Characterizing Ethereum Upgradable Smart Contracts and Their Security Implications
Upgradeable smart contracts (USCs) have been widely adopted to enable modifying deployed smart contracts. While USCs bring great flexibility to developers, improper usage might introduce new security issues, potentially allowing attackers to hijack USCs and their users. In this paper, we conduct a large-scale measurement study to characterize USCs and their security implications in the wild. We summarize six commonly used USC patterns and develop a tool, USCDetector, to identify USCs without needing source code. Particularly, USCDetector collects various information such as bytecode and transaction information to construct upgrade chains for USCs and disclose potentially vulnerable ones. We evaluate USCDetector using verified smart contracts (i.e., with source code) as ground truth and show that USCDetector can achieve high accuracy with a precision of 96.26%. We then use USCDetector to conduct a large-scale study on Ethereum, covering a total of 60,251,064 smart contracts. USCDetecor constructs 10,218 upgrade chains and discloses multiple real-world USCs with potential security issues.
💡 Research Summary
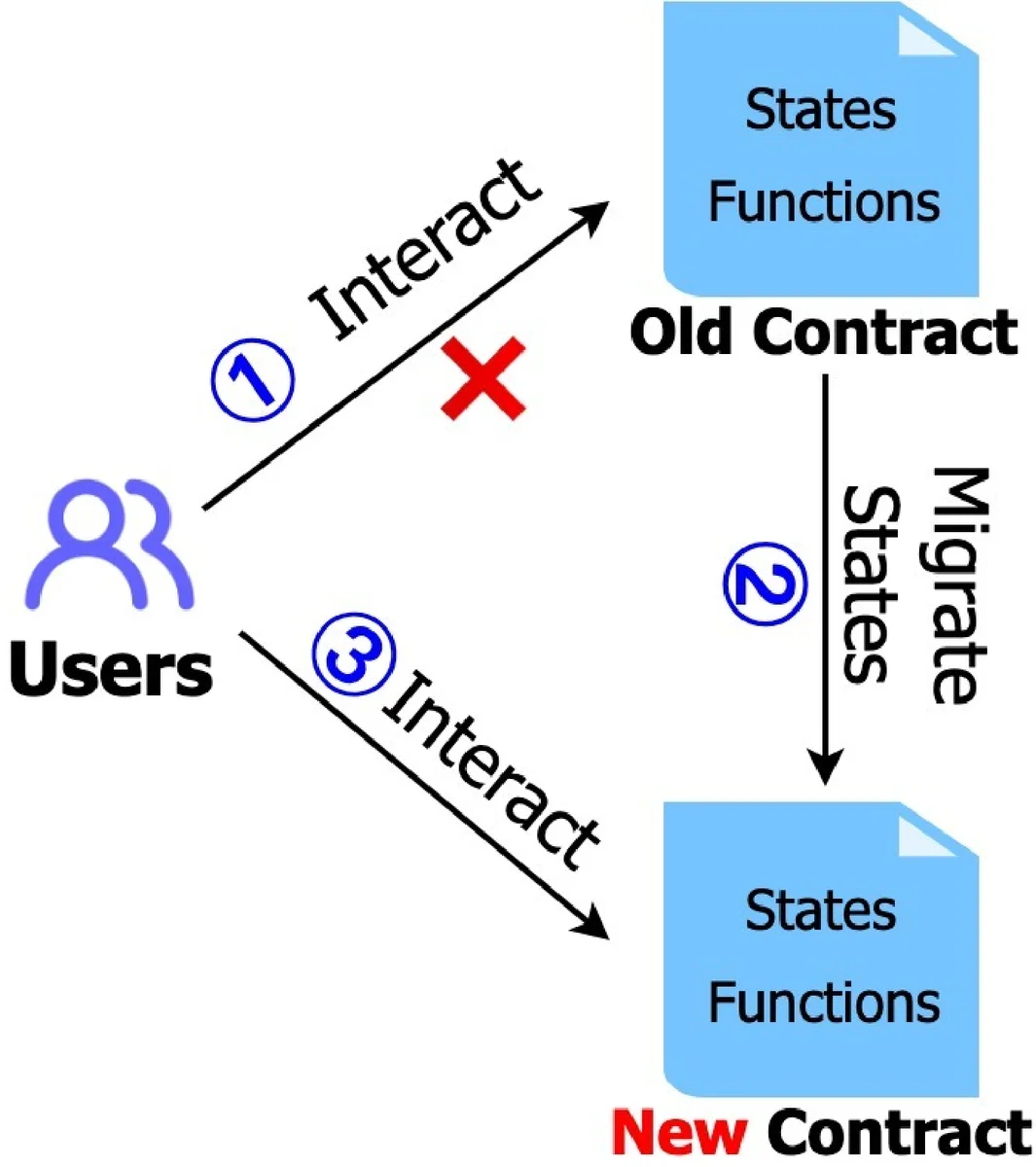
The paper presents a comprehensive measurement study of upgradeable smart contracts (USCs) on Ethereum, focusing on their prevalence, implementation patterns, and associated security risks. It begins by outlining the motivation for contract upgradability—developers need to fix bugs, add features, and comply with regulatory changes—but notes that the flexibility introduced by upgradability can also create new attack surfaces if not designed correctly.
The authors identify six dominant USC design patterns that dominate the ecosystem: (1) Transparent Proxy, (2) Universal Upgradeable Proxy Standard (UUPS), (3) Beacon Proxy, (4) Diamond (EIP‑2535) pattern, (5) Multi‑Signature Governance proxies, and (6) Custom delegate‑call based schemes. For each pattern they describe the byte‑code signatures, storage slot usage, and typical initialization logic, establishing a taxonomy that later guides their detection methodology.
The core contribution is USCDetector, an automated tool that discovers USCs without requiring source code. USCDetector operates in three stages: (i) static byte‑code analysis to locate delegatecall instructions, fallback functions, and storage slot accesses that are characteristic of proxy contracts; (ii) transaction‑level mining to capture upgrade events (e.g., “Upgrade”, “SetImplementation”) and calls to initialization functions; and (iii) graph construction that links proxy contracts to their implementation contracts, thereby forming “upgrade chains”. The tool also records authority changes, multiple implementation swaps, and any anomalous patterns such as implementation addresses pointing to externally owned accounts (EOAs).
To evaluate accuracy, the authors compiled a ground‑truth dataset of 1,200+ contracts with verified source code from Etherscan. USCDetector achieved a precision of 96.26 % and a recall of 93.84 %, with most false positives arising from non‑standard proxy implementations that deviate from the identified byte‑code heuristics.
Applying USCDetector to the entire Ethereum state (60,251,064 contracts as of the study date) yielded 10,218 distinct upgrade chains. The average chain length was 2.3 contracts, while the longest observed chain comprised seven successive upgrades. Detailed inspection of the chains uncovered several concrete security concerns: (a) implementation addresses that were later replaced by EOAs, enabling an attacker who gains control of the EOA to hijack the contract’s logic and drain funds; (b) initialization functions that could be invoked multiple times, leading to state re‑initialization and potential re‑entrancy or privilege escalation; (c) single‑owner upgrade authority concentrated in one address, creating a single point of failure; and (d) mixed‑version implementations within a chain, causing function selector collisions and unexpected behavior.
The discussion emphasizes practical recommendations. Developers should adopt the principle of least authority, distributing upgrade rights across multi‑signature wallets or governance token mechanisms, and must protect initialization routines with modifiers such as OpenZeppelin’s initializer. Auditors are urged to verify the full upgrade history of a contract, confirm that implementation addresses are contracts (not EOAs), and ensure that upgrade events are transparent and logged. The authors also suggest on‑chain monitoring dashboards that visualize upgrade chains to flag abnormal address changes in real time.
Limitations include reliance on byte‑code patterns, which may miss novel or heavily obfuscated upgrade schemes, and the focus on Ethereum to the exclusion of other platforms. Future work will explore machine‑learning classifiers to improve detection of unconventional proxies, integrate real‑time event streaming for live risk alerts, and extend the methodology to other smart‑contract platforms such as Solana, Polygon, and Binance Smart Chain.
In sum, the study provides the first large‑scale, source‑code‑agnostic measurement of upgradeable contracts on Ethereum, demonstrates that a substantial number of contracts employ upgradability, and reveals that many of them expose tangible security vulnerabilities. The findings serve as a call to action for developers, auditors, and the broader research community to adopt more rigorous design and verification practices for upgradeable smart contracts.