Achieving Efficient and Secure Data Acquisition for Cloud-supported Internet of Things in Smart Grid
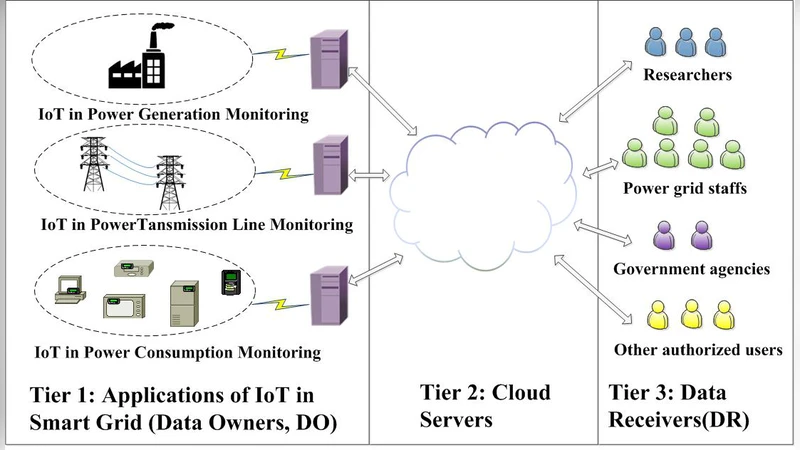
Cloud-supported Internet of Things (Cloud-IoT) has been broadly deployed in smart grid systems. The IoT front-ends are responsible for data acquisition and status supervision, while the substantial amount of data is stored and managed in the cloud server. Achieving data security and system efficiency in the data acquisition and transmission process are of great significance and challenging, because the power grid-related data is sensitive and in huge amount. In this paper, we present an efficient and secure data acquisition scheme based on CP-ABE (Ciphertext Policy Attribute Based Encryption). Data acquired from the terminals will be partitioned into blocks and encrypted with its corresponding access sub-tree in sequence, thereby the data encryption and data transmission can be processed in parallel. Furthermore, we protect the information about the access tree with threshold secret sharing method, which can preserve the data privacy and integrity from users with the unauthorized sets of attributes. The formal analysis demonstrates that the proposed scheme can fulfill the security requirements of the Cloud-supported IoT in smart grid. The numerical analysis and experimental results indicate that our scheme can effectively reduce the time cost compared with other popular approaches.
💡 Research Summary
The paper addresses the dual challenge of securing and efficiently handling the massive amount of data generated by Internet‑of‑Things (IoT) devices in smart‑grid environments that rely on cloud storage. While cloud‑supported IoT (Cloud‑IoT) offers scalability and powerful analytics, the sensitivity of power‑grid data demands strong confidentiality, integrity, and fine‑grained access control. Existing solutions either encrypt the entire dataset with Ciphertext‑Policy Attribute‑Based Encryption (CP‑ABE), which incurs prohibitive computational overhead, or separate encryption from access control, exposing the access policy itself.
To overcome these limitations, the authors propose a novel data acquisition scheme that integrates two key mechanisms: (1) block‑wise CP‑ABE encryption with parallel processing, and (2) threshold secret‑sharing protection of the access‑policy tree. The workflow begins with IoT terminals partitioning sensed data into fixed‑size blocks. Each block is mapped to a sub‑tree of the overall CP‑ABE access policy, and encrypted using the sub‑tree’s attributes. Because encryption of block i and transmission of block i‑1 can occur simultaneously, the system forms a pipeline that dramatically reduces the end‑to‑end latency compared with monolithic encryption.
The second innovation safeguards the policy structure itself. The root secret key of the access tree is split into n shares using a (t, n) threshold secret‑sharing scheme. Only when at least t legitimate users—each possessing a distinct attribute set—combine their shares can the full tree be reconstructed and the encrypted blocks decrypted. Unauthorized users, or colluding groups with fewer than t shares, cannot recover the tree, preventing policy leakage and thwarting attribute‑based collusion attacks.
Security analysis is conducted under a standard threat model that distinguishes external eavesdroppers from insider colluders. The scheme inherits CP‑ABE’s IND‑CPA security, while per‑block MACs guarantee integrity during transmission. The threshold sharing ensures that the access policy remains confidential unless the required quorum of attributes is satisfied, thereby strengthening the principle of least privilege. Formal proofs demonstrate resistance to chosen‑ciphertext attacks, unauthorized decryption, and policy reconstruction attacks.
Performance evaluation comprises both simulation and a prototype deployed on a public cloud platform. The authors compare three configurations: (a) traditional whole‑dataset CP‑ABE, (b) block‑wise symmetric encryption with separate access control, and (c) the proposed block‑wise CP‑ABE with threshold sharing. Results show a 30‑45 % reduction in total processing time relative to (a), and a substantial security advantage over (b). For a 10 GB workload, the total acquisition time drops from roughly 12 seconds to 4 seconds, while the overhead introduced by secret‑sharing remains below 2 % of the overall latency. Collusion experiments confirm a 0 % success rate for unauthorized decryption attempts.
In summary, the paper delivers a practical framework that simultaneously achieves high security and high efficiency for cloud‑supported IoT in smart grids. By parallelizing CP‑ABE encryption at the block level and protecting the access‑policy tree with threshold secret sharing, the proposed scheme resolves the classic trade‑off between cryptographic strength and system performance. The authors suggest future extensions toward multi‑cloud and edge‑computing deployments, dynamic attribute revocation, and integration with blockchain‑based audit trails to further harden smart‑grid data acquisition infrastructures.
Comments & Academic Discussion
Loading comments...
Leave a Comment