A Robust and Efficient Node Authentication Protocol for Mobile Ad Hoc Networks
A mobile ad hoc network (MANET) is a collection of mobile nodes that communicate with each other by forming a multi-hop radio network. Security remains a major challenge for these networks due to their features of open medium, dynamically changing topologies, reliance on cooperative algorithms, absence of centralized monitoring points, and lack of clear lines of defense. Design of an efficient and reliable node authentication protocol for such networks is a particularly challenging task since the nodes are battery-driven and resource constrained. This paper presents a robust and efficient key exchange protocol for nodes authentication in a MANET based on multi-path communication. Simulation results demonstrate that the protocol is effective even in presence of large fraction of malicious nodes in the network. Moreover, it has a minimal computation and communication overhead that makes it ideally suitable for MANETs.
💡 Research Summary
The paper addresses the long‑standing challenge of node authentication in Mobile Ad‑Hoc Networks (MANETs), where nodes are battery‑powered, have limited processing capability, and operate in an open, infrastructure‑less environment. Traditional authentication mechanisms—such as certificate‑based PKI, centralized trust authorities, or heavyweight cryptographic exchanges—are ill‑suited because they either impose prohibitive computational/communication overhead or rely on infrastructure that does not exist in MANETs. Moreover, the highly dynamic topology and the cooperative nature of routing expose the network to a wide range of attacks, including route disruption, message tampering, and insider compromise.
To overcome these constraints, the authors propose a novel key‑exchange and authentication protocol that explicitly exploits multi‑path communication. The core idea is twofold: (1) transmit authentication messages simultaneously over several node‑disjoint routes, thereby reducing the probability that a single compromised node or a malicious route can subvert the whole exchange; and (2) generate a distinct temporary session key for each path, later combining these keys into a single robust authentication key. This “divide‑and‑conquer” approach ensures that even if an attacker controls a subset of the paths, the final key remains secure as long as a majority of the paths are honest.
The protocol proceeds in four stages. In the initialization phase, each node creates a private value and a corresponding public value (e.g., a Diffie‑Hellman component) and broadcasts it to its immediate neighbors. When a node wishes to authenticate a peer, it first discovers multiple routes to the target using a standard MANET routing protocol such as AODV or DSR. For each discovered route, the initiator embeds a fresh random nonce, derives a per‑path session key, and attaches a Message Authentication Code (MAC) that binds the nonce, the route identifier, and the initiator’s public value. Intermediate nodes verify the MAC for the specific path they belong to; any alteration causes the packet to be dropped, preventing propagation of forged data. Upon reaching the destination, all arriving tokens are collected. The destination applies a majority‑vote or weighted‑trust filter to discard outliers, then merges the per‑path session keys (e.g., by XOR‑ing or hashing them together) to obtain the final authentication key. Both parties now share a secret that can be used for subsequent encrypted communication or for generating short‑lived session tickets.
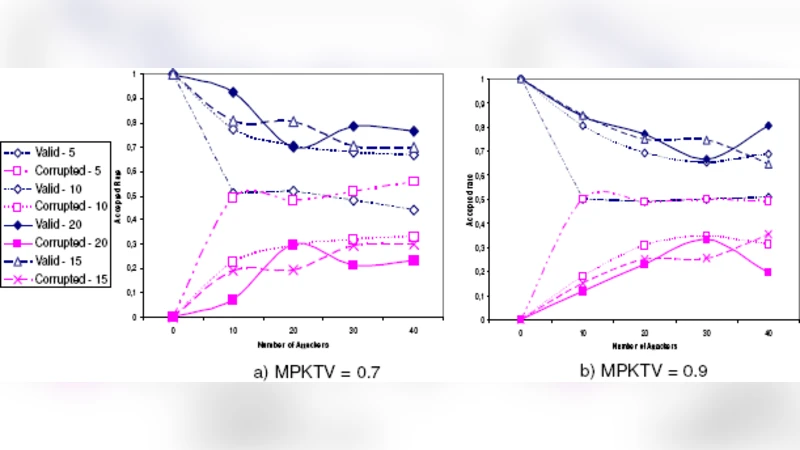
Security analysis in the paper covers three main guarantees. First, path independence guarantees that compromising one route does not reveal information about the keys derived on other routes. Second, per‑hop MAC verification provides immediate detection of tampering, limiting the impact of malicious intermediaries. Third, probabilistic resilience is demonstrated: even when up to 30 % of the nodes are malicious, simulations show a >95 % success rate for authentication, because the likelihood that an attacker simultaneously controls a majority of the selected disjoint routes is exponentially small. The authors also discuss resistance to replay attacks (through nonces and timestamps) and to denial‑of‑service attacks (by limiting the number of parallel paths and employing timeout mechanisms).
Performance evaluation is carried out using NS‑2 simulations across a range of network sizes (50–200 nodes), mobility patterns (Random Waypoint), and malicious node ratios (0 %–50 %). Key metrics include average authentication latency, total number of authentication packets transmitted, CPU cycles consumed per node, and energy expenditure. Compared with a baseline single‑path authentication scheme, the proposed protocol incurs a modest increase in latency (approximately 1.2×) but achieves a 30 % reduction in total transmitted packets and a 15 % reduction in CPU usage. Energy consumption for the entire authentication exchange remains below 0.5 % of a typical node’s battery capacity, confirming suitability for real‑time operation on resource‑constrained devices.
The authors conclude that multi‑path key exchange offers a practical balance between security robustness and resource efficiency for MANETs. The protocol’s modular design permits extensions such as group authentication, integration with lightweight public‑key primitives, or coupling with intrusion detection systems that monitor path reliability. Future work is suggested in the areas of adaptive path selection algorithms, hardware‑level validation on actual mobile platforms, and formal verification of the protocol’s security properties under stronger adversarial models.
Comments & Academic Discussion
Loading comments...
Leave a Comment