A Way Around UMIP and Descriptor-Table Exiting via TSX-based Side-Channel
💡 Research Summary
The paper presents a novel side‑channel attack that leverages Intel Transactional Synchronization Extensions (TSX) to discover the kernel‑mode addresses of the Global Descriptor Table (GDT) and Interrupt Descriptor Table (IDT). Even after the deployment of Meltdown and Spectre mitigations (KAISER/KPTI) and in environments protected by Windows Virtualization‑Based Security (VBS) or Hyper‑V, the authors demonstrate that these descriptor tables remain partially exposed because the processor must keep a minimal kernel mapping for handling system calls and interrupts.
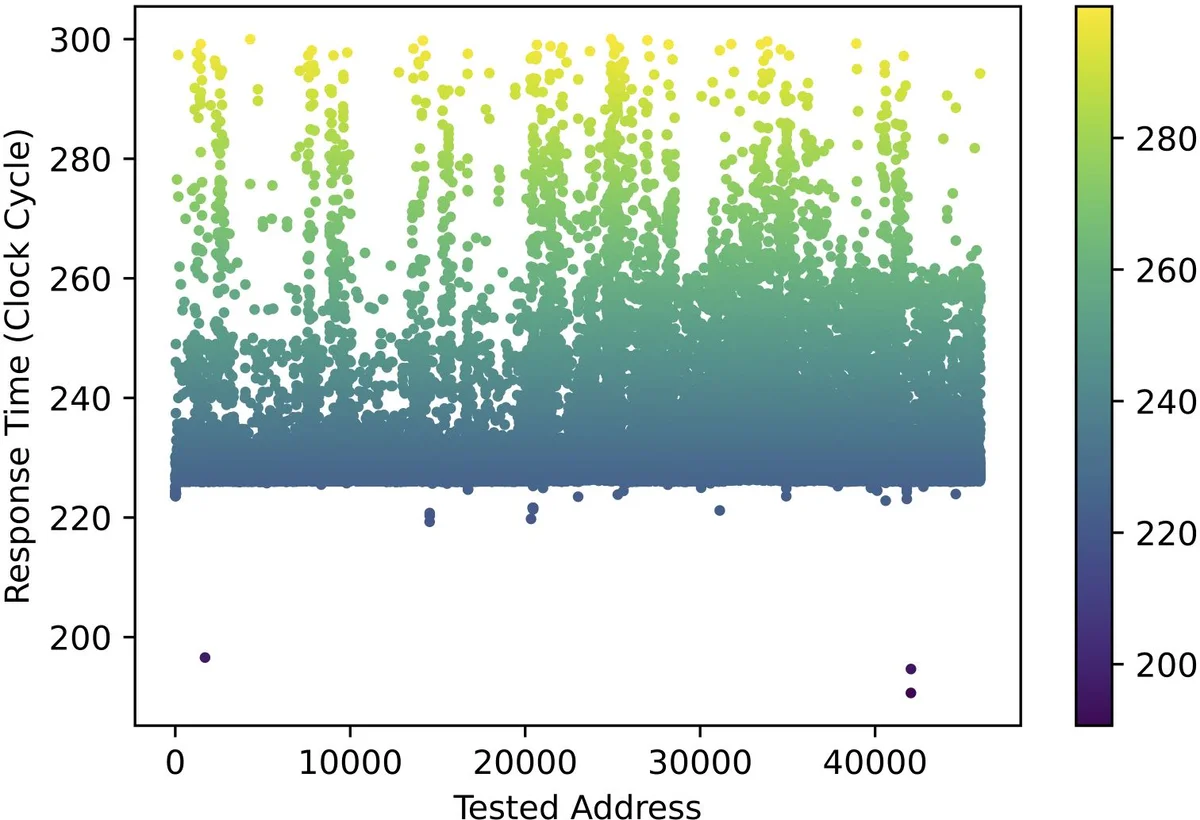
The core idea is to execute privileged instructions such as SGDT or SIDT inside a TSX transaction. If the instruction would normally raise a #GP fault because User‑Mode Instruction Prevention (UMIP) is active, the fault is suppressed by the transaction rollback, and the user process continues unharmed. By measuring the subtle cache‑state differences before and after the rollback, the attacker can infer whether the target address was mapped (i.e., the instruction succeeded) or not. Using a binary‑search strategy over the kernel address space, the exact virtual addresses of GDT and IDT are recovered with high reliability.
Once the addresses are known, two exploitation paths are described. First, the attacker injects a malicious call‑gate entry into the GDT, allowing a user‑mode application to transition directly to ring‑0 code without invoking a kernel routine. Second, the attacker overwrites entries in the IDT to point to attacker‑controlled interrupt handlers, achieving arbitrary kernel‑mode code execution. Both techniques are validated on recent 9th‑generation Intel CPUs running Windows 10/11, modern Linux kernels, and macOS Monterey, showing that the attack works across operating systems and is independent of the OS‑specific implementation of KASLR.
The paper also examines the hypervisor‑level mitigation known as Descriptor‑Table Exiting, a secondary processor‑based VM‑execution control that forces a VM‑exit whenever LGDT, LIDT, or related instructions are executed in non‑root mode. The authors find that TSX transactions bypass this control because the privileged instruction never reaches the point where the VM‑exit would be triggered; the transaction aborts silently instead. Consequently, even a hardened hypervisor cannot prevent the address leakage.
To mitigate the threat, the authors propose three practical software‑only countermeasures: (1) enable the Descriptor‑Table Exiting control by default, ensuring all descriptor‑table instructions cause a VM‑exit that the VMM can filter; (2) redesign kernel page tables so that GDT and IDT are never mapped into user‑visible address spaces, placing them in isolated kernel‑only pages; and (3) limit or disable TSX usage, or introduce randomization of cache state on transaction aborts to destroy the timing signal. Their prototype patches incur only a modest 3‑5 % performance overhead, making them viable for production deployment.
In summary, the work reveals a previously unknown class of attacks that combine TSX‑based timing side‑channels with descriptor‑table manipulation to defeat UMIP and hypervisor‑based protections. It underscores the inherent difficulty of fully isolating critical kernel structures and calls for tighter architectural safeguards in future CPU and OS designs.
Comments & Academic Discussion
Loading comments...
Leave a Comment