Half-Duplex Active Eavesdropping in Fast Fading Channels: A Block-Markov Wyner Secrecy Encoding Scheme
In this paper we study the problem of half-duplex active eavesdropping in fast fading channels. The active eavesdropper is a more powerful adversary than the classical eavesdropper. It can choose between two functional modes: eavesdropping the transm…
Authors: : John Doe, Jane Smith, Michael Johnson
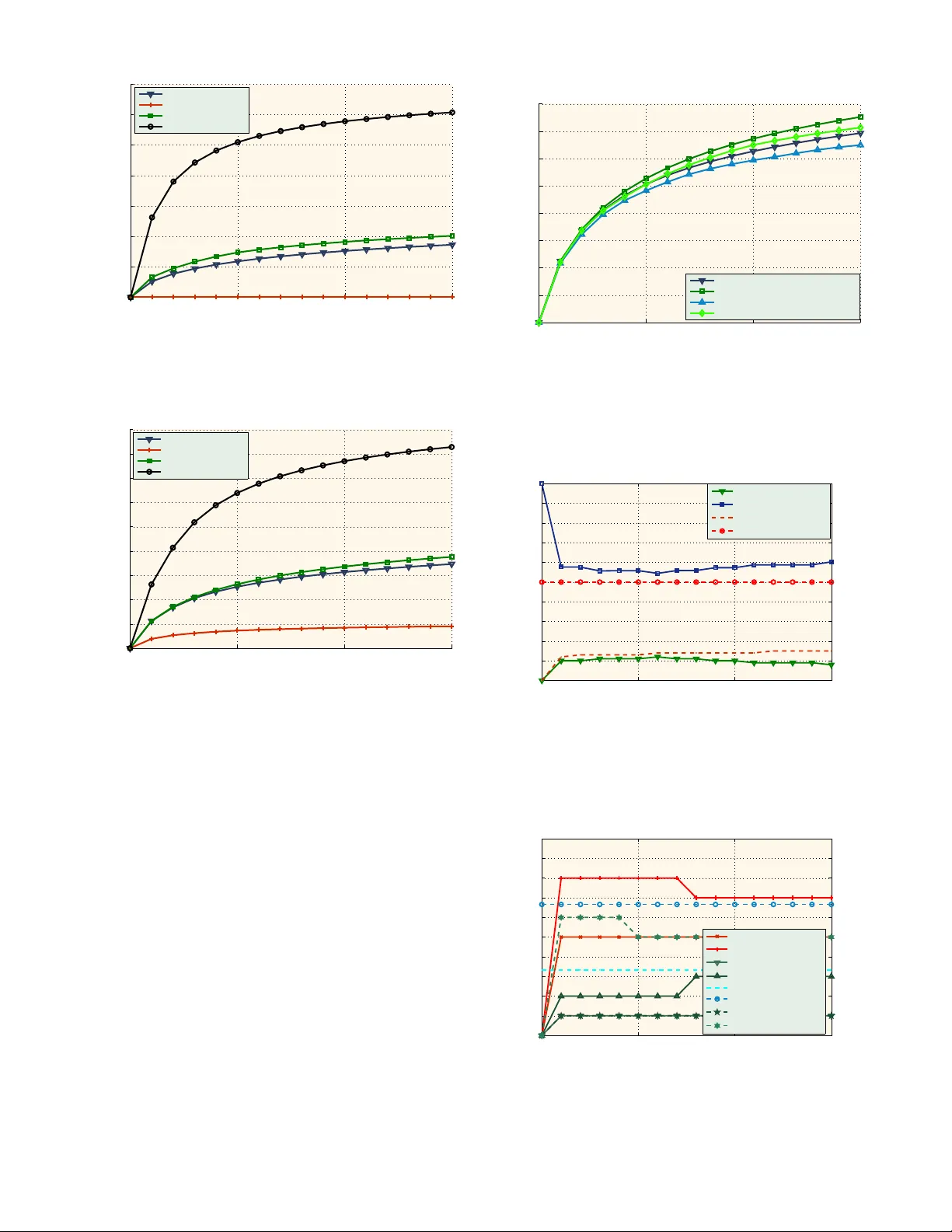
1 Half-Duple x Acti v e Ea v esdropp ing in Fast F ading Channels: A Block-Mark o v W yner Secrec y E ncoding Scheme George T . Ama riucai, Member IEEE, and Sh uangqing W ei, Member IEEE Abstract —In this paper we study the problem of half- duplex activ e eav esdropping in fast fading channels. The activ e ea vesdropper is a more po werful adversary than the classical ea vesdropper . It can choose between two functional modes: ea vesdropping the transmission b etween the legitimate parties (Ex mode), and jamming it (Jx mode) – the active ea vesdropper cannot function in full d uplex mode. W e consider a conserv ative scenario, when the active ea vesdr op per can choose i ts strategy based on the legitimate transmitter -receiv er pair’ s strategy – and th us th e transmitter and legitimate receiv er hav e to plan fo r the worst. W e show that con ventional physical-lay er secrec y approaches perform poorly (if at all), and we introduce a novel encoding scheme, b ased on very limited and unsecured feedback – the Block-Mark ov W yner (BMW) encoding scheme – wh ich outperfor ms any schemes cu rrently av ailable. Index T erms —Eav esdropper Channel, Secrec y Capacity , Bi- nary S ymmetric Ch annels, Feedback. I . I N T RO D U C T I O N A great nu mber of r ecent work s have b een f ueled by the still growing interest in p hysical lay er secrecy . Most of th em attempt to overco me the limitations of the c lassical wiretap- per/eavesdropper scenarios o f [1] or [2] ( namely th at no secret message can be successfully tran smitted if the eavesdropper’ s channel is less noisy than the legitimate receiv er’ s chan nel) by using some fo rm of diversity . The benefits of the ergodic- fading div ersity upon the achiev- able secrecy rates have b een exposed by works like [3], [4], [5] or [6]. A fast-fading eav esdropp er ch annel is studied in [3] under the assump tion th at the m ain ch annel is a fixed-SNR additive white Gau ssian n oise (A WGN) ch annel. Although the secrecy capacity for fast-fading eavesdropper chan nels is still unknown, [3] provid es achie vable secrecy rates and shows that sometimes noise injection at th e transmitter can imp rove these rates. The d ifferent ap proach of [4] m odels bo th the main and the eav esdroppe r chann els as ergodicly-fading A WGN chan nels. Howe ver, the fading is assumed to be slow enou gh to be considered co nstant f or infinitely long block s of transmitted symbols. The secrecy ca pacity is derived for th is mo del, an d the achiev ab ility part is p roved by using separate chann el encodin g for each o f the b locks. A similar appr oach is taken G. Amariuca i is with the Department of ECpE, Io wa State Uni versity . E- mail: gamari@ia s tate.e du. S. W ei is with the Department of E CE, Louisiana State Univ ersity . E-mail: swei@ece . lsu.edu. This paper was supported in part by the Board of Regents of Louisiana under grants LEQSF(2004-08)-RD-A-17. in [5] and [6], where the fading b roadcast chan nel with confidential me ssages (BCC) is co nsidered equiv alent to a parallel A WGN BCC. Howe ver, the slow fading ergodic c hannel mode l is quite restrictiv e. Althou gh the m odel can b e ar tificially c reated by a multiplexing/dem ultiplexing arch itecture as in [7], it still requires either coar se q uantization or lon g delay s (e .g. unde r fine q uantization, fo r a chan nel state with low prob ability it may take a very lar ge number of transmitted symbols to enable almost-erro r-free dec oding). W ith these consideratio ns, we focus in stead o n a more practical scenario wh ere both th e main and the eavesdropper ’ s channel a re affected by fast stationary fading. Howe ver, unlike [3], we are con cerned with a muc h strong er adversar y: a h alf- duplex active eavesdr o pper . In our ch annel model, dep icted in Figure 1, the eaves dropp er (Eve) has two o ptions: either to jam the co n versation b etween the legitimate tr ansmitter (Alice) and the legitimate rec ei ver (Bob) – Jx mo de – or to eavesdrop – Ex mode – (our eav esdroppe r canno t function in full d uplex m ode, i.e. she cannot transmit and rec ei ve o n the sam e fr equency slot, at the same time) . Both Alice and Eve (in Jx m ode) are constrained by average (over each co deword) power budgets P and J , respectively . Eve’ s purp ose is to minimize the secrecy rate achiev ab le by Alice, and to that extent she has to decide on the optimal alternation between the jamming mode and the eav esdroppin g mode. The state of each of the main and eavesdropper chan nels, i.e. the abso lute squar ed cha nnel coefficients (o r simply “th e channel coe fficients” hence f orth), which we d enote by h M and h W , respectively , are assumed to be available to the respective receivers. Howe ver, Bob does not know the exact state of Eve’ s channel, nor does Eve have any inform ation ab out Bob’ s channel, except its statistics. In addition to fading, each chan nel is furth er distor ted by an in depend ent add iti ve wh ite com plex Gau ssian no ise of variance σ 2 N . There exists a low-rate, unprotec ted (i.e. pub lic) feedback channe l b etween Bob and Alice. The p resent paper is limited to the following simplifyin g (althoug h not un common ) assumption s. i) Rayleigh fadin g: h M and h W are e xpone ntially dis- tributed, with parameter s λ M and λ W respectively . ii) The ch annel that links Eve (when in Jx mo de) and Bob is error free and d oes not experien ce fading [8], [9]. iii) Eve o nly uses white Gau ssian noise for jamming [10], [8], since this is the most har mful uncorrelated jamming strategy [11]. 2 Alice Bob Eve x M h W h M n W n y z w Fig. 1. Channel model iv) E ve’ s exact jam ming strategy (i.e. when and with what power she jams) is perfectly known to Bob (a posteriori) 1 so that Bob ca n employ coh erent d etection and commun icate Eve’ s strategy to Alice, via the low-rate feedbac k link . v) The instantaneou s state of the main cha nnel cann ot be known to the transmitter Alice non -causally . vi) The cod ew or ds are long enou gh such that n ot only the channel fading, b ut also the com bination of channel fluctuation and Eve’ s alternatio n between jammin g an d eavesdropping display ergodic proper ties over the duratio n of a cod ew o rd. vii) Eve employs an ergod ic strategy , i.e. she u ses the sam e statistics for alternating b etween Jx mo de and E x mo de for ev e ry co dew ord. viii) Eve has access to the exact value of h W only after she made her d ecision to eavesdrop (Ex mod e), an d h as no informa tion abou t the value(s) that h W might take while she is in Jx mode. This scena rio mod els a situation w here the training seq uences, which are tran smitted by Alice at a lo w rate, an d are u sed by Bob to estimate the ch annel co efficient before th e tra nsmission of a bloc k of symb ols, are protected against eavesdropping (for instance, b y u sing some fo rm of secrecy encodin g designed for non-co herent recep tion) o r are simply unknown to Eve. Therefo re, Eve cannot use the training sequences for estimating h W . Howe ver, if Eve’ s chann el is fading slowly en ough , E ve may be able to perfor m some form of blind chan nel estimation. Nevertheless, this kind of proced ure would require Eve to first listen to the inco ming signal for a longer time inter val, po ssibly a s long as h er channel co herence time. Un der these c ircumstances, Eve has to take the decision on whether to jam or eavesdrop in the absence of any non-cau sal channel state info rmation (i.e. random ly). Our contr ibutions can be stated as fo llows: • W e in troduce the con cept o f (half- duplex) a cti ve eaves- dropp er; • W e show that, u nder ou r con servati ve scena rio, W yner’ s scheme [1] p erform s poo rly (if at all); 1 T o estimat e exactly where Eve jams, one may argue that Bob needs the coheren ce time of the channel (which include s Eve’ s alternat ion between jam- ming and eavesdrop ping) to span seve ral channel uses. But since the jammer’ s hardwa re const ruction will most pro bably pre vent Eve from switchin g between Ex and Jx modes instan taneou sly , the coherence time of the jamming is not lik ely to pose any problems. On the other hand, the coherenc e time of the channe l coeffici ent h W can be assumed large enough to allo w for Bob’ s binary hypothesis testing (Ex or Jx) without bringing up any of the problems of [4], [5], [6], where the coherence time needs to be large enough to allo w hypothesi s testing (decodi ng) between a number of hypotheses (code words) which increase s exponentia lly with the code word length. • W e provid e a novel bloc k-Markov W yner (BMW) secrecy encodin g sch eme, which req uires a lo w-rate, un secured feedback link fr om Bob to Alice, a nd can im prove the secrecy rate significantly; • Our BMW sch eme employs a diversity of co ncepts, such a s a- posteriori W yner-type binn ing, block- Markov secrecy en coding an d encoding for a comp ound ch annel; • W e p rovide a secrecy-encoding method for multiple- access chan nels (M A Cs), where even if some o f the users are not d ecodable by the receiver , th ey can still help with the transmission o f secrecy . W e should note that ou r BMW scheme display s greater generality , an d is not limited to the present scenario. In fact, we are cur rently inves tigating its use in extending the concepts of physical-lay er secrecy to more realistic slowly-fading- channel models. I I . T H E C O N S E RV AT I V E S C E N A R I O A N D T H E A C H I E V A B L E S E C R E C Y R AT E S Physical-layer secrecy is synonymou s to W yner-type secrecy-encod ing sch emes [1]. The main id ea behind these schemes is to cre ate a special chan nel code, taylo red to exploit the physical d isadvantages o f Eve’ s c hannel. Alice and Bob agree on a certain binn ing s trategy , taylored to a certa in pair of on e main and o ne eavesdropper chann els. Nev e rtheless, Eve’ s actual chan nel qu ality remains unkn own. In fact, in most passi ve-eavesdropper scenarios, Eve herself remains undetec ted. Ther efore, the W yner-type sche mes are not influenc ed b y Eve’ s p osition, but b y the legitimate par ties’ perception about h er position. In our ac ti ve-e av esd ropper scen ario, Eve can a lternate be- tween jam ming and eav esdropp ing. Howev er, it is not this feature that turns out to be dev astatin g f or the transmission of secret messages, a s much as the legitimate pa rties’ un certainty about Eve’ s strategy . T o provide a stable f ramework for our in vestigation, we shall agree on the f ollowing notatio n and concepts. Thro ugho ut this paper, we shall d enote q = P r { E x mode } the prob ability that Eve is in Ex mode over a given frame. Note that unde r o ur assumptions, q uniquely determines Eve’ s strategy over a fr ame, and remains unkn own to Alice un til the end of the frame. Obviously , Eve’ s presence causes a modification o f th e channel statistics (as Alice and Bob see th em). For example , whenever Eve is eavesdroppin g (in Ex mode), the main channel in stantaneous SNR is h M P σ 2 N , while the SNR o f Eve’ s 3 channel is h W P σ 2 N – no modification here. Howe ver, when Eve is jam ming (in Jx mode), the ma in chann el instantaneou s SNR is h M P σ 2 N + J , where J is the instantaneo us jamm ing power sub ject to the constraint E J ≤ J , while the SNR of Eve’ s ch annel is zero (recall that whenever Eve jams, she cannot simultaneously listen on th e same fre quency slot). From Alice’ s and Bob ’ s perspective, the new eq uivalent channel coefficients c an be wr itten as g h M = ( h M if Ex m ode h M σ 2 N σ 2 N + J if Jx mode (1) and g h W = h W if Ex m ode 0 if Jx mode , (2) with the o bservation th at Alice and Bob still have to agree in advance on h ow lon g Eve should be considered in Ex m ode, and how lo ng she should be co nsidered in Jx mod e (i.e. on the value o f q ). This k ind of inf ormation will determ ine the encodin g strategy and the achievable secrecy rate. Denote by X the rand om variable at the inpu t o f the two channels, a nd by Y and Z the co rrespon ding random variables received b y Bob and Eve, respectively . Accor ding to [2 ], the secrecy capac ity of o ur mod el (un der the assumption that the equiv ale nt channel coefficients g H M and g H W become perf ectly known to Bob an d Eve d uring tran smission, and hence can be considered as o utputs of th e channel) is given by C s = max V → X → Y Z h I ( V ; Y , g H M ) − I ( V ; Z, g H W ) i ≥ ≥ max V → X → Y Z h I ( V ; Y | g H M ) − I ( V ; Z | g H W ) i , (3) where the maximization is over all jo int pr obability distribu- tions of V and X such th at V → X → Y Z f orm a M arkov chain. The inequality in (3) follows fro m th e indepen dence between V and H W , and holds with equa lity if V is also indepen dent of H M (i.e. Alice h as n o a-pr iori chan nel state informa tion – CSI). Since the op timal choice of V and X is presently unknown, we shall henceforth concentrate on the achievable secr ecy rate ( instead of secr ecy capacity) obtained by setting V = X and picking a complex Gau ssian distribution for X , with zero mean and variance P . Unde r these constrain ts, the achievable secrecy ra te (over a fr ame) becomes: R s = E g h M ,P " log(1 + g h M P σ 2 N ) # − − E ^ h W ,P " log(1 + g h W P σ 2 N ) # , (4) where P is th e instantaneou s tran smitter power and is subject to the co nstraint E P ≤ P . As we have mention ed earlier, a classical W y ner-type secrecy-encod ing scheme uses a cod ebook designed bef ore- hand, and taylor ed to the spec ific chan nel cond itions (assumed known in ad vance). If a codebo ok were designed f or a specific parameter q = q 0 , it would fail if Eve decided to use any different strategy . More p recisely , if Eve used q 1 > q 0 , the perfect secrecy of the message would be comprom ised (we call this secr ecy outage ), wh ile if Eve u sed q 2 < q 0 , the secret message would b ecome unintelligible to Bob (we call this intelligibility o utage ). As a result, the legitimate parties have to use a transmission strategy that can pro tect both the secrecy and th e intellig ibility of th e secret messag e, un der any strategy that Eve might use. This p roblem is be st mode led by th e con servati ve scenario that ma kes the assum ption that Eve knows Alice’ s strategy in advance. Results for the be st-case scenario (or the minimax scenario ), wher e Alice a nd Bob know Eve’ s strategy in advance, a re g i ven in [12]. Although th ose resu lts have less practical value, they can f unction as an upp er-bound for th e achiev ab le secrecy r ate, and will b e used fo r co mparison in the numer ical results section. The simplest encod ing scheme that offers secrecy protection in ou r conservativ e scenario is one of W yner typ e, with a forwarding rate low en ough to p rotect the me ssage again st the most powerful attempt to indu ce intelligibility outage (i.e. when Eve is in Jx mod e all the time), and with a secrecy rate low enoug h to offer protection again st the mo st powerful attempt to induce secre cy outag e (i.e. when Eve is in Ex mod e all th e time). The achievable secrecy rate fo r this k ind of scheme is R s,wc s = " E h M ,P, J h log(1 + h M P σ 2 N + J ) i − − E h W ,P h log(1 + h W P σ 2 N ) i # + (5) (the subscript “wcs” stand s f or “worst-ca se scen ario”), a nd is achieved under the equiv alent chan nel coefficients g h M = h M σ 2 N σ 2 N + J and g h W = h W . The following two propo sitions show that ran domizing the instan taneous power is no t a geed idea for eith er Alice ( P ) o r Eve ( J ). Pr oposition 1: When no chann el state in formation is av ail- able to the transmitter , the optimal transmitter strategy is to allocate constant p ower P = P to each symbol. Pr oof: Recall our assumption that both h M and h W are exponentially distributed, with para meters λ M and λ W , respectively . T his means that g h M is also expon entially dis- tributed, with parameter λ M (1 + J σ 2 N ) . Deno te the pr obability distribution of g h M by f M ( x ) = λ M e − λ M x , a nd of g h W = h W by f W ( x ) = λ W e − λ W x . If λ M (1 + J σ 2 N ) ≥ λ W (Eve’ s equivalent ch annel is statisti- cally “be tter”), then the ach iev able secrecy rate is zero. In this case the way Alice distributes her p ower (without k nowledge of the exact channel coefficients) is ir relev ant, and a con stant power allocation is as go od as any . Hence we shall concentr ate on the case when λ M (1 + J σ 2 N ) < λ W . W e need to prove th at f or this case, the fu nction R s,wc s ( P ) = E h M ,J log(1 + g h M P σ 2 N ) − − E h W log(1 + h W P σ 2 N ) (6) 4 x ) ( 1 x f ) ( 2 x f ) ( ) ( 2 1 x f x f − 0 x Fig. 2. Exponential distribut ions and their diffe rence. is a co ncave T function of P . W e can write R s,wc s ( P ) = Z ∞ 0 log(1 + xP σ 2 N )( f M ( x ) − f W ( x )) dx. (7) Note th at f M ( x ) − f W ( x ) is negative for x ∈ [0 , x 0 ) a nd positive for x ∈ [ x 0 , ∞ ) , where x 0 is the (uniqu e) solutio n of f M ( x ) = f W ( x ) . Moreover , R ∞ 0 f M ( x ) dx = R ∞ 0 f W ( x ) dx = 1 , which re sults in Z x 0 0 [ f W ( x ) − f M ( x )] dx = Z ∞ x 0 [ f M ( x ) − f W ( x )] dx. (8) A graph ical rep resentation of these functions is gi ven in Figure 2, whe re we used the notation f 1 = f M and f 2 = f W . T ake an incr easing func tion G ( x ) . W e c an write Z x 0 0 G ( x )[ f W ( x ) − f M ( x )] dx ≤ ≤ Z x 0 0 G ( x 0 )[ f W ( x ) − f M ( x )] dx = = Z ∞ x 0 G ( x 0 )[ f M ( x ) − f W ( x )] dx ≤ ≤ Z ∞ x 0 G ( x )[ f M ( x ) − f W ( x )] dx. (9) Now , taking G ( x ) = log(1 + xP σ 2 N ) we see th at R s,wc s ( P ) is a positiv e fun ction o f P ; tak ing G ( x ) = dF ( P ) dP = x σ 2 N + xP we see R s,wc s ( P ) is inc reasing; and taking G ( x ) = d 2 F ( P ) dP 2 = − x σ 2 N + xP 2 we see th at R s,wc s ( P ) is c oncave. Pr oposition 2: When in jamming (Jx ) mod e, Eve’ s optim al strategy is to use the same jamm ing power J = J 1 − q across all chan nel realiza tions in volved. Pr oof: T he result f ollows directly f rom (5), wher e only the first term depen ds on J , and that term is a c on vex function of J . As a result, the achievable worst-case- scenario secrecy rate is now simp ly R s,wc s = " E h M h log(1 + h M P σ 2 N + J 1 − q ) i − − E h W h log(1 + h W P σ 2 N ) i # + (10) and is rar ely strictly po siti ve (if a nd only if λ W > λ M (1 + J σ 2 N ) ). For a large jamming -power -to-noise r atio J /σ 2 N , this implies that Eve’ s p hysical chan nel needs to be im practically worse th an Bob’ s. Howe ver, the above scheme does not take full ad vantage of the model character istics. Recall the origina l assumption that Eve can f unction on ly as a half-d uplex termin al. Theref ore, whenever Eve is in Jx m ode, sh e cannot eaves drop – so the whole transmission remain s perfectly secret to Eve – and conv e rsely , if she is in Ex mo de, Eve can not simultan eously jam the tr ansmission. In the next section we develop an altern ativ e tr ansmission scheme, which g reatly imp roves th e achievable secrecy rate, and is tun ed to spec ifically exp loit th e active eavesdropper’ s limitations. More specifically , we “qu antize” the in terval [0 , 1] to which Eve’ s strategy q belongs into sev e ral sm aller inter- vals, and we desig n an encodin g/decodin g strategy such th at the worst-case scenario outlined above is only app lied on one of these sub-inter vals. Th e finer the resolution , the smaller the lo ss of secrecy rate du e to the u ncertainty abo ut Eve’ s strategy . T o m ake this e ncoding strategy work , we use th e following tech niques: (i) a poster iori W yne r-type binning, (ii) secret ke y genera tion, (iii) block -Markov secr ecy en coding and (iv) enco ding fo r a com pound ch annel. I I I . T H E B L O C K - M A R K OV W Y N E R ( B M W ) E N C O D I N G S C H E M E There are two main r easons why W yne r’ s sche me [1] do es not work in our model. First, Alice do es not know the statistics of Bob’ s chan nel in advance – Eve h as con trol over the signal- to-noise ratio of th is chann el. Th erefore, the m ain ch annel can be m odeled as a co mpoun d channe l. In order to r eliably transmit a message to Bob, Alice shou ld u se a special k ind of enco ding. It was shown in [13] th at the s ame lay ered encodin g techn ique that achieves the p oints on the bound ary of the capacity region for bro adcast chann els can also be used for transmission over co mpoun d chan nels. Ou r scheme uses the broad cast la yered encodin g of [13] to ensure that re liable transmission is po ssible betwee n Alice and Bob even in the most unfav o rable co nditions. Howe ver, even if such a sch eme is used, Alice ca nnot know in ad vance which messag es will actually be de codable by Bob. The second r eason is th at Alice does not know the statistics of Eve’ s channel in advance – due to th e a lternation between jamming and eav esd roppin g, Eve’ s equiv alen t chan nel is actu- ally weaker than her ph ysical channel. There fore, Alice cann ot directly transmit a secret m essage at a rate larger than R s,wc s in (10), be cause she is no t sure wheth er th e secrecy would be compro mised or no t. 5 W e solve these two problem s by introdu cing a posterior- binning W y ner-type encod ing scheme. Instead of transmitting a secr et m essage by W yner ’ s scheme, we ch oose to transmit white noise, an d agree on a secret key at the end of tran smis- sion, once the chann el quality becomes a vailable (a po steriori). The secret key is then u sed over the next tran smission interval, to encr ypt a secre t message, which is then transmitted a t the same time with another sequen ce of white noise from which a new secret key is distilled, and so o n. Ou r approac h is a seque ntial on e, and re quires that Bob sh ould be a cti vely in volved in th e secrecy en coding pro cess. Bob’ s inv o lvement consists of e stimating and f eeding back to Alice the exact value of Eve’ s strategy q . The detailed descrip tion is g iv en below . Howe ver , befor e we g et to that, we need to pr esent some con siderations on W yner’ s orig inal encoding scheme [1], which will help build some intuition regardin g the princ iple of our own scheme. A. An alternative to W yner’s secrecy encodin g scheme for r egular pa ssive-eavesdr op per channels: a posteriori binning W e begin this discussion b y study ing a scenario whe re, before the tr ansmission takes place, Alice and Bob alread y share a secret key (p erhaps on e that was agreed up on after the p revious tran smission). Then in addition to the secre t message that can be encode d by W yner’ s scheme , ano ther secret message can be tran smitted over the channel. This latter message is encryp ted using the secret key . W e pr ovide two enco ding schem es that ca n b oth ac hiev e the simultaneo us transmission of th e two secret m essages. Denote the capa cities of the ch annels from Alice to Bo b and from Alice to Eve by C M and C E , respectively , the ach ie vable secrecy rate (und er W yner ’ s o riginal scheme) by R k , the ra te of th e encry pted message by R s and the codeword leng th by N . Scheme 1: W yner’ s scheme with an en crypted message . Alice bins the c odeboo k (containin g 2 N C M codewords) into 2 N R k “super-bins”, such th at R k ≤ C M − C E . T he first secret me ssage picks the index of a supe r-bin. The super-bin is then b inned again into 2 N ( C M − R s − R k ) bins (ea ch con taining 2 N R s bin-words). On e of the b ins is picked r andomly , wh ile a specific codeword in that bin is picked acco rding to the encryp ted message. Scheme 2: The alternative e ncoding scheme . T he codeboo k is random ly binn ed into 2 N ( C M − R s ) bins – let us den ote these as “ pre-bin s”. Each pre-bin co nsists of 2 N R s bin-words. The bins are then ra ndomly group ed into 2 N R k “super-bins”, such tha t each supe r-bin co nsists of 2 N ( C M − R s − R k ) bins, an d where R k is picked to satisfy R k ≤ C M − C E . The first secret message picks t he index of a super-bin. A bin inside that super- bin is rando mly picked, an d th e transmitted cod ew o rd is then picked by the en crypted message in side this bin. The two schemes ar e e quiv alen t, and they are described in Figure 3. Howe ver, as we sh all see shor tly , the applicab ility of Scheme 2 is more relevant to our compo und channe l scenario. W e should recall h ere that W yner’ s o riginal enc oding scheme [1] inv o lves a random binning of the codebo ok into bins which are, each of them, good cod es for Eve’ s channel. Wyner’s secrecy encoding scheme with an encrypted message Alternative encoding scheme for binning at the end of the frame ) ( 2 K S M R R C N − − S NR 2 b in - words bins ) ( 2 K M R C N − K NR 2 S uper - bins M NC 2 S uper - bins K NR 2 ) ( 2 K S M R R C N − − bins ) ( 2 S M R C N − M NC 2 S NR 2 b in - words Fig. 3. Alterna ti ve binning: W yner’ s secre cy encoding scheme with an additi onal encrypted m essage, and the basis of our block-Mark ov W yner encodin g scheme. The actual transmission does not contain any infor mation about th e binning itself. Hence, th e same “ random ” b inning needs to be done separate ly at Alice (befor e the tran smission takes place ) and at Bob (be fore he can begin decodin g). The reason why Alice per forms the binning of th e codebo ok before transmitting is beca use she ne eds to send a mean ingful secret message over the com ing frame. T herefor e, the tran smitted codeword n eeds to belon g to the p articular bin indexed by th e secret message. This suggests that if the “secret message” transmitted b y Alice had no meaning (i.e. if Alice picked this me ssage in a ran dom fashion), both Alice and Bob could p erform the binning of the codeb ook af ter the transmission ends. The “secret message” genera ted th is way could be th ought of as a secr et key for en crypting a meaning ful message over the n ext shared fram e. Suppose that Eve’ s ch annel is unknown to Alice an d Bob until the transm ission of th e current codeword ends. The first transmitted codeword is rando mly selected fro m the who le un- binned cod ebook. Af ter the transmission ends, Alice and Bob realize that the secr ecy capacity was R s . Both Bob and Alice can now proce ed to the (same) binnin g of the codeb ook. As a result, th e same single bin will b e iden tified by bo th legitimate parties as containing the transmitted message, and its index will b e secret to Eve. Clear ly , the secret message conv eyed by the index o f this bin has n o meanin g. Nevertheless, it can be u sed over the next fr ame, as a secr et key . Over the second frame, Alice and Bo b use S cheme 2 ab ove. The codeb ook is random ly binne d be fore transmission, into 2 N ( C M − R s ) bins th at could each be r egarded as a co de f or carrying th e encryp ted message. On e of th e bin s will be selected rando mly , and the encr ypted message will select th e exact codeword to be transmitted. Th is meth od of transmission ensures that th e encryp ted message does n ot overlap with the secret key th at needs to be generated at the end of the fr ame – the en crypted message has noth ing to do with how th e bins are ultima tely chosen, as seen in Figure 3. The en crypted message may be decoda ble, but not decryptab le by Eve. After the transmission of the seco nd fra me takes place, Alice and Bob realize that the secrecy c apacity was R k . T he ind ices of th e bins are “rando mly” grou ped by both Alice and Bob into 2 N R k super- 6 bins , and a n ew secret key is agreed upo n b y the legitimate parties. The p rotocol continu es in the same m anner . Three observations are in or der . First, the secret key ( de- cided up on at the end of the frame) and the encry pted message (carried by the fr ame) c annot overlap and m aintain th e same equiv o cation at Eve – see the one-time pa d [14]. Hence, in the above description of the pro tocol, it is requir ed that R s + R k ≤ C M . Second, no te that R s = R k (since the key is used as a one-time pad to en crypt the secret m essage of the next f rame), ther efore, if ou r previous con dition holds in the form R s < C M / 2 , the tran smission of the meanin gful secret message c an b e done at almost the secr ecy capac ity , with a small in itial penalty (du e to the fact that the first f rame d oes not carry an encr ypted message) which bec omes negligible as the nu mber o f transmitted frame s in creases. 2 Third, o ur new p rotocol can be u sed whenever Alice d oes not have a good descrip tion of Eve’ s chan nel over a fram e until the transmission of the cor respondin g co dew ord ends, which is precisely the case with o ur curre nt mo del. B. Deta iled description of th e BMW en coding scheme At this po int, we restrict our an alysis to particular frame (we sh all d enote th e span of a codeword by “ frame”). How Eve shou ld deal with d ifferent f rames w ill b e discu ssed in Theorem 5. Over this frame, we assum e that Eve chooses an arbitrary strategy q = P r { Ex m ode } . Once the transm ission of the co dew o rd is fin ished, Bob can accur ately ev aluate the parameter q . Bob c an then feed this value back to Alice . No te that the k nowledge of q provide s Alice with the statistical description o f both the main channe l – determined by the jamming probab ility (1 − q ) – and the eav esdroppe r’ s ch annel – determined by th e ea vesdroppin g probability q . Before learning Eve’ s strategy , the ch annel between Alice a nd Bob appears like a comp ound channel to the legitimate par ties. The p ossible states of this ch annel are given by the possible values of Eve’ s strategy q , which b elongs to the interval [0 , 1] . T o transfo rm this un countable set of po ssible cha nnel states into a finite set, we divide the interval [0 , 1] to which q belon gs into n sub intervals such th at [0 , 1] = [ q 0 , q 1 ) ∪ [ q 1 , q 2 ) . . . ∪ [ q n − 1 , q n ] (11) where q 0 = 0 and q n = 1 . For conve y ing a message to Bob , Alice uses an n -level broadc ast-channel-ty pe code book, as in [13]. Level i is al- located p ower (1 − α i ) α i − 1 . . . α 1 P (with α j ∈ [0 , 1] ∀ j = 1 , . . . , n − 1 and α n = 0 ) and is desig ned to deal with a jammer which is on with prob ability 1 − q i − 1 over each cha nnel u se. Also n ote that q 0 < q 1 < . . . < q n . I n the rem ainder of this 2 Assume that Eve ’ s channel condition s are a lways the same. As an e xample, consider a codebo ok with 10000 code words, which is used for transmitting a secret message of length log(50) bits, according to our protocol. T ake any random frame. For transmitting the encrypted m essage, the codebook is binned into 200 bins, each containing 50 code words. One of the bins is pic ked randomly , and the encrypt ed message picks one of the 50 code words in the bin. After the transmission ta kes plac e, Alice and Bob both group the original 200 bins into 50 “super-bins” (eac h conta ining 4 original bins), using th e same “recip e”. The secret k ey is the inde x of the super-b in to which the transmit ted code word belongs. Note that the actual code word that was transmitted inside this super -bin is picked indepe ndently of the choic e of the super-bin. paper, we sh all say that level i is “strong er” than level j if i < j , i.e. if level i can dea l with a jamm er which is on mo re often. The no tation is fu lly justified by Lemma 3 b elow . Denote the ra tes of the different encod ing lev els as: R 1 = E h M h log 1 + (1 − α 1 ) P h M σ 2 N + α 1 P h M + J i (12) for the strongest level, which can deal with the case when E ve is always in Jx mode, i.e. q = q 0 = 0 , R i = E h M " q i − 1 log 1 + + (1 − α i ) α i − 1 . . . α 1 P h M σ 2 N + α i . . . α 1 P h M + (1 − q i − 1 ) log 1 + + (1 − α i ) α i − 1 . . . α 1 P h M σ 2 N + α i . . . α 1 P h M + J 1 − q i − 1 # , (13) for i = 2 , 3 . . . n − 1 , and fin ally R n = E h M " q n − 1 log 1 + α n − 1 . . . α 1 P h M σ 2 N ! + +(1 − q n − 1 ) log 1 + α n − 1 . . . α 1 P h M σ 2 N + J 1 − q n − 1 !# , (14) for the weakest level, co rrespond ing to the case whe n Eve is in Jx m ode with pr obability 1 − q n − 1 . Note th at the en coding lev els ar e d esigned such that Bob d ecodes the stro nger lev els first, and tre ats the re maining un-d ecoded messages as white noise. The codeboo k for level i contains 2 N R i codewords of len gth N , gen erated such th at each co mpone nt of each codeword represen ts an in depend ent realization of a Gaussian random v ariab le of mean 0 and variance (1 − α i ) α i − 1 . . . α 1 P , where α n = 0 for co mpatibility . Also n ote that ou r scheme uses a constant transmit power P = P ov er the who le frame. Althou gh rand omizing the transmit power may sometimes improve the achiev a ble secrecy rate, this study is beyond the scope of o ur paper . Howev e r , w e already kn ow that Eve’ s op timal strategy is to u se a constan t jamming po wer J on all jamm ed channel u ses. T his is because all the r ates R 1 , . . . , R n defined ab ove are convex function s of J (see Propo sition 2) . The relative strength of the encodin g lev els is established by the fo llowing lemma. Lemma 3: If Eve u ses a parame ter q ∈ [ q i − 1 , q i ) over a frame, then the messages enco ded in levels 1 , 2 , . . . , i are in- telligible by Bob at the end of the fr ame. Th us the forwarding rate from Alice to Bob is R M ,i = R 1 + R 2 + . . . + R i . Pr oof: I n orde r to prove that the en coding lev e ls with lower indices are stronger in the sense that they can deal with a worse jamming situation, it is eno ugh to show that R i as defined in (13) is an in creasing fu nction of q . In other words, encodin g level i , transmitting at a rate R i , is intellig ible by Bob whenever Eve is in jamming mod e with a pr obability less than (1 − q i − 1 ) . But this is a direct co nsequen ce of Le mma 7 in Ap pendix A, if we simply r eplace x by (1 − α i ) α i − 1 ...α 1 P h M σ 2 N + α i ...α 1 P h M and y by J σ 2 N + α i ...α 1 P h M (see App endix A). 7 Consider the first fra me, f or which th e transmitted me s- sage car ries no useful informatio n, but ra ther its symbols are selected in a rand om, i.i.d. fashion . Once Alice receives the feedbac k sequ ence f rom Bob at the end of the frame, describing Eve’ s strategy (i.e. th e value of q – actually , as we shall see shortly , only the interval [ q i − 1 , q i ) that contains q is enoug h info rmation for Alice, thu s the length of th e feed back sequence need n ot be larger than log( n ) ) , Alice and Bo b can separately agree on the same secret message, as describ ed in the proto col above. This message will f unction as a secret key f or encry pting a meanin gful secr et message over th e next frame. In turn , the secret message ag reed upon at the en d of the seco nd fram e can function as a secret key for the third frame, and so on. T o form alize the intu iti ve descriptio n above, we begin by stating sev eral definition s: • The “enc rypted message” is a meaning ful s ecret message, encryp ted with th e help of a secret key that was generated in the p revious frame. • The “secret key” is a meanin gless rando m message, which is pe rfectly secret to Eve, is agreed upon by bo th Alice and Bob at the end of the fr ame, and can be used for the encr yption o f a secret message (of a t m ost the same leng th) over the next frame. • The term “secret key rate” r efers to the rate at which a secret key is gene rated at the e nd of a frame – the correspo ndent of W y ner’ s “secrecy capacity”. • The term “achiev able secrecy rate” refer s to the rate of transmission of th e encryp ted message . Our encod ing scheme works as follows. First, the n cod e- books, indexed by i , with i ∈ { 1 , 2 , . . . , n } are gen erated as described above, and are made av ailab le to all parties. O n a giv en f rame, Alice tr ansmits an encry pted message, at a rate R s ≤ 0 . 5 R 1 (15) (this co nstraint is a result of planning ah ead for Eve’ s most destructive b ehavior , an d we show in The orem 5 be low that it does no t incu r any lo ss of perf ormance u nder Eve’ s o ptimal strategy) – note th at the en crypted me ssage is encr ypted with the help of a secret key generated over a previous fram e. T o transmit the encry pted message, Alice rando mly b ins code- book 1 into 2 N ( R 1 − R s ) bins. On e of the bins (each contain ing 2 N R s codewords) will be picked ran domly (unifor mly), and the encry pted me ssage will pick a co dew ord f rom th is bin for transmission. Recall that the reason why Alice canno t directly bin the codeb ook for g enerating th e secret key is because Eve’ s strategy (hence her equ iv alent ch annel) is unknown until the end of the f rame. An additional n − 1 co dew o rds are also chosen r andomly , one fr om each of the r emaining n − 1 cod ebooks of ra tes R 2 , R 3 , . . . , R n . Alice’ s transmitted sequence is the sum o f the n c odewords. At th e end of the frame , Bob f eeds bac k to Alice the exact value of Eve’ s strategy q over that frame. In or der to agr ee on a secret key , Alice an d Bob first need to know which e ncoding lev els are decod able b y Bob , and which are deco dable by Eve. Only the inform ation e ncoded in those levels that are decodab le by Bob, but ar e no t p erfectly decodab le by Eve, can contribute to the g eneration of the secret key . Due to the construc tion of the co de ( see Lemma 3), it is clear t hat under an y jamming/ eavesdropping strategy , Bob will be able to de code the strongest level first, treating the oth er lev els a s wh ite no ise, and then perfor m successi ve interfere nce cancellation to decod e inc reasingly weaker le vels. Howe ver , the same statemen t c annot be mad e fo r Eve. Eve’ s chan nel is quite different from Bob’ s. While the co de is designe d to handle Bob’ s unk nown-length interf erence channe l, Eve sees an interference-f ree chann el that is totally interrupted (1 − q ) of the time. In th e gen eral case, it is thu s possible that the o rder of stren gth o f the encod ing levels, fro m Eve’ s perspective, is not the same as tha t from Bob’ s per spectiv e. For example, for a cod e with 7 levels Bob migh t be ab le to decod e only lev els 1 , 2 , 3 , 4 , while Eve-A may be able to perfec tly deco de only lev els 1 , 4 , 6 , 7 . In this case, we ca n re-o rder the levels from Eve-A ’ s per spectiv e, a s 1 , 4 , 6 , 7 , 2 , 3 , 5 . The first fo ur lev els are decod able by Eve-A perfectly , the next two are decod able by Bob, but no t by Eve-A , and the last level is deco dable by neither . Only levels 2 an d 3 can be used for g enerating the secret key . For the g eneral case, we shall den ote the order ed set o f indices corresp onding to the en coding levels specified by th eir rates in (12)-(1 4) by I , an d th e set of ind ices co rrespon ding to the ord er of stren gth o f th e encodin g levels from Eve’ s perspective b y c I . Th ere exists a bijection (i.e. a re -orderin g) B : I → c I , d efined as f ollows: (1 ) th e set o f indices (in arbitrary o rder) co rrespond ing to levels that are perfec tly decodab le by Eve is de noted I e ; (2) the set of indices (in arbitrary o rder) corre sponding to levels that ar e not perfe ctly decodab le b y Eve, but p erfectly decod able by Bob is deno ted I k ; (3) the set of indices (in arbitr ary o rder) co rrespond ing to lev els that ar e n ot perfectly deco dable by either Eve or Bo b is deno ted I n ; ( 4) th e ord ered set c I is defined as c I = { I e , I k , I n } . (16) Furthermo re, we d efine I ne = { I k , I n } as th e set of indices correspo nding to encod ing le vels which ar e not perfectly decodab le by Eve. T he method o f en coding is describ ed in Figure 4. Theorem 4 below provides the achievable secret key rate for the gene ral case. Theor e m 4 : Con sider a given quantization { q i | i ∈ c I } o f the interval [0 , 1] , and a given power allocation between the correspo nding encoding levels { α i | i ∈ c I } . Supp ose that Eve picks a strate g y q ∈ [ q i − 1 , q i ) over a frame. Then the fo llowing secret key r ate is ach iev able over that f rame ( where th e key is generated at the end of the fr ame): R k,i = X j ∈ I k [ R j − R E ,j ] , (17) where: • R j are defined a s in (12)-( 14) for j = 1 , 2 , . . . , n , • R E ,j , j ∈ I ne are selected such th at they satisfy th e following set o f conditio ns: R E , 1 ≥ 0 . 5 R 1 if 1 ∈ I ne , (18) (this con dition states tha t th e secret key rate assigned to the first encoding level should not exceed 0 . 5 R 1 , because 8 Supe r-bin s 1 , 2 K NR ) ( 1 , 1 2 K S R R R N − − bins ) ( 1 2 S R R N − S NR 2 Encry pted mes sa ge 1 2 NR 2 , 2 K NR ) ( 2 , 2 2 K R R N − 2 2 NR i K NR , 2 ) ( , 2 i K i R R N − j NR 2 S NR 2 Bef ore tran sm i ssi on Af ter tr a n sm i ssi on Se cr e t ke y Bin-words Level 1 Level 2 Level j T h e si ze of th e secret key can n ot be la rger th an ) 5 . 0 ( 1 2 R N Fig. 4. BMW encoding method – most general case, when 1 ∈ I ne . otherwise Eve mig ht cho ose q = q 1 , and the ach iev able secrecy rate could n ot exceed R 1 − R k – see The orem 5) R E ,l ≤ R l ∀ l ∈ I ne (19) (this con dition ensu res the feasib ility of encod ing), X l ∈ S R E ,l ≤ q E h W h log 1 + + P l ∈ S (1 − α l ) α l − 1 . . . α 1 P h W σ 2 N i − ǫ, (20) for any subset S o f I ne , and X l ∈ I ne R E ,l = q E h W h log 1 + + P l ∈ I ne (1 − α l ) α l − 1 . . . α 1 P h W σ 2 N i − ǫ, (21) with ǫ positi ve and arbitrarily close to zero (the latter two condition s ensure th e secrecy of the key). The expr essions in (2 0) an d (2 1) use th e convention α n = 0 . Note that the bijectio n B defined above a lso d epends on Eve’ s strategy q , and hence on the interval i to which q b elongs. Therefo re, the set of ind ices I k depend s o n i . The following o bservations are in ord er . (1) Som etimes (when Eve’ s chann el is mu ch worse than Bob’ s) the system o f ineq ualities in (1 8) - (21) may hav e no feasible solu tion. Un der these circu mstances, one possible approa ch is to find a solution of the inequ alities in (19) - (21) ( i.e. to ig nore the condition in (1 8)). This would distill a secret key at a rate larger than 0 . 5 R 1 . Nevertheless, the entire secret key may be used by time sh aring. For examp le, for I ne = { 1 } , we ca n take R E , 1 = 0 . 25 R 1 for two co nsecutive frames (th e first lev el would generate 2 × 0 . 75 N R 1 = 1 . 5 N R 1 secret key bits, and transmit only 2 × 0 . 25 N R 1 = 0 . 5 N R 1 bits o f th e secr et m essage), fo r the third fram e we can use th e entire level 1 (at rate R 1 ) to transmit an encr ypted message (of length 1 . 5 N R 1 − 0 . 5 N R 1 = N R 1 bits). W ith this o bservation, in the rem ainder of this work we shall only f ocus on the cases in which (18) - ( 21) admit feasible solu tions. (2) Since th e f undame ntals o f ou r app roach to the proo f of this theo rem r eside in W yner ’ s o riginal results [1], we are currently c onstrained to in volving all u sers in I ne in the generation of the secret key . That is, we are subject to the constraint in (2 1), a nd its essentiality w ill be reflected in th e proof . Altho ugh a larger secrecy rate might be achieved by in volving only a prope r subset of I ne in the generation of the secret key , this kind of improvement is beyond the purp ose of this pape r , and will be consid ered f or furth er re search. (3) Altho ugh similar-fla vor resu lts hav e been o btained in [15], [16], our results are q uite different because they in volve “users” which are no t d ecodable b y Bob. A discu ssion of the issues addre ssed in [15], [16] is provid ed in Ap pendix B. Pr oof: The pro of is based on two observations. First, we have already sh own th at if the secret message is not a meaningf ul on e, the binn ing of W yner ’ s scheme can b e done at the end of the transmission, when the statistical properties of Eve’ s ch annel are known to both Bob and ( throug h feed back) to Alice. T o ac complish th is, b oth Alice an d Bob will h av e to mem orize a set of “ binning recip es”, one fo r each possible value of E ve’ s strategy (actually only the interval [ q i − 1 , q i ) to which q b elongs, and no t the exact value of q , matters in o ur case). This is a bit different from W yner ’ s o riginal scheme [1] wh ere on ly on e such recipe n eeded to be memor ized. Therefo re, in the rem ainder of the proo f, we can and shall treat the p rocess of distilling a secre t key as if Eve’ s chan nel were known to all parties in ad vance, without losing any generality . That is, fo r the sake of u sing familiar notation an d terminolo gy , we shall talk about “enco ding” a secret key at Alice, for “transm ission” to Bo b, alth ough the secret key is only agreed u pon at the en d of the frame. Second, a secret key K = S j ∈ I ne K j is “en coded” into a ll encodin g levels j belo nging to I ne , i. e. over levels belong ing to both I k and I n . Recall that Bob can not decode the lev els of I n . W e do this because it is easier to pr ove that th e whole key K is secret to Eve. On ce this is accomp lished, we shall follow a simple argumen t o f [15] ( which w e r eplicate in (33) for completen ess) to show that the sub-key S j ∈ I k K j , which can actually be decoded an d used b y Bob, is also p erfectly 9 secret. W e use a separate secre t key en coding f or each o f Alice’ s encodin g levels in I ne . As a conseq uence, Eve sees a fast fading m ultiple access channel, wh ere the transmitters h av e different power constraints, but the same chann el coefficient. In this context, we note that the cond itions set forth for the rates R j,E in (20) and (21 ) are exactly the con ditions necessary for these r ates to b elong to the bound ary of the capacity region of Eve’ s eq uiv alent m ultiple access c hannel. Th e pro blem of a multiple access eavesdropper A WGN channel was discussed in [15]. Howe ver, som e of the results in [15] do not necessarily reflect o ur v ie ws. W e p rovide an explanation of this assertion in Appen dix B. Th erefore , we con tinue with describing a correct encod ing meth od wh ich y ields an achievable secret key rate. For any level of encoding j ∈ I ne , we enco de a secret key K j accordin g to W yner’ s scheme [1], [17]. Tha t is, if j 6 = 1 , we randomly bin the randomly generated N - dimensiona l codeb ook of 2 N R j codewords into 2 N ( R j − R E ,j ) bins. T he secret m essage correspo nds to the in dex of the bin, while the exact co dew o rd in the b in is ra ndomly picked. The rates R E ,j are selected as in the statemen t of the theorem. If j = 1 ∈ I ne (recall that codebo ok 1 was already binned once), Bob generates the bin s in two steps: first he identifies the 2 N ( R 1 − R s ) bins used for tran smitting Alice’ s encryp ted message, and then he r andomly gr oups th ese bins into 2 N ( R 1 − R E , 1 ) larger bins. A secret message is encoded into the indices of the resulting larger bin s. Denote the resulting N -d imensional outp ut sequ ence of lev el j by X j , and denote the p -th com ponent of X j by X j ( p ) . Also d enote the unio n o f the N -seq uences fro m all lev els (inclu ding tho se fro m I e which do not carry a secret key) by X = S j ∈ b I X j . The no tation X ( p ) now d enotes the n - dimension al set consisting of the p -th com ponen ts of the ou tput sequences fr om every en coding lev e l, that is X ( p ) = S j ∈ b I X j ( p ) . Eve’ s received sequenc e is now Z = H W · P j ∈ b I X j + Q , wh ere H W is the N - dimensiona l vector of chan nel realizations correspon ding to th e N sym bols, Q is Eve’ s N -d imensional additi ve white Gaussian noise sequence , and ( · ) d enotes componen t-wise m ultiplication. The p -th scalar compon ents of these vectors will be de noted by Z ( p ) , H W ( p ) and Q ( p ) , respectively . The notation X S will be used for the union of the o utput sequences corresp onding to levels with indices in S , i. e. X S = S j ∈ S X j , and th e notation for the p -th comp onents is extended correspo ndingly . Eve’ s equiv o cation ab out the secret key can be written as follows ∆ = H ( K | Z , H W ) H ( K ) = H ( K , Z , H W ) − H ( Z , H W ) H ( K ) ( a ) = = H ( K ) + H ( Z , H W , X | K ) H ( K ) − − H ( X | Z , H W , K ) + H ( Z , H W ) H ( K ) ( b ) = = H ( K ) + H ( Z , H W | X , K ) + H ( X | K ) H ( K ) − − H ( X | Z , H W , K ) + H ( Z , H W ) H ( K ) ( c ) = = 1 − I ( X ; Z , H W ) − I ( X ; Z , H W | K ) H ( K ) , ( 22) where both ( a ) an d ( b ) result fro m th e chain ru le f or entro py , while (c ) from the fact th at K → X → Z form a Markov chain. Denote D = I ( X ; Z , H W ) − I ( X ; Z , H W | K ) . W e can now write I ( X ; Z , H W ) = H ( X I e ) + H ( X I ne ) − − H ( X I e | Z , H W ) − H ( X I ne | X I e , Z , H W ) , (23) H ( X | K ) = H ( X I e ) + H ( X I ne | K ) , (24) and H ( X | Z , H W , K ) = = H ( X I e | Z , H W , K ) + H ( X I ne | X I e , Z , H W , K ) ≤ ≤ H ( X I e | Z , H W ) + H ( X I ne | X I e , Z , H W , K ) , (2 5) where we u sed the fact tha t { X j : j ∈ I } are all indepe ndent of each o ther, and that con ditioning r educes en tropy . Substi- tuting (23)-(2 5) in th e expression o f D above, a nd notin g that H ( X I ne ) = H ( X I ne | X I e ) , we o btain D ≤ I ( X I ne ; Z , H W | X I e ) − H ( X I ne | K ) + + H ( X I ne | X I e , Z , H W , K ) . (26) By the cod e construction, and recalling that the rates R E ,j in the statement of the theor em are picked suc h that they belong to the bound ary of the ca pacity region of Eve’ s eq uiv alent multiple ac cess channel (they satisfy (2 1)), we can use Fano’ s inequality , the u nion boun d an d argumen ts similar to th ose used in d riving equation (78 ) of [1], to upper bo und H ( X I ne | X I e , Z , H W , K ) ≤ N δ N , (27) where δ N → 0 as N → ∞ . This is quite in tuitiv e , since g iv en the secret key , th e other inform ation is tran smitted by A lice using cod es which are good for Eve’ s multiple a ccess ch annel. In fact δ N = X j ∈ I ne 1 N h ( p e,j ) + p e,j R E ,j , (28) where p e,j is th e probab ility of err or for the layer- j such co de, and h ( · ) is the bin ary entropy function h ( x ) = − x log 2 ( x ) − 10 (1 − x ) log 2 (1 − x ) . Since the rando m, complem entary-to -the- secret-key infor mation is carried by these co des a t a total rate almost equal to the capacity of the virtual MAC between Alice and Eve, correspo nding to th e encoding levels in I ne , we also have H ( X I ne | K ) = N q E h W h log 1 + + P j ∈ I ne (1 − α j ) α j − 1 . . . α 1 P h W σ 2 N i − N ǫ . ( 29) T o upper bound the first term on the right hand side of (26), we write I ( X I ne ; Z , H W | X I e ) = = H ( Z , H W | X I e ) − H ( Z , H W | X I ) ( a ) = = H ( Z , H W | X I e ) − N H ( Z ( p ) , H W ( p ) | X I ( p )) ( b ) ≤ ≤ N H ( Z ( p ) , H W ( p ) | X I e ( p )) − − N H ( Z ( p ) , H W ( p ) | X I ( p )) = = N I ( X I ne ( p ); Z ( p ) , H W ( p ) | X I e ( p )) ( c ) ≤ ≤ N q E h W h log 1 + + P j ∈ I ne (1 − α j ) α j − 1 . . . α 1 P h W σ 2 N i . (30) Equality in ( a ) fo llows from the fact that the chann el is memory less, ( b ) follows from the chain r ule for entr opy and the fact th at conditio ning does not incre ase entropy , a nd ( c ) is obtained by using Jensen’ s ine quality , as in the pro of of the conv e rse to th e A WGN channel coding theorem in Section 9.2. of [18]. Putting togeth er (2 7), (29) an d (30), we obtain D ≤ N ( ǫ + δ N ) , (3 1) which in turn implies ∆ ≥ 1 − N ǫ + δ N H ( K ) . (32) Since H ( K ) N is a con stant, the right-han d side of (32) co n verges to 1 as N → ∞ . T hus, we have p roved th at the key K remains secret fro m Eve as long as the co dew o rd leng th N goes to infinity . Howe ver , no te th at the entire key K canno t be unde rstood by Bob . In fact, Bob and Alice can o nly agree on th e par t K I k of th e key . But the secre cy of the en tire key guaran tees the secrecy of any part o f the key [15]. For the sake of comp leteness, we restate the f ollowing pro of f rom [15]. H ( K I k | Z , H W ) ( a ) = = H ( K I ne | Z , H W ) − H ( K I n | K I k , Z , H W ) ( b ) ≥ ≥ H ( K ) − N ( ǫ + δ N ) − − H ( K I n | K I k , Z , H W ) ( c ) ≥ ≥ H ( K I k ) + H ( K I n ) − N ( ǫ + δ N ) − − H ( K I n | K I k , Z , H W ) ( d ) ≥ ≥ H ( K I k ) − N ( ǫ + δ N ) , (33) where ( a ) fo llows from th e chain r ule, ( b ) fr om ( 32) and the definition o f ∆ , ( c ) fr om the indep endence of the keys from different encodin g levels, a nd ( d ) from the fact that condition ing doe s no t increase entro py . This results in H ( K I k | Z , H W ) H ( K I k ) ≥ 1 − N ǫ + δ N H ( K I k ) → 1 (34) as N → ∞ ( because H ( K I k ) N is a constan t). The refore, a per- fectly secret key can be d istilled from th e r andom infor mation transmitted by the encod ing levels in I k . W e have seen the b est achievable secret key rate if q ∈ [ q i − 1 , q i ) . Th e next th eorem pr ovides Eve’ s optim al strategy , i.e. which is the most destructive value o f q un der th e present conservati ve scenario, and also Alice ’ s best ach iev able secrecy rate under this eavesdropper strategy . Note that a lthough th e game b etween Eve a nd the legitimate p arties A lice and Bob is a dy namic on e, where Bob and Alice need to re -ev aluate their strategies over each fr ame, the f ollowing result c an be though t of as some form of equilibriu m. Ind eed, un der o ur assumptions, it is sub- optimal for either Eve or the Alice/Bob pair to deviate from th e following strategies. Theor e m 5 : Con sider a given quantization { q i | i ∈ c I } o f the interval [0 , 1] , and a given power allocation between the correspo nding encod ing levels { α i | i ∈ c I } . (1) I f Eve’ s op timal value of q is such th at q ∈ [ q i − 1 , q i ) , then q is arbitra rily close to q i . (2) Eve’ s optimal strategy q und er our conservati ve scenario is the sam e over all frames. (3) Denote the achievable secre t key r ates by { R k,i : i = 1 , 2 , . . . , n } , wher e R k,i is th e best achiev ab le secret key rate giv en by The orem 4, under q = q i . Th en Eve’ s optimal strategy is q i opt = arg min q i { R k,i } , if min q i { R k,i } < 0 . 5 R 1 , and q i opt = q 1 , othe rwise. (4) Under Eve’ s optima l strategy , th e maxim um achievable secrecy rate (und er the c urrent setup) is R s = min { 0 . 5 R 1 , R k,i opt } . (35) (5) Ther e is n o loss of pe rforman ce incurr ed by restrictin g the rate o f the en crypted message to R s ≤ 0 . 5 R 1 in (15). Pr oof: (1) Using Theorem 4, it is easy to check that, gi ven q ∈ [ q i − 1 , q i ) , the achiev ab le secr et key rate is a decr easing function of q . Theref ore, if q ∈ [ q i − 1 , q i ) , Eve’ s optimal strategy is to p ick q arbitrarily close to q i . (2),(3 ),(4) W e h av e alread y m entioned that o ur en coding strategy r estricts the r ate of th e encryp ted message to R s ≤ 0 . 5 R 1 , b y restricting the rate of g eneration o f the secret key to R k ≤ 0 . 5 R 1 . If min q i { R k,i } is ach iev ed by q i opt and is less than 0 . 5 R 1 , then b y switching to a different strategy q d , Eve will on ly increa se the ra te of generation of the secret key , and hen ce the rate o f tran smission of the encryp ted me ssage. On the other ha nd, if min q i { R k,i } ≥ 0 . 5 R 1 , then no matter what Eve’ s strategy is, the secrecy rate will be co nstrained by the encod ing sch eme to 0 . 5 R 1 . (5) The co nstraint introd uced by the encod ing scheme is a conservati ve one. Although the secret k ey may be generated by multiple layers, at the end of a frame, the encr ypted message is tran smitted on ly by the first encoding level. This is beca use 11 neither Alice, nor Bob know the chann el q uality in ad vance, and thus, to e nsure reliab le dec oding of the secret message, they h av e to p lan fo r the worse. For example, Eve mig ht choose to constantly play a strategy q ∈ [0 , q 1 ) , which implies that Bob will o nly be ab le to decod e level 1 o f the code. This message, tr ansmitted at a m aximum rate of R 1 , has to carry the encry pted message and gen erate a secret key , simultaneou sly . But since Eve’ s strategy rem ains in [0 , q 1 ) over the next frames, the rate of th e encrypte d message cannot exceed 0 . 5 R 1 – ther e would no t be enou gh secr et key bits to encryp t it. Therefo re, the strategy q ∈ [0 , q 1 ) can functio n as a “default” state for Eve, w here she could take refuge if the ach iev able secrecy r ate un der any other strategy exceeded 0 . 5 R 1 . Theorem s 4 and 5 above offer a g ood d escription of the achiev ab le secrecy rates. Howe ver, in Theorem 4 we assumed that the set I e of in dices correspo nding to the levels tha t are perfectly decoda ble b y Eve , and the sets I k and I n are readily available. Du e to th e fact tha t our encodin g scheme is designed such that Bob should perfor m successi ve interfer ence cancellation, th e set of levels th at are n ot deco dable by Bob is easy to co mpute. However , the ch aracterization of the set I e and its complemen t I ne is no t straightforward. The fo llowing propo sition shows how these sets can be foun d. Its p roof results fro m Lem ma 8 in Append ix C. Pr oposition 6: The maximal set o f indices I e correspo nd- ing to the le vels that are perf ectly deco dable by Eve is the largest o f the sets V e for which X j ∈ S R j ≤ q E h W h log 1 + + P j ∈ S (1 − α j ) α j − 1 . . . α 1 P h W σ 2 N + P i ∈ V c e (1 − α i ) α i − 1 . . . α 1 P h W i , ∀ S ⊆ V e , ( 36) where V c e is the c omplemen t of V e with respe ct to c I C. On the Complexity o f the Algorithm: Selectin g { α i } a nd { q i } . Our results so far facilitate the compu tation of an achiev ab le secrecy r ate, given a par tition of th e interval [0 , 1] expressed in terms of the par ameters { q 1 , q 2 , . . . , q n − 1 } , and a p ower allocation be tween the enco ding lev e ls, g i ven by the par ame- ters { α 1 , α 2 , . . . , α n − 1 } . If Alice an d Bob wish to exploit the full secrecy capa bilities of the mod el, they should per form a maximization of the achiev able secr ecy rate with respect to the par ameters { ( q i , α i ) : i = 1 , 2 , . . . , n − 1 } . The optim ization pr oblem re quires a high co mplexity nu- merical algorithm . Recall that for each value of the para meter vector { ( q i , α i ) : i = 1 , 2 , . . . , n − 1 } we need to find the set I e as in the Prop osition 6 , which inv olves co mbinator ial complexity . Given I e , we need to find the op timal set o f encodin g layers th at sh ould b e inv olved in the elabo ration of the secret key . The following example illustra tes the steps of the algo rithm fo r the least in volved scenario : th at of n = 2 . A simple c ase: n = 2 W e start b y selectin g a value for the parameter vector ( q 1 , α 1 ) . The tran smission rate s f or th e two encodin g levels 2 Ω 1 Ω 4 Ω 3 Ω 5 Ω Ω 2 , E R 1 , E R Level 1 Level 2 Fig. 5. Eve’ s equi v alent -MA C capacit y region. become: R 1 = E h M log 1 + (1 − α 1 ) P h M σ 2 N + α 1 P h M + J , (37) and R 2 = E h M " q 1 log 1 + α 1 P h M σ 2 N + +(1 − q 1 ) log 1 + α 1 P h M σ 2 N + J 1 − q 1 ! # . (38) T o illustrate a ll possible cases, we shall refer to Figure 5, where we r epresented the (eq uiv alent- ) MA C cap acity region of Eve. Althoug h this region depend s on Eve’ s strategy q ∈ { q 1 , 1 } , we shall u se it as a referen ce fra me, in wh ich the tuple ( R 1 , R 2 ) (which is fixed as ab ove) can occu py d ifferent positions, depend ing on q . Dependin g on Eve’ s strategy q ∈ { q 1 , 1 } , we have the following two algorith ms: If q = q 1 , on ly lev e l 1 is inte lligible to Bob. 1) If q 1 E h W log 1 + (1 − α 1 ) P h W σ 2 N ≥ R 1 , (39) q 1 E h W log 1 + α 1 P h W σ 2 N ≥ R 2 , (40) q 1 E h W log 1 + P h W σ 2 N ≥ R 1 + R 2 , (41) or , equiv alently , if the tuple ( R 1 , R 2 ) is inside the capacity region of Figure 5, then I e = { 1 , 2 } (i.e. b oth lev els are perf ectly decod able by Eve.) In this case, no secret key may be generated , and no secret message m ay be transmitted. 2) Else, if q 1 E h W log 1 + (1 − α 1 ) P h W σ 2 N + α 1 P h W ≥ R 1 , (42) which, along with the conditio n that we a re ou tside the capacity region implies q 1 E h W log 1 + α 1 P h W σ 2 N < R 2 , (43) that is ( R 1 , R 2 ) is in the r egion Ω 2 of Figure 5, then I e = { 1 } .But sinc e level 2 is n ot intelligible to Bob, no secret key may be gener ated. 12 3) Else, if q 1 E h W log 1 + α 1 P h W σ 2 N + (1 − α 1 ) P h W ≥ ≥ R 2 , (44) which (since not in the capacity region) implies that ( R 1 , R 2 ) is in Ω 1 , i.e. q 1 E h W log 1 + (1 − α 1 ) P h W σ 2 N < R 1 , (45) then I e = { 2 } . For this scena rio, o nly level 1 may generate a secret key at a rate equ al to min { 0 . 5 R 1 , R 1 − q 1 E h W h log 1 + (1 − α 1 ) P h W σ 2 N i } . 4) The remaining c ase is when neither of the two en- coding levels is intelligible to Eve. Under th is as- sumption, bo th le vels 1 and 2 may be inv o lved in the generation of the s ecret ke y . A secret key may be gen erated at rate min { 0 . 5 R 1 , R 1 − R E , 1 } , whe re R E , 1 is eith er equal to q 1 E h W h log 1 + (1 − α 1 ) P h W α 1 P h W + σ 2 N i if ( R 1 , R 2 ) is in Ω 4 S Ω 5 of Figur e 5, or R E , 1 = q 1 E h W h log 1 + P h W σ 2 N i } − R 2 if ( R 1 , R 2 ) is in Ω 3 S Ω N . If q = 1 , bo th levels are intellig ible to Bob. 1) If ( R 1 , R 2 ) is in Eve’ s capacity region, i.e. E h W log 1 + (1 − α 1 ) P h W σ 2 N ≥ R 1 , (46) E h W log 1 + α 1 P h W σ 2 N ≥ R 2 , (47) E h W log 1 + P h W σ 2 N ≥ R 1 + R 2 , (48) then I e = { 1 , 2 } (i.e. both levels are perfectly d ecod- able by Eve), an d no secret key may b e gene rated. 2) Else, if ( R 1 , R 2 ) ∈ Ω 2 , i.e. E h W log 1 + (1 − α 1 ) P h W σ 2 N + α 1 P h W ≥ R 1 , (49) and E h W log 1 + α 1 P h W σ 2 N < R 2 , (50) then I e = { 1 } . For this scenario, level 2 m ay genera te a secret key at rate R 2 − E h W h log 1 + α 1 P h W σ 2 N i . 3) Else, if ( R 1 , R 2 ) ∈ Ω 1 , i.e. E h W log 1 + α 1 P h W σ 2 N + (1 − α 1 ) P h W ≥ R 2 , (51) and E h W log 1 + (1 − α 1 ) P h W σ 2 N < R 1 , (52) then I e = { 2 } . For th is scen ario, level 1 may generate a secret key at rate min { 0 . 5 R 1 , R 1 − E h W h log 1 + (1 − α 1 ) P h W σ 2 N i } . 4) When neither of the two en coding le vels is intel- ligible to Eve, both lev els may be in volved in th e generation of the secret key . W e can achieve the se- cret ke y rate giv e n b y R 1 + R 2 − R E , 1 − R E , 2 , where R E , 1 and R E , 2 are cho sen such tha t R E , 1 + R E , 2 = E h W h log 1 + P h W σ 2 N i , 0 . 5 R 1 ≤ R E , 1 ≤ min { R 1 , E h W h log 1 + (1 − α 1 ) P h W σ 2 N i } , a nd R E , 2 ≤ min { R 2 , E h W h log 1 + α 1 P h W σ 2 N i } , with the ob serva- tions following Th eorem 4. Since we a re cu rrently inv e stigating the conservati ve sce- nario, E ve will pick th e strategy ( q = q 1 or q = 1 ) which yields the minimum secr ecy r ate. W e hav e to fin d the value of ( q 1 , α 1 ) which yields the largest such minimu m. Eq uiv alen tly , the optimal ( q 1 , α 1 ) will pr ovide equal achie vable secrecy rates for q = q 1 and for q = 1 . It is im portant to note that, alth ough the algo rithm may be extremely complex, it nee ds to be solved o nly o nce fo r the desired value of n . The op timal param eters may the n be stored at both legitimate parties. In an effort to reduce the com plexity of the a lgorithm, we propo se to pick the p arameters { ( q i ) : i = 1 , . . . , n − 1 } such that { q 0 , q 1 , q 2 , . . . , q n − 1 , q n } ar e all equ ally spa ced, which correspo nds to a u niform partition (or “quantizatio n”) of the interval [0 , 1] . W ith th is rule in place, the optimization needs to be perform ed only over th e ( n − 1) param eters α 1 , . . . , α n − 1 , hence the co mplexity is reduced by half. From ou r nume rical results for n = 2 and n = 3 (see Figur e 8), the loss o f o ptimality due to th e u niform partition of [0 , 1] is not very significant. W e co njecture that, as n increases, th is loss o f pe rforman ce shou ld bec ome negligible. Our r emark is based o n the fact that as n → ∞ the optim al partition of the interval [0 , 1] ap proach es a un iform partition (with a vanishing step). I V . N U M E R I C A L R E S U LT S In Figure s 6 and 7 we show th e impr ovement of ou r BMW secrecy enc oding scheme over the worst-case scenario approa ch of (1 0). Note that if Eve’ s channel coefficient is close (statistically) to Bob’ s – th e case of Figure 6 – th e worst-case approa ch of (10) – o r equivalently the case n = 1 – canno t achieve a positive secrecy r ate. Howe ver, even W y ner’ s pure s cheme implemen ted as in (10) can ach iev e a positive secrecy rate if λ W > λ M (1 + J σ 2 N ) , as discussed in Section II – see Figu re7. Th e merit o f our novel encodin g scheme is significant. The best-ca se (or “minimax ”) scenario solu tion of [12] is giv en in both Figu res 6 and 7 fo r compar ison. T he “minimax ” scenario descr ibes a situation wh en Alice and Bob can know Eve’ s strategy in advance (or, in game-th eoretic terms, Alice plays first ). Altho ugh this scenario ma y not seem like a rea- sonable mo del, it serves as a n upper-boun d on the achievable secrecy rates. Figure 8 depicts the perf ormance of the BMW secrecy encodin g scheme when the p artition of the interval [0 , 1] into intervals of the fo rm [ q i − 1 , q 1 ) is done u niformly , i.e . the parameters q 0 , q 1 , q 2 , . . . , q n are equally spaced, in stead o f 13 0 5 10 15 0 0.2 0.4 0.6 0.8 1 1.2 1.4 transmitter power P Achievable secrecy rates Achievable secrecy rates vs. transmitter power constraints. σ N 2 =1, J=5, λ M =0.2, λ W =0.8 sequential scheme, n=2 sequential scheme, n=1 sequential scheme, n=3 minimax solution Fig. 6. Achie vabl e secrecy rates with our BMW secre cy encoding scheme. Exponentia lly distrib uted channel coef fi cient s with λ M = 0 . 3 , λ W = 0 . 8 , J = 5 , σ 2 N = 1 . 0 5 10 15 0 0.2 0.4 0.6 0.8 1 1.2 1.4 1.6 1.8 transmitter power P Achievable secrecy rates Achievable secrecy rates vs. transmitter power constraint. σ N 2 =1, J=5, λ M =0.2, λ W =1.5 sequential scheme, n=2 sequential scheme, n=1 sequential scheme, n=3 minimax solution Fig. 7. Achie vabl e secrecy rates with our BMW secre cy encoding scheme. Exponentia lly distrib uted channel coef fi cient s with λ M = 0 . 2 , λ W = 1 . 5 , J = 5 , σ 2 N = 1 . being picked in an op timal way . W e note th at the degrada tion of the ach iev able secrecy rates is q uite small and decreasing as n in creases. Figur es 9 and 1 0 show the design parame ters used for o btaining the results of Figure 8 . V . C O N C L U S I O N S W e have seen how an a cti ve eavesdropper can seriou sly decrease the achiev ab le s ecrecy rate in a classical scenario of a fast-fading A WGN channel with an eav esd ropper . Our scenario models th e most conservativ e and most pr actical approac h to the active eaves dropp er . W e h av e seen th at, in order to take advantage of th e non-d uplex nature of the eav esdropp er’ s termin al, we ne ed a more elaborate, block-Ma rkov W yner encoding scheme. While in the classical eavesdropper scena rio the legitimate receiver is completely passi ve, our schem e relies heavily on the cooper ation of the receiver . That means that at the end of each frame, Bob is required to f eed b ack to Alice infor mation abou t Eve’ s strategy , and then, based on this inform ation, r eplicate Alice’ s efforts to distill a secret key . 0 5 10 15 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 transmitter power P Achievable secrecy rates Achievable secrecy rates vs. transmitter power constraint. σ N 2 =1, J=5, λ M =0.2, λ W =1.5 sequential scheme, n=2 sequential scheme, n=3 sequential scheme, n=2 − approximation sequential scheme, n=3 − approximation Fig. 8. Achie vabl e secrec y rates with our BMW secrecy encoding scheme, with uniform and with optimized partition of the interv al [0 , 1] . Exponenti ally distrib uted channe l coef ficients with λ M = 0 . 2 , λ W = 1 . 5 , J = 5 , σ 2 N = 1 . 0 5 10 15 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 transmitter power P design parameters Design parameters for n=2 −− σ N 2 =1, J=5, λ M =0.2, λ W =1.5 optimal α 1 for n=2 optimal q 1 for n=2 optimal α 1 for uniform partition q 1 =0.5 − uniform partition Fig. 9. The encoding paramete rs q 1 and α 1 for the case n = 2 : optimal and uniform partiti on of the interv al [0,1]. Exponenti ally distrib uted channel coef ficients with λ M = 0 . 2 , λ W = 1 . 5 , J = 5 , σ 2 N = 1 . 0 5 10 15 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 transmitter power P design parameters Design parameters for n=3 −− σ N 2 =1, J=5, λ M =0.2, λ W =1.5 optimal q 1 for n=3 optimal q 2 for n=3 optimal α 1 for n=3 optimal α 2 for n=3 q1=0.33 − uniform partition q 2 =0.66 − uniform partition optimal α 1 for uniform partition optimal α 2 for uniform partition Fig. 10. The encoding parameters q 1 , q 2 , α 1 and α 2 for the case n = 3 : optimal and uniform partit ion of the interv al [0,1]. Exponentia lly distribu ted channe l coef ficients with λ M = 0 . 2 , λ W = 1 . 5 , J = 5 , σ 2 N = 1 . 14 Although the per formanc e of our BMW scheme remains below the secreccy rate up per-bound provided by the best-case scenario of [12], the imp rovement it brings over the passive- receiver solution is q uite significant. A P P E N D I X A A U S E F U L L E M M A The following lem ma is used several times in th is paper . Lemma 7: The fun ction f ( q ) = q lo g(1 + x ) + (1 − q ) log 1 + x 1 + y 1 − q ! , (53) where x, y > 0 , is strictly increasin g and strictly convex as a function of q . Pr oof: It is straigh tforward to compu te d f ( q ) dq = log (1 + x ) 1 + y 1 − q 1 + x + y 1 − q ! − − xy 1 − q · 1 (1 + y 1 − q )(1 + x + y 1 − q ) , (54) and d 2 f ( q ) dq 2 = xy (1 − q ) 2 (1 + y 1 − q )(1 + x + y 1 − q ) · · " 1 − 1 + x − ( y (1 − q ) ) 2 (1 + y 1 − q )(1 + x + y 1 − q ) # . (55) Since 1 + y 1 − q > 1 and 1 + x − ( y (1 − q ) ) 2 < 1 + x + y 1 − q , we can state that d 2 f ( q ) dq 2 > 0 . Th erefore, d f ( q ) dq is a strictly increasing func tion o f q . But evaluating the first derivati ve in q = 0 we g et d f dq (0) = = log (1 + x )(1 + y ) 1 + x + y − xy (1 + y )(1 + x + y ) = = log 1 + xy 1 + x + y − xy (1 + x + y )(1 + y ) ( a ) ≥ ≥ xy (1 + x )(1 + y ) − xy (1 + x + y )(1 + y ) ( b ) > 0 , (56) where ineq uality ( a ) fo llows from log(1 + β ) > β 1+ β for any β > − 1 , β 6 = 0 , if we replace β = xy 1+ x + y , while inequality ( b ) follows since x > 0 . Ther efore d f ( q ) dq is always strictly positive and strictly incr easing, which imp lies that f ( q ) is strictly incr easing an d strictly co n vex. A P P E N D I X B C O M M E N T S O N P R E V I O U S LY E X I S T I N G R E S U LT S O N M AC S E C R E C Y The mo st notable re cent results on the achiev a ble secrecy rates for M A Cs are p rovided by [ 15] and [16]. Altho ugh the papers bring unqu estionable contributions relevant to our own scenario, such as the co ncepts of individual and collective secrecy , and the im provement o f the secrecy sum-rates by noise injection ( cooperative jamming), we f eel that there are some mislead ing issues related to their propo sed secrecy encodin g meth od. This why we re-f ormulate th e collective- secr ecy [15] enco ding meth od in the curren t pap er . The encodin g method of [15] uses a separ ate secret message encodin g f or each user, much like o ur own enco ding scheme. Howe ver, unlike the present paper, the secrecy en coding of [15] employs a “superp osition encod ing scheme” (see Section III of both [ 15] and [ 16]). I n the fo llowing parag raphs, we provide a brief de scription of this tech nique. T ake one user with power constraint P . Th e user g enerates two indepen dent codeboo ks, in th e following mann er: the first codebo ok con tains 2 N R s N -dimensio nal co dew o rds, and each letter of e ach cod ew o rd is inde penden tly gen erated, acco rding to the r ealization o f a Gaussian random variable of zero mea n and variance αP ; th e second co debook contains 2 N R 0 N - dimensiona l codewords, an d each letter of e ach codeword is indep endently gener ated, acco rding to the re alization of a Gaussian random variable of zero mean and v ariance (1 − α ) P . The s ecret message – transmitted at rate R s – picks a codew o rd from th e fir st co debook , w hile ano ther codeword is r andomly picked f rom the second c odeboo k. The message transmitted by this u ser is the su mmation of the two cod ew or ds. At a first glance, it ap pears th at the transmitted message belongs to a co deboo k of 2 N ( R s + R 0 ) N -dimensio nal code- words, in which e ach letter of each co dew ord is the realization of a Gaussian ran dom variable of variance P . Mo reover , th e codebo ok is already binned, like in W yner’ s scheme [1], [17]. Howe ver, if th e transmitted message is com pletely decod- able by Bob, the rates R s and R 0 should be situated with in the correspon ding MAC rate region. For example, if we had a Gaussian eavesdropper c hannel where the A WGN variances were 1 for both chann els, while the absolute squar ed ch annel coefficients are 1 for the main chan nel and h k for the eaves- dropp er’ s channel, th e rates should satisfy R s ≤ log [1 + αP ] , R 0 ≤ log [1 + (1 − α ) P ] , and R s + R 0 ≤ log [1 + P ] . But the first two con ditions d o not app ear in [15]. Even if the se cond itions were satisfied, we believe that the “superpo sition en coding sche me” of [ 15] is n ot equ i valent to W yner’ s scheme. The key to W yner’ s scheme is that each bin ma kes a “g ood” cod ebook for the eavesdropper . That is, giv en the secret key an d the eavesdropper’ s receiv ed message, the bin cho sen b y the secret key conv eys informa tion to the eav esdroppe r at a r ate ar bitrarily close to the eavesdropper’ s channel capacity . For the same to y model as above, the rate of each bin should be arbitrar ily close to log [1 + P h k ] . Howev e r , und er the “su- perposition encoding sch eme” of [1 5], this r ate can not exceed log [1 + αP h k ] 3 . T o achiev e the capacity of th e ea vesdro pper’ s channel, α would n eed to be arbitrarily close to 1 . But then the co deboo k associated with th e secret message would be generated with a rbitrarily small power . If a po siti ve secrecy rate R s is still desired, th e in telligibility of the secret message at the legitimate receiver is com promised. Thu s, we do not expect that the propo sed encoding meth od of [15] will achieve the secrecy rates claim ed therein. 3 Note that althoug h the second codeboo k has a rate equal to log [1 + P h k ] in [15], this rate is not sustaina ble by the ea vesdropper’ s channel with powe r constrai nt αP . 15 2 Ω 1 R 2 R 1 Ω 4 Ω 3 Ω 5 Ω N Ω Fig. 11. The capacity region of a MA C. At this point, we want to emp hasize the fact that, except for the en coding m ethod, th e results of [15] and [16] are corr ect. Howe ver, our Theor em 4 is qu ite different than th ese r esults. Our secrecy-en coding scheme in volves in the gener ation of the secret key th e levels that are non-d ecodab le by either Eve or Bob. In the con text o f [15] and [16], th is would be equiv ale nt to ha ving some user s transmit at rates n ot suppo rted by th e re ceiv er, but still h elp with the transmission of secrecy . Although this approa ch would not make much sen se in [15] and [16], it fits perfectly with the constrain ts of our co mpoun d- channel- like scenario. A P P E N D I X C P R O O F A N D M O T I V AT I O N O F P RO P O S I T I O N 6 As we stated earlier, fr om Eve’ s p oint of view , the different encodin g levels are very similar to different users. T herefor e, Eve’ s channel can be seen as a multiple access chan nel (MAC), with n users, each with a different power, but all sharing the same chan nel coefficient. Howe ver, to th e best of o ur knowledge, in th e curren t literatur e ther e is no treatment of the achievable rate region for a set o f u sers when the other users are n ot decoda ble. T o motivate Prop osition 6, we look at th e two-user Gaussian MA C, the capacity region of which is given in Figure 11. Let the capacity o f th e first user’ s channel (when user 2 is absent) be C 1 = log(1 + P 1 /σ 2 N ) , and the capacity of the second user’ s channel (when user 1 is absent) be C 2 = lo g (1 + P 2 /σ 2 N ) . W e kn ow that the ach iev able rate region is g iv e n by all pairs ( R 1 , R 2 ) that satisfy [1 8] R 1 ≤ C 1 , R 2 ≤ C 2 and R 1 + R 2 ≤ log(1 + ( P 1 + P 2 ) /σ 2 N ) . This implies that when u ser 2 transmits at a rate R 2 = C 2 , user 1 sho uld b e dec oded b y treating the second user as white Gaussian no ise, and by perfo rming successiv e interfer ence cance llation. The first user’ s m aximum decodab le transmission rate is then R 1 = log(1 + P 1 / ( σ 2 N + P 2 )) . Howe ver, it is not straightf orward to see wheth er , when the second user uses a ran domly gen erated Gau ssian codebo ok at a rate R 2 > C 2 and cann ot be decoded, the first user may employ a tran smission rate larger tha n log(1 + P 1 / ( σ 2 N + P 2 )) (region Ω 4 ) . T o justify our que stion, consider the following “decodin g” method. First , a list of possible code words is computed f or user 2 , by treating u ser 1 as interf erence, and selecting on ly tho se codewords of the second u ser’ s codeb ook that h av e a non-z ero a po steriori pro bability . T his list may be shorter tha n the second u ser’ s whole codebo ok, and th e a posteriori probab ility o f th e cod ew o rds therein may be non- unifor m. Th en, using this infor mation about user 2 , we attempt decodin g for user 1 . Propo sition 6 states th at this method is no better th an the one wh ich treats user 2 as white no ise. In the r emainder of this appen dix we form ulate and prove the following lemma, which c onsiders a g eneral Gau ssian MA C, and fro m which the pro of o f Prop osition 6 is straight- forward to derive. Lemma 8: Consider a Gaussian MAC with users j ∈ I , each with average power constraint P j , j ∈ I , and each transmitting at a rate R j , j ∈ I . L et the variance of th e ad- ditiv e white complex Gaussian noise be σ 2 N . W e are inte rested in th e maximum n umber of users th at are d ecodable by the receiver . Th e maximal set o f indices I e ⊆ I correspondin g to these u sers th at ar e p erfectly decodable b y the receiver is the largest of the sets V e for which X j ∈ S R j ≤ log 1 + P j ∈ S P j σ 2 N + P i ∈ V ne P i , ∀ S ⊆ V e , (57) where V ne is the c omplemen t of V e with respe ct to I Pr oof: Deno te the largest o f th e sets V e for which (57) holds by V ∗ e , and its co mplement in I by V ∗ ne . Assume that V ∗ ne is non -empty (if it is empty , the result of the lem ma is trivial). Note that all users in V ∗ e are decodab le. Howev er, if all users of V ∗ ne were decod able, then the p roperty in ( 57) would hold for I , hence V ∗ e would no lo nger be the largest set w ith that prop erty . Theref ore, no t all users o f V ∗ ne are decod able. For the users in V ∗ ne , consider the the r ate-region where: (1) none of the users can be decod ed by treatin g the o thers as interferen ce, (2 ) if any one user were deco dable (i.e. provid ed to the re ceiv er by a g enie), then all other users would be decodab le and (3) not all users are d ecodable. This r egion can be char acterized as Ω N = ( ( R i ) i ∈ V ∗ ne | R j > log 1 + P j σ 2 N + P k ∈ V ∗ ne \{ j } P k , ∀ j ∈ V ∗ ne , X j ∈ S R j ≤ log 1 + P j ∈ S P j σ 2 N , ∀ S ⊂ V ∗ ne \ { i } , ∀ i ∈ V ∗ ne , X j ∈ V ∗ ne R j > log 1 + P j ∈ V ∗ ne P j σ 2 N ) (for | V ∗ ne | = 2 , Ω N is represen ted in Figure 11). Next we p rove that such a ra te region is no n-empty for th e users in V ∗ ne . T o acco mplish this, we show b y mathem atical induction that X j ∈ S log 1 + P j σ 2 N + P k ∈ V ∗ ne \{ j } P k ≤ ≤ log 1 + P j ∈ S P j σ 2 N , ∀ S ⊂ V ∗ ne , (58) which m eans that if the first cond ition in the d efinition of Ω N holds for all j ∈ S , this doe s not prevent the s e cond cond ition in the d efinition of Ω N from ho lding as well. For S = { i } we have log 1 + P i σ 2 N + P j ∈ V ∗ ne \{ i } P j < log 1 + P i σ 2 N . ( 59) 16 If (58) holds for a set S , th at is X j ∈ S log 1 + P j σ 2 N + P k ∈ V ∗ ne \{ j } P k ≤ ≤ log 1 + P j ∈ S P j σ 2 N , (60) then addin g an other user r to S we get X j ∈ S S { r } log 1 + P j σ 2 N + P k ∈ V ∗ ne \{ j } P k ≤ ≤ log 1 + P j ∈ S P j σ 2 N + + log 1 + P r σ 2 N + P j ∈ V ∗ ne \{ r } P j = = log P j ∈ S P j + σ 2 N σ 2 N σ 2 N + P k ∈ V ∗ ne P k σ 2 N + P k ∈ V ∗ ne \{ r } P k ≤ ≤ log 1 + P j ∈ S S { r } P j σ 2 N , (61) where the last inequality hold s b ecause it is eq uiv alent to the inequality σ 2 N + P k ∈ V ∗ ne P k σ 2 N + P k ∈ V ∗ ne \{ r } P k ≤ σ 2 N + P j ∈ S S { r } P j σ 2 N + P j ∈ S P j , (62) which is eq uiv alent to th e inequality X k ∈ V ∗ ne P k X j ∈ S P j ≤ ≤ X k ∈ V ∗ ne \{ r } P k X j ∈ S S { r } P j , (63) which hold s b ecause P k ∈ V ∗ ne P k − P j ∈ S P j > P r . At this po int we know that Ω N is a feasible (non- empty) rate region for th e u sers in V ∗ ne and (by con struction) no user of Ω N can be de codable. Note that the first cond ition in the definition of Ω N , i.e. that no ne of the users can be deco ded by treating the o thers as inte rference, follows naturally for all users in V ∗ ne (see th e defin ition of V ∗ e above), while the third condition, i.e. that n ot all users are deco dable, is also characteristic of V ∗ ne , as we h av e already shown. Thu s, th e only restrictive cond ition on Ω N is an upp er bo und on the rates (the second conditio n). In other words, any rate tup le which is fe asible fo r the u sers in V ∗ ne can be obtained from a rate tup le in Ω N by increasing some of the rates. But since no ne o f the users is decod able for a rate tuple in Ω N , it is not po ssible that any non -empty set of users suddently becomes d ecodable as some of the tran smission rates increase. Equiv a lently , for Fig ure 11, since none of th e two users is decodab le when they transmit at a rate pair in Ω N , it is not possible that one of them beco mes deco dable b y inc reasing its rate (su ch tha t the rate pair moves to either Ω 3 or Ω 4 or Ω 5 ). T o see this, u sing the notation already established in the previous sections ( X S is the set of tr ansmitted seq uences o f all users in S , Z is the r eceiv ed seq uence, Q is the noise sequence), for any set S ⊂ V ∗ ne we can write H ( X S | Z , X V ∗ e ) = = H ( X S | X V ∗ e ) + H ( Z | X S , X V ∗ e ) − H ( Z | X V ∗ e ) = = H ( X S ) + H ( Z | X S , X V ∗ e ) − H ( Z | X V ∗ e ) = = X j ∈ S R j + H ( X i ∈ V ∗ ne \ S X j + Q ) − H ( Z | X V ∗ e ) . (64) where the last two eq ualities follow fro m the indepen dence of the users. Note tha t H ( P i ∈ V ∗ ne \ S X j + Q ) incre ases with any rate R i , i ∈ V ∗ ne \ S . But since all rate tuples under con - sideration ar e o utside the cap acity region of the u sers in V ∗ ne , the rece i ved sequence Z displays an asymptotic equipar tition proper ty , as no ticed in [19]. Intu iti vely , this happ ens because, as the r ate tuple moves outside the capacity region , the volume of the typical set o f received sequ ences bec omes as large as the volume of th e whole chann el ou tput space. The immed iate implication is that ou tside the capacity region H ( Z | X V ∗ e ) is a con stant fun ction of the rates of th e users in V ∗ ne . This conclu des our pro of that the en tropy of the user s in any subset of V ∗ ne increases as any of th e r ates increase. But since any ra te tup le f or the users in V ∗ ne , situated outside of the rate region Ω N , can b e obtain ed fr om a tuple insid e Ω N , by in creasing at le ast one of the rates, and since no ne o f the users in Ω N is de codable, this implies that none of the user s in V ∗ ne is decod able. A n otable con sequence of Lemma 8 a bove is that, in a MA C scenario emp loying Gaussian codin g, when ev er a user transmits at a rate which exceed s its channel capacity , the best strategy for the o ther u sers is to treat it as no ise. R E F E R E N C E S [1] A. D. W yner, “The wire-tap channel, ” The B ell System T echni cal J ournal , vol. 54, pp. 1355–1387, Oct. 1975. [2] I. Csiszar and J. Korn er , “Broadcast channels with confident ial mes- sages, ” IEE E T rans. Inform. Theory , vol. 24, pp. 339–348, May 1978. [3] Z. Li, R. Y ates, and W . Trappe, “Secret communicat ion with a fading eav esdropper channel, ” Pr oc. IEEE Int. Symp. on Inform. Theory (ISIT) , June 2007. [4] P . K. Gopala, L. Lai, and H. E. Gamal, “On the secrecy capacity of fadi ng channel s , ” IEE E T rans. Inform. Theory , vol. 54, pp. 4687–4698, Oct. 2008. [5] Y . Liang, H. V . Poor, and S. Sha m ai, “Secure communic ation ov er fading channe ls, ” IEEE T rans. Inform. Theory , vol. 54, pp. 2470–2492, June 2008. [6] A. Khisti, A. Tchamkerten, and G. W ornell, “Secure broadcasti ng ove r fadi ng channel s , ” IEE E T rans. Inform. Theory , vol. 54, pp. 2453–2469, June 2008. [7] A. J. Goldsmith and P . P . V araiya, “Capacity of fadin g channels with channe l state information, ” IEE E T rans. Inform. T heory , vol. 43, pp. 1986–1992, Nov . 1997. [8] S. Shafiee and S. U lukus, “Capac ity of multiple access channel s with correla ted jamming, ” Milit ary Communicati ons Confer ence , MILCOM , vol. 1, pp. 218–224, Oct. 2005. [9] A. Kashyap, T . Basar , and R. Srikant, “Correlated jamming on mimo Gaussian fadin g channels, ” IEEE Tr ans. Inform. Theory , vol. 50, pp. 2119–2123, Sept. 2004. [10] E. Altman, K. A vrache nko v , and A. Garnaev , “ A jamming game in wireless networks with transmission cost, ” Proce edings of Net-Coop, A vignon, F rance , June 2007. [11] S. N. Digga vi and T . Cov er, “The w orst additi ve noise under a cov ariance constrai nt, ” IE EE T rans. Inform. Theory , vol . 47, pp. 3072–3081, Nov . 2001. [12] G. T . Amariuca i and S. W ei, “ Acti ve eav esdropping in fast fading channe ls, ” Proc . IEEE Military Commun. Conf. (MILCOM) , Oct. 2009. 17 [13] T . M. Co ver , “Broa dcast chan nels, ” IEEE T rans. Inform. T heory , vol. 18, pp. 2–14, Jan. 1972. [14] B. Schneier , Applied cryptog raphy . J ohn W iley & Sons, 1996. [15] E. T ekin and A. Y ener , “The general Gaussian multiple-ac cess and two- way channels: achie vabl e rates and coopera tiv e jamming, ” IEEE Tr ans. Inform. Theory , vol. 54, pp. 2735–2751, June 2008. [16] ——, “The Gaussian m ultipl e acce ss wire-tap channel , ” IEE E T rans. Inform. Theory , vol. 54, pp. 5747–5755, Dec. 2008. [17] S. K. Leung-Y an -Cheong and M. E. Hellman, “The Gaussian wire-tap channe l, ” IE EE T rans. Inform. Theory , v ol. 24, pp. 451–456, July 1978. [18] T . M. Co ver and J. A. Thomas, Elements of informatio n theory (second ed.) . Hoboken, Ne w Jersey: John W iley & Sons, Inc., 2006. [19] X. Wu a nd L.-L . Xie, “ Asymptotic equipartiti on property of output when rate is abov e capa city , ” arXiv:0908.4445v1 [cs.IT] , Aug. 2009.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment