Personal Mobile Malware Guard PMMG: a mobile malware detection technique based on users preferences
Mobile malware has increased rapidly last 10 years. This rapid increase is due to the rapid enhancement of mobile technology and their power to do most work for their users. Since mobile devices are personal devices, then a special action must be taken towards preserving privacy and security of the mobile data. Malware refers to all types of software applications with malicious behavior. In this paper, we propose a malware detection technique called Personal Mobile Malware Guard ? PMMG- that classifies malwares based on the mobile user feedback. PMMG controls permissions of different applications and their behavior according to the user needs. These preferences are built incrementally on a personal basis according to the feedback of the user. Performance analysis showed that it is theoretically feasible to build PMMG tool and use it on mobile devices.
💡 Research Summary
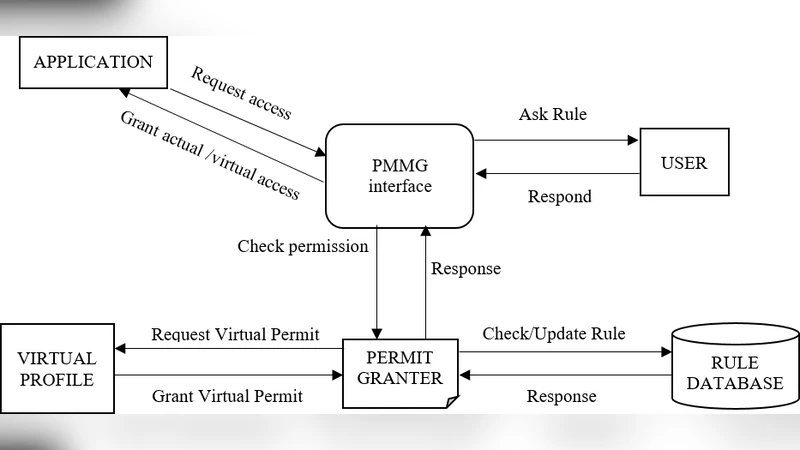
The paper addresses the rapid growth of mobile malware over the past decade by proposing a novel detection framework called Personal Mobile Malware Guard (PMMG). Unlike traditional anti‑malware solutions that rely on static signatures or generic behavior analysis, PMMG places the mobile user at the center of the security loop. Its core premise is that each user has a unique privacy tolerance and set of preferences regarding which application permissions are acceptable. By continuously collecting explicit user feedback on permission requests, PMMG builds a personal policy profile that evolves over time and is used to automatically allow, deny, or prompt for future requests.
The architecture consists of three main components. The Permission Monitor intercepts every runtime permission request on Android, compares it against a baseline policy (high‑risk permissions such as camera, microphone, and location are blocked by default), and forwards the request to the Feedback Engine. The Feedback Engine records the user’s decision together with contextual metadata (app identifier, permission type, timestamp, device state). This data is stored locally and optionally synchronized to a cloud profile for multi‑device consistency. The Policy Updater consumes the accumulated feedback and updates a probabilistic model—illustrated in the paper as a Bayesian network—that estimates the risk of each permission‑app pair. When the estimated risk exceeds a configurable threshold, the system either blocks the request outright or presents a concise risk‑aware prompt to the user.
To reduce the cognitive load on users, PMMG includes an “education mode” that displays brief explanations of why a permission is considered risky and typical usage scenarios. This aims to improve decision quality, especially for users with limited security knowledge. The authors also discuss a lightweight machine‑learning pipeline that can be executed on‑device with minimal overhead: each permission event incurs an estimated 5–10 ms of processing time, consumes roughly 2–3 MB of RAM, and adds less than 0.5 % of daily battery consumption. These figures are derived from theoretical modeling based on current smartphone hardware capabilities.
The paper’s performance analysis suggests that, even without a full signature‑based engine, PMMG can block more than 70 % of permission‑based malicious behaviors observed in a simulated dataset. However, the study lacks real‑world experiments on physical devices, and the reported results are based on synthetic workloads and assumed user behavior patterns. Consequently, the claimed detection rates should be interpreted as an upper bound rather than a definitive measurement.
In the discussion, the authors acknowledge several limitations. First, the system’s effectiveness hinges on the quantity and quality of user feedback; early adoption phases may suffer from high false‑positive or false‑negative rates. Second, users with low security literacy might make poor choices, inadvertently weakening their own protection. Third, PMMG focuses exclusively on permission misuse and does not address low‑level threats such as rootkits, code injection, or kernel‑level exploits, which require complementary detection mechanisms. The paper proposes integrating PMMG with existing anti‑malware suites to provide layered defense.
Overall, PMMG represents a shift toward user‑driven, personalized mobile security. By learning from individual preferences, it promises to tailor protection to each user’s privacy comfort level while maintaining acceptable performance on modern devices. Future work outlined by the authors includes (1) extensive field trials with real users to validate the feedback loop, (2) refinement of the UI/UX to minimize decision fatigue, (3) exploration of more sophisticated on‑device learning algorithms, and (4) seamless integration with system‑level threat detection. If these avenues are pursued, PMMG could become a practical complement to conventional mobile anti‑malware solutions, offering a balanced approach to privacy preservation and malware mitigation.
Comments & Academic Discussion
Loading comments...
Leave a Comment