LQG Control and Sensing Co-Design
We investigate a Linear-Quadratic-Gaussian (LQG) control and sensing co-design problem, where one jointly designs sensing and control policies. We focus on the realistic case where the sensing design is selected among a finite set of available sensor…
Authors: Vasileios Tzoumas, Luca Carlone, George J. Pappas
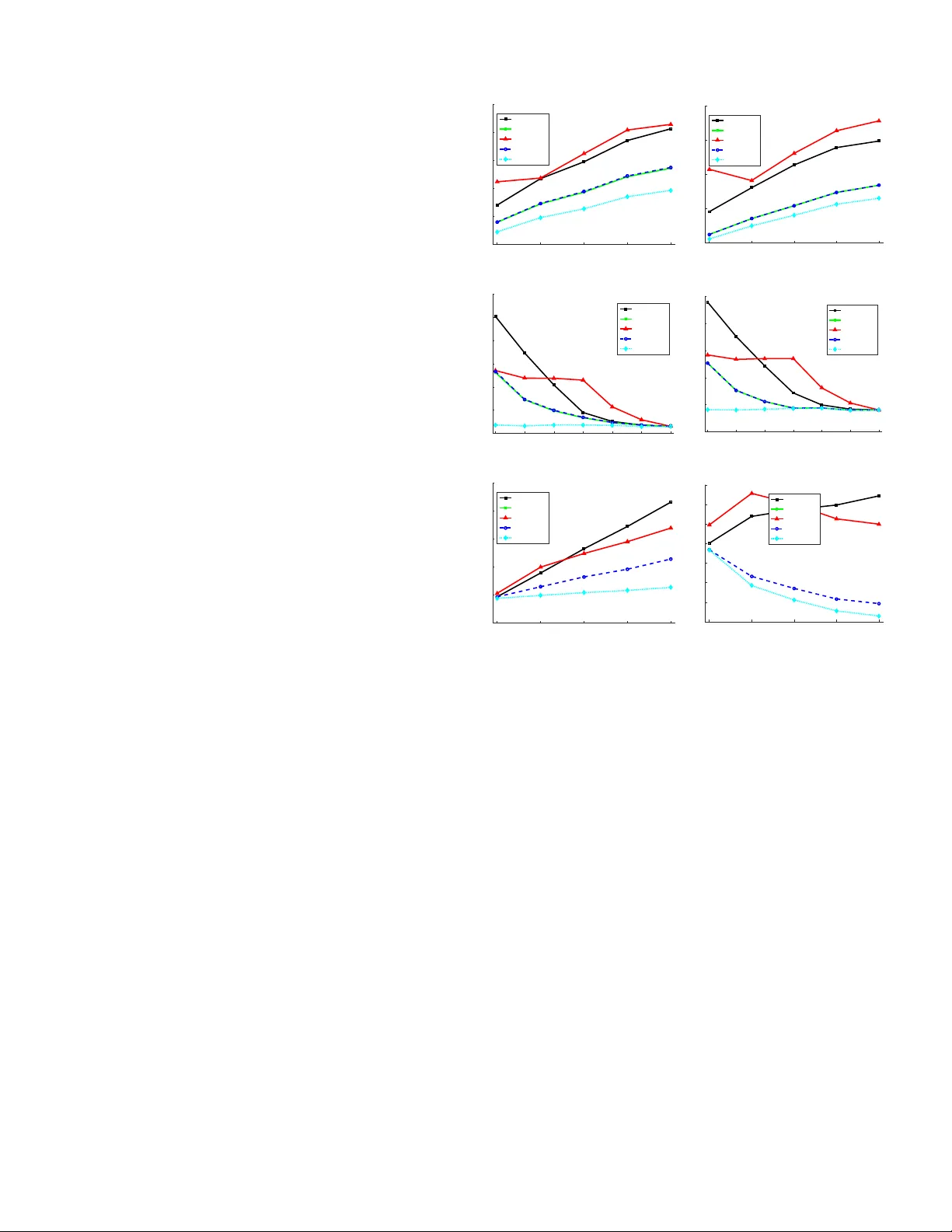
1 LQG Control and Sensing Co-Design V asileios Tzoumas, 1 Member , IEEE, Luca Carlone, 1 Senior Member , IEEE, George J. P appas, 2 F ellow , IEEE, Ali Jadbabaie, 1 F ellow , IEEE Abstract —W e in vestigate a Linear Quadratic Gaussian (LQG) control and sensing co-design pr oblem, where one jointly designs sensing and control policies. W e focus on the realistic case where the sensing design is selected among a finite set of av ailable sensors, where each sensor is associated with a different cost (e.g., power consumption). W e consider two dual problem instances: sensing-constrained LQG control , where one maximizes control performance subject to a sensor cost budget, and minimum- sensing LQG control , where one minimizes sensor cost subject to performance constraints. W e pr ove no polynomial time algorithm guarantees across all problem instances a constant approxi- mation factor from the optimal. Nonetheless, we present the first polynomial time algorithms with per -instance suboptimality guarantees. T o this end, we leverage a separation principle, that partially decouples the design of sensing and control. Then, we frame LQG co-design as the optimization of appr oximately supermodular set functions; we dev elop novel algorithms to solve the problems; and we prove original results on the perfor - mance of the algorithms, and establish connections between their suboptimality and control-theor etic quantities. W e conclude the paper by discussing tw o applications, namely , sensing-constrained formation control and resource-constrained robot navigation . This paper has been accepted for publication in the IEEE Transactions of Automatic Control. Please cite the paper as: V . Tzoumas, L. Carlone, George J. Pappas, A. Jadbabaie “LQG Control and Sensing Co-Design", IEEE Transactions of Automatic Control (T A C), 2020. I . I N T R O D U C T I O N T raditional approaches to systems control assume the choice of sensors fixed [1]. The sensors usually result from a prelim- inary design phase in which an expert selects a suitable sensor suite that accommodates estimation requirements, and system constraints (e.g., po wer consumption). Ho we ver , the control applications of the Internet of Things (IoT) and Battlefield Things (IoBT) [2], pose serious limitations to the applicability of this traditional paradigm. Now , systems are not designed from scratch; instead, existing, standardized systems come together , along with their sensors, to form heterogeneous teams (such as robot teams), tasked with various control goals: from collaborativ e object manipulation to formation control [3], [4]. In such heterogeneous networked systems, where new nodes are continuously added and removed from the network, sensor redundancies are created, depending on the task at hand. At the same time, po wer , bandwidth, and/or computation constraints limit which sensors can be acti ve [5]–[7] Therefore, to optimize the network’ s operability and prolong its operation, one needs to decide which sensors are important for the task, and acti vate only these [7]. Evidently , in large-scale networks a manual activ ation policy is not scalable. Thus, ones needs 1 The authors are with the Laboratory for Information & Decision Systems, Massachusetts Institute of T echnology , Cambridge, MA 02139, USA (email: {vtzoumas, lcarlone, jadbabai}@mit.edu ). 2 The author is with the Department of Electrical and Systems Engi- neering, Uni versity of Pennsylv ania, Philadelphia, P A 19104, USA (email: pappasg@seas.upenn.edu ). This work was supported by the AFOSR Complex Networks Program, ARL DCIST CRA W911NF-17-2-0181, and ONR RAIDER N00014-18-1-2828. to develop automated approaches. Moti vated by this need, we consider the co-design of LQG control and sensor selection subject to sensor acti vation constraints. Particularly , we as- sume that the sensor constraints are captured by a prescribed budget (e.g., available battery power), and that each sensor is associated with an acti v ation cost (e.g., po wer consumption). Related work in control. T raditionally , the control litera- ture has focused on co-designing control, estimation, actuation (i.e., actuator selection), and sensing (i.e., sensor selection) [1], [5]–[41]. Howe v er , the focus so far has mostly been different from the co-design problem we consider in this paper: a) [1], [8]–[14] assume all sensors giv en and activ e (instead of choosing a few sensors to acti vate). They focus on the co- design of control and estimation over band-limited communi- cation channels, and in vestigate trade-offs between communi- cation constraints (e.g., quantization), and control performance (e.g., stability). In more detail, they provide results on the impact of quantization [10], and of finite data rates [11], [12], as well as, on separation principles for LQG design with communication constraints [13]. Recent works also focus on priv ac y constraints [14]. For a comprehensive revie w on LQG control and estimation, we refer to [1], [8], [9]. b) [15]–[21] extend the focus of the above works, by focusing on the co-design of control, estimation, and sensing. Y et, the choice of each sensor can be arbitrary (instead, in our framew ork, a few sensors are activ ated from a giv en finite set of available ones). For example, [15]–[19], [42] propose the optimization of steady state LQG costs, subject to sparsity constraints on the sensor matrices and/or on the feedback control and estimation gains. Finally , [20], [21] augment the LQG cost with an information-theoretic re gularizer , and design the sensors matrices using semi-definite programming. c) [5]–[7], [22]–[41] focus on sensor selection, but they do not consider control aspects (with the exception of [7], [40], [41], which we discuss below). Specifically , [22] studies sensor placement to optimize maximum likelihood estimation ov er static parameters, whereas [5], [6], [23]–[27] focus on optimizing Kalman filtering and batch estimation accurac y ov er non-static parameters. [28], [29], [31]–[37] present sensor and actuator selection algorithms to optimize the av erage observability and controllability of systems; [30] focuses on actuator placement for stability in uncertain systems. For additional relev ant applications, we refer to [38]. [42, Chapter 6.1.3] focuses on selecting a sensor for each edge of a consensus-type system for H 2 optimization subject to sensor cost constraints, and sensor noise considerations (instead, we consider general systems). [39] selects the location of a phasor measurement unit (PMU) on a single edge of an electrical network to minimize estimation error (each placement happens independently of the rest). [40], [41] study sensor placement 2 to optimize a steady state LQG cost; although the latter case is similar to our framew ork (we optimize a finite horizon LQG cost, instead of a steady state), the authors focus only on a small-scale system with a few sensors, where a brute-force selection is viable, and no scalable algorithms are proposed (instead, our focus is on scalable approximation algorithms). Finally , [7] studies an LQG control and scheduling co-design problem, where decoupled systems share a wireless sensor net- work, while power consumption constraints must be satisfied. Instead, we consider coupled systems, a framework that makes our co-design problem inapproximable in polynomial time, in contrast to [7]’ s, which is optimally solved in polynomial time. Related work on set function optimization. In this paper , a fe w sensors must be activ ated among a set of available ones. This is a combinatorial problem, and we prov e it inapproximable: across all problem instances, no polynomial time algorithm can guarantee a constant approximation factor from the optimal. Thus, to provide efficient algorithms with per-instance suboptimality bounds instead, we resort to tools from combinatorial optimization, which has been a successful paradigm on this front [38], [38], [43]–[46]. Specifically , the literature on combinatorial optimization includes in v estigation into (i) supermodular optimization subject to car dinality con- straints (where only a prescribed number of sensors can be activ e) [47], [48]; (ii) supermodular optimization subject to cost constraints [49]–[51] (where only sensor combinations that meet a prescribed budget can be activ e —each sensor has a potentially different activ ation cost); and (iii) appr oxi- mately supermodular optimization subject to car dinality con- straints [43]–[46]. The literature does not cover appr oximately submodular optimization subject to cost constraints, which is the setup of interest in this paper; hence we herein dev elop algorithms and novel suboptimality bounds for this case. 1 Contributions to control theory . W e address an LQG contr ol and sensing co-design problem. The problem e xtends LQG control to the case where, besides designing an optimal controller and estimator , one has to decide which sensors to activ ate, due to sensor cost constraints and a limited budget. That is, the sensor choice is restricted to a finite selection from the av ailable sensors, rather than being arbitrary (for arbitrary sensing design, see [15]–[18], [20]). And each sensor has a cost that captures the penalty incurred for using the sensor . Since different sensors (e.g., lidars, radars, cameras, lasers) have dif ferent power consumption, bandwidth utiliza- tion, and/or monetary v alue, we allow each sensor to ha ve a different cost. W e formulate two dual instances of the LQG co- design problem. The first, sensing-constrained LQG contr ol , in volv es the joint design of control and sensing to minimize the LQG cost subject to a sensor cost budget. The second, minimum-sensing LQG contr ol , in volv es the joint design of control and sensing to minimize the cost of the acti vated sensors subject to a desired LQG cost. T o solve the proposed LQG problems, we first lev erage a separation principle that partially decouples the control and 1 The transition from cardinality to cost constraints, in terms of providing efficient algorithms with prov able suboptimality bounds, is non-tri vial, as it is observed by comparing the widely different proof techniques in [52], for the cardinality case, versus those considered in this paper, for the cost case. sensor selection. 2 As a ne gativ e result, we prove the optimal sensor selection is inapproximable in polynomial time by a constant suboptimality bound across all problem instances. Therefore, we dev elop algorithms with per-instance subopti- mality bounds instead. Particularly , we frame the sensor se- lection as the optimization of appr oximately supermodular set functions, using the notion of supermodularity ratio introduced in 2006 in [53] (see also [44]). 3 Then, we provide the first polynomial time algorithms, which prov ably retrieve a close- to-optimal choice of sensors, and the corresponding optimal control policy . Specifically , the suboptimality gaps of the algorithms depend on the supermodularity ratio γ of the LQG cost, and we establish connections between γ and control- theoretic quantities, providing computable lower bounds for γ . Contributions to set function optimization. T o pro ve the aforementioned results, we extend the literature on supermod- ular optimization. Particularly , we provide the first efficient algorithm for approximately supermodular optimization (e.g., LQG cost optimization) subject to cost constraints for subset selection (e.g., sensor selection). T o this end, we use the algorithm in [51], proposed for exactly supermodular optimiza- tion, and prove it maintains prov able suboptimality bounds for ev en appr oximately supermodular optimization. Importantly , our bounds improv e the pre viously known bounds for exactly supermodular optimization: our bounds become 1 − 1 /e for supermodular optimization, tightening the known 1 / 2(1 − 1 /e ) [51]. Noticeably , 1 − 1 /e is the best possible bound in polynomial time for supermodular optimization subject to cardinality constraints [57]. That way , our analysis equates the approximation difficulty of cost and cardinality constrained optimization for the first time (among all algorithms with at most quadratic running time). 4 That way , our results are relev ant beyond sensing in control, such as in cost effecti ve outbreak detection in networks [63]. Similarly , we provide the first algorithm for minimal cost subset selection subject to desired bounds on an approximately supermodular function. The algorithm relies on a simplifica- tion of the algorithm in [51]. Leveraging our novel bounds, we show the algorithm is the first with prov able suboptimality bounds given approximately supermodular functions. Notably , for exactly supermodular functions the bound recovers the well-known bound for cardinality minimization [48]; that way , similarly to above, our analysis equates the approximation difficulty of cost and cardinality minimization for the first time. Application examples. W e demonstrate the effecti veness of the proposed algorithms in numerical experiments, by consid- ering two application scenarios: sensing-constrained forma- tion contr ol , and resour ce-constrained r obot navigation . W e present a Monte Carlo analysis for both, which demonstrates that (i) the proposed sensor selection strate gy is near-optimal, and, particularly , the resulting LQG cost matches the optimal 2 The separation between control and sensor selection is proved with the same steps as the separation of control and estimation in standard LQG control theory; e.g., see proof of Lemma 1 in [20]. 3 The notion has met already increasing interest in the signal processing and control literature; see, for example, [26], [45], [46], [54]–[56]. 4 Other algorithms, that either achiev e the 1 − 1 /e bound b ut are slo wer ( O ( n 5 ) instead of O ( n 2 ) that ours is), or they achieve looser bounds with the same running time, such as the 1 − 1 / √ e , are found in [51], [58]–[62]. 3 selection in all tested instances for which the optimal selection could be computed via a brute-force approach; (ii) a more naiv e selection which attempts to minimize the state estimation error [24] (rather than the LQG cost) has degraded LQG performance, often comparable to a random selection; and (iii) the selection of a small subset of sensors using the proposed algorithms ensures an LQG cost that is close to the one obtained by using all av ailable sensors, hence providing an effecti v e alternative for control under sensing constraints. Comparison with the preliminary results in [52] (which coincides with the preprint [64]). This paper (which coin- cides with the preprint [65]) extends the preliminary results in [52], and provides comprehensiv e presentation of the LQG co-design problem, by including both the sensing-constrained LQG control (introduced in [52]) and the minimum-sensing LQG control problem (not previously published). Moreover , we generalize the setup in [52] to account for any sensor costs (in [52] each sensor has unit cost, whereas herein sensors hav e dif ferent costs). Also, we extend the numerical analysis accordingly . Moreover , we prove the inapproximability of the problem. Most of the technical results (Theorems 1-4, and Algorithms 2-4) are no vel, and have not been published. Organization of the rest of the paper . Section II for- mulates the LQG control and sensing co-design problems. Section III presents a separation principle, the inapproximabil- ity theorem, and introduces the algorithms for the co-design problems. Section IV characterizes the performance of the algorithms, and establishes connections between their sub- optimality bounds and control-theoretic quantities. Section V presents two examples of the co-design problems. Section VI concludes the paper . All pr oofs ar e giv en in the appendix. Notation. Lo wercase letters denote vectors and scalars (e.g., v ); uppercase letters denote matrices (e.g., M ). Calligraphic fonts denote sets (e.g., S ). I denotes the identity matrix. I I . P R O B L E M F O R M U L A T I O N : L Q G C O N T RO L A N D S E N S I N G C O - D E S I G N Here we formalize the LQG control and sensing co-design problem considered in this paper . Specifically , we present two “dual” statements of the problem: the sensing-constrained LQG contr ol , and the minimum-sensing LQG contr ol . A. System, sensors, and contr ol policies W e start by introducing the paper’ s framew ork: a) System: W e consider a discrete-time time-varying linear system with additi ve Gaussian noise, x t +1 = A t x t + B t u t + w t , t = 1 , 2 , . . . , T , (1) where x t ∈ R n is the system’ s state at time t , u t ∈ R m t is the control action, w t is the process noise, A t and B t are known matrices, and T is a finite horizon. Also, x 1 is a Gaussian random variable with cov ariance Σ 1 | 1 , and w t is a Gaussian random variable with mean zero and cov ariance W t , such that w t is independent of x 1 and w t 0 for all t 0 = 1 , 2 , . . . , T , t 0 6 = t . b) Sensors: W e consider the availability of a (potentially large) set V of sensors, which can take noisy linear observ a- tions of the system’ s state. Particularly , y i,t = C i,t x t + v i,t , i ∈ V , (2) where y i,t ∈ R p i,t is the measurement of sensor i at time t , C i,t is a sensing matrix, and v i,t is the measurement noise. W e assume v i,t to be a Gaussian random v ariable with mean zero and positi ve definite covariance V i,t , such that v i,t is independent of x 1 , and of w t 0 for any t 0 6 = t , and independent of v i 0 ,t 0 for all t 0 6 = t , and any i 0 ∈ V , i 0 6 = i . When only a subset S ⊆ V of the sensors is activ e for all t = 1 , 2 , . . . , T , then the measurement model becomes y t ( S ) = C t ( S ) x t + v t ( S ) , (3) where y t ( S ) , [ y T i 1 ,t , y T i 2 ,t , . . . , y T i |S | ,t ] T , C t ( S ) , [ C T i 1 ,t , . . . , C T i |S | ,t ] T , and v t ( S ) is a mean zero Gaussian noise with cova- riance V t ( S ) , diag V i 1 ,t , . . . , V i |S | ,t . Each sensor is associated with a (possibly different) cost, which captures, for example, the sensor’ s monetary cost, its power consumption, or its bandwidth utilization. Specifically , we denote the cost of sensor i by c ( i ) ≥ 0 ; and the cost of a sensor set S by c ( S ) , where we set c ( S ) , X i ∈S c ( i ) . (4) c) Contr ol policies: W e consider control policies u t informed only by the acti ve sensor set S : u t = u t ( S ) = u t ( y 1 ( S ) , y 2 ( S ) , . . . , y t ( S )) , t = 1 , 2 , . . . , T . B. LQG co-design pr oblems W e define two versions of the co-design problem: sensing- constrained LQG contr ol and minimum-sensing LQG contr ol . Their unifying goal is to find active sensors S and a policy u 1: T ( S ) , { u 1 ( S ) , u 2 ( S ) , . . . , u T ( S ) } , such that the sensor cost c ( S ) is lo w and the finite horizon LQG cost h ( S , u 1: T ( S )) below is optimized: h ( S , u 1: T ( S )) , T X t =1 E k x t +1 ( S ) k 2 Q t + k u t ( S ) k 2 R t , (5) where Q 1 , . . . , Q T are known positive semi-definite matricies, R 1 , . . . , R T are known positi ve definite matricies, and the expectation is taken with respect to x 1 , w 1: T , and v 1: T ( S ) . Particularly , the sensing-constrained LQG contr ol minimizes the LQG cost subject to a sensor cost budget, and the dual minimum-sensing LQG contr ol minimizes the sensor cost subject to a desired LQG cost. Problem 1 (Sensing-constrained LQG control). Given a budg et b ≥ 0 on the sensor cost, find sensors S and a policy u 1: T ( S ) , { u 1 ( S ) , u 2 ( S ) , . . . , u T ( S ) } to minimize the finite horizon LQG cost h ( S , u 1: T ( S )) : min S ⊆ V , u 1: T ( S ) h ( S , u 1: T ( S )) , s . t . c ( S ) ≤ b. (6) Problem 1 models the practical case where we cannot acti- vate all sensors (due to power , cost, or bandwidth constraints), 4 and instead need to activ ate a fe w sensors to optimize control performance. If the budget is increased so all sensors can be activ e, then Problem 1 reduces to standard LQG control. Problem 2 (Minimum-sensing LQG control). F ind a min- imal cost sensor set S , and a policy u 1: T ( S ) , such that the finite horizon LQG cost h ( S , u 1: T ( S )) is at most κ , wher e κ ≥ 0 is given: min S ⊆ V , u 1: T ( S ) c ( S ) , s . t . h ( S , u 1: T ( S )) ≤ κ. (7) Problem 2 models the practical case where one wants to design a system with a prescribed performance, while incurring in the smallest sensor cost. Remark 1 (Case of unif orm-cost sensors). When all sensors i ∈ V have the same cost , say c ( i ) = ¯ c > 0 , the sensor budget constraint becomes a cardinality constraint: c ( S ) ≤ b ⇔ X i ∈S c ( i ) ≤ b ⇔ |S | ¯ c ≤ b ⇔ |S |≤ b ¯ c . (8) I I I . C O - D E S I G N P R I N C I P L E S , H A R D N E S S , A N D A L G O R I T H M S W e leverage a separation principle to derive that the opti- mization of the sensor set S and of the control policy u 1: T ( S ) can happen in cascade. Ho wev er , we show that optimizing for S is inapproximable in polynomial time. Nonetheless, we then present polynomial time algorithms for Problem 1 and Problem 2 with provable per-instance suboptimality bounds. Particularly , the bounds are presented in Section IV. 5 A. Separability of optimal sensing and contr ol design W e characterize the jointly optimal control and sensing solutions for Problem 1 and Problem 2, and prove they can be found in two separate steps, where first the sensor set is found, and then the control policy is computed. Theorem 1 (Separability of optimal sensor set and control policy design). F or any active sensor set S , let ˆ x t ( S ) be the Kalman estimator of the state x t , and Σ t | t ( S ) be ˆ x t ( S ) ’s err or covariance. Additionally , let the matrices Θ t and K t be the solution of the following backwar d Riccati r ecursion S t = Q t + N t +1 , N t = A T t ( S − 1 t + B t R − 1 t B T t ) − 1 A t , M t = B T t S t B t + R t , K t = − M − 1 t B T t S t A t , Θ t = K T t M t K t , (9) with boundary condition N T +1 = 0 . 1) (Separability in Problem 1) Any optimal solution ( S ? , u ? 1: T ) to Problem 1 can be computed in cascade: S ? ∈ arg min S ⊆V T X t =1 tr [Θ t Σ t | t ( S )] , s . t . c ( S ) ≤ b, (10) u ? t = K t ˆ x t ( S ? ) , t = 1 , . . . , T . (11) 5 The novelty of the algorithms is also discussed in Section IV. 2) (Separability in Problem 2) Define the constant ¯ κ , κ − tr Σ 1 | 1 N 1 − P T t =1 tr ( W t S t ) . Any optimal solution ( S ? , u ? 1: T ) to Problem 2 can be computed in cascade: S ? ∈ arg min S ⊆V c ( S ) , s . t . T X t =1 tr [Θ t Σ t | t ( S )] ≤ ¯ κ, (12) u ? t = K t ˆ x t ( S ? ) , t = 1 , . . . , T . (13) Remark 2 (Certainty equivalence principle). The control gain matrices K 1 , K 2 , . . . , K T ar e the same as the ones that make the contr ollers ( K 1 x 1 , K 1 x 2 , . . . , K T x T ) optimal for the perfect state-information version of Problem 1, wher e the state x t is known to the contr ollers [1, Chapter 4]. Theorem 1 decouples the sensing design from the control policy design. Particularly , once an optimal sensor set S ? is found, then the optimal controllers are equal to K t ˆ x t ( S ? ) , which correspond to the standard LQG control polic y . An intuitiv e interpretation of the sensor design steps in eqs. (10) and (12) follo ws next. Remark 3 (Control-aware sensor design). T o pro vide insight on P T t =1 tr [Θ t Σ t | t ( S )] in eqs. (10) and (12) , we r ewrite it as T X t =1 tr [Θ t Σ t | t ( S )] = T X t =1 E tr { [ x t − ˆ x t ( S )] T Θ t [ x t − ˆ x t ( S )] } = T X t =1 E k K t x t − K t ˆ x t ( S ) k 2 M t , (14) since Σ t | t ( S ) = E ( x t − ˆ x t ( S ))( x t − ˆ x t ( S )) T , and Θ t = K T t M t K t . F r om eq. (14) , each tr [Θ t Σ t | t ( S )] captur es the mismatch between the imperfect state-information contr oller u t ( S ) = K t ˆ x t ( S ) (which is only awar e of the measur ements fr om the active sensors) and the perfect state-information contr oller K t x t . That is, while standar d sensor selection min- imizes the estimation covariance, for instance by minimizing T X t =1 tr [Σ t | t ( S )] , T X t =1 E k x t − ˆ x t ( S ) k 2 2 , (15) the pr oposed LQG cost formulation selectively minimizes the estimation err or focusing on the states that are most informative for contr ol purposes. F or e xample, the mismatch contribution in eq. (14) of any x t − ˆ x t ( S ) in the null space of K t is zer o; accor dingly , the pr oposed sensor design appr oac h has no incentive in activating sensors to observe states which ar e irr elevant for contr ol purposes. B. Inappr oximability of optimal sensing design Theorem 2 (Inapproximability). If NP 6 = P , then ther e is no polynomial time algorithm for Pr oblems 1 and 2 that returns an approximate solution within a constant factor fr om the optimal. This remains true, even if all sensors have cost 1 . W e prov e the theorem by reducing the inapproximable problem in [66] —sensor selection with cost constraints for optimal steady state Kalman filtering error— to eq. (10). Motiv ated by the inapproximability of Problem 1 and Prob- lem 2, we next present practical algorithms, which in Sec- tion IV we prove to enjoy per-instance suboptimality bounds. 5 Algorithm 1 Joint sensing and control design for Problem 1. Input: Horizon T ; system in eq. (1); cov ariance Σ 1 | 1 ; LQG cost matrices Q t and R t in eq. (5); sensors in eq. (2); sensor budget b ; sensor cost c ( i ) , for all i ∈ V . Output: Activ e sensors b S , and controls ˆ u 1 , ˆ u 2 , . . . , ˆ u T . 1: Compute Θ 1 , Θ 2 , . . . , Θ T using eq. (9). 2: Return b S returned by Algorithm 2, which finds a solution to the optimization problem in eq. (10); 3: Compute K 1 , K 2 , . . . , K T using eq. (9). 4: At each t = 1 . . . , T , compute the Kalman estimate of x t : ˆ x t , E [ x t | y 1 ( b S ) , y 2 ( b S ) , . . . , y t ( b S )]; 5: At each t = 1 , . . . , T , return ˆ u t = K t ˆ x t . C. Co-design algorithms for Pr oblem 1 W e present a practical algorithm for the sensing-constrained LQG control Problem 1 (Algorithm 1). The algorithm follows Theorem 1: it first computes a sensing design, and then a control design, as described belo w . Sensing design f or Problem 1. Theorem 1 implies an optimal sensor design for Problem 1 can be computed by solving eq. (10). T o this end, Algorithm 1 first computes Θ 1 , Θ 2 , . . . , Θ T (Algorithm 1’ s line 1). Next, since eq. (10) is inapproximable (Theorem 2), Algorithm 1 calls a greedy algorithm (Algorithm 2) to compute a solution to eq. (10) (Algorithm 1’ s line 2). Algorithm 2 computes a solution to eq. (10) as follows: first, Algorithm 2 creates two candidate acti ve sensor sets b S 1 and b S 2 (lines 1-2), of which only one will be selected as the solution to eq. (10) (line 20). In more detail, Algorithm 2’ s line 1 lets b S 1 be composed of a single sensor , namely the sensor i ∈ V that achie ves the smallest value of the objectiv e function in eq. (10) and has smaller cost than the budget b ( c ( i ) ≤ b ). Then, Algorithm 2’ s line 2 initializes b S 2 with the empty set, and after the construction of b S 2 in Algorithm 2’ s lines 3–19, Algorithm 2’ s line 20 computes which of b S 1 and b S 2 achiev es the smallest value for the objectiv e function in eq. (10), and returns this set as the solution to eq. (10). Specifically , Algorithm 2’ s lines 3–19 construct b S 2 as fol- lows: at each iteration of the “while loop” (lines 3-16) a sensor is greedily added to b S 2 , as long as b S 2 ’ s cost does not exceed b . Particularly , for each remaining sensor a in V \ b S 2 , the “for loop” (lines 4-12) computes first the estimation cov ariance resulting by adding a in b S 2 , and then the marginal gain in the objectiv e function in eq. (10) (line 11). Afterwards, the sensor inducing the largest marginal gain (normalized by the sensor’ s cost) is selected (line 13), and is added in b S 2 (line 14). Finally , the “if ” in lines 17-19 ensure b S 2 has cost at most b , by removing last sensor added in b S 2 if necessary . Control design f or Problem 1. Theorem 1 implies that giv en a sensor set, the controls for Problem 1 can be computed according to the eq. (11). T o this end, Algorithm 1 first computes K 1 , K 2 , . . . , K T (line 3), and then, at each time t = 1 , 2 , . . . , T , the Kalman estimate of the current state x t (line 4), and the corresponding control (line 5). Algorithm 2 Sensing design for Problem 1. Input: Horizon T ; system in eq. (1); cov ariance Σ 1 | 1 ; LQG cost matrices Q t and R t in eq. (5); sensors in eq. (2); sensor budget b ; sensor cost c ( i ) , for all i ∈ V . Output: Sensor set b S . 1: b S 1 ← arg min i ∈V ,c ( i ) ≤ b P T t =1 tr [Θ t Σ t | t ( { i } )] ; 2: b S 2 ← ∅ ; V 0 ← V ; 3: while V 0 6 = ∅ and c ( b S 2 ) ≤ b do 4: for all a ∈ V 0 do 5: b S 2 ,α ← b S 2 ∪ { a } ; Σ 1 | 1 ( b S 2 ,α ) ← Σ 1 | 1 ; 6: for all t = 1 , . . . , T do 7: Σ t +1 | t ( b S 2 ,α ) ← A t Σ t | t ( b S 2 ,α ) A T t + W t ; 8: Σ t | t ( b S 2 ,α ) ← 9: [Σ t | t − 1 ( b S 2 ,α ) − 1 + C t ( b S 2 ,α ) T V t ( b S 2 ,α ) − 1 C t ( b S 2 ,α )] − 1 ; 10: end for 11: gain a ← P T t =1 tr { Θ t [Σ t | t ( b S 2 ) − Σ t | t ( b S 2 ,α )] } ; 12: end for 13: s ← arg max a ∈V 0 [ gain a /c ( a )] ; 14: b S 2 ← b S 2 ∪ { s } ; 15: V 0 ← V 0 \ { s } ; 16: end while 17: if c ( b S 2 ) > b then 18: b S 2 ← b S 2 \ { s } ; 19: end if 20: b S ← arg min S ∈{ b S 1 , b S 2 } P T t =1 tr [Θ t Σ t | t ( S )] . D. Co-design algorithms for Pr oblem 2 This section presents a practical algorithm for Problem 2 (Algorithm 3). Since the algorithm shares steps with Algo- rithm 1, we focus on the different ones. Particularly , as Algorithm 1 calls Algorithm 2 to solve eq. (10), similarly , Algorithm 3 calls Algorithm 4 to solve eq. (12). Algorithm 4 is similar to Algorithm 2, with the difference that Algorithm 4 selects sensors until the upper bound ¯ κ in eq. (12) is met (Algorithm 4’ s line 3), whereas Algorithm 2 selects sensors up to the point the cost budget b is violated (Algorithm 2’ s line 3). I V . P E R F O R M A N C E G U A R A NT E E S F O R L Q G C O - D E S I G N W e now quantify the suboptimality and running time of Algorithms 1 and Algorithms 3. Particularly , we prov e both algorithms enjoy per-instance suboptimality bounds, 6 and run in quadratic time. T o this end, we present a notion of su- permodularity ratio (Definition 3), which we use to prove the suboptimality bounds. W e then establish connections be- tween the ratio and control-theoretic quantities (Theorem 5), and conclude that the algorithms’ suboptimality bounds are non-vanishing under control-theoretic conditions encountered in most real-world systems (Theorem 6). A. Supermodularity ratio T o present the definition of supermodularity ratio , we start by defining monotonicity and supermodularity . 6 Instead of constant suboptimality bounds across all instances, which is impossible due to Theorem 2. 6 Algorithm 3 Joint Sensing and Control design for Problem 2. Input: Horizon T ; system in eq. (1); cov ariance Σ 1 | 1 ; LQG cost matrices Q t and R t in eq. (5); LQG cost bound κ l sensors in eq. (2); sensor cost c ( i ) , for all i ∈ V . Output: Activ e sensors b S , and controls ˆ u 1 , ˆ u 2 , . . . , ˆ u T . 1: Compute Θ 1 , Θ 2 , . . . , Θ T using eq. (9). 2: Return b S returned by Algorithm 4, which finds a solution to the optimization problem in eq. (7) ; 3: Compute K 1 , K 2 , . . . , K T using eq. (9). 4: At each t = 1 . . . , T , compute the Kalman estimate of x t : ˆ x t , E [ x t | y 1 ( b S ) , y 2 ( b S ) , . . . , y t ( b S )]; 5: At each t = 1 , . . . , T , return ˆ u t = K t ˆ x t . Definition 1 (Monotonicity [47]). Consider any finite set V . The set function f : 2 V 7→ R is non-increasing if and only if for any sets A ⊆ B ⊆ V , it holds f ( A ) ≥ f ( B ) . Definition 2 (Supermodularity [47, Proposition 2.1]). Con- sider any finite set V . The set function f : 2 V 7→ R is supermodular if and only if for any sets A ⊆ B ⊆ V , and any element v ∈ V , it holds f ( A ) − f ( A∪{ v } ) ≥ f ( B ) − f ( B ∪{ v } ) . That is, f is supermodular if and only if it satisfies a diminishing returns property: for any v ∈ V , the drop f ( A ) − f ( A ∪ { v } ) diminishes as the set A grows. Definition 3 (Supermodularity ratio [53]). Consider any finite set V , and a non-incr easing set function f : 2 V 7→ R . W e define the supermodularity ratio of f as γ f , min A⊆B⊆V ,v ∈V \B f ( A ) − f ( A ∪ { v } ) f ( B ) − f ( B ∪ { v } ) . The supermodularity ratio γ f measures how f ar f is from being supermodular . Particularly , γ f takes values in [0 , 1] , and if γ f = 1 , then f ( A ) − f ( A ∪ { v } ) ≥ f ( B ) − f ( B ∪ { v } ) , i.e., f is supermodular . Whereas, if 0 <γ f < 1 , then f ( A ) − f ( A ∪ { v } ) ≥ γ f [ f ( B ) − f ( B ∪ { v } )] , i.e., γ f captures ho w much ones needs to discount f ( B ) − f ( B ∪ { v } ) , such that f ( A ) − f ( A ∪ { v } ) is at least f ( B ) − f ( B ∪ { v } ) . In this case, f is called appr oximately (or weakly) supermodular [67]. B. P erformance analysis for Algorithm 1 W e quantify Algorithm 1’ s running time and suboptimality , using the notion of supermodularity ratio. W e use the notation: • g ( S ) is the optimal value of h [ S , u 1: T ( S )] across all u 1: T ( S ) , gi ven any S : g ( S ) , min u 1: T ( S ) h [ S , u 1: T ( S )] , (16) • h ? , min S ⊆V ,u 1: T ( S ) h [ S , u 1: T ( S )] , s . t . c ( S ) ≤ b , i.e., the optimal value of Problem 1; • b ? , min S ⊆V ,u 1: T ( S ) c ( S ) , s . t . h [ S , u 1: T ( S )] ≤ κ , i.e., the optimal value of Problem 2. Algorithm 4 Sensing design for Problem 2. Input: Horizon T ; system in eq. (1); cov ariance Σ 1 | 1 ; LQG cost matrices Q t and R t in eq. (5); LQG cost bound κ l sensors in eq. (2); sensor cost c ( i ) , for all i ∈ V . Output: Activ e sensors b S . 1: ¯ κ ← κ − tr Σ 1 | 1 N 1 − P T t =1 tr ( W t S t ) 2: b S ← ∅ ; V 0 ← V ; 3: while V 0 6 = ∅ and P T t =1 tr [Θ t Σ t | t ( b S )] > ¯ κ do 4: for all a ∈ V 0 do 5: b S α ← b S ∪ { a } ; Σ 1 | 1 ( b S α ) ← Σ 1 | 1 ; 6: for all t = 1 , . . . , T do 7: Σ t +1 | t ( b S α ) ← A t Σ t | t ( b S α ) A T t + W t ; 8: Σ t | t ( b S α ) ← 9: [Σ t | t − 1 ( b S α ) − 1 + C t ( b S α ) T V t ( b S α ) − 1 C t ( b S α )] − 1 ; 10: end for 11: gain a ← P T t =1 tr { Θ t [Σ t | t ( b S ) − Σ t | t ( b S α )] } ; 12: end for 13: s ← arg max a ∈V 0 [ gain a /c ( a )] ; 14: b S ← b S ∪ { s } ; 15: V 0 ← V 0 \ { s } ; 16: end while Theorem 3 (Perf ormance of Algorithm 1). Algorithm 1 r eturns a sensor set b S and contr ol policies u 1: T ( b S ) such that h [ ∅ , u 1: T ( ∅ )] − h [ b S , u 1: T ( b S )] h [ ∅ , u 1: T ( ∅ )] − h ? ≥ max h γ g 2 1 − e − γ g , 1 − e − γ g c ( b S ) /b i , (17) wher e γ g is the supermodularity r atio of g ( S ) in eq. (16) . Mor eover , Algorithm 1 runs in O ( |V | 2 T n 2 . 4 ) time. In ineq. (17), h [ ∅ , u 1: T ( ∅ )] − h [ b S , u 1: T ( b S )] quantifies the gain from selecting b S , and ineq. (17)’ s right-hand-side guar - antees the gain is close to the optimal h [ ∅ , u 1: T ( ∅ )] − h ? . 7 Specifically , when either of the bounds in ineq. (17)’ s right- hand-side is 1 , then the algorithm returns an optimal solution. For comparison, in Fig. 1 we plot the bounds for c ( b S ) /b ∈ { 2 / 5 , 1 , 2 } and all γ g ∈ [0 , 1] . W e observe that 1 − e − γ g c ( b S ) /b dominates γ g / 2 (1 − e − γ g ) for c ( b S ) /b > 2 / 5 . Moreover , as c ( b S ) /b and γ g increase, then 1 − e − γ g c ( b S ) /b tends to 1 , in which case, Algorithm 1 returns an optimal solution. Remark 4 (Novelty of algorithm and bounds). Algorithm 1 is the first scalable algorithm for Pr oblem 1. Notably , although Algorithm 2 (used in Algorithm 1) is the same as the Algo- rithm 1 in [51], the latter was intr oduced for exactly super- modular optimization, instead of approximately supermodular optimization , which is the optimization framework in this paper . Ther efor e, one of our contrib utions with Theorem 3 is to pr ove Algorithm 2 maintains suboptimality bounds even for appr oximately supermodular optimization. The novel bounds in Theor em 3 also impr ove upon the pr eviously known [51], [63] for e xactly supermodular optimization: particularly , our bounds can become 1 − 1 /e for supermodular optimization (the 7 Even if no sensors are active, observe h [ ∅ , u 1: T ( ∅ )] is well defined and finite, since it is the LQG cost over a finite horizon T . 7 0 . 2 0 . 4 0 . 6 0 . 8 1 0 0 . 2 0 . 4 0 . 6 0 . 8 1 γ g f 1 ( γ g ) = γ g / 2 (1 − e − γ g ) f 2 ( γ g ) = 1 − e − 2 γ g / 5 f 3 ( γ g ) = 1 − e − γ g f 4 ( γ g ) = 1 − e − 2 γ g Fig. 1. Plot of f i ( γ g ) , where i = 1 , 2 , 3 , 4 , for increasing values of γ g (each f i is defined in the figure’s legend). By Definition 3 of γ g , γ g takes values between 0 and 1 . closer c ( b S ) /b is to 1), tightening the known 1 / 2(1 − 1 /e ) [51], [63]. Noticeably , 1 − 1 /e is the best possible bound in polyno- mial time for submodular optimization subject to cardinality constraints [47], instead of the general cost constraints in this paper . That way , our analysis equates the appr oximation difficulty of cost and cardinality constrained optimization for the first time (among all algorithms with at most quadratic running time in the number of available elements in V , i.e., those in [47], [51], [63], and ours). All in all, Theorem 3 guarantees that Algorithm 1 achie ves a close-to-optimal solution for Problem 1, whenev er γ g > 0 . In Section IV -D we present conditions such that γ g > 0 . Finally , Theorem 3 also quantifies the scalability of Algorithm 1. Particularly , Algorithm 1’ s running time O ( |V | 2 T n 2 . 4 ) is in the worst-case quadratic in the number of available sensors V (when all must be chosen acti ve), and linear in the Kalman filter’ s running time: specifically , the multiplier T n 2 . 4 is due to the complexity of computing all Σ t | t for t = 1 , 2 , . . . , T [1, Appendix E]. C. P erformance analysis for Algorithm 3 Theorem 4 (Perf ormance of Algorithm 3). Consider Algo- rithm 3 r eturns a sensor set b S and contr ol policies u 1: T ( b S ) . Let s l be the last sensor added to b S . Then, h [ b S , u 1: T ( b S )] ≤ κ ; (18) c ( b S ) ≤ c ( s l ) + 1 γ g log h [ ∅ , u 1: T ( ∅ )] − κ h [ b S l − 1 , u 1: T ( b S l − 1 )] − κ ! b ? , (19) wher e b S l − 1 , b S \ { s l } . Additionally , Algorithm 3 runs in O ( |V | 2 T n 2 . 4 ) time. Remark 5 (Novelty of algorithm and bound). Algorithm 3 is the first scalable algorithm for Pr oblem 2. Importantly , Al- gorithm 4, used in Algorithm 3, is the first scalable algorithm with suboptimality guarantees for the problem of minimal cost set selection wher e a bound to an approximately supermodular g must be met. P articularly , Algorithm 4, generalizes pr evious algorithms [48] that focus instead on minimal cardinality set selection subject to bounds on an exactly supermodular func- tion g (in which case, γ g = 1 ). Notably , for γ g = 1 , ineq. (19) ’ s bound r ecover s the guarantee established in [48, Theorem 1]. All in all, ineq. (18) implies Algorithm 3 returns a solution to Problem 2 with the prescribed LQG performance. And parallel to ineq. (17), ineq. (19) implies for γ g > 0 that Algorithm 3 achieves a close-to-optimal sensor cost. D. Conditions for γ g > 0 W e provide control-theoretic conditions such that γ g is non-zero, in which case both Algorithm 1 and Algorithm 3 guarantee a close-to-optimal performance. Particularly , we first prov e that if P T t =1 Θ t 0 , then γ g is non-zero. Afterwards, we show the condition holds true in all problem instances one typically encounters in the real-world. Specifically , we prov e P T t =1 Θ t 0 holds whenev er zero control would result in a suboptimal behavior for the system; that is, we prov e P T t =1 Θ t 0 holds in all systems where LQG control improv es system performance. Theorem 5 (Non-zero computable bound for the supermod- ularity ratio γ g ). F or any sensor i ∈ V , let ¯ C i,t , V − 1 / 2 i,t C i,t be the whitened measur ement matrix. If the strict inequality P T t =1 Θ t 0 holds, then γ g 6 = 0 . Additionally , if we assume tr ¯ C i,t ¯ C T i,t = 1 , and tr [Σ t | t ( ∅ )] ≤ λ 2 max [Σ t | t ( ∅ )] , then γ g ≥ λ min ( P T t =1 Θ t ) λ max ( P T t =1 Θ t ) min t ∈{ 1 , 2 ,...,T } λ 2 min [Σ t | t ( V )] max t ∈{ 1 , 2 ,...,T } λ 2 max [Σ t | t ( ∅ )] 1 + min i ∈V ,t ∈{ 1 , 2 ...,T } λ min [ ¯ C i Σ t | t ( V ) ¯ C T i ] 2 + max i ∈V ,t ∈{ 1 , 2 ...,T } λ max [ ¯ C i Σ t | t ( ∅ ) ¯ C T i ] . (20) Ineq. (20) suggests ways γ g can increase, and, correspond- ingly , the bounds for Algorithm 1 and of Algorithm 3 can improv e: when λ min ( P T t =1 Θ t ) /λ max ( P T t =1 Θ t ) increases to 1 , then the right-hand-side in ineq. (20) increases. Therefore, since each Θ t weight the states depending on their rele- vance for control purposes (Remark 3), the right-hand-side in ineq. (20) increases when all the directions in the state space become equally important for control purposes. Indeed, in the extreme case where λ max (Θ t ) = λ min (Θ t ) = λ , the objecti ve function in eq. (10) becomes T X t =1 tr [Θ t Σ t | t ( S )] = λ T X t =1 tr [Σ t | t ( S )] , which matches the cost function in the classical sensor selec- tion where all states are equally important (per eq. (15)). Theorem 5 states γ g is non-zero whenev er P T t =1 Θ t 0 . T o provide insight on the type of control problems for which this result holds, next we translate the technical condition P T t =1 Θ t 0 into an equi valent control-theoretic condition. Theorem 6 (Control-theor etic condition f or near -optimal co-design). Consider the (noiseless, perfect state-information) LQG problem wher e at any t = 1 , 2 , . . . , T , the state x t is known to each contr oller u t and the pr ocess noise w t is zero, i.e., the optimal contr ol problem min u 1: T P T t =1 [ k x t +1 k 2 Q t + k u t ( x t ) k 2 R t ] Σ t | t = W t =0 . (21) 8 -9 -8 -7 -6 -5 -4 -3 -2 -1 0 1 2 3 4 5 6 7 8 9 x [meters] -9 -8 -7 -6 -5 -4 -3 -2 -1 0 1 2 3 4 5 6 7 8 9 y [meters] (a) formation control (b) robot navigation Fig. 2. Applications of the LQG control and sensing co-design framew ork. Let A t be in vertible for all t = 1 , 2 , . . . , T ; the strict inequality P T t =1 Θ t 0 holds if and only if for all non- zer o initial conditions x 1 , the all-zer oes contr ol policy u ◦ 1: T , (0 , 0 , . . . , 0) is not an optimal solution to eq. (21) : u ◦ 1: T / ∈ arg min u 1: T P T t =1 [ k x t +1 k 2 Q t + k u t ( x t ) k 2 R t ] Σ t | t = W t =0 . Theorem 6 suggests P T t =1 Θ t 0 holds if and only if for any non-zero initial condition x 1 the all-zeroes control policy u ◦ 1: T = (0 , 0 , . . . , 0) is suboptimal for the noiseless, perfect state-information LQG problem. Intuitively , this en- compasses most practical control design problems where a zero controller would result in a suboptimal behavior of the system (LQG control design itself would be unnecessary in the case where a zero controller, i.e., no control action, can already attain the desired system performance). Overall, Algorithm 1 and Algorithm 3 are the first scalable algorithms for Problem 1 and Problem 2, respectiv ely , and they achiev e non-vanishing per -instance performance guarantees. V . N U M E R I C A L E V A L UA T I O N S W e consider two applications for the LQG control and sens- ing co-design frame work: formation contr ol and autonomous navigation . W e present a Monte Carlo analysis for both, which demonstrates: (i) the proposed sensor selection strategy is near-optimal; particularly , the resulting LQG cost matches the optimal selection in all instances for which the optimal could be computed via a brute-force approach; (ii) a more naiv e selection which attempts to minimize the state estimation cov ariance [24] (rather than the LQG cost) has degraded LQG performance, often comparable to a random selection; (iii) in the considered instances, a clev er selection of a small subset of sensors can ensure an LQG cost that is close to the one obtained by using all av ailable sensors, hence providing an effecti v e alternative for control under sensing constraints. A. Sensing-constrained formation contr ol Simulation setup. The application scenario is illustrated in Fig. 2(a). A team of n agents (blue triangles) mov es in 2D. At t = 1 , the agents are randomly deployed in a 10m × 10m square. Their objectiv e is to reach a target formation shape (red stars); in Fig. 2(a) the desired formation has an hexagonal shape, while in general for a formation of n , the desired formation is an equilateral polygon with n vertices. Each robot is modeled as a double-integrator , with state x i = [ p i v i ] T ∈ R 4 ( p i is agent i ’ s position, and v i its velocity), and can control its acceleration u i ∈ R 2 . The process noise is a diagonal matrix W = diag [1 e − 2 , 1 e − 2 , 1 e − 4 , 1 e − 4 ] . Each robot i is equipped with a GPS, which measures the agent position p i with a cov ariance V g ps,i = 2 · I 2 . Moreov er , the agents are equipped with lidars allowing each agent i to measure the relativ e position of another agent j with cov ariance V lidar,ij = 0 . 1 · I 2 . The agents have limited on- board resources, hence the y want to acti v ate only k sensors. For our tests, we consider two setups. In the first, named homogeneous formation contr ol , the LQG weight matrix Q is a block diagonal matrix with 4 × 4 blocks, and each block i chosen as Q i = 0 . 1 · I 4 ; since each block of Q weights equally the tracking error of a robot, in the homogeneous case the tracking error of all agents is equally important. In the second setup, named hetero geneous formation contr ol , Q is chose as abov e, except for one of the agents, say robot 1, for which we choose Q 1 = 10 · I 4 ; this setup models the case in which each agent has a different role or importance, hence one weights differently the tracking error of the agents. In both cases the matrix R is chosen to be the identity matrix. The simulation is carried on over T time steps, and T is also chosen as LQG horizon. Results are av eraged ov er 100 Monte Carlo runs: at each run we randomize the initial estimation cov ariance Σ 1 | 1 . Compared techniques. W e compare fi ve techniques. All techniques use an LQG-based estimator and controller , and they only differ by the selections of the acti ve sensors. The first approach is the optimal sensor selection, denoted as optimal , which attains the minimum in eq. (10), and which we compute by enumerating all possible subsets. The second approach is a pseudo-random sensor selection, denoted as random ∗ , which selects all the GPS measurements and a random subset of the lidar measurements. The third approach, denoted as logdet , selects sensors so to minimize the av erage log det of the estimation cov ariance ov er the horizon; this approach resembles [24] and is agnostic to the control task. The fourth approach is the proposed sensor selection strategy (Algorithm 2), and is denoted as s-LQG . Finally , we also report the LQG performance when all sensors are selected. This approach is denoted as allSensors . Results. The results of the numerical analysis are reported in Fig. 3. When not specified otherwise, we consider a formation of n = 4 agents, which can only use a total of k = 6 sensors, and a control horizon T = 20 . Fig. 3(a) shows the LQG cost for the homogeneous case and for increasing horizon. W e note that, in all tested instance, the proposed approach s-LQG matches the optimal selection optimal , and both approaches are relatively close to allSensors , which selects all the av ailable sensors. On the other hand, logdet leads to worse tracking performance, and is often close to random ∗ . These considerations are confirmed by the heterogeneous setup, in Fig. 3(b). In this case, the separation between our proposed approach and logdet becomes ev en larger; the intuition is that the heterogeneous case rew ards differently the tracking errors at different agents, hence while logdet attempts to equally reduce the estimation error across the formation, the proposed approach s-LQG selects sensors in a task-oriented fashion, since the matrices Θ t for all 9 t = 1 , 2 , . . . , T in the cost function in eq. (10) incorporate the LQG weight matrices. Fig. 3(c) shows the LQG cost attained for increasing num- ber of selected sensors k and for the homogeneous case. For increasing number of sensors all techniques con verge to allSensors (since the entire ground set is selected). Fig. 3(d) shows the same statistics for the heterogeneous case. Now , s-LQG matches allSensors earlier , starting at k = 7 ; intuitiv ely , in the heterogeneous case, adding more sensors may have marginal impact on the LQG cost (e.g., if the cost rew ards a small tracking error for robot 1, it may be of little value to tak e a lidar measurement between robot 3 and 4). This further stresses the importance of the proposed framework as a parsimonious way to control a system with minimal resources. Fig. 3(e) and Fig. 3(f) show the LQG cost attained by the compared techniques for increasing number of agents. optimal quickly becomes intractable to compute, hence we omit values beyond n = 4 . In both figures, the separation among the techniques increases with the number of agents, since the set of av ailable sensors quickly increases with n . In the heterogeneous case s-LQG remains relativ ely close to allSensors , implying that for the purpose of LQG control, using a cle verly selected small subset of sensors still ensures excellent tracking performance. B. Resour ce-constrained r obot navigation Simulation setup. The second application scenario is illus- trated in Fig. 2(b). An unmanned aerial robot (U A V) mov es in a 3D space, starting from a randomly selected location. The objectiv e of the U A V is to land, and specifically , to reach [0 , 0 , 0] with zero velocity . The U A V is modeled as a double- integrator , with state x = [ p v ] T ∈ R 6 ( p is the position, while v its velocity), and can control its acceleration u ∈ R 3 . The process noise is W = I 6 . The U A V is equipped with multiple sensors. It has an on-board GPS, measuring the UA V position p with a covariance 2 · I 3 , and an altimeter, measuring only the last component of p (altitude) with standard deviation 0 . 5m . Moreov er , the UA V can use a stereo camera to measure the relativ e position of ` landmarks on the ground; we assume the location of each landmark to be known approximately , and we associate to each landmark an uncertainty cov ariance (red ellipsoids in Fig. 2(b)), which is randomly generated at the beginning of each run. The U A V has limited on- board resources, hence it wants to use only a few of sensing modalities. For instance, the resource-constraints may be due to the power consumption of the GPS and the altimeter , or may be due to computational constraints that prev ent to run multiple object-detection algorithms to detect all landmarks on the ground. W e consider two sensing-constrained scenarios: (i) all sensors to hav e the same cost (equal to 1 ), in which case, the U A V can activ ate at most k sensors; (ii) the sensors to hav e heterogeneous costs: particularly , the GPS’ s cost is set equal to 3 ; the altimeter’ s cost is set equal to 2; and each landmark’ s cost is set equal to 1 . W e use Q = diag [1 e − 3 , 1 e − 3 , 10 , 1 e − 3 , 1 e − 3 , 10] and R = I 3 . The structure of Q reflects the fact that during landing we are particularly interested in controlling the v ertical 10 15 20 25 30 horizon 2 4 6 8 10 12 LQG cost random * optima l logdet s-LQG allSens ors (a) homogeneous 10 15 20 25 30 horizon 50 100 150 200 250 LQG cost random * optimal logdet s-LQG allSenso rs (b) heterogeneous 4 5 6 7 8 9 10 maxNrUsedSensors 4 6 8 10 12 14 16 LQG cost random * optimal logdet s-LQG allSenso rs (c) homogeneous 4 5 6 7 8 9 10 maxNrUsedSensors 50 100 150 200 250 300 LQG cost random * optimal logdet s-LQG allSenso rs (d) heterogeneous 3 5 7 9 11 nrRobots 0 5 10 15 20 25 LQG cost random * optima l logdet s-LQG allSens ors (e) homogeneous 3 5 7 9 11 nrRobots 40 60 80 100 120 140 160 180 LQG cost random * optimal logdet s-LQG allSenso rs (f) heterogeneous Fig. 3. LQG cost for increasing (a)-(b) control horizon T , (c)-(d) number of used sensors k (all sensors are considered to have sensor-cost 1), and (e)-(f) number of agents n . Statistics are reported for the homogeneous formation control setup (left column), and the heterogeneous setup (right column). direction and the vertical velocity (entries with larger weight in Q ), while we are less interested in controlling accurately the horizontal position and v elocity (assuming a suf ficiently large landing site). In the following, we present results av eraged ov er 100 Monte Carlo runs: in each run, we randomize the cov ariances describing the landmark position uncertainty . Compared techniques. W e consider the fi ve techniques discussed in the pre vious section. Results. The results of our numerical analysis are reported in Fig. 4 for the case where all sensors have the same sensor- cost, and in Fig. 5 for the case where sensors hav e different costs. When not specified otherwise, we consider a total of k = 3 sensors to be selected, and a control horizon T = 20 . In Fig. 4(a) we plot the LQG cost normalized by the horizon, which makes more visible the differences among the tech- niques. Similarly to the formation control example, s-LQG matches the optimal selection optimal , while logdet and random ∗ hav e suboptimal performance. Fig. 4(b) shows the LQG cost attained by the compared techniques for increasing number of selected sensors k . All techniques con v erge to allSensors for increasing k , but in the regime in which fe w sensors are used s-LQG still outperforms alternative sensor selection schemes, and matches optimal . 10 10 20 30 40 50 horizon 90 100 110 120 130 LQG cost / T random * optimal logdet s-LQG allSenso rs (a) heterogeneous 4 6 8 10 12 maxNrUsedSensors 2250 2300 2350 2400 2450 2500 LQG cost random* optimal logdet s-LQG allSenso rs (b) heterogeneous Fig. 4. LQG cost for increasing (a) horizon T , and (b) number of used sensors k (all sensors are considered to have cost 1). Fig. 5 shows the LQG cost attained by the compared techniques for increasing control horizon and various sensor cost budgets b . Similarly to Fig. 4, s-LQG has the same performance as optimal , whereas logdet and random ∗ hav e suboptimal performance. Notably , for b = 15 all sensors can be chosen; for this reason in Fig. 5(d) all compared techniques (but the random) have the same performance. V I . C O N C L U D I N G R E M A R K S W e addressed an LQG control and sensing co-design prob- lem, where one jointly designs control and sensing policies under resource constraints. The problem is central in modern IoT and IoBT control applications, ranging from large-scale networked systems to miniaturized robotic networks. Moti- vated by the inapproximability of the problem, we provided the first scalable algorithms with per-instance suboptimality bounds. Importantly , the bounds are non-vanishing under general control-theoretic conditions, encountered in most real- world systems. T o this end, we also extended the literature on supermodular optimization: by providing scalable algorithms for optimizing approximately supermodular functions subject to heterogeneous cost constraints; and by providing no vel suboptimality bounds that improve the known bounds ev en for exactly supermodular optimization. The paper opens several av enues for future research. First, the development of distributed implementations of the pro- posed algorithms would of fer computational speedups. Sec- ond, other co-design problems are interesting to be explored, such as the co-design of control-sensing-actuation. Third, while we provide bounds on an approximate sensor design against optimal design, one could provide bounds against the case where all sensors are used [68]. Finally , in adversarial or failure-prone scenarios, one must account for sensor failures; to this end, one could le verage recent results on r obust combinatorial optimization [69]. A P P E N D I X A : P R E L I M I N A RY FAC T S Lemma 1 ([70, Proposition 8.5.5]). Consider two positive definite matrices A 1 and A 2 . If A 1 A 2 , then A − 1 2 A − 1 1 . Lemma 2 (T race inequality [70, Pr oposition 8.4.13]). Con- sider a symmetric A , and a positive semi-definite B . Then, λ min ( A ) tr ( B ) ≤ tr ( AB ) ≤ λ max ( A ) tr ( B ) . 10 20 30 40 50 horizon 100 120 140 160 180 200 LQG cost/T (a) budget b = 6 10 20 30 40 50 horizon 105 110 115 120 125 130 135 140 LQG cost/T (b) budget b = 8 10 20 30 40 50 horizon 105 110 115 120 125 130 LQG cost/T (c) budget b = 10 10 20 30 40 50 horizon 106 108 110 112 114 116 118 120 LQG cost/T (d) budget b = 15 Fig. 5. LQG cost for increasing horizon T and for various sensing b udgets b . Lemma 3 (W oodbury identity [70, Corollary 2.8.8]). Con- sider A , C , U and V such that A , C , and A + U C V ar e in vertible. Then, ( A + U C V ) − 1 = A − 1 − A − 1 U ( C − 1 + V A − 1 U ) − 1 V A − 1 . Lemma 4 ([70, Proposition 8.5.12]). Consider two symmetric matrices A 1 and A 2 , and a positive semi-definite matrix B . If A 1 A 2 , then tr ( A 1 B ) ≤ tr ( A 2 B ) . Lemma 5 ([1, A ppendix E]). F or any sensors S , Σ t | t ( S ) is the solution of the Kalman filtering recur sion Σ t | t ( S ) = [Σ t | t − 1 ( S ) − 1 + C t ( S ) T V t ( S ) − 1 C t ( S )] − 1 , Σ t +1 | t ( S ) = A t Σ t | t ( S ) A T t + W t , (22) with boundary condition Σ 1 | 1 ( S ) = Σ 1 | 1 . Lemma 6 ([64, Lemma 6]). Consider two sensor sets S 1 , S 2 ⊆ V . If S 1 ⊆ S 2 , then Σ 1 | 1 ( S 1 ) Σ 1 | 1 ( S 2 ) . Lemma 7 ([64, Corollary 1]). Let Σ t | t be defined as in eq. (22) with boundary condition Σ 1 | 1 ; similarly , let ¯ Σ t | t be defined as in eq. (22) with boundary condition ¯ Σ 1 | 1 . If Σ t | t ¯ Σ t | t , then Σ t + i | t + i ¯ Σ t + i | t + i for any positive inte ger i . Lemma 8 ([64, Corollary 2]). Let Σ t | t be defined as in eq. (22) with boundary condition Σ 1 | 1 ; similarly , let ¯ Σ t | t be defined as in eq. (22) with boundary condition ¯ Σ 1 | 1 . If Σ t | t ¯ Σ t | t , then Σ t + i | t + i − 1 ¯ Σ t + i | t + i − 1 for any positive inte ger i . Lemma 9. Consider positive r eal number s a , b , γ , a 1 , a 2 , . . . , a n such that P n i =1 a i = a . Then, f ( a 1 , a 2 , . . . , a n ) = 1 − n Y i =1 1 − γ a i b has its minimum at a 1 = a 2 = . . . = a n = a/n , and f ( a/n, a/n, . . . , a/n ) = 1 − 1 − aγ bn n ≥ 1 − e − aγ /b . 11 Pr oof of Lemma 9: The proof is obtained using the method of Lagrange multipliers, and is omitted (for a complete proof, see [65, Proof of Lemma 9]) Lemma 10 (Monotonicity of cost function in eq. (10) [64, Proposition 2]). Consider P T t =1 tr Θ t Σ t | t ( S ) in eq. (10) . If S 1 ⊆ S 2 , then P T t =1 tr Θ t Σ t | t ( S 1 ) ≥ P T t =1 tr Θ t Σ t | t ( S 2 ) . A P P E N D I X B : P R O O F O F T H E O R E M 1 B.1. Pr oof of part (1) of Theor em 1 Lemma 11. Consider any S , and let u ? 1: T ( S ) be the vector of control policies ( K 1 ˆ x 1 ( S ) , K 2 ˆ x 2 ( S ) , . . . , K T ˆ x T ( S )) . Then u ? 1: T ( S ) is an optimal control policy: u ? 1: T ( S ) ∈ arg min u 1: T ( S ) h [ S , u 1: T ( S )] , (23) and, particularly , u ? 1: T ( S ) attains an LQG cost equal to: h [ S , u ? 1: T ( S )] = E ( k x 1 k N 1 )+ T X t =1 tr [Θ t Σ t | t ( S )] + tr ( W t S t ) . (24) Pr oof of Lemma 11: The proof follows Lemma 1’ s proof in [20], and can also be found in [65, Appendix B]. Pr oof of part (1) of Theor em 1: Eq. (10) is a direct consequence of eq. (24), since the value of Problem 1 is equal to min S ⊆V ,c ( S ) ≤ b h [ S , u ? 1: T ( S )] , and both E ( k x 1 k N 1 ) = tr Σ 1 | 1 N 1 and P T t =1 tr ( W t S t ) are independent of S . Finally , eq. (11) directly follo ws from eq. (23). B.1. Pr oof of part (2) of Theor em 1 Lemma 12. S ? , and u ? 1: T ar e a solution to Pr oblem 2 if and only if they ar e a solution to min S ⊆V ,u 1: T ( S ) c ( S ) , s . t . min u 1: T ( S ) h [ S , u 1: T ( S )] ≤ κ. (25) Pr oof of Lemma 12: W e prove the lemma by contradic- tion. Particularly , let S ? and u ? 1: T be a solution to Problem 2, and assume by contradiction that they are not to eq. (25), which instead has solution b S and b u 1: T . By optimality of b S and b u 1: T (and suboptimality of S ? and u ? 1: T ) in eq. (25), it follows c ( b S ) < c ( S ? ) . In addition, g ( b S ) ≤ κ , since ( b S , b u 1: T ) must be feasible for eq. (25). Howe ver , the latter implies h b S , b u 1: T ≤ κ . Therefore, ( b S , b u 1: T ) is feasible for Problem 2 and has a better objective value with respect to the optimal solution ( S ? , u ? 1: T ) (we already observed c ( b S ) < c ( S ? ) ), leading to contradiction. For the other direction, now let S ? and u ? 1: T be a solution to eq. (25), and assume that they are not to Problem 2, which instead has solution ( b S , b u 1: T ) . By optimality of ( b S , b u 1: T ) (and suboptimality of S ? and u ? 1: T ) in Problem 2, it follows c ( b S ) < c ( S ? ) . In addition, h b S , b u 1: T ≤ κ , since ( b S , b u 1: T ) must be feasible for Problem 2, and, as a result, g ( b S ) ≤ κ . Therefore, ( b S , b u 1: T ) is feasible for eq. (25) and has a better objectiv e value with respect to the optimal solution ( S ? , u ? 1: T ) (we already observed c ( b S ) < c ( S ? ) ), leading to contradiction. Pr oof of part (2) of Theor em 1: The proof follows from Lemma 11 and Lemma 12. A P P E N D I X C : P R O O F O F T H E O R E M 2 Consider a problem instance for Problem 1 and Problem 2, where T = 1 , and A 1 = B 1 = C 1 = Q 1 = R 1 = I . Then, Θ 1 = I / 2 , and, as a result, the objectiv e function in eq. (10) becomes 1 / 2 tr [Σ 1 | 1 ( S )] . No w , choosing Σ 1 | 1 ( S ) to be the steady state Kalman filtering matrix defined in [66, Theorem 2], as well as, c ( S ) , b be as in [66, Theorem 2], makes eq. (10) and the optimization problem in [66] equiv- alent. But, the latter is inapproximable in polynomial time [66, Theorem 2] (namely , unless NP = P , there is no polyno- mial time algorithm that guarantees a constant suboptimality bound). Therefore, eq. (10) is too, and due to Theorem 1 both Problem 1 and Problem 2 as well. A P P E N D I X D : P R O O F O F T H E O R E M 3 For any S , let f ( S ) , P T t =1 tr [Θ t Σ t | t ( S )] be the objectiv e function in eq. (10), S ? be a solution in eq. (10), and b ? , c ( S ? ) . Let b S 2 be the set Algorithm 2 constructs by the end of line 19; let G , b S 2 . Let s i be the i -th element added in G during the i -th iteration of Algorithm 2’ s “while loop” (lines 3- 16). Let G i , { s 1 , s 2 , . . . , s i } . Finally , consider Algorithm 2’ s “while loop” terminates after l + 1 iterations. Algorithm 2’ s “while loop” terminates: (i) when V 0 = ∅ , that is, when all av ailable sensors in V can been chosen by Algorithm 2 as active while satisfying the budget constraint b ; and (ii) when c ( G l +1 ) > b , that is, when the addition of s l +1 in G l makes the cost of G l +1 to violate the budget b . Henceforth, we focus on the second scenario, which implies s l +1 will be removed by the “if ” statement in Algorithm 2’ s lines 17–19 and, as a result, G l = b S 2 . Lemma 13 (Generalization of [51, Lemma 2]). F or i = 1 , 2 , . . . , l + 1 , it holds f ( G i − 1 ) − f ( G i ) ≥ γ f c ( s i ) b ? ( f ( G i − 1 ) − f ( S ? )) . Pr oof of Lemma 13: Due to the monotonicity of the cost function f in eq. (10) (Lemma 10), f ( G i − 1 ) − f ( S ? ) ≤ f ( G i − 1 ) − f ( S ? ∪ G i − 1 ) = f ( G i − 1 ) − f [( S ? \ G i − 1 ) ∪ G i − 1 ] . Let { z 1 , z 2 , . . . , z m } , S ? \ G i − 1 , and also let d j , f ( G i − 1 ∪{ z 1 , z 2 , . . . , z j − 1 } ) − f ( G i − 1 ∪{ z 1 , z 2 , . . . , z j } ) , for j = 1 , 2 , . . . , m . Then, f ( G i − 1 ) − f ( S ? ) ≤ P m j =1 d j . Now , d j c ( z j ) ≤ f ( G i − 1 ) − f ( G i − 1 ∪ { z j } ) γ f c ( z j ) ≤ f ( G i − 1 ) − f ( G i ) γ f c ( s i ) , where the first inequality holds due to the Definition 3 of γ f , and the second due to the greedy rule (Algorithm 2’ s line 13) and the definitions of G i , and s i . Since P m j =1 c ( z j ) ≤ b ? , f ( G i − 1 ) − f ( S ? ) ≤ m X j =1 d j ≤ b ? f ( G i − 1 ) − f ( G i ) γ f c ( s i ) . 12 Lemma 14 (Adapation of [51, Lemma 3]). F or i = 1 , 2 , . . . , l + 1 , f ( ∅ ) − f ( G i ) ≥ 1 − i Y j =1 1 − γ f c ( s j ) b ? [ f ( ∅ ) − f ( S ? )] . Pr oof of Lemma 14: W e complete the proof induc- tiv ely . For i = 1 , we need to prov e f ( ∅ ) − f ( G 1 ) ≥ γ f c ( s 1 ) /b ? [ f ( ∅ ) − f ( S ? )] , which follows from Lemma 13 for i = 1 . Then, for i > 1 , f ( ∅ ) − f ( G i ) = f ( ∅ ) − f ( G i − 1 ) + [ f ( G i − 1 ) − f ( G i )] ≥ f ( ∅ ) − f ( G i − 1 )+ γ f c ( s i ) b ? ( f ( G i − 1 ) − f ( S ? )) = 1 − γ f c ( s i ) b ? [ f ( ∅ ) − f ( G i − 1 ])+ γ f c ( s i ) b ? [ f ( ∅ ) − f ( S ? )] ≥ 1 − γ f c ( s i ) b ? 1 − i − 1 Y j =1 1 − γ f c ( s j ) b ? [ f ( ∅ ) − f ( S ? )] + γ f c ( s i ) b ? [ f ( ∅ ) − f ( S ? )] = 1 − i Y j =1 1 − γ f c ( s j ) b ? [ f ( ∅ ) − f ( S ? )] , where we used Lemma 13 for the first inequality , and the induction hypothesis for the second. Pr oof of part (1) of Theor em 3: T o prov e Algo- rithm 1’ s approximation bound γ g / 2 (1 − e − γ g ) , we let b 0 , P l +1 j =1 c ( s j ) . Then, f ( ∅ ) − f ( G l +1 ) ≥ 1 − l +1 Y j =1 1 − γ f c ( s j ) b ? [ f ( ∅ ) − f ( S ? )] ≥ 1 − e − γ f b 0 /b ? [ f ( ∅ ) − f ( S ? )] , ≥ 1 − e − γ f [ f ( ∅ ) − f ( S ? )] , (26) where the first inequality follows from Lemma 14, the second from Lemma 9, and ineq. (26) from that b 0 /b ? ≥ 1 and, as a result, e − γ f b 0 /b ? ≤ e − γ f , that is, 1 − e − γ f b 0 /b ? ≥ 1 − e − γ f . Also, f ( ∅ ) − f ( b S 1 ) ≥ γ f [ f ( G l ) − f ( G l +1 )] due to the Definition 3 of γ g and, as a result, γ f [ f ( ∅ ) − f ( G l +1 )] ≤ f ( ∅ ) − f ( b S 1 ) + γ f [ f ( ∅ ) − f ( G l )] ≤ 2 max n f ( ∅ ) − f ( b S 1 ) , γ f [ f ( ∅ ) − f ( G l )] o . (27) Substituting ineq. (26) in ineq. (27), and rearranging, giv es max n f ( ∅ ) − f ( b S 1 ) , γ f [ f ( ∅ ) − f ( G l )] o ≥ γ f 2 1 − e − γ f [ f ( ∅ ) − f ( S ? )] , which implies (since γ f takes values in [0 , 1] ) max h f ( ∅ ) − f ( b S 1 ) , f ( ∅ ) − f ( G l ) i ≥ γ f 2 1 − e − γ f [ f ( ∅ ) − f ( S ? )] . (28) Finally , the bound γ g / 2 (1 − e − γ g ) follows from ineq. (28) as the combination of the following three observ ations: i) G l = b S 2 , and, as a result, f ( ∅ ) − f ( G l ) = f ( ∅ ) − f ( b S 2 ) . ii) Algorithm 2 returns b S such at b S ∈ arg max S ∈{ b S 1 , b S 2 } [ f ( ∅ ) − f ( S )] and, as a result, the previous observation, along with ineq. (28), gives: f ( ∅ ) − f ( b S ) ≥ γ f 2 1 − e − γ f [ f ( ∅ ) − f ( S ? )] . (29) iii) Finally , Lemma 11 implies that for any S , S 0 , g ( S ) = f ( S ) + E ( k x 1 k N 1 ) + P T t =1 tr ( W t S t ) , where E ( k x 1 k N 1 ) + P T t =1 tr ( W t S t ) is independent of S . As a result, for any S , S 0 ⊆ V , then f ( S ) − f ( S 0 ) = g ( S ) − g ( S 0 ) , which implies γ f = γ g due to Definition 3. In addition, Lemma 11 implies for any S ⊆ V that g ( S ) = h [ S , u 1: T ( S )] and g ? = g ( S ? ) . Thereby , for any S that f ( ∅ ) − f ( S ) = g ( ∅ ) − g ( S ) = h [ ∅ , u 1: T ( ∅ )] − h [ S , u 1: T ( S )] and f ( ∅ ) − f ( S ? ) = g ( ∅ ) − g ( S ? ) = h [ ∅ , u 1: T ( ∅ )] − g ? . Overall, ineq. (29) is written as h [ ∅ , u 1: T ( ∅ )] − h [ b S , u 1: T ( b S )] ≥ γ f 2 1 − e − γ f { h [ ∅ , u 1: T ( ∅ )] − g ? } , which implies the bound γ g / 2 (1 − e − γ g ) . It remains to pro ve 1 − e − γ g c ( b S ) /b : f ( ∅ ) − f ( G l ) ≥ 1 − l Y j =1 1 − γ f c ( s j ) b ? [ f ( ∅ ) − f ( G l )] ≥ 1 − e − γ f c ( G l ) /b ? [ f ( ∅ ) − f ( S ? )] , ≥ 1 − e − γ f c ( G l ) /b [ f ( ∅ ) − f ( S ? )] , (30) where the first inequality follows from Lemma 14, the second from Lemma 9, and ineq. (30) from that c ( G l ) /b ? ≥ c ( G l ) /b , since b ? ≤ b , which implies e − γ f c ( G l ) /b ? ≤ e − γ f c ( G l ) /b , i.e., 1 − e − γ f b 0 /b ? ≥ 1 − e − γ f c ( G l ) /b . The proof is completed using the observations (i)-(iii) above for γ g / 2 (1 − e − γ g ) . Pr oof of part (2) of Theor em 3: The proof is parallel to that of Theorem 2 in [71]. A P P E N D I X E : P R O O F O F T H E O R E M 4 W e consider the notation in Appendix D. Also, let S ? be a solution to Problem 2, and b ? = c ( S ? ) . Consider the computation of the set b S in Algorithm 4, and let G , b S be the returned one. Let s i be the i -th element added in G during the i -th iteration of Algorithm 4’ s “while loop. ” Finally , let G i , { s 1 , s 2 , . . . , s i } . Lemma 15 (Adaptation of Lemma 13). F or i = 1 , 2 , . . . , |G | , f ( G i − 1 ) − f ( G i ) ≥ γ f c ( s i ) b ? ( f ( G i − 1 ) − f ( S ? )) . Pr oof: The proof is parallel to Lemma 13’ s proof. 13 Lemma 16 (Adaptation of Lemma 14). F or i = 1 , 2 , . . . , |G | , f ( ∅ ) − f ( G i ) ≥ 1 − i Y j =1 1 − γ f c ( s j ) b ? [ f ( ∅ ) − f ( S ? )] . Pr oof: The proof is parallel to Lemma 14’ s proof. Pr oof of part (1) of Theor em 4: W e first ob- serve ineq. (18) holds since Algorithm 3 returns b S once h [ b S , u 1: T ( b S )] ≤ κ is satisfied. It remains to prove ineq. (19). Let l , |G | ; then, G l = G , by the definition of G i , and from Lemma 14 for i = l − 1 , f ( ∅ ) − f ( G l − 1 ) ≥ 1 − l − 1 Y j =1 1 − γ f c ( s j ) b ? [ f ( ∅ ) − f ( S ? )] ≥ 1 − e − γ f c ( G l − 1 ) /b ? [ f ( ∅ ) − f ( S ? )] , (31) where ineq. (31) follo ws from Lemma 9. Moreo ver , Lemma 11 implies that for any S , S 0 , it is g ( S ) = f ( S ) + E ( k x 1 k N 1 ) + P T t =1 tr ( W t S t ) , where E ( k x 1 k N 1 ) + P T t =1 tr ( W t S t ) is inde- pendent of S , and, as a result, f ( S ) − f ( S 0 ) = g ( S ) − g ( S 0 ) , which implies γ f = γ g . Moreover , Lemma 11 implies for any S ⊆ that g ( S ) = h [ S , u 1: T ( S )] , and, as a result, f ( ∅ ) − f ( G l − 1 ) = h [ ∅ , u 1: T ( ∅ )] − h [ G l − 1 , u 1: T ( G l − 1 )] and f ( ∅ ) − f ( S ? ) = h [ ∅ , u 1: T ( ∅ )] − h [ S ? , u 1: T ( S ? )] . In sum, ineq. (31) is the same as the inequality h [ ∅ , u 1: T ( ∅ )] − h [ G l − 1 , u 1: T ( G l − 1 )] ≥ 1 − e − γ g c ( G l − 1 ) /b ? { h [ ∅ , u 1: T ( ∅ )] − h [ S ? , u 1: T ( S ? )] } , which, by letting β , 1 − e − γ g c ( G l − 1 ) /b ? and rearranging, gi ves h [ G l − 1 , u 1: T ( G l − 1 )] ≤ (1 − β ) h [ ∅ , u 1: T ( ∅ )] + β h [ S ? , u 1: T ( S ? )] ≤ (1 − β ) h [ ∅ , u 1: T ( ∅ )] + β κ, (32) where the second inequality holds because S ? is a solution to Problem 2 and, as result, h [ S ? , u 1: T ( S ? )] ≤ κ . Now , we recall Algorithm 4 returns G = G l when for i = l it is the first time h [ G i , u 1: T ( G i )] ≤ κ . Therefore, h [ G l − 1 , u 1: T ( G l − 1 )] > κ and, as a result, there exists > 0 such that h [ G l − 1 , u 1: T ( G l − 1 )] = (1 + ) κ , and ineq. (32) gives (1 + ) κ ≤ (1 − β ) h [ ∅ , u 1: T ( ∅ )] + β κ ⇒ κ ≤ (1 − β ) h [ ∅ , u 1: T ( ∅ )] − (1 − β ) κ ⇒ κ ≤ (1 − β ) { h [ ∅ , u 1: T ( ∅ )] − κ } ⇒ κ ≤ e − γ g c ( G l − 1 ) /b ? { h [ ∅ , u 1: T ( ∅ )] − κ } ⇒ log κ h [ ∅ , u 1: T ( ∅ )] − κ ≤ − γ g c ( G l − 1 ) /b ? ⇒ c ( G l − 1 ) ≤ 1 γ g log h [ ∅ , u 1: T ( ∅ )] − κ κ b ? ⇒ c ( G ) ≤ c ( s l ) + 1 γ g log h [ ∅ , u 1: T ( ∅ )] − κ κ b ? , where the latter holds since G = G l − 1 ∪ { s l } , due to the definitions of G , G l − 1 , and s l , and since c ( G ) = c ( G l − 1 ) + c ( s l ) . Finally , since the definition of implies κ = h [ G l − 1 , u 1: T ( G l − 1 )] − κ , and the definition of G is G = b S , the proof of ineq. (18) is complete. Pr oof of part (2) of Theor em 4: The proof is similar to the proof of part (2) of Theorem 3. A P P E N D I X F : P R O O F O F T H E O R E M 5 W e complete the proof by first deri ving a lower bound for the numerator of γ g , and then, by deriving an upper bound for the denominator γ g . W e use the follo wing no- tation: c , E ( x T 1 N 1 x 1 ) + P T t =1 tr ( W t S t ) , and for any S , and time t = 1 , 2 , . . . , T , f t ( S ) , tr Θ t Σ t | t ( S ) . Then, g ( S ) = c + P T t =1 f t ( S ) , due to eq. (24) in Lemma 11. a) Lower bound for the numerator of γ g : The numerator of γ g has the form P T t =1 [ f t ( S ) − f t ( S ∪ { v } )] , for some S , and v ∈ V . W e no w lo wer bound each f t ( S ) − f t ( S ∪ { v } ) : from eq. (22) in Lemma 5, observe Σ t | t ( S ∪ { v } ) = [Σ − 1 t | t − 1 ( S ∪ { v } ) + P i ∈S ∪{ v } ¯ C T i,t ¯ C i,t ] − 1 . Define Ω t = Σ − 1 t | t − 1 ( S ) + P T i ∈S ¯ C T i,t ¯ C i,t , and ¯ Ω t = Σ − 1 t | t − 1 ( S ∪ { v } ) + P T i ∈S ¯ C T i,t ¯ C i,t ; using Lemma 3, f t ( S ∪ { v } ) = tr Θ t ¯ Ω − 1 t − tr Θ t ¯ Ω − 1 t ¯ C T v ,t ( I + ¯ C v ,t ¯ Ω − 1 t ¯ C T v ,t ) − 1 ¯ C v ,t ¯ Ω − 1 t . Therefore, for any time t ∈ { 1 , 2 . . . , T } , f t ( S ) − f t ( S ∪ { v } ) = tr Θ t Ω − 1 t − tr Θ t ¯ Ω − 1 t + tr Θ t ¯ Ω − 1 t ¯ C T v ,t ( I + ¯ C v ,t ¯ Ω − 1 t ¯ C T v ,t ) − 1 ¯ C v ,t ¯ Ω − 1 t ≥ tr Θ t ¯ Ω − 1 t ¯ C T v ,t ( I + ¯ C v ,t ¯ Ω − 1 t ¯ C T v ,t ) − 1 ¯ C v ,t ¯ Ω − 1 t , (33) where ineq. (33) holds because tr Θ t Ω − 1 t ≥ tr Θ t ¯ Ω − 1 t . In particular, tr Θ t Ω − 1 t ≥ tr Θ t ¯ Ω − 1 t is implied as follo ws: Lemma 6 implies Σ 1 | 1 ( S ) Σ 1 | 1 ( S ∪ { v } ) . Then, Corollary 8 implies Σ t | t − 1 ( S ) Σ t | t − 1 ( S ∪ { v } ) , and as a result, Lemma 1 implies Σ t | t − 1 ( S ) − 1 Σ t | t − 1 ( S ∪ { v } ) − 1 . Now , Σ t | t − 1 ( S ) − 1 Σ t | t − 1 ( S ∪ { v } ) − 1 and the definition of Ω t and of ¯ Ω t imply Ω t ¯ Ω t . Next, Lemma 1 implies Ω − 1 t ¯ Ω − 1 t . As a result, since also Θ t is a symmetric matrix, Lem- ma 4 gives the desired inequality tr Θ t Ω − 1 t ≥ tr Θ t ¯ Ω − 1 t . Continuing from the ineq. (33), f t ( S ) − f t ( S ∪ { v } ) ≥ tr ¯ C v ,t ¯ Ω − 1 t Θ t ¯ Ω − 1 t ¯ C T v ,t ( I + ¯ C v ,t ¯ Ω − 1 t ¯ C T v ,t ) − 1 ≥ λ min (( I + ¯ C v ,t ¯ Ω − 1 t ¯ C T v ,t ) − 1 ) tr ¯ C v ,t ¯ Ω − 1 t Θ t ¯ Ω − 1 t ¯ C T v ,t , (34) where ineq. (34) holds due to Lemma 2. From ineq. (34), f t ( S ) − f t ( S ∪ { v } ) ≥ = λ − 1 max ( I + ¯ C v ,t ¯ Ω − 1 t ¯ C T v ,t ) tr ¯ C v ,t ¯ Ω − 1 t Θ t ¯ Ω − 1 t ¯ C T v ,t ≥ λ − 1 max ( I + ¯ C v ,t Σ t | t ( ∅ ) ¯ C T v ,t ) tr ¯ C v ,t ¯ Ω − 1 t Θ t ¯ Ω − 1 t ¯ C T v ,t = λ − 1 max ( I + ¯ C v ,t Σ t | t ( ∅ ) ¯ C T v ,t ) tr Θ t ¯ Ω − 1 t ¯ C T v ,t ¯ C v ,t ¯ Ω − 1 t , (35) where we used ¯ Ω − 1 t Σ t | t ( ∅ ) , which holds since: ¯ Ω t implies ¯ Ω t Σ − 1 t | t − 1 ( S ∪ { v } ) , and as a result, from Lemma 1 ¯ Ω − 1 t Σ t | t − 1 ( S ∪ { v } ) . In addition, Corollary 8 and Σ 1 | 1 ( S ∪ { v } ) Σ 1 | 1 ( ∅ ) , which holds due to Lemma 6, 14 imply Σ t | t − 1 ( S ∪ { v } ) Σ t | t − 1 ( ∅ ) . Finally , from eq. (22) in Lemma 5, Σ t | t − 1 ( ∅ ) = Σ t | t ( ∅ ) . Overall, ¯ Ω − 1 t Σ t | t ( ∅ ) . Consider t 0 ∈ { 1 , 2 . . . , T } such that ¯ Ω − 1 t 0 ¯ C T v ,t 0 ¯ C v ,t 0 ¯ Ω − 1 t 0 ¯ Ω − 1 t ¯ C T v ,t ¯ C v ,t ¯ Ω − 1 t , for any t = 1 , . . . , T . Also, let Φ , ¯ Ω − 1 t 0 ¯ C T v ,t 0 ¯ C v ,t 0 ¯ Ω − 1 t 0 , and l , min t ∈{ 1 , 2 ...,T } ,v ∈V λ − 1 max ( I + ¯ C v ,t Σ t | t ( ∅ ) ¯ C T v ,t ) . Summing ineq. (35) across all t ∈ { 1 , 2 . . . , T } , and using Lemmata 2 and 4, g ( S ) − g ( S ∪ { v } ) ≥ l P T t =1 tr Θ t ¯ Ω − 1 t ¯ C T v ,t ¯ C v ,t ¯ Ω − 1 t ≥ l λ min P T t =1 Θ t tr (Φ) > 0 , which is non-zero because P T t =1 Θ t 0 and Φ is a non-zero positiv e semi-definite matrix. Finally , we lo wer bound tr (Φ) , using Lemma 2: tr (Φ) = tr ¯ Ω − 1 t 0 ¯ C T v ,t 0 ¯ C v ,t 0 ¯ Ω − 1 t 0 ≥ λ min ( ¯ Ω − 2 t 0 ) tr ¯ C T v ,t 0 ¯ C v ,t 0 ≥ λ 2 min (Σ t 0 | t 0 ( V )) tr ¯ C T v ,t 0 ¯ C v ,t 0 , (36) where ineq. (36) holds because ¯ Ω − 1 t 0 Σ t 0 | t 0 ( V ) . Particularly , ¯ Ω − 1 t 0 Σ t 0 | t 0 ( S ∪ { v } ) is deriv ed by applying Lemma 1 to ¯ Ω t 0 ¯ Ω t 0 + ¯ C T v ,t ¯ C T v ,t = Σ − 1 t 0 | t 0 ( S ∪ { v } ) , where the equality holds by the definition of ¯ Ω t 0 . In addition, due to Lemma 6, Σ 1 | 1 ( S ∪ { v } ) Σ 1 | 1 ( V ) , and as a result, from Corollary 7, Σ t 0 | t 0 ( S ∪ { v } ) Σ t 0 | t 0 ( V ) . Overall, ¯ Ω − 1 t 0 Σ t 0 | t 0 ( V ) holds. b) Upper bound for the denominator of γ g : The proof follows similar ideas as abov e, and is omitted (for a complete proof, see [65, Proof of Theorem 5]). A P P E N D I X G : P R O O F O F T H E O R E M 6 Lemma 17 (System-lev el condition f or near-optimal co-de- sign). Let N 1 be defined as in eq. (9) . The contr ol policy u ◦ 1: T , (0 , 0 , . . . , 0) is suboptimal for the LQG problem in eq. (21) for all non-zer o initial conditions x 1 if and only if P T t =1 A T 1 · · · A T t Q t A t · · · A 1 N 1 . (37) Pr oof of Lemma 17: For any x 1 , eq. (24) in Lemma 11 implies for eq. (21): min u 1: T P T t =1 [ k x t +1 k 2 Q t + k u t ( x t ) k 2 R t ] Σ t | t = W t =0 = x T 1 N 1 x 1 , (38) since E ( k x 1 k 2 N 1 ) = x T 1 N 1 x 1 , because x 1 is known ( Σ 1 | 1 = 0 ), and Σ t | t and W t are zero. In addition, for u 1: T = (0 , 0 , . . . , 0) , the objectiv e function in eq. (21) is P T t =1 [ k x t +1 k 2 Q t + k u t ( x t ) k 2 R t ] Σ t | t = W t =0 = P T t =1 x T t +1 Q t x t +1 = x T 1 P T t =1 A T 1 A T 2 · · · A T t Q t A t A t − 1 · · · A 1 x 1 , (39) since x t +1 = A t A t − 1 · · · A 1 x 1 when all u 1 , . . . , u T are zero. From eqs. (38) and (39), we have that x T 1 N 1 x 1 < x T 1 P T t =1 A T 1 A T 2 · · · A T t Q t A t A t − 1 · · · A 1 x 1 holds for any non-zero x 1 if and only if N 1 ≺ P T t =1 A T 1 · · · A T t Q t A t A t − 1 · · · A 1 . Lemma 18. Θ t = A T t S t A t + Q t − 1 − S t − 1 , for t = 1 , . . . , T . Pr oof of Lemma 18: Using the W oobury identity in Lemma 3, and the notation in eq. (9), N t = A T t ( S − 1 t + B t R − 1 t B T t ) − 1 A t = A T t S t A t − Θ t . The latter , giv es Θ t = A T t S t A t − N t . In addition, from eq. (9), − N t = Q t − 1 − S t − 1 , since S t = Q t + N t +1 . Lemma 19. P T t =1 A T 1 A T 2 · · · A T t Q t A t A t − 1 · · · A 1 N 1 if and only if P T t =1 A T 1 A T 2 · · · A T t − 1 Θ t A t − 1 A t − 2 · · · A 1 0 . Pr oof: For i = t − 1 , . . . , 1 , we pre- and post-multiply the identity in Lemma 18 with A T i and A i , respectiv ely: Θ t = A T t S t A t + Q t − 1 − S t − 1 ⇒ A T t − 1 Θ t A t − 1 = A T t − 1 A T t S t A t A t − 1 + A T t − 1 Q t − 1 A t − 1 − A T t − 1 S t − 1 A t − 1 ⇒ A T t − 1 Θ t A t − 1 = A T t − 1 A T t S t A t A t − 1 + A T t − 1 Q t − 1 A t − 1 − Θ t − 1 + Q t − 2 − S t − 2 ⇒ Θ t − 1 + A T t − 1 Θ t A t − 1 = A T t − 1 A T t S t A t A t − 1 + A T t − 1 Q t − 1 A t − 1 + Q t − 2 − S t − 2 ⇒ . . . ⇒ . . . + A T 2 Q 2 A 2 + Q 1 − S 1 ⇒ Θ 1 + A T 1 Θ 2 A 1 + . . . + A T 1 · · · A T t − 1 Θ t A t − 1 · · · A 1 = A T 1 · · · A T t S t A t · · · A 1 + A T 1 · · · A T t − 1 Q t − 1 A t − 1 · · · A 1 + . . . + A T 1 Q 1 A 1 − N 1 ⇒ P T t =1 A T 1 · · · A T t − 1 Θ t A t − 1 · · · A 1 = P T t =1 A T 1 · · · A T t Q t A t · · · A 1 − N 1 . Lemma 20. Consider for any t = 1 , 2 , . . . , T that A t is in vertible. P T t =1 A T 1 A T 2 · · · A T t − 1 Θ t A t − 1 A t − 2 · · · A 1 0 if and only if P T t =1 Θ t 0 . Pr oof of Lemma 20: Let U t = A t − 1 A t − 2 · · · A 1 . W e first prove that for any non-zero vector z , if it is P T t =1 A T 1 A T 2 · · · A T t − 1 Θ t A t − 1 A t − 2 · · · A 1 0 , then P T t =1 z T Θ t z > 0 . Particularly , since U t is in vertible, — because for any t ∈ { 1 , 2 , . . . , T } , A t is,— P T t =1 z T Θ t z = P T t =1 z T U −> t U T t Θ t U t U − 1 t z = P T t =1 tr φ t φ T t U T t Θ t U t , (40) where we let φ t , U − 1 t z . Consider a time t 0 such that for any time t ∈ { 1 , 2 . . . , T } , φ t 0 φ T t 0 φ t φ T t . From eq. (40), using Lemmata 2 and 4, P T t =1 z T Θ t z ≥ P T t =1 tr φ t 0 φ T t 0 U T t Θ t U t = k φ t 0 k 2 2 λ min ( P T t =1 U T t Θ t U t ) > 0 . W e finally prove that for any non-zero vector z , if P T t =1 Θ t 0 , then P T t =1 z A T 1 · · · A T t − 1 Θ t A t − 1 · · · A 1 z 0 : P T t =1 z T U T t Θ t U t z = P T t =1 tr ξ T t Θ t ξ t , (41) where we let ξ t , U t z . Consider time t 0 such that for any time t ∈ { 1 , . . . , T } , ξ t 0 ξ T t 0 ξ t ξ T t . From eq. (40), P T t =1 tr ξ T t Θ t ξ t ≥ tr ξ t 0 ξ T t 0 P T t =1 Θ t = k ξ t 0 k 2 2 λ min ( P T t =1 Θ t ) > 0 . Pr oof of Theor em 6: Theorem 6 follows from the sequential application of Lemmata 17, 19, and 20. R E F E R E N C E S [1] D. P . Bertsekas, Dynamic pro gramming and optimal contr ol, V ol. I . Athena Scientific, 2005. 15 [2] T . Abdelzaher , N. A yanian, T . Basar, S. Diggavi, J. Diesner, D. Ganesan, R. Govindan, S. Jha, T . Lepoint, B. Marlin et al. , “T o ward an internet of battlefield things: A resilience perspective, ” Computer , vol. 51, no. 11, pp. 24–36, 2018. [3] N. Michael, J. Fink, and V . Kumar, “Cooperative manipulation and transportation with aerial robots, ” Autonomous Robots , vol. 30, no. 1, pp. 73–86, 2011. [4] A. Prorok, M. A. Hsieh, and V . Kumar , “The impact of diversity on optimal control policies for heterogeneous robot swarms, ” IEEE T ransactions on Robotics , vol. 33, no. 2, pp. 346–358. [5] V . Gupta, T . H. Chung, B. Hassibi, and R. M. Murray , “On a stochastic sensor selection algorithm with applications in sensor scheduling and sensor coverage, ” Automatica , vol. 42, no. 2, pp. 251–260, 2006. [6] L. Carlone and S. Karaman, “ Attention and anticipation in fast visual- inertial navigation, ” in IEEE International Confer ence on Robotics and Automation , 2017, pp. 3886–3893. [7] T . Iw aki and K. H. Johansson, “Lqg control and scheduling co-design for wireless sensor and actuator networks, ” in IEEE International W orkshop on Signal Pr ocessing Advances in Wir eless Communications , 2018, pp. 1–5. [8] G. Nair, F . Fagnani, S. Zampieri, and R. Evans, “Feedback control under data rate constraints: An overview , ” Pr oceedings of the IEEE , vol. 95, no. 1, pp. 108–137, 2007. [9] J. Baillieul and P . Antsaklis, “Control and communication challenges in networked real-time systems, ” Pr oceedings of the IEEE , vol. 95, no. 1, pp. 9–28, 2007. [10] N. Elia and S. Mitter, “Stabilization of linear systems with limited information, ” IEEE Tr ans. on Automatic Control , v ol. 46, no. 9, pp. 1384–1400, 2001. [11] G. Nair and R. Evans, “Stabilizability of stochastic linear systems with finite feedback data rates, ” SIAM Journal on Contr ol and Optimization , vol. 43, no. 2, pp. 413–436, 2004. [12] S. T atikonda and S. Mitter , “Control under communication constraints, ” IEEE T rans. on Automatic Control , vol. 49, no. 7, pp. 1056–1068, 2004. [13] V . Borkar and S. Mitter, “LQG control with communication constraints, ” Comm., Comp., Control, and Signal Pr ocessing , pp. 365–373, 1997. [14] J. L. Ny and G. Pappas, “Differentially private filtering, ” IEEE T rans. on Automatic Contr ol , vol. 59, no. 2, pp. 341–354, 2014. [15] F . Lin and V . Adetola, “Sparse output feedback synthesis via proximal alternating linearization method, ” arXiv preprint:1706.08191 , 2017. [16] F . Lin, M. Fardad, and M. R. Jovano vic, “ Augmented lagrangian approach to design of structured optimal state feedback gains, ” IEEE T ransactions on Automatic Contr ol , v ol. 56, no. 12, pp. 2923–2929, 2011. [17] F . Lin, M. Fardad, and M. R. Jov anovi ´ c, “Design of optimal sparse feedback gains via the alternating direction method of multipliers, ” IEEE T ransactions on Automatic Contr ol , vol. 58, no. 9, pp. 2426–2431, 2013. [18] A. Zare, H. Mohammadi, N. K. Dhingra, M. R. Jovano vi ´ c, and T . T . Georgiou, “Proximal algorithms for large-scale statistical modeling and optimal sensor/actuator selection, ” arXiv preprint:1807.01739 , 2018. [19] T . Liu, S. Azarm, and N. Chopra, “On decentralized optimization for a class of multisubsystem codesign problems, ” Journal of Mechanical Design , vol. 139, no. 12, p. 121404, 2017. [20] T . T anaka and H. Sandberg, “SDP-based joint sensor and controller design for information-regularized optimal LQG control, ” in IEEE Confer ence on Decision and Contr ol , 2015, pp. 4486–4491. [21] T . T anaka, P . M. Esfahani, and S. K. Mitter, “LQG control with minimum directed information: Semidefinite programming approach, ” IEEE T rans. on Automatic Contr ol , vol. 63, no. 1, pp. 37–52, 2018. [22] S. Joshi and S. Boyd, “Sensor selection via con vex optimization, ” IEEE T ransactions on Signal Pr ocessing , vol. 57, no. 2, pp. 451–462, 2009. [23] J. L. Ny , E. Feron, and M. A. Dahleh, “Scheduling continuous-time kalman filters, ” IEEE T rans. on Aut. Contr ol , vol. 56, no. 6, pp. 1381– 1394, 2011. [24] S. T . Jawaid and S. L. Smith, “Submodularity and greedy algorithms in sensor scheduling for linear dynamical systems, ” Automatica , v ol. 61, pp. 282–288, 2015. [25] Y . Zhao, F . Pasqualetti, and J. Cortés, “Scheduling of control nodes for improved network controllability , ” in IEEE Conf. on Decision and Contr ol , 2016, pp. 1859–1864. [26] L. F . Chamon, G. J. Pappas, and A. Ribeiro, “The mean square error in kalman filtering sensor selection is approximately supermodular, ” in IEEE Conf. on Decision and Contr ol , 2017, pp. 343–350. [27] V . Tzoumas, A. Jadbabaie, and G. J. P appas, “Sensor placement for optimal Kalman filtering, ” in Amer . Contr . Conf. , 2016, pp. 191–196. [28] A. Clark, L. Bushnell, and R. Poov endran, “On leader selection for performance and controllability in multi-agent systems, ” in IEEE 51st IEEE Conference on Decision and Control , 2012, pp. 86–93. [29] A. Clark, B. Alomair, L. Bushnell, and R. Poovendran, “Input selection for performance and controllability of structured linear descriptor sys- tems, ” SIAM J ournal on Contr ol and Optimization , vol. 55, no. 1, pp. 457–485, 2017. [30] Z. Liu, Y . Long, A. Clark, P . Lee, L. Bushnell, D. Kirschen, and R. Poov endran, “Minimal input selection for robust control, ” in IEEE 56th Annual Conference on Decision and Control , 2017, pp. 2659–2966. [31] S. Pequito, S. Kar, and A. P . Aguiar, “ A framework for structural input/output and control configuration selection in large-scale systems, ” IEEE T ransactions on Automatic Contr ol , vol. 61, no. 2, pp. 303–318, 2015. [32] T . H. Summers, F . L. Cortesi, and J. L ygeros, “On submodularity and controllability in complex dynamical networks, ” IEEE T ransactions on Contr ol of Network Systems , vol. 3, no. 1, pp. 91–101, 2016. [33] V . Tzoumas, M. A. Rahimian, G. J. Pappas, and A. Jadbabaie, “Minimal actuator placement with bounds on control effort, ” IEEE Tr ansactions on Contr ol of Network Systems , vol. 3, no. 1, pp. 67–78, 2015. [34] T . Summers and M. Kamgarpour , “Performance guarantees for greedy maximization of non-submodular set functions in systems and control, ” arXiv preprint:1712.04122 , 2017. [35] T . Summers and J. Ruths, “Performance bounds for optimal feedback control in networks, ” in American Control Confer ence , 2018, pp. 203– 209. [36] E. Nozari, F . Pasqualetti, and J. Cortés, “T ime-inv ariant versus time- varying actuator scheduling in complex networks, ” in American Control Confer ence , 2017, pp. 4995–5000. [37] A. F . T aha, N. Gatsis, T . Summers, and S. Nugroho, “Time-v arying sensor and actuator selection for uncertain cyber-physical systems, ” IEEE T ransactions on Contr ol of Network Systems , vol. 6, no. 2, pp. 750–762, 2019. [38] A. Clark, B. Alomair , L. Bushnell, and R. Poovendran, Submodularity in dynamics and control of networked systems . Springer, 2017. [39] A. Chakrabortty and C. F . Martin, “Optimal measurement allocation algorithms for parametric model identification of power systems, ” IEEE T ransactions on Contr ol Systems T ec hnology , vol. 22, no. 5, pp. 1801– 1812, 2014. [40] C. P . Moreno, H. Pfifer, and G. J. Balas, “ Actuator and sensor selection for robust control of aeroservoelastic systems, ” in American Contr ol Confer ence , 2015, pp. 1899–1904. [41] K. Lim, “Method for optimal actuator and sensor placement for large flexible structures, ” J ournal of Guidance, Control, and Dynamics , vol. 15, no. 1, pp. 49–57, 1992. [42] D. Zelazo, “Graph-theoretic methods for the analysis and synthesis of networked dynamic systems, ” Ph.D. dissertation, Uni versity of W ash- ington. [43] A. Das and D. Kempe, “Submodular meets spectral: Greedy algorithms for subset selection, sparse approximation and dictionary selection, ” in Intl. Conf. on Machine Learning , 2011, pp. 1057–1064. [44] Z. W ang, B. Moran, X. W ang, and Q. Pan, “ Approximation for maxi- mizing monotone non-decreasing set functions with a greedy method, ” Journal of Combinatorial Optimization , vol. 31, no. 1, pp. 29–43, 2016. [45] M. Sviridenko, J. V ondrák, and J. W ard, “Optimal approximation for submodular and supermodular optimization with bounded curvature, ” arXiv preprint:1311.4728 , 2013. [46] ——, “Optimal approximation for submodular and supermodular opti- mization with bounded curvature, ” Mathematics of Operations Researc h , vol. 42, no. 4, pp. 1197–1218, 2017. [47] G. Nemhauser , L. W olsey , and M. Fisher, “ An analysis of approximations for maximizing submodular set functions – I, ” Mathematical Pr ogram- ming , vol. 14, no. 1, pp. 265–294, 1978. [48] L. A. W olsey , “ An analysis of the greedy algorithm for the submodular set covering problem, ” Combinatorica , vol. 2, no. 4, pp. 385–393, 1982. [49] S. Khuller, A. Moss, and J. S. Naor, “The budgeted maximum coverage problem, ” Info. Pr ocessing Letters , vol. 70, no. 1, pp. 39–45, 1999. [50] M. Sviridenko, “ A note on maximizing a submodular set function subject to a knapsack constraint, ” Operations Researc h Letters , vol. 32, no. 1, pp. 41–43, 2004. [51] A. Krause and C. Guestrin, “ A note on the budgeted maximization of submodular functions, ” 2005. [52] V . Tzoumas, L. Carlone, G. J. Pappas, and A. Jadbabaie, “Sensing- constrained LQG control, ” in American Control Confer ence , 2018. [53] B. Lehmann, D. Lehmann, and N. Nisan, “Combinatorial auctions with decreasing marginal utilities, ” Games and Economic Behavior , vol. 55, no. 2, pp. 270–296, 2006. [54] L. F . Chamon and A. Ribeiro, “Near-optimality of greedy set selection in the sampling of graph signals, ” in IEEE Global Conference on Signal 16 and Information Processing , 2016, pp. 1265–1269. [55] A. Hashemi, M. Ghasemi, H. V ikalo, and U. T opcu, “Submodular observation selection and information gathering for quadratic models, ” in Intl. Conf. on Machine Learning , 2019, pp. 2653–2662. [56] B. Guo, O. Karaca, T . Summers, and M. Kamgarpour , “ Actuator placement for optimizing network performance under controllability constraints, ” arXiv pr eprint:1903.08120 , 2019. [57] U. Feige, “ A threshold of ln ( n ) for approximating set cover , ” Journal of the ACM , vol. 45, no. 4, pp. 634–652, 1998. [58] M. Sviridenko, “ A note on maximizing a submodular set function subject to a knapsack constraint, ” Operations Researc h Letters , vol. 32, no. 1, pp. 41–43, 2004. [59] H. Nguyen and R. Zheng, “On budgeted influence maximization in social networks, ” IEEE Journal on Selected Areas in Communications , vol. 31, no. 6, pp. 1084–1094, 2013. [60] R. K. Iyer and J. A. Bilmes, “Submodular optimization with submodular cover and submodular knapsack constraints, ” in Advances in Neural Information Pr ocessing Systems , 2013, pp. 2436–2444. [61] H. Zhang and Y . V orobeychik, “Submodular optimization with routing constraints, ” in AAAI Conference on Artificial Intelligence , 2016. [62] C. Qian, J.-C. Shi, Y . Y u, and K. T ang, “On subset selection with general cost constraints, ” in International Joint Confer ence on Artificial Intelligence , 2017, pp. 2613–2619. [63] J. Leskovec, A. Krause, C. Guestrin, C. Faloutsos, C. Faloutsos, J. V an- Briesen, and N. Glance, “Cost-effectiv e outbreak detection in networks, ” in ACM SIGKDD international confer ence on Knowledge discovery and data mining , 2007, pp. 420–429. [64] V . Tzoumas, L. Carlone, G. J. Pappas, and A. Jadbabaie, “Sensing- constrained LQG Control, ” arXiv preprint: 1709.08826 , 2017. [65] ——, “LQG control and sensing co-design, ” arXiv preprint:1802.08376 , 2018. [66] L. Y e, S. Ro y , and S. Sundaram, “On the complexity and approximability of optimal sensor selection for Kalman filtering, ” in American Contr ol Confer ence , 2018, pp. 5049–5054. [67] A. Krause and V . Cevher , “Submodular dictionary selection for sparse representation, ” in International Confer ence on Mac hine Learning , 2010. [68] M. Siami and A. Jadbabaie, “Deterministic polynomial-time actuator scheduling with guaranteed performance, ” in European Control Confer- ence , 2018, pp. 113–118. [69] V . Tzoumas, K. Gatsis, A. Jadbabaie, and G. J. Pappas, “Resilient monotone submodular maximization, ” in IEEE Conf. on Decision and Contr ol , 2017. [70] D. S. Bernstein, Matrix mathematics . Princeton Univ ersity Press, 2005. [71] V . Tzoumas, A. Jadbabaie, and G. J. Pappas, “Near-optimal sensor scheduling for batch state estimation: Complexity , algorithms, and limits, ” in IEEE Conference on Decision and Contr ol , 2016, pp. 2695– 2702. V asileios Tzoumas (S’12-M’18) starts as an Assis- tant Professor at the Univ ersity of Michigan, Ann Arbor , on January 2021. Currently , he is a research scientist at the Department of Aeronautics and As- tronautics, and the Laboratory for Information and Decision Systems (LIDS) at MIT , where he previ- ously was a post-doctoral associate. He recei ved his Ph.D. at the Department of Electrical and Systems Engineering, Uni versity of Pennsylvania (2018). He was a visiting Ph.D. student at the MIT Institute for Data, Systems, and Society in 2017. He holds a diploma in Electrical and Computer Engineering from the National T echnical Univ ersity of Athens (2012); a Master of Science in Electrical Engineering from the University of Pennsylvania (2016); and a Master of Arts in Statistics from the Wharton School of Business at the University of Pennsylvania (2016). His research interests include control theory , perception, learning, and combinatorial and non-conve x optimization, with applications to robotics, resource-constrained c yber-physical systems, and unmanned aerospace sys- tems. He aims for a prov ably trustworthy autonomy . His work includes seminal results on provably optimal resilient combinatorial optimization, with applications to multi-robot information gathering for resiliency against robotic failures and adversarial removals. Dr . Tzoumas was a Best Student Paper A w ard finalist at the 56th IEEE Conference in Decision and Control (2017), and a Best Paper A ward finalist in Robotic V ision at the 2020 IEEE International Conference on Robotics and Automation (ICRA). Luca Carlone is the Charles Stark Draper Assistant Professor in the Department of Aeronautics and As- tronautics at the Massachusetts Institute of T echnol- ogy , and a Principal Inv estigator in the Laboratory for Information & Decision Systems (LIDS). He has obtained a B.S. degree in mechatronics from the Polytechnic Univ ersity of Turin, Italy , in 2006; an S.M. degree in mechatronics from the Polytechnic Univ ersity of T urin, Italy , in 2008; an S.M. degree in automation engineering from the Polytechnic Uni- versity of Milan, Italy , in 2008; and a Ph.D. degree in robotics also the Polytechnic Univ ersity of T urin in 2012. He joined LIDS as a postdoctoral associate (2015) and later as a Research Scientist (2016), after spending two years as a postdoctoral fellow at the Georgia Institute of T echnology (2013-2015). His research interests include nonlinear estimation, numerical and distributed optimization, and probabilistic inference, applied to sensing, perception, and decision-making in single and multi-robot systems. His work includes seminal results on certifiably correct algorithms for localization and mapping, as well as approaches for visual inertial na vigation and distributed mapping. He is a recipient of the 2017 T ransactions on Robotics King-Sun Fu Memorial Best Paper A ward, the Best Paper award at W AFR 2016, the Best Student P aper award at the 2018 Symposium on VLSI Circuits, and was best paper finalist at RSS 2015 and ICRA 2020. George J. Pappas (S’90-M’91-SM’04-F’09) re- ceiv ed the Ph.D. degree in electrical engineering and computer sciences from the University of Cal- ifornia, Berkeley , CA, USA, in 1998. He is cur- rently the Joseph Moore Professor and Chair of the Department of Electrical and Systems Engineering, Univ ersity of Pennsylvania, Philadelphia, P A, USA. He also holds a secondary appointment with the Department of Computer and Information Sciences and the Department of Mechanical Engineering and Applied Mechanics. He is a Member of the GRASP Lab and the PRECISE Center . He had previously served as the Deputy Dean for Research with the School of Engineering and Applied Science. His research interests include control theory and, in particular , hybrid systems, embedded systems, cyberphysical systems, and hierarchical and distributed control systems, with applications to unmanned aerial vehicles, distributed robotics, green buildings, and biomolecular networks. Dr . Pappas has received various awards, such as the Antonio Ruberti Y oung Researcher Prize, the George S. Axelby A w ard, the Hugo Schuck Best Paper A ward, the George H. Heilmeier A ward, the National Science Foundation PECASE award and numerous best student papers awards. Ali Jadbabaie (S’99-M’08-SM’13-F’15) is the JR East Professor of Engineering and Associate Direc- tor of the Institute for Data, Systems and Society at MIT , where he is also on the faculty of the department of ci vil and en vironmental engineering and a principal inv estigator in the Laboratory for Information and Decision Systems (LIDS). He is the director of the Sociotechnical Systems Research Center , one of MIT’ s 13 laboratories. He recei ved his Bachelors (with high honors) from Sharif University of T echnology in T ehran, Iran, a Masters degree in electrical and computer engineering from the Univ ersity of New Mexico, and his Ph.D. in control and dynamical systems from the California Institute of T echnology . He was a postdoctoral scholar at Y ale University before joining the faculty at Penn in July 2002. Prior to joining MIT faculty , he was the Alfred Fitler Moore a Professor of Netw ork Science and held secondary appointments in computer and information science and operations, information and decisions in the Wharton School. He was the inaugural editor-in-chief of IEEE Transactions on Network Science and Engineering, a new interdisciplinary journal sponsored by several IEEE societies. He is a recipient of a National Science Foundation Career A ward, an Office of Naval Research Y oung In vestigator A ward, the O. Hugo Schuck Best Paper A ward from the American Automatic Control Council, and the George S. Axelby Best Paper A ward from the IEEE Control Systems Society . His students hav e been winners and finalists of student best paper awards at various A CC and CDC conferences. He is an IEEE fellow and a recipient of the V annevar Bush Fellowship from the office of Secretary of Defense. His current research interests include the interplay of dynamic systems and networks with specific emphasis on multi-agent coordination and control, distributed optimization, network science, and network economics.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment