A Robust and Efficient Trust Management Scheme for Peer-to-Peer Networks
Studies on the large scale peer-to-peer (P2P) network like Gnutella have shown the presence of large number of free riders. Moreover, the open and decentralized nature of P2P network is exploited by malicious users who distribute unauthentic or harmful contents. Despite the existence of a number of trust management schemes in the literature for combating against free riding and distribution of malicious files, these mechanisms are not scalable due to their high computational, communication and storage overhead. These schemes also do not consider effect of trust management on quality-of-service (QoS) of the search. This paper presents a trust management scheme for P2P networks that minimizes distribution of spurious files by a novel technique called topology adaptation. It also reduces search time since most of the queries are resolved within the community of trustworthy peers. Simulation results indicate that the trust management overhead due to the pr oposed mechanism decreases considerably as the network topology stabilizes. The mechanism is also found to be robust even in presence of a large percentage of malicious peers.
💡 Research Summary
The paper addresses two pervasive problems in large‑scale unstructured peer‑to‑peer (P2P) file‑sharing systems such as Gnutella: the presence of free riders who consume resources without contributing, and the distribution of malicious or fake files by adversarial peers. Existing trust‑management schemes mitigate these issues but suffer from high computational, communication, and storage overhead, making them unsuitable for scalable deployments and often ignoring the impact on search quality (QoS). To overcome these limitations, the authors propose a novel trust‑aware topology‑adaptation framework that simultaneously improves security, reduces search latency, and limits overhead.
Trust Management Module
Each peer maintains a Least‑Recently‑Used (LRU) cache of its most recent 32 transactions. When a file is downloaded, the transaction is rated +1 for authentic files and –1 for fake files. The fraction of successful downloads from peer j to peer i (Sij) is computed as the ratio of positive ratings to total interactions. A threshold of 0.5 classifies peers as trustworthy (Sij > 0.5), malicious (Sij < 0.5), or neutral (0.5 ≥ Sij ≥ 0.0). For neutral peers, i solicits recommendations from other peers, thereby leveraging collective experience without incurring excessive messaging.
Topology Adaptation
The underlying network is generated using the Barabási‑Albert model, yielding a power‑law degree distribution (6 000 nodes, ≈ 18 000 edges). Two types of edges exist: connectivity links (the original graph) and community links (added between peers that trust each other). To bound bandwidth consumption, each peer may add community links only up to a relative increase in degree (RIC) of 0.3 (edge_limit). A rewiring probability (0.3) governs the creation of new community links and the removal of links to malicious peers. When a peer i receives a genuine file from peer j, and both satisfy the edge_limit condition, a bidirectional community link is formed after j’s approval. Conversely, if i discovers that j supplied a fake file, i deletes the community link. This dynamic rewiring gradually clusters trustworthy peers together while isolating malicious nodes.
Search Procedure
Initially, queries are propagated using a TTL‑limited breadth‑first search (BFS) with TTL = 5. As the network stabilizes and community links dominate, the algorithm switches to a directed depth‑first search (DFS) with TTL = 10. Each query packet carries the file identifier (category c, rank r), the current TTL, and the node’s Prob_com (probability of community formation), computed from the node’s degree and edge_limit. When forwarding, a peer ranks its neighbors by (1) trustworthiness, (2) similarity of interest (same content category), and (3) presence of the requested file in its local repository. Queries are first sent to trusted community neighbors; only when insufficient community links exist are connectivity links used. Upon receipt, a peer checks the sender’s trust rating; if the sender is deemed malicious, the query is dropped. If the file is found, a response is sent back; otherwise, the query continues until TTL expires.
Performance Evaluation
The authors evaluate the scheme using a discrete‑event simulator written in C. The simulation parameters include: 6 000 peers, 32 content categories, Zipf‑distributed file popularity (α = 0.8), Poisson‑distributed query generation, edge_limit = 0.3, and rewiring degree = 0.3. Three metrics are measured:
- Attempt Ratio (AR) – probability that the first download attempt yields an authentic file.
- Effective Attempt Ratio (EAR) – comparative measure of AR between good and malicious peers.
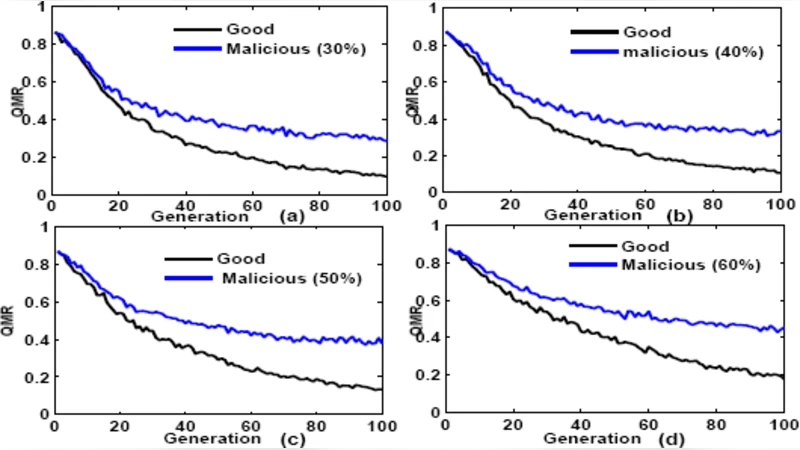
- Query Miss Ratio (QMR) – proportion of queries that fail to locate the requested file.
Results show that with 10 % malicious peers, EAR for good peers reaches ≈ 80 % and remains above 70 % even when the malicious fraction rises to 60 %. QMR for good peers drops below 0.2 after a few generations as community links become dominant, whereas malicious peers experience higher QMR because their queries are frequently blocked. The overhead of trust management (storage of LRU caches, computation of Sij, and occasional recommendation exchanges) diminishes as the topology stabilizes, confirming the scheme’s scalability.
Conclusions
The proposed trust‑aware topology‑adaptation algorithm effectively curtails free‑riding and malicious file distribution while maintaining low overhead and high search efficiency. By continuously reshaping the overlay based on observed trust, the system isolates adversarial nodes and creates high‑quality search paths among trustworthy peers. The simulation validates robustness under varying malicious peer ratios and demonstrates that the approach scales to thousands of nodes. Future work may explore defenses against white‑washing (peers leaving and rejoining to reset trust), integration with incentive mechanisms, and real‑world deployment on existing P2P clients.
Comments & Academic Discussion
Loading comments...
Leave a Comment