Quantum Depth in the Random Oracle Model
We give a comprehensive characterisation of the computational power of shallow quantum circuits combined with classical computation. Specifically, for classes of search problems, we show that the following statements hold, relative to a random oracle: (a) BPPQNCBPP ≠ BQP. This refutes Jozsa’s conjecture in the random oracle model. As a result, this gives the first instantiatable separation between the classes by replacing the oracle with a cryptographic hash function, yielding a resolution to one of Aaronson’s ten semi-grand challenges in quantum computing. (b) BPPQNC ⊈ QNCBPP and QNCBPP ⊈ BPPQNC. This shows that there is a subtle interplay between classical computation and shallow quantum computation. In fact, for the second separation, we establish that, for some problems, the ability to perform adaptive measurements in a single shallow quantum circuit, is more useful than the ability to perform polynomially many shallow quantum circuits without adaptive measurements. We also show that BPPQNC and BPPQNC are both strictly contained in BPPQNCBPP. (c) There exists a 2-message proof of quantum depth protocol. Such a protocol allows a classical verifier to efficiently certify that a prover must be performing a computation of some minimum quantum depth. Our proof of quantum depth can be instantiated using the recent proof of quantumness construction by Yamakawa and Zhandry.
💡 Research Summary
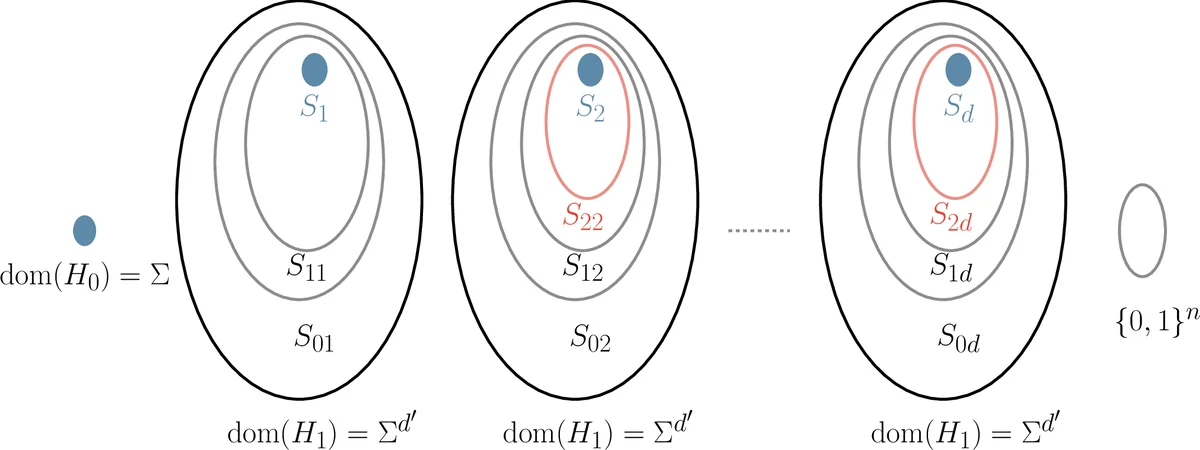
The paper provides a comprehensive characterization of the computational power of hybrid models that combine shallow quantum circuits (QNC) with classical polynomial‑time computation (BPP) in the random oracle model. The authors focus on four hybrid classes: BPP·QNC·BPP (classical computation interleaved with multiple depth‑d quantum subroutines), BPP·QNC (classical pre‑ and post‑processing around a single shallow quantum circuit), QNC·BPP (a depth‑d quantum circuit that can invoke classical computation after each layer), and the related class BPP·QNC·BPP_d where the quantum depth is bounded by a function d(n) ≤ poly(n).
The main contributions are threefold.
-
Separation of BPP·QNC·BPP from BQP.
The authors prove that for any polynomial depth d, relative to a random oracle, BPP·QNC·BPP_d is strictly weaker than BQP. The proof hinges on a new “classical query soundness” property and a lifting lemma that transforms any BPP‑vs‑BQP separation problem satisfying this property into a separation between BPP·QNC·BPP_d and BQP. Known problems such as Fourier‑Fishing and Collision‑Hashing satisfy the property, so the result applies to concrete, instantiable problems. By treating oracle queries as depth‑1 quantum gates, the separation holds even when the oracle is instantiated with a cryptographic hash function (e.g., SHA‑2 or SHA‑3), thereby providing the first plausible instantiation of a problem solvable in BQP but not in BPP·QNC·BPP_d. This refutes Jozsa’s conjecture in the random‑oracle setting and resolves Aaronson’s “semi‑grand challenge” concerning an explicit separation between hybrid models and BQP. -
Incomparability of BPP·QNC and QNC·BPP.
The paper shows that BPP·QNC is not contained in QNC·BPP and vice‑versa, again relative to a random oracle. The key insight is that adaptive measurements within a single shallow quantum circuit (the QNC·BPP model) can extract more information than a sequence of non‑adaptive shallow circuits surrounded by classical processing (the BPP·QNC model). Consequently, both hybrid classes are strictly contained in BPP·QNC·BPP, establishing a nuanced hierarchy:
BPP·QNC ⊂ BPP·QNC·BPP ⊃ QNC·BPP, with both inclusions strict. -
Proof‑of‑Quantum‑Depth Protocols.
Extending the separation techniques, the authors construct a two‑message interactive protocol that allows a classical verifier to certify that a quantum prover must possess at least depth‑d quantum capability. The protocol builds on the recent proof‑of‑quantumness construction by Yamakawa and Zhandry. Completeness guarantees that an honest BQP prover succeeds with overwhelming probability, while soundness ensures that any prover limited to BPP·QNC·BPP_d cannot cheat except with negligible probability. The authors discuss why longer interactive protocols would artificially inflate the required depth due to message delays, and argue that the two‑message design captures the intended notion of quantum depth without such artifacts.
Additional results include a finer granularity separation: BPP·QNC·BPP_d ⊂ BPP·QNC·BPP_{2d+O(1)}, showing that even modest increases in allowed quantum depth strictly increase computational power. The paper notes that many quantum‑secure hash functions can be evaluated in logarithmic or constant depth, making the depth parameters realistic for practical instantiations.
Overall, the work settles several open questions about the power of shallow quantum circuits when combined with classical processing, provides concrete, cryptographically instantiable separations, and introduces a new primitive—proofs of quantum depth—that bridges complexity theory and quantum cryptographic protocols. The results have implications for quantum algorithm design, quantum‑secure cryptography, and the theoretical limits of near‑term quantum devices that are depth‑constrained.
Comments & Academic Discussion
Loading comments...
Leave a Comment