The Feasibility of a Smart Contract "Kill Switch"
The advent of blockchain technology and its adoption across various sectors have raised critical discussions about the need for regulatory mechanisms to ensure consumer protection, maintain financial stability, and address privacy concerns without compromising the foundational principles of decentralization and immutability inherent in blockchain platforms. We examine the existing mechanisms for smart contract termination across several major blockchain platforms, including Ethereum, BNB Smart Chain, Cardano, Solana, Hyperledger Fabric, Corda, IOTA, Apotos, and Sui. We assess the compatibility of these mechanisms with the requirements of the EU Data Act, focusing on aspects such as consumer protection, error correction, and regulatory compliance. Our analysis reveals a diverse landscape of approaches, from immutable smart contracts with built-in termination conditions to upgradable smart contracts that allow for post-deployment modifications. We discuss the challenges associated with implementing the so-called smart contract “kill switches,” such as the balance between enabling regulatory compliance and preserving the decentralized ethos, the technical feasibility of such mechanisms, and the implications for security and trust in the ecosystem.
💡 Research Summary
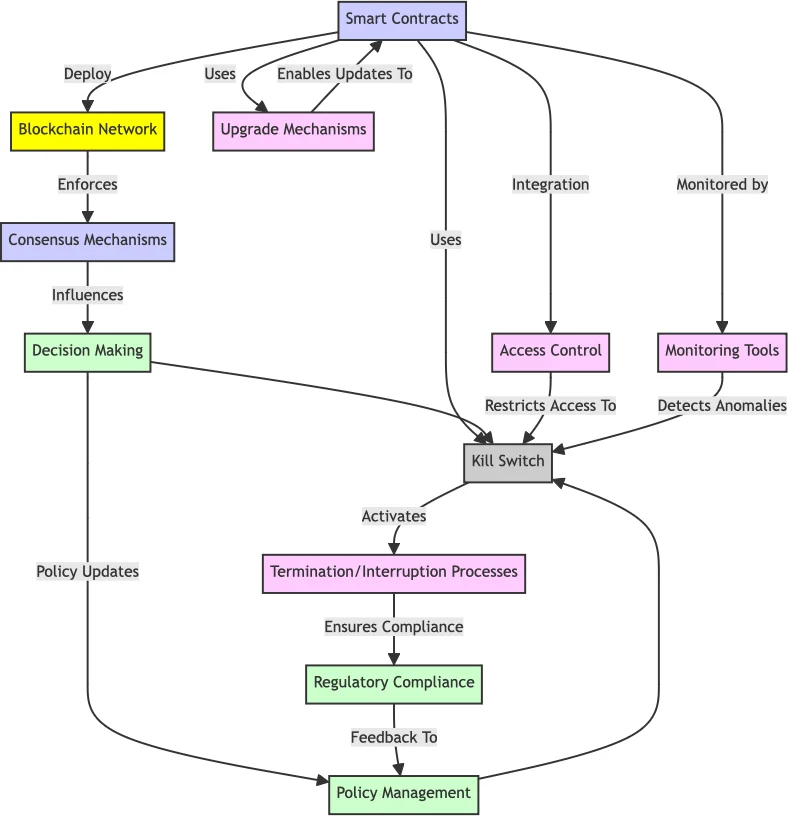
The paper investigates the concept of a “kill switch” for smart contracts—an on‑chain mechanism that allows a contract to be disabled or altered after deployment—and evaluates its feasibility across a representative set of blockchain platforms in light of the European Union’s Data Act. The authors begin by outlining the tension between blockchain’s core principles of immutability and decentralization and the regulatory need for consumer protection, error correction, and the right to delete or modify data. They then map the key obligations of the Data Act (prompt remediation, transparency of actions, and limited, accountable authority) to the technical capabilities of each platform.
Methodology
A systematic review was performed on nine platforms: Ethereum, BNB Smart Chain, Cardano, Solana, Hyperledger Fabric, Corda, IOTA, Apotos, and Sui. For each, the authors examined official documentation, open‑source implementations, and interviews with core developers. The analysis framework comprised five dimensions: (1) termination or upgrade mechanisms, (2) authority model, (3) degree of decentralization retained, (4) alignment with Data Act requirements, and (5) security and trust implications.
Platform‑Specific Findings
-
Ethereum – Uses proxy patterns (e.g., TransparentUpgradeableProxy) that separate storage from logic. By combining a multi‑signature wallet (Gnosis Safe) with timelocks, a kill‑switch can be triggered with 2‑3 approvals, satisfying both speed and accountability. However, the upgrade path introduces re‑entrancy and storage‑collision risks that must be mitigated with initializer guards.
-
BNB Smart Chain – Fully EVM‑compatible, allowing the same proxy‑based approach. In addition, BNB’s native governance token can be leveraged for DAO‑style voting on contract deactivation, which aligns well with the Data Act’s transparency clause.
-
Cardano – Smart contracts are written in Plutus and lack a native “self‑destruct” primitive. Only limited parameter updates are possible, and any kill‑switch would require an external governance layer that adds considerable complexity and may conflict with Cardano’s emphasis on formal verification.
-
Solana – Supports program upgrades, but the upgrade authority is typically a single key. Introducing multi‑signature or threshold schemes can enable a kill‑switch, yet no standardized process exists yet.
-
Hyperledger Fabric – As a permissioned network, chaincode can be installed, upgraded, or removed by organizational administrators. This gives regulators immediate control, satisfying the Data Act’s promptness requirement, but it sacrifices the decentralization that public blockchains aim to preserve.
-
Corda – Contracts are represented as states that can be “consumed” only with the consent of all involved parties. A regulator can be granted a privileged role to consume a state, effectively disabling the contract, but this again leans toward a centralized authority model.
-
IOTA – Relies on off‑chain authentication to decide whether a smart contract transaction is accepted. If the authentication service revokes a certificate, the contract is effectively disabled. However, the system’s security hinges on the trustworthiness of that external service, creating a single point of failure.
-
Apotos – Early‑stage platform that provides a built‑in “conditional termination” function. Only a pre‑designated manager address can issue a termination transaction, which is simple but concentrates power.
-
Sui – Built on the Move language, Sui supports upgradeable packages. By requiring a threshold of signatures and a timelock before a package can be replaced, a kill‑switch can be realized without breaking the Move safety guarantees.
Alignment with the EU Data Act
The Data Act demands rapid, auditable deactivation of contracts that mishandle personal data or violate consumer rights. Permissioned platforms (Fabric, Corda) meet the speed requirement but do so at the cost of decentralization. Public platforms need a hybrid approach: on‑chain multi‑signature approval, timelocks, and transparent event logs. Ethereum, BNB Smart Chain, and Sui emerge as the most adaptable because their proxy/upgrade mechanisms can be wrapped with governance controls that satisfy the Data Act’s three pillars (promptness, transparency, limited authority).
Security and Trust Trade‑offs
Introducing a kill‑switch inevitably expands the attack surface. Proxy address changes can be exploited for re‑entrancy attacks; governance voting can be subverted by a 51 % style collusion; off‑chain authentication can be spoofed. The authors recommend a set of hardening measures: (1) immutable audit events emitted before and after a kill‑switch activation, (2) mandatory multi‑signature plus timelock to prevent rushed or unilateral actions, (3) role separation where the entity that can trigger the switch is distinct from the entity that can propose upgrades, and (4) optional external watchdogs (e.g., regulatory auditors) that can verify the legitimacy of a deactivation request using on‑chain proofs.
Policy Recommendations
The paper calls for the EU to develop a “Smart Contract Kill‑Switch Standard” that defines minimum governance and audit requirements, encouraging blockchain communities to adopt a common multi‑stage approval protocol. Developers should embed termination logic at design time, include clearly defined upgrade paths, and expose transparent logs for regulator inspection.
Conclusion
A smart‑contract kill‑switch is technically feasible across most major platforms, but its implementation must be carefully balanced against the core blockchain values of immutability and decentralization. A hybrid model that couples on‑chain upgradeability with multi‑signature, timelocked, and publicly auditable governance offers the most pragmatic solution, delivering the regulatory compliance demanded by the Data Act while preserving a meaningful degree of trustlessness. The authors conclude that future research should focus on formal verification of kill‑switch logic and on interoperable standards that can be adopted across heterogeneous blockchain ecosystems.
Comments & Academic Discussion
Loading comments...
Leave a Comment