Locating privileged spreaders on an Online Social Network
Social media have provided plentiful evidence of their capacity for information diffusion. Fads and rumors, but also social unrest and riots travel fast and affect large fractions of the population participating in online social networks (OSNs). This has spurred much research regarding the mechanisms that underlie social contagion, and also who (if any) can unleash system-wide information dissemination. Access to real data, both regarding topology –the network of friendships– and dynamics –the actual way in which OSNs users interact–, is crucial to decipher how the former facilitates the latter’s success, understood as efficiency in information spreading. With the quantitative analysis that stems from complex network theory, we discuss who (and why) has privileged spreading capabilities when it comes to information diffusion. This is done considering the evolution of an episode of political protest which took place in Spain, spanning one month in 2011.
💡 Research Summary
The paper investigates who the “privileged spreaders” are in an online social network (OSN) by analysing a real‑world dataset from the Spanish “15 M” protest movement of 2011. The authors collected 535,192 tweets posted between April 25 and May 26 2011 that contained any of 70 protest‑related hashtags, authored by 85,851 unique users. They then reconstructed the directed follower network of the 87,569 users who participated, obtaining a static graph where an edge points from a user to each of his/her followers. The network exhibits classic small‑world properties (short average path length, high clustering) and a scale‑free degree distribution, indicating the presence of a few highly connected hubs.
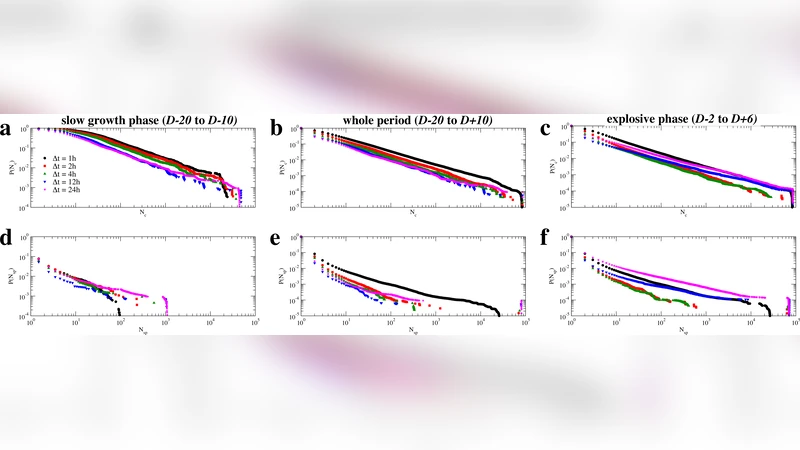
To study information diffusion, the authors define an “activity cascade”. A seed tweet at time t₀ is instantly received by all of the seed’s followers (listeners). If any listener posts a tweet within a short time window Δt (≤ 24 h), that listener becomes a spreader and his/her followers are added to the cascade, and the process repeats recursively. A cascade is considered global when its final size N_c is comparable to the total number of users N. Two types of cascades are measured: (i) information cascades that count both listeners and spreaders, and (ii) spreader‑only cascades that count only the active propagators.
The authors split the month‑long observation period into three temporal regimes: (a) a “slow‑growth” phase (D‑20 to D‑10) where activity rose slowly (< 5 % of users became active), (b) an “explosive” or “bursty” phase (D‑2 to D + 6) where activity surged dramatically (from < 10 % to > 80 % of users), and (c) the full period (D‑20 to D + 10) which combines both. For each regime they compute the probability distributions of cascade sizes and of the number of spreaders involved. Large cascades (size O(N)) appear in all regimes but are rare, following a power‑law tail. However, the distribution of spreader counts differs markedly: the slow‑growth phase requires far fewer spreaders to achieve a large cascade than the bursty phase, suggesting a shift from a sub‑critical to a super‑critical spreading regime.
To identify structural predictors of spreading power, the authors apply k‑core decomposition to the follower network. The k‑core of a node is obtained by iteratively removing all vertices whose total degree (in‑degree + out‑degree) is less than k; the remaining subgraph defines the k‑core, and each node receives a coreness value equal to the highest k for which it survives. This measure is computationally cheap (O(N + E)) and has been shown to correlate with epidemic spreading ability in other contexts. The paper compares coreness with simple degree centrality as predictors of cascade size.
Results show that nodes with high coreness are far more likely to act as privileged spreaders than nodes with high degree alone. Even during the low‑activity slow‑growth phase, a few high‑coreness users can trigger cascades that involve a substantial fraction of the network. During the bursty phase, many more spreaders participate, but the cascade’s ultimate reach is still dominated by a small set of high‑coreness nodes. Thus, structural position (core location) is a more reliable indicator of influence than raw follower count.
The study concludes that privileged spreaders are not randomly scattered but occupy central positions in the network’s core. Their influence persists across different activity regimes, implying that models of information diffusion should incorporate both temporal dynamics and core‑based centrality. Practically, the findings suggest that viral marketing, public‑health messaging, or political mobilization campaigns could be made more efficient by targeting high‑coreness users rather than simply those with many followers. Moreover, the methodology—combining cascade reconstruction with k‑core analysis—offers a scalable framework for real‑time identification of influential actors in large OSNs.
Comments & Academic Discussion
Loading comments...
Leave a Comment