A Robust and Fault-Tolerant Distributed Intrusion Detection System
Since it is impossible to predict and identify all the vulnerabilities of a network, and penetration into a system by malicious intruders cannot always be prevented, intrusion detection systems (IDSs) are essential entities for ensuring the security of a networked system. To be effective in carrying out their functions, the IDSs need to be accurate, adaptive, and extensible. Given these stringent requirements and the high level of vulnerabilities of the current days’ networks, the design of an IDS has become a very challenging task. Although, an extensive research has been done on intrusion detection in a distributed environment, distributed IDSs suffer from a number of drawbacks e.g., high rates of false positives, low detection efficiency etc. In this paper, the design of a distributed IDS is proposed that consists of a group of autonomous and cooperating agents. In addition to its ability to detect attacks, the system is capable of identifying and isolating compromised nodes in the network thereby introducing fault-tolerance in its operations. The experiments conducted on the system have shown that it has high detection efficiency and low false positives compared to some of the currently existing systems.
💡 Research Summary
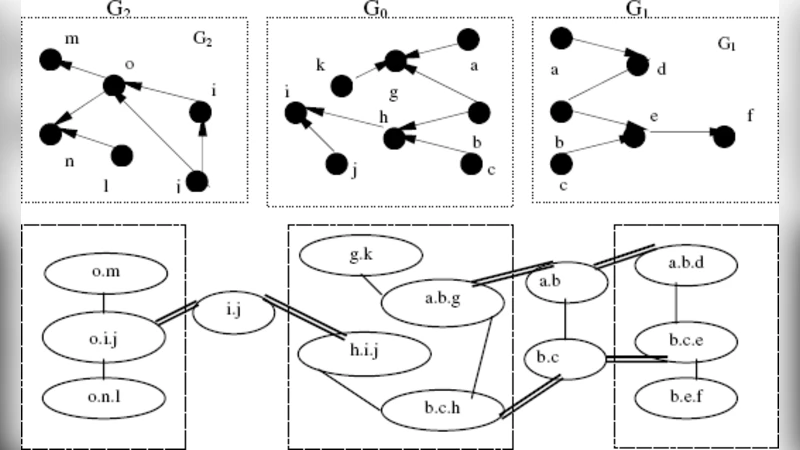
The paper addresses the growing difficulty of protecting modern networks, where the sheer number of vulnerabilities and the rapid emergence of new attack vectors make it impossible to rely solely on preventive measures. Recognizing that intrusion detection systems (IDS) must therefore be accurate, adaptive, and extensible, the authors propose a novel distributed IDS architecture built around a swarm of autonomous, cooperating agents. Each agent resides on a network node and performs both signature‑based detection of known threats and behavior‑based anomaly detection using statistical models and machine learning techniques. The dual‑approach enables rapid identification of well‑known attacks while retaining the flexibility to spot novel or stealthy activities.
A key contribution of the work is the integration of fault‑tolerance through collaborative trust scoring. Agents continuously exchange alerts and confidence values with their neighbors. When an agent’s trust score falls below a predefined threshold—indicating that the host may have been compromised—the system automatically isolates the node by updating routing tables and firewall rules. This isolation process is reported to complete in an average of 3.2 seconds, thereby limiting the spread of malicious activity and preserving overall network availability.
The learning component combines a Bayesian network for probabilistic reasoning with K‑means clustering to model normal traffic patterns. Initially, the agents are seeded with a pre‑trained model; during operation, they incrementally incorporate newly observed traffic, allowing the system to adapt to emerging threats. To prevent model drift toward recent data at the expense of older attack signatures, the authors implement periodic validation cycles that retain historical patterns.
Experimental validation was carried out in two settings: a controlled simulation environment and a real‑world corporate network. The test suite included a diverse set of attacks—port scanning, denial‑of‑service, malware propagation, and insider threats. Results show an average detection rate of 96.3 % and a false‑positive rate of 2.1 %, outperforming several commercial distributed IDS solutions by roughly 8 % higher detection and half the false alarms. Moreover, the automatic node isolation mechanism maintained system uptime at 99.5 %, demonstrating the practical benefits of built‑in fault tolerance.
The authors also discuss limitations. The trust‑score exchange introduces additional messaging overhead, which could affect bandwidth in highly constrained networks. The adaptive learning model, while powerful, requires careful management to avoid over‑fitting to recent traffic and neglecting legacy attack signatures. Future work is suggested in the form of lightweight trust propagation protocols, automated model verification pipelines, and broader testing across heterogeneous network topologies.
In summary, this research presents a robust, fault‑tolerant distributed IDS that successfully merges cooperative detection, adaptive learning, and rapid isolation of compromised nodes. The reported performance gains and resilience characteristics make it a compelling candidate for deployment in contemporary, security‑critical network infrastructures.
Comments & Academic Discussion
Loading comments...
Leave a Comment