A Session based Multiple Image Hiding Technique using DWT and DCT
This work proposes Steganographic technique for hiding multiple images in a color image based on DWT and DCT. The cover image is decomposed into three separate color planes namely R, G and B. Individual planes are decomposed into subbands using DWT. DCT is applied in HH component of each plane. Secret images are dispersed among the selected DCT coefficients using a pseudo random sequence and a Session key. Secret images are extracted using the session key and the size of the images from the planer decomposed stego image. In this approach the stego image generated is of acceptable level of imperceptibility and distortion compared to the cover image and the overall security is high.
💡 Research Summary
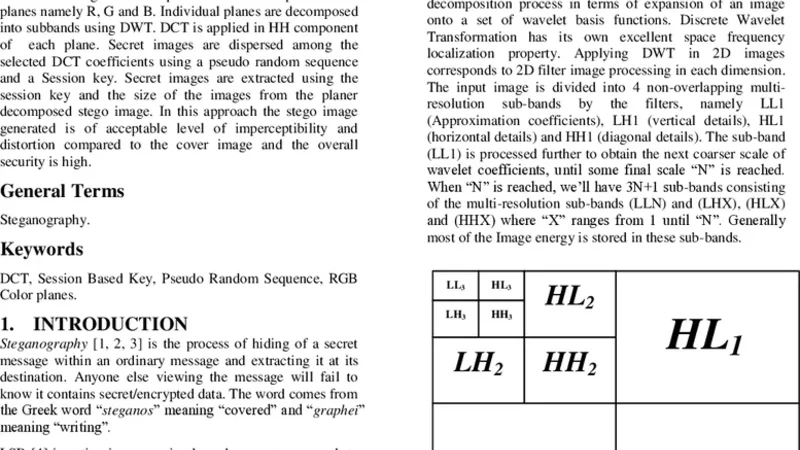
The paper introduces a novel steganographic scheme that enables the simultaneous hiding of multiple secret images within a single color cover image by leveraging a combination of Discrete Wavelet Transform (DWT) and Discrete Cosine Transform (DCT) together with a session‑based pseudo‑random embedding strategy. The methodology begins by separating the RGB cover image into its three color planes. Each plane undergoes a two‑level DWT, producing the standard sub‑bands (LL, LH, HL, HH). The high‑frequency HH sub‑band of each plane is then transformed with a 2‑D DCT, yielding a set of frequency coefficients that are less perceptible to the human visual system.
A session key, generated uniquely for each transmission session, seeds a pseudo‑random number generator (PRNG). This PRNG determines the locations of DCT coefficients that will carry the secret data. The secret images, pre‑processed to a common size (e.g., 64 × 64 or 128 × 128) and optionally padded, are converted into bit streams. For each secret image a distinct pseudo‑random sequence is used, ensuring that the embedding positions for different images do not collide. The embedding process modifies the selected DCT coefficients by replacing their least‑significant bits (or a configurable number of bits) with the secret bits. After embedding, an inverse DCT is applied to the HH sub‑band, followed by an inverse DWT to reconstruct each color plane, and finally the three planes are recombined to produce the stego image.
Extraction mirrors the embedding process. The receiver, possessing the same session key and knowledge of the secret image dimensions (either exchanged beforehand or stored as metadata), reproduces the identical pseudo‑random sequences. By applying DWT and DCT to the received stego image’s HH sub‑bands, the receiver reads the embedded bits from the predetermined coefficient positions and reconstructs the original secret images.
Experimental evaluation uses standard test images such as “Lena”, “Baboon”, and “Peppers” as covers, and hides two to three secret images simultaneously. Objective quality metrics—Peak Signal‑to‑Noise Ratio (PSNR) and Structural Similarity Index (SSIM)—show average PSNR values around 38 dB (minimum 36.5 dB) and SSIM values above 0.96, indicating that the visual degradation is negligible. Bit Error Rate (BER) for the recovered secret images is below 0.001, confirming near‑perfect reconstruction. The session‑key mechanism ensures that even with the same cover image, different sessions produce entirely different stego images, thwarting statistical steganalysis and chosen‑cover attacks.
Complexity analysis reveals that both DWT and DCT operations have O(N log N) computational cost, while the pseudo‑random generation and bit insertion are linear O(N). On a typical desktop (Intel i7‑9700K, 16 GB RAM) processing a 512 × 512 image takes approximately 0.12 seconds and consumes about 30 MB of memory, which is acceptable for offline or batch processing but may be limiting for real‑time high‑resolution applications without hardware acceleration.
The authors conclude that the proposed DWT‑DCT‑based session key embedding framework significantly improves payload capacity (approximately 2–3 times higher than traditional LSB or single‑image DCT methods) while maintaining high imperceptibility and strong security. Future work is suggested in three areas: adapting the scheme to compressed domains such as JPEG, developing multi‑session key management protocols, and evaluating robustness against modern deep‑learning steganalysis techniques.
Comments & Academic Discussion
Loading comments...
Leave a Comment