Secure and Privacy- Aware Searching in Peer-to-Peer Networks
The existing peer-to-peer networks have several problems such as fake content distribution, free riding, white-washing and poor search scalability, lack of a robust trust model and absence of user privacy protection mechanism. Although, several trust management and semantic community-based mechanisms for combating free riding and distribution of malicious contents have been proposed by some researchers, most of these schemes lack scalability due to their high computational, communication and storage overhead. This paper presents a robust trust management scheme for P2P networks that utilizes topology adaptation by constructing an overlay of trusted peers where the neighbors are selected based on their trust ratings and content similarities. While increasing the search efficiency by intelligently exploiting the formation of semantic community structures by topology adaptation among the trustworthy peers, the scheme provides the users a very high level of privacy protection of their usage and consumption patterns of network resources. Simulation results demonstrate that the proposed scheme provides efficient searching to good peers while penalizing the malicious peers by increasing their search times as the network topology stabilizes.
💡 Research Summary
The paper addresses several critical shortcomings of existing peer‑to‑peer (P2P) file‑sharing systems, namely the distribution of fake content, free‑riding, white‑washing, poor search scalability, lack of a robust trust model, and the absence of user privacy protection. While prior work has introduced trust‑aware routing (e.g., P‑walk) and topology‑adaptation schemes (APT, RC‑ATP), these solutions either target structured networks, incur high communication/computation overhead, or fail to protect user identity.
The authors propose a comprehensive solution that combines a robust trust management engine with topology adaptation that creates semantic communities, while simultaneously preserving user privacy. Trust is modeled using a Beta distribution: each peer i records the number of successful (αij) and unsuccessful (βij) transactions with peer j. The expected trust value Eij = (αij+1)/(αij+βij+2) is used as a scalar reputation. In addition to first‑hand observations, second‑hand recommendations from neighbors are incorporated via Dempster‑Shafer theory and a belief‑discounting model, giving more weight to recent interactions. A peer is considered trustworthy if its trust exceeds 0.5, otherwise it is treated as malicious.
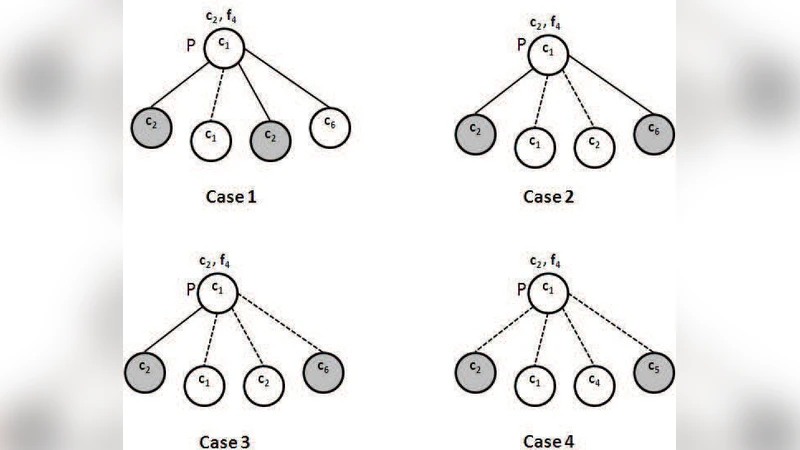
The underlying network is initially a power‑law graph (typical of unstructured P2P overlays). Two kinds of edges are distinguished: connectivity links, which are the original graph edges and are never removed (preventing network partitioning), and community links, which are added probabilistically between peers that share high trust and similar content categories. A per‑node limit (edge_limit) caps the number of additional community links to control bandwidth and query‑processing overhead. This dynamic edge addition/deletion naturally yields semantic clusters where most queries are resolved locally, dramatically reducing search hops.
Privacy protection is achieved by assigning each peer a 1024‑bit RSA key pair; the public key serves as a persistent identifier. A distributed hash table (DHT) stores transient IP/port information, signed with the peer’s private key and encrypted with its public key. DHT entries are indexed by a 20‑byte random secret agreed upon during the first successful connection, making the mapping independent of the peer’s static identity and thwarting systematic monitoring of specific key‑space regions.
The authors evaluate the scheme using simulations on a 10,000‑node power‑law network with 32 content categories following a Zipf distribution (α = 0.8). Query generation follows a Poisson process per peer, and 10 % of peers are designated malicious. Two threat models are considered: (A) malicious peers occasionally provide good files to gain trust before injecting fake content, and (B) a coalition of malicious peers first builds up connections up to the edge limit with good files, then launches a large‑scale poisoning attack.
Results show that trustworthy peers experience a reduction in average search rounds from 3.2 to 2.1 and an increase in successful download probability from 92 % to 96 %. Malicious peers suffer a rise in average search rounds to 7.8 and a drop in success rate below 30 %. Message overhead is reduced by roughly 35 % compared with P‑walk, and each node stores only a small set of Beta parameters (≈12) for its neighbors. The system also demonstrates resilience to churn: when 10 % of nodes randomly become inactive each generation, the community structure and trust tables recover within five search cycles.
Compared with APT and RC‑ATP, the proposed approach avoids link deletion (preventing fragmentation), employs a richer trust model that fuses second‑hand recommendations, and leverages semantic communities to improve QoS without resorting to flooding. Moreover, the privacy layer (RSA‑based IDs and encrypted DHT entries) provides strong anonymity absent in prior work.
The paper concludes that integrating trust‑driven topology adaptation, semantic community formation, and cryptographic privacy safeguards yields a scalable, secure, and privacy‑preserving P2P search mechanism. Future work is suggested in areas such as bootstrapping trust for newcomers, dynamic tuning of edge_limit, lightweight alternatives to Dempster‑Shafer for real‑time environments, and prototype deployment on actual file‑sharing platforms, possibly augmented with blockchain‑based immutable reputation records.
Comments & Academic Discussion
Loading comments...
Leave a Comment