst Course in Electr onic W arfare Artech house, 2001. [3] Li Neng-Jing and Zhang Y i-T ing “ A survey of radar ecm and eccm, ” IEEE Tr ansactions on Aer ospace and Electr onic Sys- tems , vol. 31, no. 3, pp. 1110–1120, 1995. [4] Y uzhuo W ang and Shengqi Zhu “Main-Beam Range Deceptive Jamming Suppression W ith Simulated Annealing FD A-MIMO Radar, ” IEEE Sensors Journal , vol. 20, no. 16, pp. 9056–9070, Aug. 2020. [5] SJ Roome “Digital radio frequency memory , ” Electr onics & com- munication engineering journal , vol. 2, no. 4, pp. 147–153, 1990. [6] W .D. Blair, G.A. W atson, T . Kirubarajan, and Y . Bar-Shalom “Benchmark for radar allocation and tracking in ECM, ” IEEE T ransactions on Aerospace and Electr onic Systems , vol. 34, no. 4, pp. 1097–1114, Oct. 1998. [7] Y uanhang W ang, Tianxian Zhang, Lingjiang K ong, and Zhijie Ma “Strategy optimization for range gate pull-off track-deception jamming under black-box circumstance, ” IEEE Tr ansactions on Aer ospace and Electronic Systems , vol. 59, no. 4, pp. 4262– 4273, 2023. [8] Rui Jia, Tianxian Zhang, Y uanhang W ang, Y anhong Deng, and Lingjiang Kong “ An Intelligent Range Gate Pull-of f (RGPO) Jamming Method, ” in 2020 International Confer ence on UK- China Emerging T echnologies (UCET) , Glasgow , United King- dom, Aug. 2020, pp. 1–4, IEEE. [9] Y uanhang W ang, Tianxian Zhang, Lingjiang Kong, and Zhijie Ma “ A stochastic simulation optimization-based range gate pull-off jamming method, ” IEEE T ransactions on Evolutionary Computation , vol. 27, no. 3, pp. 580–594, 2023. [10] Gang Lu, Shuangcai Luo, Haiyan Gu, Y ongping Li, and Bin T ang “ Adaptive biased weight-based rgpo/rgpi eccm algorithm, ” in Pr oceedings of 2011 IEEE CIE International Confer ence on Radar , 2011, vol. 2, pp. 1067–1070. [11] Jindong Zhang, Daiyin Zhu, and Gong Zhang “New Antiv elocity Deception Jamming T echnique using Pulses with Adaptive Initial Phases, ” IEEE T ransactions on Aer ospace and Electr onic Systems , vol. 49, no. 2, pp. 1290–1300, Apr . 2013. [12] Jabran Akhtar “ An ECCM Scheme for Orthogonal Independent Range-Focusing of Real and False T argets, ” in 2007 IEEE Radar Conference , W altham, MA, USA, Apr. 2007, pp. 846– 849, IEEE, ISSN: 1097-5659. [13] Jonathan Schuerger and Dmitriy Garmatyuk “Performance of ran- dom OFDM radar signals in deception jamming scenarios, ” in 2009 IEEE Radar Conference . IEEE, 2009, pp. 1–6. [14] Chuan He, Shaopeng W ei, Y achao Li, and Lei Zhang “Feature- Aided RGPO Jamming Discrimination W ithin Wideband Radar Maneuvering T arget Tracking, ” IEEE T ransactions on Aer ospace and Electronic Systems , vol. 59, no. 6, pp. 7938– 7950, Dec. 2023. [15] Lan Lan, Jingwei Xu, Guisheng Liao, Y uhong Zhang, Francesco Fioranelli, and Hing Cheung So “Suppression of mainbeam deceptiv e jammer with fda-mimo radar, ” IEEE T ransactions on V ehicular T echnology , vol. 69, no. 10, pp. 11584–11598, 2020. [16] B.J. Slocumb, P .D. W est, T .N. Shirey , and E.W . Kamen “Tracking a maneuvering target in the presence of false returns and ecm using a variable state dimension kalman filter, ” in Proceedings of 1995 American Control Conference - ACC’95 , 1995, vol. 4, pp. 2611–2615 vol.4. [17] X. Li, Benjamin Slocumb, and Philip W est “T racking in the presence of range deception ecm and clutter by decomposition and fusion, ” Pr oceedings of SPIE - The International Society for Optical Engineering , 10 1999. [18] Maria Greco, Fulvio Gini, and Alfonso Farina “Radar detection and classification of jamming signals belonging to a cone class, ” IEEE T ransactions on Signal Pr ocessing , vol. 56, no. 5, pp. 1984–1993, 2008. [19] Shanshan Zhao, Nan Liu, Linrang Zhang, Y u Zhou, and Qiang Li “Discrimination of deception targets in multistatic radar based on clustering analysis, ” IEEE Sensors Journal , vol. 16, no. 8, pp. 2500–2508, 2016. [20] D. Reid “ An algorithm for tracking multiple targets, ” IEEE T rans- actions on Automatic Control , vol. 24, no. 6, pp. 843–854, 1979. [21] S.S. Blackman “Multiple hypothesis tracking for multiple target tracking, ” IEEE Aer ospace and Electr onic Systems Magazine , vol. 19, no. 1, pp. 5–18, 2004. [22] T . Kirubarajan, Y . Bar-Shalom, W .D. Blair , and G.A. W atson “Immpdaf for radar management and tracking benchmark with ecm, ” IEEE T ransactions on Aer ospace and Electronic Systems , vol. 34, no. 4, pp. 1115–1134, 1998. [23] S.S. Blackman, R.J. Dempster, M.T . Busch, and R.F . Popoli “Imm/mht solution to radar benchmark tracking problem, ” IEEE T ransactions on Aerospace and Electr onic Systems , vol. 35, no. 2, pp. 730–738, 1999. [24] Jing Hou, Y an Y ang, Y i Chen, and Linfeng Xu “Multiple hypoth- esis tracker in the presence of RGPO/RGPI using amplitude information, ” . [25] Ronald P . S. Mahler Statistical multisource-multitar get information fusion Artech House information warfare library . Artech House, Boston, 2007, OCLC: ocn122257615. [26] Lin Gao, Giorgio Battistelli, Luigi Chisci, and Alfonso Farina “Fusion-based multidetection multitarget tracking with random finite sets, ” IEEE T ransactions on Aer ospace and Electronic Systems , vol. 57, no. 4, pp. 2438–2458, 2021. [27] P . Ticha vsky , C.H. Muravchik, and A. Nehorai “Posterior cramer- rao bounds for discrete-time nonlinear filtering, ” IEEE T rans- actions on Signal Pr ocessing , vol. 46, no. 5, pp. 1386–1396, 1998. [28] ´ Angel F . Garc ´ ıa-Fern ´ andez and Lennart Svensson “Tracking mul- tiple spawning targets using Poisson multi-Bernoulli mixtures on sets of tree trajectories, ” IEEE T ransactions on Signal Pr ocessing , vol. 70, pp. 1987–1999, 2022, arXiv:2111.05620 [cs, eess, stat]. [29] Daniel S. Bryant, Ba-Tuong V o, Ba-Ngu V o, and Brandon A. Jones “ A Generalized Labeled Multi-Bernoulli Filter With Object Spawning, ” IEEE T ransactions on Signal Processing , vol. 66, no. 23, pp. 6177–6189, Dec. 2018. [30] Pengfei W an, Y uanlong W eng, Jingwei Xu, and Guisheng Liao “Range Gate Pull-Off Mainlobe Jamming Suppression Ap- proach with FDA-MIMO Radar: Theoretical Formalism and Numerical Study, ” Remote Sensing , vol. 14, no. 6, pp. 1499, Mar . 2022. [31] Ba-T uong V o, Ba-Ngu V o, and Antonio Cantoni “Bayesian Filter- ing With Random Finite Set Observations, ” IEEE T ransactions on Signal Pr ocessing , vol. 56, no. 4, pp. 1313–1326, Apr . 2008. CALA TRA V A ET AL.: MITIGA TION OF RADAR RANGE DECEPTION J AMMING USING RANDOM FINITE SETS 11 [32] D. J. Salmond “Mixture reduction algorithms for point and extended object tracking in clutter , ” IEEE T ransactions on Aer ospace and Electronic Systems , vol. 45, no. 2, pp. 667–686, 2009. [33] Branko Ristic, Sanjeev Arulampalam, and Neil J. Gordon “Beyond the kalman filter: Particle filters for tracking applications, ” 2004. [34] Y . Ho and R. Lee “ A bayesian approach to problems in stochas- tic estimation and control, ” IEEE T ransactions on Automatic Contr ol , vol. 9, no. 4, pp. 333–339, 1964. [35] S. Cong and L. Hong “Computational complexity analysis for multiple hypothesis tracking, ” Mathematical and Computer Modelling , vol. 29, no. 9, pp. 1–16, 1999. [36] Ke vin Murphy and Stuart Russell, Rao-Blackwellised P article Filtering for Dynamic Bayesian Networks , pp. 499–515, Springer New Y ork, New Y ork, NY , 2001. Helena Calatrava receiv ed her BS and MS degrees in Electrical Engineering from Uni- versitat Polit ` ecnica de Catalunya, Barcelona, Spain, in 2020 and 2022, respecti vely . She is currently a PhD candidate in Electrical En- gineering at Northeastern Univ ersity , Boston, MA. Her research focuses on Bayesian filter- ing, physics-informed machine learning, anti- jamming and signal processing for GNSS and radar applications. Aanjhan Ranganathan is Associate Profes- sor at Northeastern University , Boston. His re- search revolves around the security and priv acy of wireless networks with a strong focus on autonomous cyber-ph ysical systems and smart ecosystems. He is a recipient of several aw ards, including the prestigious NSF CAREER award, the outstanding dissertation aw ard from ETH Zurich, the regional winner of European Space Agency’ s Satellite Navigation competition, and the Cyber A ward from armasuisse (Switzerland’ s Department of De- fense). T ales Imbiriba (Member, IEEE) is an Assis- tant Research Professor at the ECE dept., and Senior Research Scientist at the Institute for Experiential AI, both at Northeastern Univer - sity (NU), Boston, MA, USA. He recei ved his Doctorate degree from the Department of Elec- trical Engineering (DEE) of the Federal Uni ver - sity of Santa Catarina (UFSC), Florian ´ opolis, Brazil, in 2016. He served as a Postdoctoral Researcher at the DEE–UFSC (2017–2019) and at the ECE dept. of the NU (2019–2021). His research interests include audio and image processing, pattern recognition, Bayesian inference, online learning, and physics-guided machine learning. Gunar Schirner (S’04–M’08) holds PhD (2008) and MS (2005) degrees in electrical and computer engineering from the Univer - sity of California, Irvine. He is currently an Associate Professor in Electrical and Com- puter Engineering at Northeastern University . His research interests include the modelling and design automation principles for domain platforms, real-time c yber-physical systems and the algorithm/architecture co-design of high- performance efficient edge compute systems. Murat Akcakaya (Senior Member , IEEE) re- ceiv ed his Ph.D. degree in Electrical Engi- neering from the W ashington University in St. Louis, MO, USA, in December 2010. He is cur- rently an Associate Professor in the Electrical and Computer Engineering Department of the Univ ersity of Pittsburgh. His research interests are in the areas of statistical signal processing and machine learning. Pau Closas (Senior Member, IEEE), is an Associate Professor in Electrical and Com- puter Engineering at Northeastern University , Boston MA. He recei ved the MS and PhD in Electrical Engineering from UPC in 2003 and 2009, respectively , and a MS in Advanced Mathematics from UPC in 2014. His primary areas of interest include statistical signal pro- cessing and machine learning, with applications to positioning and localization systems. 12 IEEE TRANSACTIONS ON AER OSP A CE AND ELECTR ONIC SYSTEMS V OL. XX, No. XX XXXXX 2024
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment