A Formal Approach to Physics-Based Attacks in Cyber-Physical Systems (Extended Version)
We apply formal methods to lay and streamline theoretical foundations to reason about Cyber-Physical Systems (CPSs) and physics-based attacks, i.e., attacks targeting physical devices. We focus on a formal treatment of both integrity and denial of service attacks to sensors and actuators of CPSs, and on the timing aspects of these attacks. Our contributions are fourfold. (1)~We define a hybrid process calculus to model both CPSs and physics-based attacks. (2)~We formalise a threat model that specifies MITM attacks that can manipulate sensor readings or control commands in order to drive a CPS into an undesired state, and we provide the means to assess attack tolerance/vulnerability with respect to a given attack. (3)~We formalise how to estimate the impact of a successful attack on a CPS and investigate possible quantifications of the success chances of an attack. (4)~We illustrate our definitions and results by formalising a non-trivial running example in Uppaal SMC, the statistical extension of the Uppaal model checker; we use Uppaal SMC as an automatic tool for carrying out a static security analysis of our running example in isolation and when exposed to three different physics-based attacks with different impacts.
💡 Research Summary
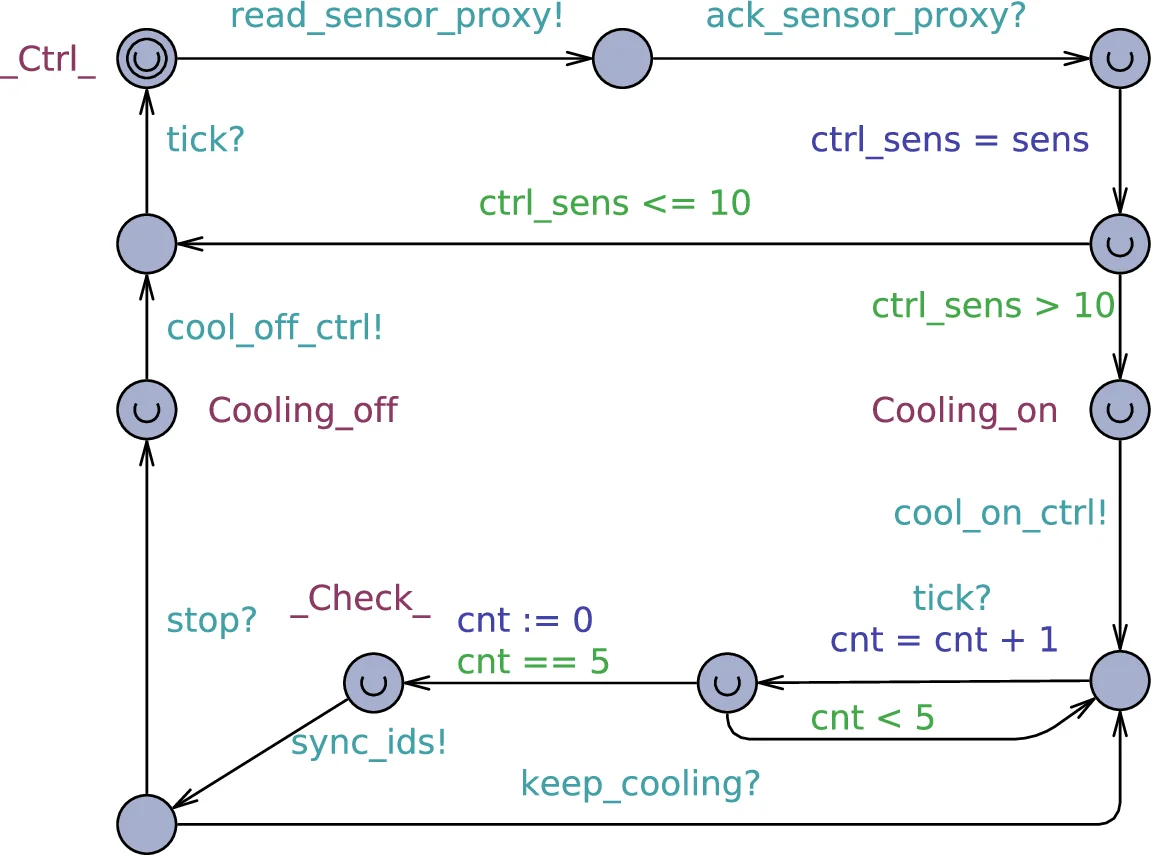
The paper addresses a gap in cyber‑physical system (CPS) security research: the lack of a systematic, formal treatment of attacks that directly target physical devices such as sensors and actuators. To fill this gap, the authors introduce a new hybrid process calculus called CCPSA (Calculus of Cyber‑Physical Systems and Attacks). CCPSA explicitly separates a CPS into a physical component (the plant) and a cyber component (the logical controller). The physical component is described by a state vector, a set of sensors, a set of actuators, and two maps: an evolution map that captures the plant’s dynamics (including actuator influence and uncertainty) and a measurement map that models sensor readings with error. The calculus adopts a discrete‑time labelled transition system (LTS) that can observe both physical events (deadlock, safety violations) and cyber events (channel communications).
Attacks are modelled as man‑in‑the‑middle (MITM) manipulations of sensor readings (y_k → y_a_k) or actuator commands (u_k → u_a_k). The authors define a set I of possible malicious actions on physical devices and a timing interval m..n during which the attack is active. An attack class C is a total function C ∈
Comments & Academic Discussion
Loading comments...
Leave a Comment