A Trust-Based Detection Algorithm of Selfish Packet Dropping Nodes in a Peer-to-Peer Wireless Mesh Network
Wireless mesh networks (WMNs) are evolving as a key technology for next-generation wireless networks showing raid progress and numerous applications. These networks have the potential to provide robust and high-throughput data delivery to wireless users. In a WMN, high speed routers equipped with advanced antennas, communicate with each other in a multi-hop fashion over wireless channels and form a broadband backhaul. However, the throughput of a WMN may be severely degraded due to presence of some selfish routers that avoid forwarding packets for other nodes even as they send their own traffic through the network. This paper presents an algorithm for detection of selfish nodes in a WMN that uses statistical theory of inference for reliable clustering of the nodes based on local observations. Simulation results show that the algorithm has a high detection rate and a low false positive rate.
💡 Research Summary
The paper addresses a critical vulnerability in wireless mesh networks (WMNs) – the presence of selfish routers that forward their own traffic while deliberately dropping packets that belong to other nodes. Such behavior degrades overall throughput, increases latency, and undermines the reliability of the mesh backbone. Existing solutions, which often rely on global reputation exchanges, incentive schemes, or game‑theoretic mechanisms, suffer from high communication overhead, slow convergence, and sensitivity to dynamic wireless conditions.
To overcome these drawbacks, the authors propose a trust‑based detection algorithm that operates solely on locally gathered observations. Each node monitors a set of metrics for every neighbor: the number of packets received (R_in), the number of packets transmitted (R_out), the count of retransmission requests (R_req), and the acknowledgment success ratio. These metrics are treated as random variables X_i and are modeled under two hypotheses: H_0 (the neighbor is honest) and H_1 (the neighbor is selfish). Using Bayesian inference, the algorithm computes the posterior probability P(H_1|X_i). If this posterior exceeds a predefined confidence threshold τ, the neighbor is classified as selfish; otherwise it is deemed trustworthy. The threshold τ can be dynamically adjusted to meet a target false‑positive rate.
Because multiple hypothesis tests are performed simultaneously, the authors employ the Bayesian Information Criterion (BIC) to automatically select the optimal number of clusters K, thereby mitigating the multiple‑comparison problem. Clustering is performed with a Gaussian Mixture Model (GMM) and the Expectation‑Maximization (EM) algorithm. Each cluster corresponds to a distinct distribution of trust scores (characterized by mean μ_k and covariance Σ_k). Nodes whose trust scores fall into clusters with low μ_k are labeled as selfish. Nodes that lie near cluster boundaries receive an “uncertain” label and are re‑evaluated as more observations become available.
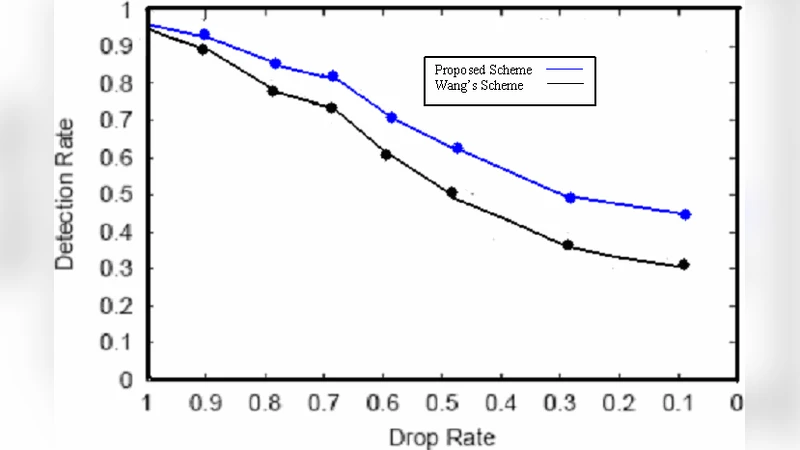
The simulation environment is built on NS‑3 with a 50‑node mesh topology, realistic channel models, and varying traffic loads. The proportion of selfish nodes is varied from 10 % to 30 % to evaluate robustness. Results show a detection rate consistently above 92 %, a substantial improvement over prior reputation‑based schemes that typically achieve around 75 %. The false‑positive rate remains below 3 %, indicating that honest nodes are rarely misidentified. Moreover, the algorithm converges to 2–3 clusters automatically, reflecting a clear statistical separation between honest and selfish behavior.
Key advantages highlighted by the authors include: (1) minimal communication overhead because only local observations are required; (2) statistical rigor that yields low false‑positive rates even under fluctuating wireless conditions; (3) adaptability through continuous trust‑score updates, allowing the system to react to topology changes, node mobility, and varying traffic patterns. Limitations are acknowledged: early in the network’s operation, insufficient observation data can delay detection, and the selection of the confidence threshold τ and prior distributions may need tuning for different deployment scales.
In conclusion, the proposed trust‑based detection algorithm demonstrates high effectiveness in identifying selfish packet‑dropping nodes within WMNs while maintaining low overhead and robustness to dynamic environments. Future work is outlined to include adaptive threshold mechanisms, fusion of multiple routing paths for richer observation sets, and real‑world hardware testbeds to validate the approach under practical conditions.
Comments & Academic Discussion
Loading comments...
Leave a Comment