Distributed Ledger Technology for IoT: Parasite Chain Attacks
Directed Acyclic Graph (DAG) based Distributed Ledgers can be useful in a number of applications in the IoT domain. A distributed ledger should serve as an immutable and irreversible record of transactions, however, a DAG structure is a more complicated mathematical object than its blockchain counterparts, and as a result, providing guarantees of immutability and irreversibility is more involved. In this paper, we analyse a commonly discussed attack scenario known as a parasite chain attack for the IOTA Foundation DAG based ledger. We analyse the efficacy of IOTA core MCMC algorithm using a matrix model and present an extension which improves the ledger resistance to these attacks.
💡 Research Summary
The paper investigates the security of the IOTA Foundation’s DAG‑based distributed ledger, known as the Tangle, against a well‑known double‑spending strategy called the parasite‑chain attack. After a concise introduction that motivates the use of distributed ledgers for the Internet of Things (IoT) – emphasizing decentralisation, immutability, pseudo‑anonymity and lightweight cryptographic primitives – the authors describe the structural fundamentals of the Tangle. Each transaction (vertex) approves two previous transactions (edges) and carries a unit weight; the cumulative weight H(t) of a transaction is the sum of its own weight plus the number of vertices that directly or indirectly approve it. A tip is a vertex with no approvals, and tip selection is the core mechanism that determines how new transactions are attached to the graph.
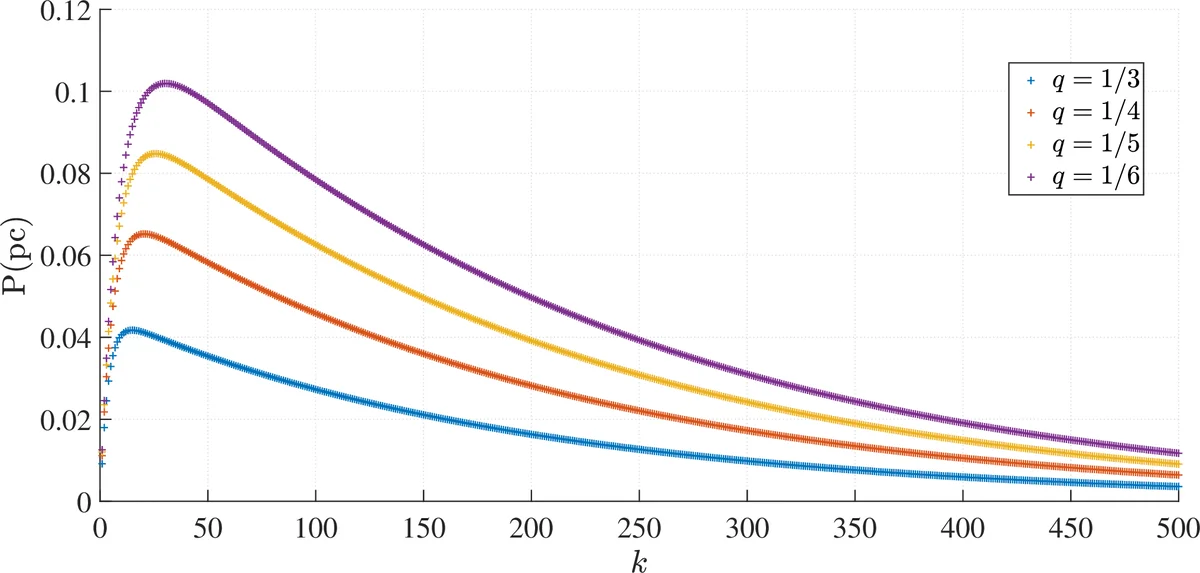
Three tip‑selection strategies are reviewed: (i) Uniform Random Tip Selection (URTS), which simply picks two tips uniformly at random and is trivially vulnerable; (ii) the Biased Random Walk (BRW) algorithm, also called the Monte‑Carlo Markov Chain (MCMC) tip selector, which launches two independent random walks from a deep point in the graph. The transition probability from vertex j to k is proportional to f(−α(Hj−Hk)), where f is a monotone increasing function (typically exponential) and α is a positive parameter that plays the role of an inverse temperature. Large α forces the walk toward high‑cumulative‑weight vertices, while small α makes the walk almost uniform. (iii) A hybrid approach that mixes a high‑α BRW for security with a low‑α or URTS component to guarantee eventual approval of all tips.
The parasite‑chain attack is then formalised. An adversary first issues a legitimate transaction (the “yellow” vertex) and, in secret, creates a conflicting transaction (the “green” vertex) followed by a chain that initially references the main Tangle for k steps and then diverges, forming a private sub‑graph. The attacker’s goal is to grow this sub‑graph until its cumulative weight overtakes that of the honest portion, thereby causing later honest transactions to approve the malicious tip and effectively reversing the original transaction.
To analyse the success probability, the authors model the BRW as an absorbing Markov chain. The state space consists of all vertices; absorbing states correspond to tips. Transition probabilities are derived from the α‑biased edge weights. The parasite chain is represented as a separate set of states that can be entered after the initial k honest references. By solving the fundamental matrix of the chain, the authors obtain closed‑form expressions for the probability that a random walk terminates on a malicious tip as a function of α and the attacker’s relative hash power β (the fraction of total computational power controlled by the adversary).
The analytical results reveal a clear trade‑off. When α is large (e.g., α ≥ 5), the walk strongly favours high‑weight tips, and an attacker needs a substantial share of the network’s hash power (≈30 % or more) to make the parasite chain competitive. Conversely, for small α (α ≤ 1) the walk behaves almost uniformly, and even a modest attacker (β ≈ 10 %) can achieve a non‑negligible success probability. Moreover, a fixed high α leads to “tip starvation”: some honest tips may never be selected, which harms liveness and throughput.
To mitigate both vulnerabilities, the paper proposes a dynamic α‑adjustment scheme that monitors the distribution of cumulative weights among current tips. If the weight gap between the heaviest and lightest tip falls below a threshold δ, the algorithm temporarily lowers α (or switches a fraction of walks to URTS) to ensure that all tips receive approvals. When the gap exceeds δ, α is raised to reinforce security. This hybrid, adaptive approach preserves the deterministic security benefits of a high‑α BRW while guaranteeing eventual tip approval.
Extensive simulations on synthetic Tangle graphs (1 k–5 k nodes) with varying attacker hash‑power ratios (10 %–40 %) confirm the theoretical predictions. The adaptive scheme reduces the parasite‑chain success probability by a factor of 2–3 compared with a static high‑α configuration, and the average tip‑approval latency increases by less than 15 %, effectively eliminating tip starvation.
In conclusion, the authors demonstrate that DAG‑based ledgers can indeed meet IoT requirements, but only if tip‑selection parameters are tuned adaptively rather than statically. The absorbing‑Markov‑chain framework provides a rigorous tool for quantifying attack success probabilities and can be extended to other DAG protocols (e.g., Hedera Hashgraph, Conflux) or to analyse different attack vectors such as eclipse or Sybil attacks. Future work includes integrating the proposed adaptive selector into the IOTA reference implementation, exploring VDF‑based proof‑of‑work alternatives, and applying the Markov‑chain analysis to multi‑token or sharded DAG architectures.
Comments & Academic Discussion
Loading comments...
Leave a Comment