Discovering IoT Physical Channel Vulnerabilities
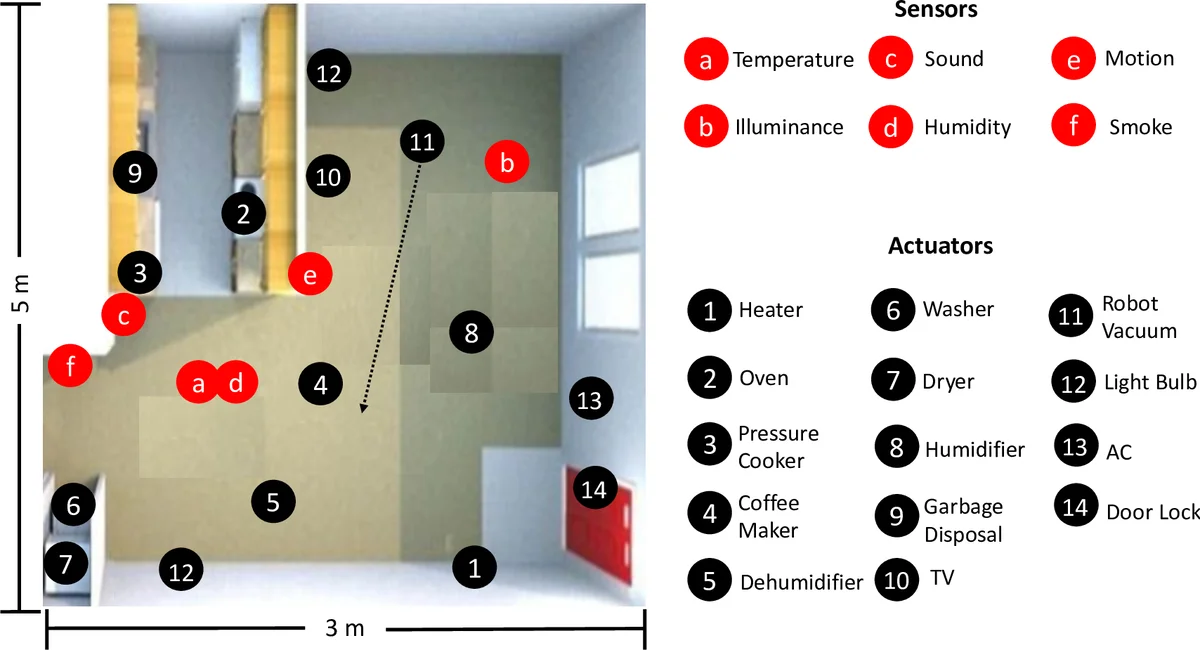
Smart homes contain diverse sensors and actuators controlled by IoT apps that provide custom automation. Prior works showed that an adversary could exploit physical interaction vulnerabilities among apps and put the users and environment at risk, e.g., to break into a house, an adversary turns on the heater to trigger an app that opens windows when the temperature exceeds a threshold. Currently, the safe behavior of physical interactions relies on either app code analysis or dynamic analysis of device states with manually derived policies by developers. However, existing works fail to achieve sufficient breadth and fidelity to translate the app code into their physical behavior or provide incomplete security policies, causing poor accuracy and false alarms. In this paper, we introduce a new approach, IoTSeer, which efficiently combines app code analysis and dynamic analysis with new security policies to discover physical interaction vulnerabilities. IoTSeer works by first translating sensor events and actuator commands of each app into a physical execution model (PeM) and unifying PeMs to express composite physical execution of apps (CPeM). CPeM allows us to deploy IoTSeer in different smart homes by defining its execution parameters with minimal data collection. IoTSeer supports new security policies with intended/unintended physical channel labels. It then efficiently checks them on the CPeM via falsification, which addresses the undecidability of verification due to the continuous and discrete behavior of IoT devices. We evaluate IoTSeer in an actual house with 14 actuators, six sensors, and 39 apps. IoTSeer discovers 16 unique policy violations, whereas prior works identify only 2 out of 16 with 18 falsely flagged violations. IoTSeer only requires 30 mins of data collection for each actuator to set the CPeM parameters and is adaptive to newly added, removed, and relocated devices.
💡 Research Summary
The paper introduces IoTSeer, a novel framework for discovering and preventing physical‑channel vulnerabilities in smart homes. Existing approaches either analyze app source code to find software‑level interactions or rely on manually crafted mappings and simple dynamic checks for physical interactions, leading to both over‑approximation (false positives) and under‑approximation (missed vulnerabilities). IoTSeer bridges this gap by first extracting sensor events and actuator commands from each app’s source code and translating them into a Physical Execution Model (PeM). A PeM captures how a specific command influences a physical channel (e.g., temperature) using a function f(X) that models both continuous and discrete dynamics. To calibrate the model, IoTSeer collects short traces (≈30 minutes per actuator) from the actual devices, ensuring that the parameters reflect real‑world behavior while keeping data‑collection overhead low.
Multiple PeMs are then unified into a Composite Physical Execution Model (CPeM), which represents the joint physical behavior of all interacting apps in a home. This unified model enables the definition of new security policies that label channels as “intended” or “unintended.” Policies are expressed in Metric Temporal Logic (MTL) and are checked against the CPeM using an optimization‑guided falsification technique. Falsification searches for command sequences that cause the model to violate a policy, effectively handling the undecidability of verification in hybrid (continuous‑discrete) IoT systems.
The authors evaluate IoTSeer in a real house equipped with 14 actuators, six sensors, and 39 apps from popular platforms. IoTSeer discovers 16 distinct policy violations, whereas prior state‑of‑the‑art methods identify only 2 of these and generate 18 false positives. Validation in the live environment confirms that all 16 violations are true positives. The framework adapts to device additions, removals, and relocations by re‑collecting traces for the affected devices, and policy checking averages 21 seconds per four‑app interaction, demonstrating practical scalability.
Key contributions include: (1) a systematic translation from app code to physical behavior models, (2) a compositional architecture (CPeM) for joint physical execution, (3) novel intended/unintended channel policies with formal MTL validation via falsification, (4) extensive real‑world evaluation showing high detection accuracy and low false‑alarm rates, and (5) an open‑source implementation. Limitations involve the need for modest trace collection and the abstraction of complex physical phenomena into simple functions, which the authors suggest addressing in future work through automated parameter learning and richer physical simulations.
Comments & Academic Discussion
Loading comments...
Leave a Comment