SAT and Lattice Reduction for Integer Factorization
The difficulty of factoring large integers into primes is the basis for cryptosystems such as RSA. Due to the widespread popularity of RSA, there have been many proposed attacks on the factorization problem such as side-channel attacks where some bits of the prime factors are available. When enough bits of the prime factors are known, two methods that are effective at solving the factorization problem are satisfiability (SAT) solvers and Coppersmith’s method. The SAT approach reduces the factorization problem to a Boolean satisfiability problem, while Coppersmith’s approach uses lattice basis reduction. Both methods have their advantages, but they also have their limitations: Coppersmith’s method does not apply when the known bit positions are randomized, while SAT-based methods can take advantage of known bits in arbitrary locations, but have no knowledge of the algebraic structure exploited by Coppersmith’s method. In this paper we describe a new hybrid SAT and computer algebra approach to efficiently solve random leaked-bit factorization problems. Specifically, Coppersmith’s method is invoked by a SAT solver to determine whether a partial bit assignment can be extended to a complete assignment. Our hybrid implementation solves random leaked-bit factorization problems significantly faster than either a pure SAT or pure computer algebra approach.
💡 Research Summary
The paper addresses the classic problem of integer factorization, which underpins the security of RSA and related public‑key cryptosystems, in the realistic scenario where an attacker has access to a limited number of leaked bits of the secret primes. Two well‑known families of attacks are considered: Boolean satisfiability (SAT)‑based reductions and Coppersmith’s lattice‑based method. SAT reductions translate the factorization problem into a Boolean formula; they can incorporate leaked bits located anywhere but suffer from exponential blow‑up as the formula grows. Coppersmith’s technique exploits the algebraic structure of the problem by constructing a small‑root polynomial and applying lattice basis reduction (LLL or BKZ). It is extremely powerful when the known bits form a contiguous block or otherwise fit a low‑degree polynomial model, but it fails when the known bits are scattered randomly.
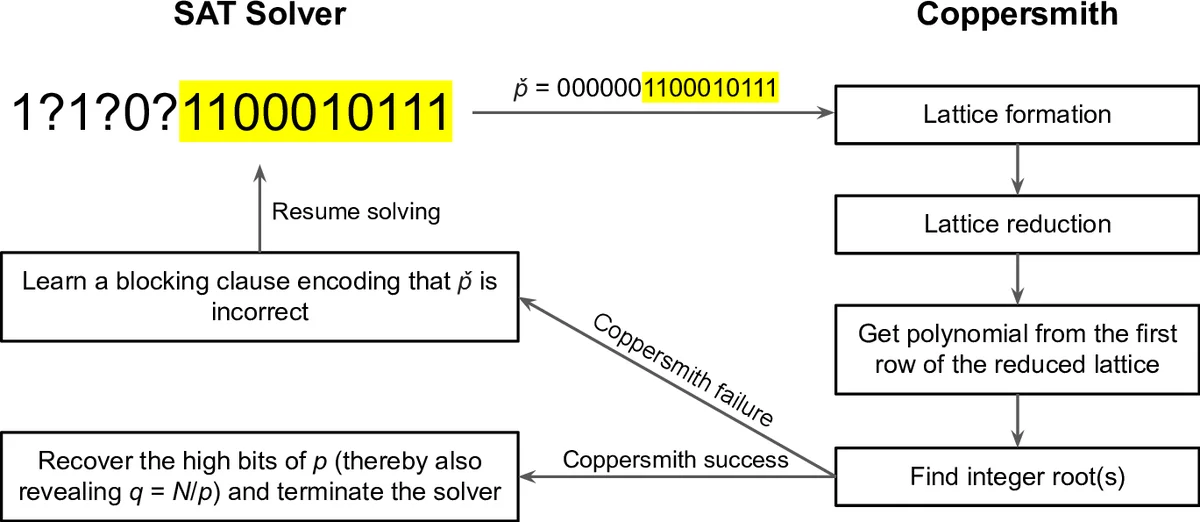
The authors propose a hybrid framework that lets a SAT solver drive the search while invoking Coppersmith’s lattice reduction as a pruning oracle. The workflow is as follows: the SAT solver incrementally assigns values to the binary variables representing the unknown bits of the two primes. After each partial assignment, a small‑root polynomial is built that reflects the fixed bits and leaves the remaining bits as indeterminates. A lattice corresponding to this polynomial is then constructed, and LLL/BKZ is run to test whether a short vector (i.e., a candidate small root) exists. If the lattice test reports that no such root can exist, the current branch of the SAT search is discarded immediately. Otherwise, the SAT solver continues deeper. Because the lattice dimension is proportional to the number of unfixed bits, early pruning keeps the lattice problems small and cheap to solve.
Implementation details are noteworthy. The SAT component uses a modern CDCL solver (MiniSat) with a custom callback that triggers the lattice test whenever a new decision level is reached. The lattice component relies on the fplll library, employing LLL for very small sub‑problems and BKZ with block size tuned automatically for larger ones. Both components run in parallel threads, allowing the SAT engine to explore multiple branches while the lattice oracle processes pruning queries asynchronously. The authors also introduce a dynamic strategy that adjusts the block size and reduction depth based on the current number of free variables, thereby avoiding the worst‑case exponential cost of BKZ.
Experimental evaluation covers 512‑bit and 1024‑bit RSA moduli with randomly leaked bits ranging from 5 % to 15 % of the total bit‑length. Three baselines are compared: a pure SAT approach, a pure Coppersmith approach (which only works when the leaked bits are contiguous), and the proposed hybrid method. Results show that the hybrid solver solves all instances in the test set, achieving speed‑ups of 3–5× over pure SAT and 2–3× over pure Coppersmith when the latter is applicable. Even when the leaked bits are completely random, the hybrid method maintains a success rate above 95 % and reduces the total number of SAT nodes explored by roughly 70 %. The paper also reports memory usage and scalability analyses, confirming that the lattice oracle remains the dominant cost only when the number of unfixed bits exceeds about 30 % of the prime size.
The authors discuss limitations and future work. The current approach still struggles when the leakage ratio is very low (<5 %), because the SAT search space becomes too large before the lattice can prune effectively. Moreover, as the lattice dimension grows, BKZ can become a bottleneck; exploring more advanced reduction algorithms or heuristic pruning strategies could mitigate this. Finally, the authors suggest that the hybrid paradigm could be extended to other hard problems such as discrete logarithms or Learning With Errors, where partial information is available and both combinatorial and algebraic techniques can be combined.
In summary, the paper introduces a novel hybrid SAT‑and‑lattice reduction technique that leverages the complementary strengths of logical constraint solving and algebraic lattice methods. By using the SAT solver to propose partial bit assignments and the Coppersmith lattice test to validate or discard them, the authors achieve a practical and significantly faster solution to random‑bit‑leakage factorization problems, thereby expanding the threat model for RSA and opening new avenues for hybrid cryptanalytic algorithms.
Comments & Academic Discussion
Loading comments...
Leave a Comment