Quantum sealed-bid auction using a modified scheme for multiparty circular quantum key agreement
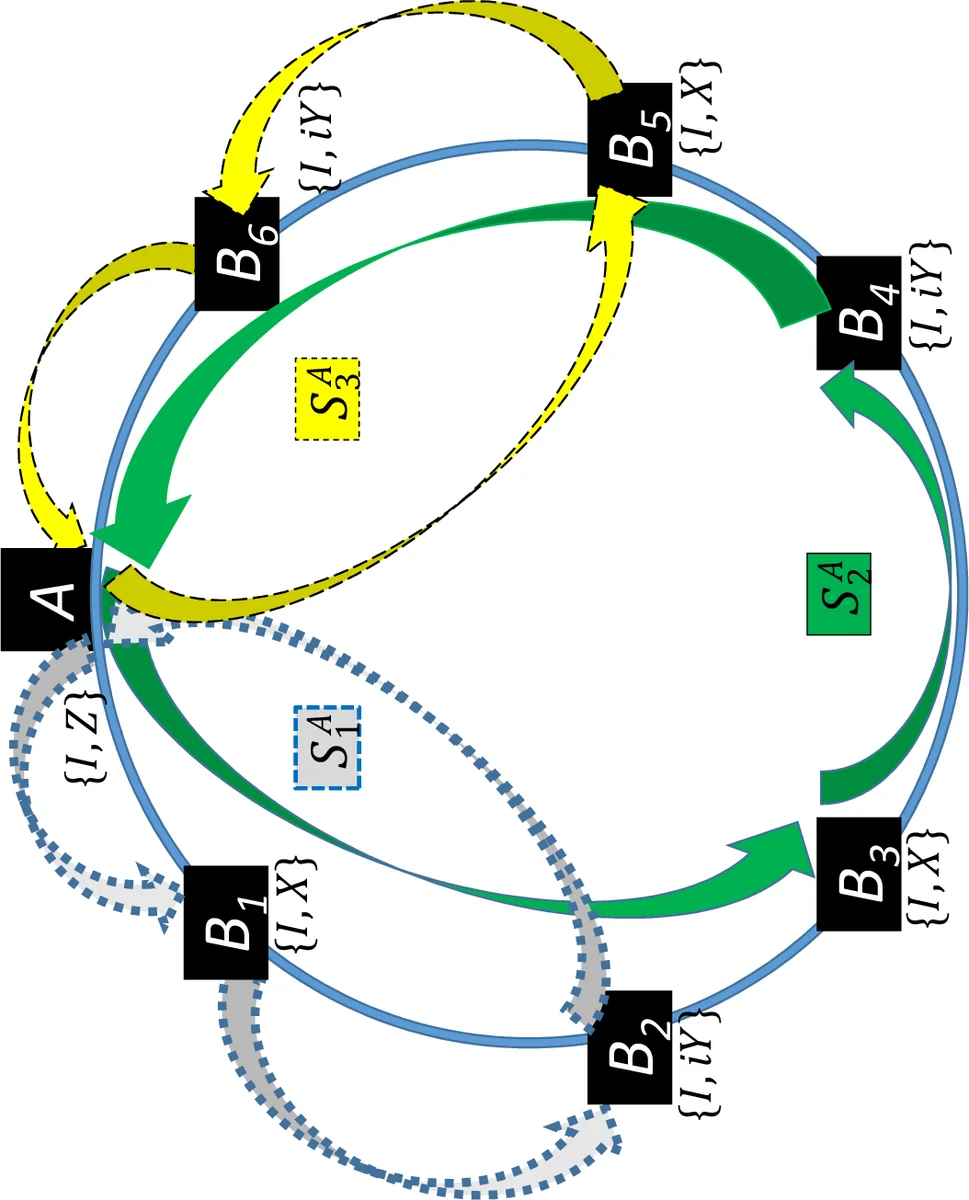
A feasible, secure and collusion-attack-free quantum sealed-bid auction protocol is proposed using a modified scheme for multi-party circular quantum key agreement. In the proposed protocol, the set of all ($n$) bidders is grouped in to $l$ subsets (sub-circles) in such a way that only the initiator (who prepares the quantum state to be distributed for a particular round of communication and acts as the receiver in that round) is a member of all the subsets (sub-circles) prepared for a particular round, while any other bidder is part of only a single subset. All $n$ bidders and auctioneer initiate one round of communication, and each of them prepares $l$ copies of a $\left(r-1\right)$-partite entangled state (one for each sub-circle), where $r=\frac{n}{l}+1$. The efficiency and security\textcolor{blue}{{} }of the proposed protocol are critically analyzed. It is shown that the proposed protocol is free from the collusion attacks that are possible on the existing schemes of quantum sealed-bid auction. Further, it is observed that the security against collusion attack increases with the increase in $l$, but that reduces the complexity (number of entangled qubits in each entangled state) of the entangled states to be used and that makes the scheme scalable and implementable with the available technologies. The additional security and scalability is shown to arise due to the use of a circular structure in place of a complete-graph or tree-type structure used earlier.
💡 Research Summary
**
The paper addresses the problem of designing a quantum sealed‑bid auction that is both practically implementable and resistant to collusion attacks. Classical sealed‑bid (Vickrey) auctions require the confidentiality of each bidder’s value until the winner is announced, a requirement that can be met with unconditional security only by quantum cryptographic techniques. Existing quantum auction protocols, however, suffer from structural weaknesses: tree‑type schemes place the auctioneer at the root, allowing a colluding auctioneer and bidder to manipulate the outcome; complete‑graph schemes require every participant to exchange quantum information with all others, leading to scalability, resource, and security issues (e.g., multi‑party collusion and measurement‑based eavesdropping).
To overcome these limitations, the authors propose a protocol based on a circular multi‑party quantum key agreement (CMQKA) that has been modified to eliminate participant attacks. The main idea is to arrange the auctioneer and all bidders on a circle and then partition this circle into l sub‑circles (or sub‑circuits). Each sub‑circle contains r = n/l + 1 parties, where n is the number of bidders; the auctioneer belongs to every sub‑circle, while each bidder belongs to exactly one sub‑circle. For each sub‑circle, every participant prepares an (r‑1)‑partite entangled state (e.g., GHZ‑type) and splits it into a travel qubit sequence (t_i) and a home qubit sequence (h_i).
The protocol proceeds in seven steps:
- Circle partitioning – the auctioneer defines the l sub‑circles; each bidder independently defines his own set of sub‑circles, always keeping himself in all circles he creates.
- State preparation – the auctioneer and each bidder generate l copies of an (r‑1)‑qubit entangled state and separate travel/home qubits.
- Distribution of travel qubits – travel sequences are sent to the first member of each sub‑circle after inserting a random set of decoy qubits for eavesdropping detection.
- Eavesdropping check – sender and receiver compare measurement results on decoys; if the error rate exceeds a threshold, the protocol aborts.
- Encoding of bids – each participant encodes his bid bits on the received travel qubits using a disjoint subgroup {I, U_i} of unitary operators (the subgroups intersect only at the identity). This ensures that no two participants use the same encoding operation, preserving a bijective mapping between the set of applied unitaries and the final entangled state.
- Iterative forwarding – after encoding, the enlarged sequence (including fresh decoys) is forwarded to the next party in the sub‑circle. The same eavesdropping check and encoding are repeated until the last party returns the sequence to the original preparer.
- Measurement and bid extraction – each participant now possesses both the home qubits and the final travel qubits of the states he prepared. By measuring in the original entangled basis, the combined effect of all applied unitaries is revealed, allowing the exact reconstruction of every bidder’s binary bid. The auctioneer announces the highest bid; all bidders can verify the result.
Security analysis focuses on three attack families:
- Auctioneer‑collusion – because the auctioneer is the only party present in all sub‑circles, a colluding bidder cannot gain information about bids that belong to other sub‑circles. The circular flow ensures that a bid must travel through parties that are not under the colluding pair’s control before reaching the auctioneer.
- Participant collusion – the use of mutually disjoint unitary subgroups prevents two bidders from applying the same operation, which would otherwise create ambiguity and enable a joint measurement to extract another’s bid.
- External eavesdropping – decoy‑qubit insertion and standard BB84‑type error checking guarantee unconditional security against intercept‑resend or measurement attacks.
The protocol’s efficiency stems from the fact that each entangled state involves only (r‑1) qubits, which can be made small by increasing l. Larger l also raises collusion resistance, while smaller l reduces the number of required entangled states, offering a tunable trade‑off between security and experimental complexity. Compared with tree‑type and complete‑graph schemes, the circular design reduces the number of quantum channels each participant must maintain (only two neighbours) and lowers memory requirements, making the scheme more amenable to current quantum‑optical technology.
The authors also demonstrate that the proposed framework generalizes existing structures: setting l = n yields a complete‑graph configuration (every bidder exchanges information with every other), while l = 1 collapses to a tree‑type configuration (only the auctioneer distributes and collects bids). Thus, the protocol provides a unified platform that can be adapted to various network topologies and scalability requirements.
In conclusion, the paper presents a scalable, collusion‑attack‑free quantum sealed‑bid auction that leverages a modified circular multi‑party key agreement. By carefully partitioning participants into sub‑circles, employing disjoint unitary encoding, and integrating decoy‑based eavesdropping detection, the scheme achieves unconditional security while demanding fewer entangled qubits than prior proposals. The flexibility of the l‑parameter and the compatibility with existing quantum communication hardware suggest that the protocol is a promising candidate for real‑world quantum‑enhanced auction systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment