Neural Network Cognitive Engine for Autonomous and Distributed Underlay Dynamic Spectrum Access
Two key challenges in underlay dynamic spectrum access (DSA) are how to establish an interference limit from the primary network (PN) and how cognitive radios (CRs) in the secondary network (SN) become aware of the interference they create on the PN,…
Authors: Fatemeh Shah-Mohammadi, Andres Kwasinski
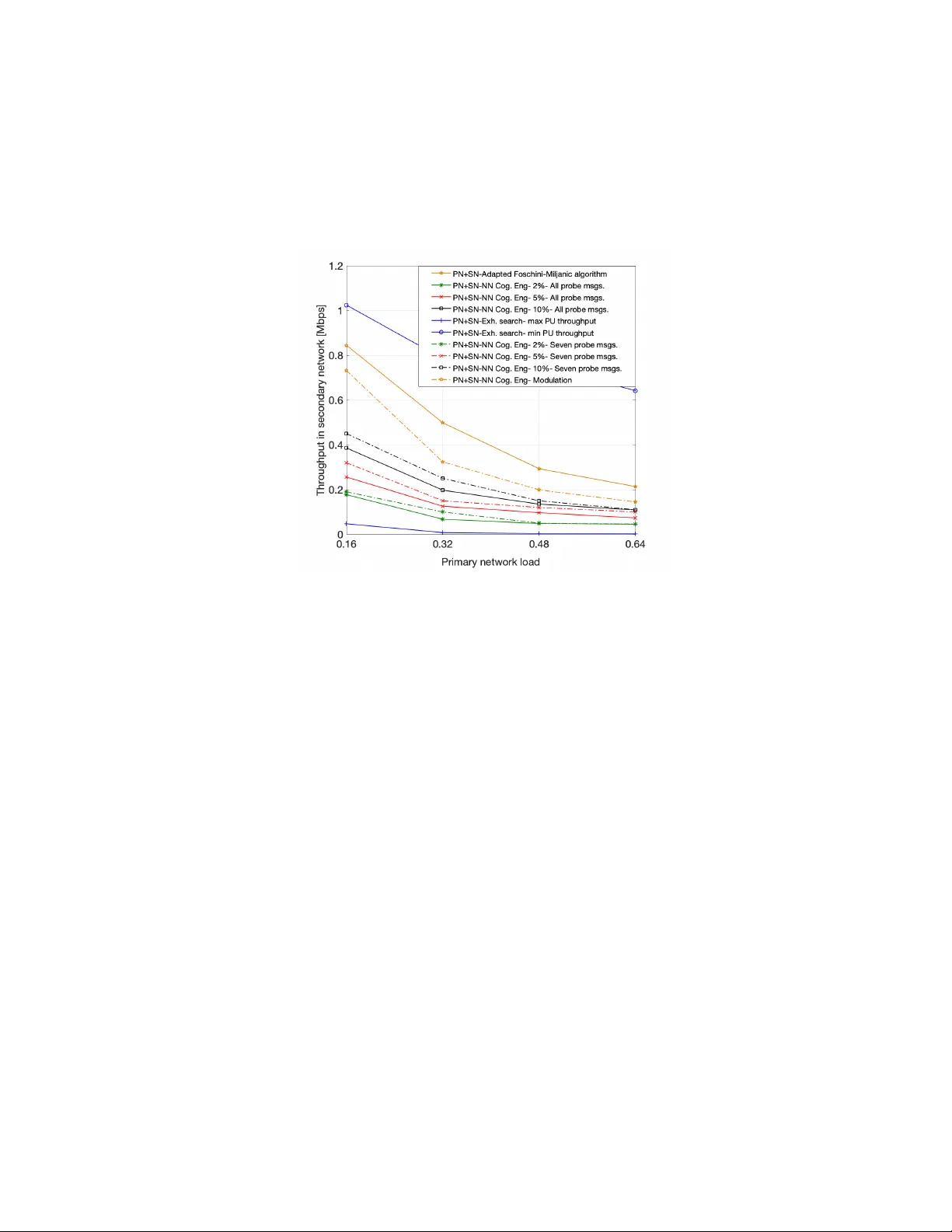
Neural Network Cogniti v e Engine for Autonomous and Distrib uted Underlay Dynamic Spectrum Access Fatemeh Shah-Mohammadi and Andres Kwasinski Kate Gleason College of Engineering Rochester Institute of T echnology , Rochester, Ne w Y ork 14623, USA Abstract T wo key challenges in underlay dynamic spectrum access (DSA) are how to establish an interference limit from the primary network (PN) and how cognitiv e radios (CRs) in the secondary network (SN) become aw are of the interference they create on the PN, especially when there is no e xchange of information between the two networks. These challenges are addressed in this paper by presenting a fully autonomous and distributed underlay DSA scheme where each CR operates based on predicting its transmission effect on the PN. The scheme is based on a cognitive engine with an artificial neural network that predicts, without e xchanging information between the networks, the adaptiv e modulation and coding configuration for the primary link nearest to a transmitting CR. By managing the effect of the SN on the PN, the presented technique maintains the relati ve average throughput change in the PN within a prescribed maximum value, while also finding transmit settings for the CRs that result in throughput as large as allo wed by the PN interference limit. Simulation results show that the ability of the cognitiv e engine in estimating the ef fect of a CR transmission on the full adaptive modulation and coding (AMC) mode leads to a much more fine underlay transmit power control. This ability also provides higher transmission opportunities for the CRs, compared to a scheme that can only estimate the modulation scheme used at the PN link. I . I N T RO D U C T I O N The cognitiv e radio (CR) paradigm is seen as a ke y solution to the radio spectrum scarcity problem stemming from the inefficiency of the established static spectrum allocation policy , [1], and the growing connectivity needs from wireless applications. A CR is a wireless device with the ability to autonomously gain a wareness of the wireless 2 network en vironment and to learn ho w to adapt its operating parameters to best meet the end-user goals [2]. As a result, CRs hav e frequently been considered as an enabling technology for dynamic spectrum access (DSA). Through DSA, a network of CRs, called the secondary network (SN), operates by sharing the radio spectrum with a primary network (PN) which is the incumbent owner of the spectrum band in use. Of the three main DSA approaches (overlay , underlay , and interweave DSA [3]), this paper focuses on underlay DSA. The underlay DSA allows CRs in the SN (called hereafter “secondary users” - SUs) to transmit over the same spectrum band being used by the PN by limiting their transmit po wer lev el so that the interference they create on the PN remains below a tolerable threshold [4]. Despite ha ving been studied for almost tw o decades, the main challenges in underlay DSA remain on ho w to establish the interference threshold for the PN links and how the SUs autonomously become aware of the interference they create on the PN, specially when following an ideal operating setup where there is no exchange of information between primary and secondary networks. In order for the SN to assess its ef fect on the PN and protect the PN transmissions, researchers have proposed different techniques that usually assume that the secondary transmitter ( 𝑆𝑈 𝑇 𝑋 ) knows the gain of the primary channel (that between the primary transmitter, 𝑃𝑈 𝑇 𝑋 , and the primary recei ver , 𝑃𝑈 𝑅 𝑋 ) and/or the cross-channel gain from the 𝑆𝑈 𝑇 𝑋 to the 𝑃𝑈 𝑅 𝑋 , [5]–[13]. The common theme between these works is that they make use of the information that is sent ov er a feedback channel in the PN. Since feedback channels are part of most wireless communication standards [14], [15], they ha ve often been used, under the assumption that SUs can access them, to not only estimate the primary channel gain, but also assess the effect of the SN on PN transmissions. Examples of a CR obtaining information about the primary link from a PN feedback channel are found in [6]–[9], [13] for the case of the rate/power control feedback channel, in [10] and [11] for the ARQ feedback channel, and in [12] for the feedback of the channel state information (CSI). In general, by relying on listening to feedback channels from the PN all works mentioned above share a setup where primary and secondary networks are not completely separated and exchange information with each other . In fact, the access of a control channel from another network calls into question as to whether there are really two separate network or , as we would argue, a single network with two different types of nodes. W ith a dif ferent approach, the works in [16] and [17] proposed solutions to obtain the cross-channel gain without listening to the PN feedback channels. The typical process in these works consists of the SU observing a change in the primary’ s wa veform po wer and/or modulation order that results from the transmission of a probe message from 3 the SU, [16], or the SU acting as a relay by sending the amplified version of the signal receiv ed from the PU, [17]. Howe ver , in these works a CR transmitter can not estimate the cross-channel gain, and later assess the effect of SN on PN, unless it observes a change in primary signal po wer and/or modulation order . Moreov er , these work did not considered the combined effect from scenarios with multiple links in the PN and the SN, as they focused on a setup with one link in each network. In contrast to these works, the technique to be presented here is not limited by the need to observe a change in transmit power or modulation order and is able to directly estimate the effect of an SN transmission on the PN much more accurately by also estimating the channel coding rate in a PN link. Moreov er , the work herein is on scenarios consisting of multiple links in the PN and SN. In addition, our presented technique meets a ke y requirement by not relying on any information exchange between the networks. But, instead, our technique takes adv antage of the use at the PN of adaptiv e modulation and coding (AMC), a technique where the modulation scheme and channel coding rate (a pair of parameters known as the AMC mode) are adapted based on the quality of the transmission link. The use of AMC has been part of all high performance wireless communications standards dev eloped over the past two decades and, thus, expected to be used by a typical PN [18]–[20]. Since the AMC mode in use depends on the link’ s SINR, by estimating the AMC mode used in a primary link, it becomes possible for a CR to learn the signal-to-interference-plus-noise ratio (SINR) experienced at that link, from which the ef fect of CR transmission on the PU link can be assessed. Specifically , we propose an underlay DSA technique that configures the transmit power for a SU based on estimating the throughput at its nearest PN link that corresponds to the AMC mode that would be chosen based on the interference created by the SU’ s transmission. On the other hand, leveraging the use of adapti ve modulation in the PN will allow us not only to assess the ef fects of the SN on the PN, but will also allow us to establish the PN interference threshold. As shown in [21], the use of adaptiv e modulation allows for the background noise to increase up to a certain level before the av erage throughput in a network starts to decrease. In the context of underlay DSA where the PN does not exchange any information with the SN, the interference imposed on the PN by an underlay-transmitting CR can be seen as a background noise for the PN, that can be increased up to a lev el which does not af fect the average throughput in the primary network. Therefore, a CR can become aware about the interference that is creating on the primary link and decide on its transmit power by inferring the change in experienced throughput of the primary link (details in section IV). The core of our technique is a non-linear autoregressi ve exogenous neural network (NARX-NN)-based cognitive 4 engine (CE) that estimates the throughput on a PN link (equiv alently , the full AMC mode), an indicator of the interference induced by the SU on the PN link. The proposed CE uses as input an estimate of the modulation scheme being used at the PN link. As such, to the best of our kno wledge, our presented cognitive engine is the first to be capable of estimating the channel coding rate setting for an AMC mode, a capability well beyond the estimation of the modulation scheme that has been realized through multiple signal processing or machine learning techniques. While modulation classification, the technique to estimate the modulation scheme used in a radio waveform, is applied in our DSA technique to deriv e an input for the cognitiv e engine, it is not the subject of this work. Instead, we lev erage the already large volume of existing research. In this regard, the work in [22] studied modulation classification based on second and higher order time variant periodic cumulant function of the sensed signal for which it is required a prior knowledge of the signal parameters. Authors in [23] used the same framew ork to perform signal pre-processing, along with utilizing artificial neural networks to address the issues associated with classification when the signal parameters are unkno wn. The work in [24] proposed a fully automated modulation classification scheme which employs two stages of signal processing to classify the modulation of an incoming signal. In this paper we assume that each SU applies the technique proposed in [24] on the nearest primary link to infer its used modulation scheme (details are omitted here). Therefore, the main contribution of this paper resides in presenting an underlay DSA technique to infer, without tapping into feedback or control channels from another network, the experienced throughput and accordingly the modulation order and the channel coding rate used in the transmission of the other network (the primary network here), and to lev erage this inference in the realization of a fully autonomous and distributed underlay DSA scheme. This ability to estimate the effecti v e throughput enables a finer control knob for a more accurate power allocation at the SN with less harmful effect on PN transmissions as compared to techniques that rely only on the estimation of modulation order (from applying signal processing on the transmission waveform). Our simulation results will show that the presented technique is able to maintain the relativ e change in PN average throughput within a prescribed fine-grained target maximum v alue (as an indicator of maximum allowed interference in PN), while at the same time finding transmit settings for the SUs that will result in as large throughput in the SN as could be allowed by the PN interference limit. As such, while succeeding in its main goal of autonomously and distributi vely determining the transmit power of the SUs such that the interference they create remains below the PN 5 Fig. 1. Considered network model composed of 𝑁 𝑝 primary transceivers and 𝑁 𝑠 cognitiv e radio users. allowed interference limit, our proposed technique is also able to manage the tradeoff between the effect of the SN on the PN and the achie vable throughput at the SN. Specifically , simulation results will show that for the proposed system with a target PN maximum relati ve av erage throughput change of 2%, the achieved relati ve change is less than 3%, while at the same time achieving useful av erage throughput values in the SN between 180 and 50 kbps. In addition, it will be seen that the implementation of a variation of the proposed scheme that reduces three times the ov erhead from transmitting probe messages still exhibits the ability to finely control the effect on the primary network throughput, although, as is to expect, compared to the case of sending all probe messages it increases by at most 1%, only at the very low PN load of 0.16, the relati ve av erage throughput change. The rest of this paper is organized as follows. Section II presents the overall system setup. Section III presents an analytical framework to assess the effect of transmission in the SN on the PN, under the assumed fully autonomous transmission scenario. The rationale on how AMC can be leveraged to address the main two challenges associated with underlay DSA is outlined in Section IV. Section V describes our proposed distributed underlay DSA technique. Simulation results are presented in Section VI, follo wed by conclusions in Section VII. I I . S Y S T E M S E T U P W e consider a primary network with 𝑁 𝑃 activ e primary links coexisting with 𝑁 𝑆 activ e secondary links, with both networks transmitting over the same frequency band. The system model is sho wn in Fig.1, where 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 denoted as cross-channel gain is the path gain from 𝑗 th. transmitting SU to the receiver in 𝑖 th. primary link, 𝐺 ( 𝑠 𝑠 ) 𝑖 𝑗 is the path gain from the transmitter in the 𝑗 th. secondary link to the receiv er in the 𝑖 th. secondary link, 𝐺 ( 𝑠 𝑝 ) 𝑖 𝑗 is the path 6 gain from the transmitter in 𝑗 th. primary link to the receiv er in 𝑖 th. SU link, 𝐺 ( 𝑝 𝑝 ) 𝑖 𝑖 is the path gain from the 𝑖 th. primary transmitter to its corresponding receiver , and 𝐺 ( 𝑠 𝑠 ) 𝑖 𝑖 is the path gain from the 𝑖 th. secondary transmitter to its corresponding recei ver . While, ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 is the path gain from the transmitter in 𝑗 th. secondary link to the transmitter in 𝑖 th. primary link. In this section we focus on describing the operation of the PN, which is incumbent to the considered radio spectrum band. Section V will present the underlay DSA scheme implemented in the SN. W e assume that the PUs receive service from 𝑁 𝑃 𝐵 𝑆 transmitting base stations (BSs), and we call the ratio 𝑁 𝑃 / 𝑁 𝑃 𝐵 𝑆 as the primary network load. Each PU is assigned to the base station that presents the best channel gain. In addition, AMC is used in all transmissions (primary and secondary networks). This means that a transmitter has information about its link quality , in terms of SINR, and based on this assessment chooses, from a set of options, the modulation scheme and channel coding rate that results in highest throughput while at the same time meeting a maximum bit error rate (BER) limit. Let 𝑃 ( 𝑝 ) 𝑖 denotes the transmit power in the 𝑖 th. active primary link ( 𝑖 = 1 , 2 , . . . , 𝑁 𝑃 ). Then, in the absence of the SN, the SINR in the 𝑖 th. primary link (which is used to decide on the AMC mode) can be written as, 𝛾 ( 𝑝 ) 𝑖 = 𝐺 ( 𝑝 𝑝 ) 𝑖 𝑖 𝑃 ( 𝑝 ) 𝑖 𝑗 ≠ 𝑖 𝐺 ( 𝑝 𝑝 ) 𝑖 𝑗 𝑃 ( 𝑝 ) 𝑗 + 𝜎 2 𝑝 , 𝑖 = 1 , 2 , . .. , 𝑁 𝑃 , (1) where 𝜎 2 𝑝 is the background noise power . In addition to AMC, without loss of generality , we adopt for the primary network the variable transmit power allocation algorithm proposed in [21]. This is an iterative power control algorithm that con ver ges to a global optimum solution that maximizes the product of SINRs across all activ e links. In the algorithm, the transmit po wer at the 𝑖 th. primary link is updated as, 𝑃 ( 𝑝 ) 𝑖 ← − © « 𝑗 ≠ 𝑖 𝐺 ( 𝑝 𝑝 ) 𝑗 𝑖 Í 𝑚 ≠ 𝑗 𝐺 ( 𝑝 𝑝 ) 𝑗 𝑚 𝑃 ( 𝑝 ) 𝑚 + 𝜎 2 𝑝 ª ® ¬ − 1 . (2) I I I . S U T R A N S M I S S I O N E FF E C T A S S E S S M E N T O N T H E P U : A N A L Y T I C A L F R A M E W O R K In this section, we de velop an analytical framew ork to explore, under a fully autonomous and distrib uted transmission scenario, the possibility of closed-form analytical estimation of the interference created by a transmitting CR to its nearest PU link. It is assumed that the PUs are oblivious to the existence of the SUs and treat the interference from transmitting CRs as additional noise at their receiver . As mentioned earlier , we consider a practical scenario where 7 the CRs have no access to any control channel in the PN from which to obtain any side information (e.g., 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 ) that might facilitate their interference control on the PN. Similar to our proposed technique to be presented inhere, we assume a two-stage operation in the SN. During the first stage, e very SU in the SN listens to the transmissions in the PN and observes the receiv ed signal power . In the second stage, e very SU broadcasts a probing signal. This probing signal, transmitted with the same po wer by all SUs, will create some interfere on the PN. Since PUs make use of variable transmit po wer and AMC, upon experiencing the interference from the probing signal, ev ery receiv er in the PN sends back a control signal to its corresponding transmitter to adapt its transmit po wer and rate (specifically , the AMC mode) accordingly . These adaptation in transmission parameter at the primary links are observed by the SUs. W e assume that SUs know the primary transmission protocol and are able to synchronize their operation with the primary transmissions, and that all the channel gains in v olved in Fig. 1 remain constant during this process. Let 𝑃 ( 𝑝 ) 𝑖 [ 0 ] denotes the initial transmit power in the 𝑖 th. activ e primary link ( 𝑖 = 1 , 2 , . . . , 𝑁 𝑃 ) while SUs listen to the transmissions in the PN. The received signal power at this stage (i.e. listening stage) at 𝑖 th. SU transmitter can be written as 𝑆 𝑖 [ 0 ] = 𝑁 𝑃 𝑗 = 1 ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 𝑃 ( 𝑝 ) 𝑗 [ 0 ] . This equation further can be separated into two parts: one for the power receiv ed from the nearest PU transmitter and a second component for the receiv ed power from the rest of acti ve PUs in the system, as in, 𝑆 𝑖 [ 0 ] = ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑛 𝑃 ( 𝑝 ) 𝑛 [ 0 ] + 𝑁 𝑃 𝑗 = 1 𝑗 ≠ 𝑛 ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 𝑃 ( 𝑝 ) 𝑗 [ 0 ] , (3) where ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑛 𝑃 ( 𝑝 ) 𝑛 [ 0 ] shows the po wer recei ved from the nearest PU active link (the subscript 𝑛 is used to highlight, among all activ e transmission links in the PN, the nearest link to the 𝑖 th. SU). Considering the same probing signal power for all SUs to be as 𝑃 ( 𝑠 ) , the observed power at the 𝑖 th. SU transmitter during the probing stage can be also written as: 𝑆 𝑖 [ 1 ] = ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑛 𝑃 ( 𝑝 ) 𝑛 [ 1 ] + 𝑁 𝑃 𝑗 = 1 𝑗 ≠ 𝑛 ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 𝑃 ( 𝑝 ) 𝑗 [ 1 ] + 𝐼 𝑠 𝑠 , (4) where 𝐼 𝑠 𝑠 = 𝑁 𝑆 𝑗 = 1 , 𝑗 ≠ 𝑖 𝐺 ( 𝑠 𝑠 ) 𝑖 𝑗 𝑃 ( 𝑠 ) denotes the total interference from the SN to the 𝑖 th. transmitting SU, and 𝑃 ( 𝑝 ) 𝑗 [ 1 ] denotes, for the 𝑗 th. PU transmit link, the new adapted transmit power . Without loss of generality it can be assumed that 𝑃 ( 𝑝 ) 𝑖 [ 0 ] > 0 , and thus 𝑆 𝑖 [ 0 ] > 0 , because if 𝑃 ( 𝑝 ) 𝑖 [ 0 ] = 0 , the SU can simply transmits as the spectrum band is 8 unoccupied; and the estimation of the created interference becomes unnecessary . The receiv ed signal powers during the listening and probing stage contain the information about the cross-channel gain between 𝑖 th. SU transmitter and its corresponding nearest PU receiv er 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑛 . As mentioned earlier , the cross-channel gain can be used at the SU to assess its effect of transmission on the PU. Thus, in the following we explore whether each SU can determine 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑛 using its observations. By di viding the signal powers receiv ed at the 𝑖 th. SU transmitter across two listening and probing stages 𝑆 𝑖 [ 0 ] and 𝑆 𝑖 [ 1 ] , we have: 𝑆 𝑖 [ 1 ] 𝑆 𝑖 [ 0 ] = ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑛 𝑃 ( 𝑝 ) 𝑛 [ 1 ] + 𝑁 𝑃 𝑗 ≠ 𝑛 ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 𝑃 ( 𝑝 ) 𝑗 [ 1 ] + 𝐼 𝑠 𝑠 ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑛 𝑃 ( 𝑝 ) 𝑛 [ 0 ] + 𝑁 𝑃 𝑗 = 1 , 𝑗 ≠ 𝑛 ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 𝑃 ( 𝑝 ) 𝑗 [ 0 ] (5) On the other hand, based on the assumption we made in this paper, each SU is able to perfectly estimate the adapted modulation order (number of bits per modulation symbols) of its nearest PU link. Due to the use of AMC at every transmission link in the system, the relation between modulation order and the experienced SINR at 𝑖 th. primary link receiv er can be expressed as [21], [25], 𝑀 ( 𝑝 ) 𝑖 = log 2 ( 1 + 𝑘 𝛾 ( 𝑝 ) 𝑖 ) , (6) where 𝑀 ( 𝑝 ) 𝑖 is the 𝑖 th. PU’ s modulation order, 𝑘 is the in verse SNR gap constant 𝑘 = 1 . 5 − ln ( 5 𝐵 𝐸 𝑅 ) which depends on a target maximum transmit bit error rate (BER) requirement, and 𝛾 ( 𝑝 ) 𝑖 is the SINR at the receiver of this link. During the listening stage, the 𝛾 ( 𝑝 ) 𝑖 can be expressed as, 𝛾 ( 𝑝 ) 𝑖 [ 0 ] = 𝐺 ( 𝑝 𝑝 ) 𝑖 𝑖 𝑃 ( 𝑝 ) 𝑖 [ 0 ] 𝐼 𝑝 𝑝 [ 0 ] + 𝜎 2 𝑝 , (7) where 𝐼 𝑝 𝑝 [ 0 ] = 𝑁 𝑃 𝑗 = 1 , 𝑗 ≠ 𝑖 𝐺 ( 𝑝 𝑝 ) 𝑖 𝑗 𝑃 ( 𝑝 ) 𝑗 [ 0 ] denotes the interference from the PN to the 𝑖 th. primary link, and 𝜎 2 𝑝 is the background noise po wer . Using (6) and (7), 𝑃 ( 𝑝 ) 𝑖 [ 0 ] can be expressed as follo ws, 𝑃 ( 𝑝 ) 𝑖 [ 0 ] = ( 2 𝑀 ( 𝑝 ) 𝑖 [ 0 ] − 1 ) ( 𝐼 𝑝 𝑝 [ 0 ] + 𝜎 2 𝑝 ) 𝑘 𝐺 ( 𝑝 𝑝 ) 𝑖 𝑖 , (8) 9 𝑆 𝑖 [ 1 ] 𝑆 𝑖 [ 0 ] = ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑛 ( 2 𝑀 ( 𝑝 ) 𝑖 [ 1 ] − 1 ) ( 𝐼 𝑝 𝑝 [ 1 ] + 𝐼 𝑝 𝑠 + 𝜎 2 𝑝 ) 𝑘 𝐺 ( 𝑝 𝑝 ) 𝑖𝑖 + 𝑁 𝑃 𝑗 = 1 𝑗 ≠ 𝑛 ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 𝑃 ( 𝑝 ) 𝑗 [ 1 ] + 𝐼 𝑠 𝑠 ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑛 ( 2 𝑀 ( 𝑝 ) 𝑖 [ 0 ] − 1 ) ) ( 𝐼 𝑝 [ 0 ] + 𝜎 2 𝑝 ) 𝑘 𝐺 ( 𝑝 𝑝 ) 𝑖𝑖 + 𝑁 𝑃 𝑗 = 1 𝑗 ≠ 𝑛 ˜ 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 𝑃 ( 𝑝 ) 𝑗 [ 0 ] , (11) where 𝑀 ( 𝑝 ) 𝑖 [ 0 ] denotes the PU’ s modulation order . During the probing stage, due to the additional interference created by the SN, 𝛾 ( 𝑝 ) 𝑖 [ 0 ] is changed to be: 𝛾 ( 𝑝 ) 𝑖 [ 1 ] = 𝐺 ( 𝑝 𝑝 ) 𝑖 𝑖 𝑃 ( 𝑝 ) 𝑖 [ 1 ] 𝐼 𝑝 𝑝 [ 1 ] + 𝑁 𝑆 𝑗 = 1 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 𝑃 ( 𝑠 ) + 𝜎 2 𝑝 , (9) where 𝐼 𝑝 𝑝 [ 1 ] = 𝑁 𝑃 𝑗 = 1 , 𝑗 ≠ 𝑖 𝐺 ( 𝑝 𝑝 ) 𝑖 𝑗 𝑃 ( 𝑝 ) 𝑗 [ 1 ] denotes the interference from the PN to the 𝑖 th. primary link. Using (6) and (9), 𝑃 ( 𝑝 ) 𝑖 [ 1 ] can be expressed as: 𝑃 ( 𝑝 ) 𝑖 [ 1 ] = ( 2 𝑀 ( 𝑝 ) 𝑖 [ 1 ] − 1 ) © « 𝐼 𝑝 𝑝 [ 1 ] + 𝑁 𝑆 𝑗 = 1 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 𝑃 ( 𝑠 ) + 𝜎 2 𝑝 ª ® ¬ 𝑘 𝐺 ( 𝑝 𝑝 ) 𝑖 𝑖 , (10) where 𝑀 ( 𝑝 ) 𝑖 [ 1 ] denotes the PU’ s new adapted modulation order at the probing stage. By substituting 𝑃 ( 𝑝 ) 𝑛 [ 0 ] with (8), and 𝑃 ( 𝑝 ) 𝑛 [ 1 ] with (10), equation (5) can be re written as (11), where 𝐼 𝑝 𝑠 = 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑛 𝑃 ( 𝑠 ) + 𝑁 𝑆 𝑗 = 1 , 𝑗 ≠ 𝑛 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 𝑃 ( 𝑠 ) displays the interference from the SN to the 𝑖 th. SU’ s nearest primary link after probing (recall that cross-channel gain is denoted by 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑛 ). In the particular case when the primary and secondary network hav e each only one transmitting link, (11) can be simplified as: 𝑆 𝑖 [ 1 ] 𝑆 𝑖 [ 0 ] = ( 2 𝑀 ( 𝑝 ) 𝑖 [ 1 ] − 1 ) ( 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑛 𝑃 ( 𝑠 ) + 𝜎 2 𝑝 ) ( 2 𝑀 ( 𝑝 ) 𝑖 [ 0 ] − 1 ) 𝜎 2 𝑝 , (12) Provided that the 𝜎 2 𝑝 is known by the SU, the ratio 𝑆 𝑖 [ 1 ] 𝑆 𝑖 [ 0 ] can be used to estimate the cross-channel gain and subsequently the interference from only SU link in the SN to the PU, as studied in [16] and [17] (note that 𝑀 ( 𝑝 ) 𝑖 [ 1 ] and 𝑀 ( 𝑝 ) 𝑖 [ 0 ] are known at the SU transmitter). Y et, in the general case we are considering here, where there are multiple transmission links in both networks, (11) is the appropriate expression. Howe ver , (11) is not of practical use 10 because it requires from the SUs knowledge of too many system variables (the gains, etc.). Under the assumption of a fully autonomous network, it is not realistic to assume knowledge of all these in volved parameters and to be able to apply a closed-form solution to this problem (and, specifically , being able to estimate the cross-channel gains that corresponds to each SU). Therefore, we posit the use of artificial neural network to solve the problem of SUs assessing their ef fect on the PN. The rational for this decision rests on the artificial neural network’ s property of being known as universal function approximator and their ability to implicitly extract, during the learning (training) process, the interrelation between the system variables. Leveraging these characteristics of artificial neural networks in our proposed technique allo ws for the SUs to assess their transmission ef fect on the PN without the need to calculate intermediate magnitudes (e.g. the cross-channel gain(s)). I V . L E V E R AG I N G A DA P T I V E M O D U L A T I O N A N D C O D I N G I N U N D E R L A Y D S A Before presenting our proposed underlay DSA technique, in this Section we outline the main ideas on how AMC can be lev eraged to address the two main challenges associated with underlay DSA: 1) How to establish the interference threshold in the PN and 2) how SUs can autonomously become aware of the interference they create on the PN. As previously noted, AMC (or , as also called, link adaptation) has been used during the past two decades in practically all high-performance wireless communications standards and, as such, is assumed to be used in both the primary and secondary networks in this work. In this section we summarize some of the main features of AMC that are rele vant to our fully autonomous and distributed underlay DSA scheme. Fig. 2, obtained using the Matlab L TE Link Level Simulator from TU-Wien [26], [27], sho ws the throughput versus signal-to-noise ratio (SNR) performance for the L TE system under a Pedestrian B channel that will serve without loss of generality as the assumed AMC setup for the rest of this work (setup details for the simulation results sho wn in Fig. 2 are discussed in Section VI). In L TE, AMC consists of 15 different modes (each for a different “Channel Quality Indicator" - CQI) based on three possible modulation schemes which will be called “ type 0 " for QPSK (used for the smaller SNR regime), “ type 1 " for 16QAM (used at intermediate SNRs), and “ type 2 " for 64QAM (used for the larger SNRs). In AMC, alongside the modulation order, channel coding rate is also adapted [28], [29]. Fig. 2 sho ws the throughput of one L TE resource block achiev ed for each AMC mode (each curve is labeled with the corresponding CQI value and AMC mode settings, formed by the modulation type and channel coding rate) and the overall performance curve of the AMC scheme, where the modulation type and code rate are chosen to maximize throughput but with a 11 constraint on the block error rate (BLER) not to exceed 10 % . During transmission, the transmitter chooses the AMC mode with maximum throughput at the estimated SNR of the link. Fig. 2. Throughput for each CQI and maximum throughput adaptiv e selection per RB for the AMC scheme of an L TE system under a Pedestrian B channel. As was discussed in [21], the use of AMC in conjunction with transmit power control allows the background noise to increase up to a maximum value without significantly affecting the network a verage throughput. In the context of underlay DSA, this maximum noise value can be interpreted as the maximum value for the combined powers of background noise and interference from the SN. T o see this important point in detail, consider Fig. 3, which is an expanded version of Fig. 5 in [21], no w for dif ferent network loads ( 𝑁 𝑃 / 𝑁 𝑃 𝐵 𝑆 ) when using the L TE AMC setup just described and the power control algorithm from [21]. The figure sho ws the a verage throughput achieved in the PN by itself (the presence of an SN is not included in this result) as the background noise po wer increases. On the top, the figure shows the property associated with the use of adaptive modulation that for all network loads the av erage throughput remains approximately constant until noise power becomes suf ficiently significant. This is not a trivial observ ation as networks with a higher load are operating in a regime more influenced by the interference rather than the noise, but it is clear from the results that adaptive modulation manages to maintain a balance between interference and noise-dominated operation. The bottom of Fig. 3 shows as a function of noise power , the change in throughput relati ve to the throughput at the lowest noise power . The result exposes the remarkable property that the interference that would be imposed by the SN, which can be considered by a PN that is unaware of the presence of another network as part of the background noise, will not significantly affect the average throughput in the primary network as long as the combined SN interference, the interference by other primary links and actual background noise remains below a threshold approximately equal to -85 dBm (although this number somewhat depends on the network 12 load). Moreov er , relative throughput change starts to decrease at approximately the same value of noise po wer for all network loads (around -90 dBm). This is a consequence of the link adaptation performed through AMC. Moreov er , throughput relatively decreases faster with smaller network loads. W e believe that this is because at smaller network loads, interference across the network is lo wer and a larger ratio of transmissions use the less resilient higher rate modulation types. Fig. 3. Throughput vs. noise power in the primary network. While AMC entails the adaptation of both modulation order and channel coding rate, it can be seen in Fig. 2 that the modulation order provides a coarse adaptation and that the channel coding rate enables a finer adaptation within each of the choices for modulation order . Moreov er , an important difference between modulation order and channel coding rate adaptations is that while it is possible for a passive “listener" of the AMC transmission to infer the modulation order through the use of modulation classification signal processing, it is not possible to infer the channel coding rate (or equiv alently the full AMC mode). On the other hand, as can be seen in Fig. 2, when the noise power increases (or equi v alently the SN interference increases) the effect of AMC operation will be to change the AMC mode to one associated with a smaller CQI. At the same time, the modulation scheme with the smallest order is used for the smallest operating SINRs (because the transmission of less bits per symbol is more resilient to interference and noise). As the interference from secondary transmissions increases, primary links that are already using, in the absence of secondary transmissions, the lo west modulation order scheme will not switch to other modulation schemes because there is no other modulation scheme with fewer bits per symbols to switch to. This means that transmissions from an SU that otherwise would generate a change in modulation scheme would not result in any change when the nearest 13 primary link is already transmitting with the modulation scheme with smallest bits per symbol. As a result, estimation of the modulation order provides for the SU transmitter with a control nob to infer the effect of SN transmission on the PN but with sev ere limitations due to the coarse information provided by the estimated modulation order . Ho wev er , as seen in Fig. 2, although the increase in interference to the PU (and particularly increase in SU transmit po wer) may not lead to change in modulation order , it indeed results in the change in channel coding rate. Thus, the estimation of the channel coding rate (and equiv alently the full AMC mode) is necessary in order to be able to finely estimate the effect of SU transmissions. Indeed, there exists a large body of research in the area of modulation classification with some representative works briefly discussed in Sect. I (e.g. [22]–[24]). Consequently , the techniques that existed before our work hav e been limited to use only the coarse information derived from the modulation order (e.g. [16], [17]) or to rely on the sharing of information between the PN and the SN through the SUs accessing the control feedback channel in the PN to learn the finer information associated with the channel coding rate used in a primary link (e.g. [11]). As will be seen, our proposed technique is able to ov ercome the limitation of inferring the channel coding rate without exchange of information between the PN and the SN and, as such, be able to use the fine-grained information provided by channel coding rate without the SN tapping into any control channel of the PN. In the following we de velop for a transmitting CR a model to estimate the interference limit from the PN. Reg arding Fig. 3 it was stated that the property associated with the use of adaptiv e modulation allows the background noise to increase up to a maximum value without significantly af fecting the network av erage throughput; and that the maximum noise value can be interpreted as the maximum value for the combined powers of background noise and interference from the SN. For the purpose of underlay DSA, it is con venient to model the PN av erage throughput sho wn in the bottom of this figure as equal to the a verage throughput achie ved without the presence of the SN minus an average throughput loss that is a function of an equi valent interference from the SN as experienced across the PN. This is, if 𝑇 0 ( 𝜎 2 𝑝 ) is the PN average throughput without the SN (explicitly shown to be dependant on the background noise power 𝜎 2 𝑝 ), we model the PN av erage throughput 𝑇 𝑝 as 𝑇 𝑝 = 𝑇 0 ( 𝜎 2 𝑝 ) − 𝑇 𝑙 ( 𝐼 ) , where 𝑇 𝑙 is the throughput loss and 𝐼 is the equiv alent interference from the SN as experienced across the PN. Next, the throughput loss is modeled according to the SNR gap approximation for the Shannon’ s channel capacity formula, [25], yielding 𝑇 𝑝 = 𝑇 0 − 𝐵 log 2 ( 1 + Γ 10 𝐼 / 10 ) , (13) where 𝐵 is the PN system bandwidth, 𝐼 is the equiv alent interference generated by the SN on the PN (measured in 14 dBm), and Γ is the SNR gap that accounts for the use of practical coding and transmission mechanisms (we hav e also embedded into Γ a factor of 0.001 stemming from the con version of units of 𝐼 from dBm). Being the relative average throughput change in the PN 𝑇 % = ( 𝑇 𝑝 − 𝑇 0 ) / 𝑇 0 , from (13) we have, 𝑇 % = − 1 𝜁 log 2 ( 1 + Γ 10 𝐼 / 10 ) , (14) where 𝜁 = 𝑇 0 / 𝐵 is the PN spectral efficienc y that is achieved without the SN’ s effect. Figure 4 compares the relati ve av erage throughput change from Fig. 3 for loads equal to 0.16 and 0.48 only for figure clarity and their approximations (14). The approximation uses for the spectral efficienc y calculation the same system bandwidth 𝐵 as in the results in Fig. 3 (180 kHz) and, of course, the v alues 𝑇 0 from Fig. 3 at noise po wer equal to -140 dBm. Fig. 4 validates our model giv en by (13) and (14) by showing a good approximation for the relati ve av erage throughput change (the approximation shows less accuracy when the relativ e av erage throughput change grows beyond 40% which is of no concern because these are values of relativ e average throughput change too large to be used in the practical operation of underlay DSA). More importantly , Fig. 4 includes a second abscissa to highlight the meaning of the equiv alent interference in the conte xt of underlay DSA where the PN uses AMC. As mentioned earlier , the curves in Fig. 3 show for a network that uses AMC the change in a verage throughput as the background noise power increases. In the context of underlay DSA, the absence of information exchange between the PN and the SN implies that, in principle, the PN is oblivious of the presence or not of the SN. Therefore, the PN would experience the interference from the SN as an increase in the background noise, which is what we identify as the equiv alent interference 𝐼 . This is illustrated in Fig. 4 with the second abscissa, showing the increasing equiv alent interference with the same v alue as the background noise. In this way , for example, if the actual background noise is -140 dBm, an equiv alent interference of 𝐼 = 30 dBm is performance-wise percei ved by the PN as a total background noise of -110 dBm. The goal of the proposed underlay DSA mechanism at the SN is to find the transmit power at the SUs that results in an equi valent interference, denoted as interference limit 𝐼 0 , that is as large as possible (to increase throughput at the SN) while the relati ve av erage throughput change in the PN remains belo w a limit that we will denote as 𝜖 . From (14), this maximum equiv alent interference, measured in dBm and denoted as interference limit, can be expressed as a function of the limit 𝜖 as, 𝐼 0 = 10 ∗ log 2 − 𝜖 𝜁 − 1 Γ . (15) 15 Fig. 4. Relative av erage throughput change and approximation (14). Using this expression, we hav e calculated, for example with 𝜖 = − 0 . 05 , values of maximum equiv alent interference equal to 51.3 dBm and 61.1 dBm for load equal to 0.16 and 0.48, respecti vely . The expression in (15) provides an answer to one of the two main challenges in underlay DSA: the establishment of the interference threshold from the PN. Howe v er , the second challenge remains: how the SUs autonomously become aware of the interference they create on the PN, relativ e to the limit 𝐼 0 . This challenge is compounded by our setup where the SUs can only use information they sense indi vidually (the modulation scheme used at the nearest primary link) which, as explained earlier , leads to many of the parameters that would be needed for an analytical solution being not accessible to the SUs. T o solve this challenge we propose the use of artificial neural networks because of their state-of-the-art status within techniques capable of learning the relation between the equi valent interference and the SUs’ transmissions (that is implicitly represented within the training data). V . A U T O N OM O U S A N D D I S T R I B U T E D U N D E R L A Y D S A F O R C O G N I T I V E R A D I O N E T W O R K S W e no w present the main contrib ution of this paper: a fully autonomous and distributed underlay DSA technique for a secondary CR network. The operation of the SN is fully autonomous and ad-hoc. This means that SUs do not rely on any exchange of information with the PN and with other SUs (other than between transmitter -receiv er pairs) and that the transmission control algorithm in the SN needs is distributed. While there is no information exchange between primary and secondary networks, it is assumed that the SN has knowledge of the underlying timing operation in the PN because it knows the protocol used in the PN (through standard or publicly av ailable information). Because of this, the SN has knowledge of the underlying timing operation in the primary network at a broad lev el (e.g. when 16 frame transmission starts, etc.) so that CRs are able to sense and transmit at appropriate times. Detailed (symbol-level) knowledge of timing at the CRs is not required or assumed. As stated, fully autonomous operation implies that the primary and secondary networks operate as being unaware of the other (except for the mild timing assumption), considering the other network transmissions as out-of-network interference akin to background noise. Then, when adding an underlay SN, the SINR at the receiv er of the 𝑖 th. PN link now becomes, 𝛾 ( 𝑝 ) 𝑖 = 𝐺 ( 𝑝 𝑝 ) 𝑖 𝑖 𝑃 ( 𝑝 ) 𝑖 𝑁 𝑃 𝑗 ≠ 𝑖 𝐺 ( 𝑝 𝑝 ) 𝑖 𝑗 𝑃 ( 𝑝 ) 𝑗 + 𝑁 𝑆 𝑗 = 1 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 𝑃 ( 𝑠 ) 𝑗 + 𝜎 2 𝑝 , (16) where 𝑃 ( 𝑠 ) 𝑗 is the transmit power from the 𝑗 th. transmitting SU and 𝐺 ( 𝑝 𝑠 ) 𝑖 𝑗 is the path gain from a transmitting SU 𝑗 to a PU 𝑖 . Like wise, it is assumed that transmissions on the SN also make use of AMC, which is configured based on the corresponding link SINR. For this, the SINR, 𝛾 ( 𝑠 ) 𝑖 , at the receiv er of the 𝑖 th. SN link is: 𝛾 ( 𝑠 ) 𝑖 = 𝐺 ( 𝑠 𝑠 ) 𝑖 𝑖 𝑃 ( 𝑠 ) 𝑖 𝑁 𝑆 𝑗 ≠ 𝑖 𝐺 ( 𝑠 𝑠 ) 𝑖 𝑗 𝑃 ( 𝑠 ) 𝑗 + 𝑁 𝑃 𝑗 = 1 𝐺 ( 𝑠 𝑝 ) 𝑖 𝑗 𝑃 ( 𝑝 ) 𝑗 + 𝜎 2 𝑠 , (17) All transmissions are assumed to be over a quasi-static fading channel that is considered constant during a sensing and transmission period. This setup assumed for the SN is general, yet practical, as it is applicable to numerous wireless cognitiv e ad-hoc networks scenarios. In the proposed underlay DSA technique, a cognitiv e engine at each SN transmitter lev erages the use of artificial neural network to learn the functional model of the interaction between the secondary and primary networks. Often, analytical models hav e been used to characterize the performance of the SN. For example, in [30] the BER performance of different modulation orders hav e been characterized using analytical models. Howe ver , as shown in section III, our deriv ed analytical model requires from SUs kno wledge of many variables which necessitate the use of control channels between two networks (which violates our main assumption of having fully autonomous setup). Black-box modeling is an alternati ve approach to analytical models which considers analyzing the relation between input and output of a system and aims at building a predictor to estimate output values for unforeseen inputs and variations of the system configurations. In this work we will follo w a black-box modeling approach. 17 Neural Networks (NNs) have become increasingly popular as general purpose function approximators and, specifi- cally , for dynamic system modeling [31]. Neural networks hav e been successfully applied to a number of black-box modeling and time series prediction tasks. Due to the inherent capability of neural networks in modeling nonlinear systems and their higher rob ustness to noise, they frequently outperform standard linear techniques when the time series are noisy and the dynamical system that generated the time series is nonlinear [32]. There is a growing number of works that have applied neural networks for v arious communication tasks such as channel decoding, estimating the features of the user channels and predicting the anomalies for wireless sensor networks [33]–[35]. For CRs, the feed forward neural network has been used in predicting the spectrum occupancy status [36] and designing a medium access control (MA C) protocol [37]. Due to the adaptation of SU’ s transmission to the PN interference threshold, an underlay network can be seen as an example of a dynamic system, and also the throughput in the PU can be seen as a time series with a temporal dependency . As a result, we hav e considered a neural network-based cognitive engine to specifically predict the throughput in PU and characterize the behavior of such dynamic system. In the case of one-step-ahead time series prediction tasks, only the estimation of the next sample value of a time series is required. Therefore, the input contains only actual sample points of the time series, without feeding back the output as a new input to the model. While considering multi-step-ahead or long-term prediction, the neural network’ s output should be fed back to the model as a ne w input for a finite number of time steps [38]. In this case, the components of this input to the neural network, previously composed of actual samples of the time series, are gradually replaced by previously predicted values. As a result, the multi-step-ahead prediction task is conv erted to a dynamic modeling task. In this case, the neural network model behav es as an autonomous system and tries to recursiv ely emulate the dynamic beha vior of the system that generated the nonlinear time series [39]. Compared to the one-step-ahead prediction, multi-step-ahead prediction and dynamic modeling are much more complex to deal with. Howe v er , neural networks models and in particular recurrent neural architectures play an important role in dealing with these complex tasks [40]. Elman introduced in [41] a class of recurrent neural models called simple recurrent networks (SRNs) which are essentially feedforward in the signal-flow structure with a few local and/or global feedback loops. A time delay neural network (TDNN), which is an adapted version of a feedforward multilayer perceptron (MLP)-like networks with an input tapped-delay line, can be used to process time series [40]. In the case of long-term predictions, a feedforward TDNN model will eventually 18 ! " #$% ! " #$ & "% ! " #$ &' !" % (#$ & "% ! ) #$&' !) % (#$ &' ( % (#$% *$+!,-./(01 23''0$-./(01 4!,+!,-./(01 (#$5"% 6 &" 6 &" ! )- #$% 6 &" 6 &" ! )- #$ & "% 6 &" ! " #$ & )% 6 &" 6 &" 6 &" Fig. 5. NARX neural network with two delayed inputs and one delayed output. behav e similarly to the SRN architecture, since a global loop is needed to feed back the current estimated v alue into the model’ s input. T emporal gradient-based variants of the backpropagation algorithm are usually used to train the aforementioned recurrent neural networks [42]. Howe ver , training using gradient-based learning algorithms can be quite dif ficult in the case of systems with a long time temporal dependencies between their input-output signals [43]. In [44], the authors claimed that such training is more effecti ve in a class of simple recurrent network models called Nonlinear Autoregressi ve with eXogenous input (N ARX) [45]–[47] than in simple MLP-based models. This class of neural networks were proven to be powerful in pattern recognition and classification applications as well [48], [49]. In this paper , the architectural approach proposed for modeling the underlay system was chosen based upon the N ARX neural network structure. Specifically , we choose the N ARX neural network to implement the cognition task at the cognitiv e engine in each SU. W ith a topology as shown in Fig. 5 for the case of one hidden layer network, the N ARX neural network output can be mathematically represented as [50], 𝑦 ( 𝑛 + 1 ) = 𝑓 𝑦 ( 𝑛 ) , 𝑦 ( 𝑛 − 1 ) , . . . , 𝑦 ( 𝑛 − 𝑑 𝑦 ) ; 𝑢 1 ( 𝑛 ) , 𝑢 1 ( 𝑛 − 1 ) , . . . , 𝑢 1 ( 𝑛 − 𝑑 𝑢 1 ) ; 𝑢 2 ( 𝑛 ) , 𝑢 2 ( 𝑛 − 1 ) , . . . , 𝑢 2 ( 𝑛 − 𝑑 𝑢 2 ) , (18) where 𝑢 1 ( 𝑛 ) , 𝑢 2 ( 𝑛 ) and 𝑦 ( 𝑛 ) denote, respectiv ely , the two inputs and one output of the model at discrete time step 𝑛 , and 𝑑 𝑢 1 ≥ 1 , 𝑑 𝑢 2 ≥ 1 and 𝑑 𝑦 ≥ 1 , 𝑑 𝑢 1 ≥ 𝑑 𝑦 , 𝑑 𝑢 2 ≥ 𝑑 𝑦 are the inputs and output discrete delays, respectively . The 19 nonlinear mapping 𝑓 ( ·) in (18) can be approximated, for example, by a standard multilayer neural network. If the non-linear mapping can be learned accurately by a neural network of moderate size (measured in terms of number of layers and number of artificial neurons in each layer), the resource allocation based on the output of the NARX neural network can be done in real time, since passing the input through the neural network only requires a small number of simple operations. In Fig. 5 each circle represents an “artificial neuron”, an elementary operation unit in the N ARX neural network model. According to the input variables 𝑢 1 ( 𝑛 ) and 𝑢 2 ( 𝑛 ) , the output of 𝑖 -th hidden layer neuron at time step 𝑛 is obtained as: 𝐻 𝑖 ( 𝑛 ) = 𝜙 1 𝑑 𝑢 1 𝑟 = 1 𝑤 𝑖𝑟 𝑢 1 ( 𝑛 − 𝑟 ) + 𝑑 𝑢 2 𝑘 = 1 𝑤 𝑖 𝑘 𝑢 2 ( 𝑛 − 𝑘 ) + 𝑑 𝑦 𝑙 = 1 𝑤 𝑖 𝑙 𝑦 ( 𝑛 − 𝑙 ) + 𝑎 , (19) where 𝑤 𝑖𝑟 is the connection weight between the input neuron 𝑢 1 ( 𝑛 − 𝑟 ) and 𝑖 -th hidden neuron; 𝑤 𝑖 𝑘 is the connection weight between the input neuron 𝑢 2 ( 𝑛 − 𝑘 ) and 𝑖 -th hidden neuron; 𝑤 𝑖 𝑙 is the connection weight between the 𝑖 -th hidden neuron and output feedback neuron 𝑦 ( 𝑛 − 𝑙 ) ; 𝑎 is the bias of the hidden layer (not explicitly shown in Fig. 5) and 𝜙 1 ( ·) is called the “activ ation function” for the hidden layer . Combining the hidden layer output, the final prediction can be giv en as follows: ˆ 𝑦 ( 𝑛 ) = 𝜙 2 𝑛 ℎ 𝑖 = 1 𝑤 𝑖 𝐻 𝑖 ( 𝑛 ) + 𝑏 , (20) where 𝑤 𝑖 is the connection weight between the 𝑖 -th hidden neuron and predicted output; 𝑛 ℎ is the number of neurons in the hidden layer; b is the bias of the predicted output; and 𝜙 2 ( ·) is the output layer acti v ation function. In our implementation of the NARX neural neto wrk, the activ ation function 𝜙 1 ( ·) for the hidden layer is a sigmoid function while the activ ation function 𝜙 2 ( ·) used for the output layer is linear (the input layer is not truly formed by artificial neurons but rather it is con v entionally included as a representation of the connections of inputs into the neural network). Fig. 6 illustrates the block diagram of an SU with its cognitive engine based on the NARX neural network, as well as other processing steps associated with the inputs and output of the neural network. The function of this cogniti ve engine will be the setting of power control and AMC parameters for a transmitting SU, by predicting for different 20 Fig. 6. Block diagram of an SU with a cognitive engine based on the NARX neural network. transmit settings the throughput ˆ 𝑇 (equiv alently the CQI or AMC mode) of the nearest PN link. Under our imposed practical condition of no exchange of information between the primary and secondary networks, a CR can only estimate the modulation order (after performing modulation classification signal processing on the PN transmissions) and immediately has no direct way to kno w the coding rate in use. Moreover , practical limitations further dictate that the modulation classification can only be performed on the one primary transmission that it is being receiv ed with strongest power (usually this is the closest one), making the other transmissions be interference. It is assumed that the estimation of modulation type does not rely on the SU accessing any information from the PN feedback channel and is error free using any of the methods existing in the literature (e.g. [23] or [24]). As mentioned, the modulation order setting of a primary link provides a coarse indication of its experienced SINR, and accordingly of its experienced lev el of interference imposed by the transmissions in the SN. Since this created level of the interference has direct relation with the transmit power setting at each SU, we configure the NARX neural network cognitive engine to ha ve as inputs the most recent v alues of assigned transmit po wer le vels at the SU ( 𝑢 1 ( 𝑛 ) ) and, corresponding to these transmit power levels, the modulation order ( 𝑢 2 ( 𝑛 ) ) being used in the closest primary link that is inferred using a modulation classification technique. The output of the N ARX neural network cogniti ve engine is the predicted throughput ˆ 𝑇 ( 𝑛 ) at the primary link closest to the transmitting CR. The predicted throughput on a primary link corresponds to a choice of AMC mode. The proposed NARX neural network undergoes a training process to determine the v alues of its weights and biases. In this training process, the weight and bias values are updated according to the Lev enberg-Marquardt optimization method. This method in v olves a back-propagation algorithm to compute the gradients of the prediction error cor - responding to the artificial neurons [51]. It is known that in the case of function approximation problems, for the neural networks containing up to a few hundred weights, the Levenber g-Marquardt algorithm will hav e the fastest 21 con ver gence [52]. Mean square error (MSE) was chosen as the prediction error metric: 𝑀 𝑆 𝐸 = 1 𝑁 𝑁 𝑖 = 1 ( 𝑒 𝑖 ) 2 = 1 𝑁 𝑁 𝑖 = 1 ( 𝑇 𝑖 − ˆ 𝑇 𝑖 ) 2 , (21) where 𝑁 is the size of training data set, 𝑇 𝑖 and ˆ 𝑇 𝑖 are target and predicted values, respectiv ely . In order to find the number of hidden neurons and depth of the tap-delay lines in the N ARX neural network, we perform a thorough set of experiments with different configurations. The best performing structure was found to be with 50 hidden neurons and 7 time delay steps. Fig. 7 illustrates the performance of the N ARX neural network for a primary network load equal to 0.64. Further details regarding the generation of the target prediction v alues 𝑇 𝑖 used during training are provided in the next Section. Fig. 7. Throughput prediction performance of the N ARX neural network. Best v alidation performance is 0.10825 at epoch 2. The underlay DSA operation of an SU based on the NARX neural network cogniti ve engine is as follows: First the SUs a void transmission while the PN initially adjusts its power and AMC parameters using the iterativ e po wer control algorithm (2). During this stage which earlier was denoted as listening stage, the SUs listen to the PN transmissions and infer the modulation order used by their closest primary link. At this stage, each transmitting SU obtains an estimate of the modulation order used by their corresponding nearest primary link when the SN is not transmitting. Next, each SU proceeds to send a series of short probe messages configured with different transmit powers. T o devise the new adapted modulation order , each SU performs modulation classification for each probe message on its nearest primary link. The sequence of probe message transmit po wers and corresponding estimated modulation orders at the nearest primary link are fed to the N ARX neural network, which provides the sequence of corresponding estimated throughput v alues at the nearest primary link, ® ˆ 𝑇 . Note that this sequence of estimated throughput values includes the one with no transmissions from the SN. Since estimating the throughput is equiv alent to estimating the CQI and the corresponding full AMC mode (channel coding rate and modulation order), the N ARX neural network is able 22 to provide an estimate of the nearest primary link SINR with a finer resolution than what could be deriv ed from the modulation classification alone that is present at its input. The SU can use the sequence of estimated throughput values to infer what would be the effect of its transmission on the nearest primary link by comparing the change in throughput v alue against that without the SN transmission. As seen in Fig. 6, the SU uses this information to find its own transmission parameters. W e will consider two approaches for the SUs to choose transmit settings. In the first one, the SU chooses the maximum transmit po wer value that is estimated to keep the modulation order at its nearest primary link unchanged. In the second approach, the SU chooses the maximum transmit po wer value that keeps the relativ e change in throughput of its nearest primary link below a predetermined limit. Note that the second approach differs from the first one in that it fully uses the advantage provided by the N ARX neural network in providing the finer resolution full AMC mode inference on the nearest primary link, instead of the coarser inference on modulation order that the first scheme is based on. Additionally , for both approaches, those SUs that estimate that their closest primary link is transmitting in the lowest rate AMC mode when the SN is not transmitting (because of already experiencing a very low SINR, likely leaving no room for added interference from the SN) are prevented from transmitting. This guarantees that the reduction in the average rate of the primary link experiencing the poorest channel quality (CQI equal to 1) is minimized. Going back to Fig. 2 helps to gain an intuition into the N ARX neural network cognitiv e engine operation. The N ARX neural network receiv es as one input the possible SU’ s transmit power le vels organized in sequence and, as another input, the corresponding modulation order sensed from the nearest primary link. During training, the NARX neural network learns to predict the throughput values at the nearest primary link that correspond to the two input sequences. Considering (16), we can think that the sequence of transmit po wer v alues that is input to the N ARX neural network will yield a range of interference values, which will correspond to a “segment" of SINR v alues in the abscissa of Fig. 2. The position of this segment within the range of SINR v alues depends on the many factors reflected in (16) (e.g. primary channel gain, interference from other SUs, etc.) but the N ARX neural network has a sense of where the segment is thanks to the reference provided by the sequence of modulation orders at the input (e.g. if for the setup in Fig. 2, the sequence of modulation schemes are QPSK and 16QAM, the SINR segment is around 10 dB). During training, the N ARX neural network is presented with multiple different such segments from dif ferent wireless en vironment scenarios, ev entually learning the throughput vs. SINR AMC performance curve. During operation of the 23 N ARX neural network (the testing phase in machine learning terms), sensing the sequence of modulation schemes that results from the sequence of probe messages with different po wer settings allows the N ARX neural network to localize the segment of SINR values for the nearest primary link (in effect, finding the network scenario presented during training that best matches the existing wireless en vironment) and, consequently , predicts the corresponding throughput from the AMC performance curve. V I . S I M U L A T I O N R E S U LT S The performance of the presented technique was ev aluated through Monte Carlo simulations (150 runs) based on a PN “playground” consisting of a fiv e-by-fi ve BSs grid ( 𝑁 𝑃 𝐵 𝑆 = 25 ) with neighboring base stations separated by a distance of 200 m. T o av oid edge ef fects in the playground, the grid wraps around all its edges. One channel was singled out in the experiment and any of the base stations can hav e this channel activ e. In order to reflect realistic AMC settings, we assumed that all transmissions are based on an L TE 2x2 MIMO configuration, and that the channel of interest is one resource block with a bandwidth of 180 kHz. As noted earlier, we assumed that there are 𝑁 𝑃 activ e base stations that are using the same channel to communicate with their respectively assigned PU receivers. The location of the 𝑁 𝑃 PU recei vers is determined at random using a uniform distribution with the limitation that no base station could have more than one receiver assigned to it. Also, the recei vers were connected to the base station from which they received the strongest signal. Transmit powers in the primary network were limited to the range between -20 and 40 dBm. The transmit power assignment for the 𝑖 th. activ e primary link ( 𝑖 = 1 , 2 , . . . , 𝑁 𝑃 ) follo ws the same algorithm as in (2). Each primary transmission considers the other network transmissions as out of network interference akin to background noise. In the simulation, the SN consisted of 𝑁 𝑆 = 4 transmit-receiv e pairs of CRs, with the transmitters placed at random (also with a uniform distribution) on the PN playground, around their respectiv ely assigned transmitter within a distance not exceeding 50 m. In the simulation setup we intended to reflect a situation where the PN had somewhat more capabilities (achieving larger throughput and communication range) than the SN because of being the incumbent to the spectrum band under consideration. Therefore, we assumed that the SUs were smaller devices with transmit po wer in the range of -30 to 20 dBm. T wenty equally spaced power lev els in this range are considered as the set of allowed settings for transmission. The operation of the SN, as mentioned before, is fully autonomous and ad-hoc and the 24 transmission control algorithm is distributed. It is also assumed that the SUs know the primary transmission protocol and are able to synchronize their operation with the primary transmissions. All links assumed a path loss model for urban area giv en by 𝐿 = 128 . 1 + 37 . 6 log 𝑑 + 10 + 𝑆 (in dBs), where 𝑑 is the distance between transmitter and receiv er in km, 𝑆 is the shadowing loss (modeled as a zero-mean Gaussian random variable with 6 dB standard deviation) and the penetration loss is fixed at 10 dB, [53]. Our assumed small scale fading follo ws a Pedestrian B model from [27]. Noise power lev el was set at -130 dBm. It should be noted that all transmissions adopt AMC to adapt their transmission to the quality of their respectiv e link. Each neural network was trained / v alidated with a data set of 10000 samples collected from a network simulation with the setup just described. A subset of the data set (7000 samples or 70% of the data set) was used to train the neural network and to present the CRs with ne w en vironmental conditions. The rest of data was used to compare the prediction performed by the trained neural network with the actual expected performance in order to encounter new en vironment conditions. In order to generate training data for the neural network cognitiv e engine, a comparable SN was de vised that maintained the ability to use the estimated modulation order of the nearest primary link but without the cognitiv e engine sho wn in Fig. 6. Instead, this comparable system implemented a distributed power control algorithm modified to incorporate the modulation order of the nearest primary link. A number of algorithms had been proposed for distributed power control in ad-hoc wireless network. One of the first ones, and the precursor to man y related variants, is the Foschini-Miljanic algorithm, [54], which implements an iterati ve distributed power control process so as to meet a target SINR. W e adopted this iterativ e po wer allocation algorithm for the alternative SN that generated the data set to train the N ARX-NN cognitiv e engine at each SU. Specifically , po wer is calculated for a secondary link 𝑖 at each iteration 𝑚 using the update formula, 𝑃 𝑠 𝑖 [ 𝑚 + 1 ] = 𝛽 𝑖 𝛾 𝑠 𝑖 [ 𝑚 ] 𝑃 𝑠 𝑖 [ 𝑚 ] , (22) where 𝑃 𝑠 𝑖 is the transmit power , 𝛽 𝑖 is the target SINR and 𝛾 𝑠 𝑖 [ 𝑚 ] is the actual SINR measured in the 𝑚 th. iteration which can be calculated through (17). The fact that this algorithm associates po wer control with a target SINR in our case is a useful feature because the target SINR, when met, also determines the modulation order to be used as follows [21], 𝑇 ( 𝑠 ) 𝑖 = log 2 ( 1 + 𝑘 𝛾 ( 𝑠 ) 𝑖 ) , 𝑖 = 1 , 2 , . .. , 𝑁 𝑆 . (23) 25 Consequently , we can think that instead of having a set of possible [modulation, channel code] pairs, now we have a set of target SINRs to choose from. Let 𝔅 = { 𝑏 1 , 𝑏 2 , . . . , 𝑏 𝐾 } be this set, where target SINRs 𝑏 𝑖 ’ s are assumed to be sorted in ascending order . Of course, reducing the target SINR will result in decreasing the transmit po wer . As a consequence, the algorithm provides the mechanisms to both adapt transmit po wer and AMC settings in a distributed way . Moreov er , for fair comparison to the system with the proposed N ARX neural network cogniti ve engine, the transmit po wer from SUs also needs to be constrained by the goal to not degrade the SINR of the closest primary network link to the extent of reducing the modulation order (not having the N ARX neural network, this SN we are comparing against cannot operate based on the use of throughput inferred for the nearest primary link and can only make use of the modulation order estimated from the modulation classification process). Modifying the Foschini- Miljanic algorithm by reducing the target SINR allows to manage this constraint by resulting in a reduction in the SU transmit power . As such, we adopted for the control of CR transmissions in the alternati ve SN this modified version of the Foschini-Miljanic algorithm, where the SU target SINR is progressi vely reduced until there is no change in the modulation order of the nearest primary link. W e note here that while it is certainly possible to use one of the many existing enhancements to the Foschini-Miljanic algorithm, we chose to use the original version without improvements because its provides a baseline performance measure and because this po wer control algorithm or a v ariation of it are not the contribution of our work. Of course, the PUs in this system maintained the power allocation algorithm proposed in [21], as explained in Sect. II. W e also note that this benchmark SN constitutes an implementation of the central principles of [16] while also managing practical considerations not addressed therein (e.g. multiple links in the SN and PN, distributed, ad-hoc operation of the SN, etc.), and, as such, serves the purpose of providing an indication of the performance improvements of our proposed technique versus prior works. Moreov er , as briefly mentioned earlier, note that in AMC the modulation order transmitting the smallest number of bits per symbol is used for the smallest operating SINRs (because it is more resilient to interference and noise). When the interference from the SN increases, the primary links that were already using the smallest possible modulation orders when there were no secondary transmissions will not switch to other modulation orders because there is simply no other modulation order with fewer bits per symbols to switch to. This means that transmissions from an SU that otherwise would generate a change in modulation order would not result in any change when the nearest primary link is already transmitting with the modulation order with smallest bits per symbol. Moreover , primary links using this 26 modulation order , do so because their SINR is at the lower range of the operating SINRs, which implies that they are at a link state that likely may not lea ve much room for added interference from SUs. Because of these reasons, and in the interest of prioritizing the protection of primary links against excessiv e SN interference, we configured the alternativ e SN so that a CR will not transmit if it senses that its nearest primary link is using the lowest modulation order when the SN is not transmitting (as explained in Sect. V, our proposed technique implements a mechanisms with the same spirit but based on checking for the smallest CQI at the nearest primary link when the SN is not transmitting, instead of smallest modulation order). Figs. 8 through 10 study the throughput performance in the primary and secondary networks for our presented technique and contrast them against other schemes. As indicated in Sect. V, for the presented technique we considered two approaches for the SUs to choose transmit settings. The first approach, labeled in the figures as “ PN+SN- NN Cog. Eng.- Modulation ”, features our proposed cogniti ve engine with the capability for full AMC mode estimation at the nearest primary link, but it makes a limited use of this capability by making the SU choose the maximum transmit power value that is estimated to keep unchanged the modulation order (but not necessarily the channel coding rate) at its nearest primary link. The second approach makes full use of the cognitiv e engine’ s throughput (full AMC mode) estimation capabilities at the nearest primary link, by making the SU choose the maximum transmit power value that is estimated to not change the nearest primary link throughput beyond a maximum relativ e change value. This second approach is itself divided into a case where one probe message is sent for each possible po wer setting (for a total of twenty probe messages) and a second case that e xplores a reduction in the overhead from transmitting probe messages which transmits just sev en messages and uses interpolation to complete the information for the rest of av ailable transmit power settings. T o show ho w our technique is able to lev erage the estimation of the full AMC mode and provide each SU with a fine control ov er the interference it imposes to the nearest primary transmission link, we obtained results for three different limits on relativ e av erage throughput change in the PN: 2% , 5% and 10% . In the figures, we labeled the results when sending all probe messages as “ PN+SN- NN Cog. Eng- 2%- All pr obe msgs. ” for a limit on relative av erage throughput change in the PN of 2% , “ PN+SN- NN Cog. Eng- 5%- All pr obe msgs. ” for a limit on relativ e av erage throughput change in the PN of 5% , and “ PN+SN- NN Cog. Eng- 10%- All pr obe msgs. ” for a limit on relativ e a verage throughput change in the PN of 10% . Similarly , for the case when sending sev en probe messages, the labels for 2% , 5% and 10% limit on relati ve av erage throughput change in the PN are 27 respectiv ely “ PN+SN- NN Cog. Eng- 2%- Seven pr obe msgs. ”, “ PN+SN-NN Cog. Eng- 5%- Seven pr obe msgs. ” and “ PN+SN- NN Cog . Eng- 10%- Seven pr obe msgs. ”. The performance of these realizations of the proposed underlay DSA technique is compared in the figures against other schemes. The first such contrasting scheme, labeled in the figures as “ PN+SN- Adapted F oschini-Miljanic ”, is the same system used to collect training data and described earlier in this Section as the alternati ve SN. Recall that this scheme lacks the N ARX neural network cognitiv e engine’ s capability to predict the full AMC mode at the nearest primary link. In addition, we considered two schemes that select transmit power for the SUs based on an exhausti v e search across all possible setting permutations. In contradiction with our goal to av oid any exchange of information between the primary and secondary networks, these two schemes also incorporate the ability to perfectly know the CQI on the primary links as if the SN had access to the control feedback channels in the PN. The first exhausti ve search scheme, labeled “ PN+SN- Exh. searc h-Max PU throughput ”, finds across all possible SUs transmit po wer permutations, the setting that results in no change in modulation order at any primary link and maximum av erage throughput in the PN. The second exhausti ve search scheme, labeled “ PN+SN- Exh. searc h-Min PU thr oughput ”, fa vors the average throughput at the SN by finding across all possible SUs transmit power permutations, the setting that results in no change in modulation order at any primary link and minimum average throughput in the PN. Clearly , the two exhausti ve search curves present extreme performance results based on ideal setups. Finally , Fig. 8 includes a curve, “ PN without SN ”, which shows the av erage throughput achie ved by the PN when the SN is not present. Fig. 8. A verage throughput in primary network. Fig. 8 sho ws the a verage throughput achieved for the PN as a function of the PN load, 𝑁 𝑃 / 𝑁 𝑃 𝐵 𝑆 , while Fig. 9 28 shows the change in this throughput relativ e to the “PN without SN" case. It can be seen in both figures that the use of the proposed N ARX neural network cognitiv e engine results in SUs transmit settings that reduces the av erage throughput in the PN much less than the case when the modified Foschini-Miljanic algorithm is used in the SU. Moreov er , in the figures, the “PN+SN- Exh. search-Min PU throughput” curv e illustrates the extent to which the av erage throughput in the PN can be affected without changing the modulation order at the nearest primary links (as much as 17%). This indicates that considering only the modulation order provides an initial means for implementing a fully autonomous underlay DSA but with the limitations associated with the coarse indication of the primary links SINR given only by the modulation order . The “PN+SN- Adapted Foschini-Miljanic” and the “PN+SN- NN Cog. Eng.- Modulation” schemes, which both suffer from the limitation of relying on considering modulation order only , show better performance because SU transmit power is chosen in a more conserv ativ e way in terms of reducing effects to the primary network, instead of conducting an exhausti v e search for the setting that results in minimum av erage throughput in the PU. Ne vertheless, because of relying on modulation order inference only , the “PN+SN- Adapted Foschini-Miljanic” and the “PN+SN- NN Cog. Eng.- Modulation” schemes result in relativ e reduction in the PN average throughput by as much as 13.5% and 9.5%, respecti vely . The best performance in terms of controlling the effect of SN transmissions on the PN is achieved with our proposed scheme using the inference of the primary links’ full AMC mode (in actuality , the throughput) provided by the N ARX neural network cogniti ve engine. This is seen through the results obtained for the two cases (transmitting either all or sev en probe messages) designed on the premise of limiting the maximum relative change in av erage throughput at the nearest primary link, for which we show results for 2%, 5% and 10% relativ e change limit. Moreov er , these schemes include the means to control as desired the lev el of SN effect on the PN (by setting the limit maximum relative change). In fact, the “PN+SN- NN Cog. Eng- 2%- All probe messages” along with “PN+SN- NN Cog. Eng- 2%- Seven probe messages” curves ex emplify the very fine lev el of control that is possible to achieve with the proposed approach. Fig. 9 shows that the very fine lev el of control seen with our proposed scheme is achiev ed at all primary network loads, except at the lowest value of 0.16, when the relative change in average PN throughput exceeds the 2% limit in only 1% when sending all probe messages and in 1.5% when sending se ven probe messages. For the rest of cases, only in the case of 5% limit, sending sev en probe messages, and at the lowest primary network load, the relativ e change in PN av erage throughput is exceeded by just 0.5%. These differences are attributed to errors in estimating 29 Fig. 9. Relativ e throughput change in primary network. the throughput at the PN, which are discussed more in detail later in this Section. Also, the dif ferences are only seen at the smallest PN network load of 0.16 because of the larger sensiti vity of the relativ e change in PN average throughput with lower PN load as was previously highlighted for Fig. 3. Fig. 9 also shows that the scheme where a fraction of probe messages is used yields significant reduction in the transmission ov erhead of probe messages (roughly a threefold reduction) without much sacrifice in performance (maximum 3.5% instead of 2% actual achie ved relativ e change in PN throughput compared to 3% maximum change with all the probe messages, and maximum 5.5% instead of 5% actual achiev ed relative change in PN throughput compared to 5% maximum change with all the probe messages). Finally , the curve “PN+SN- Exh. search-Max PU throughput” coincides with the “PN without SN” curve as the exhausti ve search solution that maximizes a verage PN throughput is essentially the one with no transmissions in the SN (with one cav eat to be discussed in Fig. 10). Considering Fig. 9 in the context of the bottom plot of Fig. 3, we can see that the relativ e throughput change in the PN when using our proposed technique corresponds to points at equiv alent background noise po wer between -96 and -85 dBm (depending on the target maximum PN relative throughput change setting) just to the left of the “elbow" of the curves in Fig. 3. Equiv alently , in the context of Fig. 4, the related equation (15), and also depending on the preset maximum allo wed change in PN relati ve throughput our proposed technique leads to equi v alent interference to the PN between 44 and 55 dBm. This result confirms that our proposed technique succeeds in its main goal of autonomously and distributiv ely determining the transmit power of the SUs such that the interference they create remains below the maximum threshold v alue associated with the background noise power le vels that a PN with adaptiv e modulation can 30 sustain. At the same time, the proximity to the “elbow" of the curves in Figs. 3 and 4 of the equiv alent interference lev els generated by the SN, indicates that our proposed algorithm is able to find transmit settings for the SUs that will result in as large SN throughput as could be allowed by the PN interference limit. Fig. 10. A verage throughput in secondary network. Fig. 10 shows the a verage throughput achie ved in the SN as a function of the PN load. Naturally , the more a scheme affects the PN throughput, the lar ger the SN throughput it could achie ve. As such, it can be seen that our approach based on a limit maximum PN relati ve throughout change not only provides the means to control ho w much the PN is affected by the SN, but also it allows to control how large the av erage throughput at the SN is desired to be (at the expense of the PN). Even so, the realization with the more restrictiv e setting for the SN (the one with a maximum PN relativ e throughput change of 2%) still achiev es useful av erage throughput v alues between 180 and 50 kbps for a channel with 180 kHz bandwidth (in case of transmitting sev en probe messages the av erage throughput at the SN is slightly larger which is consistent with the results in Fig. 9). Also, note that at low PN loads, the “PN+SN- Exh. search-Max PU throughput” system sho ws throughput values that imply transmission in the SN. This does not contradict our earlier statement that this result essentially coincides with the “PN without SN” case. Instead, the transmissions in the SN that are seen in this case correspond to infrequent setups where the SUs are located so far away from the few acti ve primary links (consider that this effect occurs only at very low PN loads) that they can transmit with very low power with no practical effect on the PN. 31 Fig. 11 depicts the cumulati ve distribution function (CDF) of the throughput in the SN for dif ferent primary network loads. This figure presents a perspectiv e that explains an added advantage of the N ARX neural network solution compared to the modified Foschini-Miljanic algorithm-based solution. The figure sho ws that in the case of the SN that uses the modified Foschini-Miljanic algorithm, around 15% of the time SUs will be unable to transmit (throughput is zero) when the PN load equals 0.16 and this number increases to around 30% as the PN load increases. This is because the SN that uses the Foschini-Miljanic algorithm is only able to infer the modulation scheme used in the primary link and not the channel coding rate, which leads to SUs not being able to have a finer assessment of their effect on the PN when the nearest primary link is using a modulation “ type 0 ". As a result, and as discussed earlier , in order to protect the PN, those SUs using the modified Foschini-Miljanic scheme for which the nearest primary link use modulation “ type 0 " are blocked from transmitting. In contrast, the proposed technique using N ARX neural network, “ PN+SN-NN Cog.Eng.- Modulation ”, is able to estimate the finer AMC configuration of coding rate setting, making this protection and the blocking of SU unnecessary (except when the nearest link is using the AMC mode for a lowest rate, which corresponds to CQI=1). Consequently , as seen in Fig. 11, the proposed technique increases the transmission opportunities in the SN by the same percentage of time that the SUs are blocked in the case of using the modified Foschini-Miljanic algorithm-based solution. Fig. 11. Cumulative distribution function (CDF) of the throughput in the secondary network. As just seen, a key advantage of the proposed technique follows from the remarkable ability to estimate the channel coding rate used in a primary link. Therefore, we ev aluated the performance of the NARX neural network in estimating 32 the CQI in a primary link (which is equi v alent to the full AMC mode consisting of modulation order and channel coding rate). Fig. 12 shows as a function of the primary network load the relati ve frequency of the absolute error when predicting the CQI for the case of transmitting all probe messages. This Figure sho ws that as the network load increases, the probability of an accurate estimation (prediction absolute error equal to zero) increases and reaches more than 80% for a load equal to 0.48. The Figure shows that, ov erall, the probability of significant errors when predicting CQI is quite small b ut, ne vertheless, we speculate this to be a factor in the (still small) reduction in PN average throughput and in the small difference at low PN loads between the tar get maximum relativ e change in av erage PN throughput and the actual achie ved relativ e change in PN throughput for our schemes based on target maximum PN relativ e throughput change. Fig. 12. CQI estimation performance of the N ARX neural network. V I I . C O N C L U S I O N In this paper we have presented a fully autonomous and distributed underlay DSA technique that is based on a N ARX neural network cognitiv e engine. The NARX neural network of a transmitting secondary network node learns to use the sensed modulation used in the nearest primary link to predict the effect of its transmission on the nearest primary network link. It does this by predicting the throughput or , equi v alently , both the modulation scheme and the channel coding rate resulting from the configuration of adaptiv e modulation and coding at the nearest primary link. Based on this NARX neural network capability , we presented two v ariants for the proposed underlay DSA mechanism: one inspired in the current state of the art, where the SUs choose the maximum transmit po wer value that 33 is estimated to not lead to a change in modulation order at their respectiv e nearest primary link, and a second, more capable mechanism, where the SUs choose the maximum transmit po wer v alue that is estimated to not change their respectiv e nearest primary link throughput beyond a chosen maximum relativ e change value. The performance of the latter proposed underlay DSA mechanism was examined for the cases of sending all or a third of all probe messages. Simulation results show that the proposed technique is able to accurately predict the modulation scheme and channel coding rate used in a primary link without the need to exchange information between the PN and the SN (e.g. access to feedback channels). Simulation results also demonstrated that the proposed technique succeeded in its main goal of determining the transmit power of the SUs such that their created interference remains below the maximum threshold that the primary network can sustain with minimal ef fect on the av erage throughput, along with reducing the transmission ov erhead when sending a fraction of probe messages. At the same time, it was seen that our proposed algorithm is able to find transmit settings for the SUs that will result in as large throughput in the SN as could be allowed by the primary network interference limit. Specifically , for a target PN maximum relati ve av erage throughput change of 2% the proposed scheme is able to maintain the PN relativ e throughput change less than 3% when sending all probe messages, and also less than 3.5% when reducing three times the number of transmitted probe messages, while at the same time achieving useful a verage throughput v alues in the secondary network between 180 and 50 kbps for a channel with 180 kHz bandwidth. W e also discussed ho w the ability of our proposed technique to predict the full AMC mode (not just the modulation scheme) results in a significant increase in the transmission opportunities in the SN compared to schemes that only use the modulation classification information. R E F E R E N C E S [1] Force, Spectrum Policy T ask, “Spectrum policy task force report et docket no. 02-135, ” US F ederal Communications Commission , 2002. [2] S. Haykin, “Cognitive radio: brain-empowered wireless communications, ” IEEE journal on selected areas in communications , vol. 23, no. 2, pp. 201–220, 2005. [3] M. Song, C. Xin, Y . Zhao, and X. Cheng, “Dynamic spectrum access: from cognitive radio to network radio, ” IEEE W ir eless Communications , vol. 19, no. 1, pp. 23–29, February 2012. [4] A. Goldsmith, S. A. Jafar , I. Maric, and S. Sriniv asa, “Breaking spectrum gridlock with cognitive radios: An information theoretic perspective, ” Pr oceedings of the IEEE , vol. 97, no. 5, pp. 894–914, May 2009. [5] H. Hu and Q. Zhu, “Dynamic spectrum access in underlay cognitive radio system with sinr constraints, ” in 2009 5th International Confer ence on W ir eless Communications, Networking and Mobile Computing . IEEE, 2009, pp. 1–4. [6] X. Kang, R. Zhang, Y .-C. Liang, and H. K. Garg, “Optimal power allocation strategies for fading cognitiv e radio channels with primary user outage constraint, ” IEEE Journal on Selected Areas in Communications , vol. 29, no. 2, pp. 374–383, 2011. 34 [7] L. Musavian and S. Aïssa, “Capacity and power allocation for spectrum-sharing communications in fading channels, ” IEEE T ransactions on W ir eless Communications , vol. 8, no. 1, pp. 148–156, 2009. [8] A. Ghasemi and E. S. Sousa, “Capacity of fading channels under spectrum-sharing constraints, ” in 2006 IEEE International Conference on Communications , vol. 10, June 2006, pp. 4373–4378. [9] Y . Y ang, H. Ma, and S. Aissa, “Cross-layer combining of adaptive modulation and truncated arq under cognitive radio resource requirements, ” IEEE T ransactions on vehicular technology , vol. 61, no. 9, pp. 4020–4030, 2012. [10] K. Eswaran, M. Gastpar , and K. Ramchandran, “Bits through arqs: Spectrum sharing with a primary pack et system, ” in 2007 IEEE International Symposium on Information Theory , June 2007, pp. 2171–2175. [11] J. C. F . Li, W . Zhang, A. Nosratinia, and J. Y uan, “Sharp: Spectrum harvesting with arq retransmission and probing in cognitive radio, ” IEEE T r ansactions on Communications , vol. 61, no. 3, pp. 951–960, March 2013. [12] Z. Rezki and M.-S. Alouini, “Ergodic capacity of cognitive radio under imperfect channel-state information, ” IEEE T ransactions on V ehicular T echnology , vol. 61, no. 5, pp. 2108–2119, 2012. [13] E. Kayalvizhi and B. Gopalakrishnan, “Estimation of optimal channel gain in cognitive radio networks using bisectional algorithm, ” International Journal of Advanced Networking and Applications , vol. 11, no. 1, pp. 4171–4176, 2019. [14] 3rd Generation Partnership Project Std. S25.214 V5.11.0, “3GPP T echnical Specification Group Radio Access Network Physical layer procedures (FDD) (Release 5), ” T ech. Rep., 2005. [15] A. S. 802.11b 1999 (R2003), “Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications: Higher-Speed Physical Layer Extension in the 2.4 GHz Band, ” T ech. Rep., 1999. [16] R. Zhang, “On acti ve learning and supervised transmission of spectrum sharing based cognitive radios by exploiting hidden primary radio feedback, ” IEEE T ransactions on Communications , vol. 58, no. 10, pp. 2960–2970, October 2010. [17] L. Zhang, M. Xiao, G. Wu, G. Zhao, Y .-C. Liang, and S. Li, “Proactive cross-channel gain estimation for spectrum sharing in cognitive radio, ” IEEE Journal on Selected Areas in Communications , vol. 34, no. 10, pp. 2776–2790, 2016. [18] C. T arhini and T . Chahed, “On capacity of ofdma-based ieee802. 16 wimax including adapti ve modulation and coding (amc) and inter-cell interference, ” in Local & Metropolitan Area Networks, 2007. LANMAN 2007. 15th IEEE W orkshop on . IEEE, 2007, pp. 139–144. [19] J. Y ang, N. Tin, and A. K. Khandani, “ Adaptive modulation and coding in 3g wireless systems, ” in 56th V ehicular T echnology Confer ence , vol. 1. IEEE, 2002, pp. 544–548. [20] F . Zhou, Y . W u, R. Q. Hu, Y . W ang, and K.-K. W ong, “Energy-ef ficient noma enabled heterogeneous cloud radio access networks, ” arXiv pr eprint arXiv:1801.01996 , 2018. [21] X. Qiu and K. Chawla, “On the performance of adaptive modulation in cellular systems, ” IEEE Tr ansactions on Communications , vol. 47, no. 6, pp. 884–895, Jun 1999. [22] C. M. Spooner and W . A. Gardner , “The cumulant theory of cyclostationary time-series. ii. dev elopment and applications, ” IEEE T ransactions on Signal Processing , vol. 42, no. 12, pp. 3409–3429, Dec 1994. [23] A. Fehske, J. Gaeddert, and J. H. Reed, “ A new approach to signal classification using spectral correlation and neural networks, ” in Fir st IEEE International Symposium on New F r ontiers in Dynamic Spectrum Access Networks, 2005. DySP AN 2005. , Nov 2005, pp. 144–150. [24] H. Abuella and M. K. Ozdemir, “ Automatic modulation classification based on kernel density estimation, ” Canadian Journal of Electrical and Computer Engineering , vol. 39, no. 3, pp. 203–209, Summer 2016. 35 [25] J. M. Cioffi, Course Notes for Digital Communications: Signal Pr ocessing . Stanford Bookstore Custom Publishing, Stanford, CA, 2007. [26] C. Mehlführer , M. Wrulich, J. C. Ikuno, D. Bosanska, and M. Rupp, “Simulating the long term evolution physical layer, ” in 2009 17th Eur opean Signal Processing Conference , Aug 2009, pp. 1471–1478. [27] R. I.-R. M. . ITU-R Recommendations, “Guidelines for Evaluation of Radio T ransmission T echnologies for IMT -2000, ” T ech. Rep., 1997. [28] J. Cavers, “V ariable-rate transmission for rayleigh fading channels, ” IEEE T ransactions on Communications , vol. 20, no. 1, pp. 15–22, Feb 1972. [29] B. V ucetic, “ An adaptive coding scheme for time-varying channels, ” IEEE T ransactions on Communications , vol. 39, no. 5, pp. 653–663, May 1991. [30] T . R. Newman, B. A. Barker, A. M. W yglinski, A. Agah, J. B. Evans, and G. J. Minden, “Cognitive engine implementation for wireless multicarrier transceivers, ” W ir eless Communications and Mobile Computing , vol. 7, no. 9, pp. 1129–1142, 2007. [31] M. Nrgaard, O. E. Ravn, N. K. Poulsen, and L. K. Hansen, Neural Networks for Modelling and Contr ol of Dynamic Systems: A Practitioner’ s Handbook , 1st ed. Secaucus, NJ, USA: Springer-V erlag New Y ork, Inc., 2000. [32] G. E. Box, G. M. Jenkins, G. C. Reinsel, and G. M. Ljung, T ime series analysis: forecasting and control . John Wile y & Sons, 2015. [33] W . Lyu, Z. Zhang, C. Jiao, K. Qin, and H. Zhang, “Performance ev aluation of channel decoding with deep neural networks, ” arXiv pr eprint arXiv:1711.00727 , 2017. [34] S. Navabi, C. W ang, O. Y . Bursalioglu, and H. Papadopoulos, “Predicting wireless channel features using neural networks, ” arXiv preprint arXiv:1802.00107 , 2018. [35] T . Luo and S. G. Nagarajan, “Distributed anomaly detection using autoencoder neural networks in wsn for iot, ” IEEE International Confer ence on Communications , 2018. [36] V . K. Tumuluru, P . W ang, and D. Niyato, “ A neural network based spectrum prediction scheme for cognitive radio, ” in 2010 IEEE International Confer ence on Communications , May 2010, pp. 1–5. [37] Y . Y u, T . W ang, and S. C. Liew , “Deep-reinforcement learning multiple access for heterogeneous wireless networks, ” IEEE International Confer ence on Communications , 2018. [38] A. Sorjamaa, J. Hao, N. Reyhani, Y . Ji, and A. Lendasse, “Methodology for long-term prediction of time series, ” Neurocomputing , vol. 70, no. 16-18, pp. 2861–2869, 2007. [39] S. Haykin and X. B. Li, “Detection of signals in chaos, ” Pr oceedings of the IEEE , vol. 83, no. 1, pp. 95–122, 1995. [40] J. C. Principe, N. R. Euliano, and W . C. Lefebvre, Neural and adaptive systems: fundamentals through simulations . W iley New Y ork, 2000, vol. 672. [41] J. L. Elman, “Finding structure in time, ” Cognitive science , vol. 14, no. 2, pp. 179–211, 1990. [42] B. A. Pearlmutter, “Gradient calculations for dynamic recurrent neural networks: A survey , ” IEEE T ransactions on Neural networks , vol. 6, no. 5, pp. 1212–1228, 1995. [43] Y . Bengio, P . Simard, and P . Frasconi, “Learning long-term dependencies with gradient descent is difficult, ” IEEE transactions on neural networks , vol. 5, no. 2, pp. 157–166, 1994. [44] T . Lin, B. G. Horne, and C. L. Giles, “How embedded memory in recurrent neural network architectures helps learning long-term temporal dependencies, ” Neural Networks , vol. 11, no. 5, pp. 861–868, 1998. 36 [45] T . Lin, B. G. Horne, P . T ino, and C. L. Giles, “Learning long-term dependencies in narx recurrent neural networks, ” IEEE T ransactions on Neural Networks , vol. 7, no. 6, pp. 1329–1338, 1996. [46] E. Diaconescu, “The use of narx neural networks to predict chaotic time series, ” WSEAS T ransactions on Computer Resear ch , vol. 3, no. 3, pp. 182–191, 2008. [47] J. M. P . Menezes and G. A. Barreto, “Long-term time series prediction with the narx network: An empirical ev aluation, ” Neur ocomputing , vol. 71, no. 16, pp. 3335 – 3343, 2008, advances in Neural Information Processing (ICONIP 2006) / Brazilian Symposium on Neural Networks (SBRN 2006). [48] H. Allende, C. Moraga, and R. Salas, “ Artificial neural networks in time series forecasting: A comparativ e analysis, ” Kybernetika , vol. 38, no. 6, pp. 685–707, 2002. [49] T .-N. Lin, C. L. Giles, B. G. Horne, and S.-Y . Kung, “ A delay damage model selection algorithm for narx neural networks, ” IEEE T ransactions on Signal Processing , vol. 45, no. 11, pp. 2719–2730, 1997. [50] I. J. Leontarits and S. A. Billings, “Input-output parametric models for non-linear systems part i: deterministic non-linear systems, ” International Journal of Control , vol. 41, no. 2, pp. 303–328, 1985. [51] H. Mirzaee, “Long-term prediction of chaotic time series with multi-step prediction horizons by a neural network with levenber g–marquardt learning algorithm, ” Chaos, Solitons & F ractals , vol. 41, no. 4, pp. 1975–1979, 2009. [52] E. Diaconescu, “The use of narx neural networks to predict chaotic time series, ” Wseas T ransactions on computer resear ch , vol. 3, no. 3, pp. 182–191, 2008. [53] G. TSG-RAN#148, “L TE physical layer framework for performance verification, Document R1-070674, ” T ech. Rep., 2007. [54] G. J. Foschini and Z. Miljanic, “ A simple distributed autonomous power control algorithm and its con vergence, ” IEEE T r ansactions on V ehicular T echnology , vol. 42, no. 4, pp. 641–646, Nov 1993.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment