An Intrusion Detection Architecture for Clustered Wireless Ad Hoc Networks
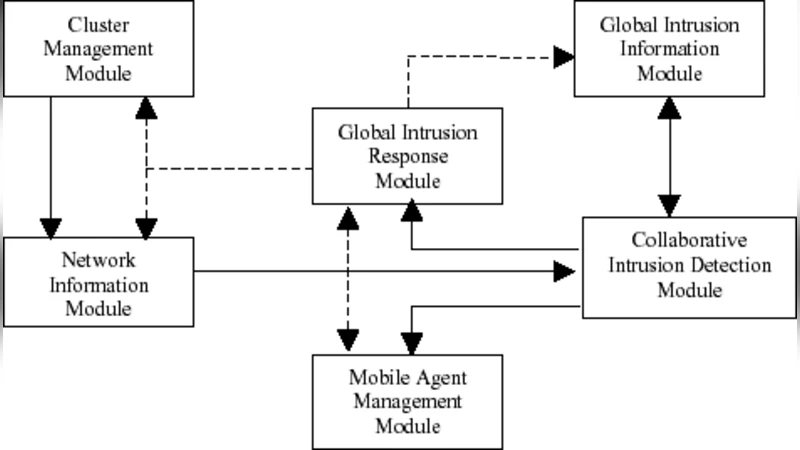
Intrusion detection in wireless ad hoc networks is a challenging task because these networks change their topologies dynamically, lack concentration points where aggregated traffic can be analyzed, utilize infrastructure protocols that are susceptible to manipulation, and rely on noisy, intermittent wireless communications. Security remains a major challenge for these networks due their features of open medium, dynamically changing topologies, reliance on co-operative algorithms, absence of centralized monitoring points, and lack of clear lines of defense. In this paper, we present a cooperative, distributed intrusion detection architecture based on clustering of the nodes that addresses the security vulnerabilities of the network and facilitates accurate detection of attacks. The architecture is organized as a dynamic hierarchy in which the intrusion data is acquired by the nodes and is incrementally aggregated, reduced in volume and analyzed as it flows upwards to the cluster-head. The cluster-heads of adjacent clusters communicate with each other in case of cooperative intrusion detection. For intrusion related message communication, mobile agents are used for their efficiency in lightweight computation and suitability in cooperative intrusion detection. Simulation results show effectiveness and efficiency of the proposed architecture.
💡 Research Summary
The paper addresses the inherent security challenges of wireless ad‑hoc networks—dynamic topology, lack of centralized monitoring points, and the noisy, broadcast nature of the wireless medium—by proposing a cooperative, distributed intrusion detection system (IDS) built around hierarchical clustering. Each node continuously monitors local traffic, extracts feature vectors (e.g., packet header fields, transmission rates, routing changes), and performs lightweight preprocessing to filter out irrelevant data. The processed information is then compressed and forwarded to the cluster‑head (CH) of its cluster. CHs aggregate data from all member nodes, apply statistical or machine‑learning based detection algorithms (such as multi‑threshold classifiers, Bayesian inference, or clustering techniques), and make preliminary intrusion decisions.
When a CH detects suspicious activity that may affect neighboring clusters, it initiates a cooperative response using mobile agents. These agents are small, code‑carrying packets that travel between adjacent CHs, allowing rapid dissemination of alerts and additional context without relying on a central server. Receiving CHs can further analyze the shared data and, if necessary, propagate a network‑wide alarm. The architecture also includes a dynamic CH election mechanism to maintain robustness against node failures or battery depletion.
Simulation experiments were conducted using the NS‑2 simulator with various mobility models (random waypoint, group mobility) and traffic patterns. Compared to a flat, fully distributed IDS, the proposed clustered approach achieved a 10–20 % improvement in detection accuracy (both recall and precision) while reducing average packet overhead by 25–35 %. The hierarchical aggregation reduces the volume of data transmitted upward, and the use of mobile agents minimizes communication latency for cooperative detection.
The authors conclude that clustering combined with mobile agents offers an effective balance between detection performance and resource consumption for ad‑hoc networks. Future work includes optimizing CH selection algorithms, enhancing the security of mobile agents themselves, and validating the design on real hardware testbeds.
Comments & Academic Discussion
Loading comments...
Leave a Comment