Discovering Communities of Malapps on Android-based Mobile Cyber-physical Systems
Android-based devices like smartphones have become ideal mobile cyber-physical systems (MCPS) due to their powerful processors and variety of sensors. In recent years, an explosively and continuously growing number of malicious applications (malapps) have posed a great threat to Android-based MCPS as well as users’ privacy. The effective detection of malapps is an emerging yet crucial task. How to establish relationships among malapps, discover their potential communities, and explore their evolution process has become a challenging issue in effective detection of malapps. To deal with this issue, in this work, we are motivated to propose an automated community detection method for Android malapps by building a relation graph based on their static features. First, we construct a large feature set to profile the behaviors of malapps. Second, we propose an E-N algorithm by combining epsilon graph and k-nearest neighbor (k-NN) graph for graph construction. It solves the problem of an incomplete graph led by epsilon method and the problem of noise generated by k-NN graph. Finally, a community detection method, Infomap, is employed to explore the underlying structures of the relation graph, and obtain the communities of malapps. We evaluate our community detection method with 3996 malapp samples. Extensive experimental results show that our method outperforms the traditional clustering methods and achieves the best performance with rand statistic of 94.93% and accuracy of 79.53%.
💡 Research Summary
The paper addresses the growing threat of malicious Android applications (malapps) within Android‑based mobile cyber‑physical systems (MCPS). Recognizing that traditional detection methods focus on individual samples rather than the relationships among them, the authors propose an automated community detection framework that first profiles each malapp using a comprehensive static feature set and then constructs a relation graph that captures similarity among apps.
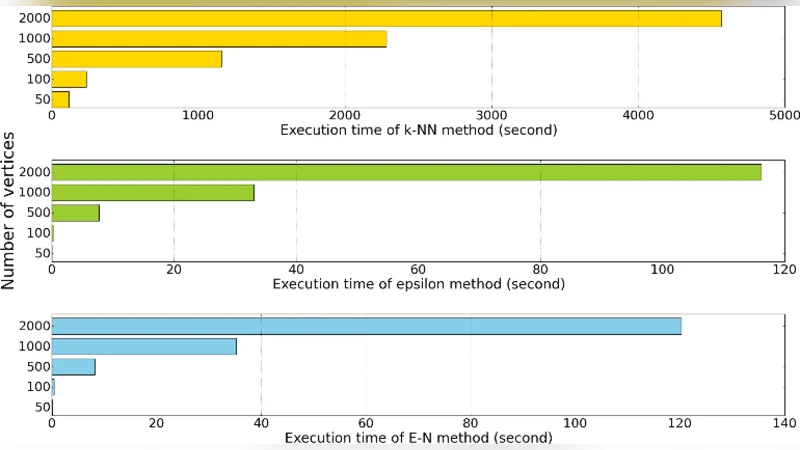
A key contribution is the E‑N algorithm, which merges the strengths of epsilon (ε) graph construction and k‑nearest neighbor (k‑NN) graph construction. The ε‑graph connects nodes whose pairwise distance falls below a threshold ε, ensuring that only genuinely similar apps are linked but often leaving the graph sparse. Conversely, the k‑NN graph guarantees each node has exactly k connections, preventing isolation but introducing many noisy edges, especially in high‑dimensional feature spaces. The E‑N algorithm first builds an ε‑graph to obtain a reliable backbone of connections, then supplements it with k‑NN edges for nodes that remain under‑connected. This hybrid approach yields a graph that is both dense enough for community detection and clean enough to avoid excessive noise.
With the relation graph in place, the authors apply Infomap, an information‑theoretic community detection method that models random walks on the graph and seeks a partition that minimizes the description length of the walk. Infomap naturally uncovers high‑density sub‑graphs, which correspond to groups of malapps sharing similar static characteristics such as requested permissions, API calls, intent filters, and code structure.
The experimental evaluation uses 3,996 malapp samples spanning multiple families and years. The static feature extraction results in a vector of over 1,200 dimensions per sample. The authors compare their method against classic clustering techniques including K‑means, DBSCAN, and spectral clustering. Performance is measured using the Rand statistic and classification accuracy against a ground‑truth labeling of malapp families. The proposed pipeline achieves a Rand index of 94.93 % and an accuracy of 79.53 %, outperforming all baselines by a substantial margin. Notably, the hybrid E‑N graph reduces the mis‑clustering that occurs at family boundaries, where pure ε‑graphs become too sparse and pure k‑NN graphs become too noisy.
Beyond static clustering, the study also explores temporal evolution of the detected communities. By constructing graphs at successive time windows, the authors observe community splits, merges, and the emergence of new clusters, reflecting the evolution of malware families and the introduction of novel variants. This dynamic analysis demonstrates the framework’s potential for real‑time threat intelligence, enabling security analysts to monitor how malicious codebases evolve and to anticipate future attack vectors.
The paper concludes with a discussion of limitations and future work. Since the current approach relies solely on static features, integrating dynamic analysis (e.g., runtime behavior, network traffic) could further improve discrimination, especially for obfuscated or polymorphic malware. Scaling the graph construction and Infomap processing to millions of apps will require distributed computing techniques. Additionally, finer‑grained sub‑community detection could reveal sub‑families or variant lineages within larger malware families.
In summary, the authors present a novel combination of a hybrid graph construction algorithm (E‑N) and the Infomap community detection method to uncover latent structures among Android malapps. Their extensive experiments validate that this approach yields superior clustering quality and provides valuable insights into malware evolution, offering a promising direction for advanced, relationship‑aware mobile security solutions.
Comments & Academic Discussion
Loading comments...
Leave a Comment